Cryptography Computations plaintext encrypt ciphertext By Jorge L
Cryptography Computations plaintext encrypt ciphertext By: Jorge L. Salazar 3/8/2021 1
Outline Cryptography n Traditional cryptography, statistical attacks, Secretkey encryption, Public-key encryption RSA cryptosystem (§ 10. 2. 3) n n Euler’s theorem, Algorithms for RSA Modular power, Modular inverse Rabin and El. Gamal public key algorithms 3/8/2021 2
Encryption Scenario: n n Alice wants to send a message (plaintext p) to Bob. The communication channel is insecure and can be eavesdropped If Alice and Bob have previously agreed on an encryption scheme (cipher), the message can be sent encrypted (ciphertext c) Issues: n n What is a good encryption scheme? What is the complexity of encrypting/decrypting? What is the size of the ciphertext, relative to the plaintext? If Alice and Bob have never interacted before, how can they agree on an encryption scheme? plaintext 3/8/2021 encrypt ciphertext decrypt plaintext 3
Traditional Cryptography Ciphers were already studied in ancient times Caesar’s cipher: n n replace a with d replace b with e. . . replace z with c Caesar’s cipher is an example of a monoalphabetic substitution cipher, which permutes the characters Armed with simple statistical knowledge, one can easily break a monoalphabetic substitution cipher n n n most frequent letters in English: e, t, o, a, n, i, . . . most frequent digrams: th, in, er, re, an, . . . most frequent trigrams: the, ing, and, ion, . . . The first description of the frequency analysis attack appears in a book written in the 9 th century by the Arab philosopher al-Kindi 3/8/2021 4
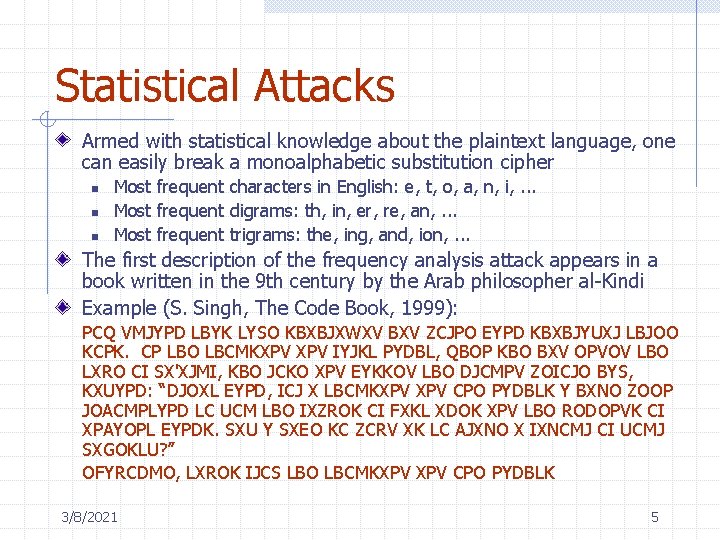
Statistical Attacks Armed with statistical knowledge about the plaintext language, one can easily break a monoalphabetic substitution cipher n n n Most frequent characters in English: e, t, o, a, n, i, . . . Most frequent digrams: th, in, er, re, an, . . . Most frequent trigrams: the, ing, and, ion, . . . The first description of the frequency analysis attack appears in a book written in the 9 th century by the Arab philosopher al-Kindi Example (S. Singh, The Code Book, 1999): PCQ VMJYPD LBYK LYSO KBXBJXWXV BXV ZCJPO EYPD KBXBJYUXJ LBJOO KCPK. CP LBO LBCMKXPV IYJKL PYDBL, QBOP KBO BXV OPVOV LBO LXRO CI SX'XJMI, KBO JCKO XPV EYKKOV LBO DJCMPV ZOICJO BYS, KXUYPD: “DJOXL EYPD, ICJ X LBCMKXPV CPO PYDBLK Y BXNO ZOOP JOACMPLYPD LC UCM LBO IXZROK CI FXKL XDOK XPV LBO RODOPVK CI XPAYOPL EYPDK. SXU Y SXEO KC ZCRV XK LC AJXNO X IXNCMJ CI UCMJ SXGOKLU? ” OFYRCDMO, LXROK IJCS LBO LBCMKXPV CPO PYDBLK 3/8/2021 5
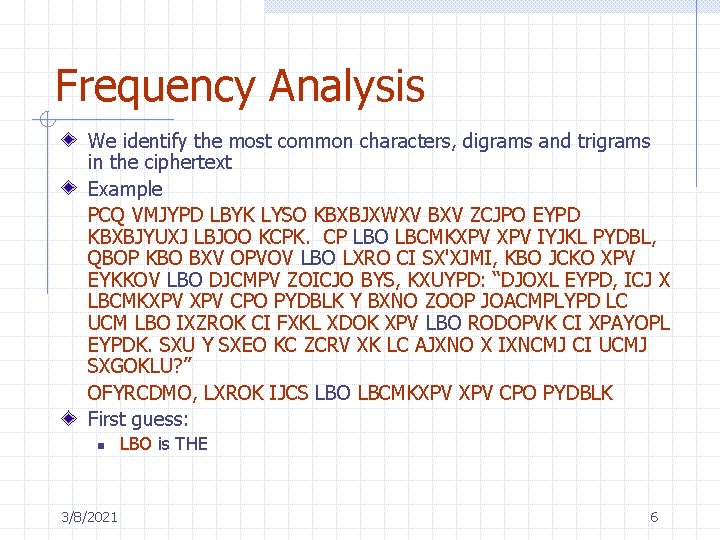
Frequency Analysis We identify the most common characters, digrams and trigrams in the ciphertext Example PCQ VMJYPD LBYK LYSO KBXBJXWXV BXV ZCJPO EYPD KBXBJYUXJ LBJOO KCPK. CP LBO LBCMKXPV IYJKL PYDBL, QBOP KBO BXV OPVOV LBO LXRO CI SX'XJMI, KBO JCKO XPV EYKKOV LBO DJCMPV ZOICJO BYS, KXUYPD: “DJOXL EYPD, ICJ X LBCMKXPV CPO PYDBLK Y BXNO ZOOP JOACMPLYPD LC UCM LBO IXZROK CI FXKL XDOK XPV LBO RODOPVK CI XPAYOPL EYPDK. SXU Y SXEO KC ZCRV XK LC AJXNO X IXNCMJ CI UCMJ SXGOKLU? ” OFYRCDMO, LXROK IJCS LBO LBCMKXPV CPO PYDBLK First guess: n 3/8/2021 LBO is THE 6
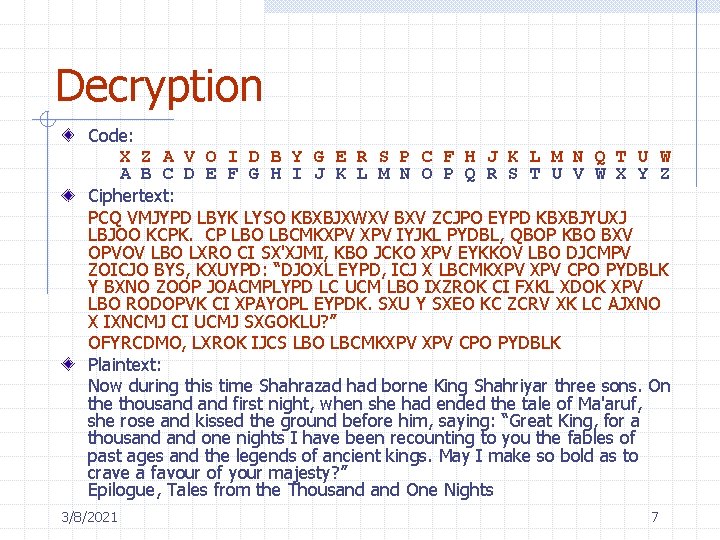
Decryption Code: X Z A V O I D B Y G E R S P C F H J K L M N Q T U W A B C D E F G H I J K L M N O P Q R S T U V W X Y Z Ciphertext: PCQ VMJYPD LBYK LYSO KBXBJXWXV BXV ZCJPO EYPD KBXBJYUXJ LBJOO KCPK. CP LBO LBCMKXPV IYJKL PYDBL, QBOP KBO BXV OPVOV LBO LXRO CI SX'XJMI, KBO JCKO XPV EYKKOV LBO DJCMPV ZOICJO BYS, KXUYPD: “DJOXL EYPD, ICJ X LBCMKXPV CPO PYDBLK Y BXNO ZOOP JOACMPLYPD LC UCM LBO IXZROK CI FXKL XDOK XPV LBO RODOPVK CI XPAYOPL EYPDK. SXU Y SXEO KC ZCRV XK LC AJXNO X IXNCMJ CI UCMJ SXGOKLU? ” OFYRCDMO, LXROK IJCS LBO LBCMKXPV CPO PYDBLK Plaintext: Now during this time Shahrazad had borne King Shahriyar three sons. On the thousand first night, when she had ended the tale of Ma'aruf, she rose and kissed the ground before him, saying: “Great King, for a thousand one nights I have been recounting to you the fables of past ages and the legends of ancient kings. May I make so bold as to crave a favour of your majesty? ” Epilogue, Tales from the Thousand One Nights 3/8/2021 7
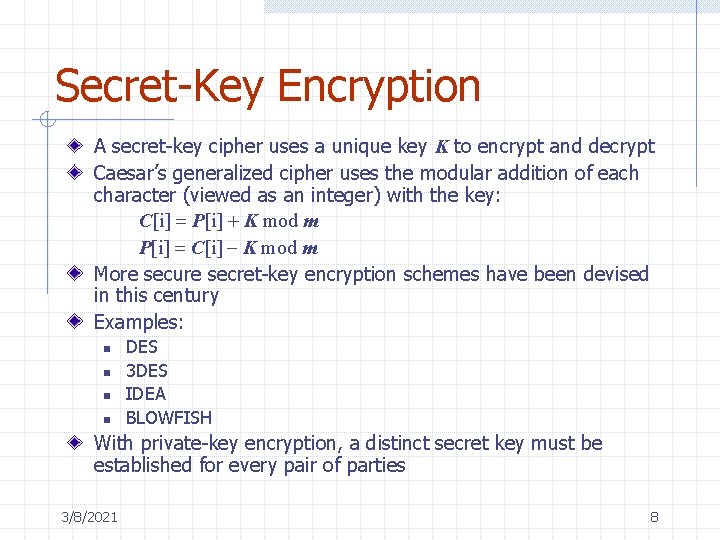
Secret-Key Encryption A secret-key cipher uses a unique key K to encrypt and decrypt Caesar’s generalized cipher uses the modular addition of each character (viewed as an integer) with the key: C[i] = P[i] + K mod m P[i] = C[i] - K mod m More secure secret-key encryption schemes have been devised in this century Examples: n n DES 3 DES IDEA BLOWFISH With private-key encryption, a distinct secret key must be established for every pair of parties 3/8/2021 8
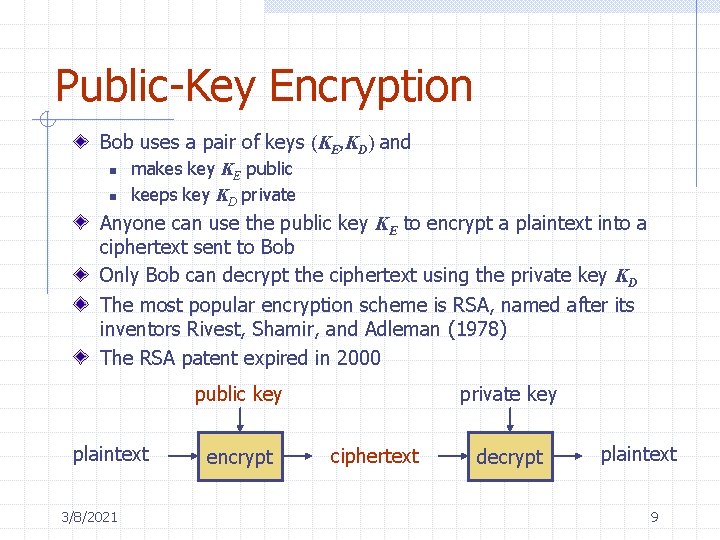
Public-Key Encryption Bob uses a pair of keys (KE, KD) and n n makes key KE public keeps key KD private Anyone can use the public key KE to encrypt a plaintext into a ciphertext sent to Bob Only Bob can decrypt the ciphertext using the private key KD The most popular encryption scheme is RSA, named after its inventors Rivest, Shamir, and Adleman (1978) The RSA patent expired in 2000 public key plaintext 3/8/2021 encrypt private key ciphertext decrypt plaintext 9
Public-Key Encryption The concept of Public –key was invented by Whitfield D and Martin Hellmann in 1970. The first public-key algorithm was DES (Data encryption Standard, I was a standard for 15 years. Schemes: n RSA n Rabin n El Gamal n Knapsack 3/8/2021 10
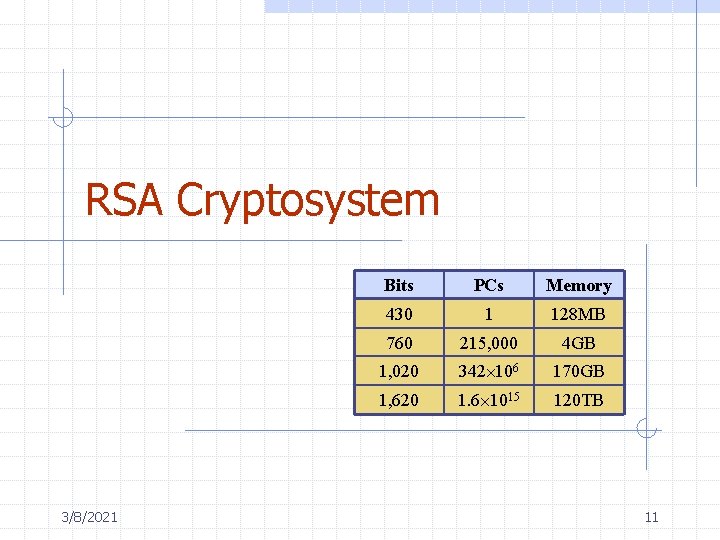
RSA Cryptosystem 3/8/2021 Bits PCs Memory 430 1 128 MB 760 215, 000 4 GB 1, 020 342 106 170 GB 1, 620 1. 6 1015 120 TB 11
Outline Euler’s theorem (§ 10. 1. 3) RSA cryptosystem (§ 10. 2. 3) n n Definition Example Security Correctness Algorithms for RSA n n n 3/8/2021 Modular power (§ 10. 1. 4) Modular inverse (§ 10. 1. 5) Randomized primality testing (§ 10. 1. 6) 12
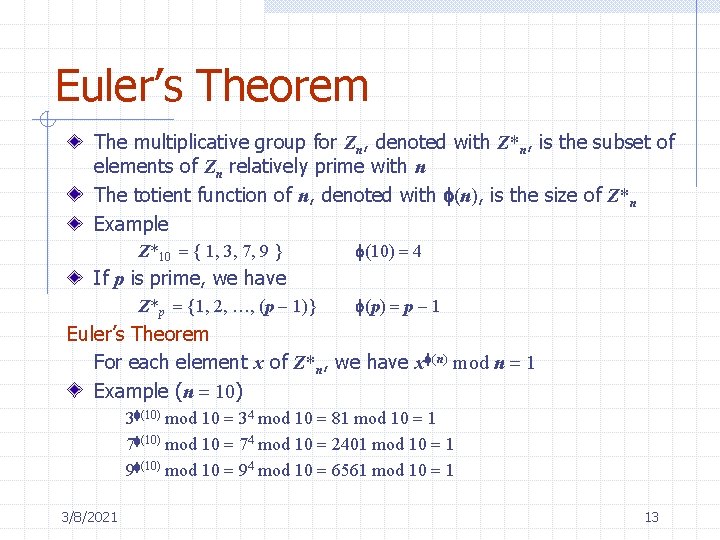
Euler’s Theorem The multiplicative group for Zn, denoted with Z*n, is the subset of elements of Zn relatively prime with n The totient function of n, denoted with f(n), is the size of Z*n Example Z*10 = { 1, 3, 7, 9 } f(10) = 4 If p is prime, we have Z*p = {1, 2, …, (p - 1)} f(p) = p - 1 Euler’s Theorem For each element x of Z*n, we have xf(n) mod n = 1 Example (n = 10) 3 f(10) mod 10 = 34 mod 10 = 81 mod 10 = 1 7 f(10) mod 10 = 74 mod 10 = 2401 mod 10 = 1 9 f(10) mod 10 = 94 mod 10 = 6561 mod 10 = 1 3/8/2021 13
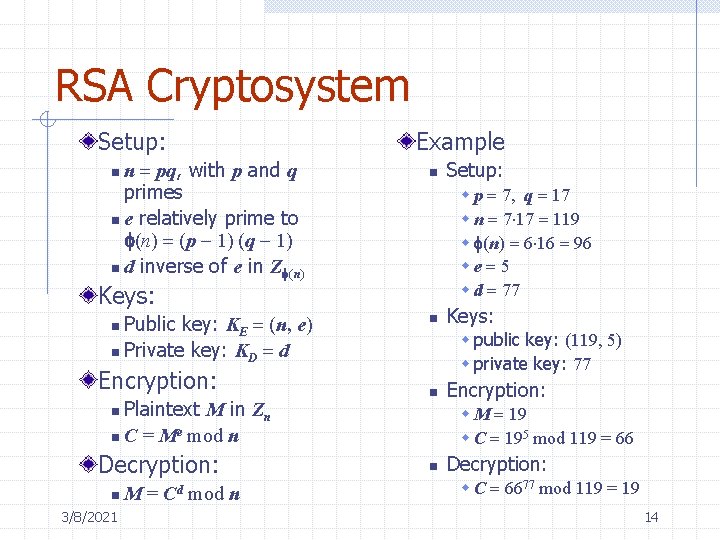
RSA Cryptosystem Setup: n = pq, with p and q primes n e relatively prime to f(n) = (p - 1) (q - 1) n d inverse of e in Zf(n) n Example n w p = 7, q = 17 w n = 7 17 = 119 w f(n) = 6 16 = 96 we = 5 w d = 77 Keys: Public key: KE = (n, e) n Private key: KD = d n Encryption: Plaintext M in Zn n C = Me mod n n n 3/8/2021 M = Cd mod n Keys: w public key: (119, 5) w private key: 77 n Encryption: w M = 19 w C = 195 mod 119 = 66 n Decryption: Setup: n Decryption: w C = 6677 mod 119 = 19 14
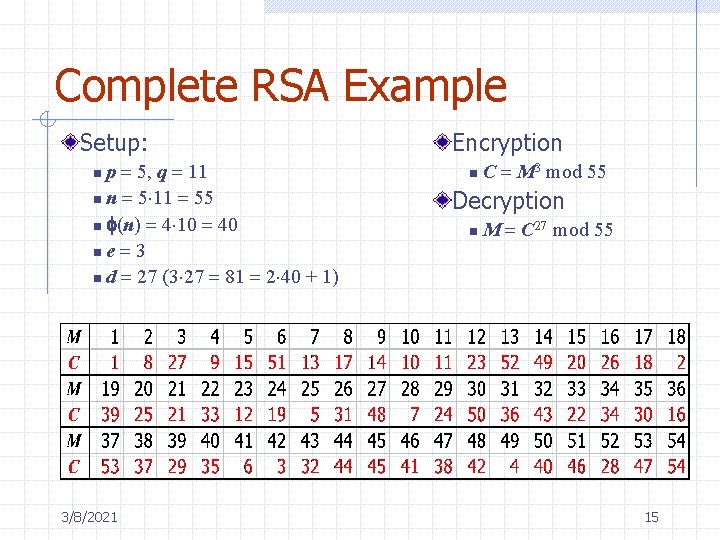
Complete RSA Example Setup: p = 5, q = 11 n n = 5 11 = 55 n f(n) = 4 10 = 40 ne = 3 n d = 27 (3 27 = 81 = 2 40 + 1) n 3/8/2021 Encryption n C = M 3 mod 55 Decryption n M = C 27 mod 55 15
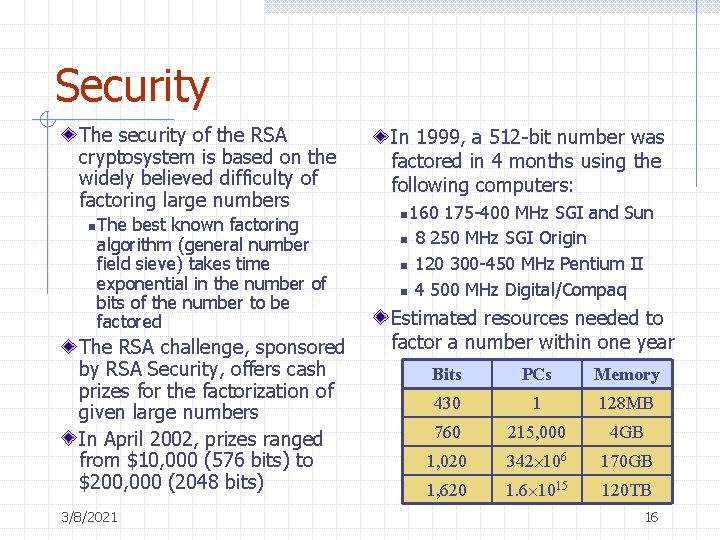
Security The security of the RSA cryptosystem is based on the widely believed difficulty of factoring large numbers n The best known factoring algorithm (general number field sieve) takes time exponential in the number of bits of the number to be factored The RSA challenge, sponsored by RSA Security, offers cash prizes for the factorization of given large numbers In April 2002, prizes ranged from $10, 000 (576 bits) to $200, 000 (2048 bits) 3/8/2021 In 1999, a 512 -bit number was factored in 4 months using the following computers: n 160 n n n 175 -400 MHz SGI and Sun 8 250 MHz SGI Origin 120 300 -450 MHz Pentium II 4 500 MHz Digital/Compaq Estimated resources needed to factor a number within one year Bits PCs Memory 430 1 128 MB 760 215, 000 4 GB 1, 020 342 106 170 GB 1, 620 1. 6 1015 120 TB 16
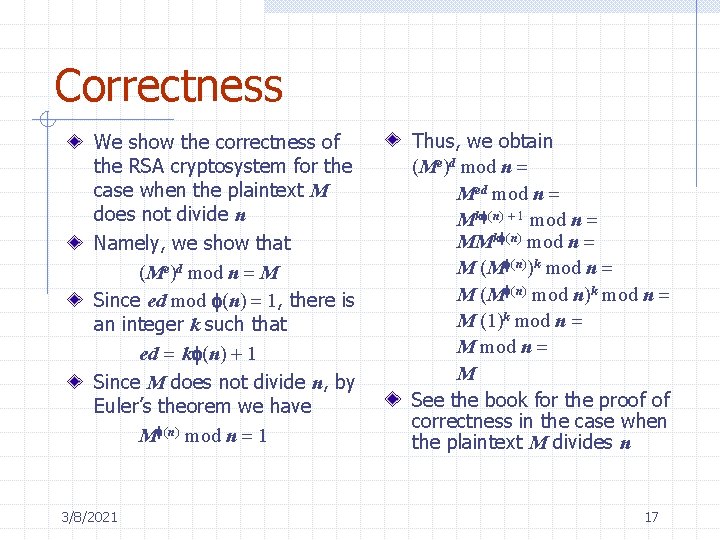
Correctness We show the correctness of the RSA cryptosystem for the case when the plaintext M does not divide n Namely, we show that (Me)d mod n = M Since ed mod f(n) = 1, there is an integer k such that ed = kf(n) + 1 Since M does not divide n, by Euler’s theorem we have Mf(n) mod n = 1 3/8/2021 Thus, we obtain (Me)d mod n = Med mod n = Mkf(n) + 1 mod n = MMkf(n) mod n = M (Mf(n))k mod n = M (Mf(n) mod n)k mod n = M (1)k mod n = M See the book for the proof of correctness in the case when the plaintext M divides n 17
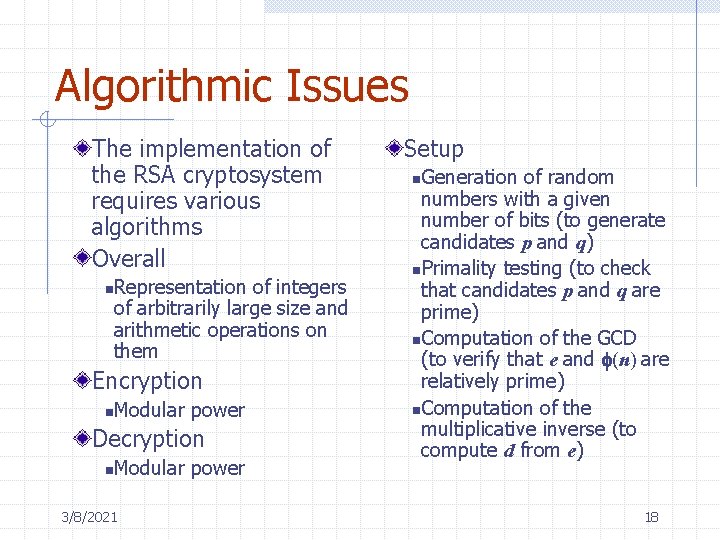
Algorithmic Issues The implementation of the RSA cryptosystem requires various algorithms Overall Representation of integers of arbitrarily large size and arithmetic operations on them n Encryption n Modular power Decryption n Modular power 3/8/2021 Setup Generation of random numbers with a given number of bits (to generate candidates p and q) n. Primality testing (to check that candidates p and q are prime) n. Computation of the GCD (to verify that e and f(n) are relatively prime) n. Computation of the multiplicative inverse (to compute d from e) n 18
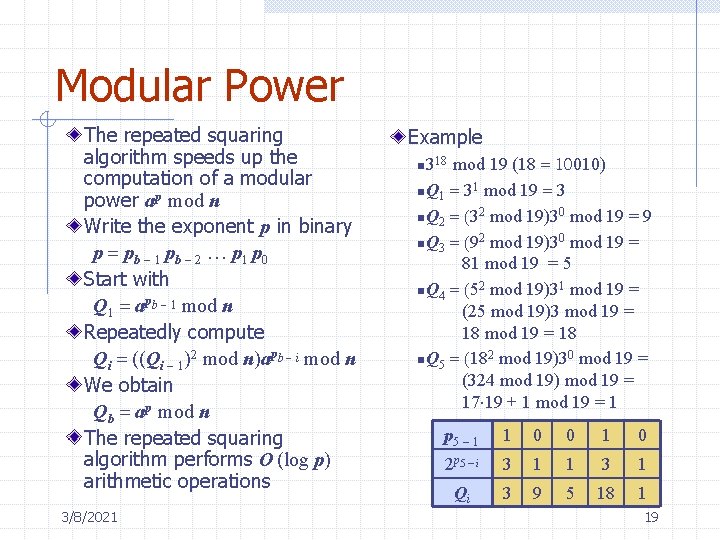
Modular Power The repeated squaring algorithm speeds up the computation of a modular power ap mod n Write the exponent p in binary p = pb - 1 pb - 2 … p 1 p 0 Start with Q 1 = apb - 1 mod n Repeatedly compute Qi = ((Qi - 1)2 mod n)apb - i mod n We obtain Qb = ap mod n The repeated squaring algorithm performs O (log p) arithmetic operations 3/8/2021 Example mod 19 (18 = 10010) n Q 1 = 31 mod 19 = 3 n Q 2 = (32 mod 19)30 mod 19 = 9 n Q 3 = (92 mod 19)30 mod 19 = 81 mod 19 = 5 n Q 4 = (52 mod 19)31 mod 19 = (25 mod 19)3 mod 19 = 18 n Q 5 = (182 mod 19)30 mod 19 = (324 mod 19) mod 19 = 17 19 + 1 mod 19 = 1 n 318 p 5 - 1 1 0 0 1 0 2 p 5 - i 3 1 1 3 1 Qi 3 9 5 18 1 19

Modular Inverse Theorem Given positive integers a and b, let d be the smallest positive integer such that d = ia + jb for some integers i and j. We have d = gcd(a, b) Example n n n 3/8/2021 a = 21 b = 15 d=3 i = 3, j = -4 3 = 3 21 + (-4) 15 = 63 - 60 = 3 Given positive integers a and b, the extended Euclid’s algorithm computes a triplet (d, i, j) such that n n d = gcd(a, b) d = ia + jb To test the existence of and compute the inverse of x Zn, we execute the extended Euclid’s algorithm on the input pair (x, n) Let (d, i, j) be the triplet returned d = ix + jn Case 1: d = 1 i is the inverse of x in Zn Case 2: d > 1 x has no inverse in Zn n 20
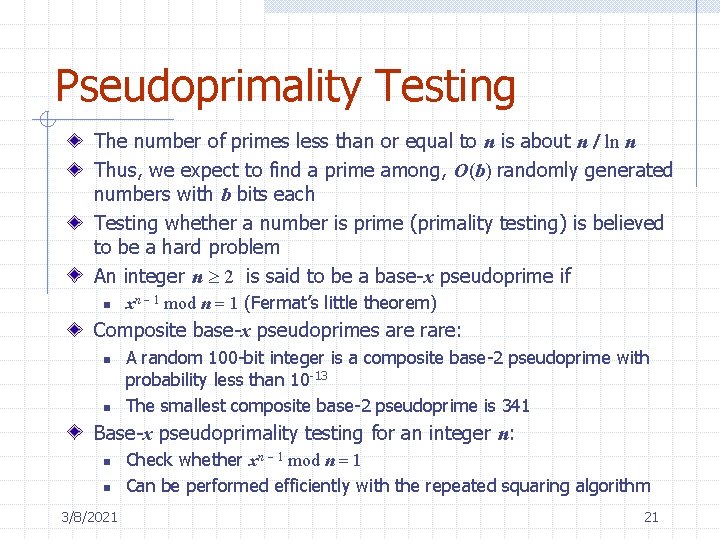
Pseudoprimality Testing The number of primes less than or equal to n is about n / ln n Thus, we expect to find a prime among, O(b) randomly generated numbers with b bits each Testing whether a number is prime (primality testing) is believed to be a hard problem An integer n 2 is said to be a base-x pseudoprime if n xn - 1 mod n = 1 (Fermat’s little theorem) Composite base-x pseudoprimes are rare: n n A random 100 -bit integer is a composite base-2 pseudoprime with probability less than 10 -13 The smallest composite base-2 pseudoprime is 341 Base-x pseudoprimality testing for an integer n: n n 3/8/2021 Check whether xn - 1 mod n = 1 Can be performed efficiently with the repeated squaring algorithm 21
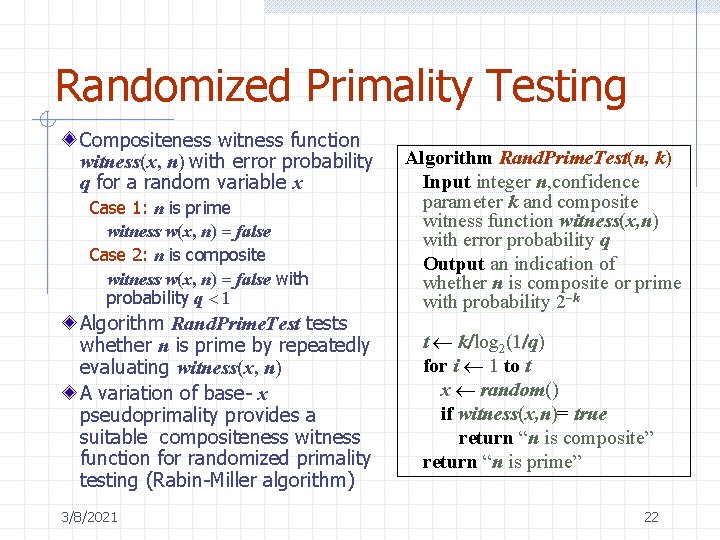
Randomized Primality Testing Compositeness witness function witness(x, n) with error probability q for a random variable x Case 1: n is prime witness w(x, n) = false Case 2: n is composite witness w(x, n) = false with probability q < 1 Algorithm Rand. Prime. Test tests whether n is prime by repeatedly evaluating witness(x, n) A variation of base- x pseudoprimality provides a suitable compositeness witness function for randomized primality testing (Rabin-Miller algorithm) 3/8/2021 Algorithm Rand. Prime. Test(n, k) Input integer n, confidence parameter k and composite witness function witness(x, n) with error probability q Output an indication of whether n is composite or prime with probability 2 -k t k/log 2(1/q) for i 1 to t x random() if witness(x, n)= true return “n is composite” return “n is prime” 22
Rabin and El. Gamal public-key encryption (Examples) 3/8/2021 23
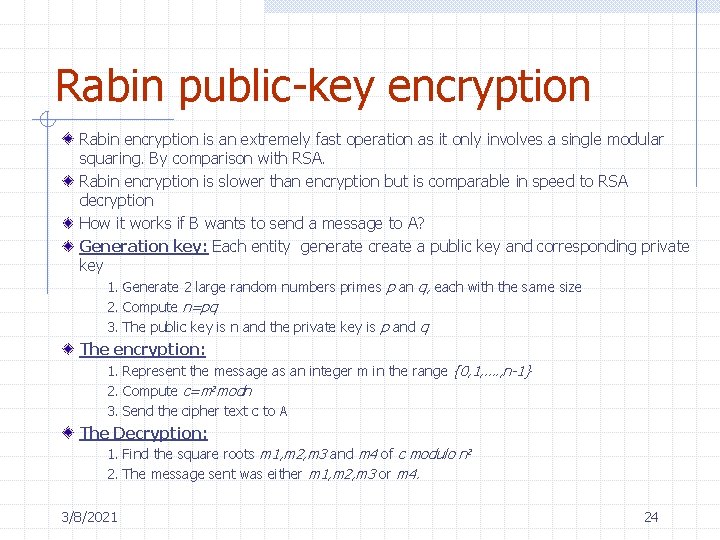
Rabin public-key encryption Rabin encryption is an extremely fast operation as it only involves a single modular squaring. By comparison with RSA. Rabin encryption is slower than encryption but is comparable in speed to RSA decryption How it works if B wants to send a message to A? Generation key: Each entity generate create a public key and corresponding private key 1. Generate 2 large random numbers primes p an q, each with the same size 2. Compute n=pq 3. The public key is n and the private key is p and q The encryption: 1. Represent the message as an integer m in the range {0, 1, …. , n-1} 2. Compute c=m 2 modn 3. Send the cipher text c to A The Decryption: 1. Find the square roots m 1, m 2, m 3 and m 4 of c modulo n 2 2. The message sent was either m 1, m 2, m 3 or m 4. 3/8/2021 24
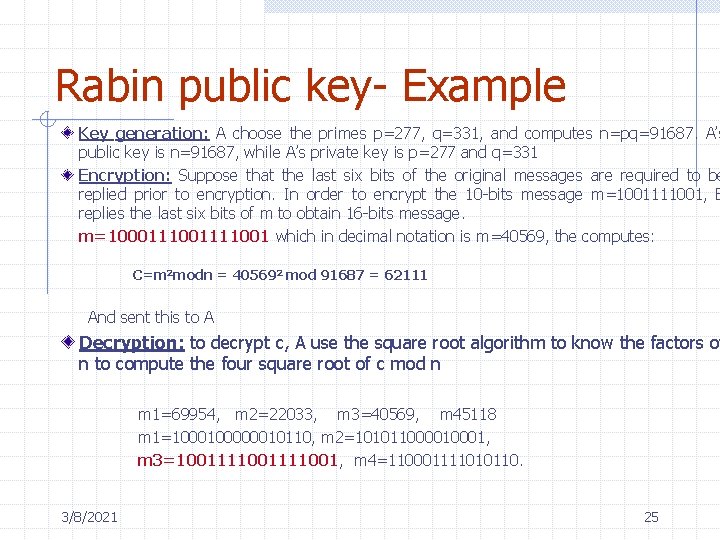
Rabin public key- Example Key generation: A choose the primes p=277, q=331, and computes n=pq=91687. A’s public key is n=91687, while A’s private key is p=277 and q=331 Encryption: Suppose that the last six bits of the original messages are required to be replied prior to encryption. In order to encrypt the 10 -bits message m=1001111001, B replies the last six bits of m to obtain 16 -bits message. m=10001111001 which in decimal notation is m=40569, the computes: C=m 2 modn = 405692 mod 91687 = 62111 And sent this to A Decryption: to decrypt c, A use the square root algorithm to know the factors of n to compute the four square root of c mod n m 1=69954, m 2=22033, m 3=40569, m 45118 m 1=100000010110, m 2=10101100001, m 3=1001111001, m 4=110001111010110. 3/8/2021 25
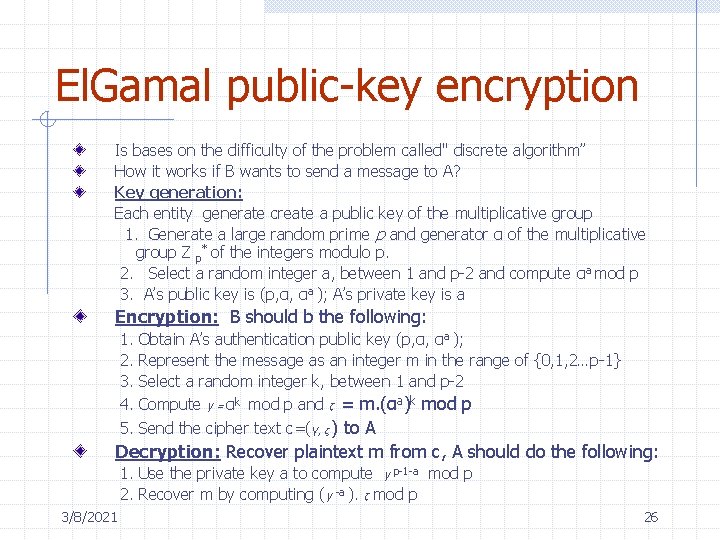
El. Gamal public-key encryption Is bases on the difficulty of the problem called" discrete algorithm” How it works if B wants to send a message to A? Key generation: Each entity generate create a public key of the multiplicative group 1. Generate a large random prime p and generator α of the multiplicative group Z p* of the integers modulo p. 2. Select a random integer a, between 1 and p-2 and compute αa mod p 3. A’s public key is (p, α, αa ); A’s private key is a Encryption: B should b the following: 1. 2. 3. 4. 5. Obtain A’s authentication public key (p, α, αa ); Represent the message as an integer m in the range of {0, 1, 2…p-1} Select a random integer k, between 1 and p-2 Compute γ = αk mod p and ζ = m. (αa)k mod p Send the cipher text c=(γ, ζ ) to A Decryption: Recover plaintext m from c, A should do the following: 1. Use the private key a to compute γ p-1 -a mod p 2. Recover m by computing (γ -a ). ζ mod p 3/8/2021 26
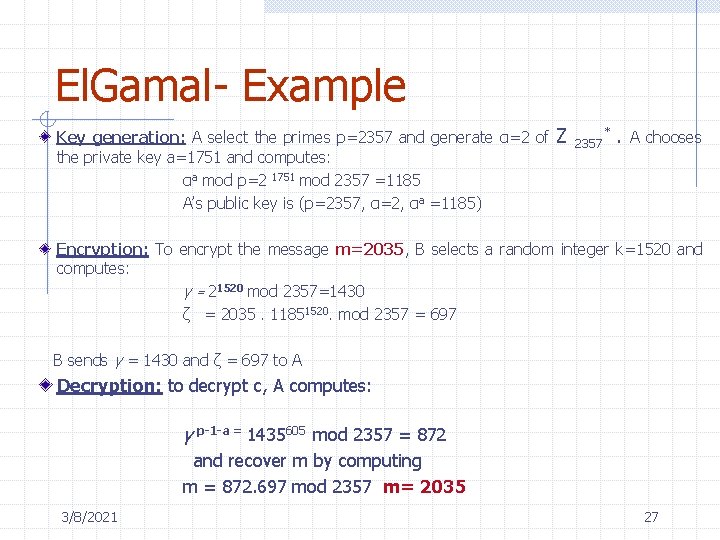
El. Gamal- Example Key generation: A select the primes p=2357 and generate α=2 of the private key a=1751 and computes: αa mod p=2 1751 mod 2357 =1185 A’s public key is (p=2357, α=2, αa =1185) Z 2357 * . A chooses Encryption: To encrypt the message m=2035, B selects a random integer k=1520 and computes: γ = 21520 mod 2357=1430 ζ = 2035. 11851520. mod 2357 = 697 B sends γ = 1430 and ζ = 697 to A Decryption: to decrypt c, A computes: γ p-1 -a = 1435605 mod 2357 = 872 and recover m by computing m = 872. 697 mod 2357 m= 2035 3/8/2021 27
Conclusions Fundaments of theory of cryptography and several powerful algorithms to protect the data integrity, authenticating, authorization and confidentiality were discussed during this presentation. A variety of cryptographic techniques have been developed to support the communications an insecure network. The goal of this presentation is present the Fundaments of theory of cryptography and several powerful algorithms to protect the data integrity, authenticating, authorization and confidentiality. 3/8/2021 28
- Slides: 28