BASIC INTERNET TERMINOLOGY World Wide Web The World
BASIC INTERNET TERMINOLOGY
World Wide Web The World Wide Web- the multimedia part of the internet: is usually called simply the ‘web’, an interconnected system of internet computer(called server) that supports specially formatted documents in multimedia form. The word multimedia, from ‘multiple media’ refers to technology that presents information in more than one medium, such as text, still images, moving images, and sound. In other words, the web provides information in more than one way. Hyper. Text Transfer Protocol(HTTP) The communications rules that allow browsers to connect with web servers. Most browsers assume that all web addresses begin with http: // , and so you don’t need to type this part; just start with whatever follows, such as www.
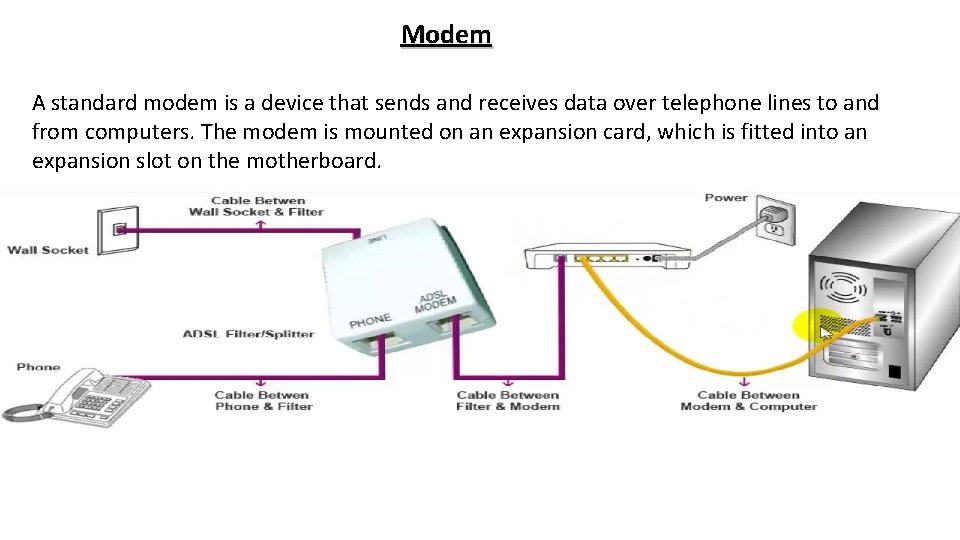
Modem A standard modem is a device that sends and receives data over telephone lines to and from computers. The modem is mounted on an expansion card, which is fitted into an expansion slot on the motherboard.
Bandwidth is an expression of how much data- text, voice, video, and so on- can be sent through a communications channel in a given amount of time. A college dormitory wired with coaxial or fiber-optic cable for high-speed internet access will have more bandwidth than will a house out in the country served by conventional copper-wire telephone lines. Internet Service Provider(ISP): -A company that connects you through your communications line to its servers, or central (host) computer, which connects you to the internet via another company’s networks access points. Some well known national ISPs, also called online services, are America Online(AOL), Earth. Link, Microsoft Networks(MNS), and AT&T World. Net. The ISPs local access number for your area is its point of presence(POP).
Internet Protocol: - Every computer on the internet has an Internet Protocol(IP) address that consists of four sets of numbers between 0 and 255 separated by decimals- for example, 1. 160. 10. 240. Each time you connect to your ISP, the ISP will assign your computer a new IP address, called a Dynamic IP Address, for your online session. When you request data from the internet, it is transmitted to your computer’s IP address. Transmission Control Protocol/ Internet Protocol: - The protocol that enables all the computers to use data transmitted on the internet is called Transmission Control Protocol/ Internet Protocol, or TCP/IP. This protocol determines: � The type of built-in error checking to be used, � The data, compression method, if any, � How the sending device will indicate that it has finished sending a message, � How the receiving device will indicate that it has received a message. TCP/IP breaks data into packets, which are largest blocks of data that can be sent across the internet. IP is used to send the packets across the internet to their final destination and TCP is used to reassemble the packets in the correct order. Internet computers use TCP/IP for all internet transactions, from sending email to downloading stock quotes or pictures off a friend’s website.
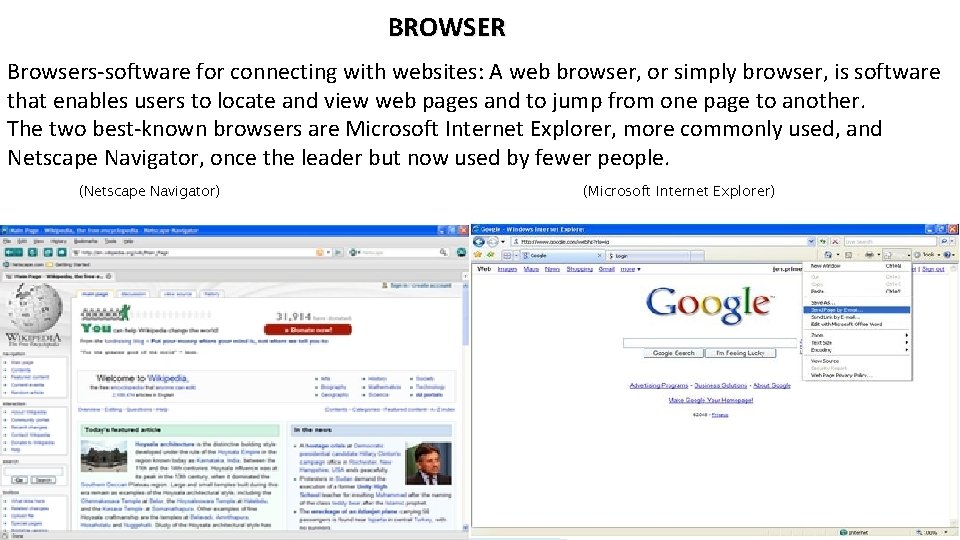
BROWSER Browsers-software for connecting with websites: A web browser, or simply browser, is software that enables users to locate and view web pages and to jump from one page to another. The two best-known browsers are Microsoft Internet Explorer, more commonly used, and Netscape Navigator, once the leader but now used by fewer people. (Netscape Navigator) (Microsoft Internet Explorer)
SEARCH ENGINES When you use a keyword to search for a topic, you are using a piece of software known as a search engine. Whereas directories are lists of websites classified by topic (as offered by portals), search engines allow you to find specific documents through keyword searches and menu choices. The type of search engines you use depends on what you’re looking for. Four types of Search Engines: � Human-Organized � Computer Created � Hybrid � Metasearch
1) Human-organized search site: -If you’re looking for a biography of Apple Computer founder Steve Jobs, a search engine based on human judgement is probably your best bet. Whereas computers can’t discriminate in organizing data, humans can judge data for relevance and categorize items in ways that are useful to you. 2) Computer-created Search Sites: -If you want to see what things show up next to Steve Job’s name or every instance in which it appears, a computer-created search site may be best. Examples of this type are Google, Excite and Web. Crawler. Google ranks listing by popularity as well as by how well they match the request. 3) Hybrid Search Sites: - Hybrid sites generally use human organizations supplemented by computer created indexes. Many of the principal sites are now hybrid: AOL search, Alta. Vista, Lycos, MNS Search, Ask Jeeves, and Snap. 4) Metasearch Sites: -Metasearch sites send your query to several other different search tools and compile the results so as to present the broadest view. Examples are Copernic, Meta. Crawler, and Dogpile.
FILE TRANSFER PROTOCOL FTP (File Transfer Protocol) is a method whereby you can connect to a remote computer called an FTP site and transfer files to your own microcomputer’s hard disk via TCI/IP over the internet. Some FTP files are open to the public(at anonymous FTP sites), some are not. For instance, a university might maintain an FTP site with private files(such as lecture transcripts) available only to professors and students with assigned user names and passwords. It might also have public FTP files open to anyone, with an email address. You can download FTP files using either your web browser or special software (called an FTP client program), such as Fetch, Cute, and FTP pro.
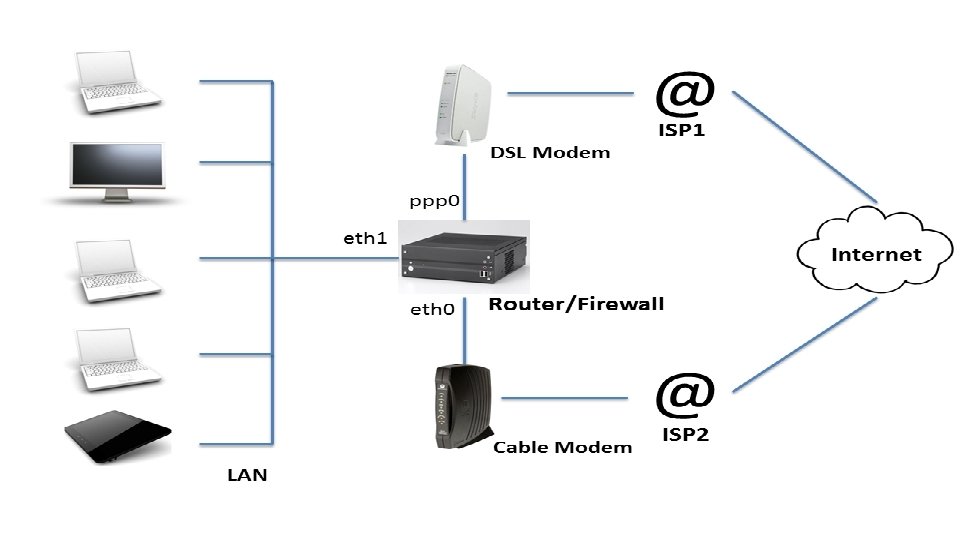
ROUTERS A router is a networking device that forwards data packets between computer networks. Routers perform the traffic directing functions on the Internet. Data sent through the internet, such as a web page or email, is in the form of data packets. A packet is typically forwarded from one router to another router through the networks that constitute an internetwork (e. g. the Internet) until it reaches its destination node. A router is connected to two or more data lines from different IP networks. When a data packet comes in on one of the lines, the router reads the network address information in the packet header to determine the ultimate destination. Then, using information in its routing table or routing policy, it directs the packet to the next network on its journey. The most familiar type of IP routers are home and small office routers that simply forward IP packets between the home computers and the Internet. An example of a router would be the owner's cable or DSL router, which connects to the Internet through an Internet service provider(ISP). More sophisticated routers, such as enterprise routers, connect large business or ISP networks up to the powerful core routers that forward data at high speed along the optical fiber lines of the Internet backbone.
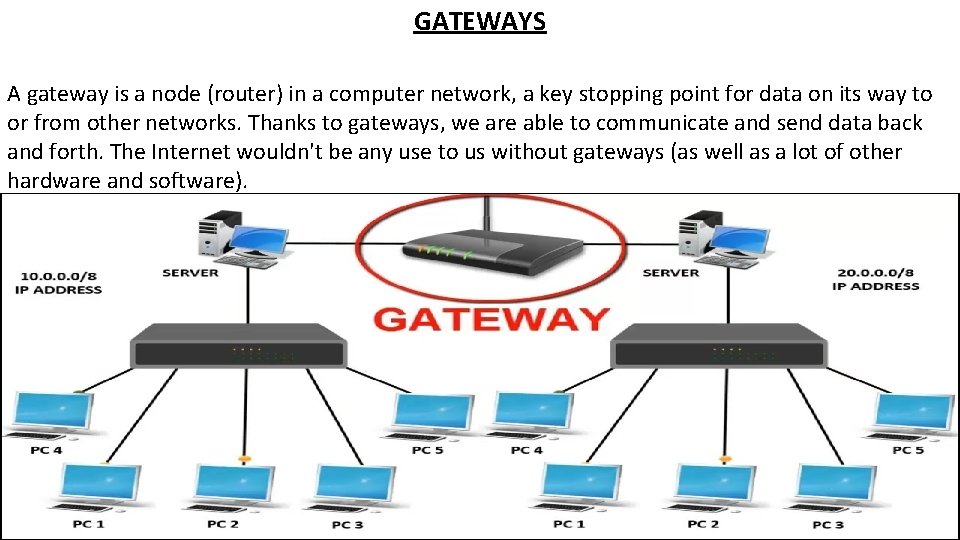
GATEWAYS A gateway is a node (router) in a computer network, a key stopping point for data on its way to or from other networks. Thanks to gateways, we are able to communicate and send data back and forth. The Internet wouldn't be any use to us without gateways (as well as a lot of other hardware and software).
Intranet: - An intranet is a private network that can only be accessed by authorized users. The prefix "intra" means "internal" and therefore implies an intranet is designed for internal communications. "Inter" (as in Internet) means "between" or "among. " Since there is only one Internet, the word "Internet" is capitalized. Extranet: - An extranet is a private network that uses Internet technology and the public telecommunication system to securely share part of a business's information or operations with suppliers, vendors, partners, customers, or other businesses. An extranet can be viewed as part of a company's intranet that is extended to users outside the company. It has also been described as a "state of mind" in which the Internet is perceived as a way to do business with other companies as well as to sell products to customers.
Cyber Security Cyber security refers to the body of technologies, processes, and practices designed to protect networks, devices, programs, and data from attack, damage, or unauthorized access. Cyber security may also be referred to as information technology security. Types of Cyber Security are nothing but the techniques used to prevent the stolen or assaulted data. Types of Cyber Attacks: � Denial of Service Attack (Dos) � Hacking � Malware � Phishing � Spoofing � Ransomware � Spamming
- Slides: 14