Chapter 4 Data Link Layer Framing Error control
![Probability of Error P[error detection failure] = P[undetectable error pattern] = P[all error patterns Probability of Error P[error detection failure] = P[undetectable error pattern] = P[all error patterns](https://slidetodoc.com/presentation_image_h/7e80ce42710f56e6c58a1ad874246125/image-14.jpg)
- Slides: 75
Chapter 4 Data Link Layer Framing Error control Flow control Multiplexing Link Maintenance Security 1
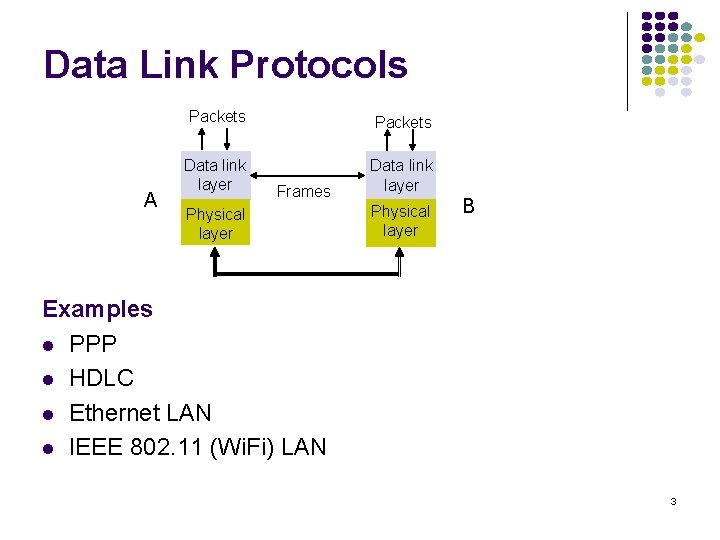
Services l Transfers frames across direct connections l l l Directly connected (can be wireless), wire-like Losses & errors, but no out-of-sequence frames More detailed services l l l Framing (bits ↔ frames) Error control (protection from impairment) Flow control Multiplexing Link Maintenance Security: Authentication & Encryption 2
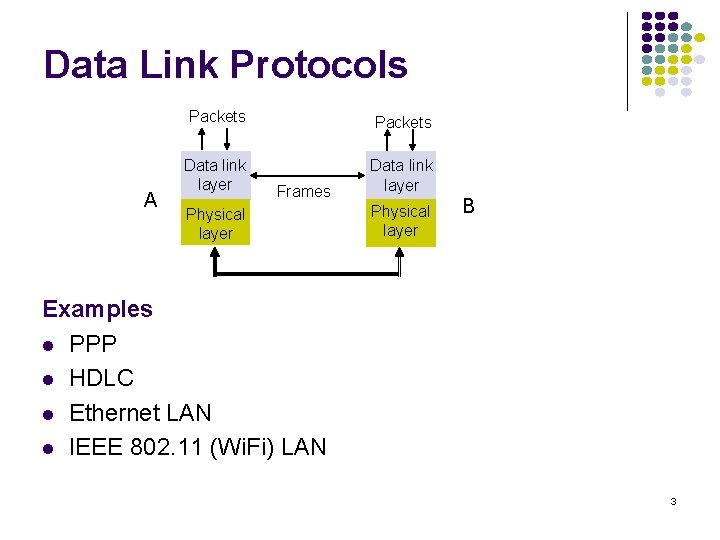
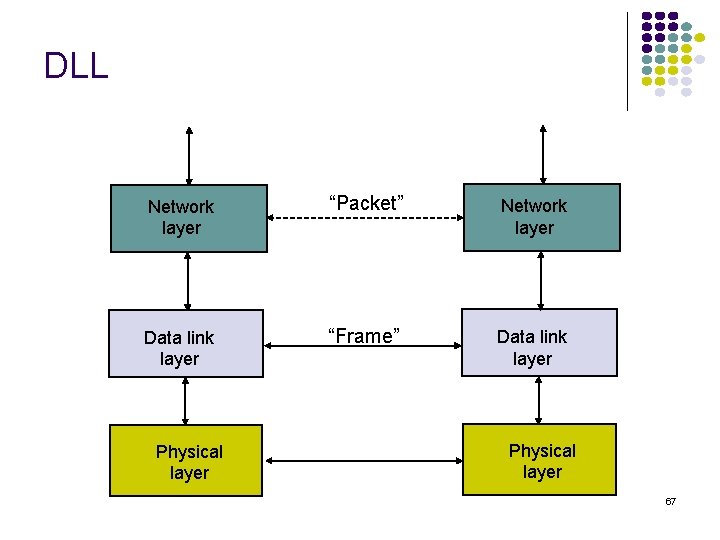
Data Link Protocols A Packets Data link layer Frames Physical layer B Examples l PPP l HDLC l Ethernet LAN l IEEE 802. 11 (Wi. Fi) LAN 3
Framing (Chapter 5. 4 in Leon-Garcia) 4
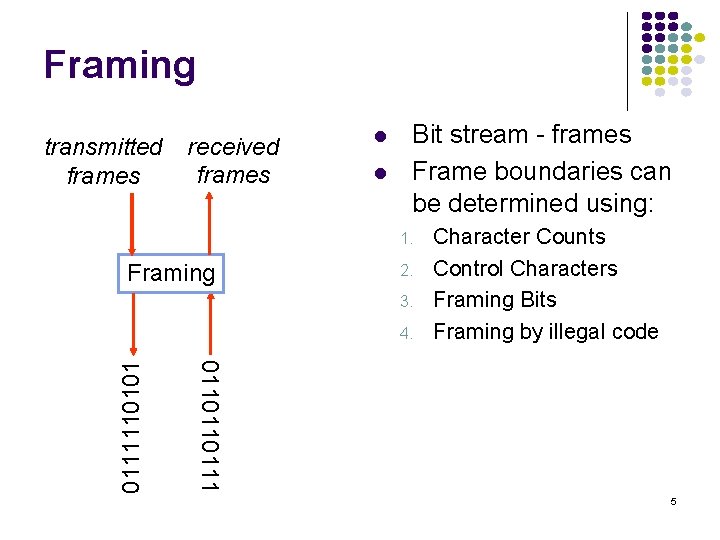
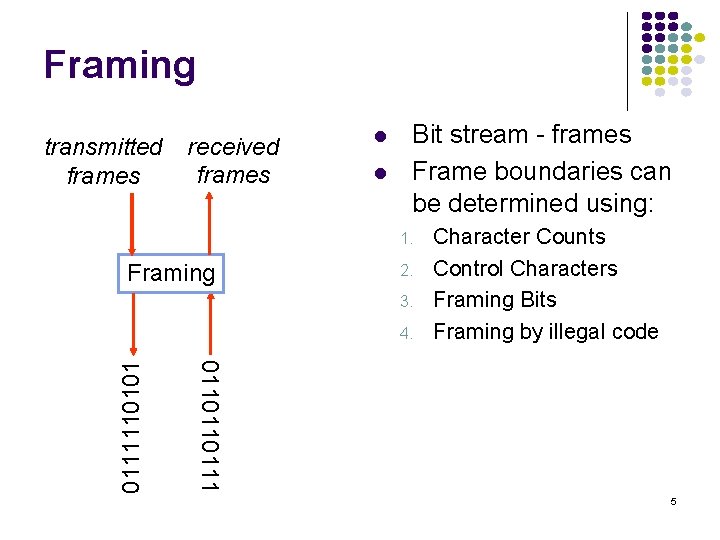
Framing transmitted frames received frames l l Bit stream - frames Frame boundaries can be determined using: 1. Framing 2. 3. 0110110111110101 4. Character Counts Control Characters Framing Bits Framing by illegal code 5
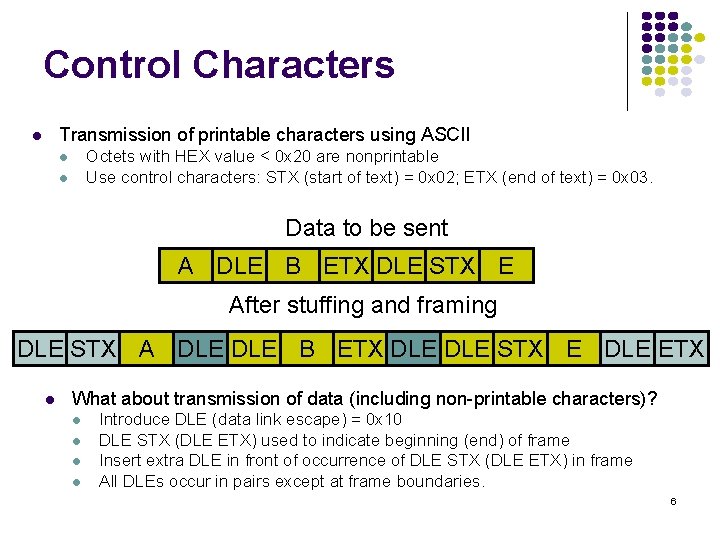
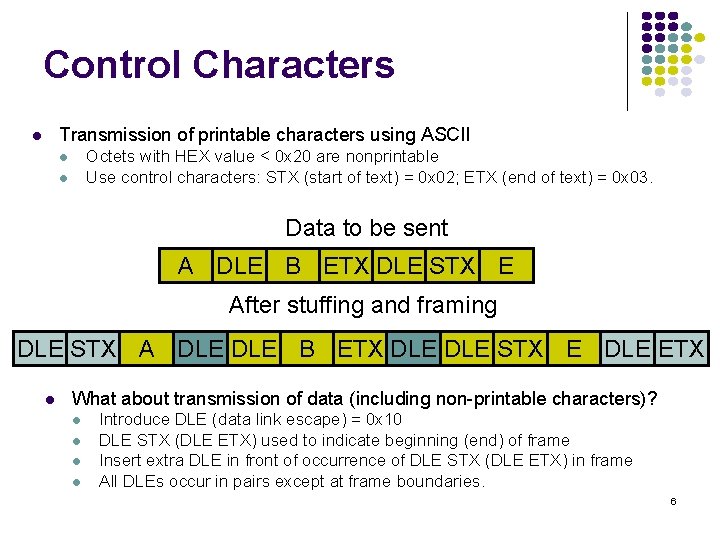
Control Characters Transmission of printable characters using ASCII l Octets with HEX value < 0 x 20 are nonprintable Use control characters: STX (start of text) = 0 x 02; ETX (end of text) = 0 x 03. l l Data to be sent A DLE B ETX DLE STX E After stuffing and framing DLE STX A DLE B ETX DLE STX E DLE ETX l What about transmission of data (including non-printable characters)? l l Introduce DLE (data link escape) = 0 x 10 DLE STX (DLE ETX) used to indicate beginning (end) of frame Insert extra DLE in front of occurrence of DLE STX (DLE ETX) in frame All DLEs occur in pairs except at frame boundaries. 6
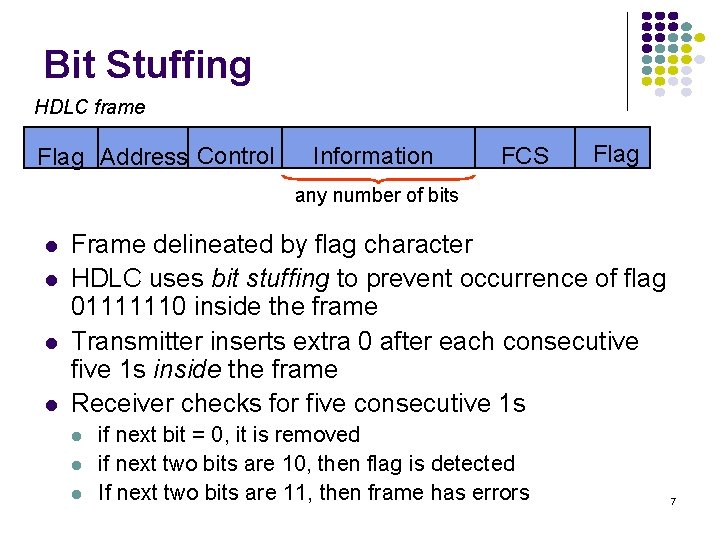
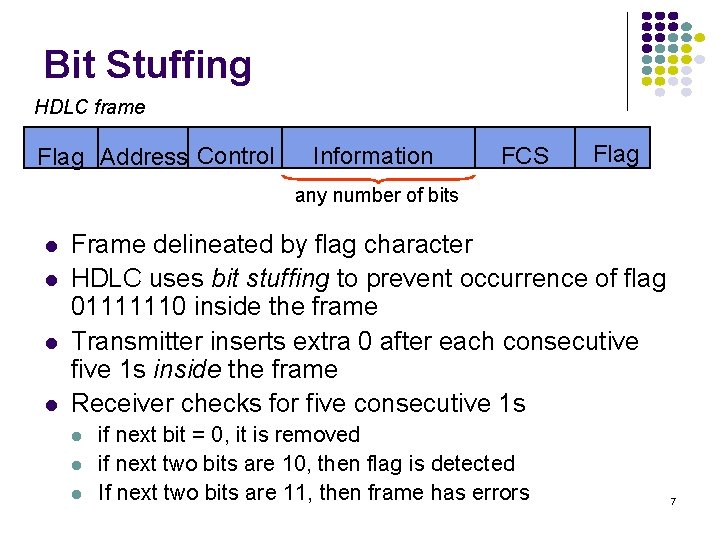
Bit Stuffing HDLC frame Flag Address Control Information FCS Flag any number of bits l l Frame delineated by flag character HDLC uses bit stuffing to prevent occurrence of flag 01111110 inside the frame Transmitter inserts extra 0 after each consecutive five 1 s inside the frame Receiver checks for five consecutive 1 s l l l if next bit = 0, it is removed if next two bits are 10, then flag is detected If next two bits are 11, then frame has errors 7
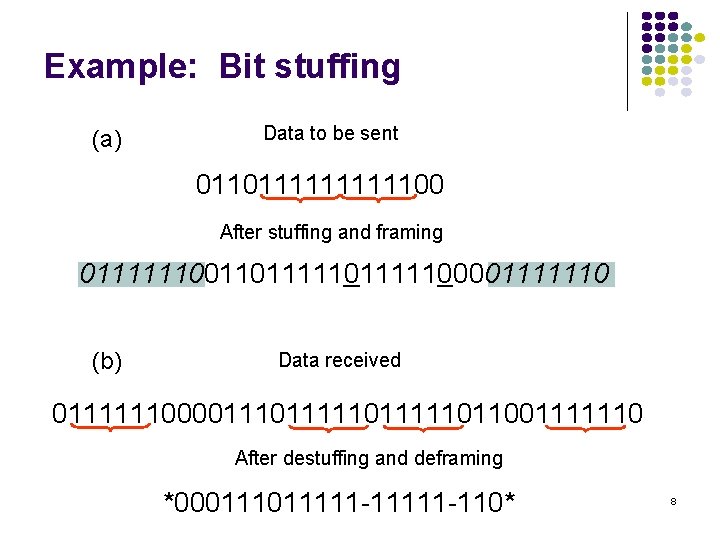
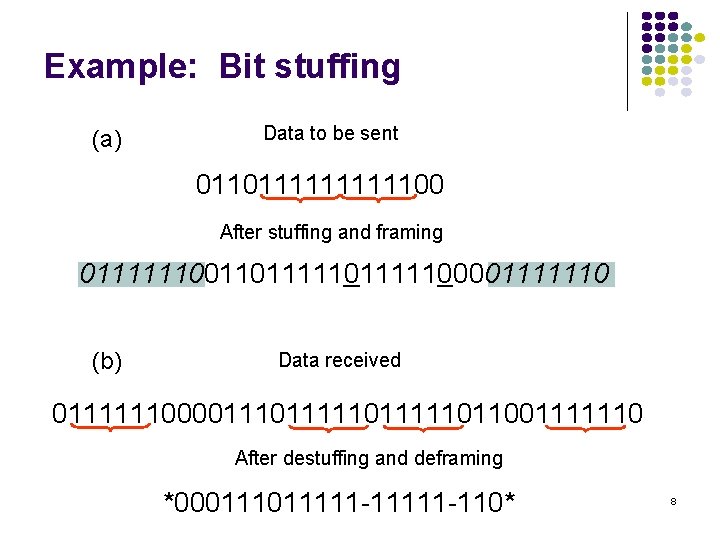
Example: Bit stuffing (a) Data to be sent 01101111100 After stuffing and framing 0111111001101111100001111110 (b) Data received 0111111000011111011111011001111110 After destuffing and deframing *00011111 -11111 -110* 8
Example: Framing in Ethernet l l Ethernet complies to standard IEEE 802. 3 An illegal manchester coding is used for framing. A character count is also included in the header. All frames have an integral number of bytes. If not, the frame is considered to be received in error. 9
Error Control Coding (Chapter 3. 9 in Leon-Garcia) 10
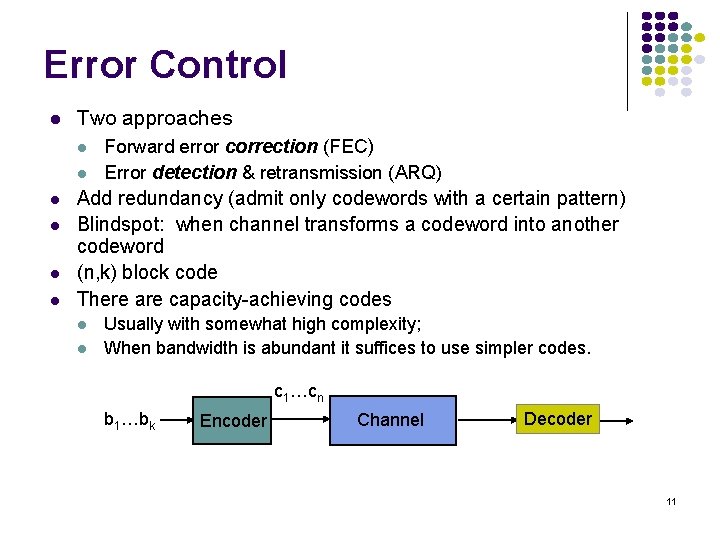
Error Control l Two approaches l l l Forward error correction (FEC) Error detection & retransmission (ARQ) Add redundancy (admit only codewords with a certain pattern) Blindspot: when channel transforms a codeword into another codeword (n, k) block code There are capacity-achieving codes l l Usually with somewhat high complexity; When bandwidth is abundant it suffices to use simpler codes. c 1…cn b 1…bk Encoder Channel Decoder 11
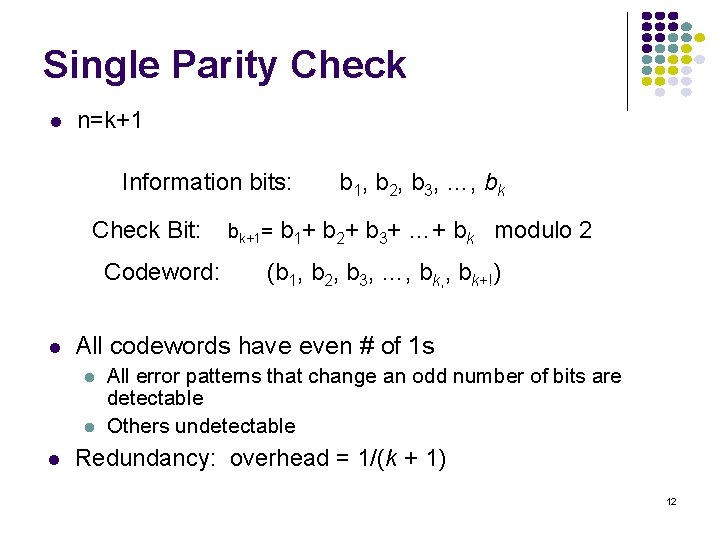
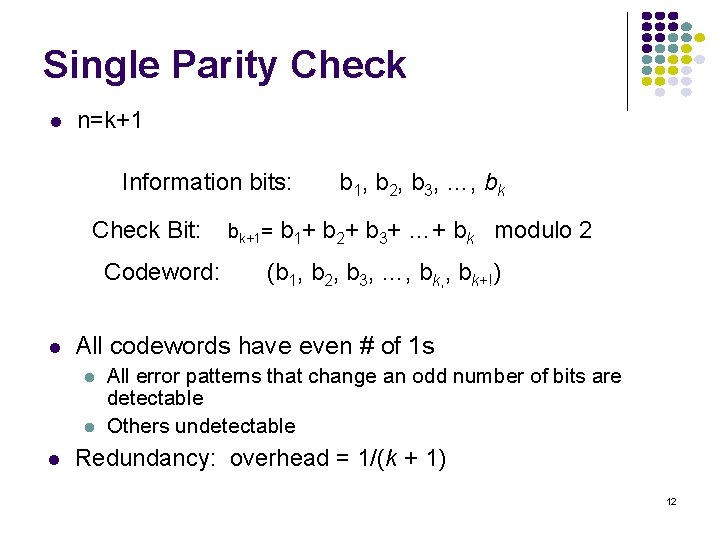
Single Parity Check l n=k+1 Information bits: Check Bit: Codeword: l b 1+ b 2+ b 3+ …+ bk modulo 2 (b 1, b 2, b 3, …, bk, , bk+!) All codewords have even # of 1 s l l l bk+1= b 1, b 2, b 3, …, bk All error patterns that change an odd number of bits are detectable Others undetectable Redundancy: overhead = 1/(k + 1) 12
Example l Information (7 bits): (0, 1, 1, 0, 0) 13
![Probability of Error Perror detection failure Pundetectable error pattern Pall error patterns Probability of Error P[error detection failure] = P[undetectable error pattern] = P[all error patterns](https://slidetodoc.com/presentation_image_h/7e80ce42710f56e6c58a1ad874246125/image-14.jpg)
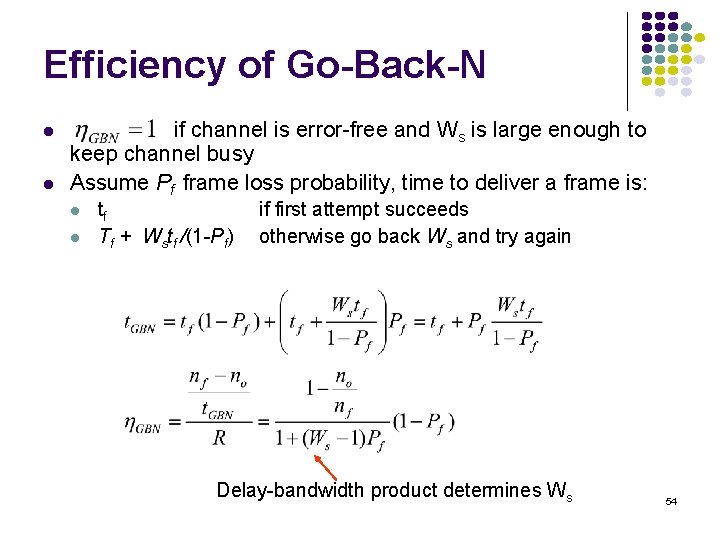
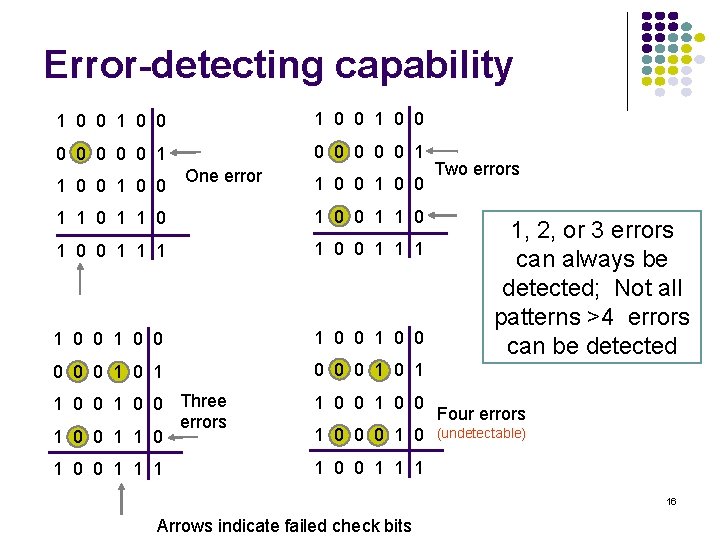
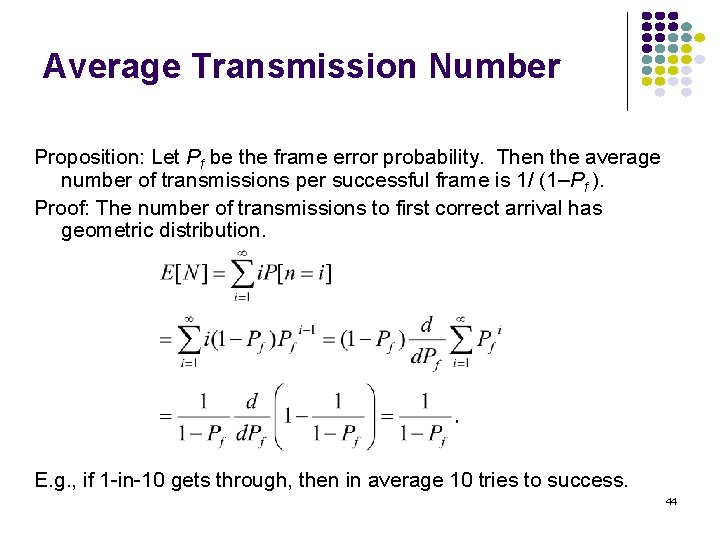
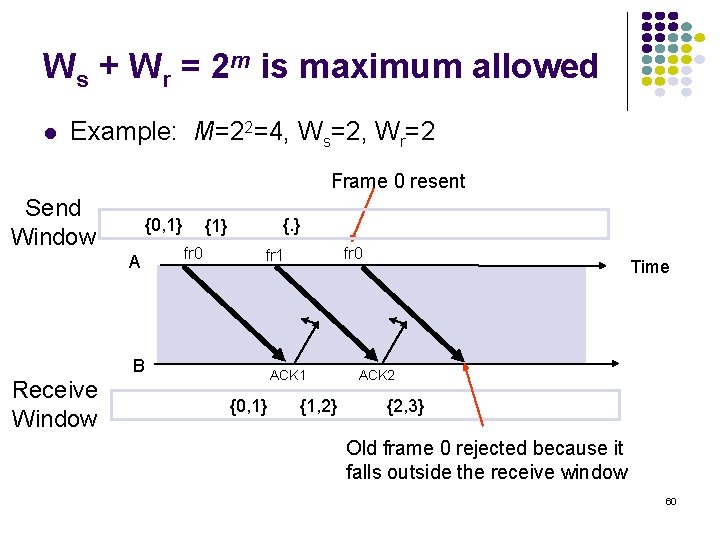
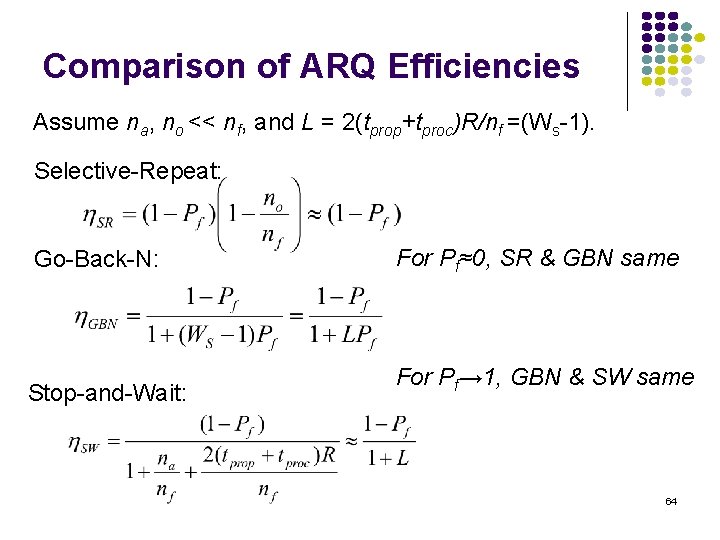
Probability of Error P[error detection failure] = P[undetectable error pattern] = P[all error patterns with even number of 1 s] = l n n 2 p (1 – p)n-2 + 4 2 p 4(1 – p)n-4 + … Example: Evaluate above for n = 6, p = 0. 01 P[undetectable error] = 0. 0014 14
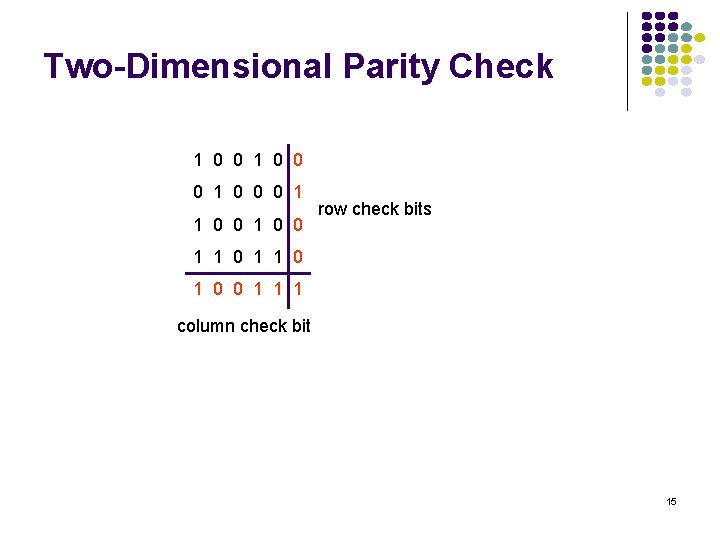
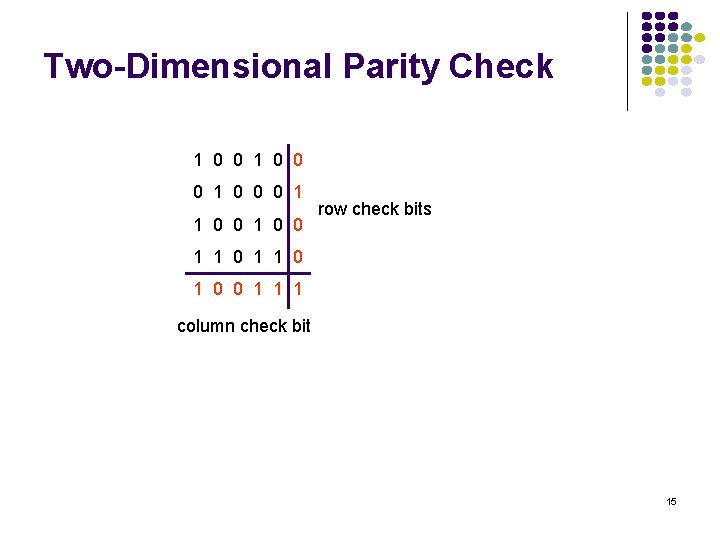
Two-Dimensional Parity Check 1 0 0 0 1 1 0 0 row check bits 1 1 0 1 0 0 1 1 1 column check bit 15
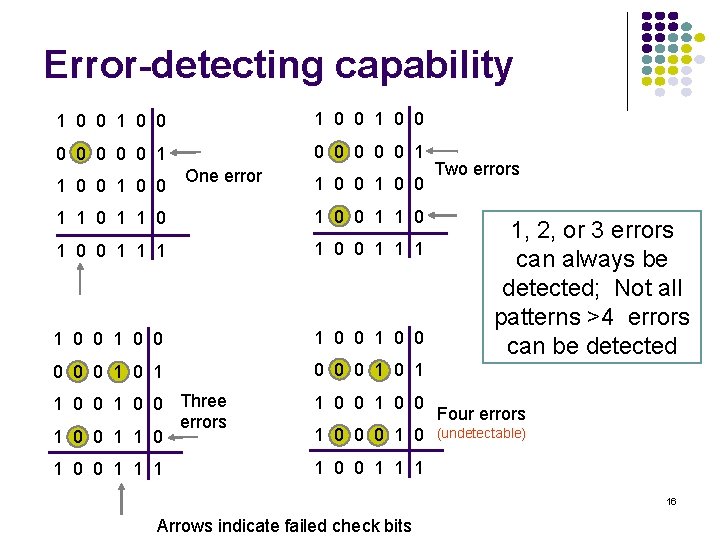
Error-detecting capability 1 0 0 0 0 0 0 0 1 1 0 0 One error 1 0 0 1 1 0 0 1 1 1 1 0 0 1 0 0 0 1 1 0 0 Three errors 1 0 0 1 0 0 1 1 1 1 0 0 0 1 0 Two errors 1, 2, or 3 errors can always be detected; Not all patterns >4 errors can be detected Four errors (undetectable) 16 Arrows indicate failed check bits
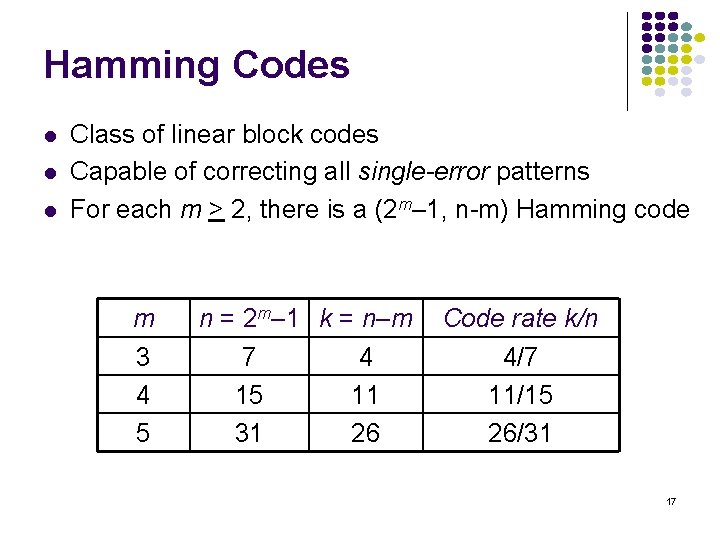
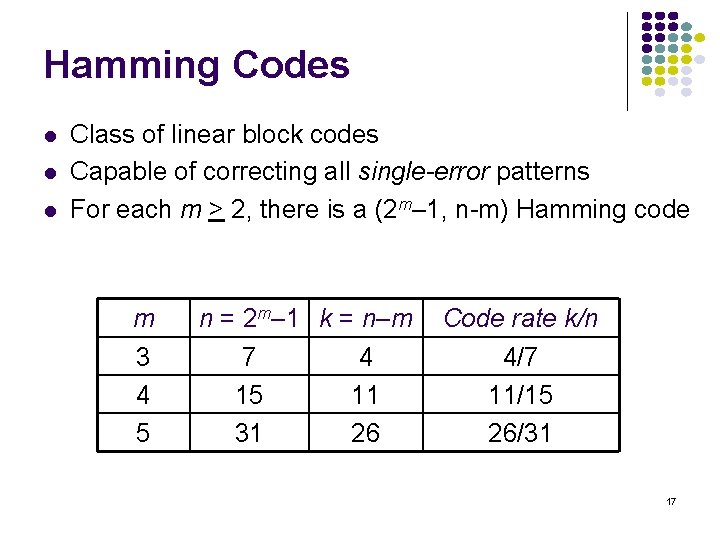
Hamming Codes l l l Class of linear block codes Capable of correcting all single-error patterns For each m > 2, there is a (2 m– 1, n-m) Hamming code m 3 4 5 n = 2 m– 1 k = n–m 7 4 15 11 31 26 Code rate k/n 4/7 11/15 26/31 17
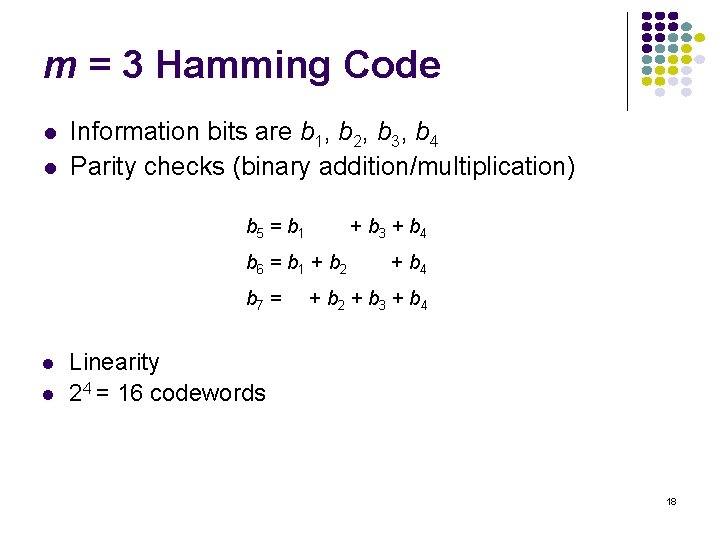
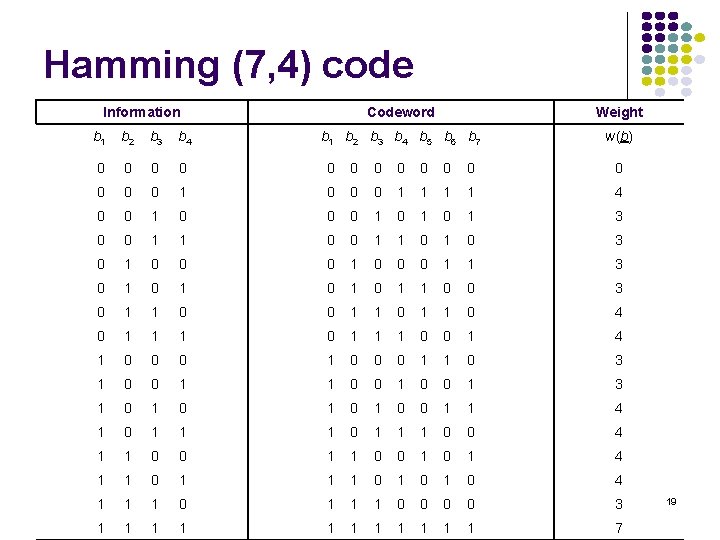
m = 3 Hamming Code l l Information bits are b 1, b 2, b 3, b 4 Parity checks (binary addition/multiplication) b 5 = b 1 + b 3 + b 4 b 6 = b 1 + b 2 b 7 = l l + b 4 + b 2 + b 3 + b 4 Linearity 24 = 16 codewords 18
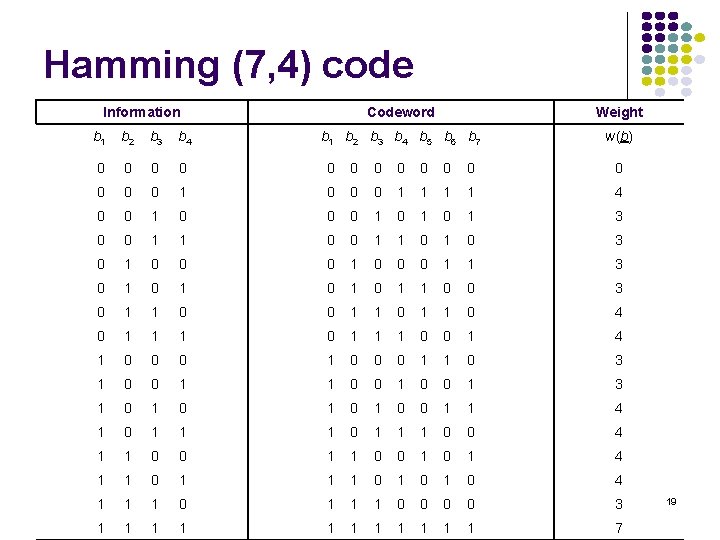
Hamming (7, 4) code Information Codeword Weight b 1 b 2 b 3 b 4 b 5 b 6 b 7 w(b) b 1 b 2 b 3 b 4 0 0 0 0 1 0 0 0 1 1 4 0 0 1 0 1 0 1 3 0 0 1 1 0 1 0 3 0 1 0 0 0 1 1 3 0 1 0 1 1 0 0 3 0 1 1 0 4 0 1 1 1 0 0 1 4 1 0 0 0 1 1 0 3 1 0 0 1 3 1 0 1 0 0 1 1 4 1 0 1 1 1 0 0 4 1 1 0 0 1 0 1 4 1 1 0 1 0 1 0 4 1 1 1 0 0 0 0 3 1 1 1 7 19
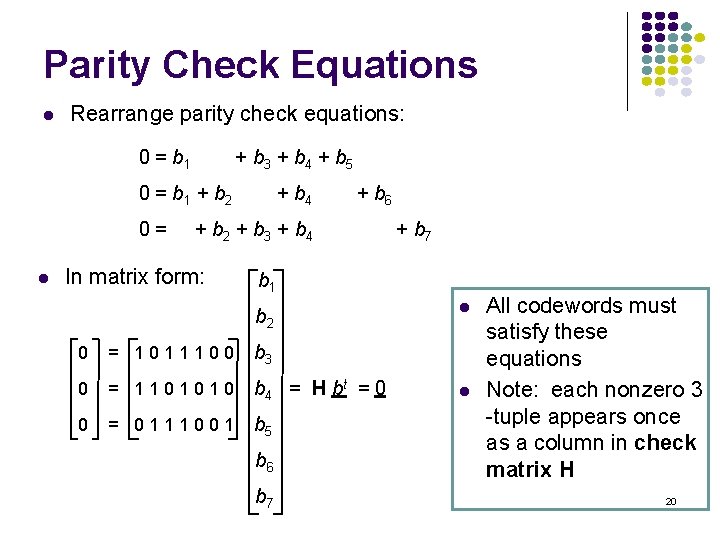
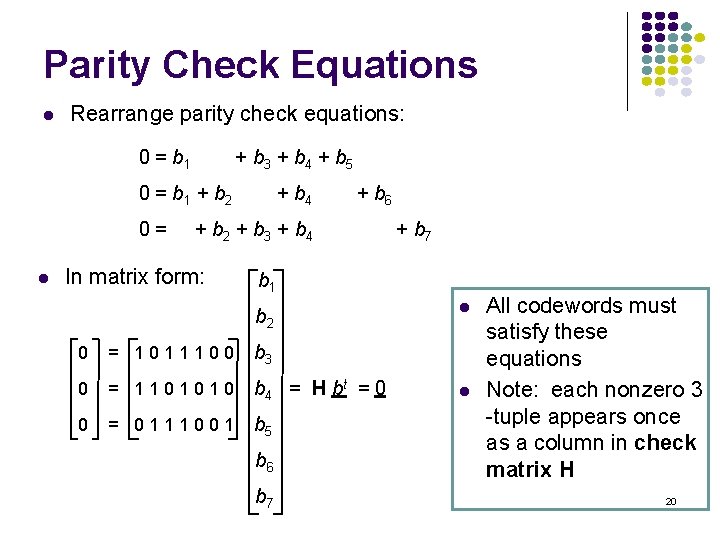
Parity Check Equations l Rearrange parity check equations: 0 = b 1 + b 3 + b 4 + b 5 0 = b 1 + b 2 0= l + b 4 + b 6 + b 2 + b 3 + b 4 In matrix form: + b 7 b 1 b 2 0 = 1011100 b 3 0 = 1101010 b 4 = H bt = 0 0 = 0111001 b 5 b 6 b 7 l l All codewords must satisfy these equations Note: each nonzero 3 -tuple appears once as a column in check matrix H 20
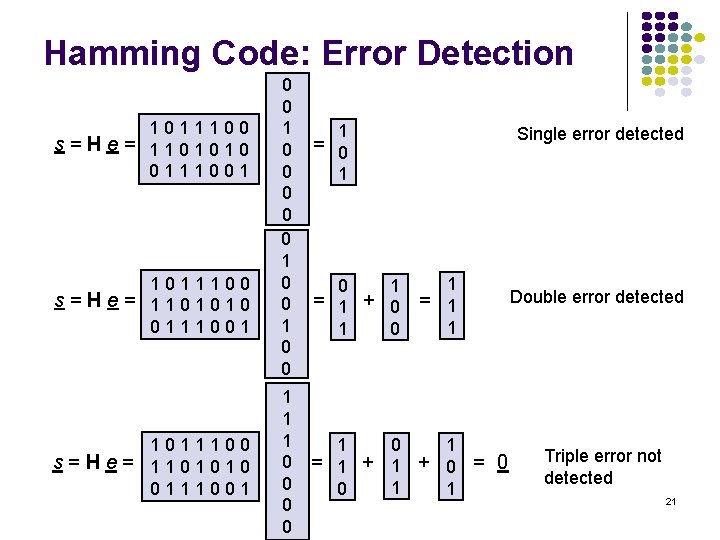
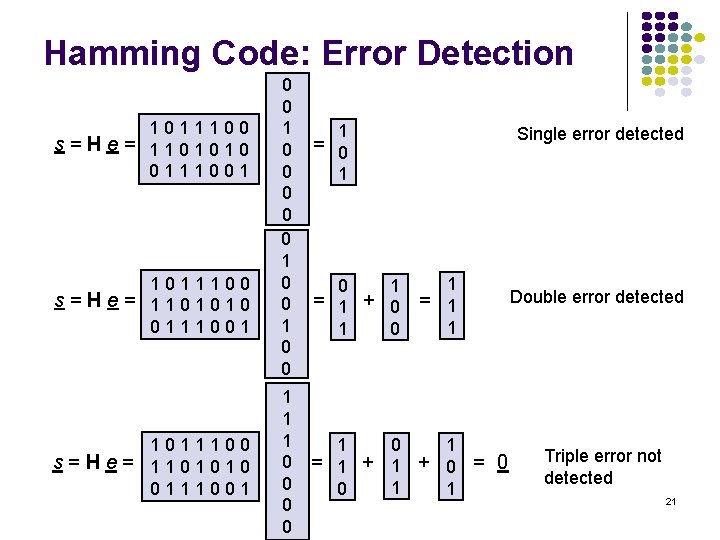
Hamming Code: Error Detection 1011100 s=He= 1101010 0111001 0 0 0 0 0 1 1 1 0 0 1 Single error detected = 0 1 0 1 = 1 + 0 1 = 1 1 0 1 1 + 0 = 0 1 1 Double error detected Triple error not detected 21
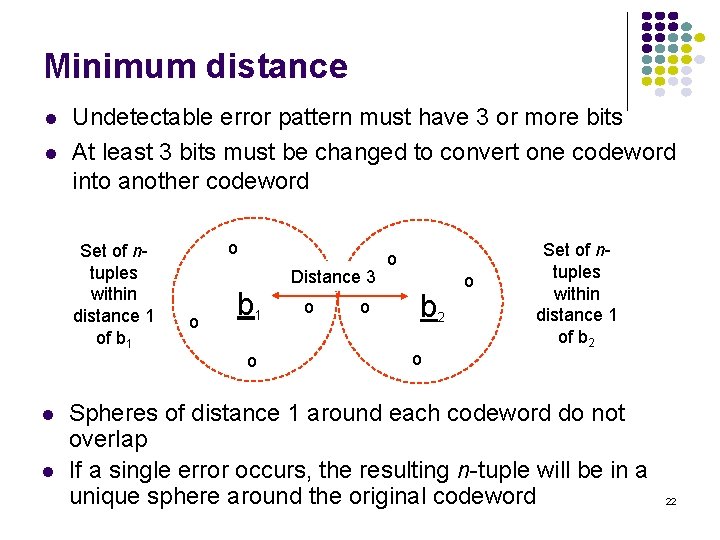
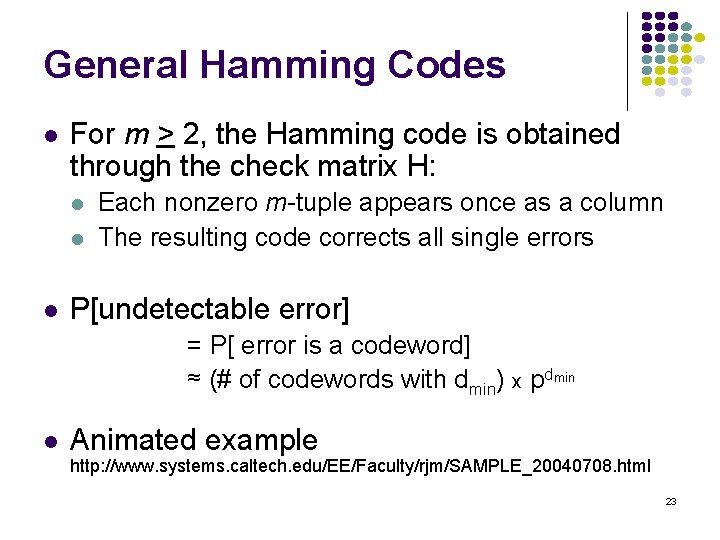
Minimum distance l l Undetectable error pattern must have 3 or more bits At least 3 bits must be changed to convert one codeword into another codeword Set of ntuples within distance 1 of b 1 l l o o b 1 o Distance 3 o o o b 2 o o Set of ntuples within distance 1 of b 2 Spheres of distance 1 around each codeword do not overlap If a single error occurs, the resulting n-tuple will be in a unique sphere around the original codeword 22
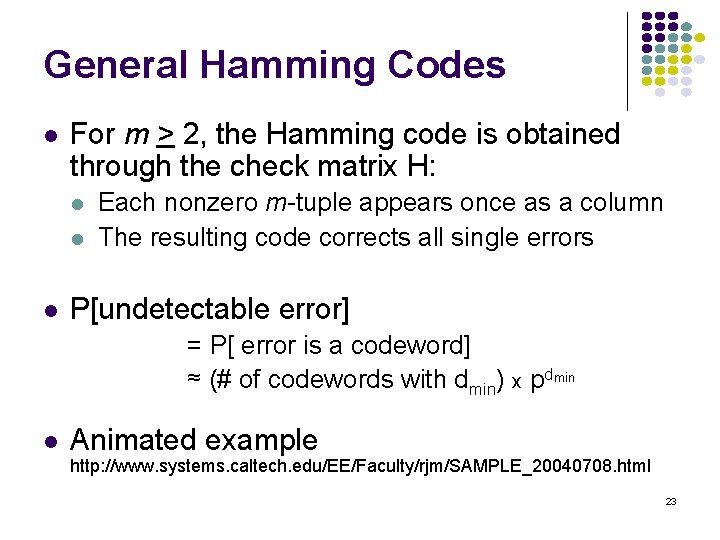
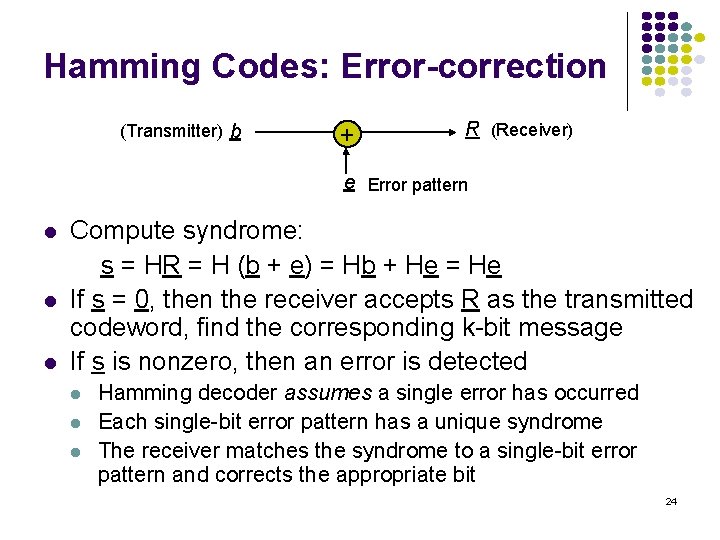
General Hamming Codes l For m > 2, the Hamming code is obtained through the check matrix H: l l l Each nonzero m-tuple appears once as a column The resulting code corrects all single errors P[undetectable error] = P[ error is a codeword] ≈ (# of codewords with dmin) x pdmin l Animated example http: //www. systems. caltech. edu/EE/Faculty/rjm/SAMPLE_20040708. html 23
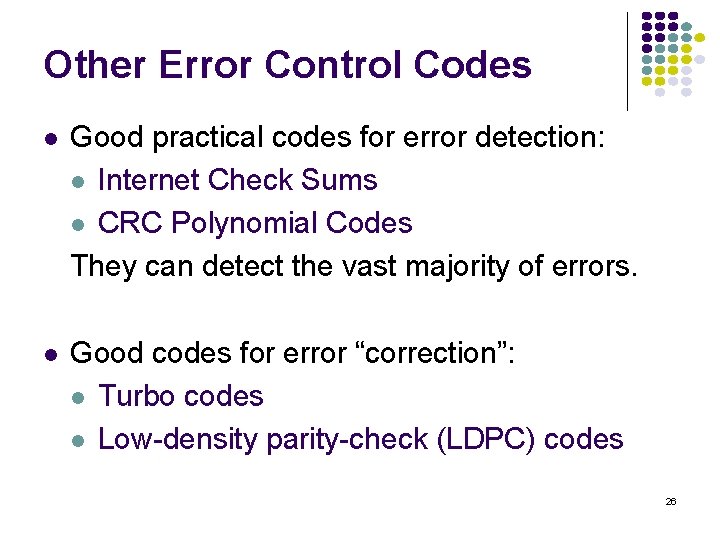
Hamming Codes: Error-correction (Transmitter) b + R (Receiver) e Error pattern l l l Compute syndrome: s = HR = H (b + e) = Hb + He = He If s = 0, then the receiver accepts R as the transmitted codeword, find the corresponding k-bit message If s is nonzero, then an error is detected l l l Hamming decoder assumes a single error has occurred Each single-bit error pattern has a unique syndrome The receiver matches the syndrome to a single-bit error pattern and corrects the appropriate bit 24
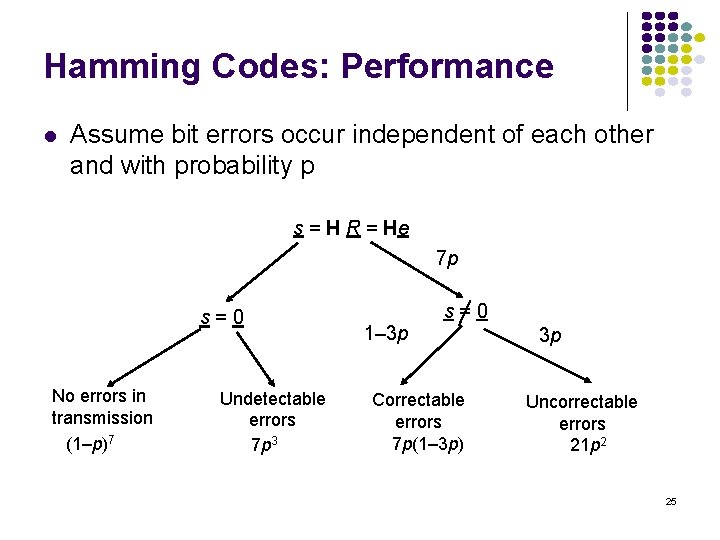
Hamming Codes: Performance l Assume bit errors occur independent of each other and with probability p s = H R = He 7 p s=0 No errors in transmission (1–p)7 Undetectable errors 7 p 3 s=0 1– 3 p Correctable errors 7 p(1– 3 p) 3 p Uncorrectable errors 21 p 2 25
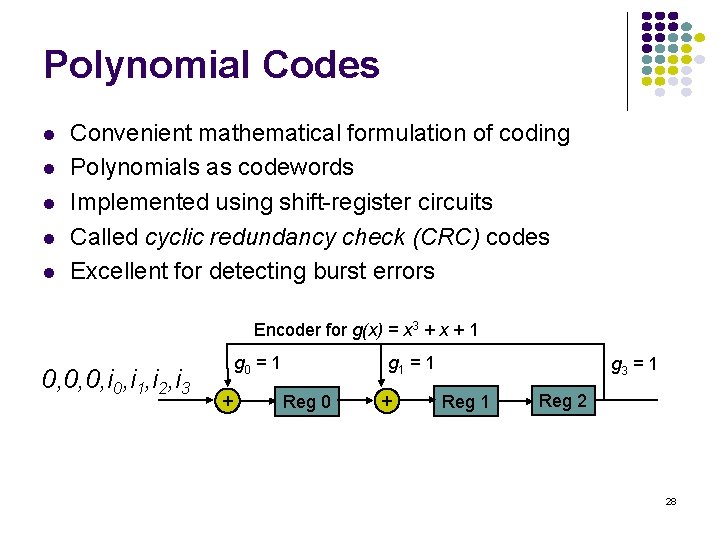
Other Error Control Codes l Good practical codes for error detection: l Internet Check Sums l CRC Polynomial Codes They can detect the vast majority of errors. l Good codes for error “correction”: l Turbo codes l Low-density parity-check (LDPC) codes 26
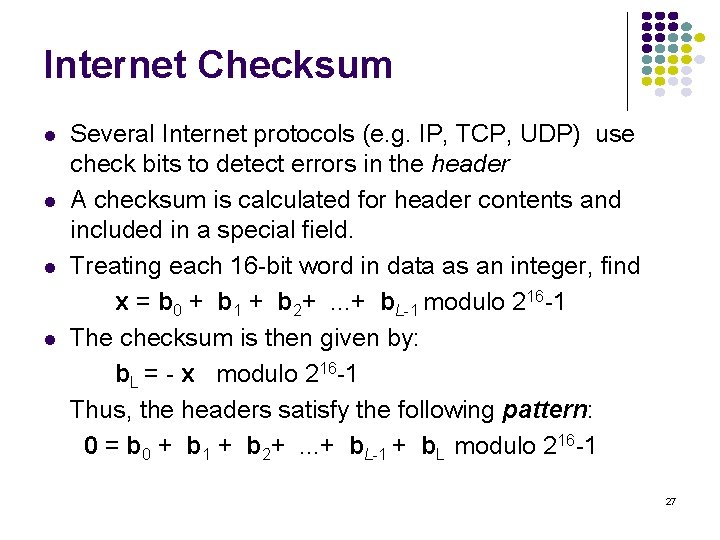
Internet Checksum l l Several Internet protocols (e. g. IP, TCP, UDP) use check bits to detect errors in the header A checksum is calculated for header contents and included in a special field. Treating each 16 -bit word in data as an integer, find x = b 0 + b 1 + b 2+. . . + b. L-1 modulo 216 -1 The checksum is then given by: b. L = - x modulo 216 -1 Thus, the headers satisfy the following pattern: 0 = b 0 + b 1 + b 2+. . . + b. L-1 + b. L modulo 216 -1 27
Polynomial Codes l l l Convenient mathematical formulation of coding Polynomials as codewords Implemented using shift-register circuits Called cyclic redundancy check (CRC) codes Excellent for detecting burst errors Encoder for g(x) = x 3 + x + 1 0, 0, 0, i 1, i 2, i 3 g 0 = 1 + g 1 = 1 Reg 0 + g 3 = 1 Reg 2 28
Automatic Repeat Request (ARQ) (Chapter 5 in Leon-Garcia) 29
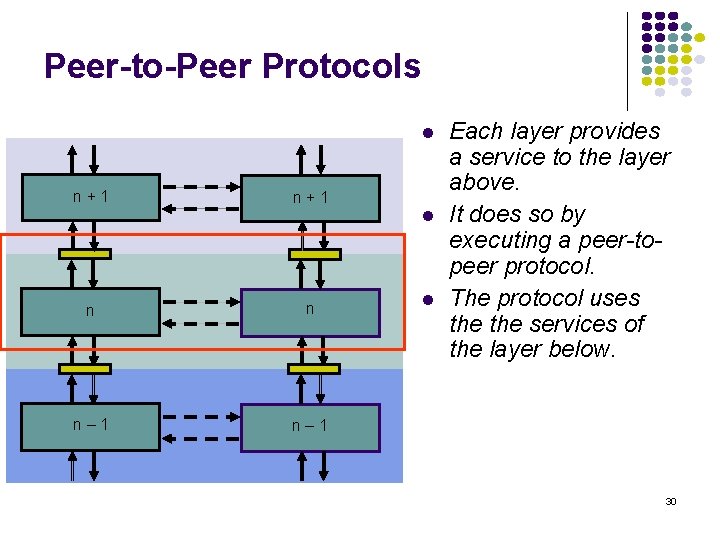
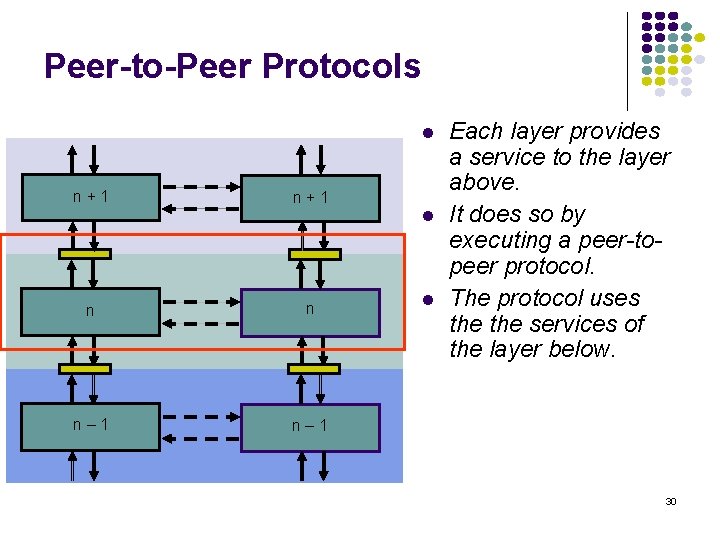
Peer-to-Peer Protocols l n+1 n n n– 1 l l Each layer provides a service to the layer above. It does so by executing a peer-topeer protocol. The protocol uses the services of the layer below. 30
Service Models l The service model specifies the manner in which information is transferred. l l Connection-oriented Connectionless 31
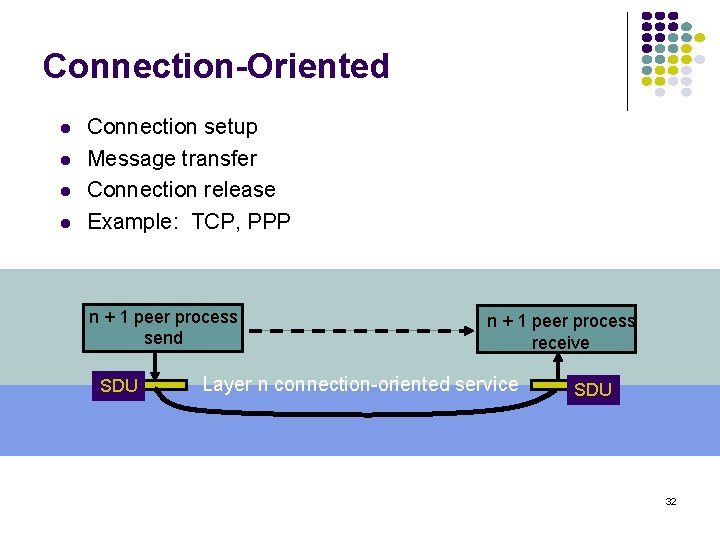
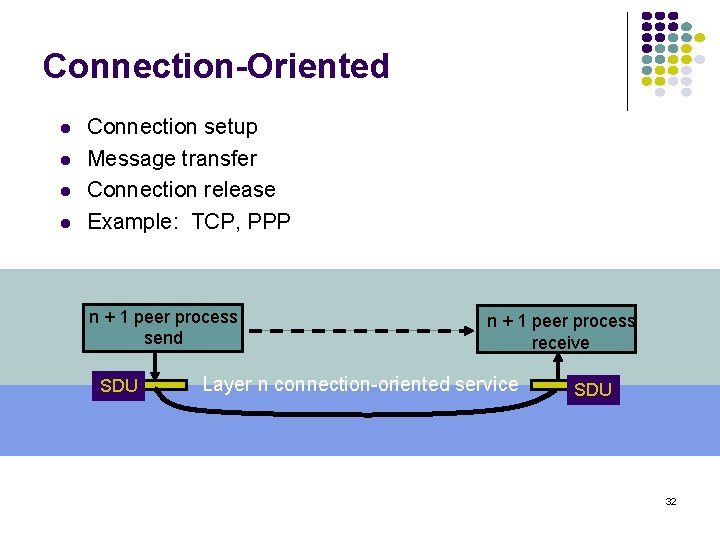
Connection-Oriented l l Connection setup Message transfer Connection release Example: TCP, PPP n + 1 peer process send SDU n + 1 peer process receive Layer n connection-oriented service SDU 32
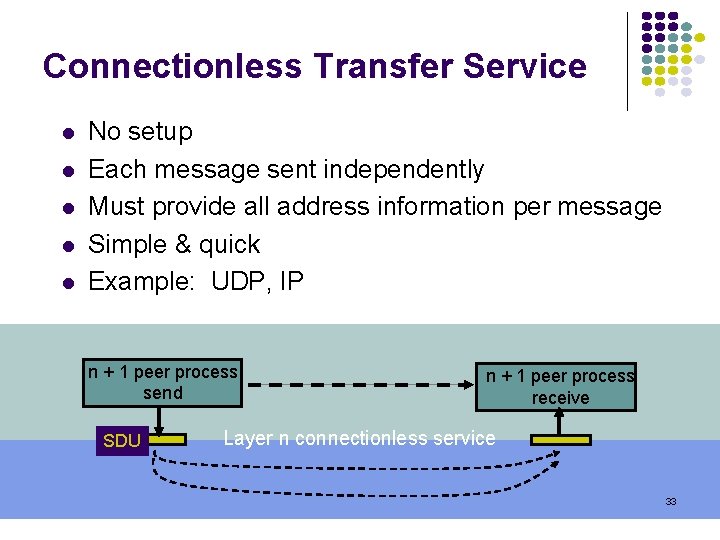
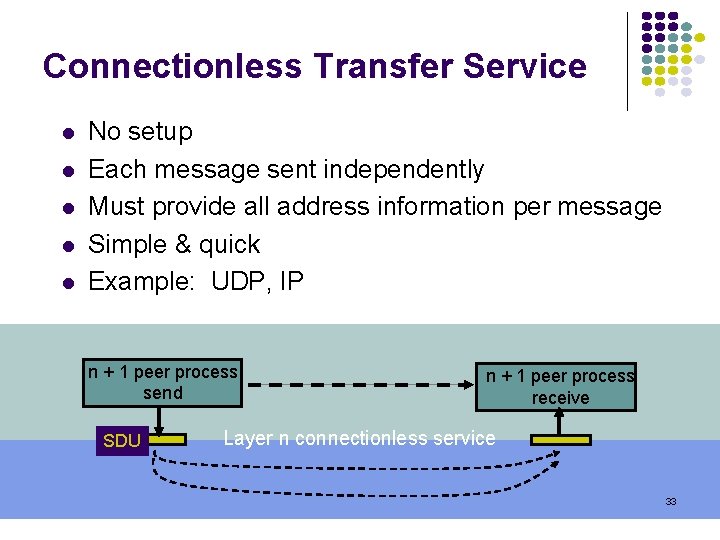
Connectionless Transfer Service l l l No setup Each message sent independently Must provide all address information per message Simple & quick Example: UDP, IP n + 1 peer process send SDU n + 1 peer process receive Layer n connectionless service 33
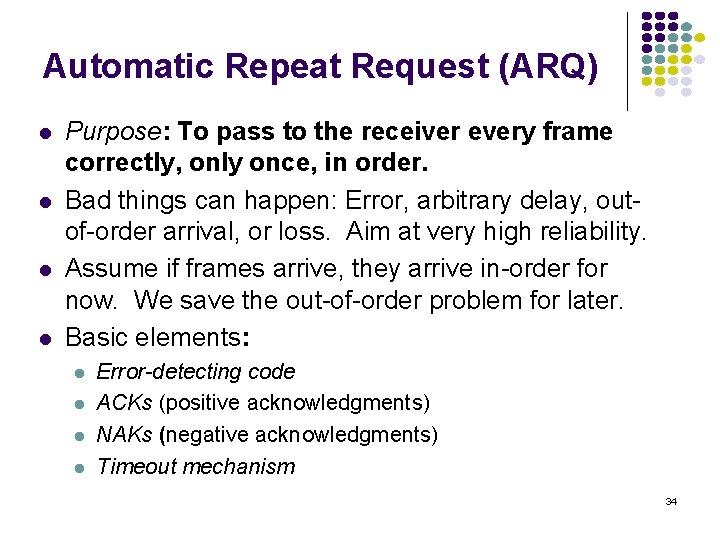
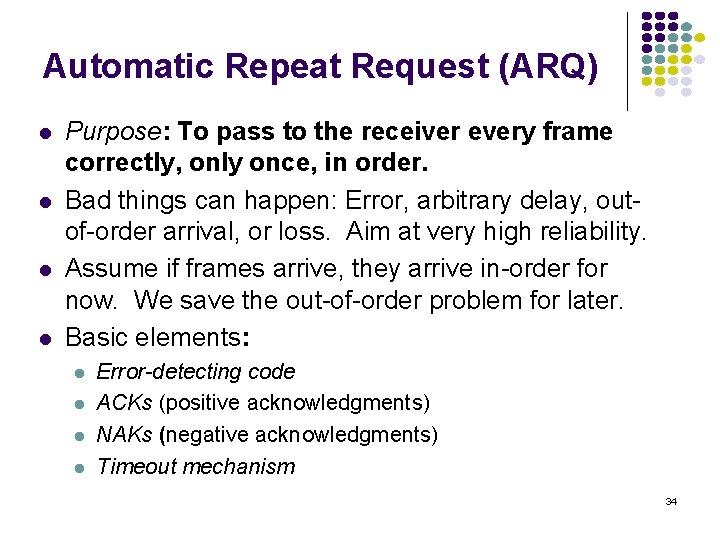
Automatic Repeat Request (ARQ) l l Purpose: To pass to the receiver every frame correctly, only once, in order. Bad things can happen: Error, arbitrary delay, outof-order arrival, or loss. Aim at very high reliability. Assume if frames arrive, they arrive in-order for now. We save the out-of-order problem for later. Basic elements: l l Error-detecting code ACKs (positive acknowledgments) NAKs (negative acknowledgments) Timeout mechanism 34
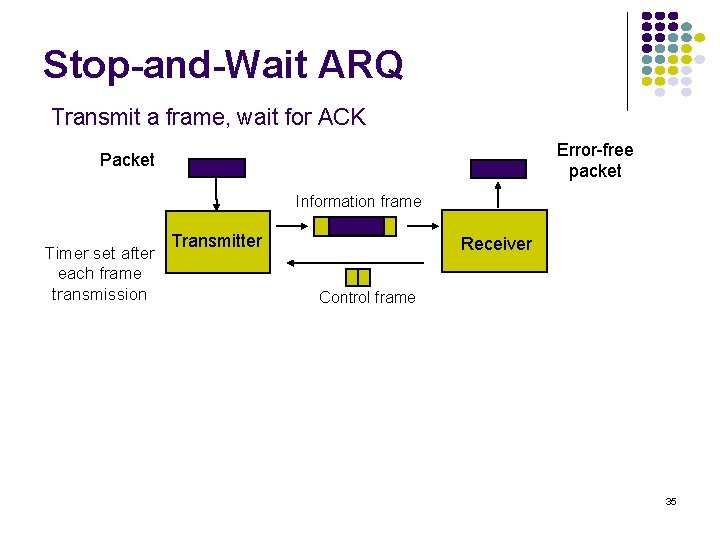
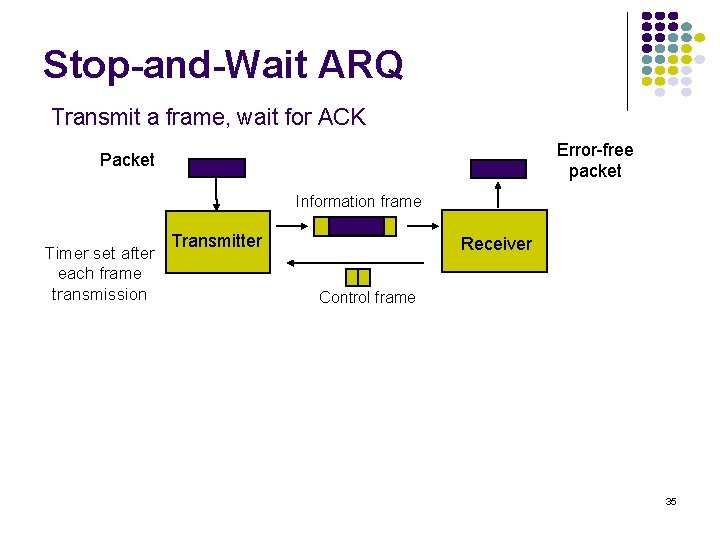
Stop-and-Wait ARQ Transmit a frame, wait for ACK Error-free packet Packet Information frame Timer set after each frame transmission Transmitter Receiver Control frame 35
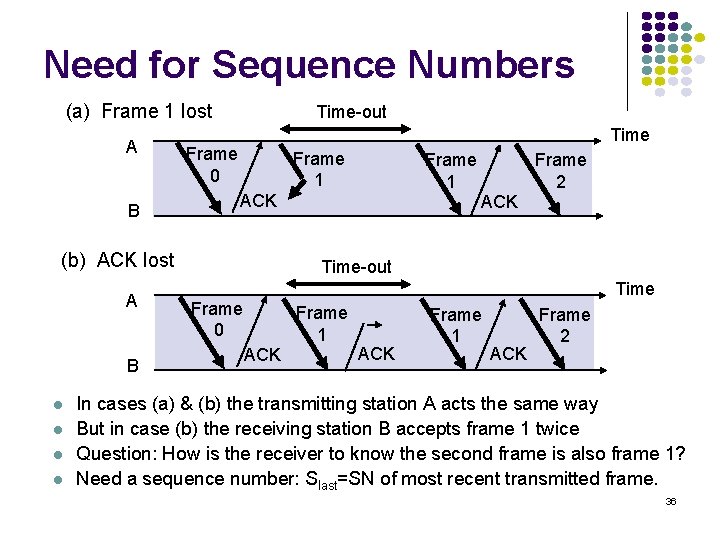
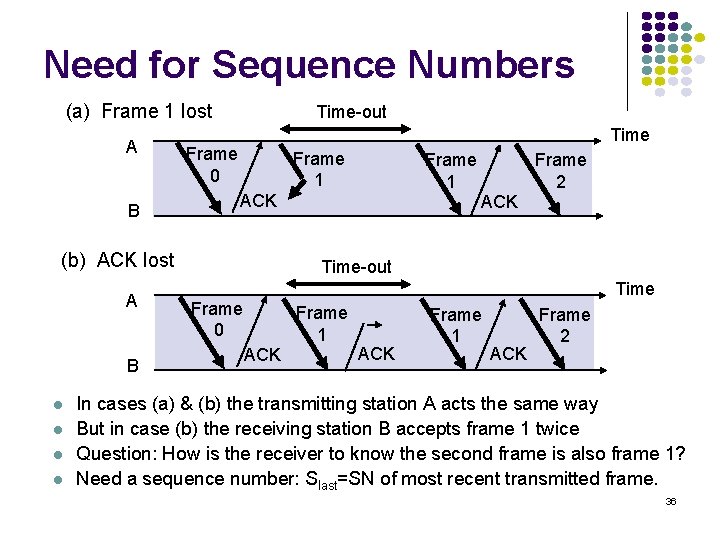
Need for Sequence Numbers (a) Frame 1 lost A B Time-out Time Frame 0 Frame 1 ACK (b) ACK lost A B l l Frame 1 Frame 2 ACK Time-out Time Frame 0 Frame 1 ACK Frame 2 In cases (a) & (b) the transmitting station A acts the same way But in case (b) the receiving station B accepts frame 1 twice Question: How is the receiver to know the second frame is also frame 1? Need a sequence number: Slast=SN of most recent transmitted frame. 36
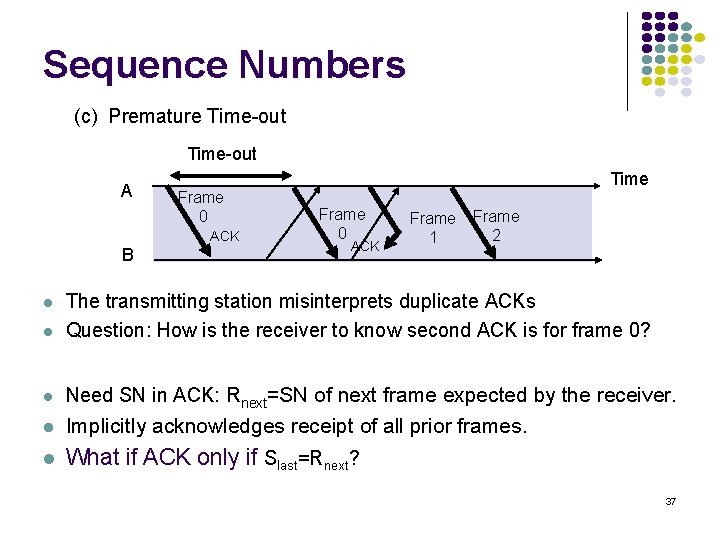
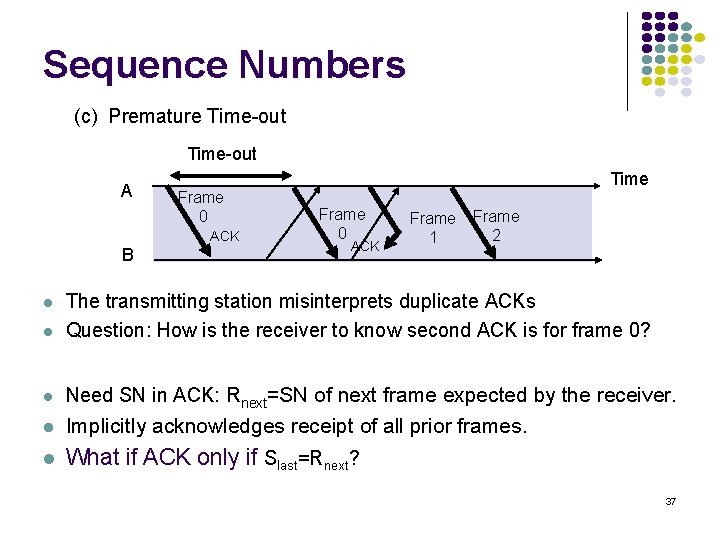
Sequence Numbers (c) Premature Time-out A Frame 0 ACK B Time Frame 0 ACK Frame 1 Frame 2 l The transmitting station misinterprets duplicate ACKs Question: How is the receiver to know second ACK is for frame 0? l Need SN in ACK: Rnext=SN of next frame expected by the receiver. l Implicitly acknowledges receipt of all prior frames. l What if ACK only if Slast=Rnext? l 37
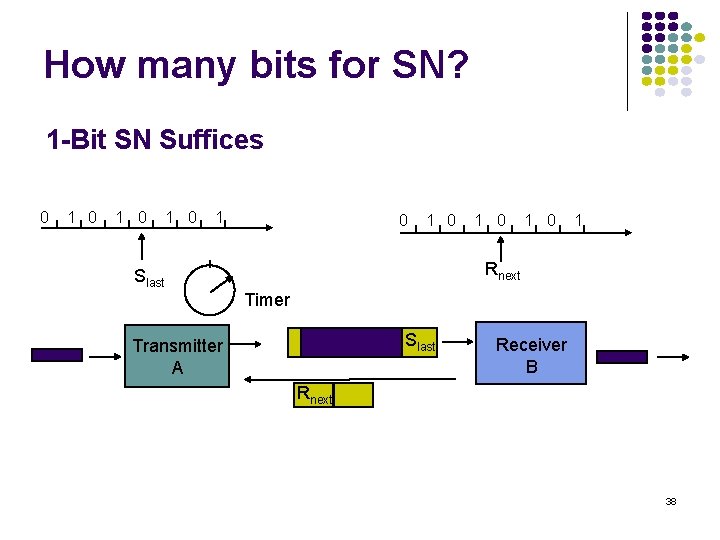
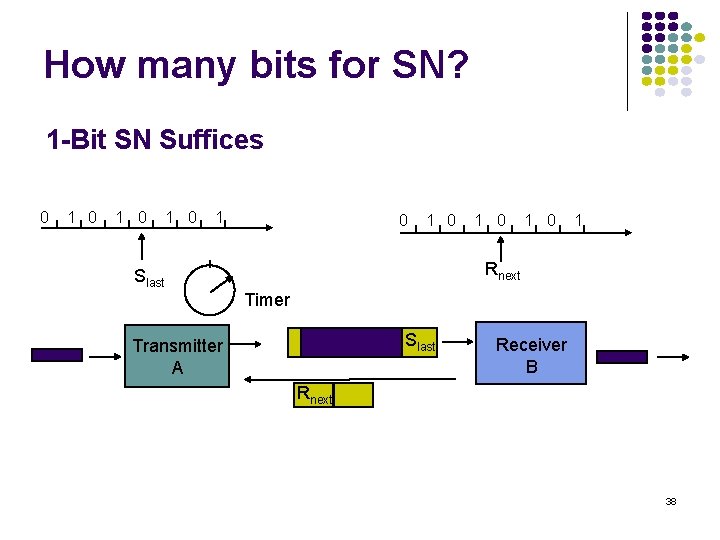
How many bits for SN? 1 -Bit SN Suffices 0 1 0 1 Rnext Slast Timer Slast Transmitter A Receiver B Rnext 38
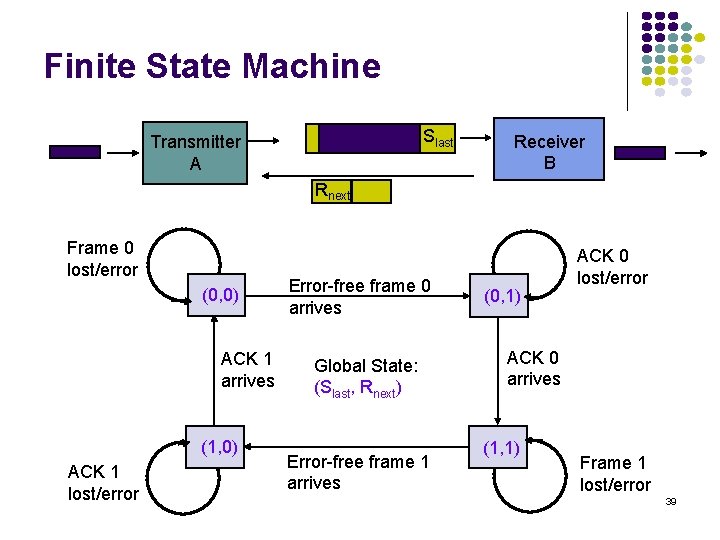
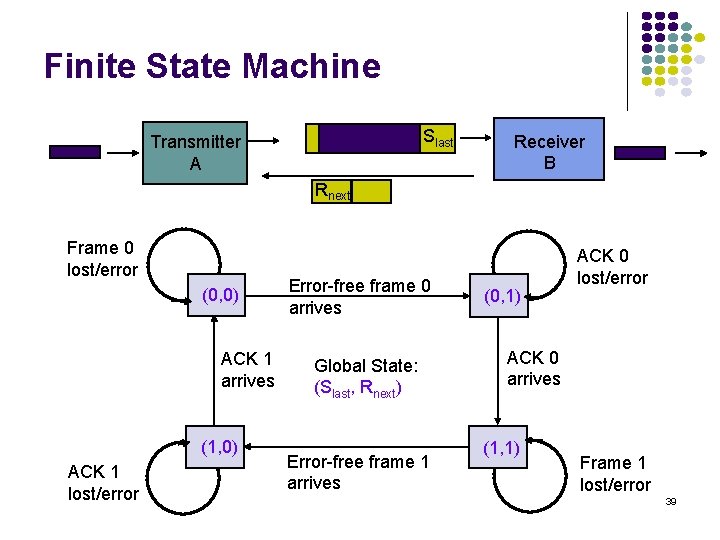
Finite State Machine Slast Transmitter A Receiver B Rnext Frame 0 lost/error (0, 0) ACK 1 arrives (1, 0) ACK 1 lost/error Error-free frame 0 arrives Global State: (Slast, Rnext) Error-free frame 1 arrives (0, 1) ACK 0 lost/error ACK 0 arrives (1, 1) Frame 1 lost/error 39
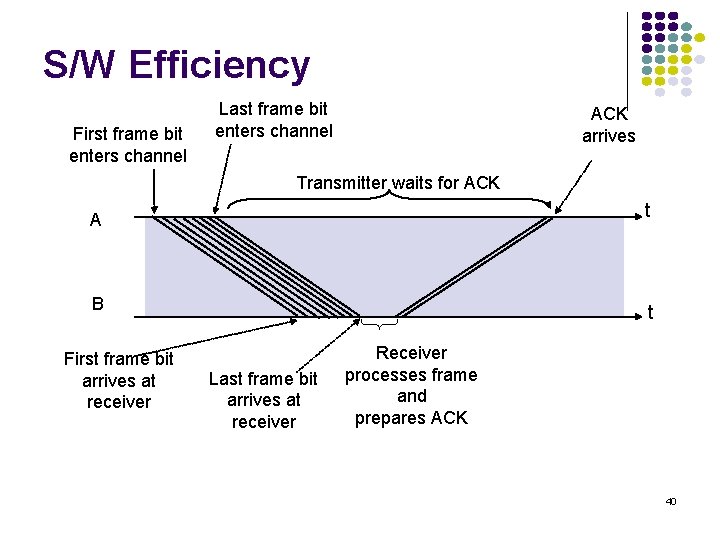
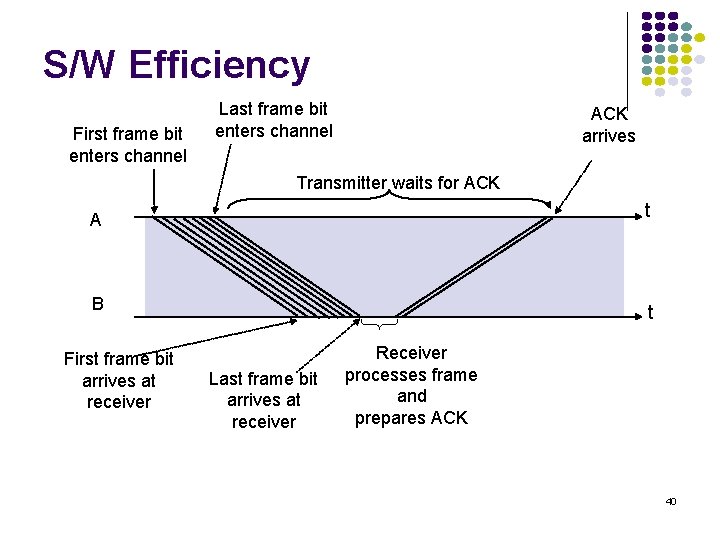
S/W Efficiency First frame bit enters channel Last frame bit enters channel ACK arrives Transmitter waits for ACK t A B First frame bit arrives at receiver t Last frame bit arrives at receiver Receiver processes frame and prepares ACK 40
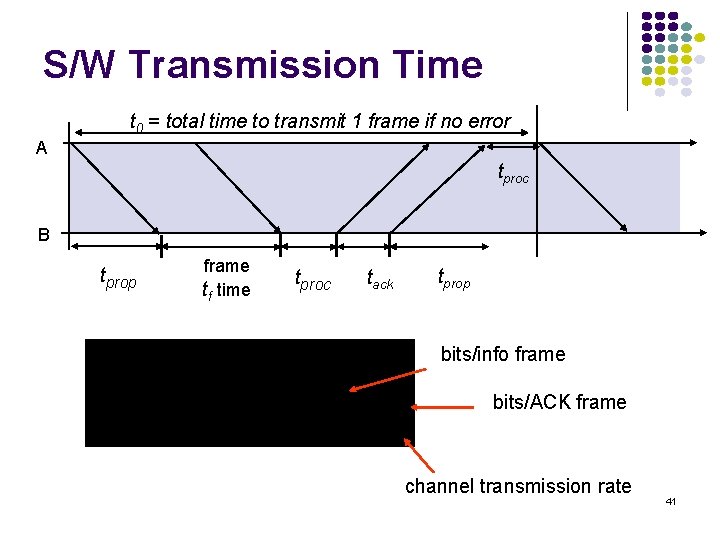
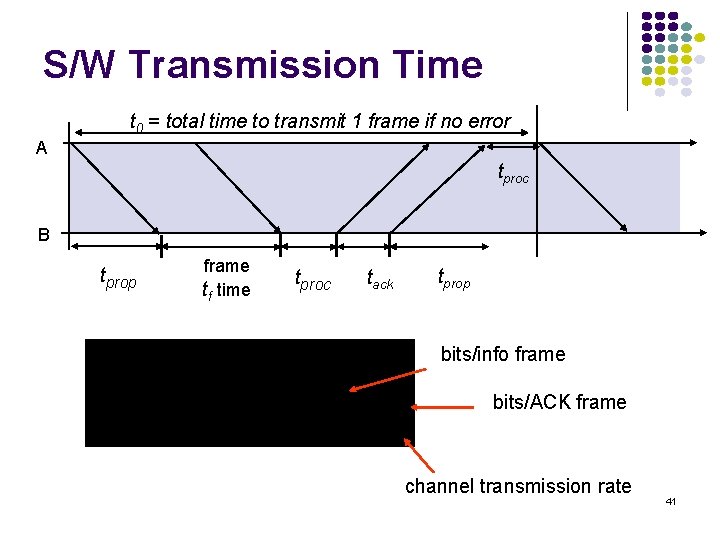
S/W Transmission Time t 0 = total time to transmit 1 frame if no error A tproc B tprop frame tf time tproc tack tprop bits/info frame bits/ACK frame channel transmission rate 41
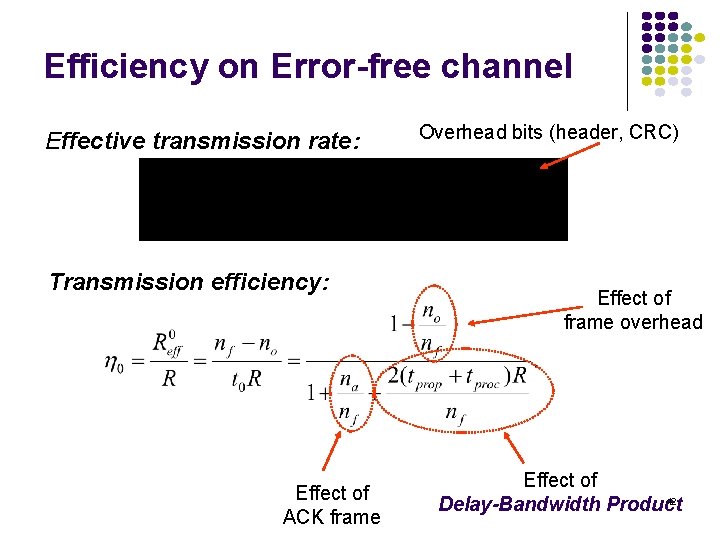
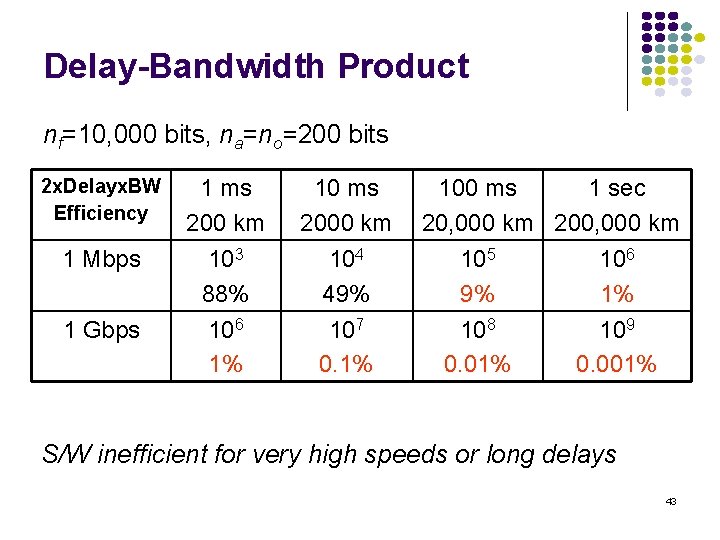
Efficiency on Error-free channel Effective transmission rate: Transmission efficiency: Effect of ACK frame Overhead bits (header, CRC) Effect of frame overhead Effect of 42 Delay-Bandwidth Product
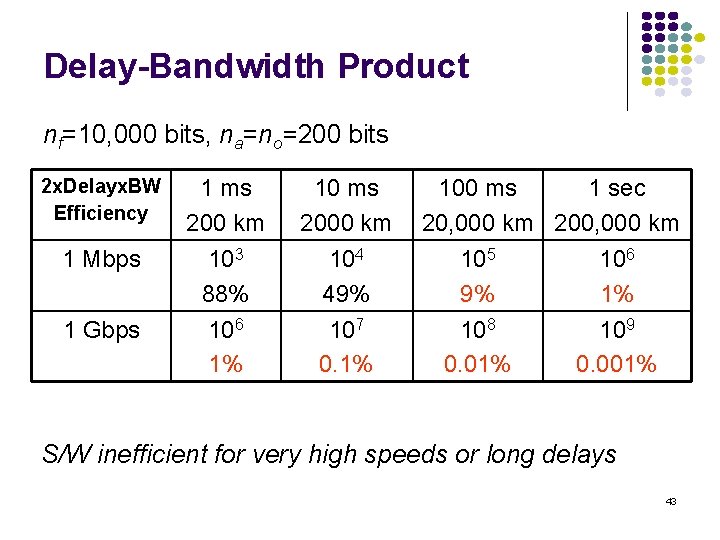
Delay-Bandwidth Product nf=10, 000 bits, na=no=200 bits 2 x. Delayx. BW Efficiency 1 Mbps 1 Gbps 1 ms 200 km 103 88% 10 ms 2000 km 104 49% 106 1% 107 0. 1% 100 ms 1 sec 20, 000 km 200, 000 km 105 106 9% 1% 108 0. 01% 109 0. 001% S/W inefficient for very high speeds or long delays 43
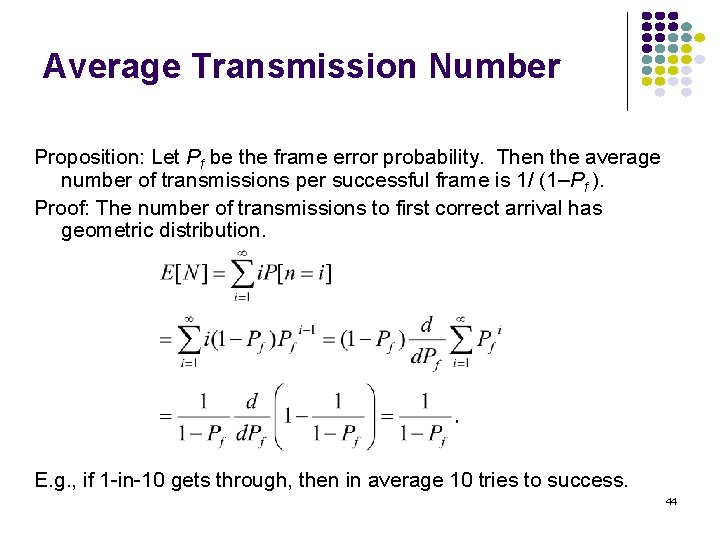
Average Transmission Number Proposition: Let Pf be the frame error probability. Then the average number of transmissions per successful frame is 1/ (1–Pf ). Proof: The number of transmissions to first correct arrival has geometric distribution. E. g. , if 1 -in-10 gets through, then in average 10 tries to success. 44
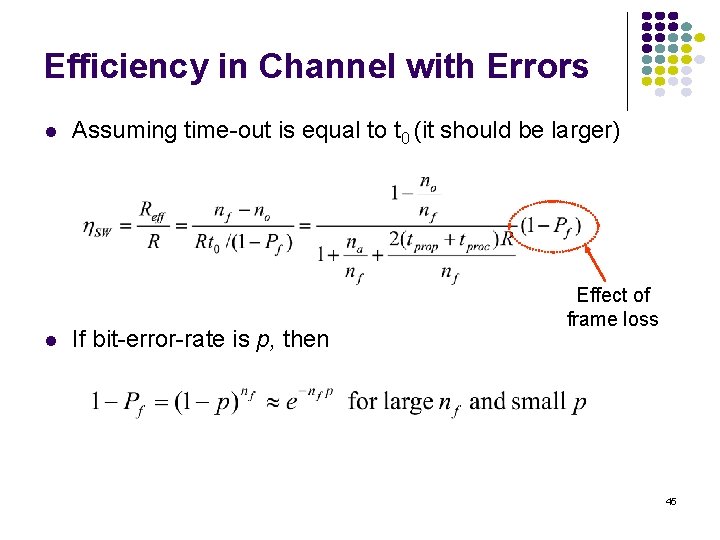
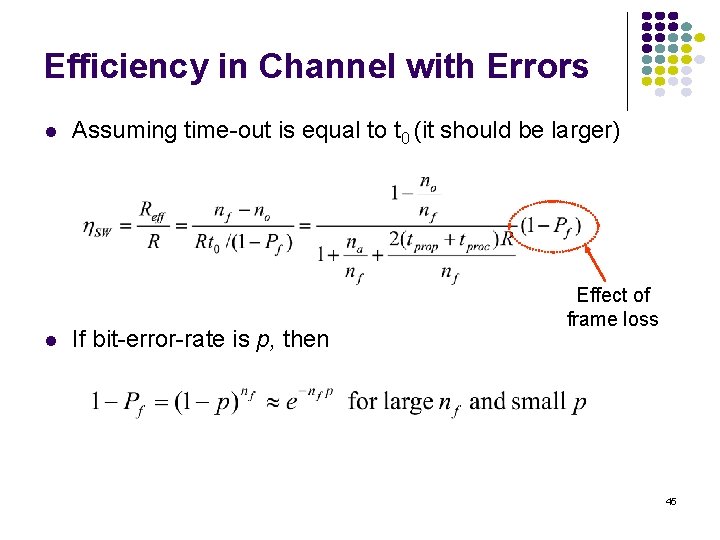
Efficiency in Channel with Errors l l Assuming time-out is equal to t 0 (it should be larger) If bit-error-rate is p, then Effect of frame loss 45
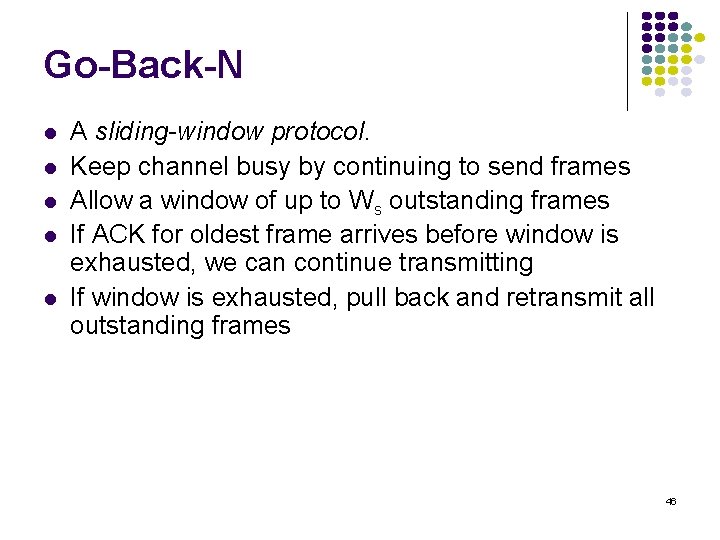
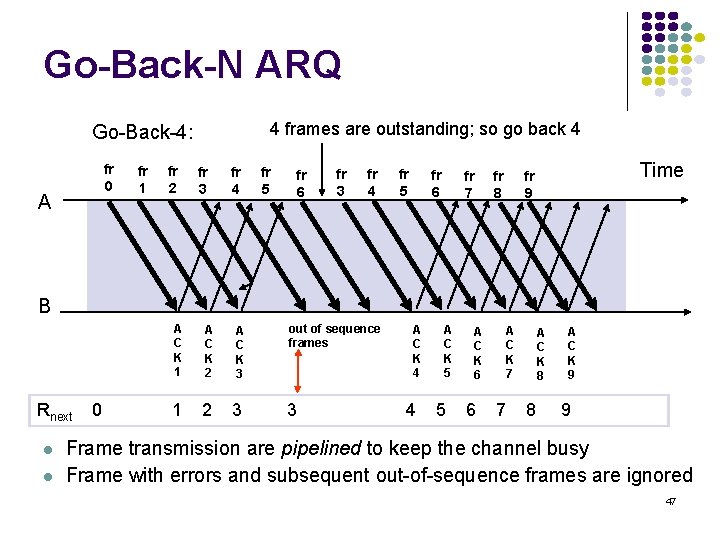
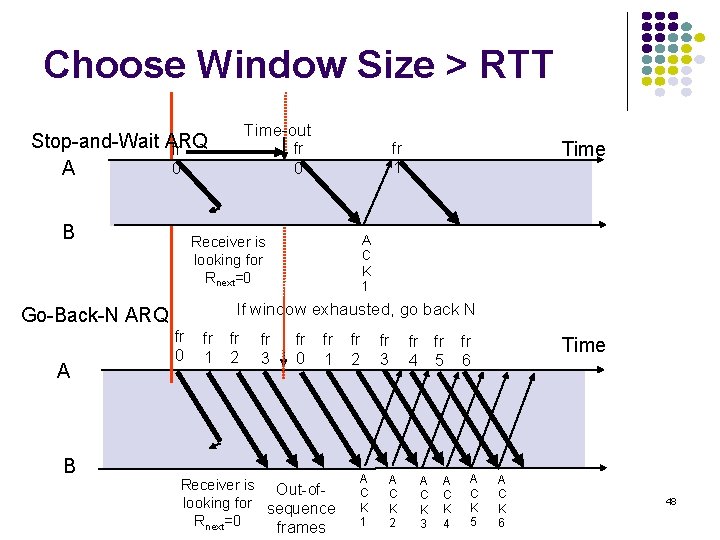
Go-Back-N l l l A sliding-window protocol. Keep channel busy by continuing to send frames Allow a window of up to Ws outstanding frames If ACK for oldest frame arrives before window is exhausted, we can continue transmitting If window is exhausted, pull back and retransmit all outstanding frames 46
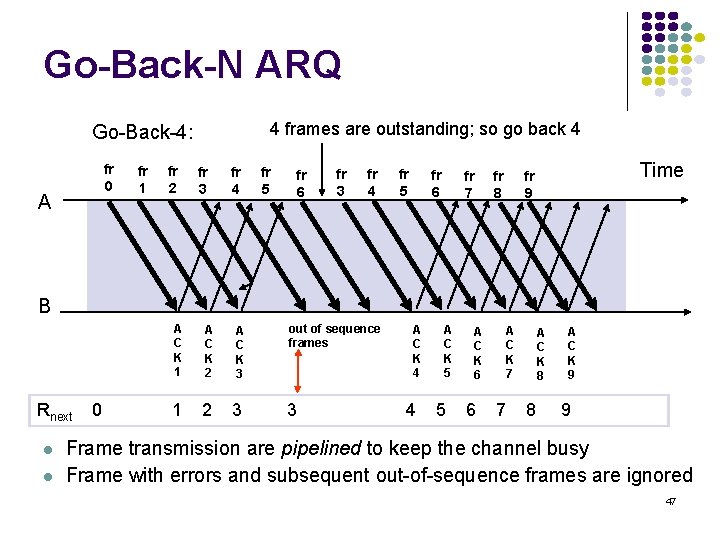
Go-Back-N ARQ 4 frames are outstanding; so go back 4 Go-Back-4: fr 0 A fr 1 fr 2 fr 3 fr 4 fr 5 fr 6 fr 7 fr 8 Time fr 9 B Rnext l l 0 A C K 1 A C K 2 A C K 3 1 2 3 out of sequence frames 3 A C K 4 4 A C K 5 5 A C K 6 6 A C K 7 7 A C K 8 8 A C K 9 9 Frame transmission are pipelined to keep the channel busy Frame with errors and subsequent out-of-sequence frames are ignored 47
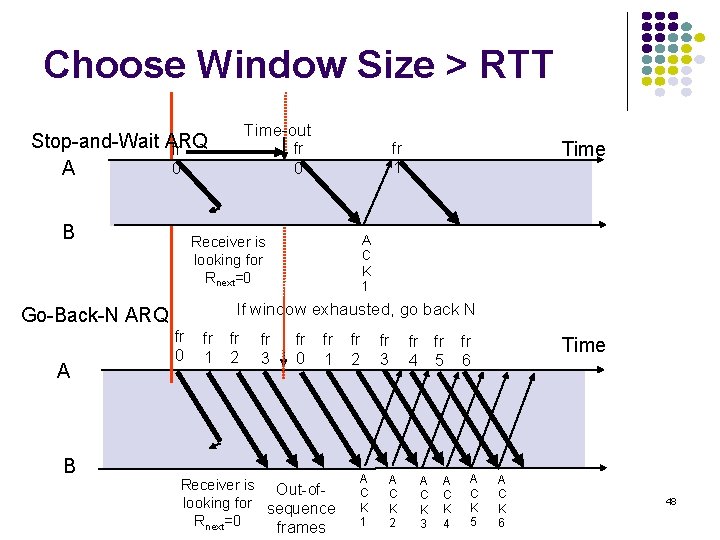
Choose Window Size > RTT Time-out Stop-and-Wait ARQ fr 0 A B B A C K 1 Receiver is looking for Rnext=0 If window exhausted, go back N Go-Back-N ARQ A Time fr 1 fr 0 fr 1 fr 2 fr 3 fr 0 fr 1 Receiver is Out-oflooking for sequence Rnext=0 frames fr 2 A C K 1 fr 3 A C K 2 fr fr 4 5 A C K 3 A C K 4 fr 6 A C K 5 Time A C K 6 48
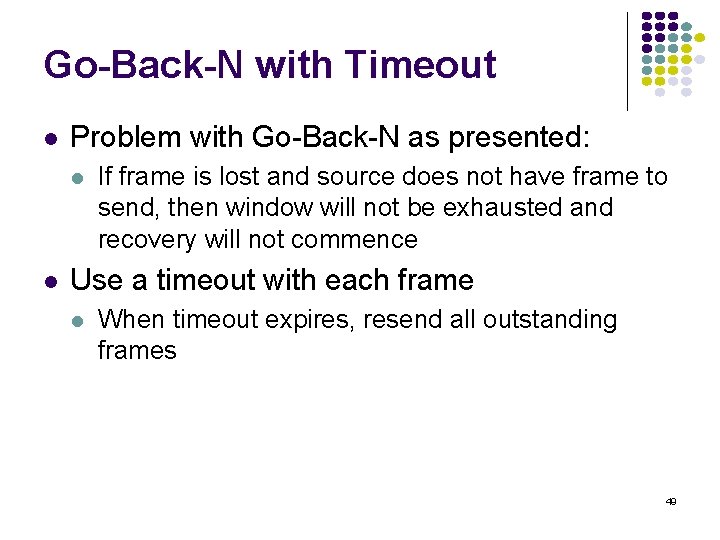
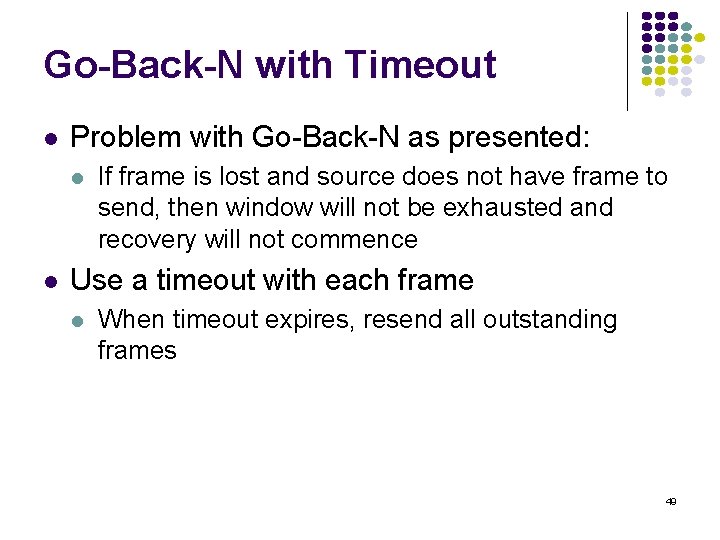
Go-Back-N with Timeout l Problem with Go-Back-N as presented: l l If frame is lost and source does not have frame to send, then window will not be exhausted and recovery will not commence Use a timeout with each frame l When timeout expires, resend all outstanding frames 49
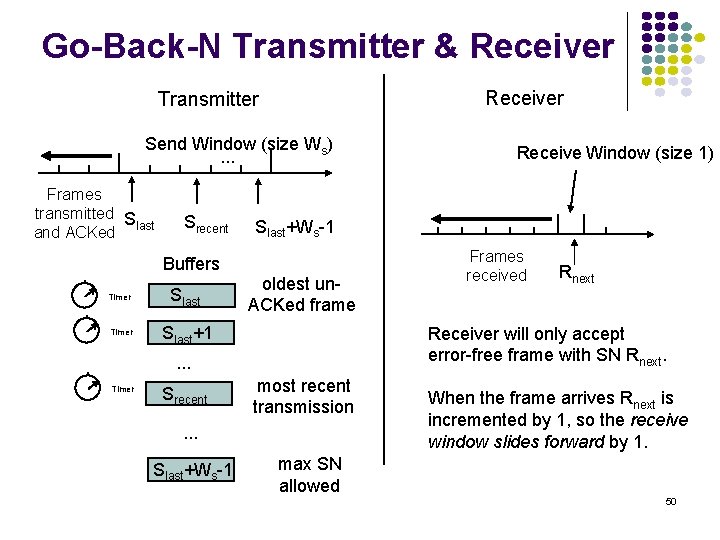
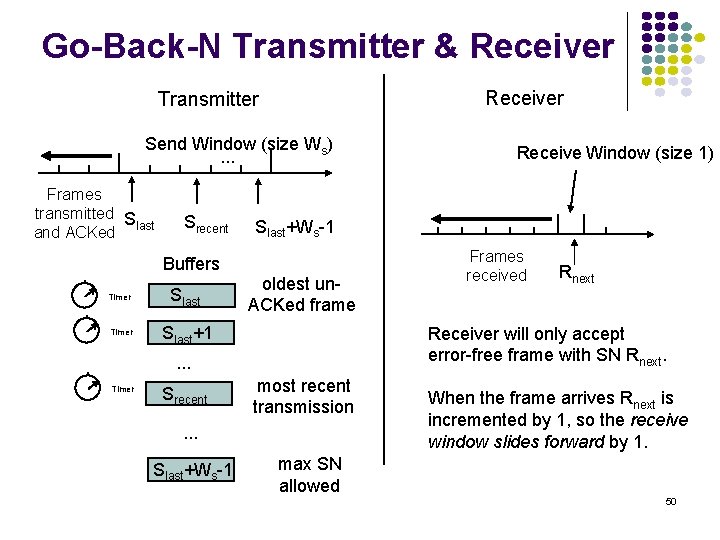
Go-Back-N Transmitter & Receiver Transmitter Send Window (size Ws). . . Frames transmitted S last and ACKed Srecent Buffers Timer Slast+1 Slast+Ws-1 oldest un. ACKed frame Srecent most recent transmission . . . Slast+Ws-1 Frames received Rnext Receiver will only accept error-free frame with SN Rnext. . Timer Receive Window (size 1) When the frame arrives Rnext is incremented by 1, so the receive window slides forward by 1. max SN allowed 50
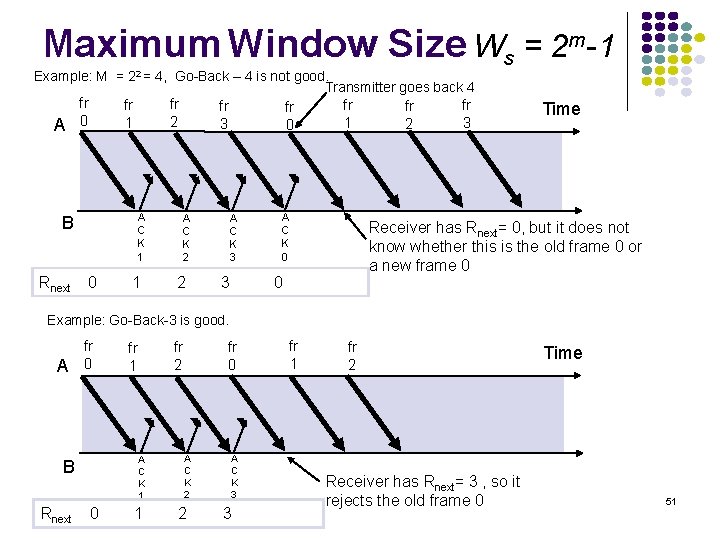
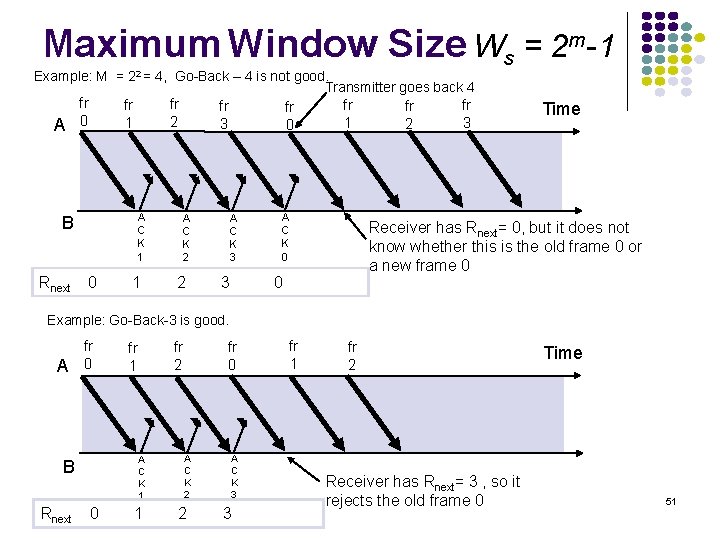
Maximum Window Size Ws = 2 m-1 Example: M = 22 = 4, Go-Back – 4 is not good. Transmitter goes back 4 A fr 0 A C K 1 B Rnext fr 2 fr 1 0 1 fr 3 A C K 2 2 fr 0 A C K 3 3 fr 1 A C K 0 fr 2 fr 3 Time Receiver has Rnext= 0, but it does not know whether this is the old frame 0 or a new frame 0 0 Example: Go-Back-3 is good. A fr 0 A C K 1 B Rnext 0 fr 2 fr 1 1 A C K 2 2 A C K 3 3 fr 1 fr 2 Receiver has Rnext= 3 , so it rejects the old frame 0 Time 51
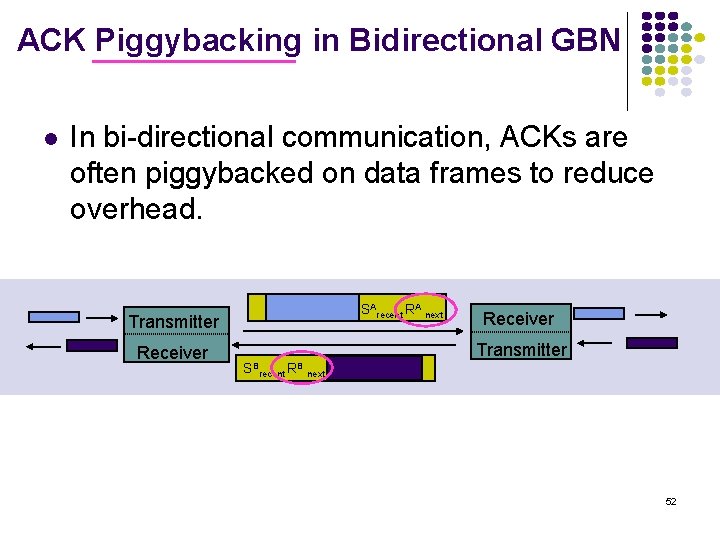
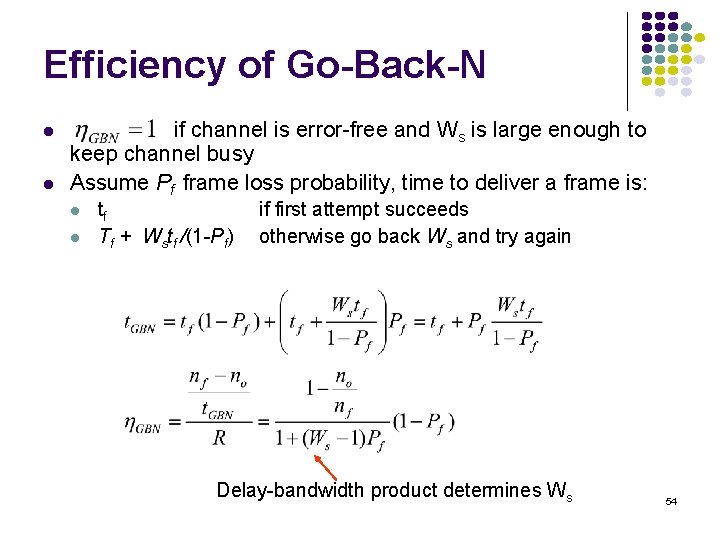
ACK Piggybacking in Bidirectional GBN l In bi-directional communication, ACKs are often piggybacked on data frames to reduce overhead. SArecent RA next Transmitter Receiver Transmitter SBrecent RB next 52
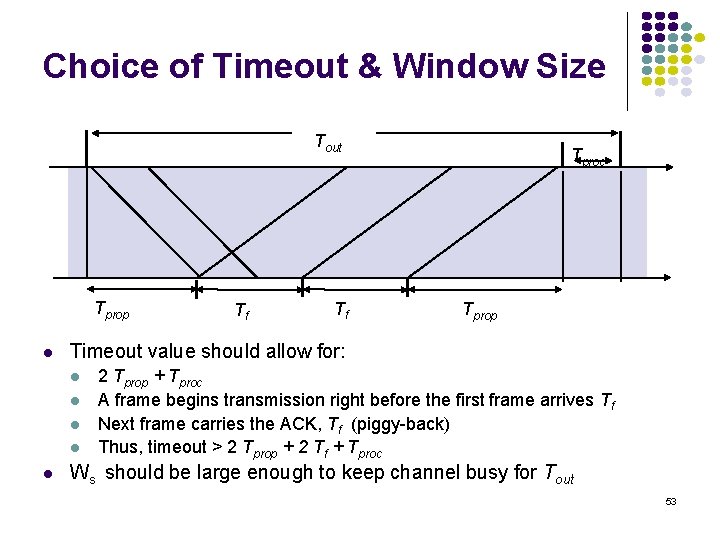
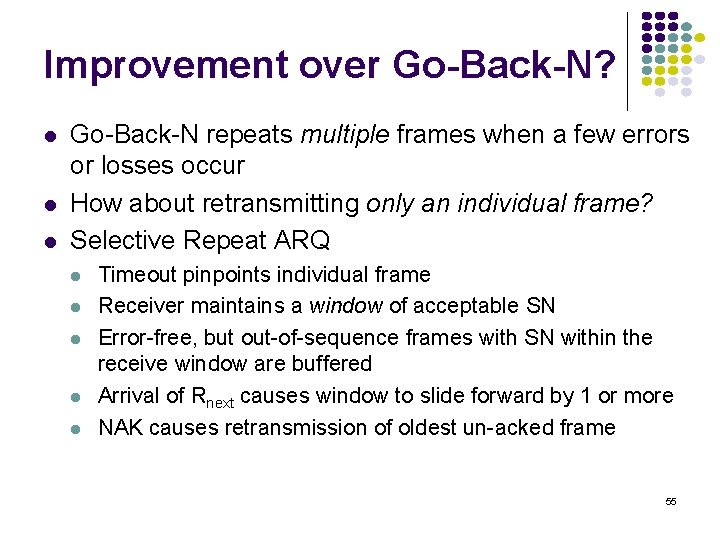
Choice of Timeout & Window Size Tout Tprop l Tf Tprop Timeout value should allow for: l l l Tf Tproc 2 Tprop + Tproc A frame begins transmission right before the first frame arrives Tf Next frame carries the ACK, Tf (piggy-back) Thus, timeout > 2 Tprop + 2 Tf + Tproc Ws should be large enough to keep channel busy for Tout 53
Efficiency of Go-Back-N l l if channel is error-free and Ws is large enough to keep channel busy Assume Pf frame loss probability, time to deliver a frame is: l l tf Tf + Wstf /(1 -Pf) if first attempt succeeds otherwise go back Ws and try again Delay-bandwidth product determines Ws 54
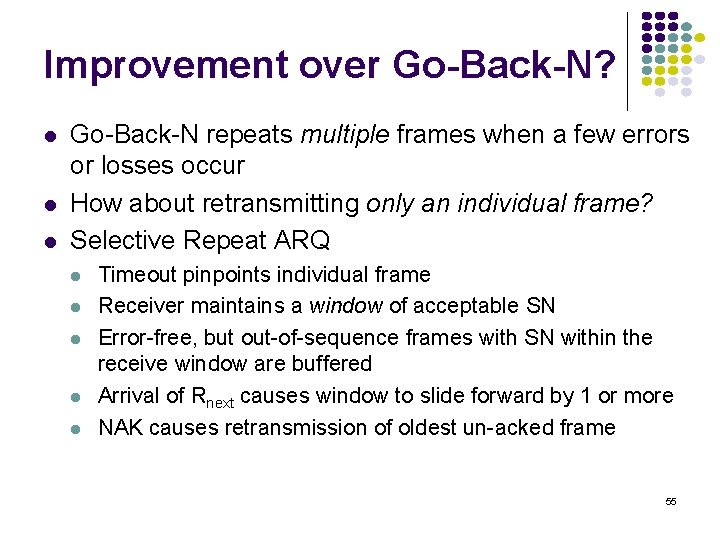
Improvement over Go-Back-N? l l l Go-Back-N repeats multiple frames when a few errors or losses occur How about retransmitting only an individual frame? Selective Repeat ARQ l l l Timeout pinpoints individual frame Receiver maintains a window of acceptable SN Error-free, but out-of-sequence frames with SN within the receive window are buffered Arrival of Rnext causes window to slide forward by 1 or more NAK causes retransmission of oldest un-acked frame 55
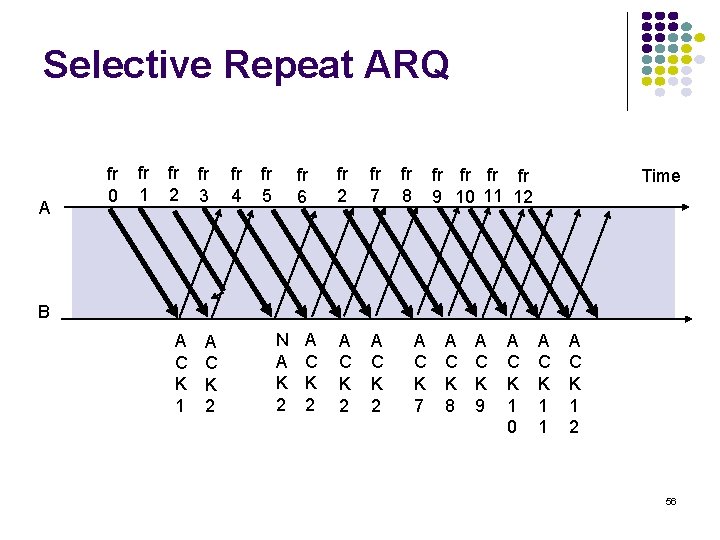
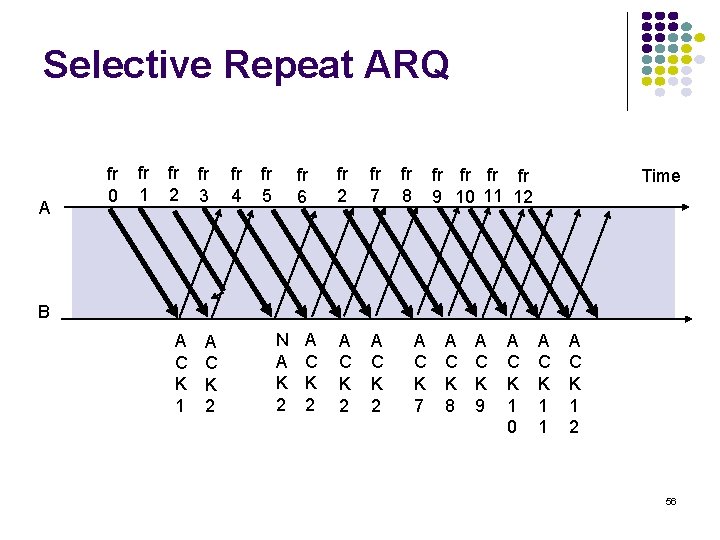
Selective Repeat ARQ A fr 0 fr 1 fr 2 fr 3 fr 4 fr 5 fr 6 fr 2 fr 7 A C K 2 fr 8 fr fr 9 10 11 12 Time B A C K 1 A C K 2 N A K 2 A C K 7 A C K 8 A C K 9 A C K 1 0 A C K 1 1 A C K 1 2 56
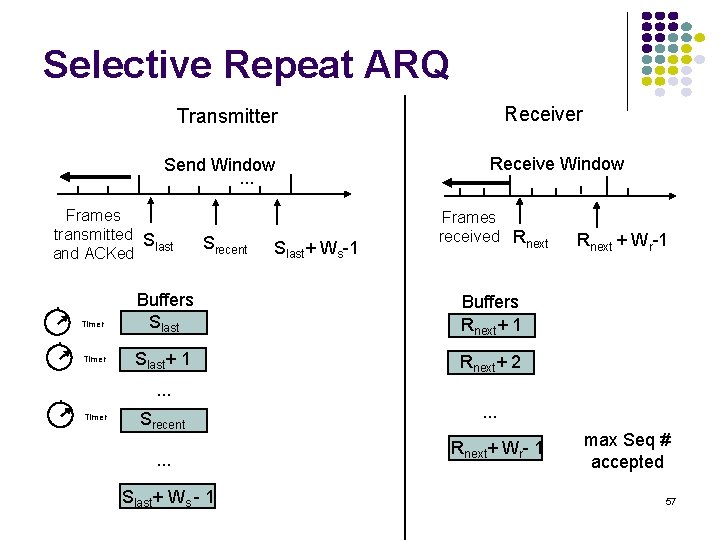
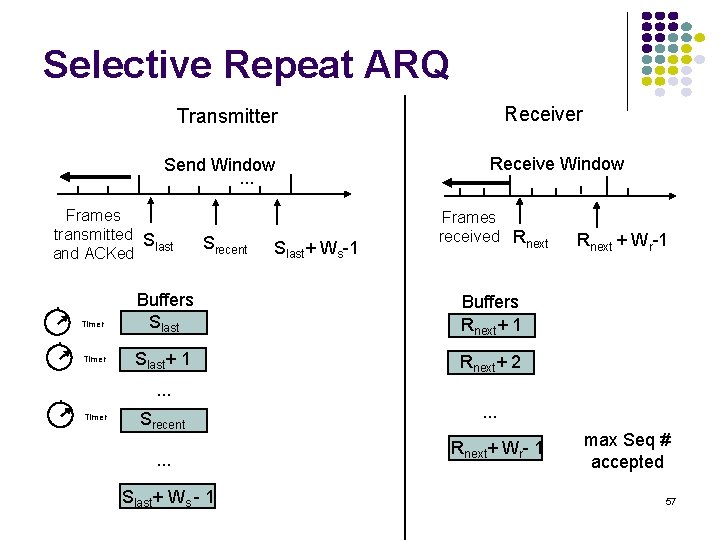
Selective Repeat ARQ Receiver Transmitter Send Window. . . Frames transmitted S last and ACKed Timer Srecent Slast+ Ws-1 Receive Window Frames received Rnext Buffers Slast Buffers Rnext+ 1 Slast+ 1 Rnext+ 2 Rnext + Wr-1 . . . Timer Srecent. . . Slast+ Ws - 1 . . . Rnext+ Wr- 1 max Seq # accepted 57
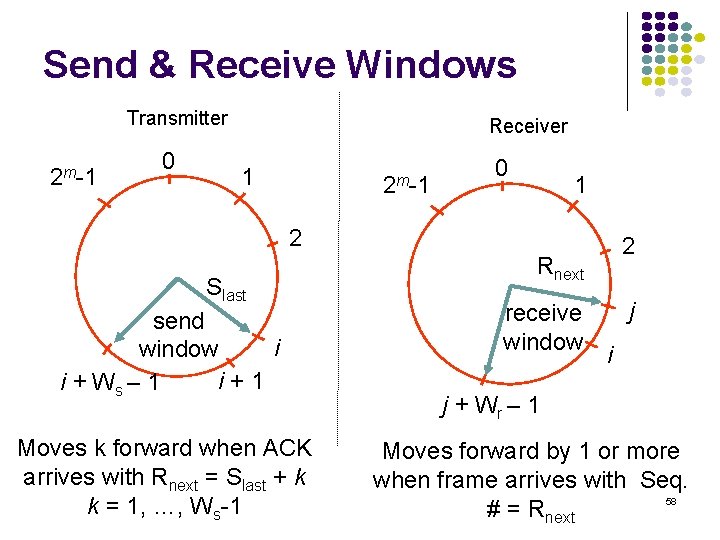
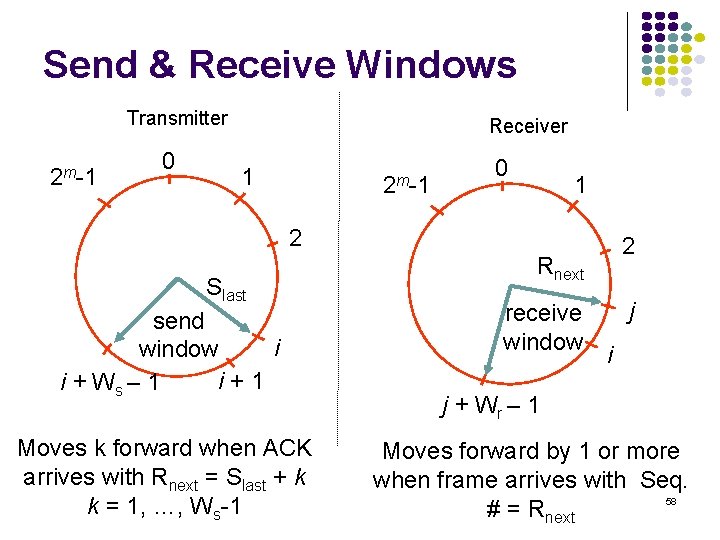
Send & Receive Windows Transmitter 2 m-1 0 Receiver 1 2 m-1 0 1 2 Slast send i window i+1 i + Ws – 1 Moves k forward when ACK arrives with Rnext = Slast + k k = 1, …, Ws-1 2 Rnext receive window j i j + Wr – 1 Moves forward by 1 or more when frame arrives with Seq. 58 # = Rnext
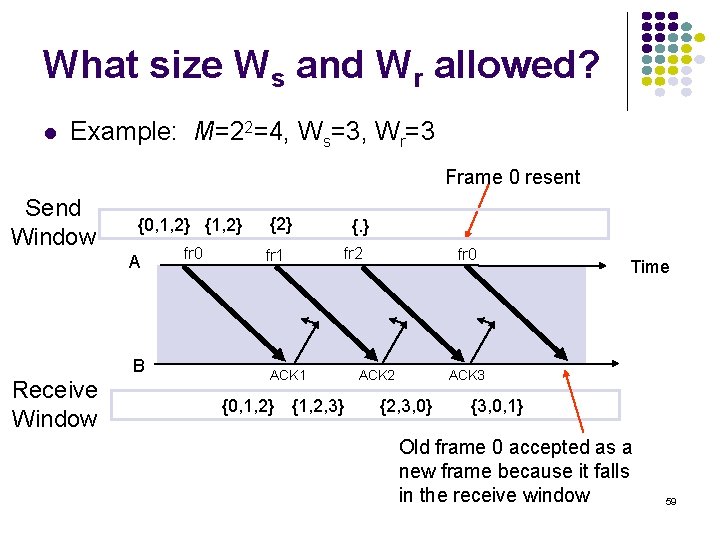
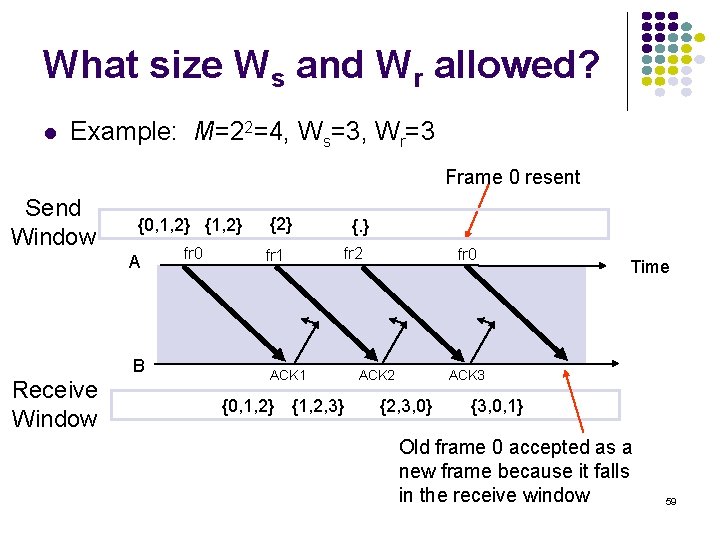
What size Ws and Wr allowed? l Example: M=22=4, Ws=3, Wr=3 Frame 0 resent Send Window {0, 1, 2} {1, 2} A B Receive Window fr 0 {2} fr 1 {. } fr 2 ACK 1 {0, 1, 2} {1, 2, 3} fr 0 ACK 2 Time ACK 3 {2, 3, 0} {3, 0, 1} Old frame 0 accepted as a new frame because it falls in the receive window 59
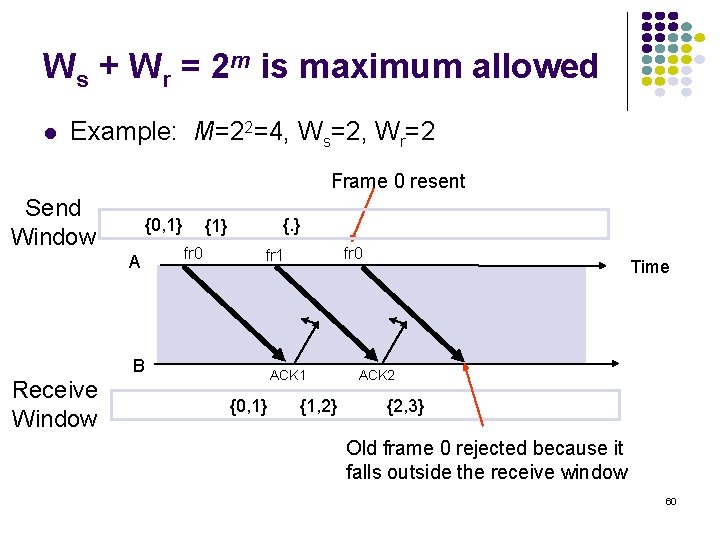
Ws + Wr = 2 m is maximum allowed l Example: M=22=4, Ws=2, Wr=2 Frame 0 resent Send Window {0, 1} A {. } {1} fr 0 B Receive Window fr 0 fr 1 ACK 1 {0, 1} {1, 2} Time ACK 2 {2, 3} Old frame 0 rejected because it falls outside the receive window 60
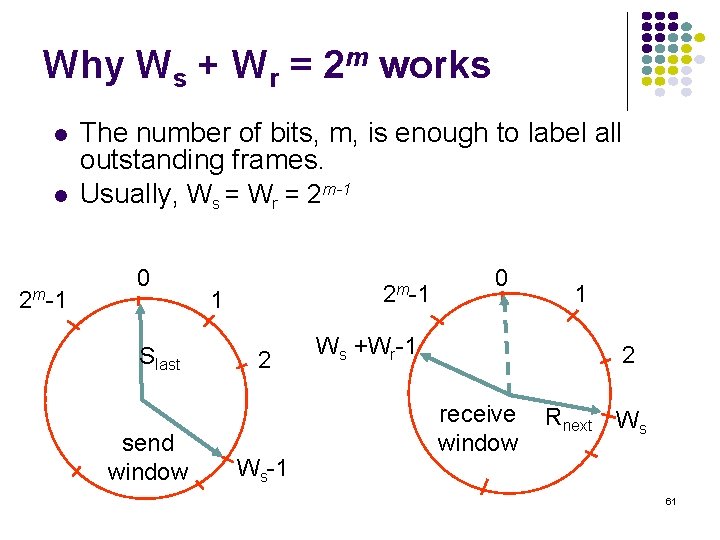
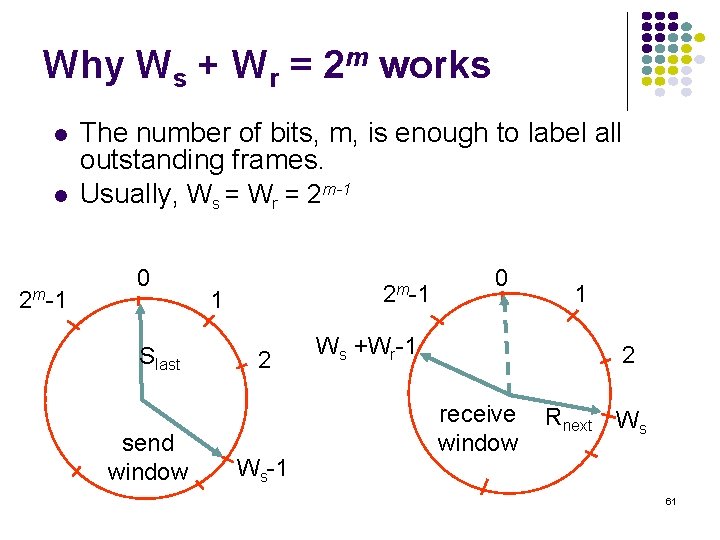
Why Ws + Wr = 2 m works l l 2 m-1 The number of bits, m, is enough to label all outstanding frames. Usually, Ws = Wr = 2 m-1 0 Slast send window 2 m-1 1 2 Ws-1 0 Ws +Wr-1 1 2 receive window Rnext Ws 61
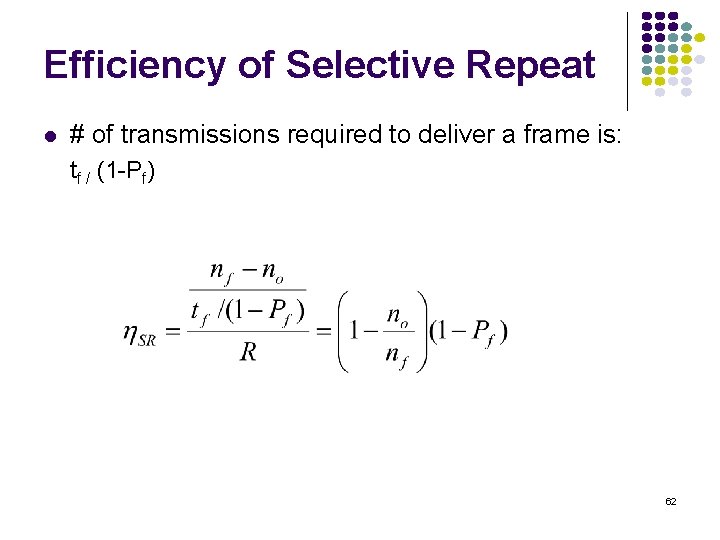
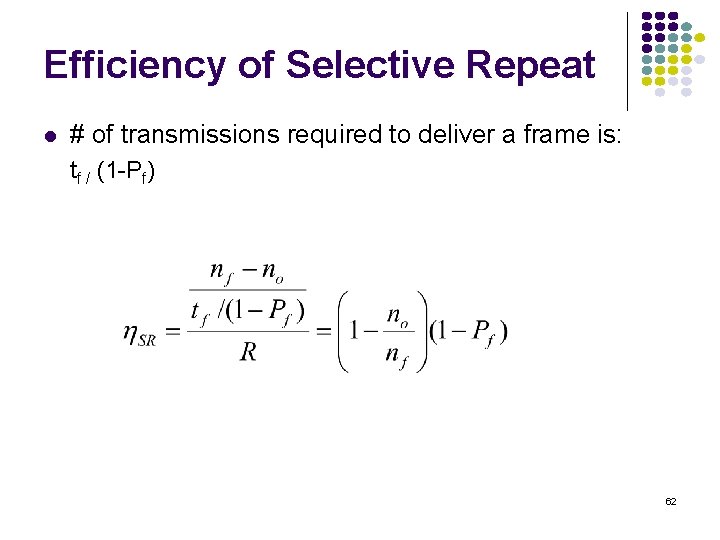
Efficiency of Selective Repeat l # of transmissions required to deliver a frame is: tf / (1 -Pf) 62
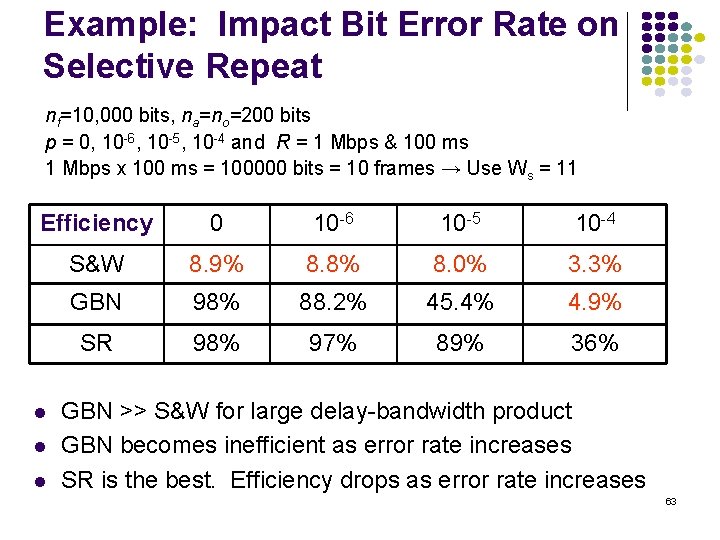
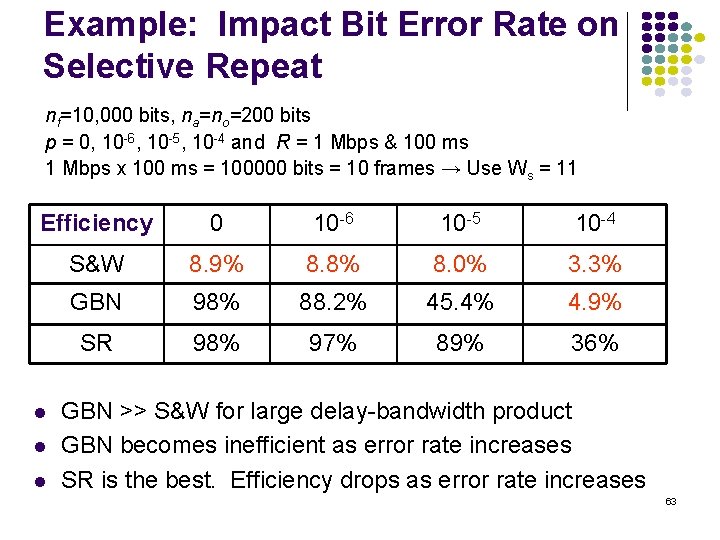
Example: Impact Bit Error Rate on Selective Repeat nf=10, 000 bits, na=no=200 bits p = 0, 10 -6, 10 -5, 10 -4 and R = 1 Mbps & 100 ms 1 Mbps x 100 ms = 100000 bits = 10 frames → Use Ws = 11 Efficiency 0 10 -6 10 -5 10 -4 S&W 8. 9% 8. 8% 8. 0% 3. 3% GBN 98% 88. 2% 45. 4% 4. 9% SR 98% 97% 89% 36% l l l GBN >> S&W for large delay-bandwidth product GBN becomes inefficient as error rate increases SR is the best. Efficiency drops as error rate increases 63
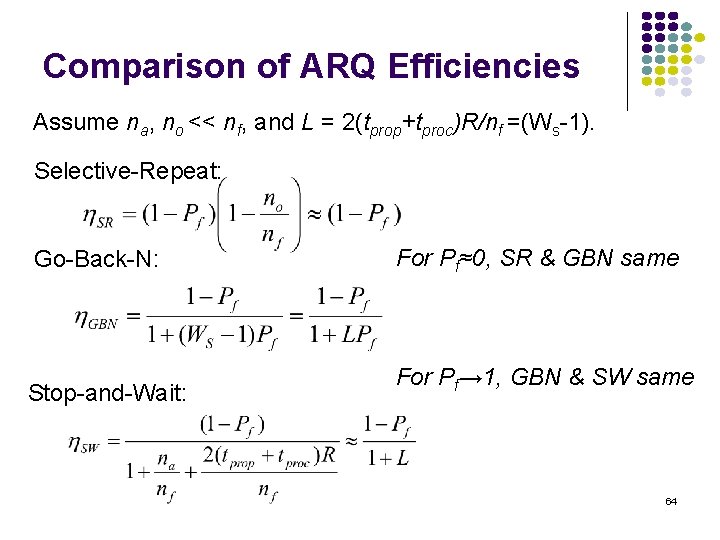
Comparison of ARQ Efficiencies Assume na, no << nf, and L = 2(tprop+tproc)R/nf =(Ws-1). Selective-Repeat: Go-Back-N: For Pf≈0, SR & GBN same Stop-and-Wait: For Pf→ 1, GBN & SW same 64
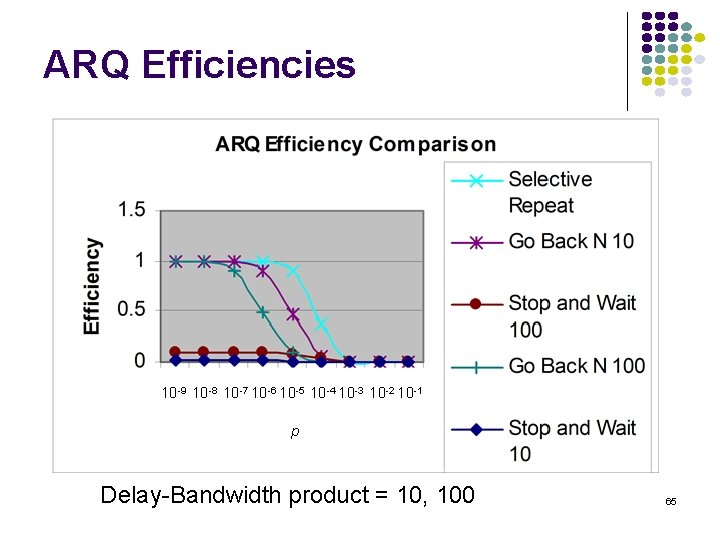
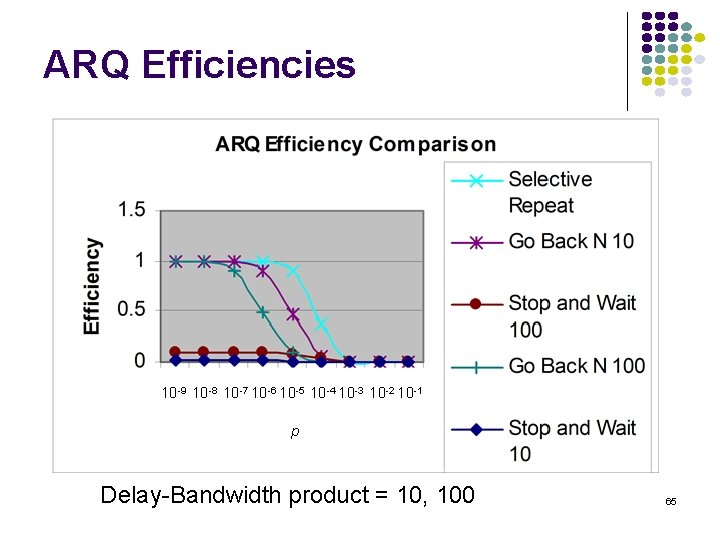
ARQ Efficiencies 10 -9 10 -8 10 -7 10 -6 10 -5 10 -4 10 -3 10 -2 10 -1 p Delay-Bandwidth product = 10, 100 65
Standard Data Link Layer Protocols: PPP & HDLC (Chapter 5. 5 -6 in Leon-Garcia) 66
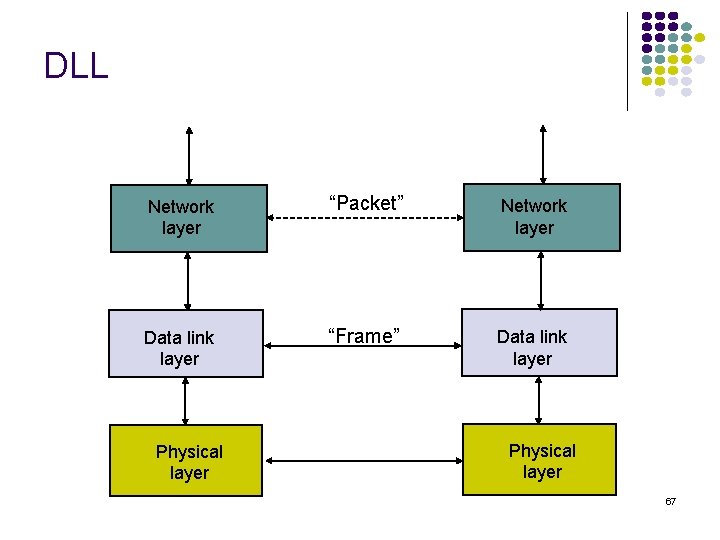
DLL Network layer “Packet” Network layer Data link layer “Frame” Data link layer Physical layer 67
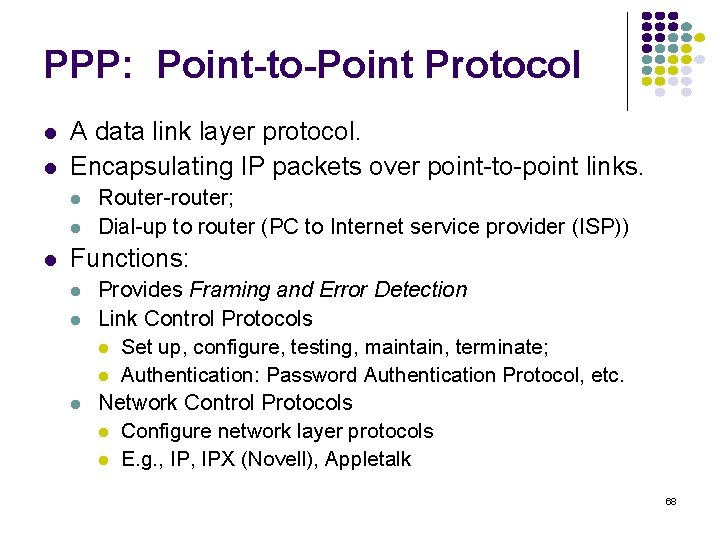
PPP: Point-to-Point Protocol l l A data link layer protocol. Encapsulating IP packets over point-to-point links. l l l Router-router; Dial-up to router (PC to Internet service provider (ISP)) Functions: l l l Provides Framing and Error Detection Link Control Protocols l Set up, configure, testing, maintain, terminate; l Authentication: Password Authentication Protocol, etc. Network Control Protocols l Configure network layer protocols l E. g. , IPX (Novell), Appletalk 68
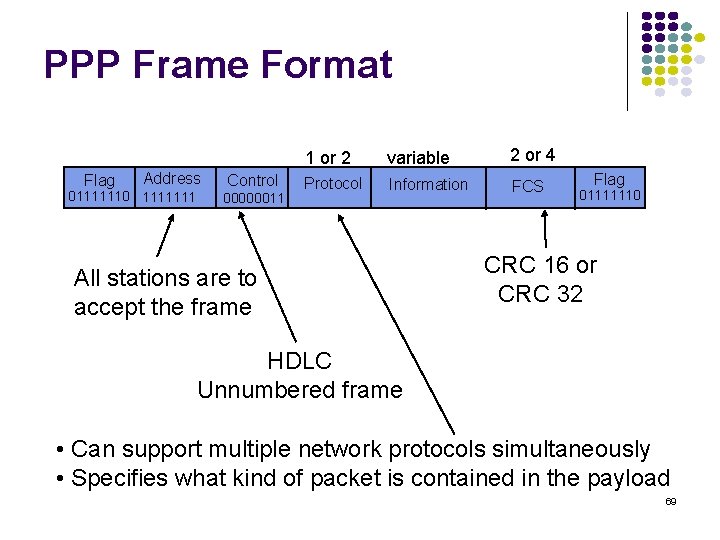
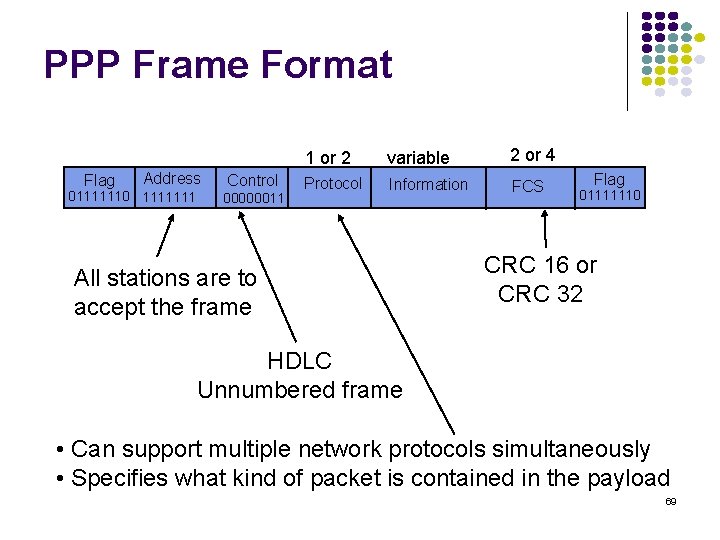
PPP Frame Format Flag Address 01111110 1111111 Control 00000011 1 or 2 variable 2 or 4 Protocol Information FCS All stations are to accept the frame Flag 01111110 CRC 16 or CRC 32 HDLC Unnumbered frame • Can support multiple network protocols simultaneously • Specifies what kind of packet is contained in the payload 69
High-Level Data Link Control (HDLC) l l Bit-oriented data link control Derived from IBM Synchronous Data Link Control (SDLC) 70
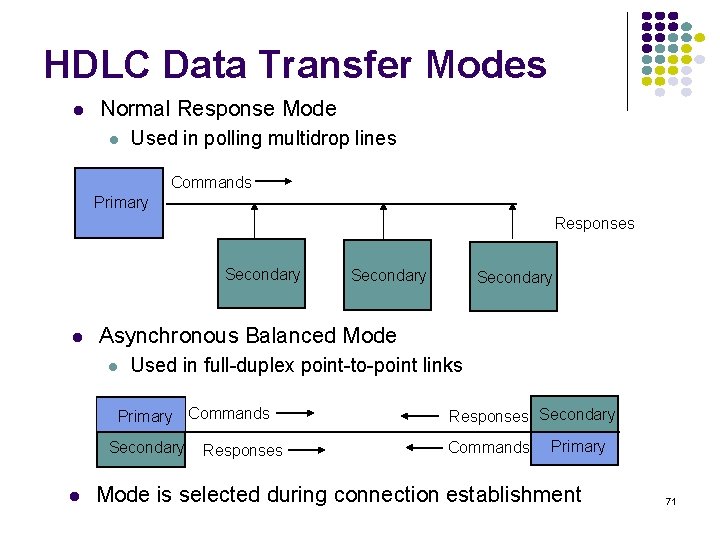
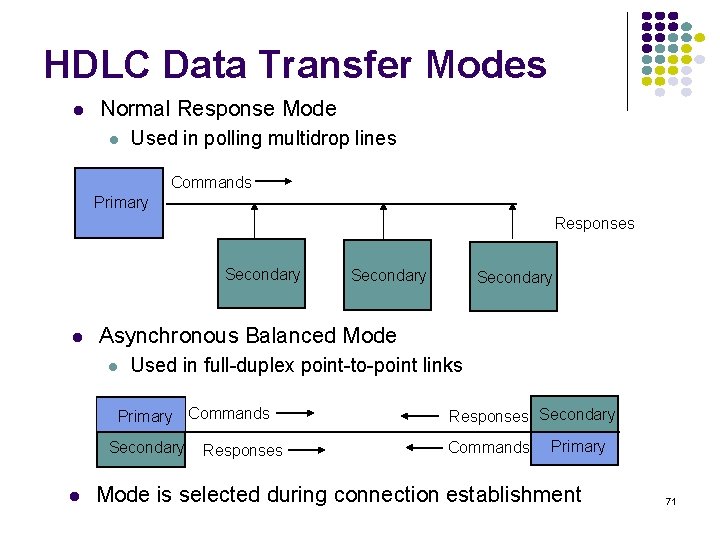
HDLC Data Transfer Modes l Normal Response Mode l Used in polling multidrop lines Commands Primary Responses Secondary l Secondary Asynchronous Balanced Mode l Used in full-duplex point-to-point links Primary Commands Secondary l Secondary Responses Secondary Commands Primary Mode is selected during connection establishment 71
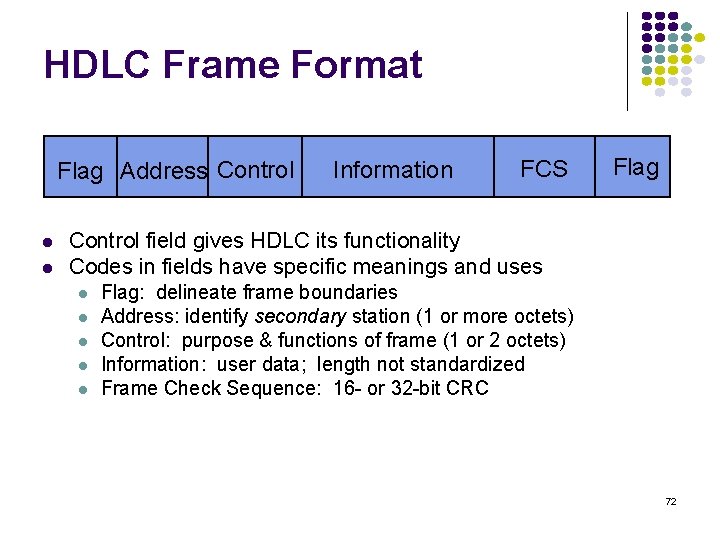
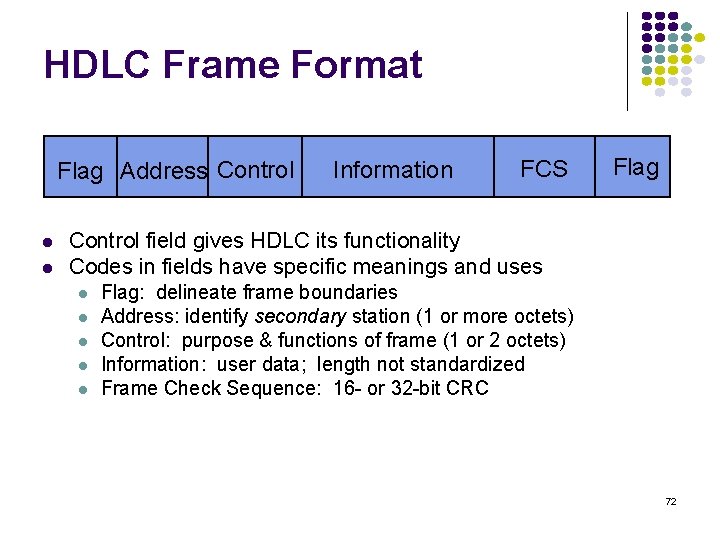
HDLC Frame Format Flag Address Control l l Information FCS Flag Control field gives HDLC its functionality Codes in fields have specific meanings and uses l l l Flag: delineate frame boundaries Address: identify secondary station (1 or more octets) Control: purpose & functions of frame (1 or 2 octets) Information: user data; length not standardized Frame Check Sequence: 16 - or 32 -bit CRC 72
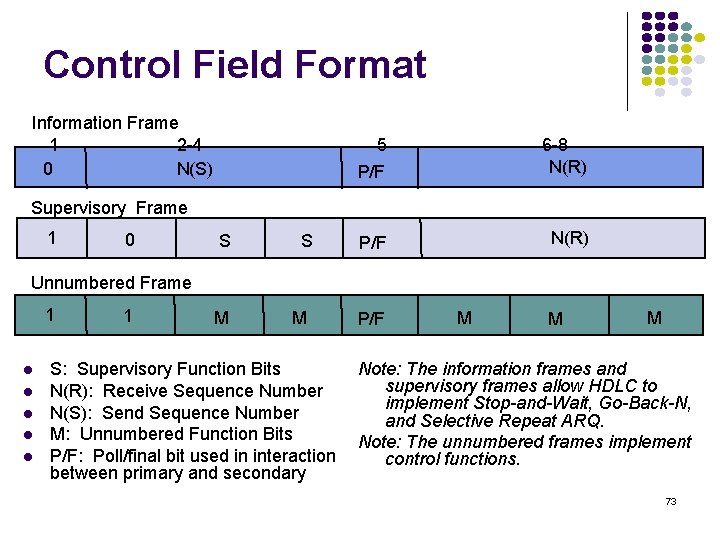
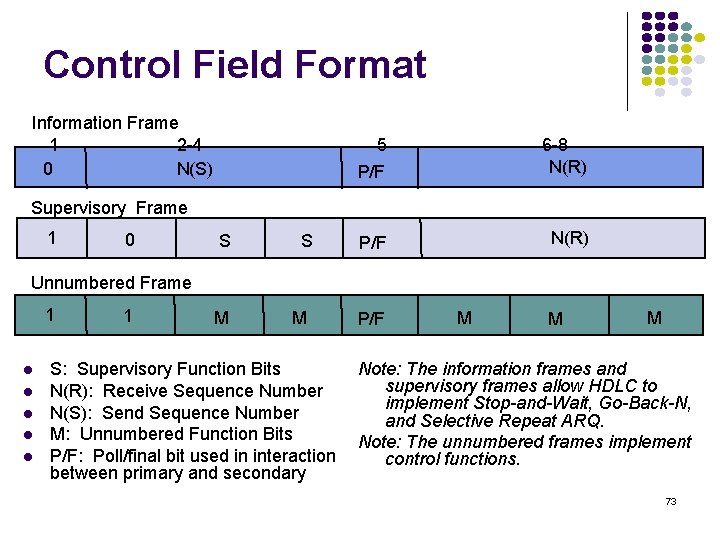
Control Field Format Information Frame 1 2 -4 0 N(S) 5 P/F 6 -8 N(R) P/F N(R) Supervisory Frame 1 0 S S Unnumbered Frame 1 l l l 1 M M S: Supervisory Function Bits N(R): Receive Sequence Number N(S): Send Sequence Number M: Unnumbered Function Bits P/F: Poll/final bit used in interaction between primary and secondary P/F M M M Note: The information frames and supervisory frames allow HDLC to implement Stop-and-Wait, Go-Back-N, and Selective Repeat ARQ. Note: The unnumbered frames implement control functions. 73
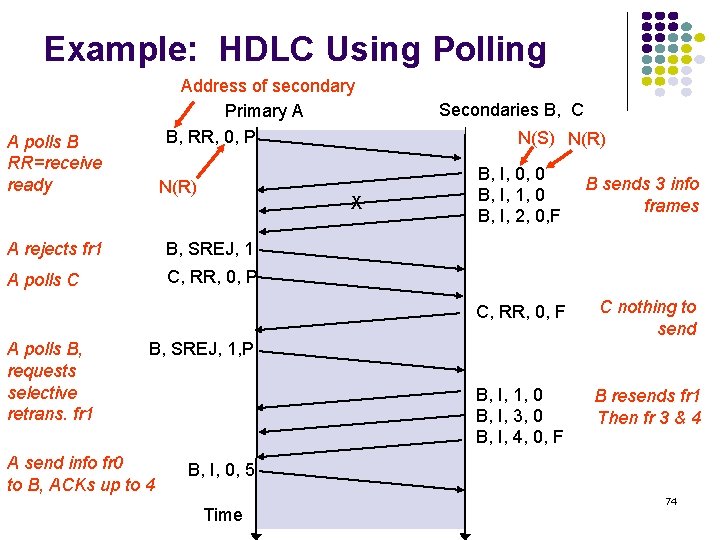
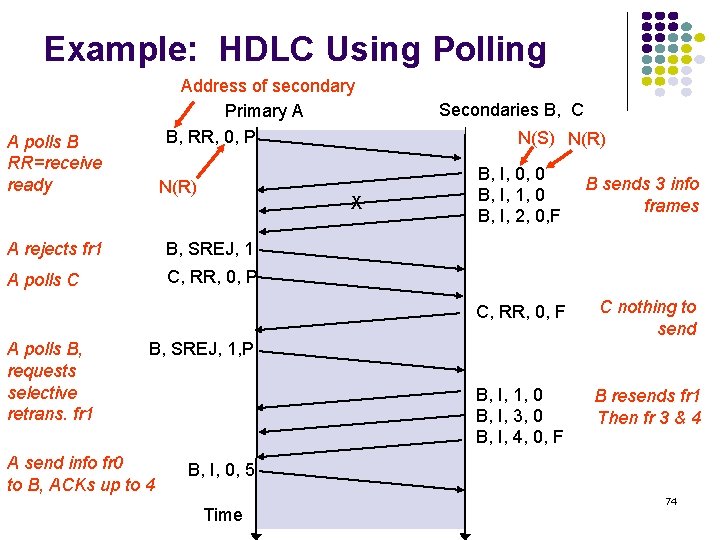
Example: HDLC Using Polling Address of secondary Primary A B, RR, 0, P A polls B RR=receive ready N(R) X A rejects fr 1 B, SREJ, 1 A polls C C, RR, 0, P A polls B, requests selective retrans. fr 1 Secondaries B, C N(S) N(R) B, I, 0, 0 B, I, 1, 0 B, I, 2, 0, F B sends 3 info frames C, RR, 0, F C nothing to send B, I, 1, 0 B, I, 3, 0 B, I, 4, 0, F B resends fr 1 Then fr 3 & 4 B, SREJ, 1, P A send info fr 0 to B, ACKs up to 4 B, I, 0, 5 Time 74
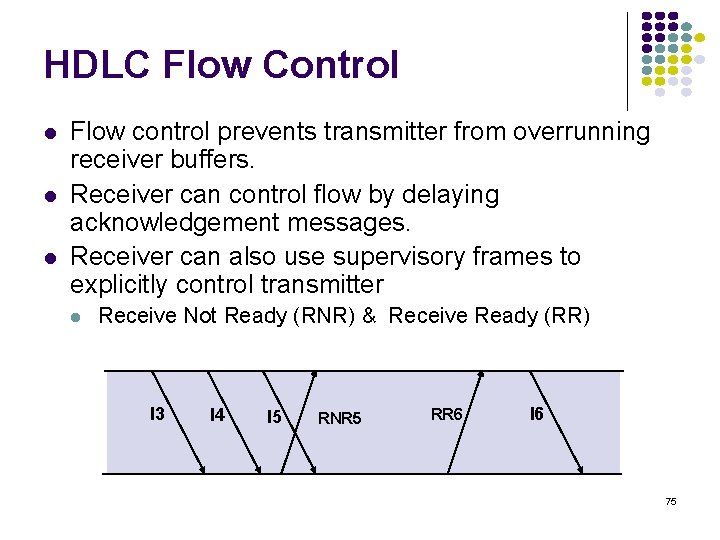
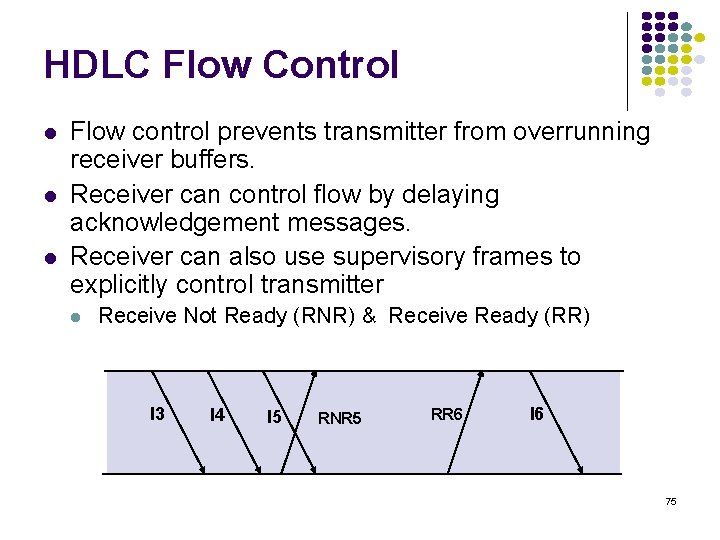
HDLC Flow Control l Flow control prevents transmitter from overrunning receiver buffers. Receiver can control flow by delaying acknowledgement messages. Receiver can also use supervisory frames to explicitly control transmitter l Receive Not Ready (RNR) & Receive Ready (RR) I 3 I 4 I 5 RNR 5 RR 6 I 6 75