A Link Layer Protocol for Quantum Networks Axel
- Slides: 55
A Link Layer Protocol for Quantum Networks Axel Dahlberg, Matt Skrzypczyk, Tim Coopmans, Leon Wubben, Filip Rozpędek, Matteo Pompili, Arian Stolk, Przemysław Pawełczak, Robert Knegjens, Julio de Oliveira Filho, Ronald Hanson, Stephanie Wehner ACM SIGCOMM 2019 – Wednesday 08/21/2019
Joint work with Axel Dahlberg Tim Coopmans Leon Wubben Filip Rozpędek Matteo Pompili Arian Stolk Przemysław Pawełczak Rob Knegjens Julio de Oliveira Filho Ronald Hanson Stephanie Wehner
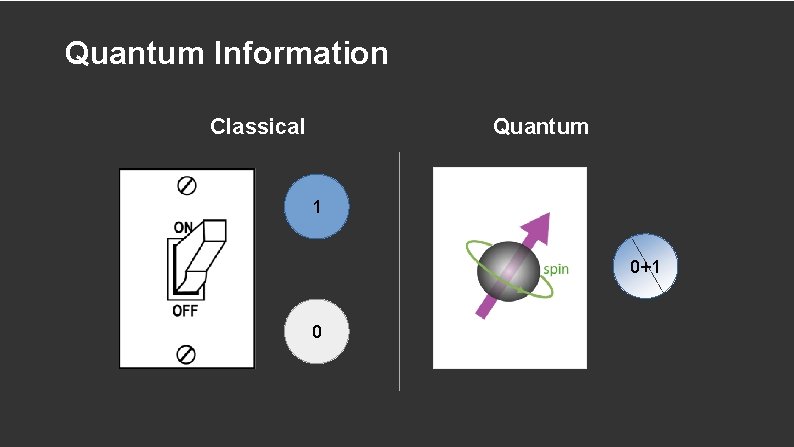
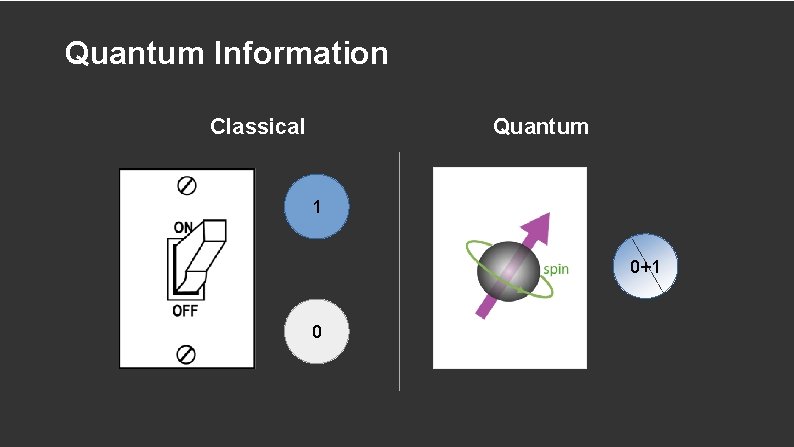
Quantum Information Classical Quantum 1 0+1 0
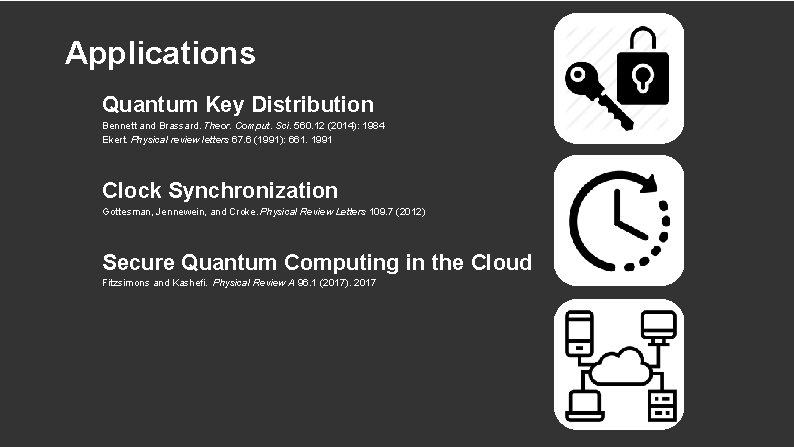
Applications Quantum Key Distribution Bennett and Brassard. Theor. Comput. Sci. 560. 12 (2014): 1984 Ekert. Physical review letters 67. 6 (1991): 661. 1991 Clock Synchronization Gottesman, Jennewein, and Croke. Physical Review Letters 109. 7 (2012) Secure Quantum Computing in the Cloud Fitzsimons and Kashefi. Physical Review A 96. 1 (2017). 2017
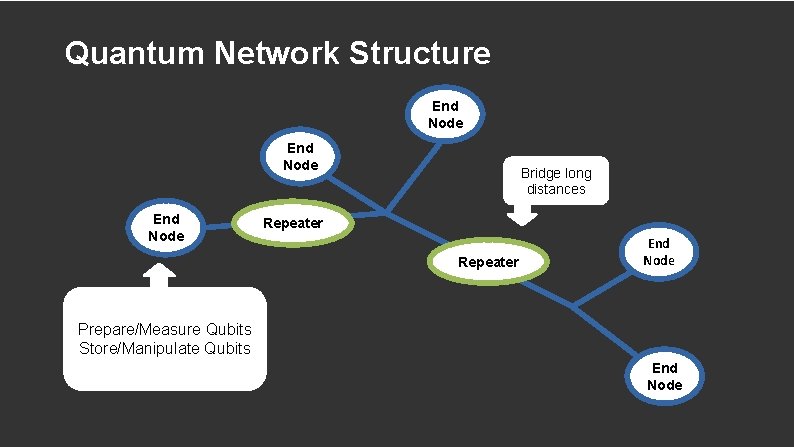
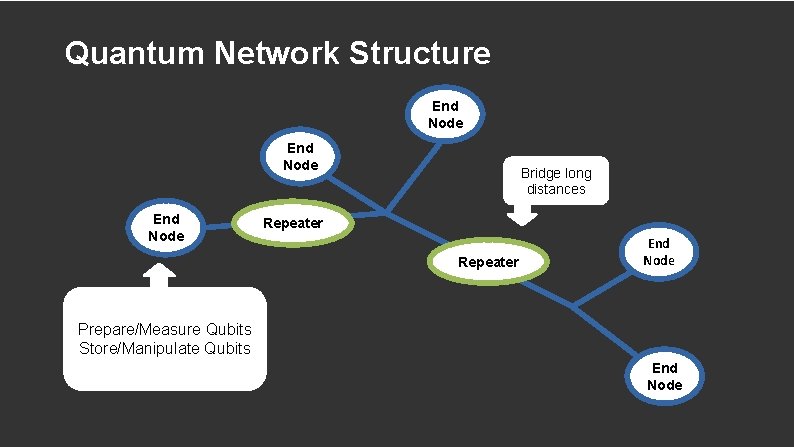
Quantum Network Structure End Node Bridge long distances Repeater End Node Prepare/Measure Qubits Store/Manipulate Qubits End Node
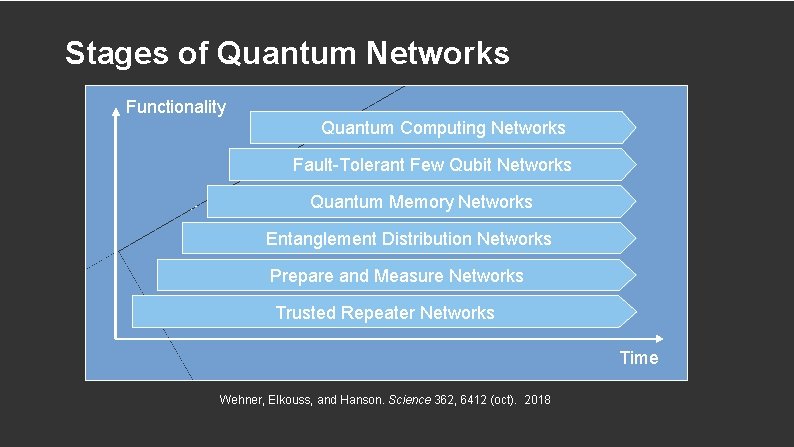
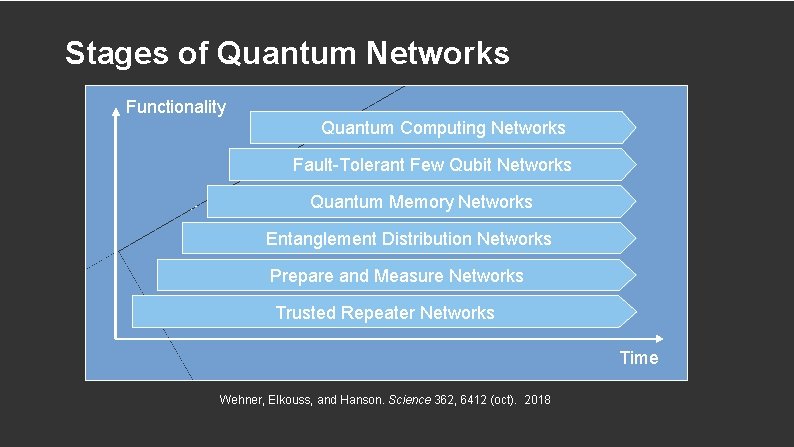
Stages of Quantum Networks Functionality Quantum Computing Networks ● ● Cryptography Fault-Tolerant Few Qubit Networks Sensing and Metrology Distributed Systems Quantum Memory Networks Secure Quantum Cloud Computing Entanglement Distribution Networks Prepare and Measure Networks Trusted Repeater Networks Time Wehner, Elkouss, and Hanson. Science 362, 6412 (oct). 2018
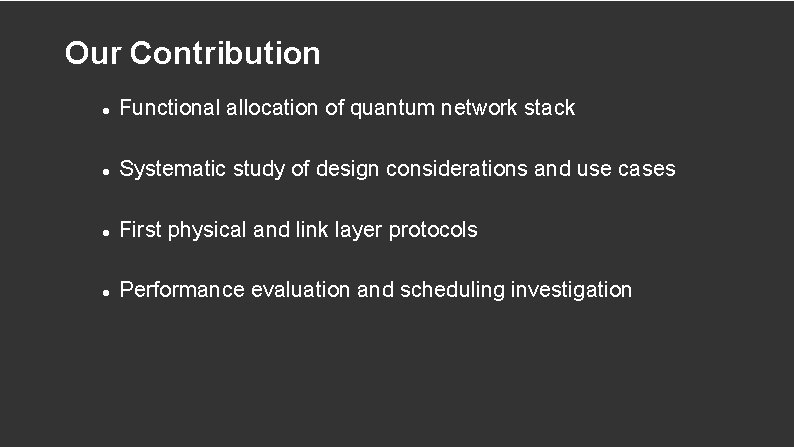
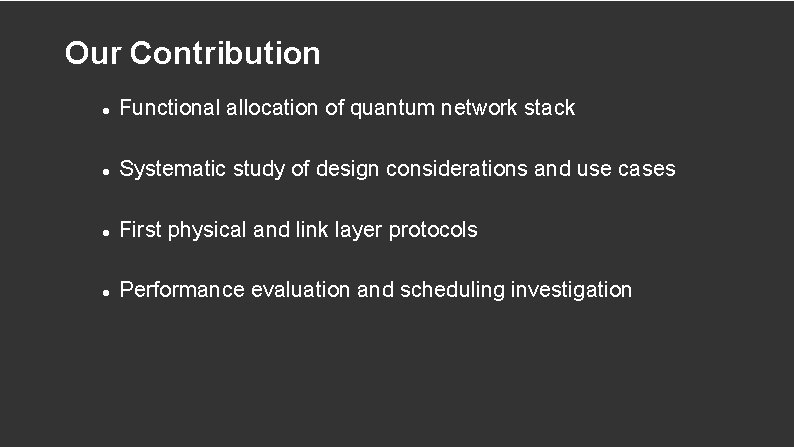
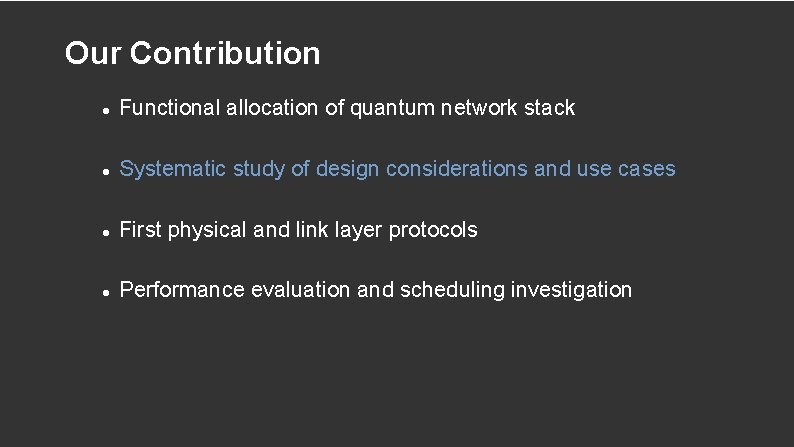
Our Contribution Functional allocation of quantum network stack Systematic study of design considerations and use cases First physical and link layer protocols Performance evaluation and scheduling investigation
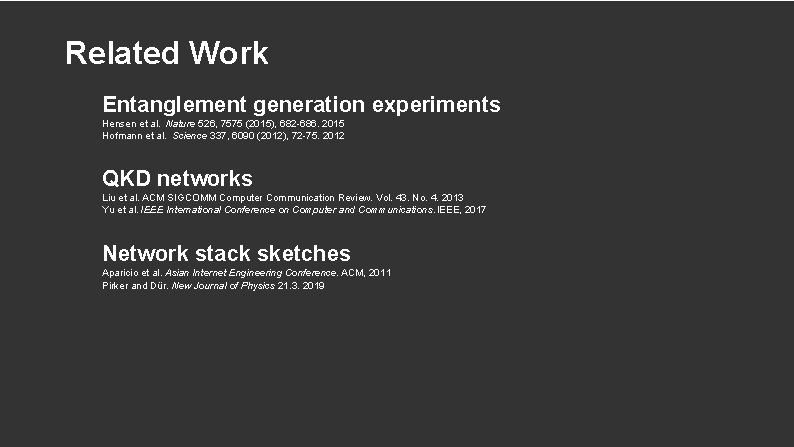
Related Work Entanglement generation experiments Hensen et al. Nature 526, 7575 (2015), 682 -686. 2015 Hofmann et al. Science 337, 6090 (2012), 72 -75. 2012 QKD networks Liu et al. ACM SIGCOMM Computer Communication Review. Vol. 43. No. 4. 2013 Yu et al. IEEE International Conference on Computer and Communications. IEEE, 2017 Network stack sketches Aparicio et al. Asian Internet Engineering Conference. ACM, 2011 Pirker and Dür. New Journal of Physics 21. 3. 2019
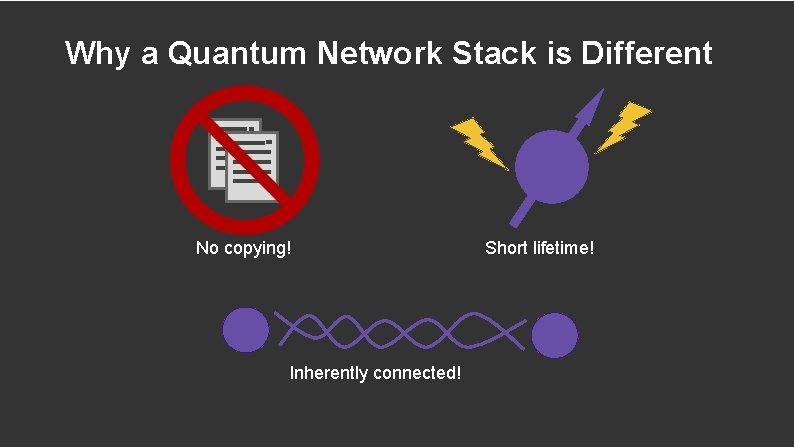
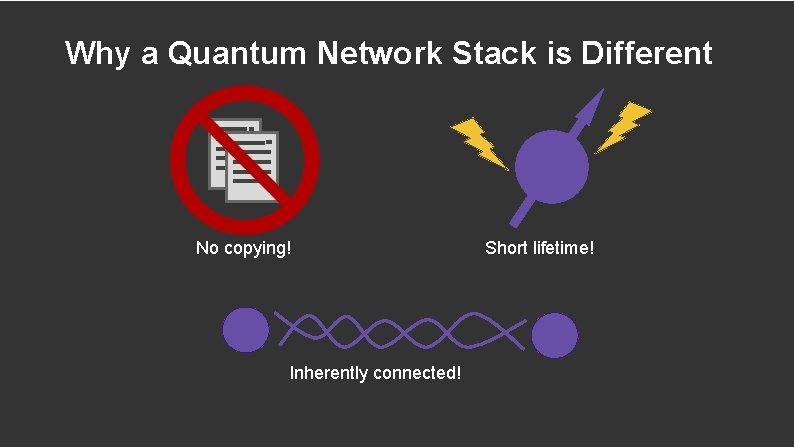
Why a Quantum Network Stack is Different No copying! Inherently connected! Short lifetime!
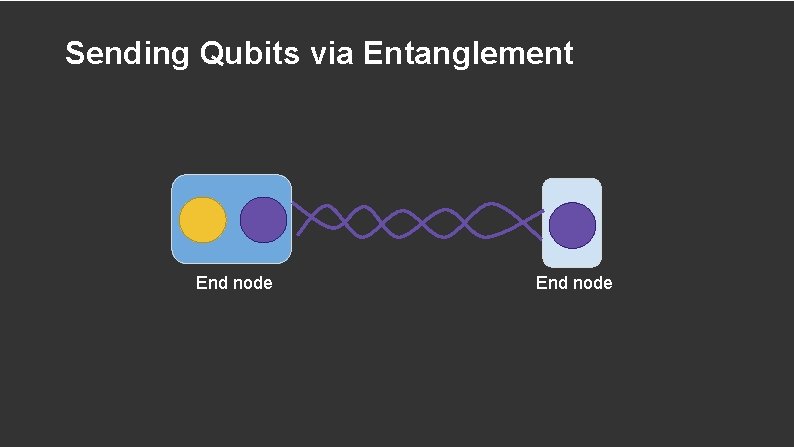
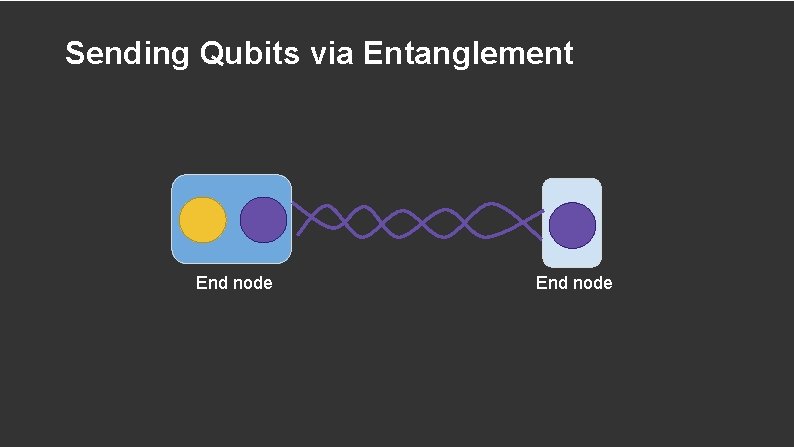
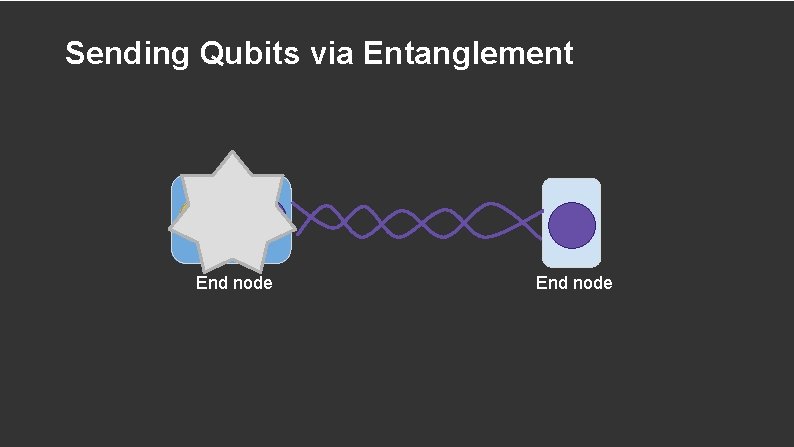
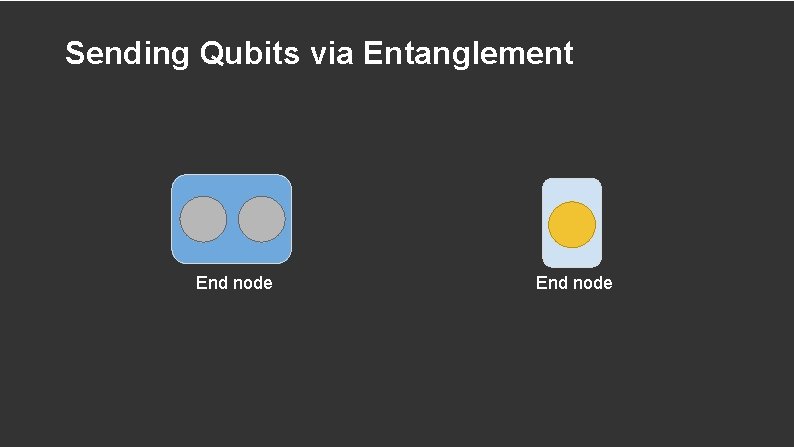
Sending Qubits via Entanglement End node
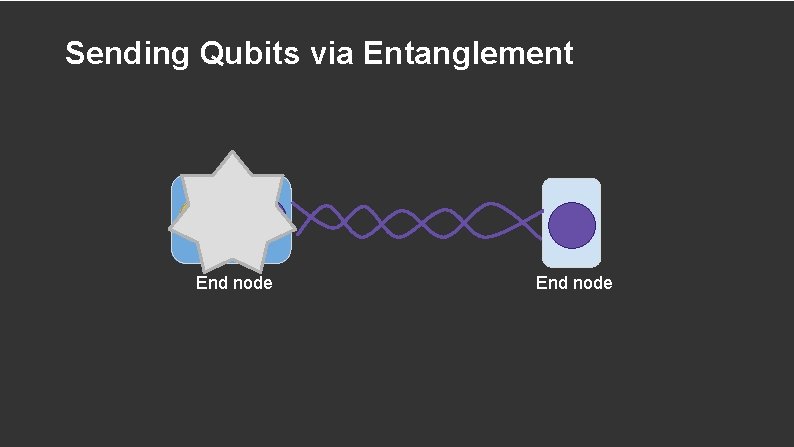
Sending Qubits via Entanglement End node
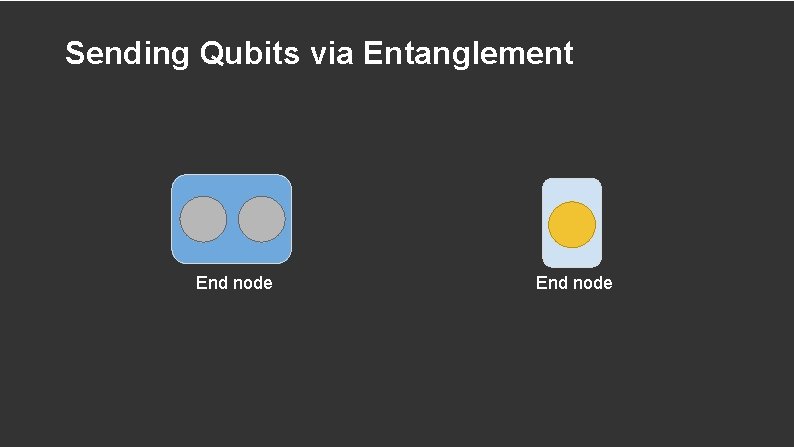
Sending Qubits via Entanglement End node
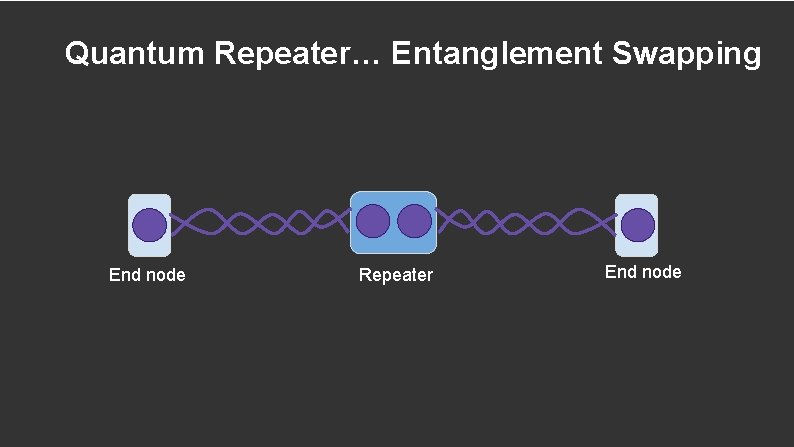
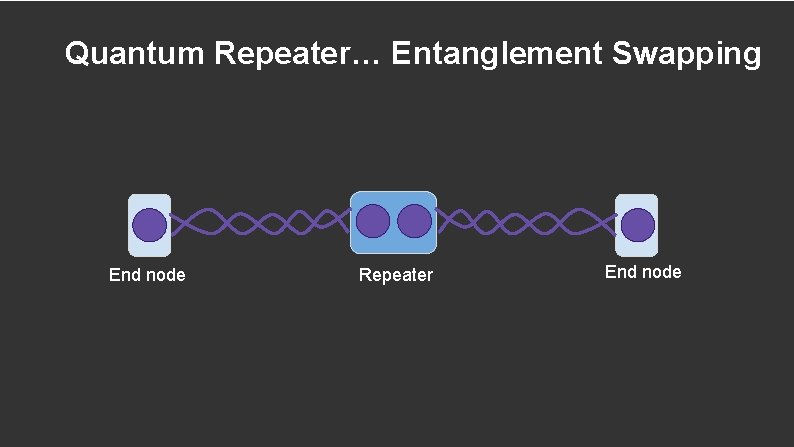
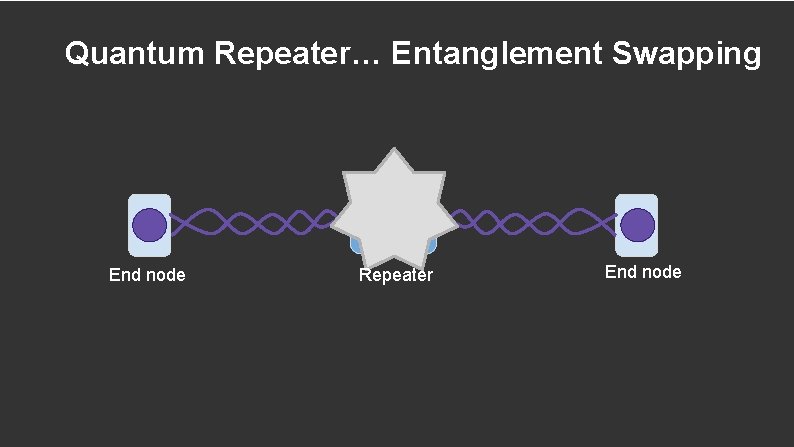
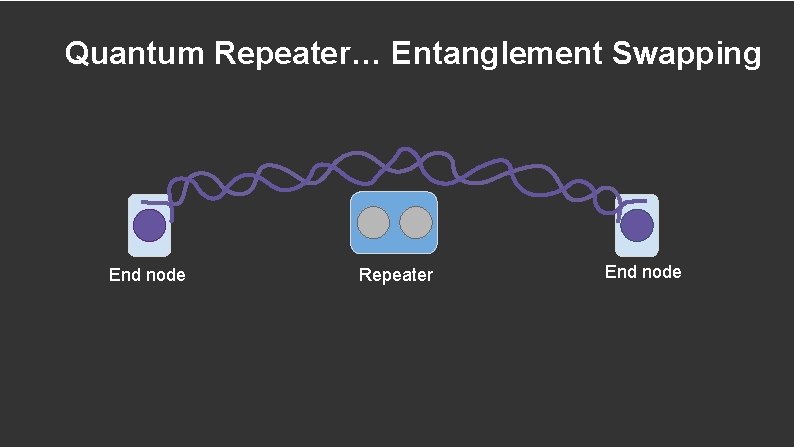
Quantum Repeater… Entanglement Swapping End node Repeater End node
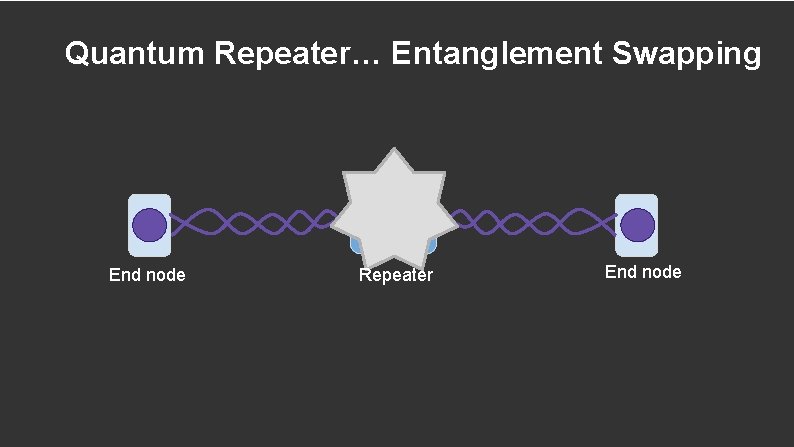
Quantum Repeater… Entanglement Swapping End node Repeater End node
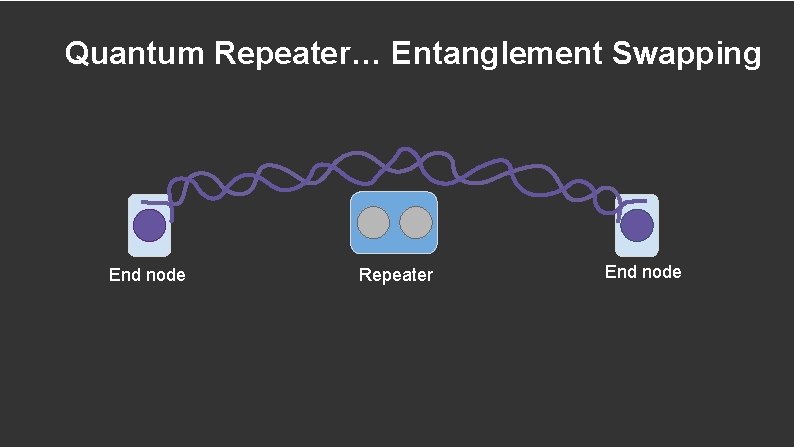
Quantum Repeater… Entanglement Swapping End node Repeater End node
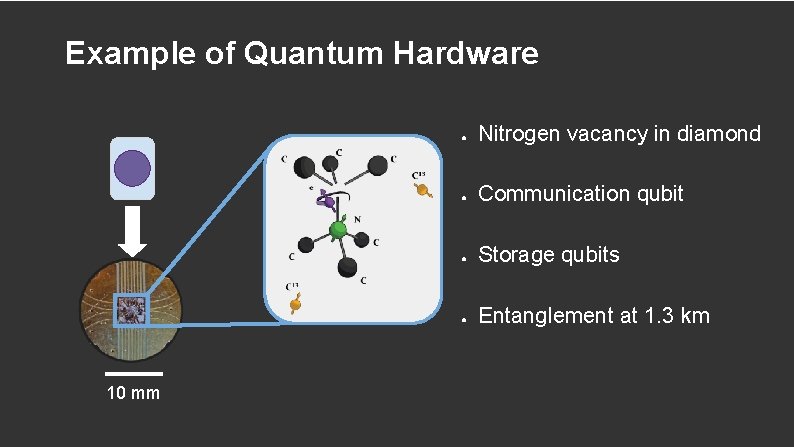
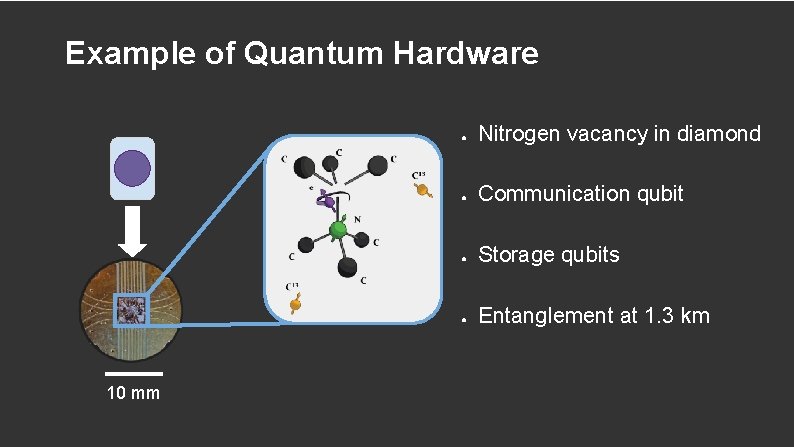
Example of Quantum Hardware 10 mm ● Nitrogen vacancy in diamond ● Communication qubit ● Storage qubits ● Entanglement at 1. 3 km
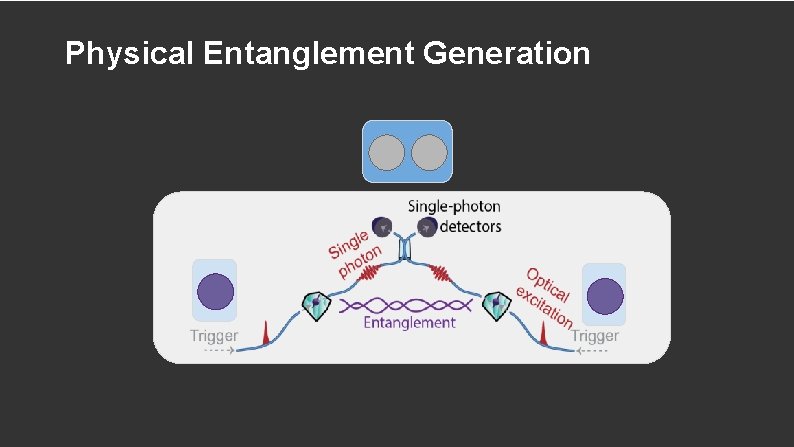
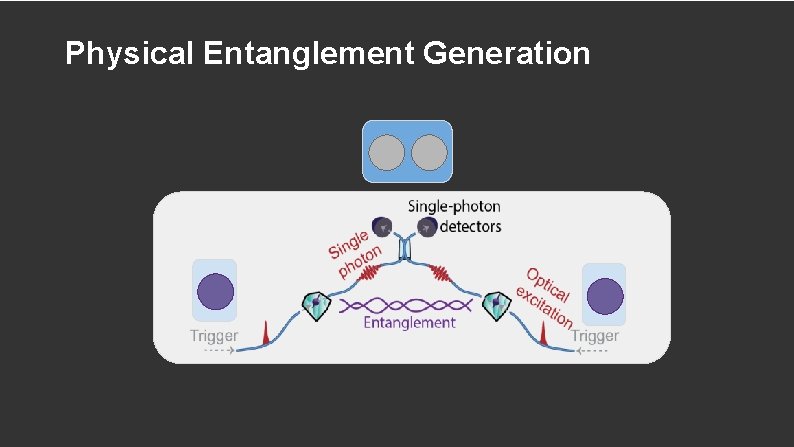
Physical Entanglement Generation
How Entanglement is Produced
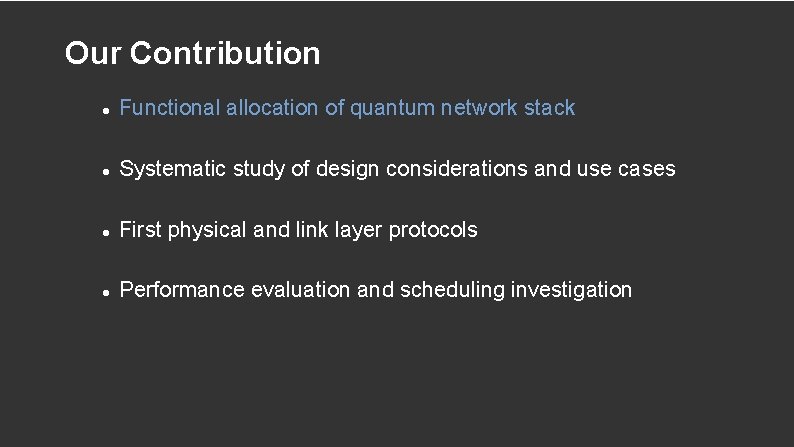
Our Contribution Functional allocation of quantum network stack Systematic study of design considerations and use cases First physical and link layer protocols Performance evaluation and scheduling investigation
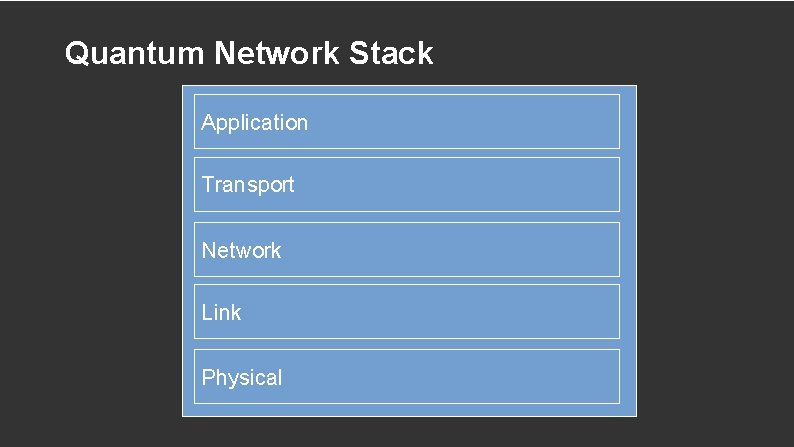
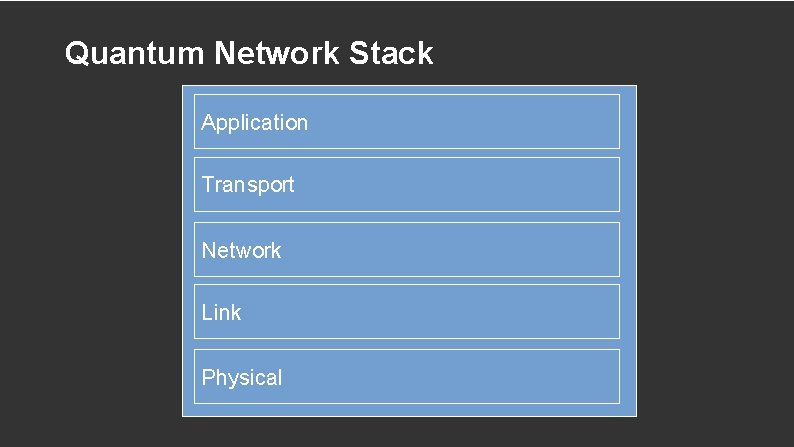
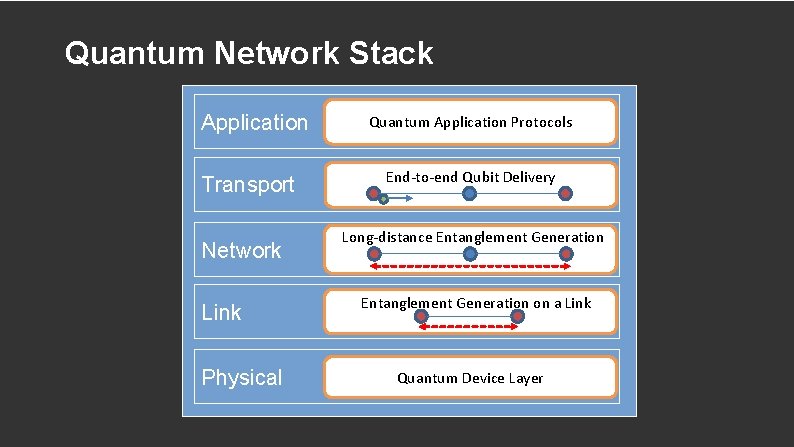
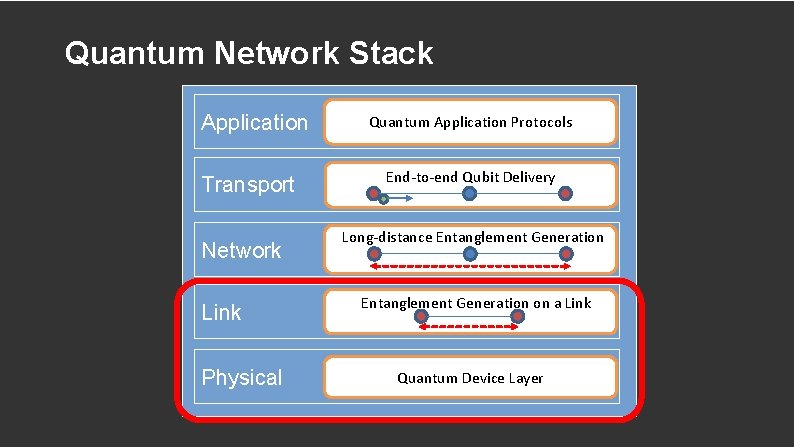
Quantum Network Stack Application Transport Network Link Physical
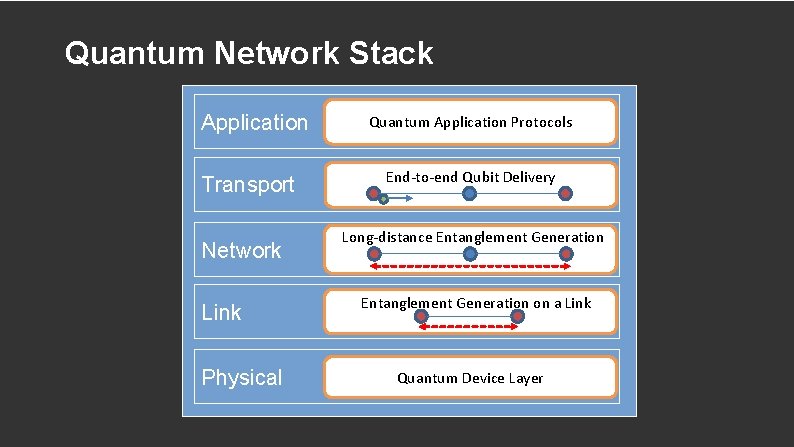
Quantum Network Stack Application Transport Network Link Physical Quantum Application Protocols End-to-end Qubit Delivery Long-distance Entanglement Generation on a Link Quantum Device Layer
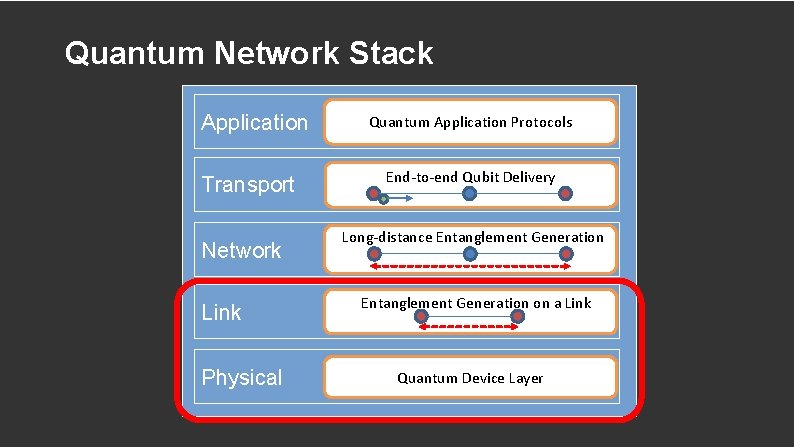
Quantum Network Stack Application Transport Network Link Physical Quantum Application Protocols End-to-end Qubit Delivery Long-distance Entanglement Generation on a Link Quantum Device Layer
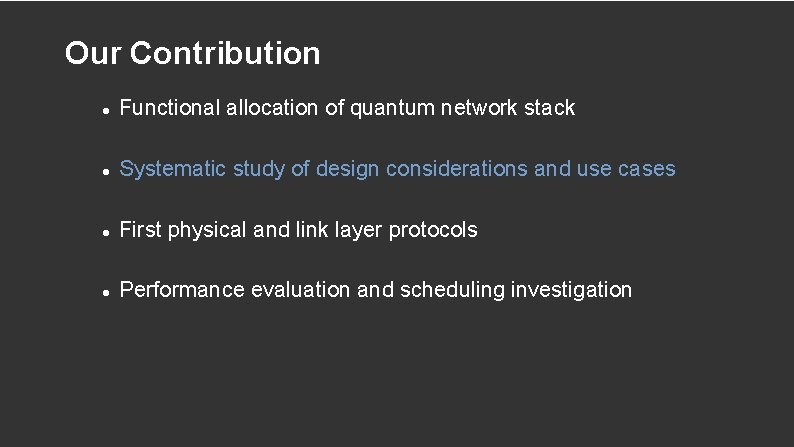
Our Contribution Functional allocation of quantum network stack Systematic study of design considerations and use cases First physical and link layer protocols Performance evaluation and scheduling investigation
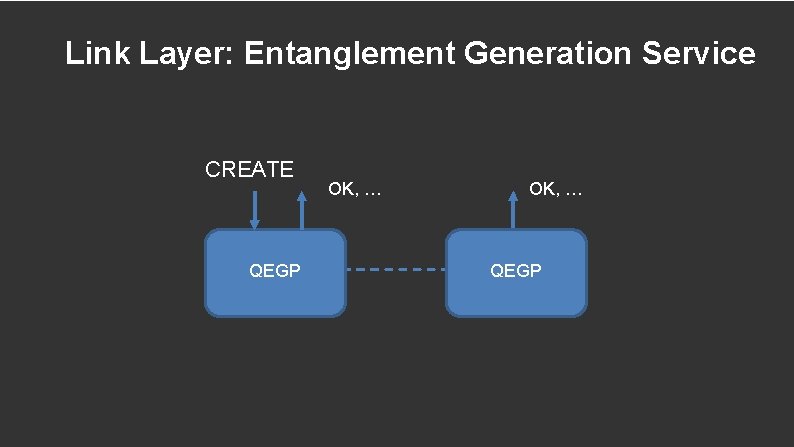
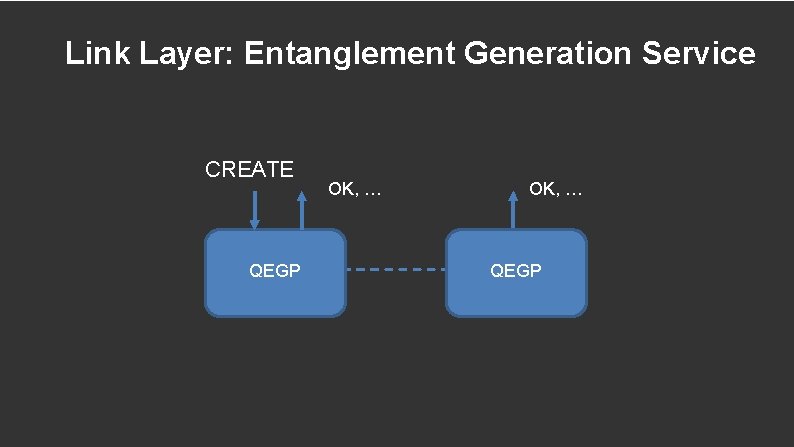
Link Layer: Entanglement Generation Service CREATE QEGP OK, … QEGP
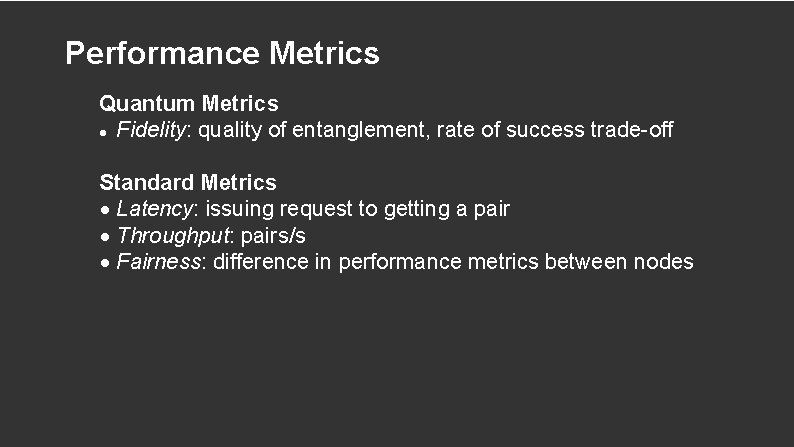
Performance Metrics Quantum Metrics Fidelity: quality of entanglement, rate of success trade-off Standard Metrics Latency: issuing request to getting a pair Throughput: pairs/s Fairness: difference in performance metrics between nodes
Use Cases Application Use Cases • Measure directly: many pairs measured immediately • Create and keep: few pair(s) stored for processing Network Layer Use Case • Create and keep: entanglement swapping with two pairs
Design Considerations Noise due to attempts • Producing entanglement induces noise on storage qubits (Kalb et al, Phys. Rev. A, 97. 2018) • Avoid triggering unless both nodes agree Noise is time dependent • Avoid waiting once entanglement made • Prior discussion preferred Quantum CRC for error detection difficult • Applications do not require perfect entanglement • Reduce complexity
Our Contribution Functional allocation of quantum network stack Systematic study of design considerations and use cases First physical and link layer protocols Performance evaluation and scheduling investigation
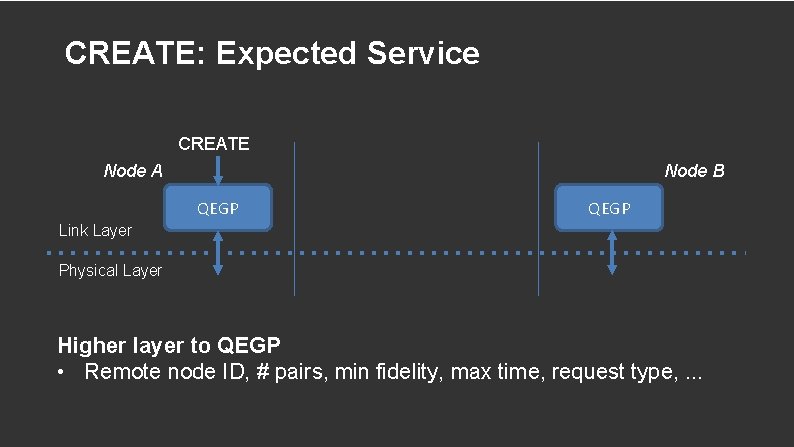
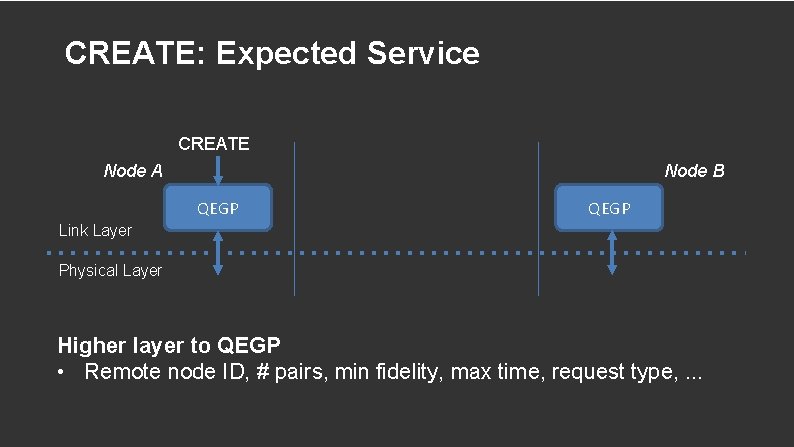
CREATE: Expected Service CREATE Node A Node B QEGP Link Layer Physical Layer Higher layer to QEGP • Remote node ID, # pairs, min fidelity, max time, request type, . . .
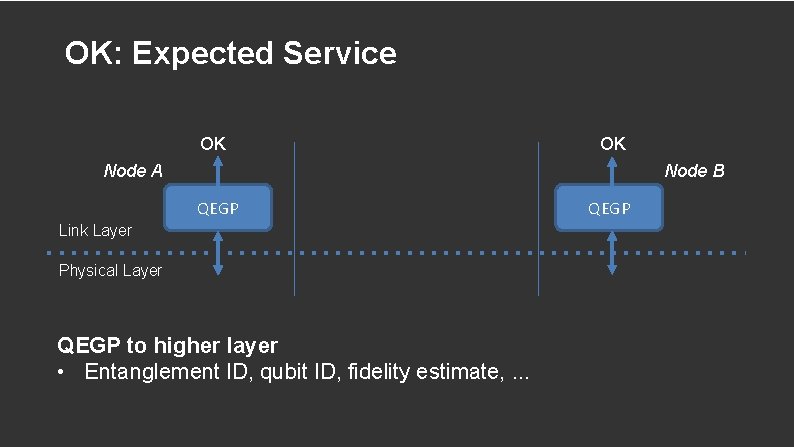
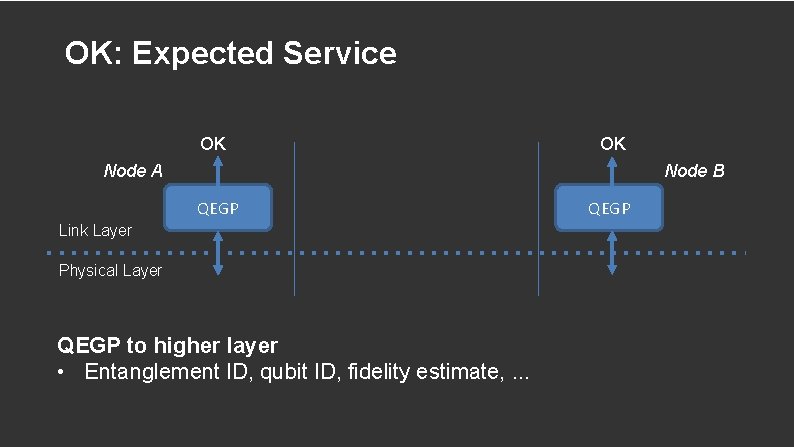
OK: Expected Service OK OK Node B Node A QEGP Link Layer Physical Layer QEGP to higher layer • Entanglement ID, qubit ID, fidelity estimate, . . . QEGP
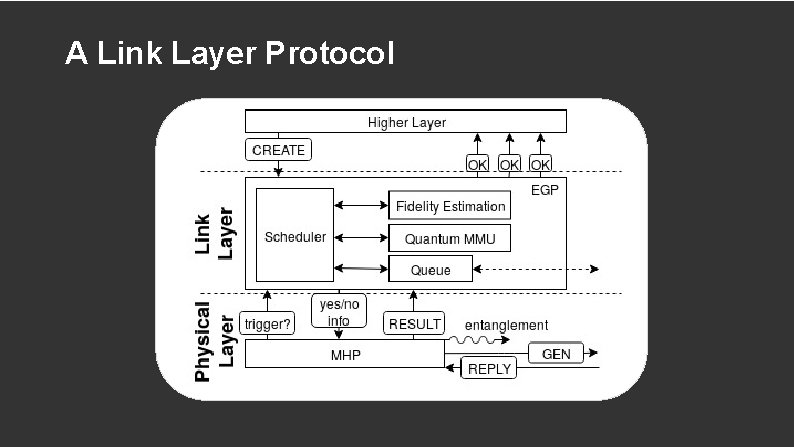
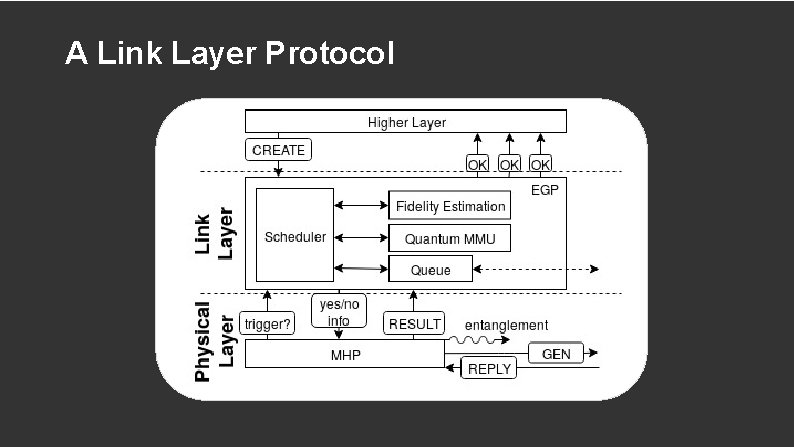
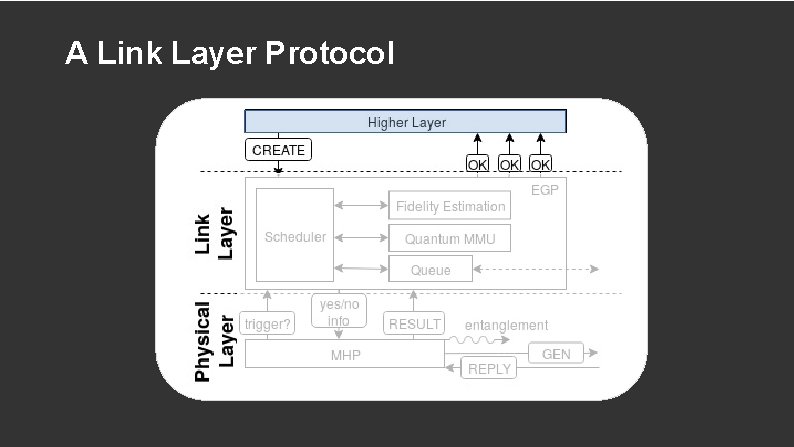
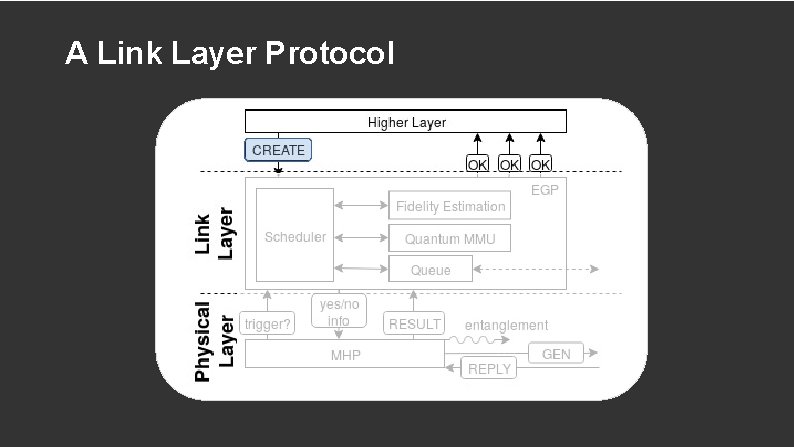
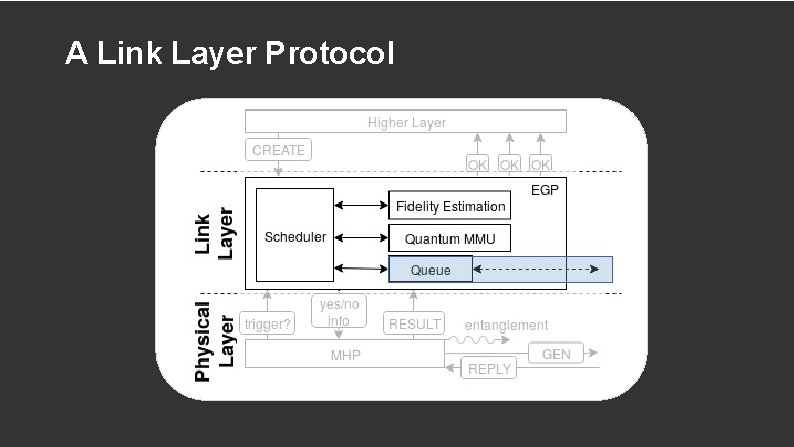
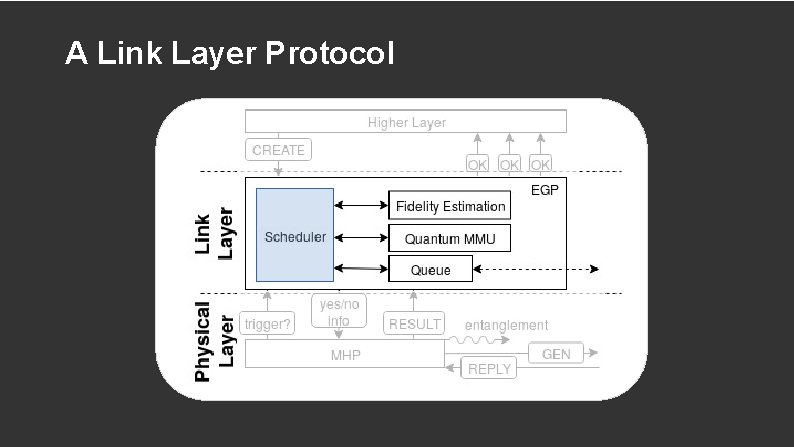
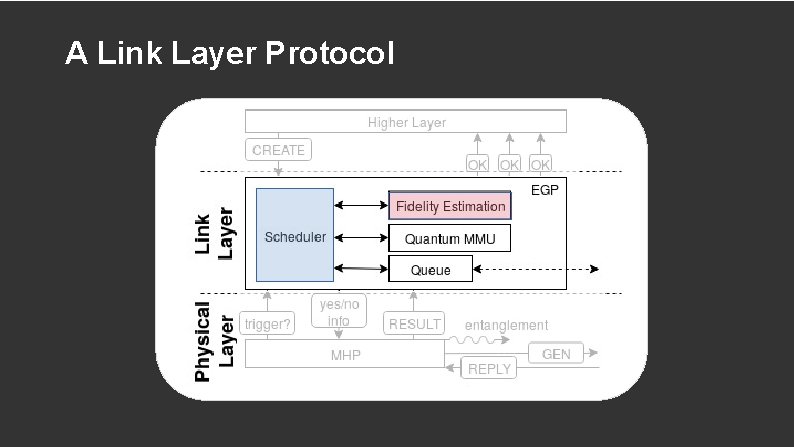
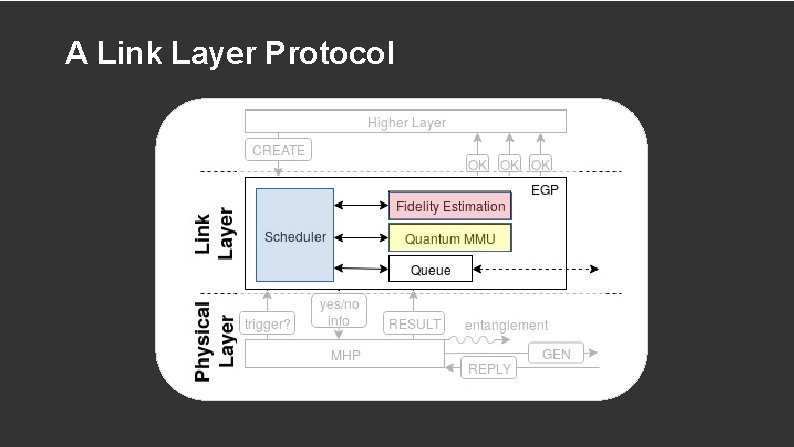
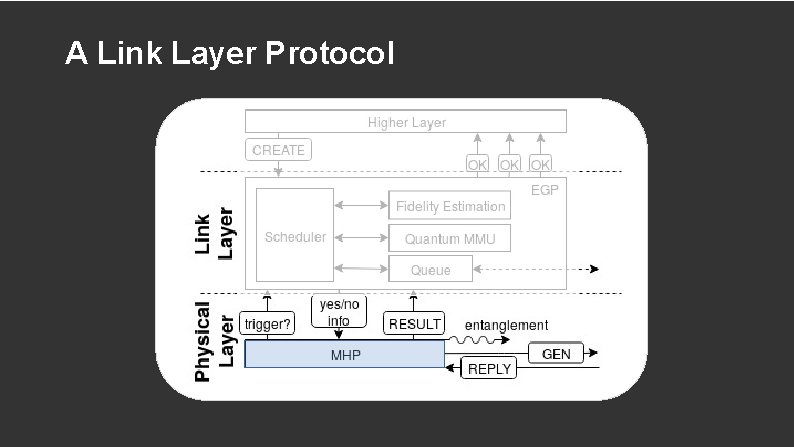
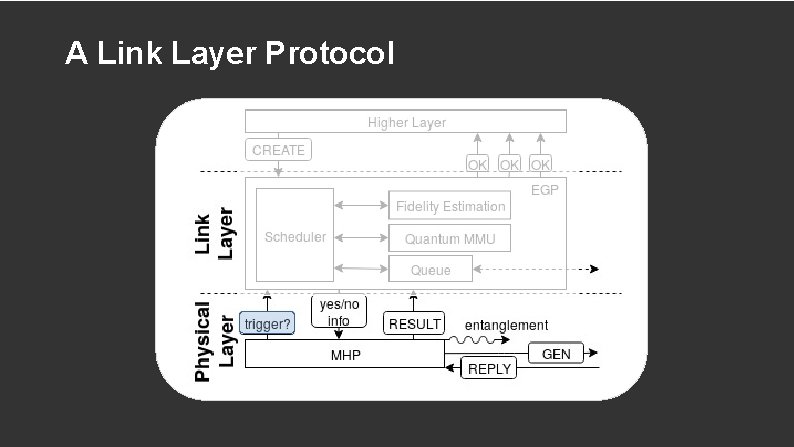
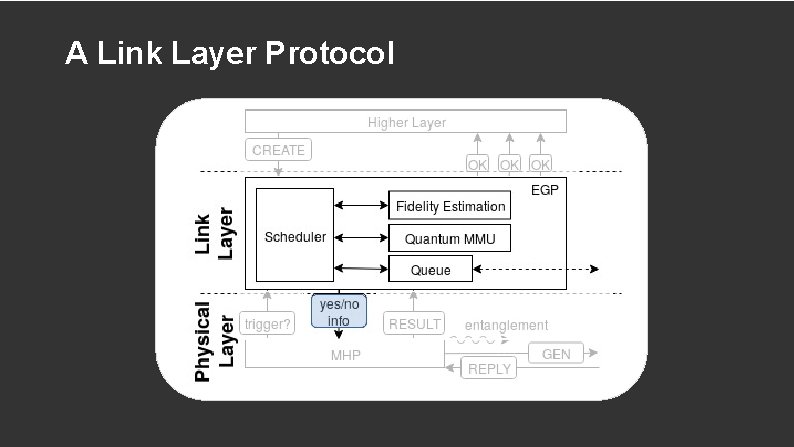
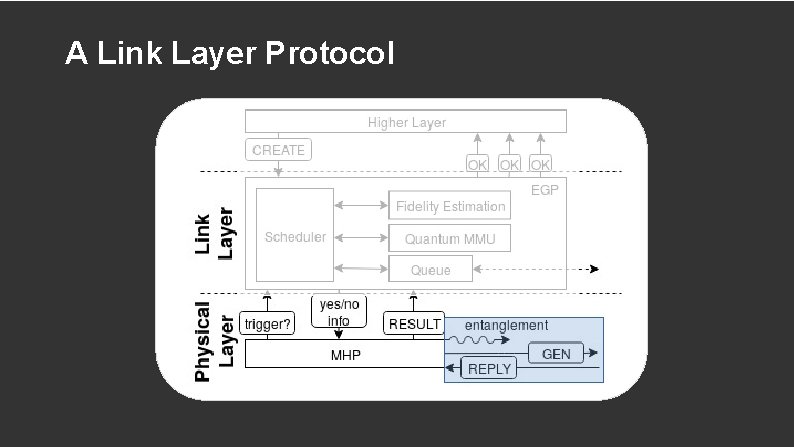
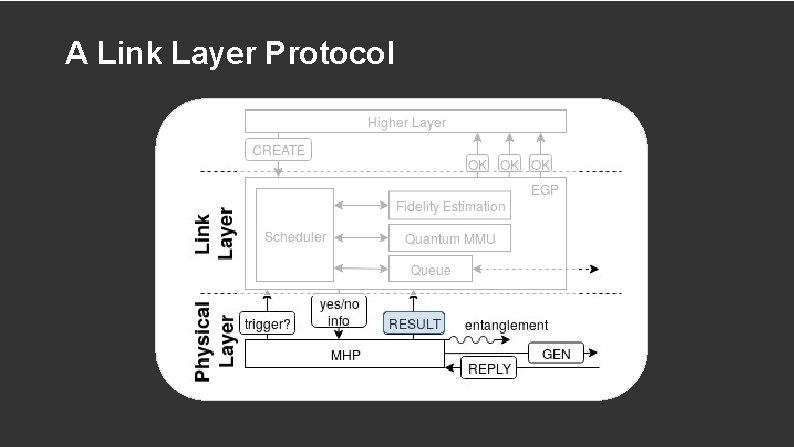
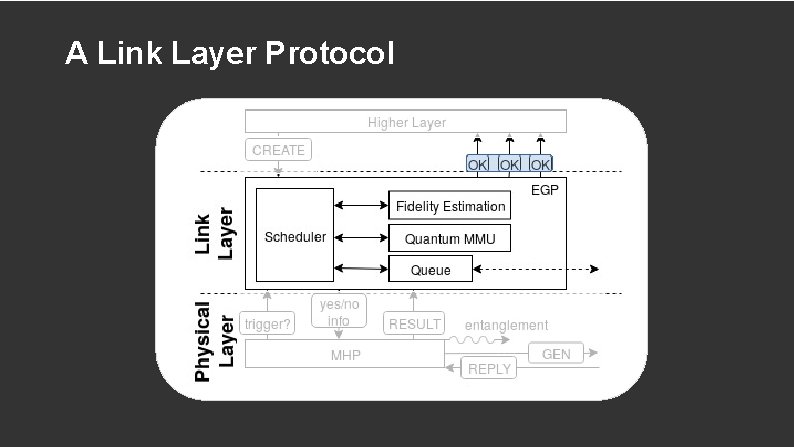
A Link Layer Protocol
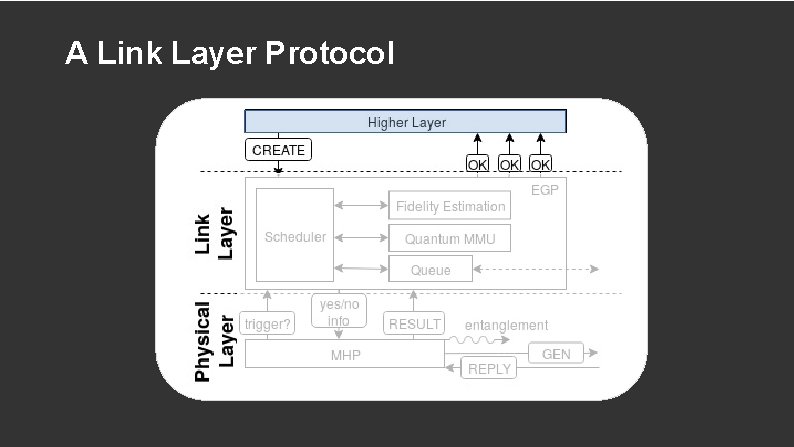
A Link Layer Protocol
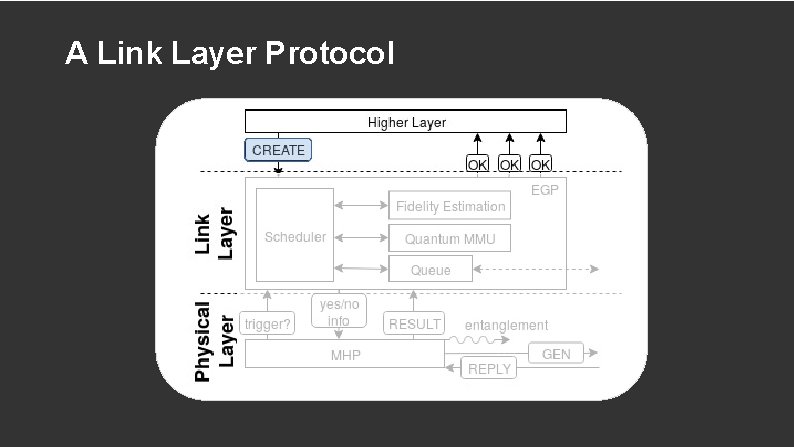
A Link Layer Protocol
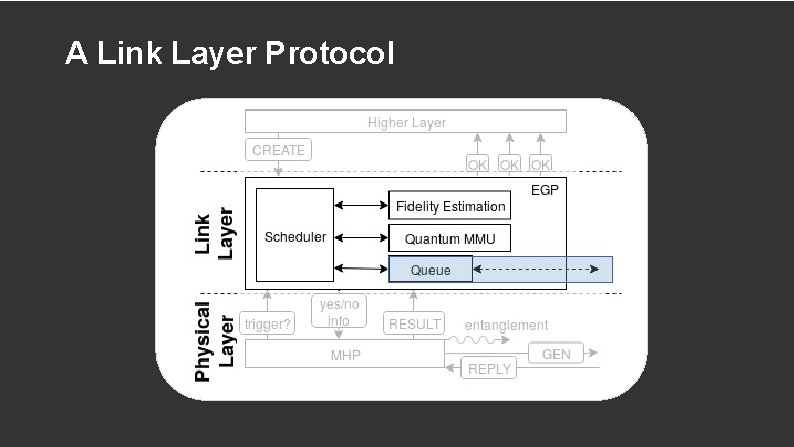
A Link Layer Protocol
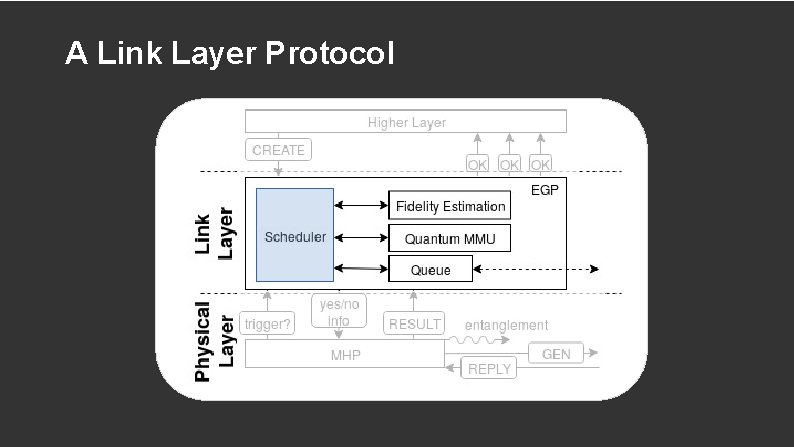
A Link Layer Protocol
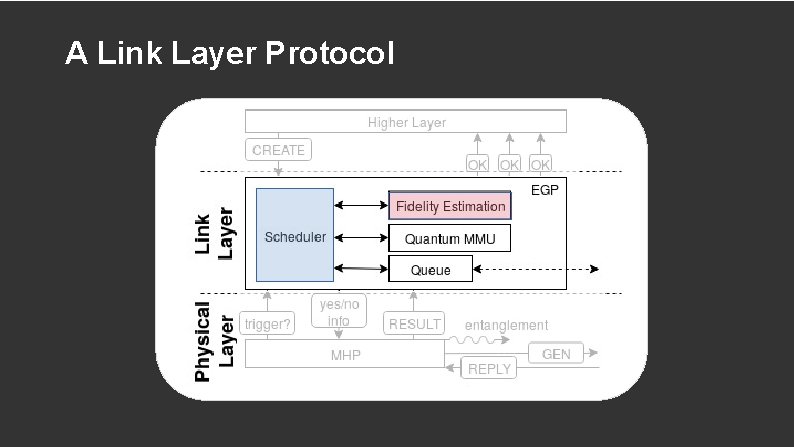
A Link Layer Protocol
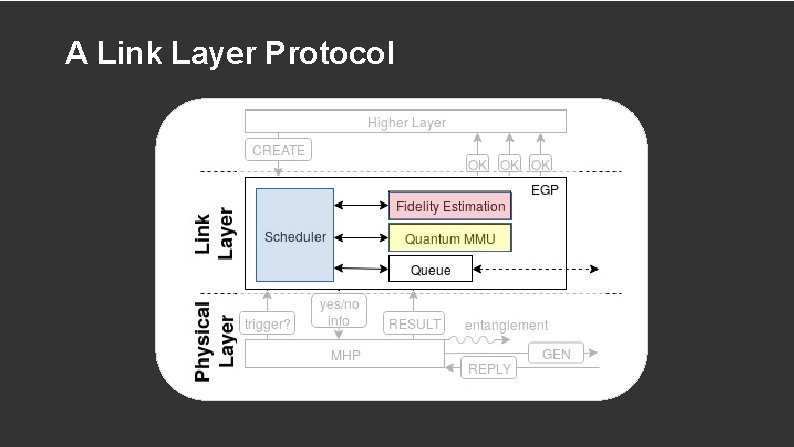
A Link Layer Protocol
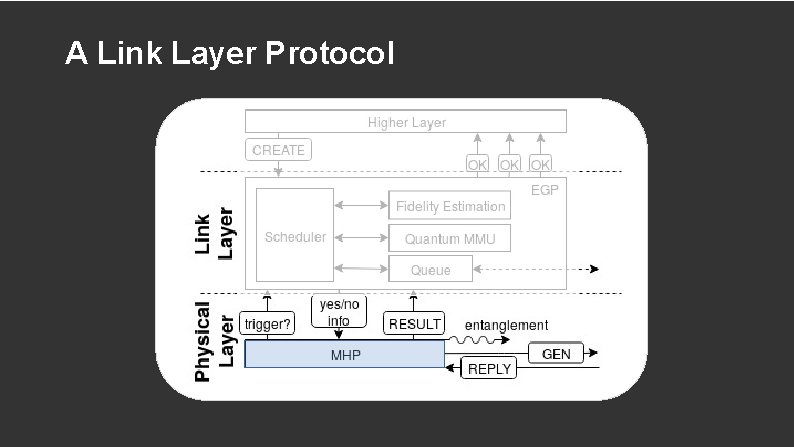
A Link Layer Protocol
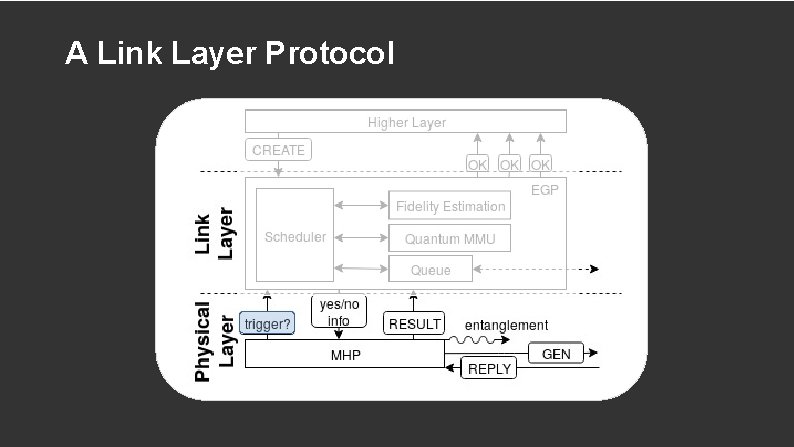
A Link Layer Protocol
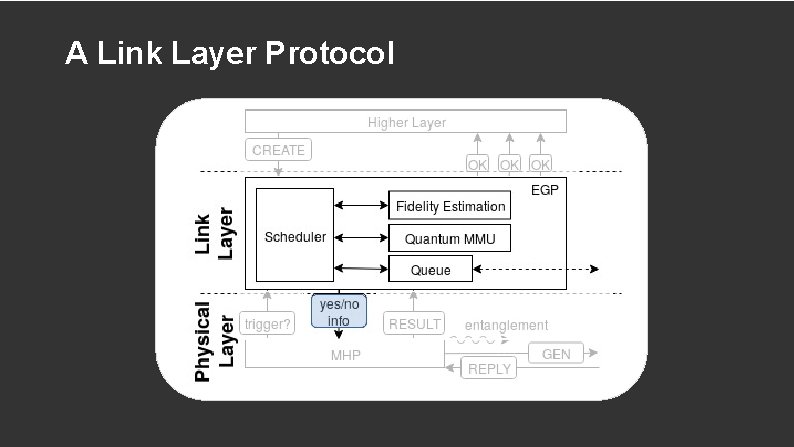
A Link Layer Protocol
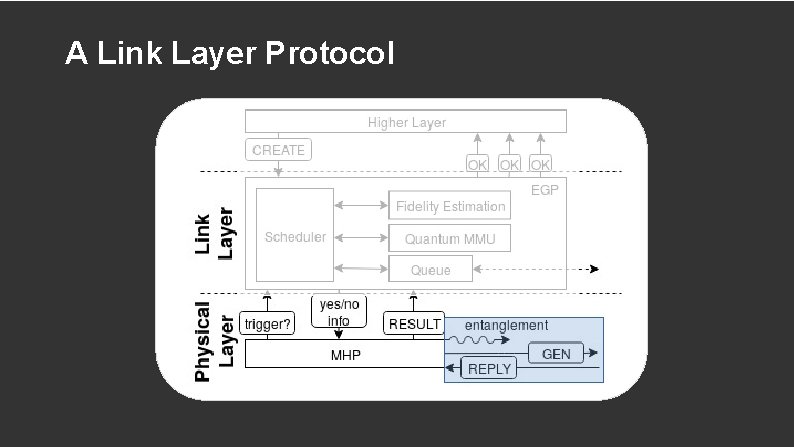
A Link Layer Protocol
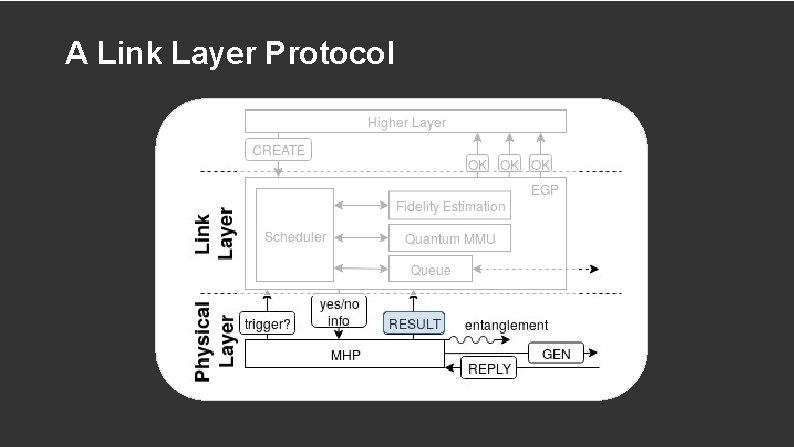
A Link Layer Protocol
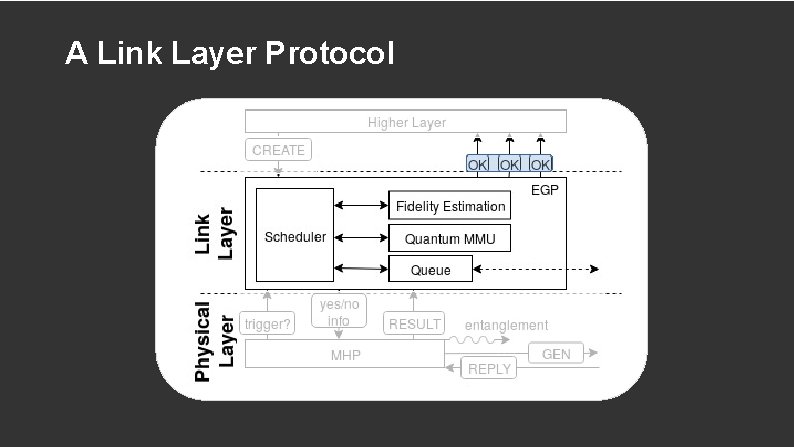
A Link Layer Protocol
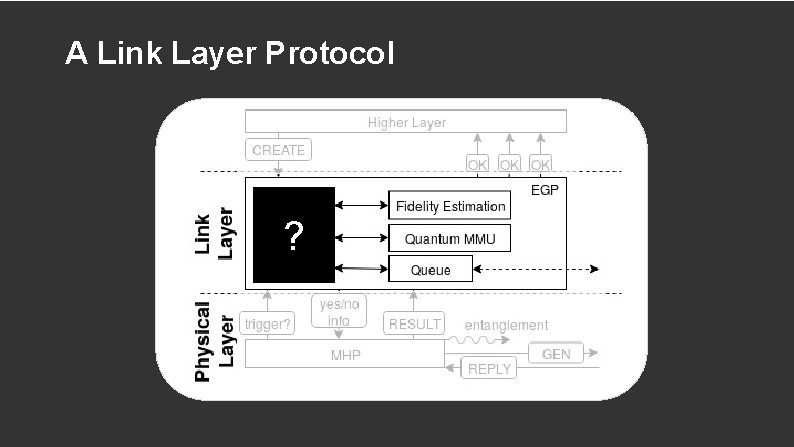
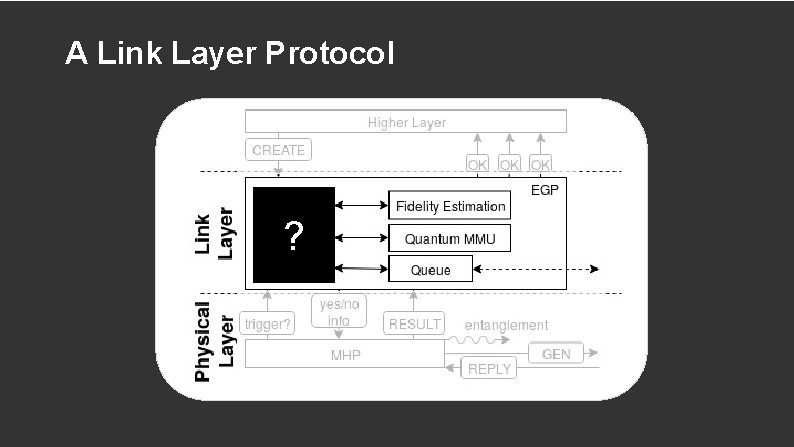
A Link Layer Protocol ?
How to Prioritize CREATE Requests Requires context and information Simple version: first come first serve More interesting: cater to different use cases
Our Contribution Functional allocation of quantum network stack Systematic study of design considerations and use cases First physical and link layer protocols Performance evaluation and scheduling investigation
Simulation Tool: Net. SQUID Discrete event simulator Model and validate simulated quantum hardware Model physical components e. g. fibers, nodes, and midpoint
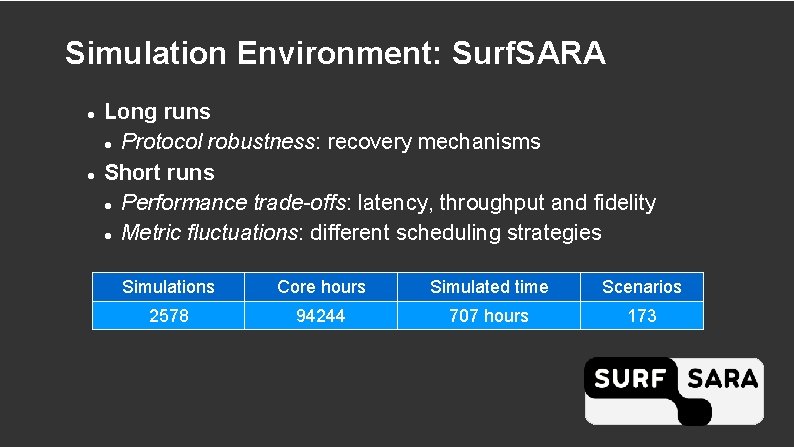
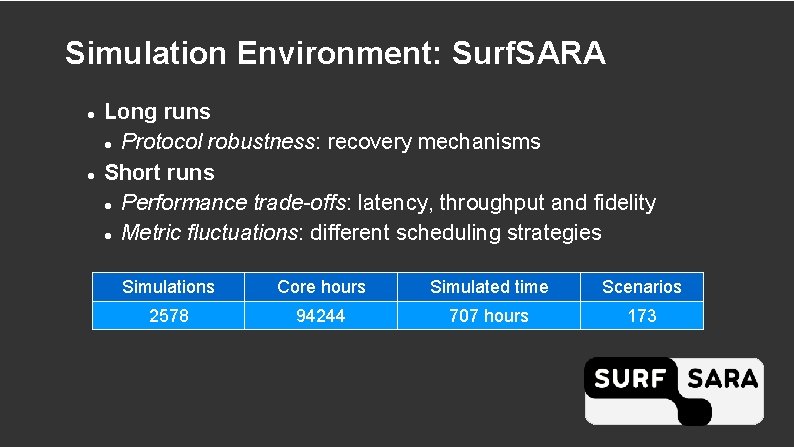
Simulation Environment: Surf. SARA Long runs Protocol robustness: recovery mechanisms Short runs Performance trade-offs: latency, throughput and fidelity Metric fluctuations: different scheduling strategies Simulations Core hours Simulated time Scenarios 2578 94244 707 hours 173
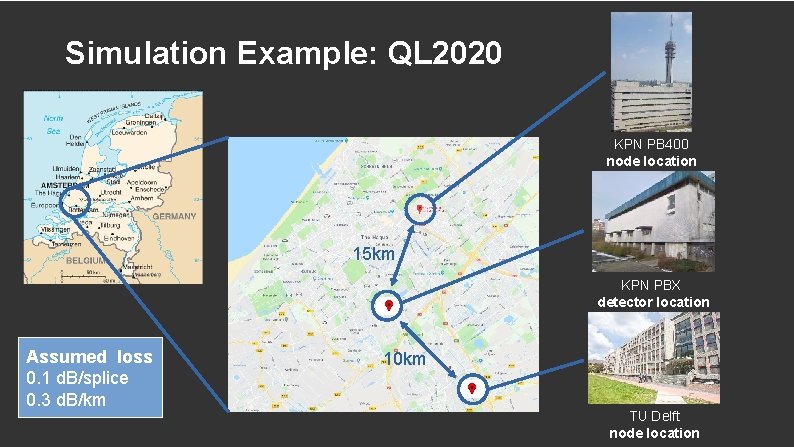
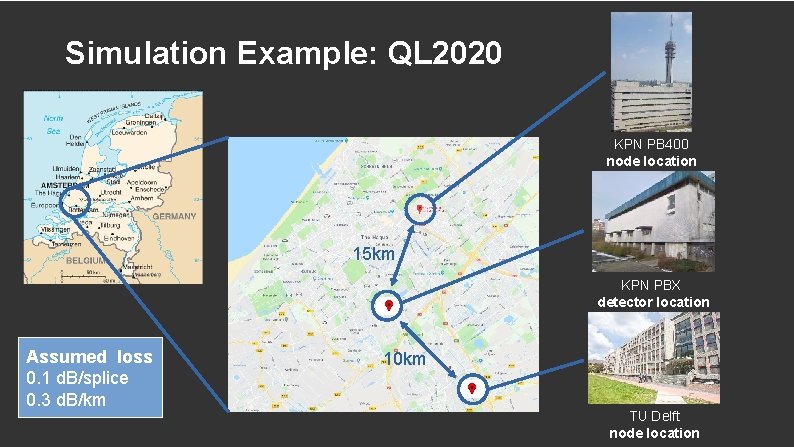
Simulation Example: QL 2020 KPN PB 400 node location 15 km KPN PBX detector location Assumed loss 0. 1 d. B/splice 0. 3 d. B/km 10 km TU Delft node location
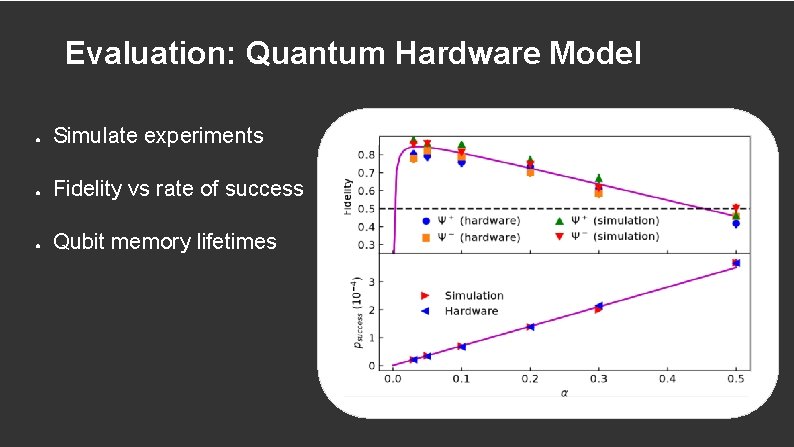
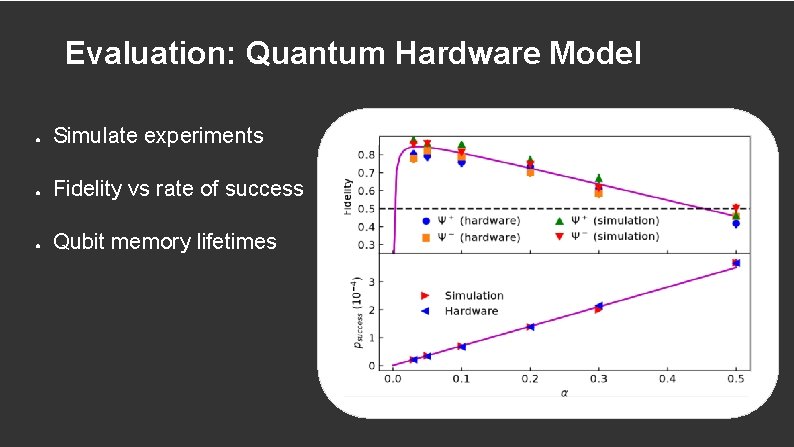
Evaluation: Quantum Hardware Model ● Simulate experiments ● Fidelity vs rate of success ● Qubit memory lifetimes
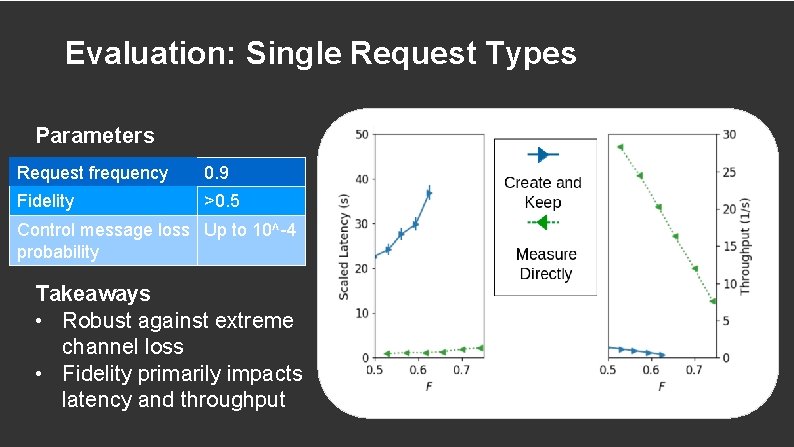
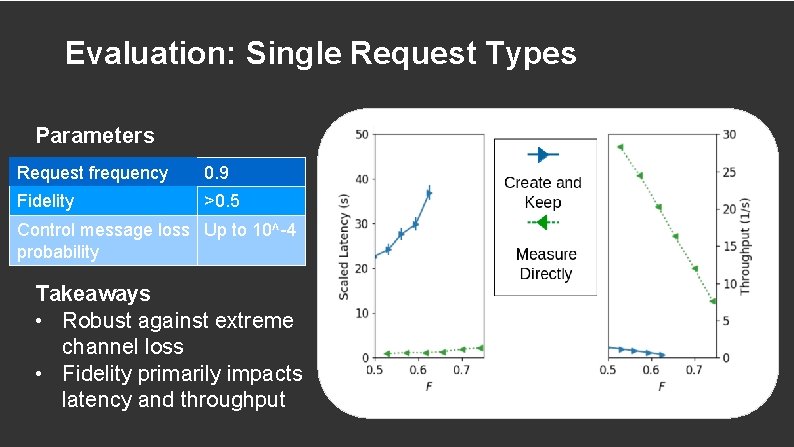
Evaluation: Single Request Types Parameters Request frequency 0. 9 Fidelity >0. 5 Control message loss Up to 10^-4 probability Takeaways • Robust against extreme channel loss • Fidelity primarily impacts latency and throughput
Some Takeaways Protocol robust Fidelity versus throughput and latency Mixed request simulations Scheduling versus performance metrics
Our Contribution Functional allocation of quantum network stack Systematic study of design considerations and use cases First physical and link layer protocols Performance evaluation and scheduling investigation
Future Work Hardware realization of Link Layer (ongoing) Network Layer Protocol Other (smarter) scheduling strategies Combat memory lifetimes Consider role of node in network
Thank you