RoleBased Access Control Prof Ravi Sandhu George Mason

Role-Based Access Control Prof. Ravi Sandhu George Mason University and NSD Security SACMAT 2003
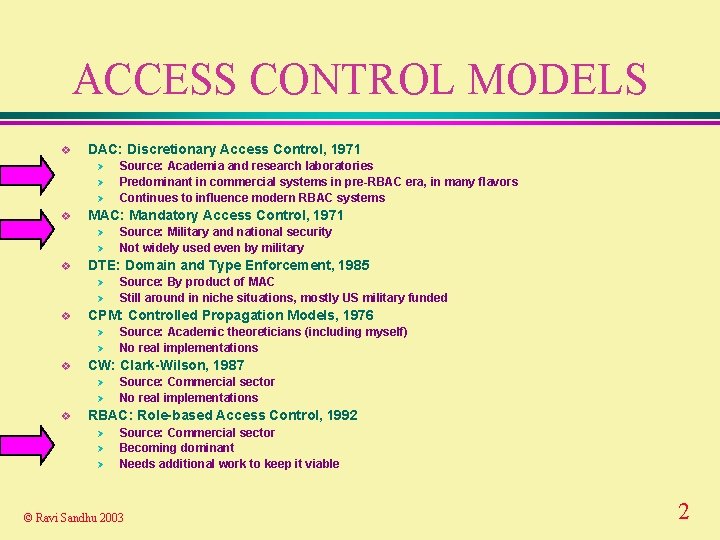
ACCESS CONTROL MODELS v DAC: Discretionary Access Control, 1971 Ø Ø Ø v MAC: Mandatory Access Control, 1971 Ø Ø v Ø Ø Source: Academic theoreticians (including myself) No real implementations CW: Clark-Wilson, 1987 Ø Ø v Source: By product of MAC Still around in niche situations, mostly US military funded CPM: Controlled Propagation Models, 1976 Ø v Source: Military and national security Not widely used even by military DTE: Domain and Type Enforcement, 1985 Ø v Source: Academia and research laboratories Predominant in commercial systems in pre-RBAC era, in many flavors Continues to influence modern RBAC systems Source: Commercial sector No real implementations RBAC: Role-based Access Control, 1992 Ø Ø Ø Source: Commercial sector Becoming dominant Needs additional work to keep it viable © Ravi Sandhu 2003 2
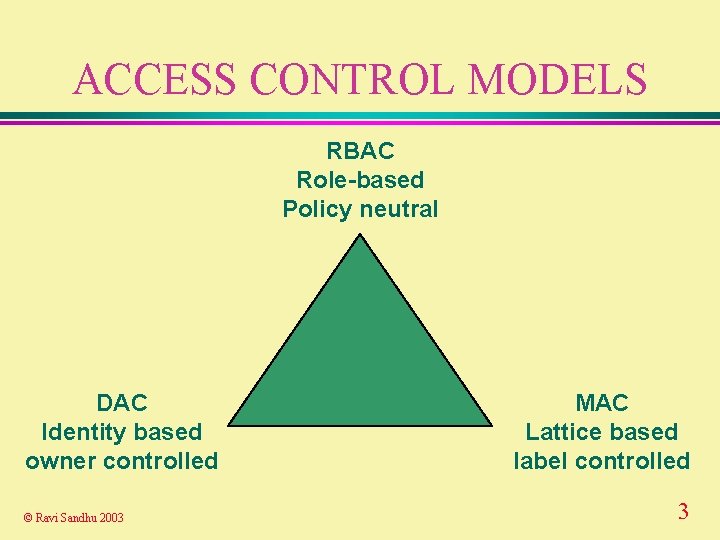
ACCESS CONTROL MODELS RBAC Role-based Policy neutral DAC Identity based owner controlled © Ravi Sandhu 2003 MAC Lattice based label controlled 3
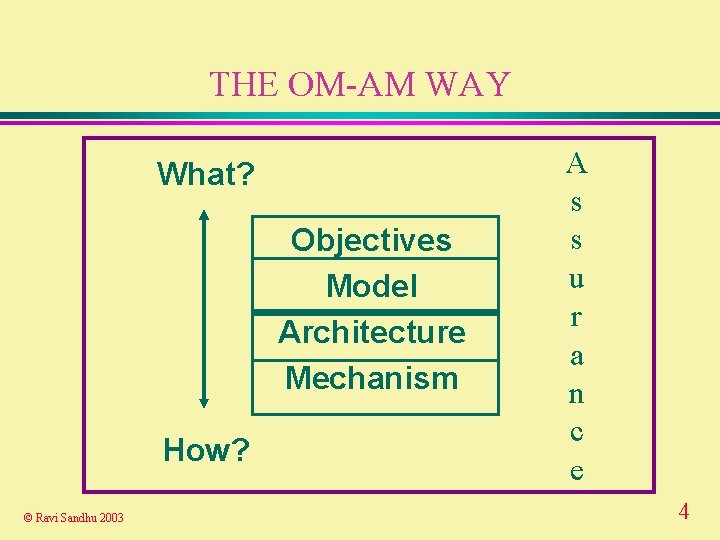
THE OM-AM WAY What? Objectives Model Architecture Mechanism How? © Ravi Sandhu 2003 A s s u r a n c e 4
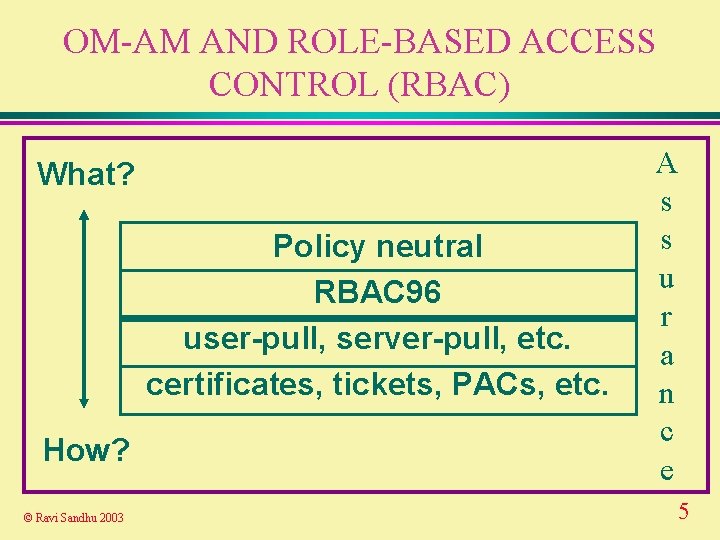
OM-AM AND ROLE-BASED ACCESS CONTROL (RBAC) What? Policy neutral RBAC 96 user-pull, server-pull, etc. certificates, tickets, PACs, etc. How? © Ravi Sandhu 2003 A s s u r a n c e 5
The RBAC 96 Model
ROLE-BASED ACCESS CONTROL (RBAC) v. A user’s permissions are determined by the user’s roles Ø rather than identity or clearance Ø roles can encode arbitrary attributes v multi-faceted v ranges from very simple to very sophisticated © Ravi Sandhu 2003 7
WHAT IS THE POLICY IN RBAC? v RBAC is a framework to help in articulating policy v The main point of RBAC is to facilitate security management © Ravi Sandhu 2003 8
RBAC SECURITY PRINCIPLES v least privilege v separation of duties v separation of administration and access v abstract operations © Ravi Sandhu 2003 9
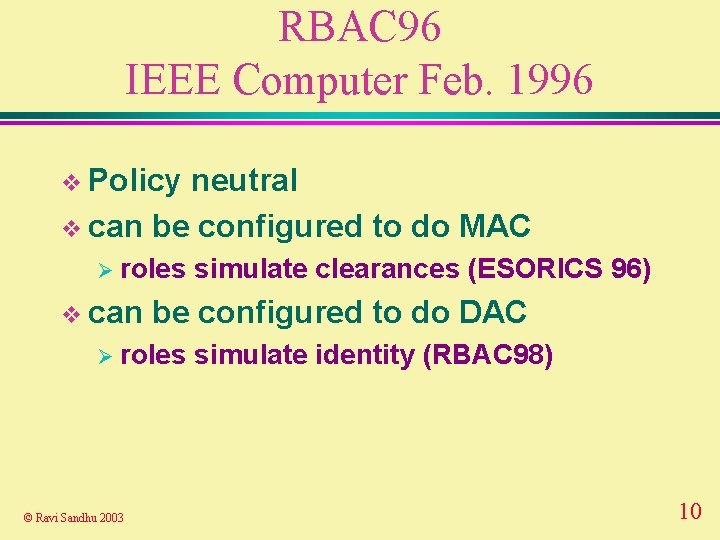
RBAC 96 IEEE Computer Feb. 1996 v Policy neutral v can be configured to do MAC Ø roles v can be configured to do DAC Ø roles © Ravi Sandhu 2003 simulate clearances (ESORICS 96) simulate identity (RBAC 98) 10
WHAT IS RBAC? v multidimensional v open ended v ranges from simple to sophisticated © Ravi Sandhu 2003 11
RBAC CONUNDRUM v turn on all roles all the time v turn on one role only at a time v turn on a user-specified subset of roles © Ravi Sandhu 2003 12
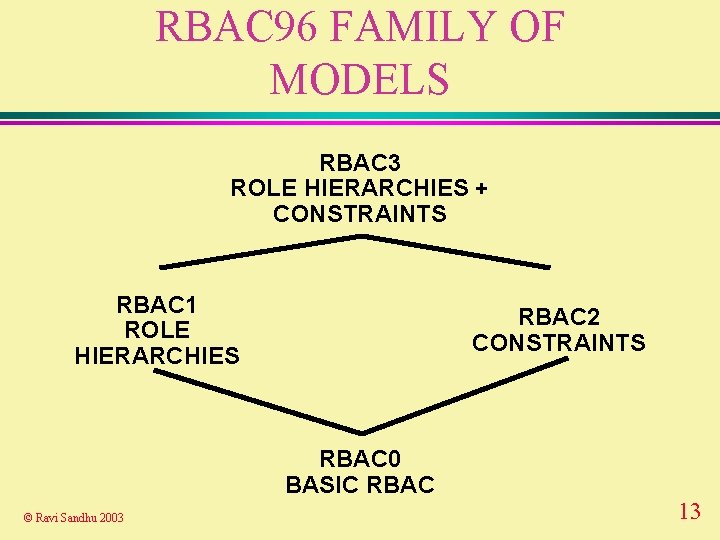
RBAC 96 FAMILY OF MODELS RBAC 3 ROLE HIERARCHIES + CONSTRAINTS RBAC 1 ROLE HIERARCHIES RBAC 2 CONSTRAINTS RBAC 0 BASIC RBAC © Ravi Sandhu 2003 13
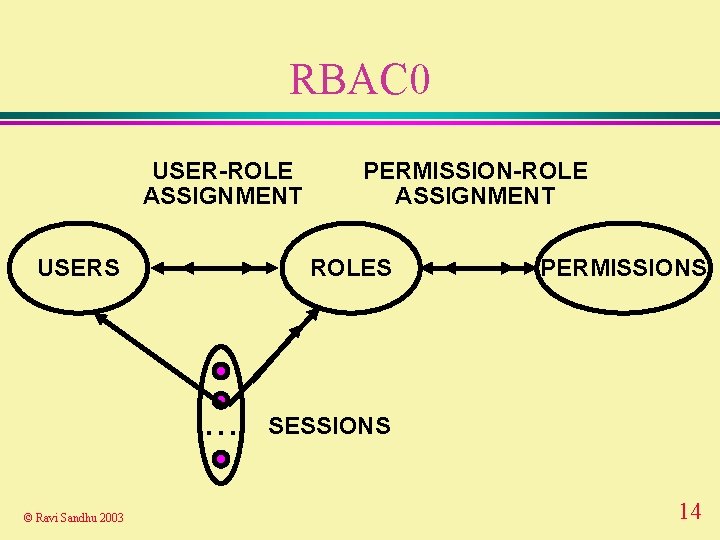
RBAC 0 USER-ROLE ASSIGNMENT USERS ROLES . . . © Ravi Sandhu 2003 PERMISSION-ROLE ASSIGNMENT PERMISSIONS SESSIONS 14
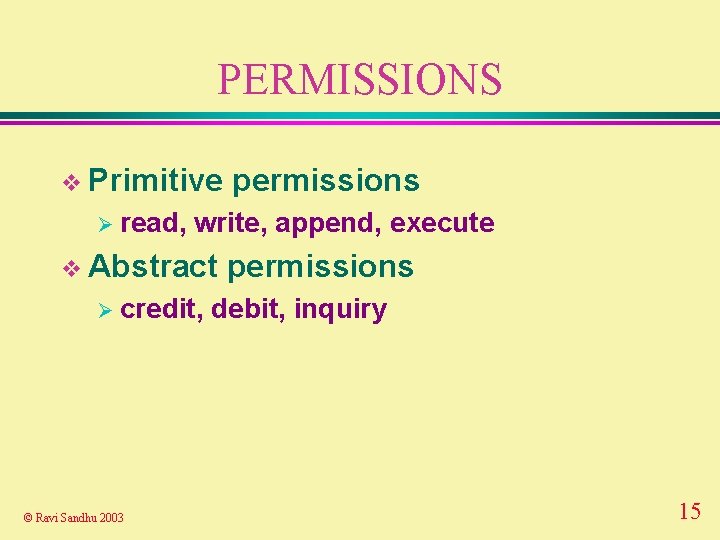
PERMISSIONS v Primitive Ø read, write, append, execute v Abstract Ø credit, © Ravi Sandhu 2003 permissions debit, inquiry 15
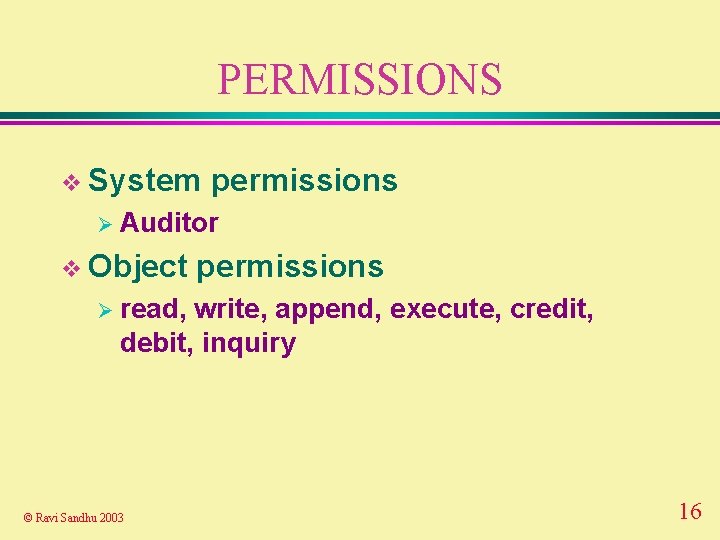
PERMISSIONS v System permissions Ø Auditor v Object permissions Ø read, write, append, execute, credit, debit, inquiry © Ravi Sandhu 2003 16
PERMISSIONS v Permissions are positive v No negative permissions or denials Ø negative permissions and denials can be handled by constraints v No Ø © Ravi Sandhu 2003 duties or obligations outside scope of access control 17
ROLES AS POLICY v. A role brings together Øa collection of users and Ø a collection of permissions v These collections will vary over time ØA role has significance and meaning beyond the particular users and permissions brought together at any moment © Ravi Sandhu 2003 18
ROLES VERSUS GROUPS v Groups Øa v. A are often defined as collection of users role is Øa collection of users and Ø a collection of permissions v Some Øa © Ravi Sandhu 2003 authors define role as collection of permissions 19
USERS v Users are Ø human beings or Ø other active agents v Each individual should be known as exactly one user © Ravi Sandhu 2003 20
USER-ROLE ASSIGNMENT v. A user can be a member of many roles v Each role can have many users as members © Ravi Sandhu 2003 21
SESSIONS v. A user can invoke multiple sessions v In each session a user can invoke any subset of roles that the user is a member of © Ravi Sandhu 2003 22
PERMISSION-ROLE ASSIGNMENT v. A permission can be assigned to many roles v Each role can have many permissions © Ravi Sandhu 2003 23
MANAGEMENT OF RBAC v Option 1: USER-ROLE-ASSIGNMENT and PERMISSION-ROLE ASSIGNMENT can be changed only by the chief security officer v Option 2: Use RBAC to manage RBAC © Ravi Sandhu 2003 24
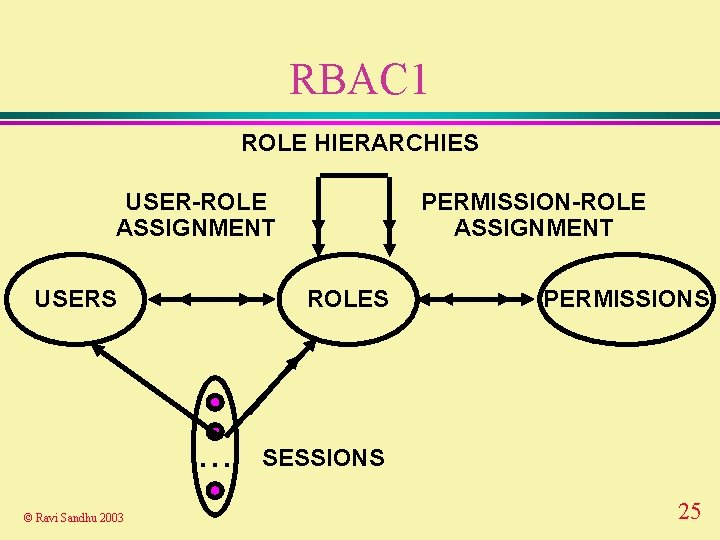
RBAC 1 ROLE HIERARCHIES USER-ROLE ASSIGNMENT USERS ROLES . . . © Ravi Sandhu 2003 PERMISSION-ROLE ASSIGNMENT PERMISSIONS SESSIONS 25
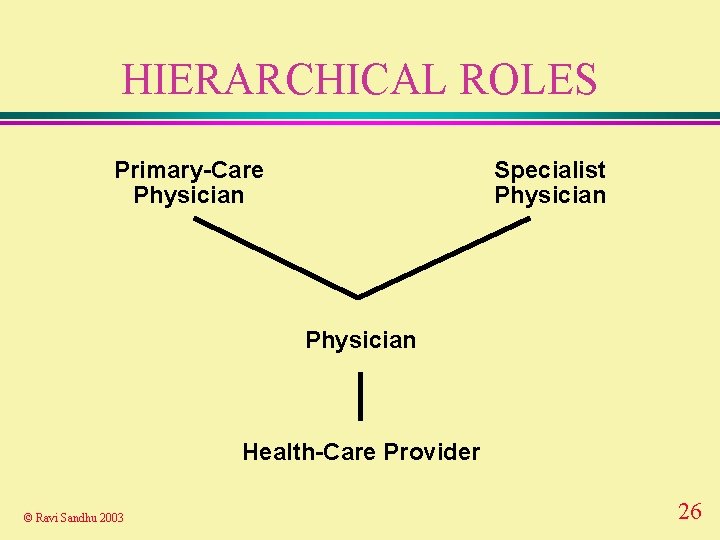
HIERARCHICAL ROLES Primary-Care Physician Specialist Physician Health-Care Provider © Ravi Sandhu 2003 26
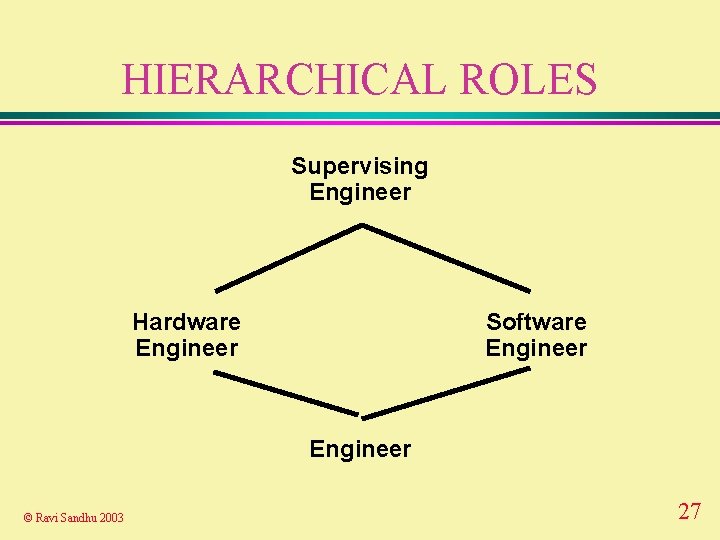
HIERARCHICAL ROLES Supervising Engineer Hardware Engineer Software Engineer © Ravi Sandhu 2003 27
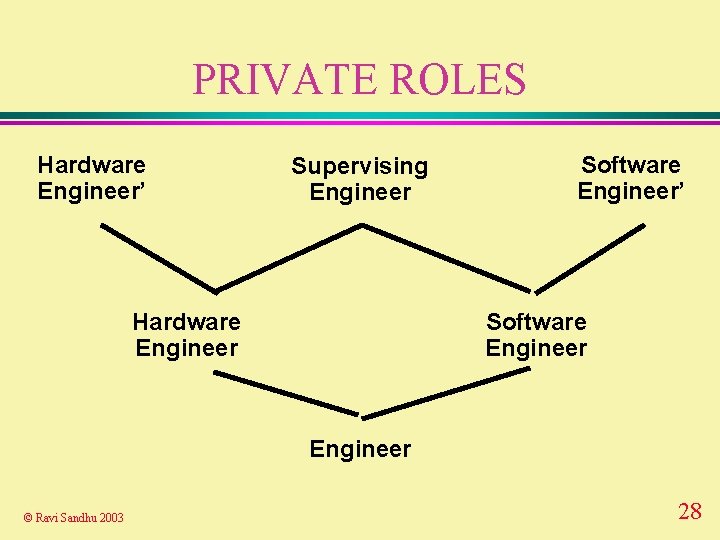
PRIVATE ROLES Hardware Engineer’ Supervising Engineer Hardware Engineer Software Engineer’ Software Engineer © Ravi Sandhu 2003 28
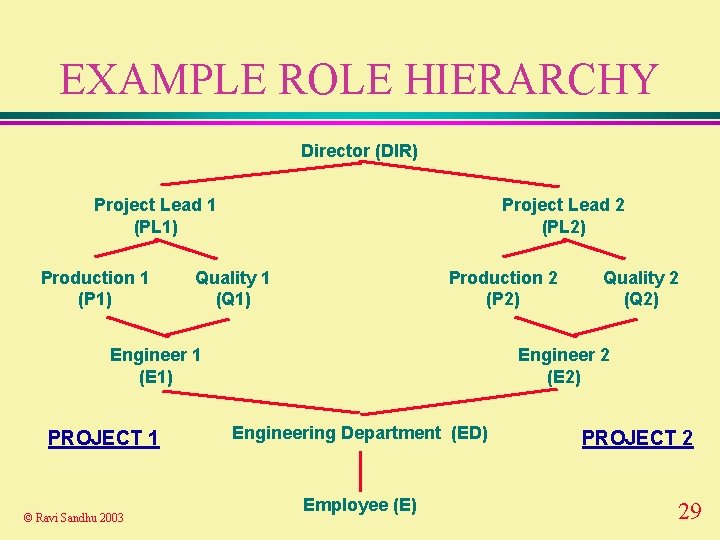
EXAMPLE ROLE HIERARCHY Director (DIR) Project Lead 1 (PL 1) Production 1 (P 1) Project Lead 2 (PL 2) Quality 1 (Q 1) Production 2 (P 2) Engineer 1 (E 1) PROJECT 1 © Ravi Sandhu 2003 Quality 2 (Q 2) Engineer 2 (E 2) Engineering Department (ED) Employee (E) PROJECT 2 29
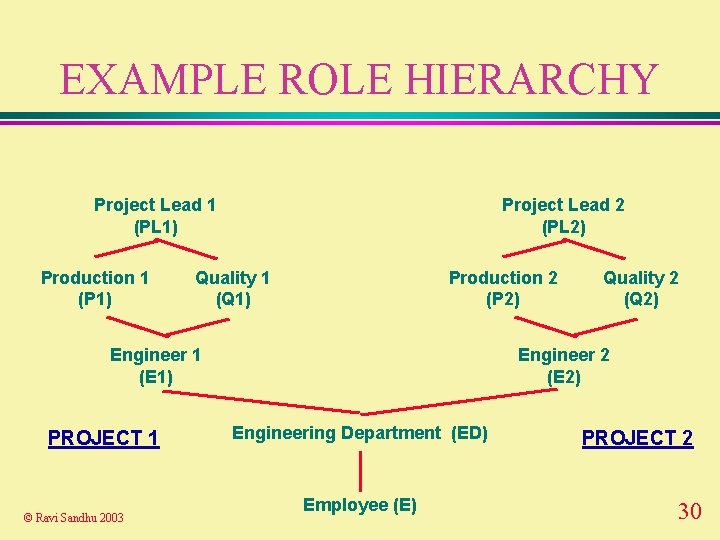
EXAMPLE ROLE HIERARCHY Project Lead 1 (PL 1) Production 1 (P 1) Project Lead 2 (PL 2) Quality 1 (Q 1) Production 2 (P 2) Engineer 1 (E 1) PROJECT 1 © Ravi Sandhu 2003 Quality 2 (Q 2) Engineer 2 (E 2) Engineering Department (ED) Employee (E) PROJECT 2 30
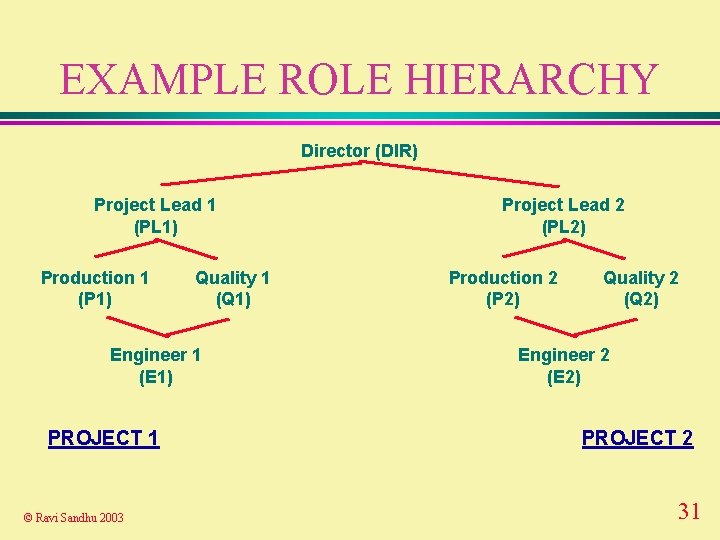
EXAMPLE ROLE HIERARCHY Director (DIR) Project Lead 1 (PL 1) Production 1 (P 1) Quality 1 (Q 1) Engineer 1 (E 1) PROJECT 1 © Ravi Sandhu 2003 Project Lead 2 (PL 2) Production 2 (P 2) Quality 2 (Q 2) Engineer 2 (E 2) PROJECT 2 31
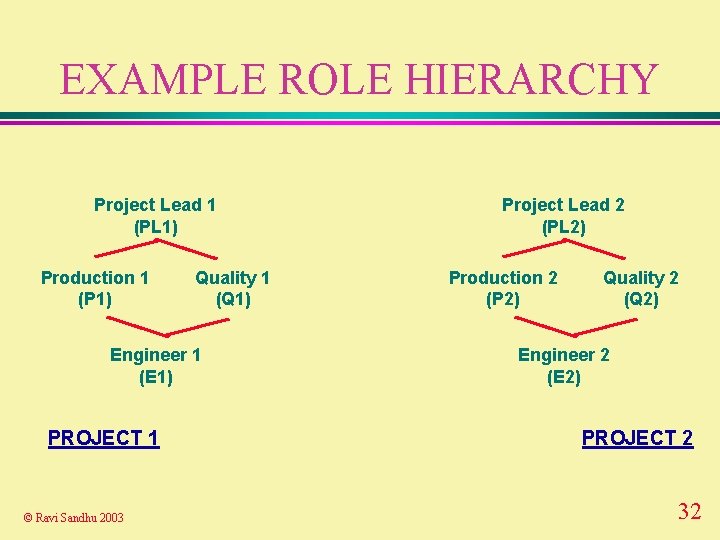
EXAMPLE ROLE HIERARCHY Project Lead 1 (PL 1) Production 1 (P 1) Quality 1 (Q 1) Engineer 1 (E 1) PROJECT 1 © Ravi Sandhu 2003 Project Lead 2 (PL 2) Production 2 (P 2) Quality 2 (Q 2) Engineer 2 (E 2) PROJECT 2 32
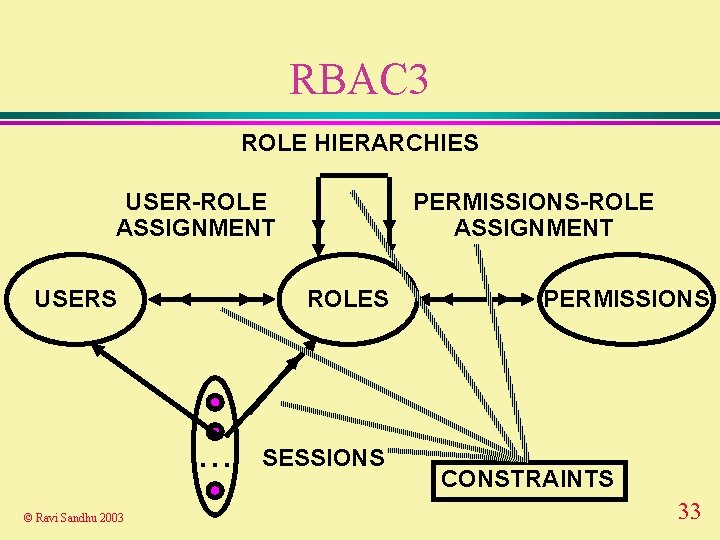
RBAC 3 ROLE HIERARCHIES USER-ROLE ASSIGNMENT USERS ROLES . . . © Ravi Sandhu 2003 PERMISSIONS-ROLE ASSIGNMENT SESSIONS PERMISSIONS CONSTRAINTS 33
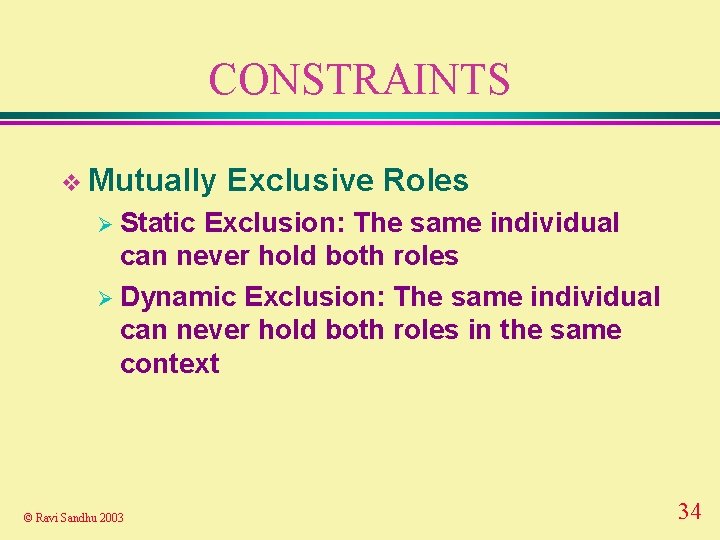
CONSTRAINTS v Mutually Exclusive Roles Ø Static Exclusion: The same individual can never hold both roles Ø Dynamic Exclusion: The same individual can never hold both roles in the same context © Ravi Sandhu 2003 34
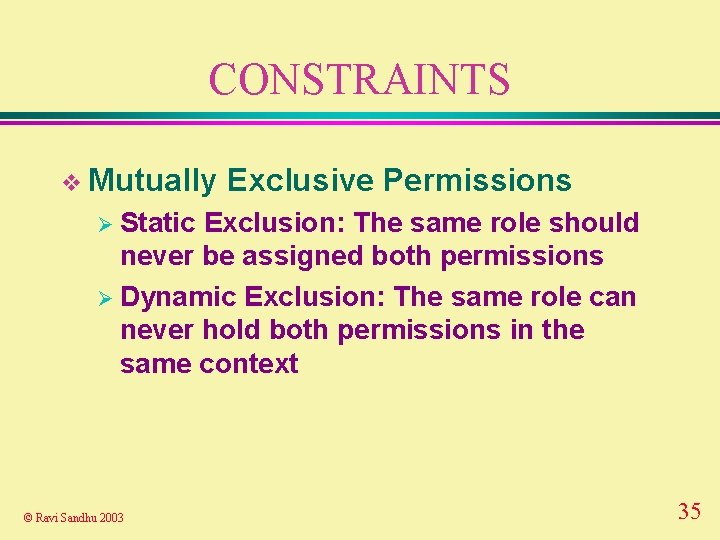
CONSTRAINTS v Mutually Exclusive Permissions Ø Static Exclusion: The same role should never be assigned both permissions Ø Dynamic Exclusion: The same role can never hold both permissions in the same context © Ravi Sandhu 2003 35
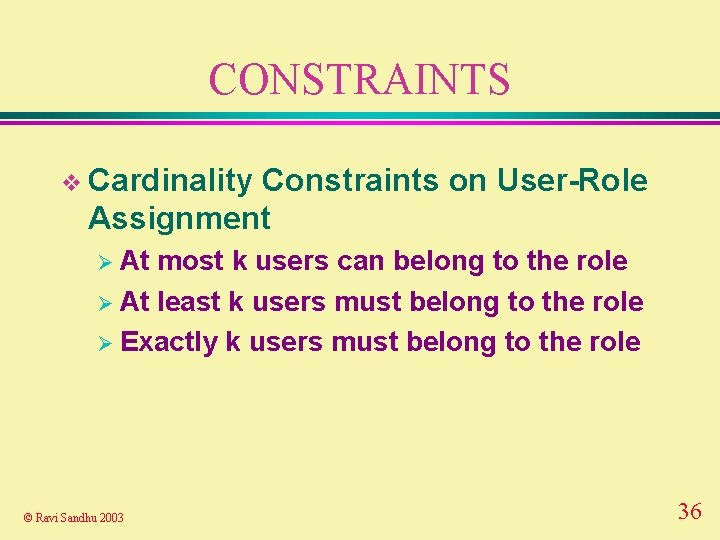
CONSTRAINTS v Cardinality Constraints on User-Role Assignment Ø At most k users can belong to the role Ø At least k users must belong to the role Ø Exactly k users must belong to the role © Ravi Sandhu 2003 36
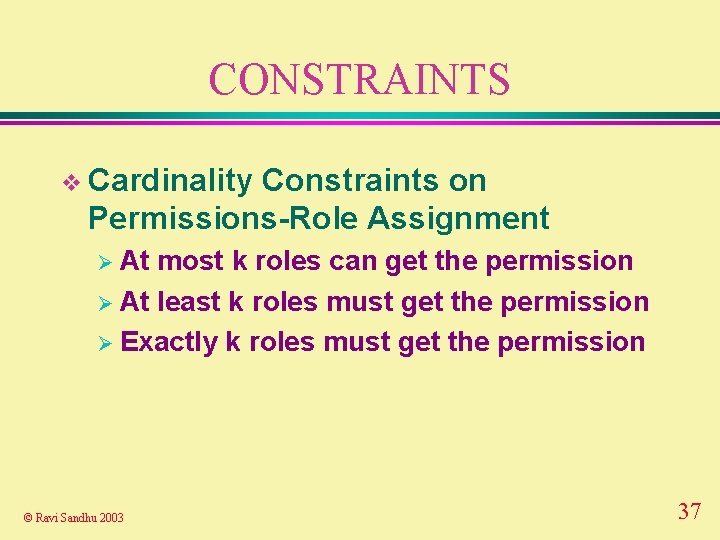
CONSTRAINTS v Cardinality Constraints on Permissions-Role Assignment Ø At most k roles can get the permission Ø At least k roles must get the permission Ø Exactly k roles must get the permission © Ravi Sandhu 2003 37
RBAC-MAC-DAC
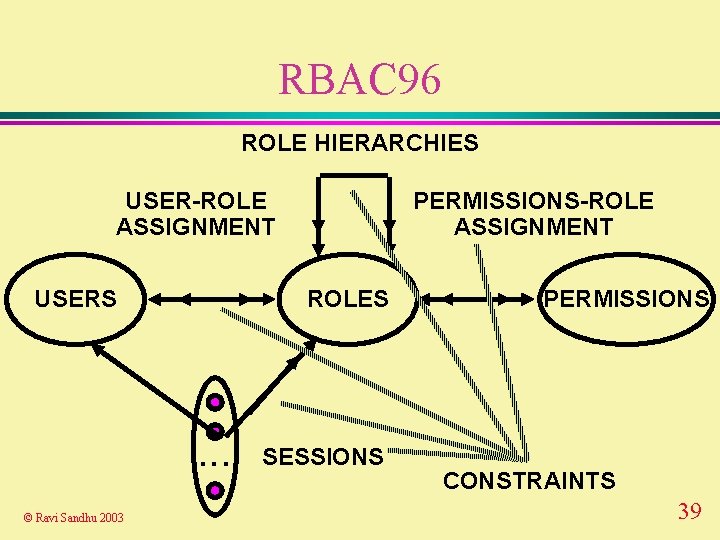
RBAC 96 ROLE HIERARCHIES USER-ROLE ASSIGNMENT USERS ROLES . . . © Ravi Sandhu 2003 PERMISSIONS-ROLE ASSIGNMENT SESSIONS PERMISSIONS CONSTRAINTS 39
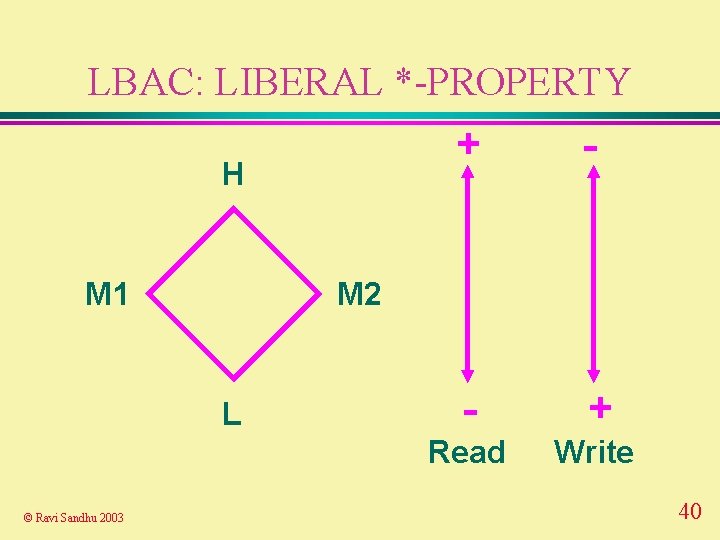
LBAC: LIBERAL *-PROPERTY H M 1 - - + Read Write M 2 L © Ravi Sandhu 2003 + 40
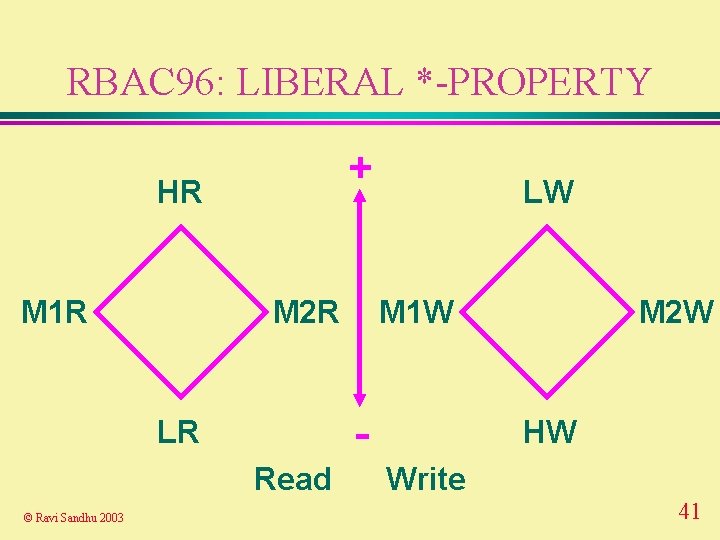
RBAC 96: LIBERAL *-PROPERTY + HR M 1 R M 2 R M 1 W - LR Read © Ravi Sandhu 2003 LW M 2 W HW Write 41
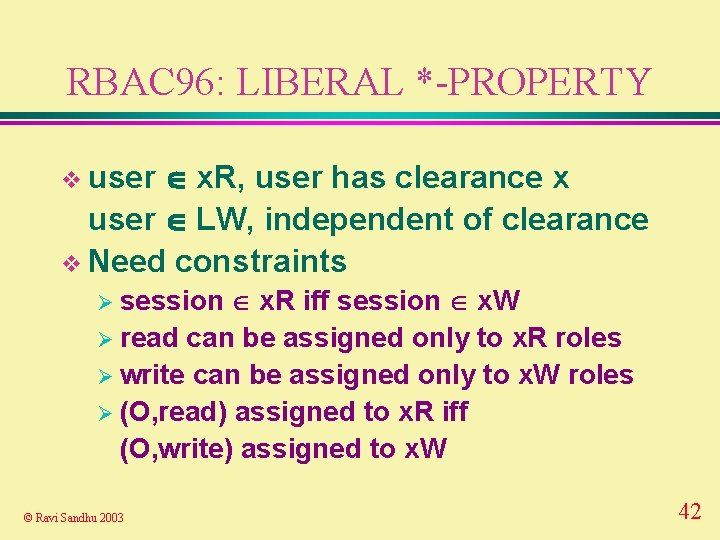
RBAC 96: LIBERAL *-PROPERTY x. R, user has clearance x user LW, independent of clearance v Need constraints v user x. R iff session x. W Ø read can be assigned only to x. R roles Ø write can be assigned only to x. W roles Ø (O, read) assigned to x. R iff (O, write) assigned to x. W Ø session © Ravi Sandhu 2003 42
DAC IN RBAC v Each user can create discretionary roles for assigning grantable permissions v For true DAC need grantable permissions for each object owned by the user © Ravi Sandhu 2003 43
Administrative RBAC ARBAC 97
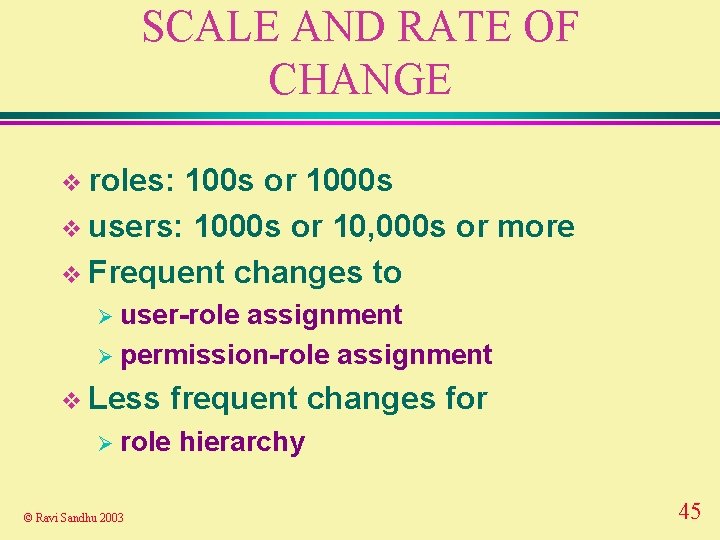
SCALE AND RATE OF CHANGE v roles: 100 s or 1000 s v users: 1000 s or 10, 000 s or more v Frequent changes to Ø user-role assignment Ø permission-role assignment v Less frequent changes for Ø role © Ravi Sandhu 2003 hierarchy 45
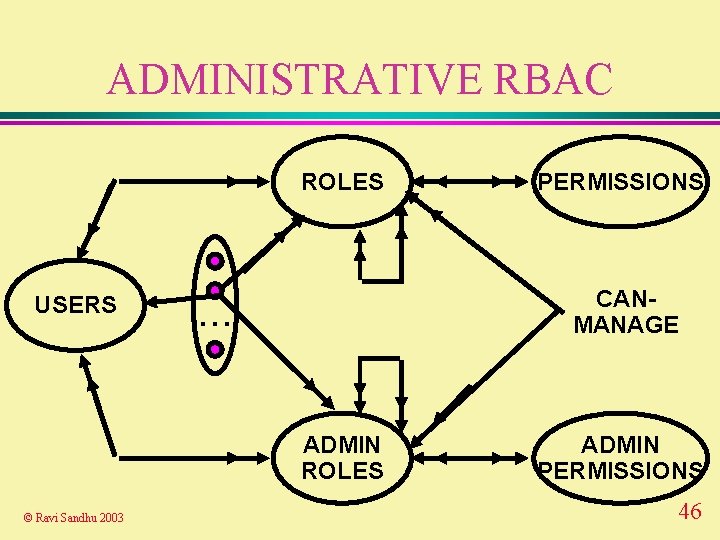
ADMINISTRATIVE RBAC ROLES USERS CANMANAGE . . . ADMIN ROLES © Ravi Sandhu 2003 PERMISSIONS ADMIN PERMISSIONS 46
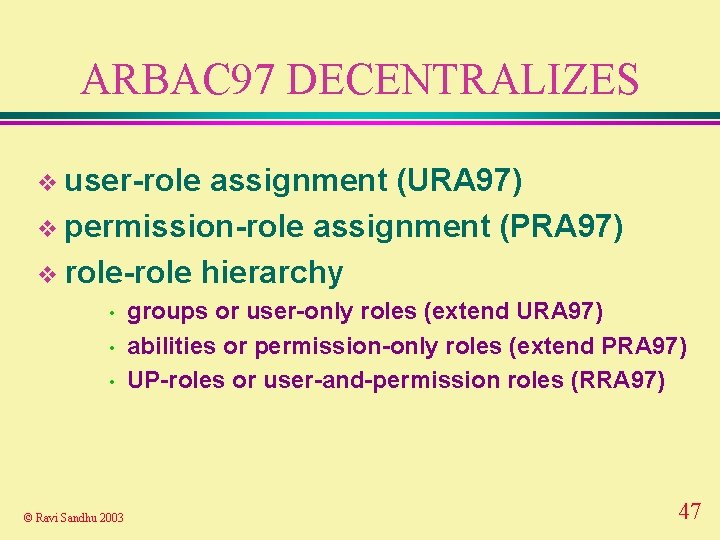
ARBAC 97 DECENTRALIZES v user-role assignment (URA 97) v permission-role assignment (PRA 97) v role-role hierarchy • • • © Ravi Sandhu 2003 groups or user-only roles (extend URA 97) abilities or permission-only roles (extend PRA 97) UP-roles or user-and-permission roles (RRA 97) 47
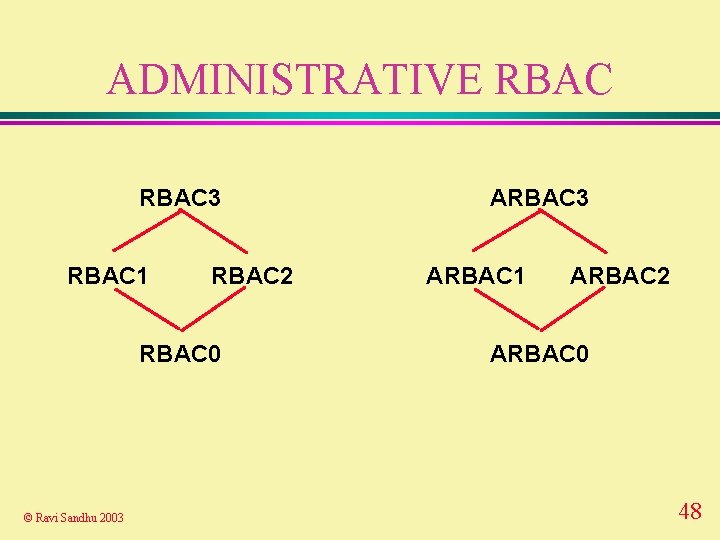
ADMINISTRATIVE RBAC 3 RBAC 1 RBAC 2 RBAC 0 © Ravi Sandhu 2003 ARBAC 1 ARBAC 2 ARBAC 0 48
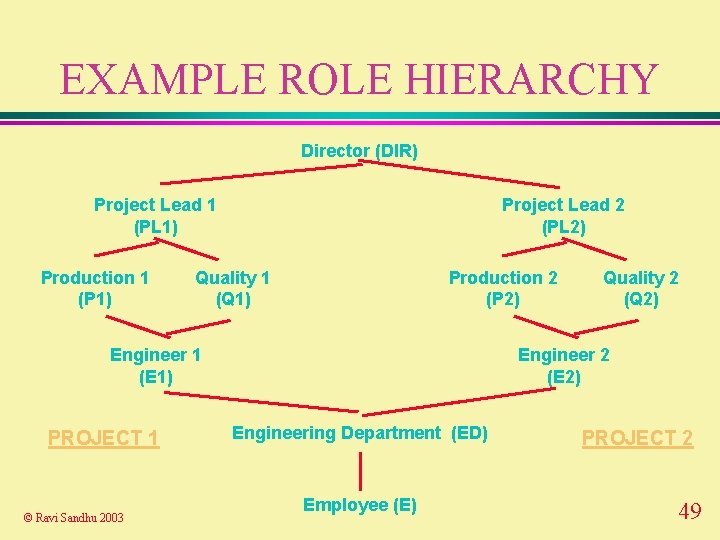
EXAMPLE ROLE HIERARCHY Director (DIR) Project Lead 1 (PL 1) Production 1 (P 1) Project Lead 2 (PL 2) Quality 1 (Q 1) Production 2 (P 2) Engineer 1 (E 1) PROJECT 1 © Ravi Sandhu 2003 Quality 2 (Q 2) Engineer 2 (E 2) Engineering Department (ED) Employee (E) PROJECT 2 49
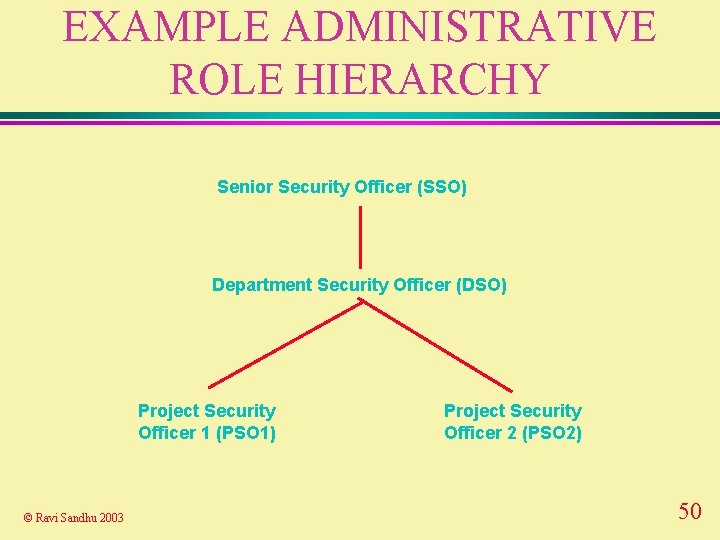
EXAMPLE ADMINISTRATIVE ROLE HIERARCHY Senior Security Officer (SSO) Department Security Officer (DSO) Project Security Officer 1 (PSO 1) © Ravi Sandhu 2003 Project Security Officer 2 (PSO 2) 50
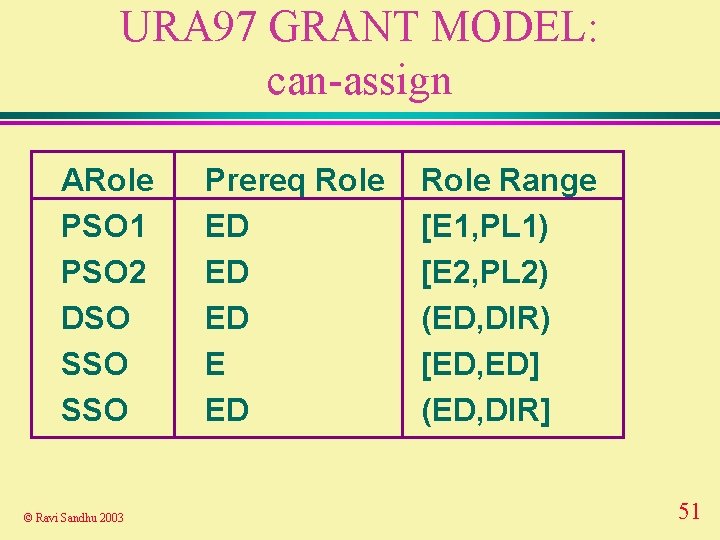
URA 97 GRANT MODEL: can-assign ARole PSO 1 PSO 2 DSO SSO © Ravi Sandhu 2003 Prereq Role ED ED ED E ED Role Range [E 1, PL 1) [E 2, PL 2) (ED, DIR) [ED, ED] (ED, DIR] 51
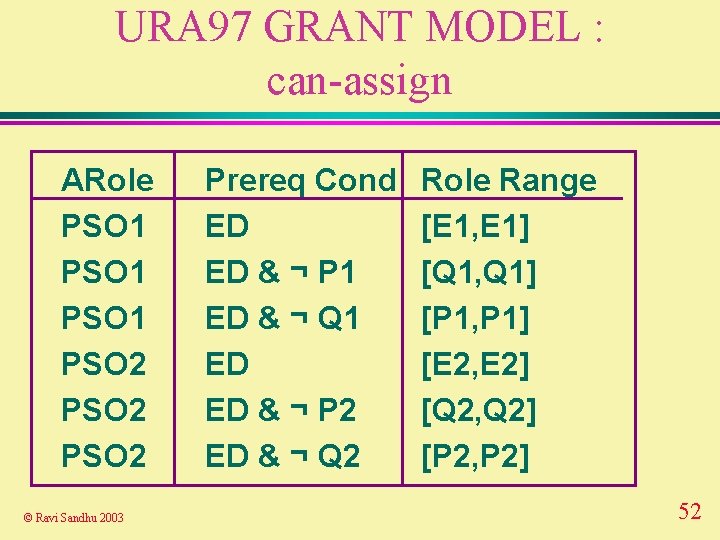
URA 97 GRANT MODEL : can-assign ARole PSO 1 PSO 2 © Ravi Sandhu 2003 Prereq Cond ED ED & ¬ P 1 ED & ¬ Q 1 ED ED & ¬ P 2 ED & ¬ Q 2 Role Range [E 1, E 1] [Q 1, Q 1] [P 1, P 1] [E 2, E 2] [Q 2, Q 2] [P 2, P 2] 52
URA 97 GRANT MODEL v “redundant” assignments to senior and junior roles Ø are allowed Ø are useful © Ravi Sandhu 2003 53
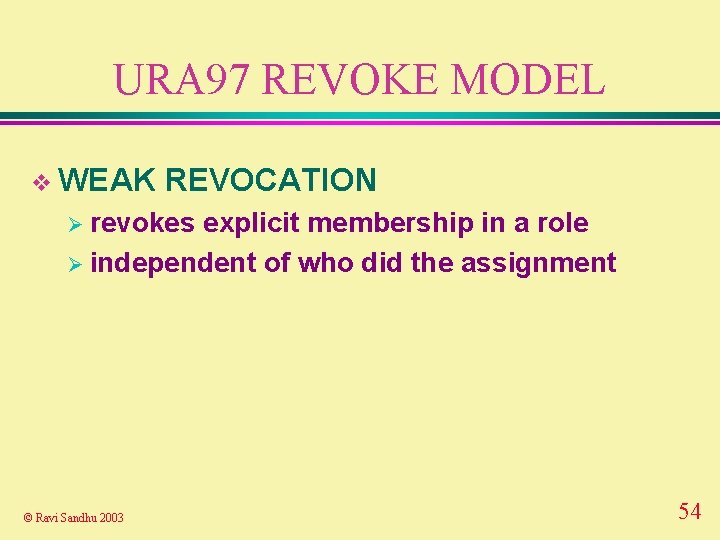
URA 97 REVOKE MODEL v WEAK REVOCATION Ø revokes explicit membership in a role Ø independent of who did the assignment © Ravi Sandhu 2003 54
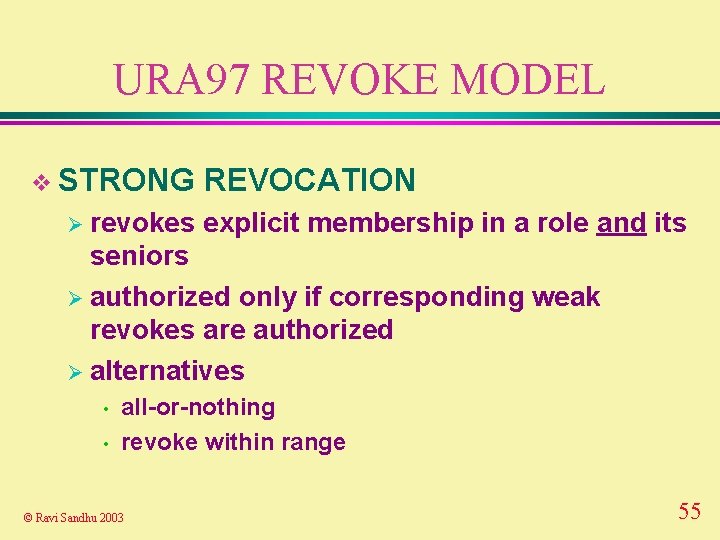
URA 97 REVOKE MODEL v STRONG Ø revokes REVOCATION explicit membership in a role and its seniors Ø authorized only if corresponding weak revokes are authorized Ø alternatives • • all-or-nothing revoke within range © Ravi Sandhu 2003 55
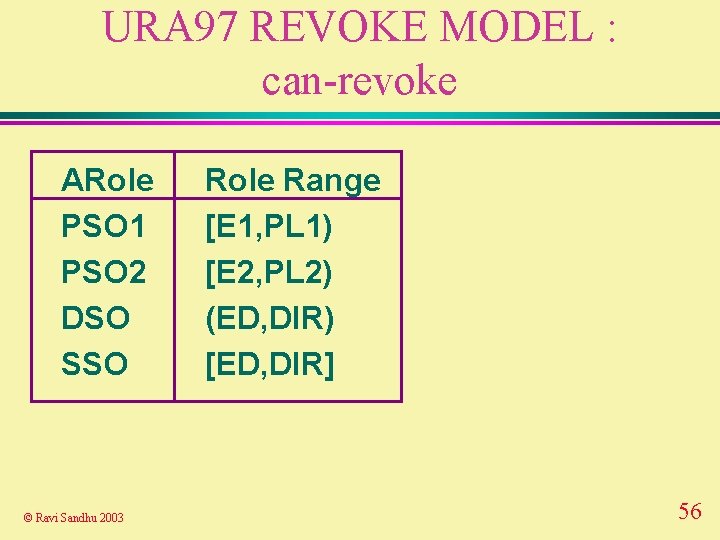
URA 97 REVOKE MODEL : can-revoke ARole PSO 1 PSO 2 DSO SSO © Ravi Sandhu 2003 Role Range [E 1, PL 1) [E 2, PL 2) (ED, DIR) [ED, DIR] 56
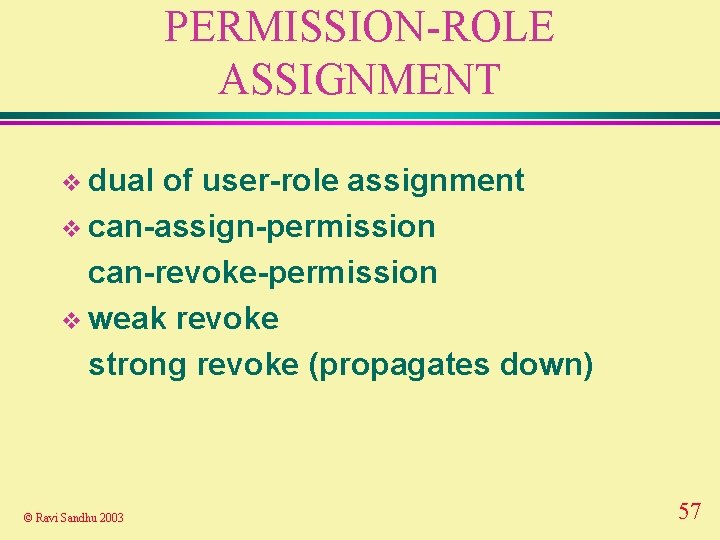
PERMISSION-ROLE ASSIGNMENT v dual of user-role assignment v can-assign-permission can-revoke-permission v weak revoke strong revoke (propagates down) © Ravi Sandhu 2003 57
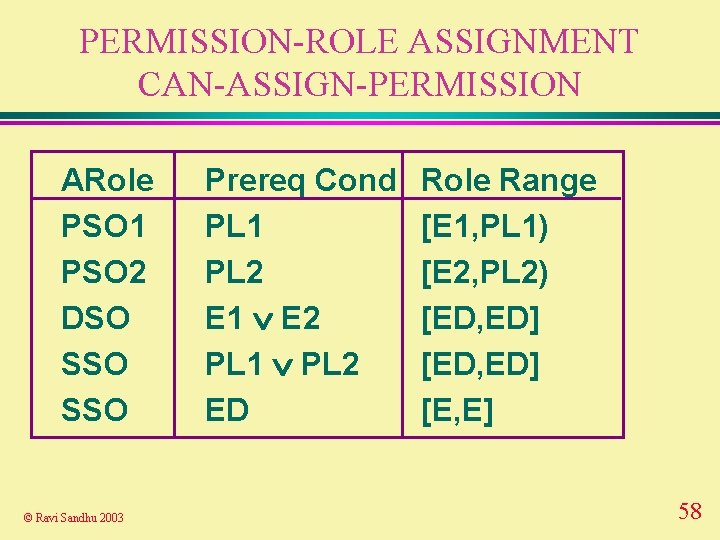
PERMISSION-ROLE ASSIGNMENT CAN-ASSIGN-PERMISSION ARole PSO 1 PSO 2 DSO SSO © Ravi Sandhu 2003 Prereq Cond PL 1 PL 2 E 1 E 2 PL 1 PL 2 ED Role Range [E 1, PL 1) [E 2, PL 2) [ED, ED] [E, E] 58
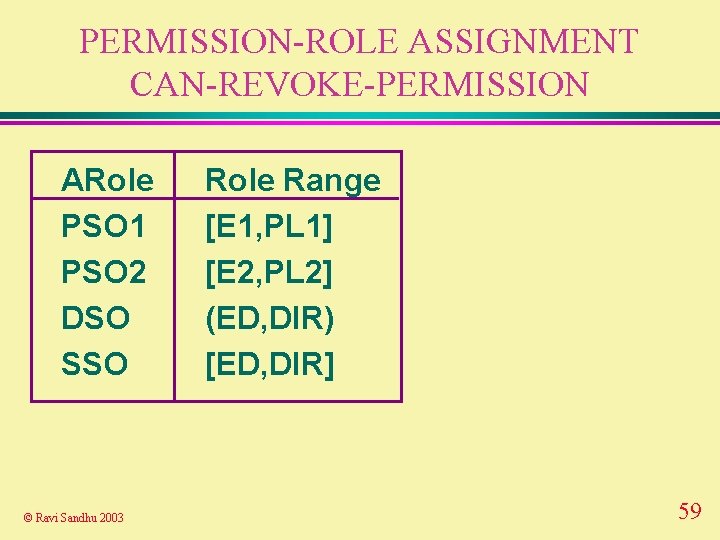
PERMISSION-ROLE ASSIGNMENT CAN-REVOKE-PERMISSION ARole PSO 1 PSO 2 DSO SSO © Ravi Sandhu 2003 Role Range [E 1, PL 1] [E 2, PL 2] (ED, DIR) [ED, DIR] 59
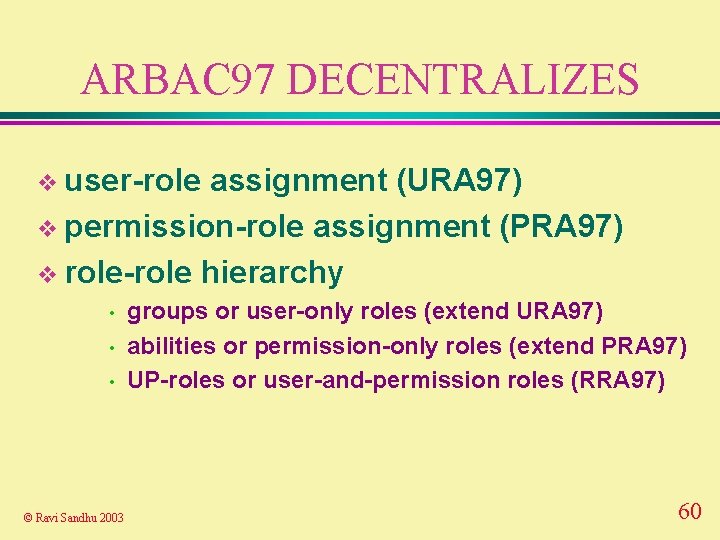
ARBAC 97 DECENTRALIZES v user-role assignment (URA 97) v permission-role assignment (PRA 97) v role-role hierarchy • • • © Ravi Sandhu 2003 groups or user-only roles (extend URA 97) abilities or permission-only roles (extend PRA 97) UP-roles or user-and-permission roles (RRA 97) 60
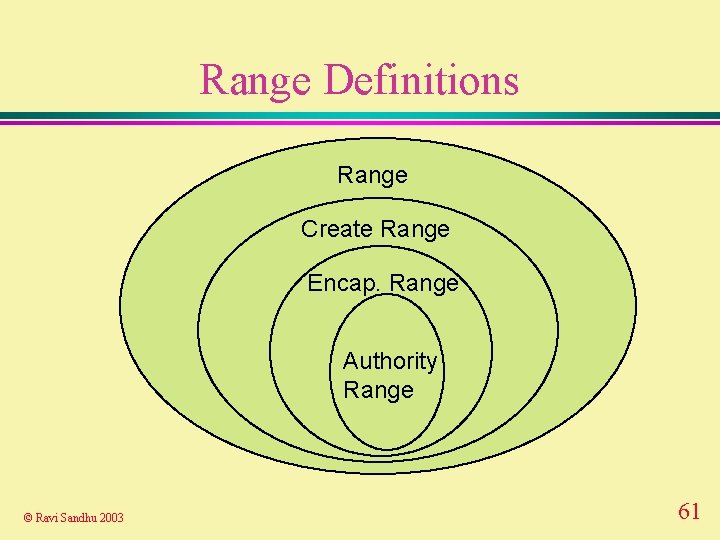
Range Definitions Range Create Range Encap. Range Authority Range © Ravi Sandhu 2003 61
RBAC Architectures and Mechanisms
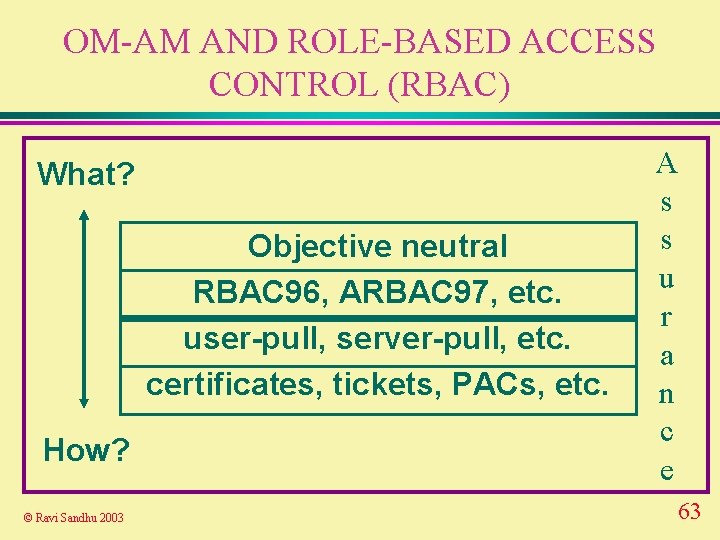
OM-AM AND ROLE-BASED ACCESS CONTROL (RBAC) What? Objective neutral RBAC 96, ARBAC 97, etc. user-pull, server-pull, etc. certificates, tickets, PACs, etc. How? © Ravi Sandhu 2003 A s s u r a n c e 63
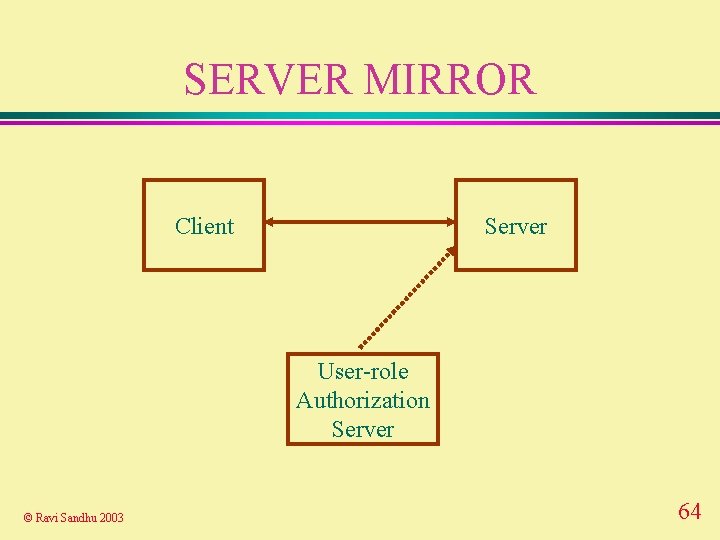
SERVER MIRROR Client Server User-role Authorization Server © Ravi Sandhu 2003 64
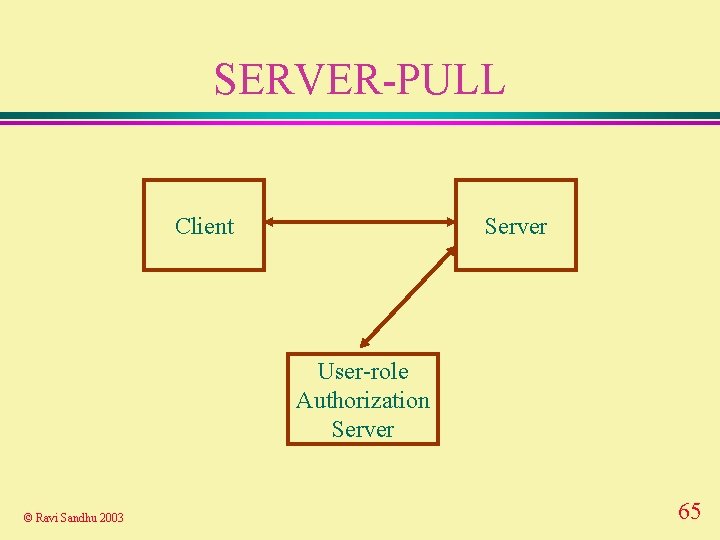
SERVER-PULL Client Server User-role Authorization Server © Ravi Sandhu 2003 65
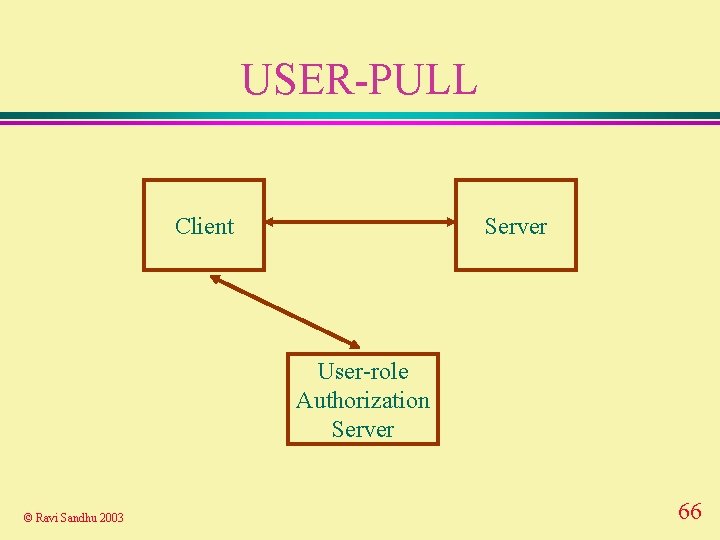
USER-PULL Client Server User-role Authorization Server © Ravi Sandhu 2003 66
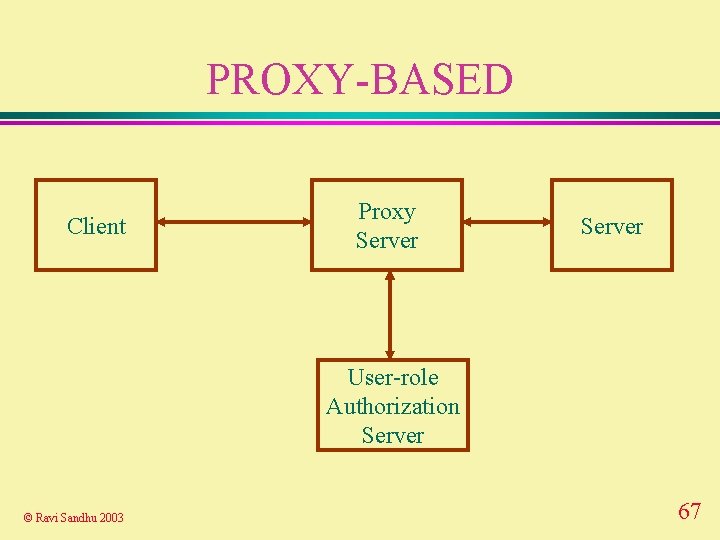
PROXY-BASED Client Proxy Server User-role Authorization Server © Ravi Sandhu 2003 67
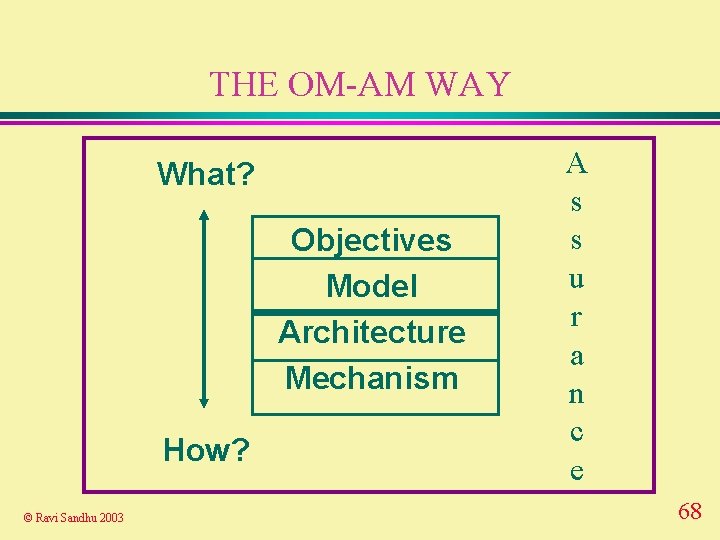
THE OM-AM WAY What? Objectives Model Architecture Mechanism How? © Ravi Sandhu 2003 A s s u r a n c e 68
- Slides: 68