Copyright Notice Copyright C 2004 Sentillion Inc All
![Impact “By [sharing context] between active applications, the end-user has the impression that all Impact “By [sharing context] between active applications, the end-user has the impression that all](https://slidetodoc.com/presentation_image/54a3fcc3ee751286b1643e59b65b103e/image-16.jpg)
- Slides: 69
Copyright Notice Copyright (C) 2004 Sentillion, Inc. All rights reserved. This presentation and related slides are proprietary to Sentillion, Inc. This presentation and related slides are provided for your company's internal use only. No part of this presentation or related slides may be reproduced, modified, displayed, distributed, sold, leased, transferred or transmitted, in any form or by any means, without the written permission of Sentillion, Inc. Copyright Sentillion, Inc. 2004
CCOW Tutorial Mark Morwood Sentillion, Inc. Mark. Morwood@sentillion. com Copyright Sentillion, Inc. 2004
Agenda 1. Users: General Concepts 2. Developers: Details of the CCOW Standard 3. Questions and Answers Copyright Sentillion, Inc. 2004
Users: General Concepts Copyright Sentillion, Inc. 2004
Healthcare’s IT Challenges Information Security Caregiver Productivity Patient Confidentiality Copyright Sentillion, Inc. 2004
Traditional Approaches Information Security via office-based technology: – Designed for 9 -to-5 environments – Assumes use of industry or de facto standards – Substantial customization Caregiver Productivity via repository with viewer: – Formidable interfacing challenges – Long implementation cycles (years) – Read-only access Patient Confidentiality: No traditional approach yet Issue: Traditional approaches not User-Centered Copyright Sentillion, Inc. 2004
User-Centered Design User is part of overall system design Not Ergonomics = Does it look, feel, smell nice Leverage what people do well, let machines do the grunt stuff Copyright Sentillion, Inc. 2004
User-Centered IT “View” and “Do” as appropriate for all applications Repeated access for short periods of time Micro-mobility Shared workstations “Interrupt-driven” workflows Speed, simplicity, and technology transparency Fact: CCOW enables User-Centered IT solutions Copyright Sentillion, Inc. 2004
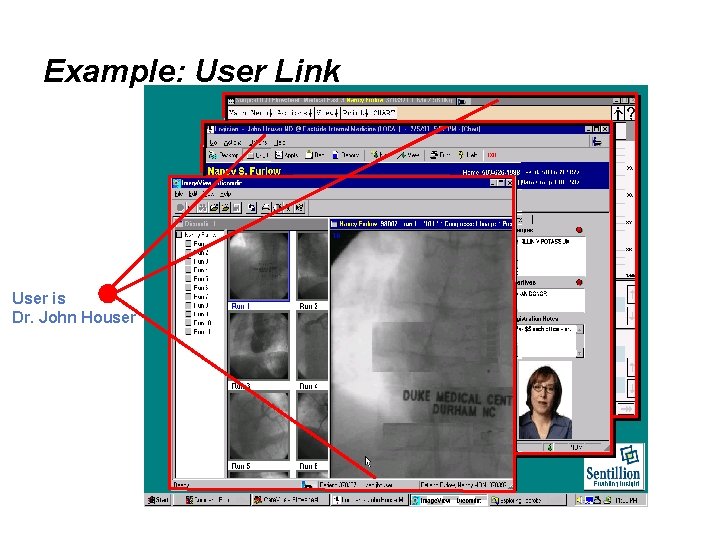
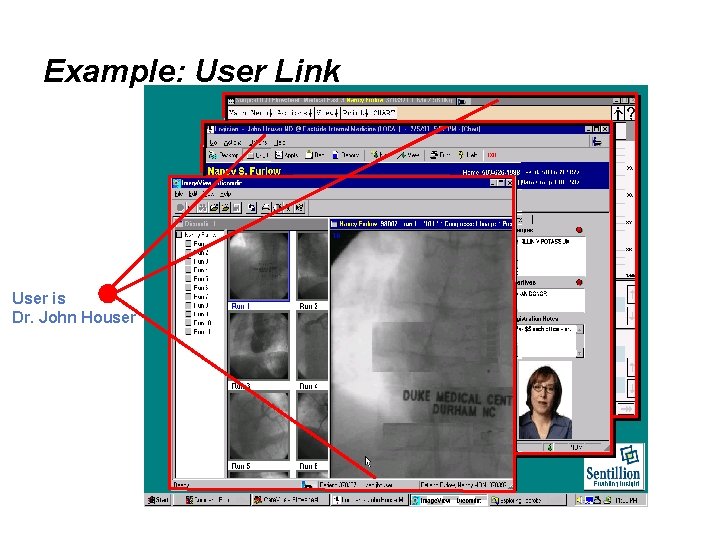
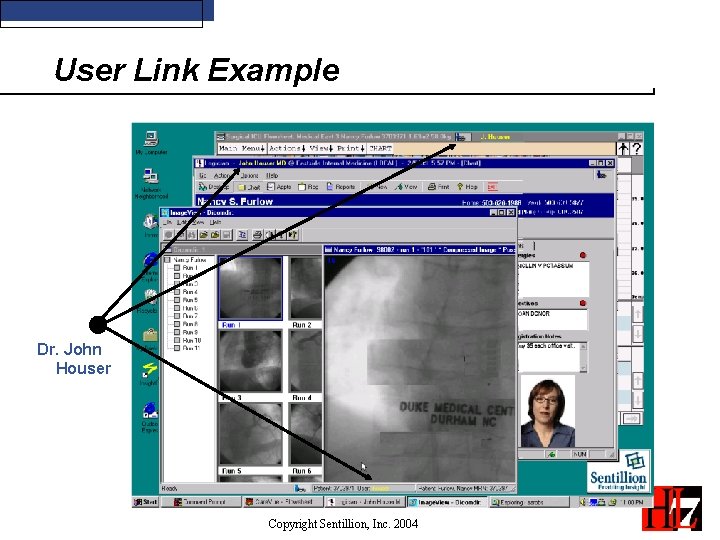
Example: User Link User is Dr. John Houser
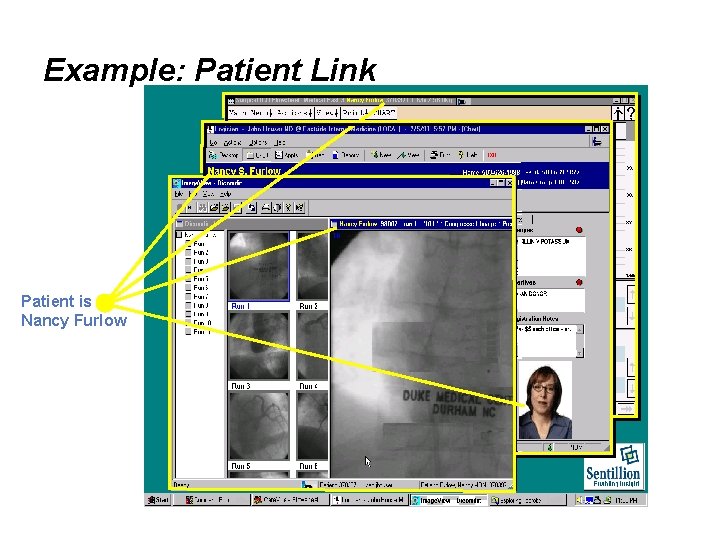
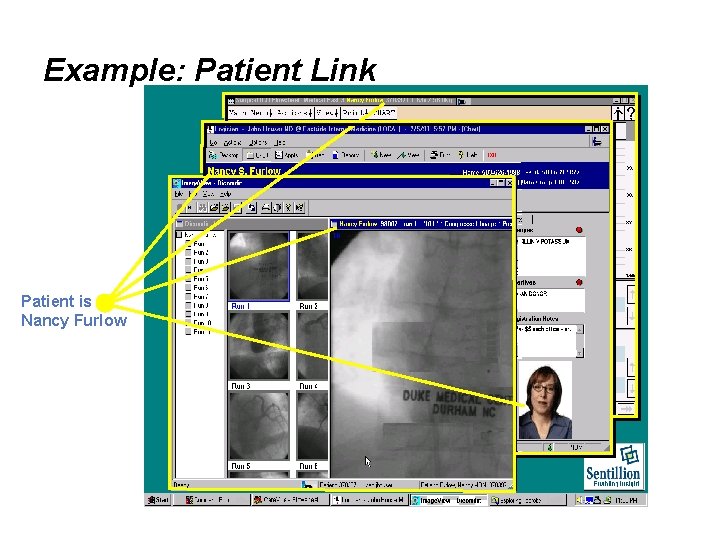
Example: Patient Link Patient is Nancy Furlow
Demonstration • CCOW Demo Copyright Sentillion, Inc. 2004
Key Benefits • Improved caregiver productivity: Eliminate repetitious logons, patient selections • Increased patient safety: Applications synchronized to same patient • Augmented security: Good security practices no longer tedious Copyright Sentillion, Inc. 2004
Developers: Details of the CCOW Standard Copyright Sentillion, Inc. 2004
The Challenge • Users in need of easy, safe, secure access to applications: physicians, nurses, therapists, administrators, etc. • Multiple disparate applications: labs, meds, cardiology, scheduling, billing, etc. • Shared as well as personal workstations: hospitals, clinics, offices, homes, etc. Copyright Sentillion, Inc. 2004
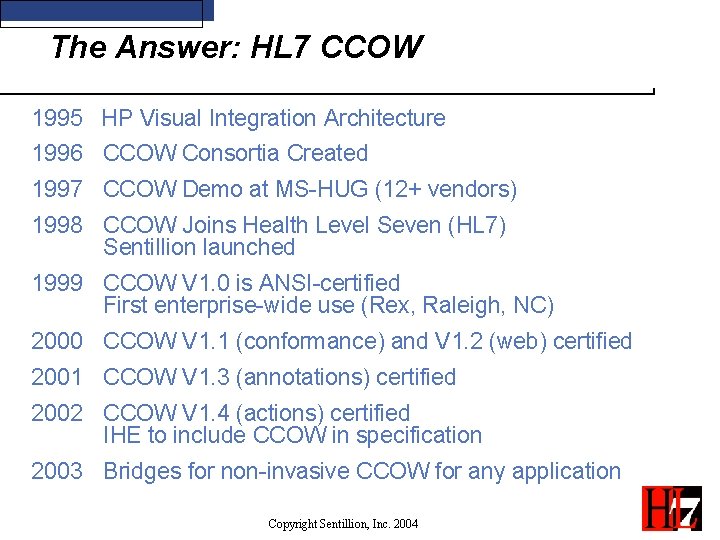
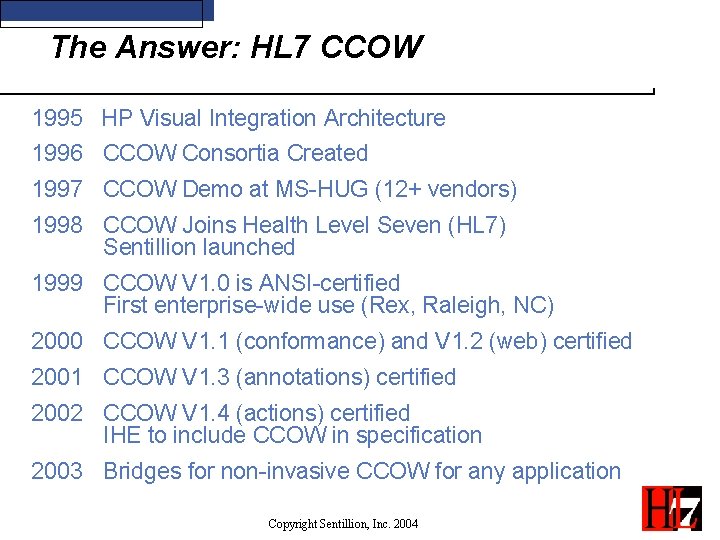
The Answer: HL 7 CCOW 1995 HP Visual Integration Architecture 1996 CCOW Consortia Created 1997 CCOW Demo at MS-HUG (12+ vendors) 1998 CCOW Joins Health Level Seven (HL 7) Sentillion launched 1999 CCOW V 1. 0 is ANSI-certified First enterprise-wide use (Rex, Raleigh, NC) 2000 CCOW V 1. 1 (conformance) and V 1. 2 (web) certified 2001 CCOW V 1. 3 (annotations) certified 2002 CCOW V 1. 4 (actions) certified IHE to include CCOW in specification 2003 Bridges for non-invasive CCOW for any application Copyright Sentillion, Inc. 2004
![Impact By sharing context between active applications the enduser has the impression that all Impact “By [sharing context] between active applications, the end-user has the impression that all](https://slidetodoc.com/presentation_image/54a3fcc3ee751286b1643e59b65b103e/image-16.jpg)
Impact “By [sharing context] between active applications, the end-user has the impression that all of their applications are acting together as a whole to access or manage different types of information about the same patient/person. ” EHRS Blueprint Version 1. 0 Copyright © 2003 Canada Health Infoway Inc. , All Rights Reserved Copyright Sentillion, Inc. 2004
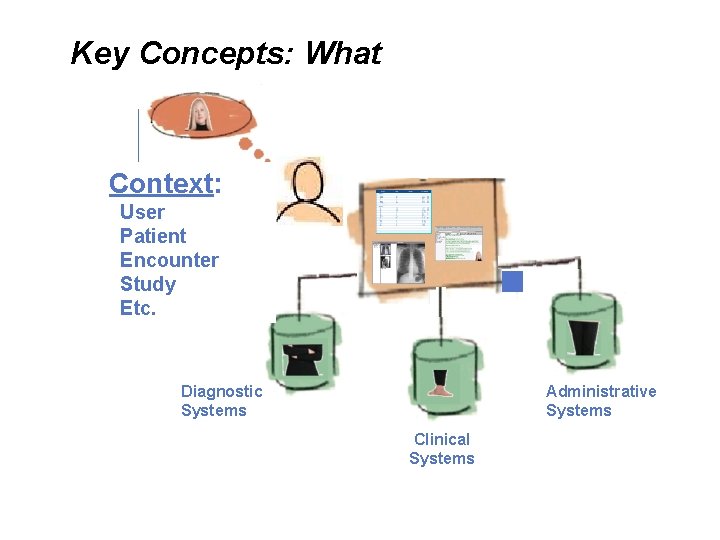
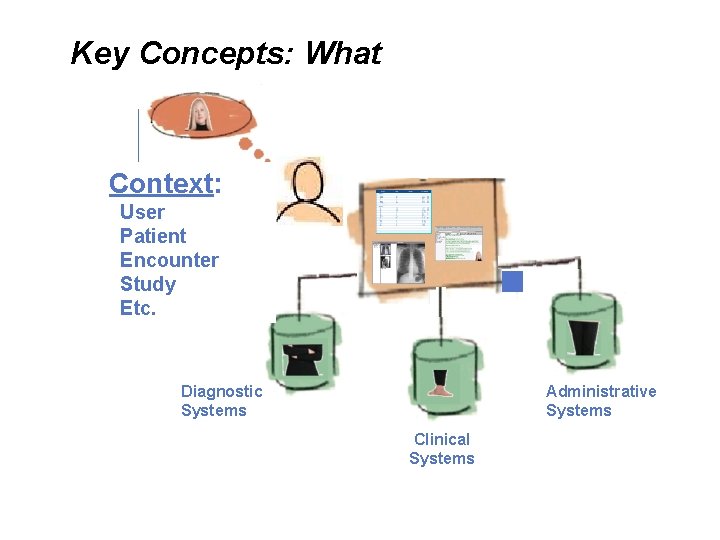
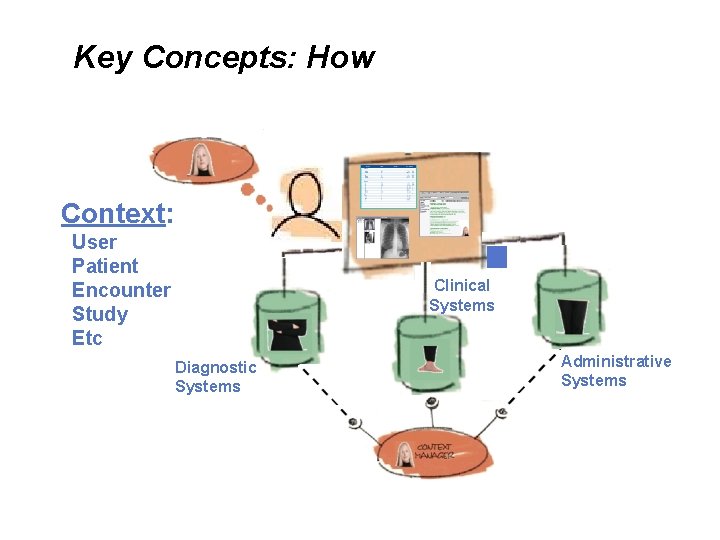
Key Concepts: What Context: User Patient Encounter Study Etc. Diagnostic Systems Administrative Systems Clinical Systems
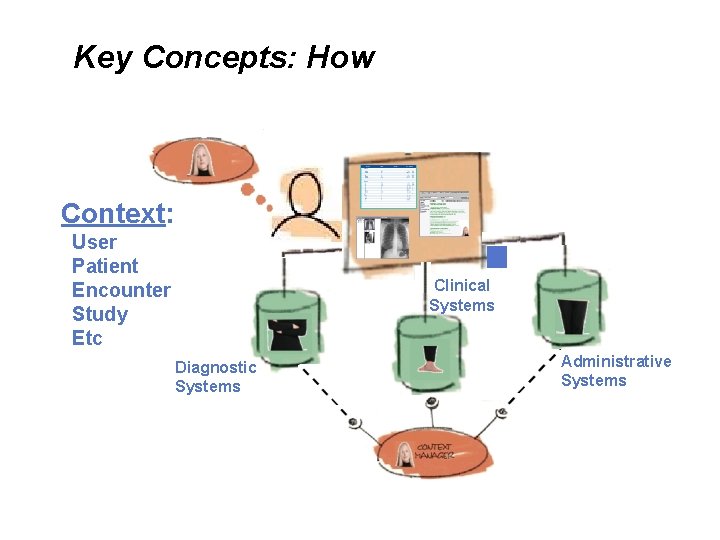
Key Concepts: How Context: User Patient Encounter Study Etc Clinical Systems Diagnostic Systems Administrative Systems
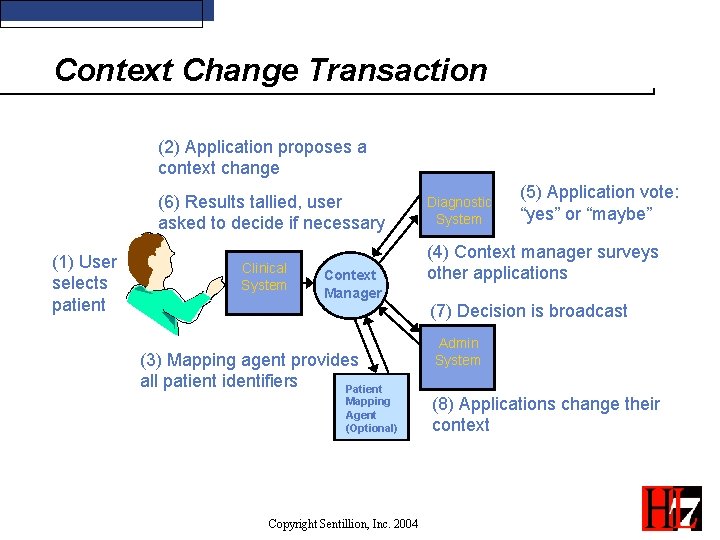
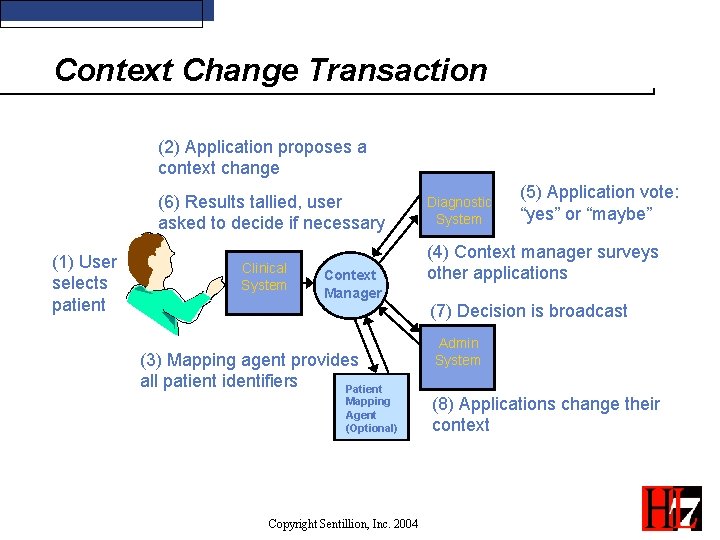
Context Change Transaction (2) Application proposes a context change (6) Results tallied, user asked to decide if necessary (1) User selects patient Clinical System Context Manager (3) Mapping agent provides all patient identifiers Patient Mapping Agent (Optional) Copyright Sentillion, Inc. 2004 Diagnostic System (5) Application vote: “yes” or “maybe” (4) Context manager surveys other applications (7) Decision is broadcast Admin System (8) Applications change their context
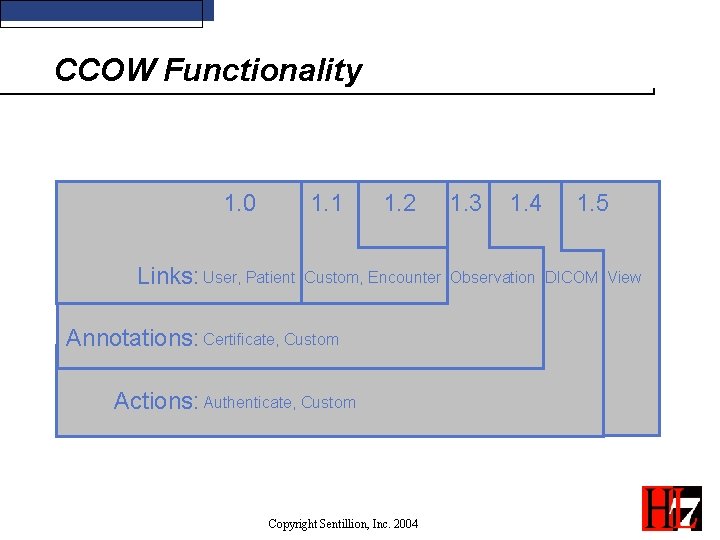
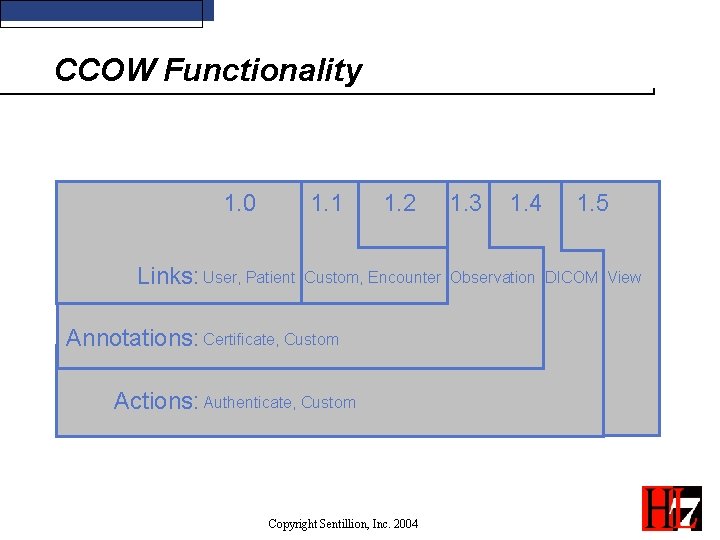
CCOW Functionality 1. 0 1. 1 1. 2 1. 3 1. 4 1. 5 Links: User, Patient Custom, Encounter Observation DICOM View Annotations: Certificate, Custom Actions: Authenticate, Custom Copyright Sentillion, Inc. 2004
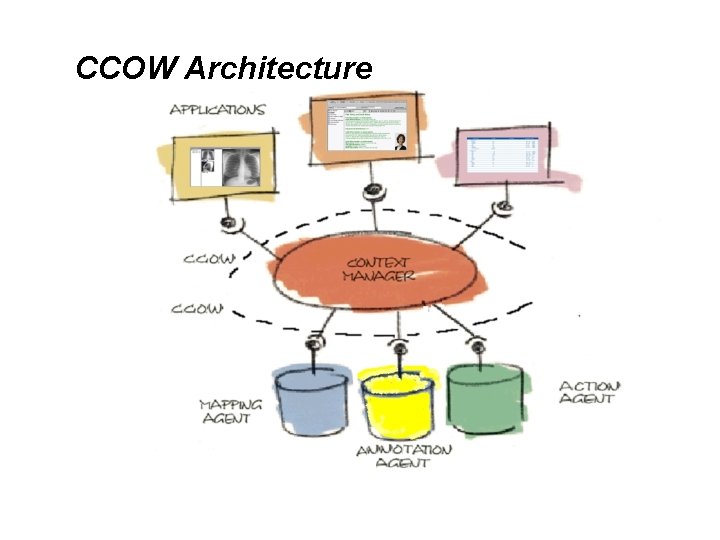
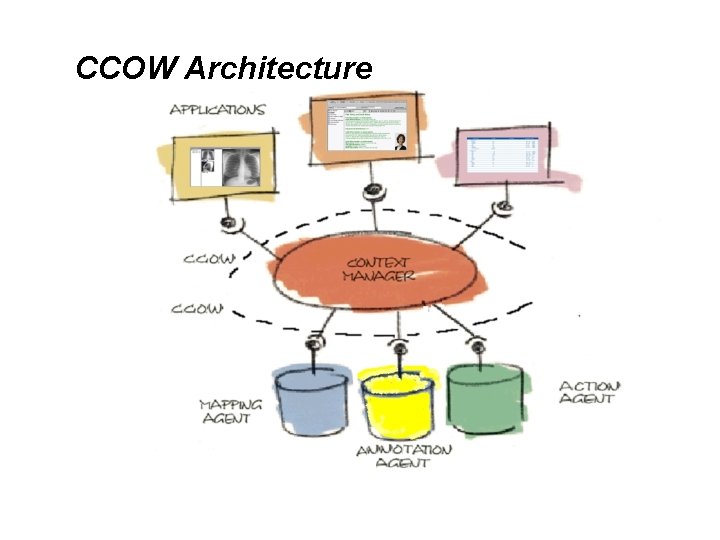
CCOW Architecture
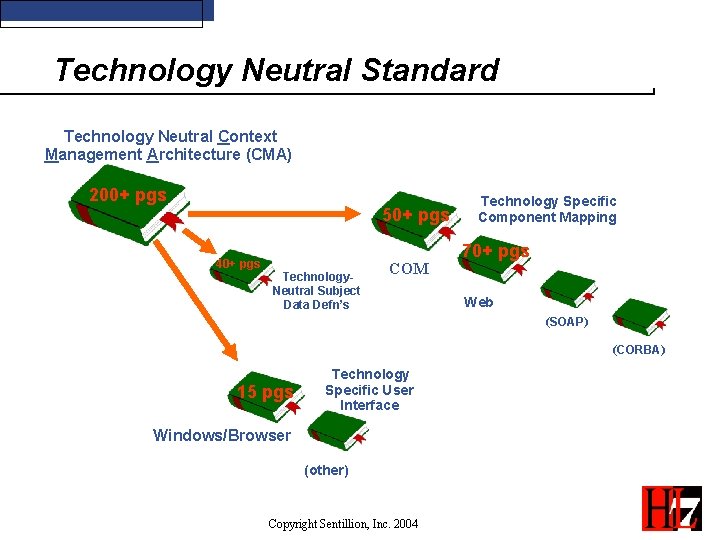
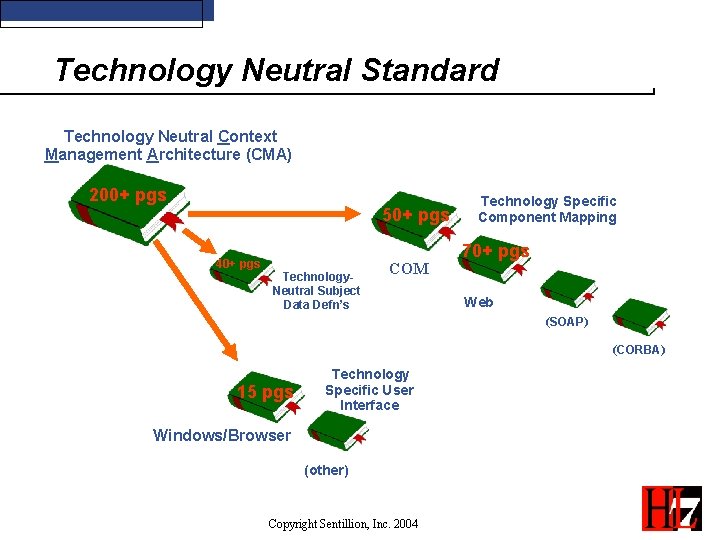
Technology Neutral Standard Technology Neutral Context Management Architecture (CMA) 200+ pgs 50+ pgs 40+ pgs Technology. Neutral Subject Data Defn’s COM Technology Specific Component Mapping 70+ pgs Web (SOAP) (CORBA) 15 pgs Technology Specific User Interface Windows/Browser (other) Copyright Sentillion, Inc. 2004
Key Architectural Principles A context subject is an identifiable real-world entity or concept Context subjects are represented by a set of name/value pairs A least one name/value pair is an identifier A subject can have multiple synonymous identifiers A context session may involve one or more subjects Only the user initiates a context change Applications never change the user’s “focus” Applications may “conditionally accept” a context change Applications never know about each other Copyright Sentillion, Inc. 2004
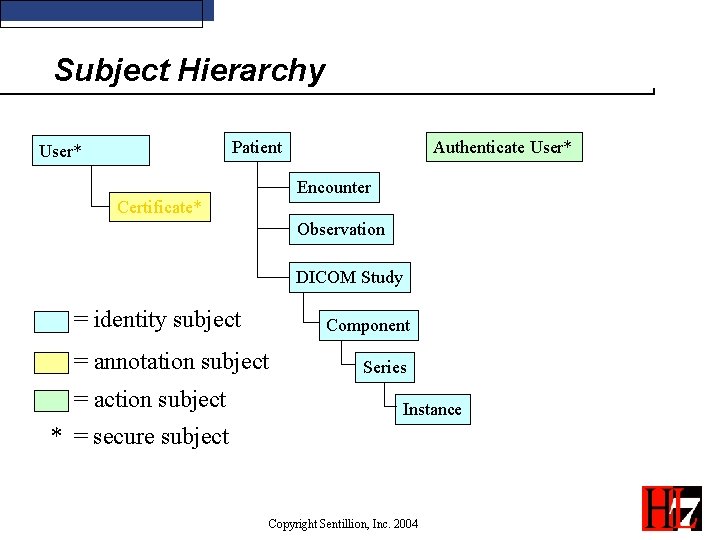
Classes of Subjects • Identity Subjects - Identifies a real world object - “User” and “Patient” are Identity subjects. • Annotation Subjects - Provides supplemental data for an Identity subject - Annotation subjects are dependent on their parent subject. - “Certificate” is an annotation to the “User” subject. • Action Subjects - Subjects that request another service to execute a task. - “Authenticate” is an action subject. Copyright Sentillion, Inc. 2004
Characteristics of Subjects • Common Subjects - Any application can get/set the contents of the subject. - “Patient” is a common subject. • Secure Subjects - Only applications with access privileges may set a secure subject. - “User” is a secure subject. Relies on the “Chain of Trust” • Dependent Subjects - The value of a dependent subject must be consistent with the value of another subject. - “Encounter” depends on “Patient”. • Custom Subjects - May be defined by healthcare providers and/or vendors separate from CCOW defined standard subjects. Copyright Sentillion, Inc. 2004
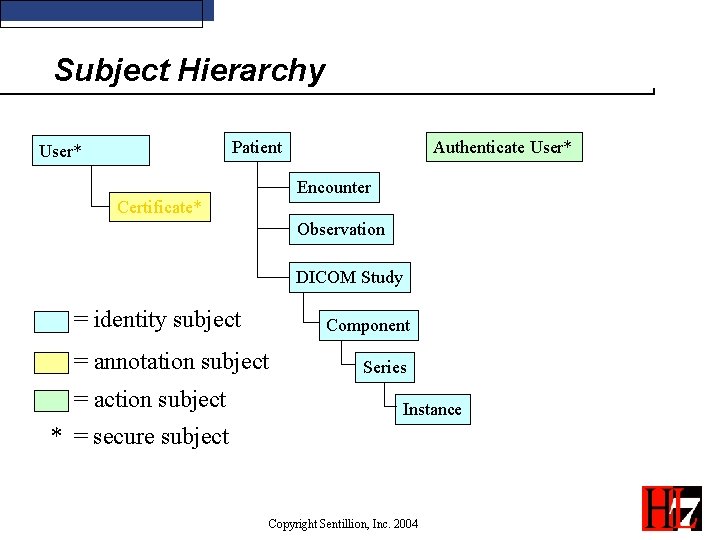
Subject Hierarchy Patient User* Authenticate User* Encounter Certificate* Observation DICOM Study = identity subject Component = annotation subject = action subject Series Instance * = secure subject Copyright Sentillion, Inc. 2004
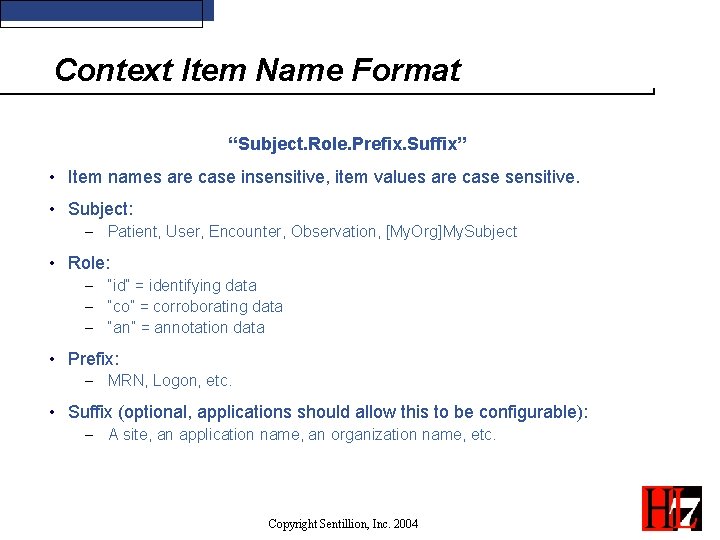
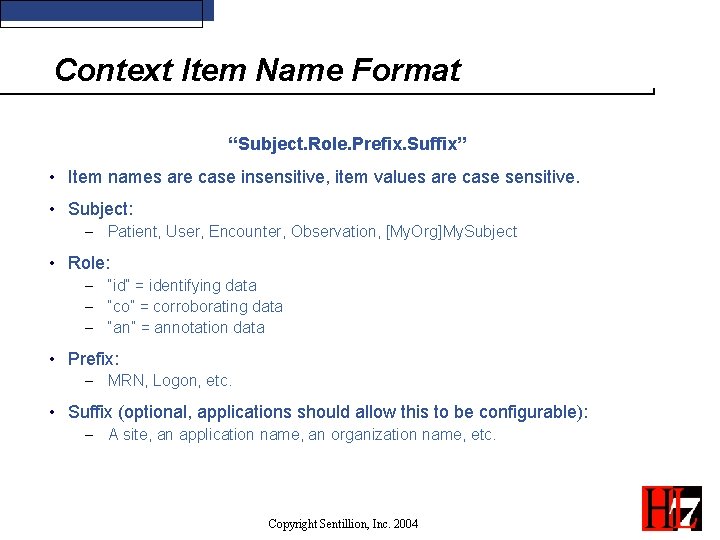
Context Item Name Format “Subject. Role. Prefix. Suffix” • Item names are case insensitive, item values are case sensitive. • Subject: - Patient, User, Encounter, Observation, [My. Org]My. Subject • Role: - “id” = identifying data - “co” = corroborating data - “an” = annotation data • Prefix: - MRN, Logon, etc. • Suffix (optional, applications should allow this to be configurable): - A site, an application name, an organization name, etc. Copyright Sentillion, Inc. 2004
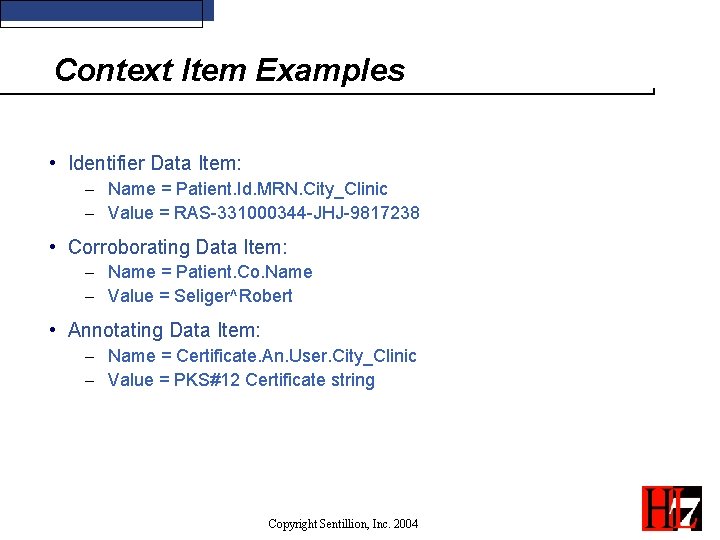
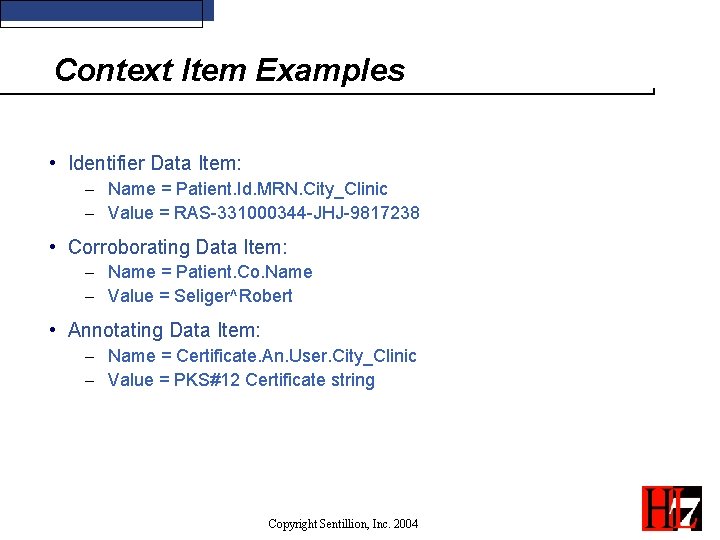
Context Item Examples • Identifier Data Item: - Name = Patient. Id. MRN. City_Clinic - Value = RAS-331000344 -JHJ-9817238 • Corroborating Data Item: - Name = Patient. Co. Name - Value = Seliger^Robert • Annotating Data Item: - Name = Certificate. An. User. City_Clinic - Value = PKS#12 Certificate string Copyright Sentillion, Inc. 2004
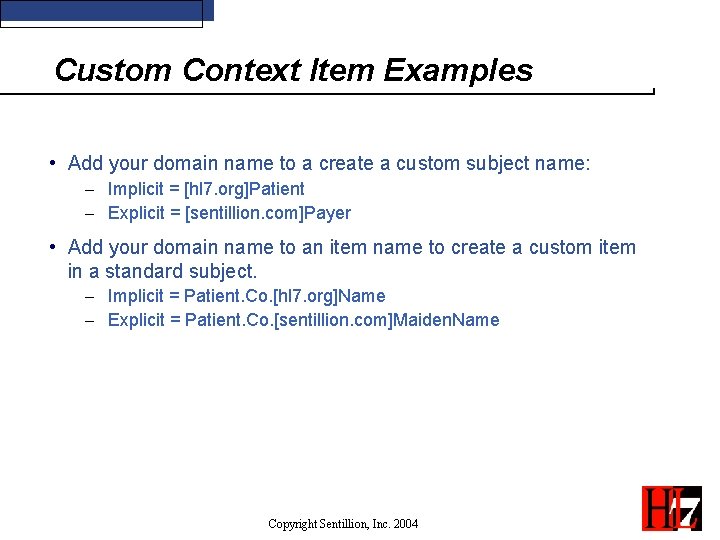
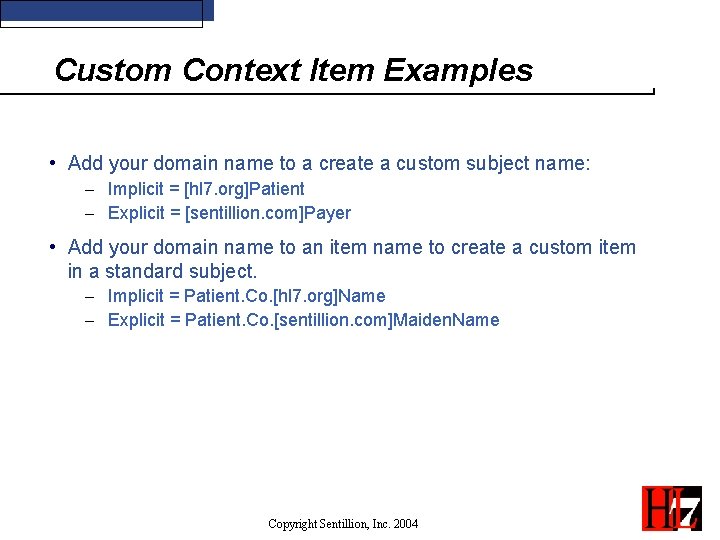
Custom Context Item Examples • Add your domain name to a create a custom subject name: - Implicit = [hl 7. org]Patient - Explicit = [sentillion. com]Payer • Add your domain name to an item name to create a custom item in a standard subject. - Implicit = Patient. Co. [hl 7. org]Name - Explicit = Patient. Co. [sentillion. com]Maiden. Name Copyright Sentillion, Inc. 2004
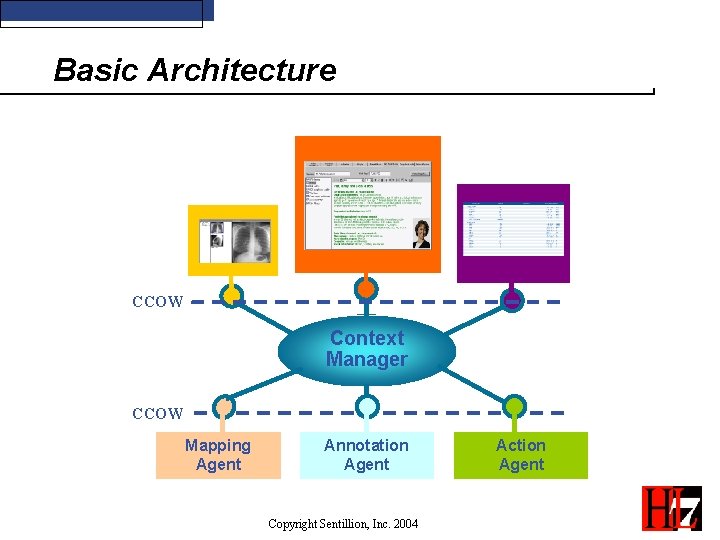
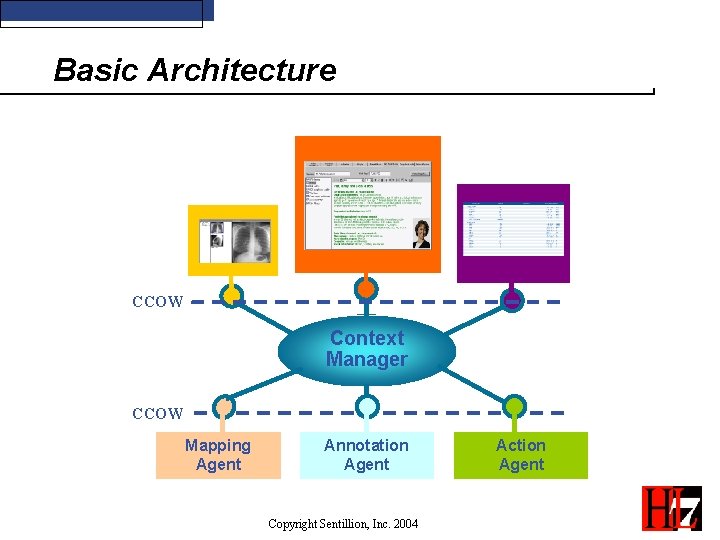
Basic Architecture CCOW Context Manager CCOW Mapping Agent Annotation Agent Copyright Sentillion, Inc. 2004 Action Agent
Key Components • Context Manager – Coordinator of context changes • Context Participant - Application that has “joined” the context • Agents – Provide supplemental data to the context - Mapping Agents: Provide identifier correlation, identifier synonyms - Annotation Agents: Provide additional data to an annotation subject. - Action Agents: Provide services for an action. Copyright Sentillion, Inc. 2004
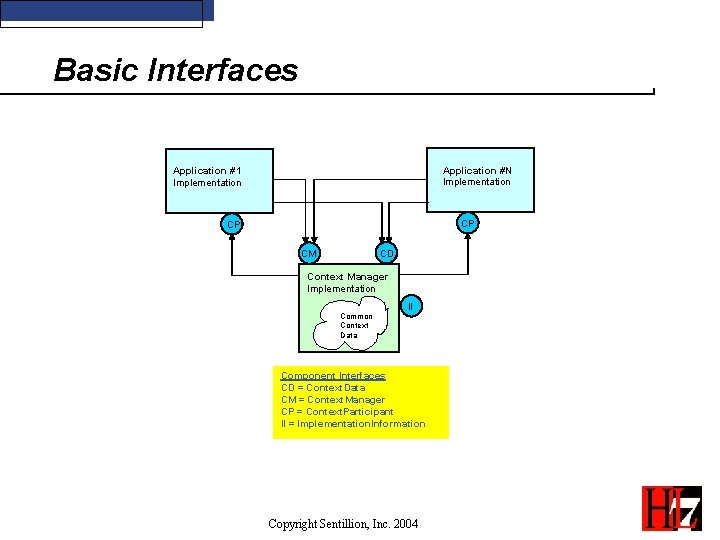
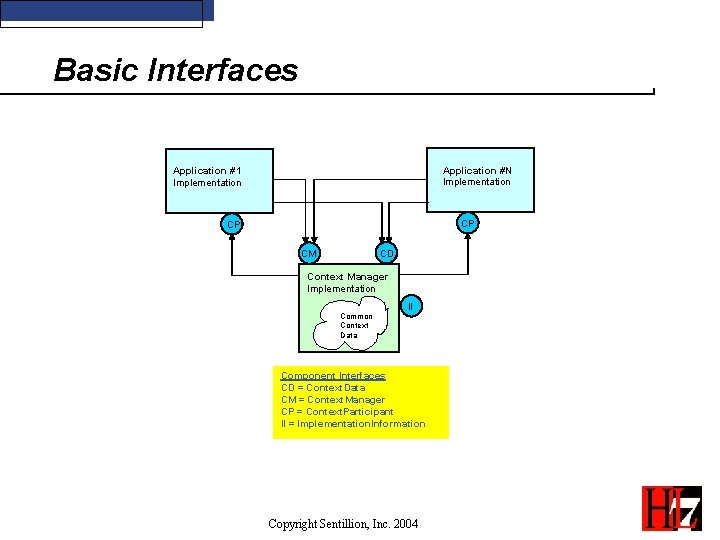
Basic Interfaces Application #N Implementation Application #1 Implementation CP CP CD CM Context Manager Implementation Common Context Data II Component Interfaces CD = Context. Data CM = Context. Manager CP = Context. Participant II = Implementation. Information Copyright Sentillion, Inc. 2004
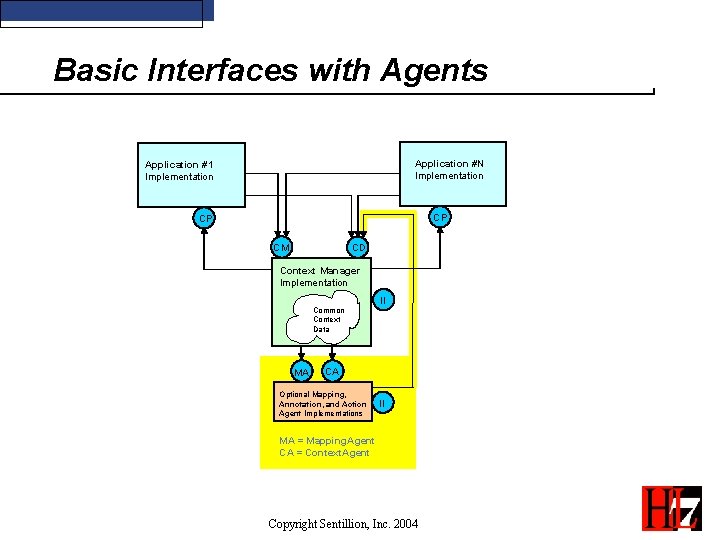
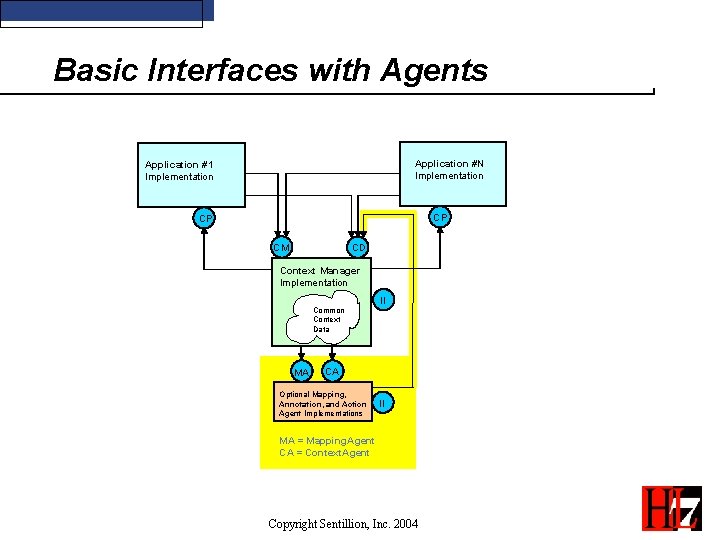
Basic Interfaces with Agents Application #N Implementation Application #1 Implementation CP CP CD CM Context Manager Implementation Common Context Data MA II CA Optional Mapping, Annotation, and Action Agent Implementations II MA = Mapping. Agent CA = Context. Agent Copyright Sentillion, Inc. 2004
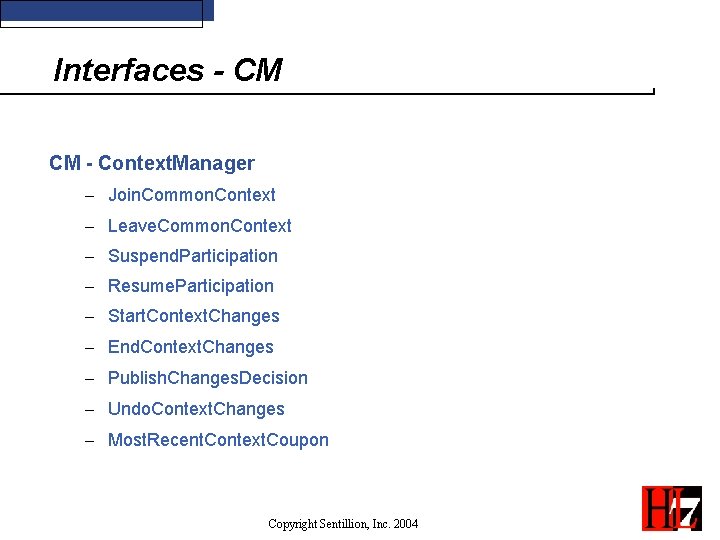
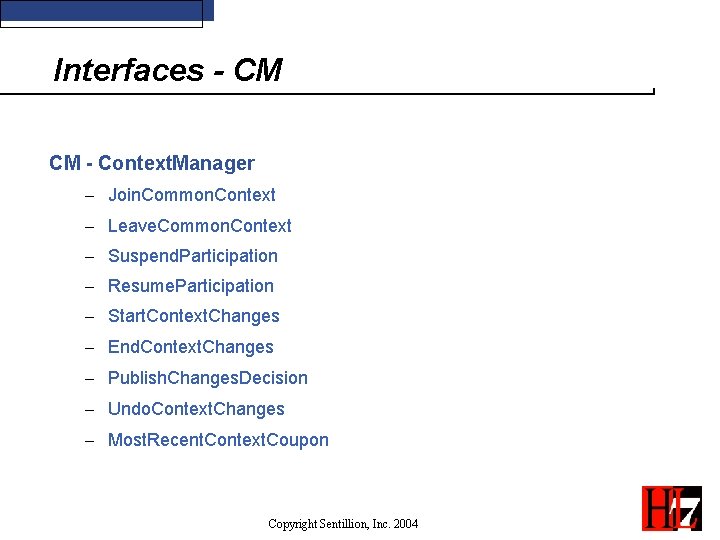
Interfaces - CM CM - Context. Manager - Join. Common. Context - Leave. Common. Context - Suspend. Participation - Resume. Participation - Start. Context. Changes - End. Context. Changes - Publish. Changes. Decision - Undo. Context. Changes - Most. Recent. Context. Coupon Copyright Sentillion, Inc. 2004
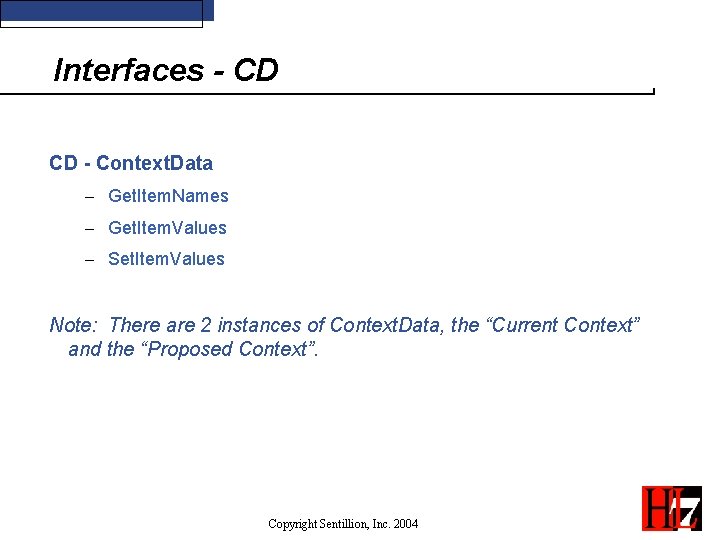
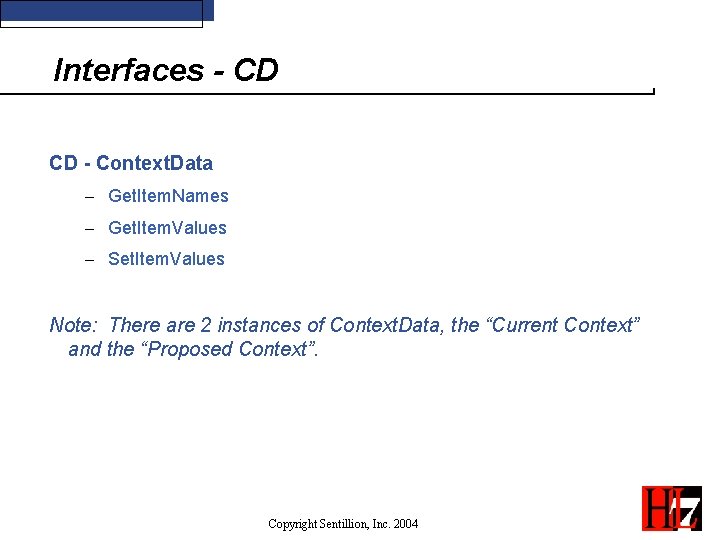
Interfaces - CD CD - Context. Data - Get. Item. Names - Get. Item. Values - Set. Item. Values Note: There are 2 instances of Context. Data, the “Current Context” and the “Proposed Context”. Copyright Sentillion, Inc. 2004
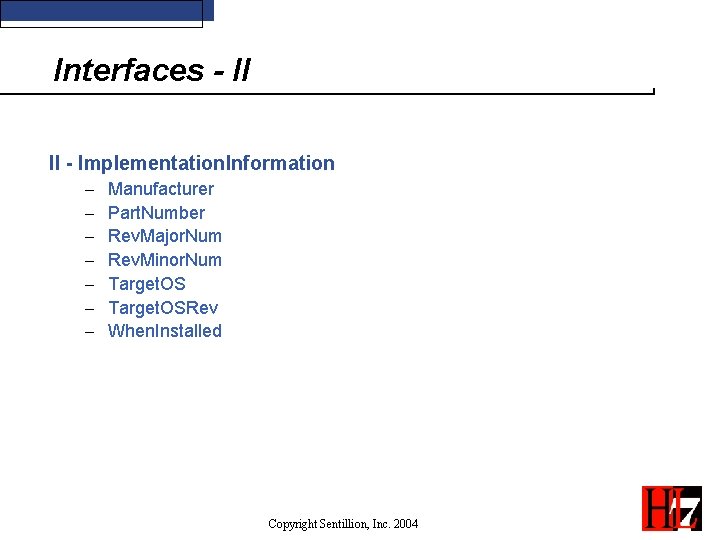
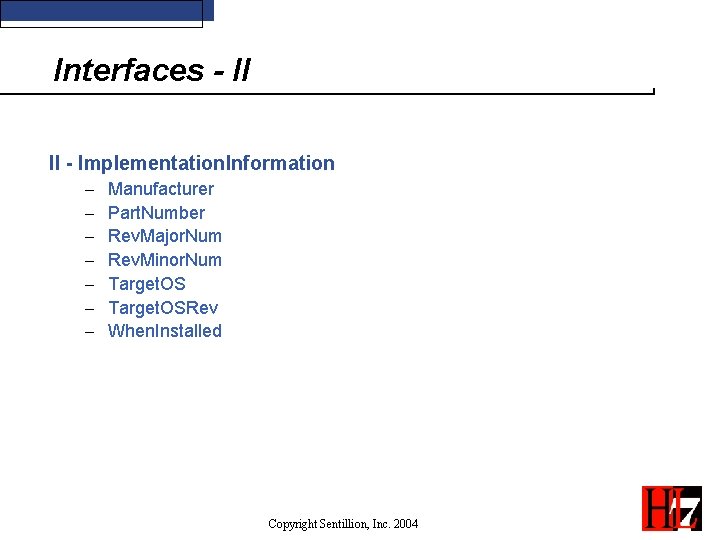
Interfaces - II II - Implementation. Information - Manufacturer Part. Number Rev. Major. Num Rev. Minor. Num Target. OSRev When. Installed Copyright Sentillion, Inc. 2004
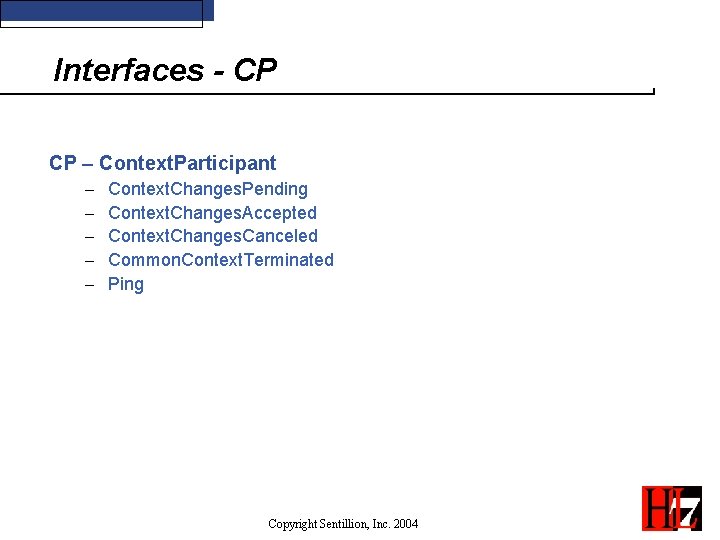
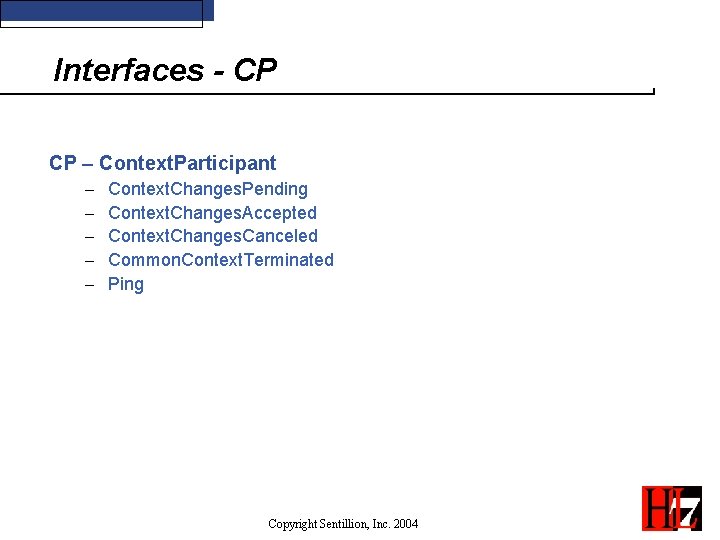
Interfaces - CP CP – Context. Participant - Context. Changes. Pending Context. Changes. Accepted Context. Changes. Canceled Common. Context. Terminated Ping Copyright Sentillion, Inc. 2004
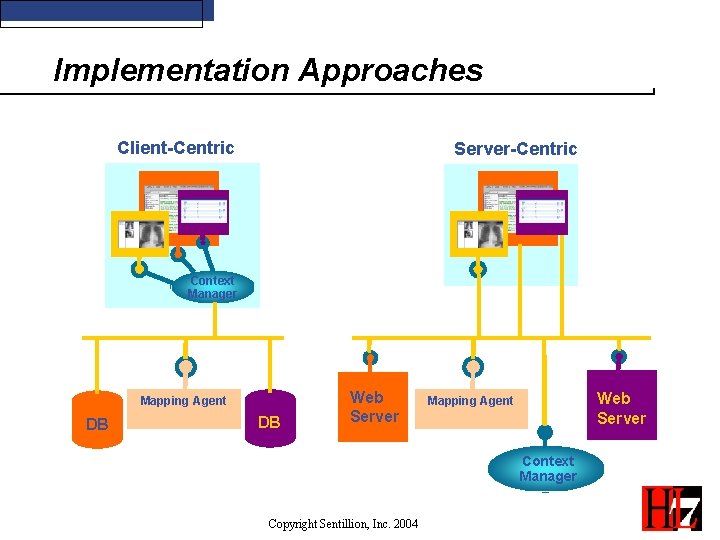
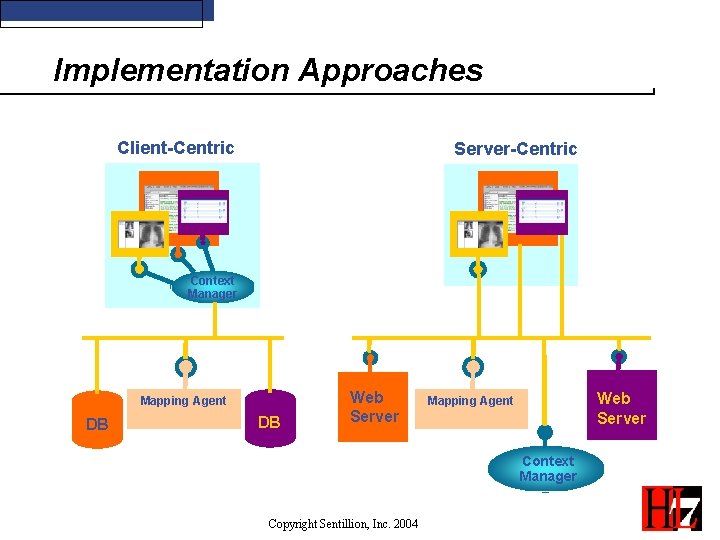
Implementation Approaches Client-Centric Server-Centric Context Manager Mapping Agent DB DB Web Server Mapping Agent Context Manager Copyright Sentillion, Inc. 2004
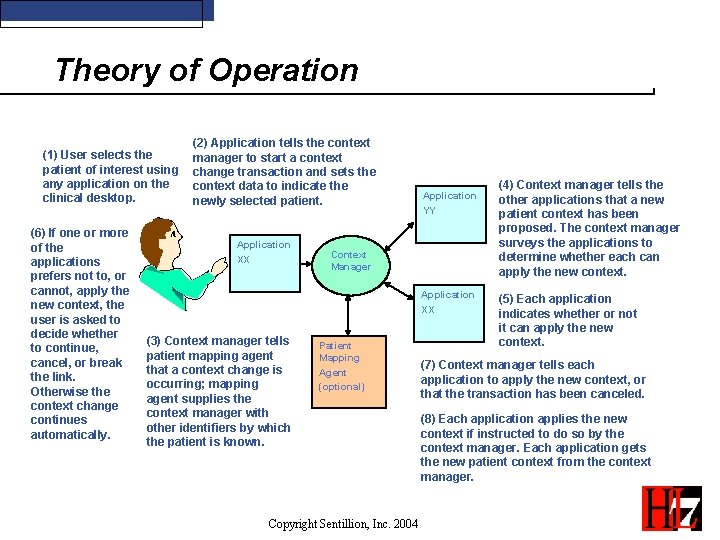
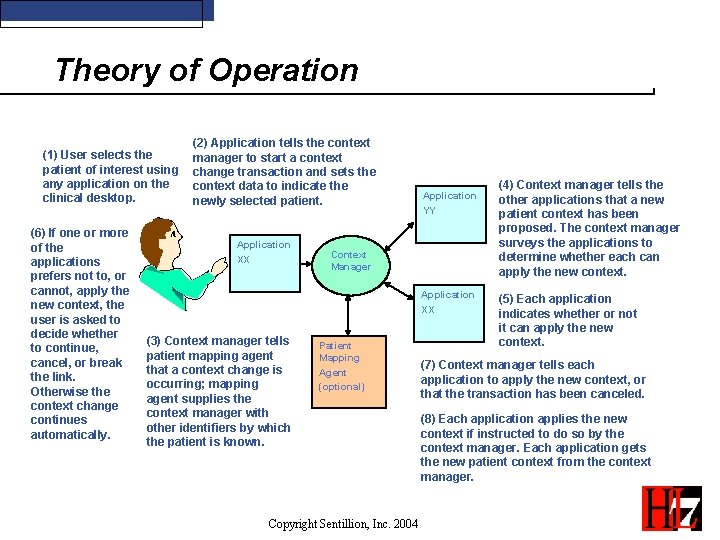
Theory of Operation (1) User selects the patient of interest using any application on the clinical desktop. (6) If one or more of the applications prefers not to, or cannot, apply the new context, the user is asked to decide whether to continue, cancel, or break the link. Otherwise the context change continues automatically. (2) Application tells the context manager to start a context change transaction and sets the context data to indicate the newly selected patient. Application XX Application YY Context Manager Application XX (3) Context manager tells patient mapping agent that a context change is occurring; mapping agent supplies the context manager with other identifiers by which the patient is known. Patient Mapping Agent (optional) Copyright Sentillion, Inc. 2004 (4) Context manager tells the other applications that a new patient context has been proposed. The context manager surveys the applications to determine whether each can apply the new context. (5) Each application indicates whether or not it can apply the new context. (7) Context manager tells each application to apply the new context, or that the transaction has been canceled. (8) Each application applies the new context if instructed to do so by the context manager. Each application gets the new patient context from the context manager.
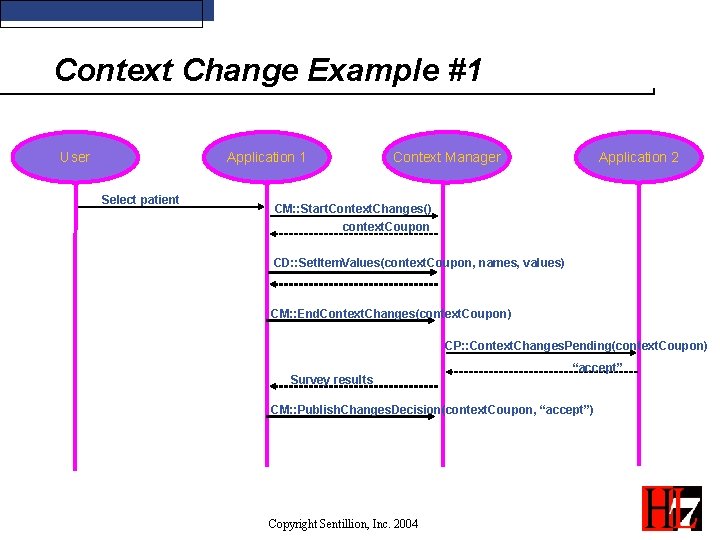
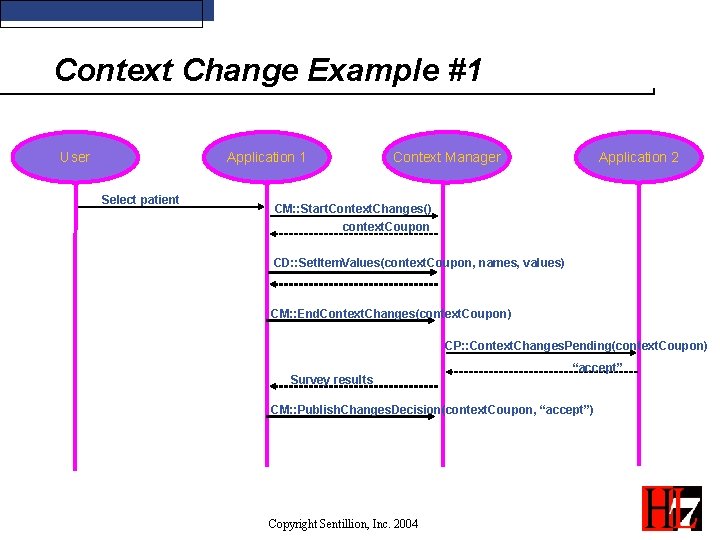
Context Change Example #1 User Application 1 Select patient Context Manager Application 2 CM: : Start. Context. Changes() context. Coupon CD: : Set. Item. Values(context. Coupon, names, values) CM: : End. Context. Changes(context. Coupon) CP: : Context. Changes. Pending(context. Coupon) Survey results “accept” CM: : Publish. Changes. Decision(context. Coupon, “accept”) Copyright Sentillion, Inc. 2004
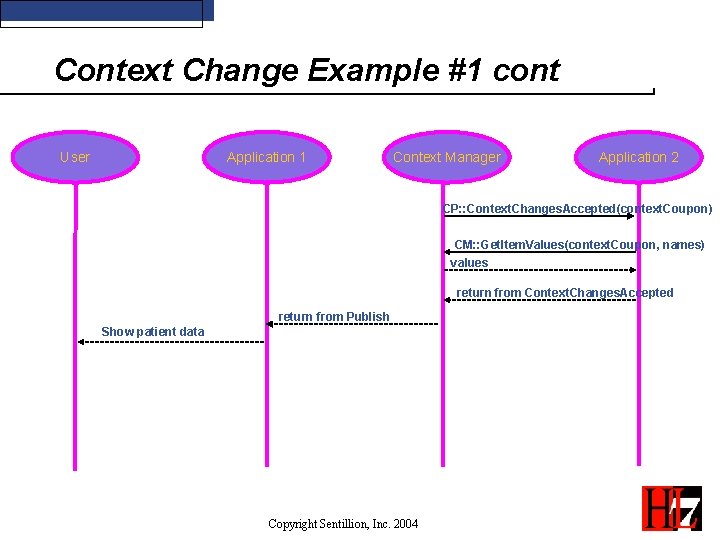
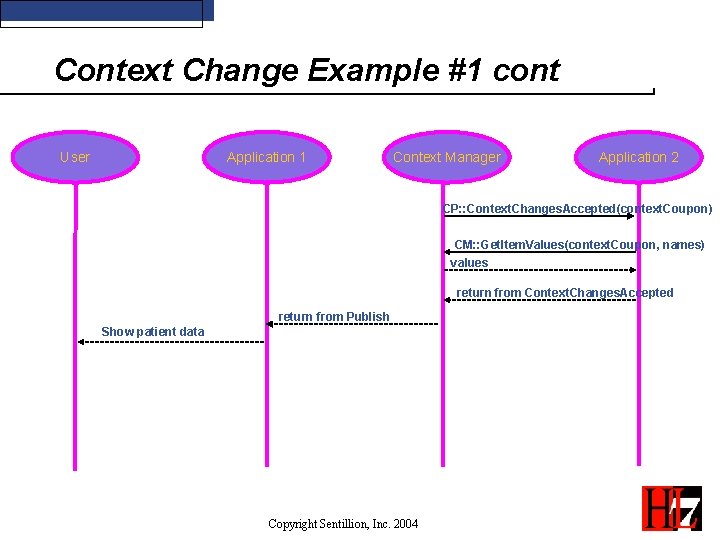
Context Change Example #1 cont User Application 1 Context Manager Application 2 CP: : Context. Changes. Accepted(context. Coupon) CM: : Get. Item. Values(context. Coupon, names) values return from Context. Changes. Accepted return from Publish Show patient data Copyright Sentillion, Inc. 2004
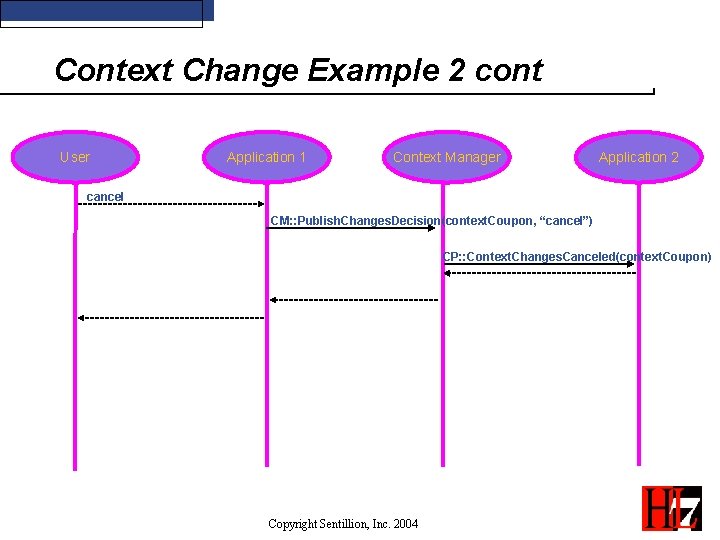
Another Ending… • User cancels context change Copyright Sentillion, Inc. 2004
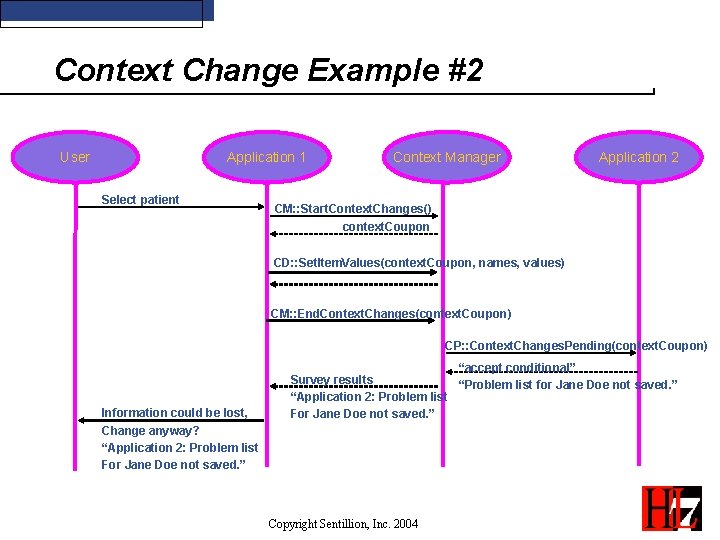
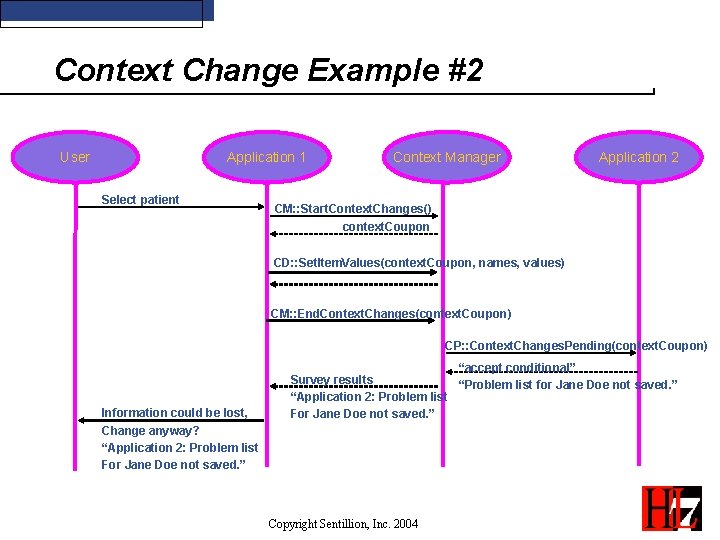
Context Change Example #2 User Application 1 Select patient Context Manager Application 2 CM: : Start. Context. Changes() context. Coupon CD: : Set. Item. Values(context. Coupon, names, values) CM: : End. Context. Changes(context. Coupon) CP: : Context. Changes. Pending(context. Coupon) Information could be lost, Change anyway? “Application 2: Problem list For Jane Doe not saved. ” “accept conditional” Survey results “Problem list for Jane Doe not saved. ” “Application 2: Problem list For Jane Doe not saved. ” Copyright Sentillion, Inc. 2004
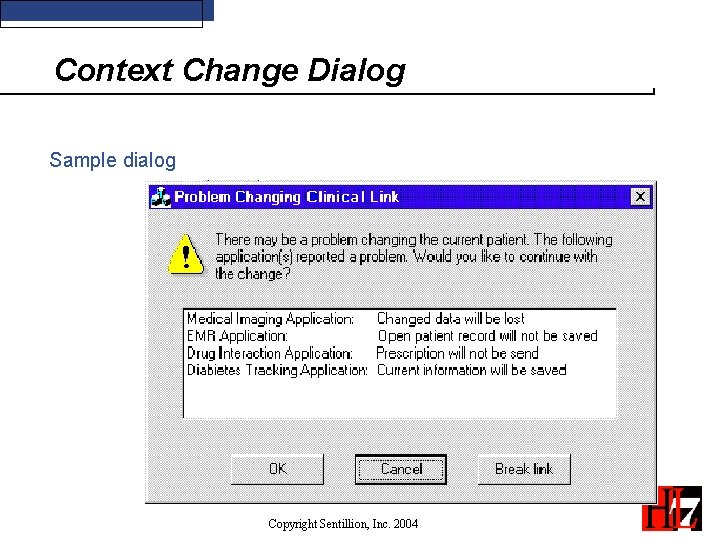
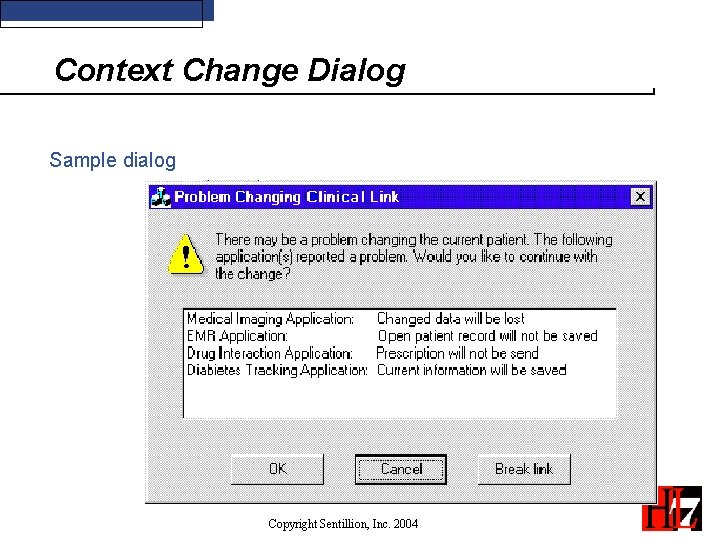
Context Change Dialog Sample dialog Copyright Sentillion, Inc. 2004
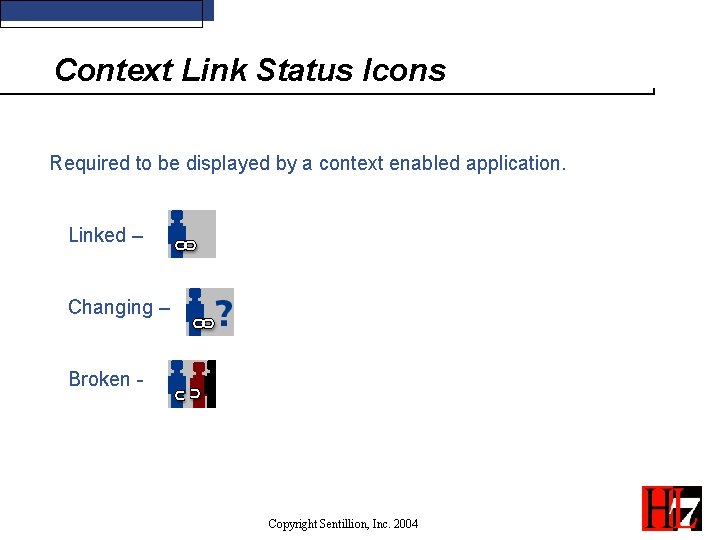
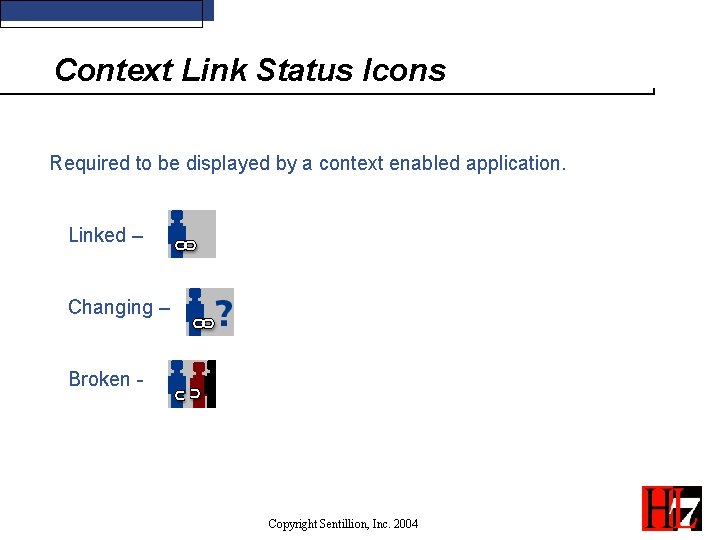
Context Link Status Icons Required to be displayed by a context enabled application. Linked – Changing – Broken - Copyright Sentillion, Inc. 2004
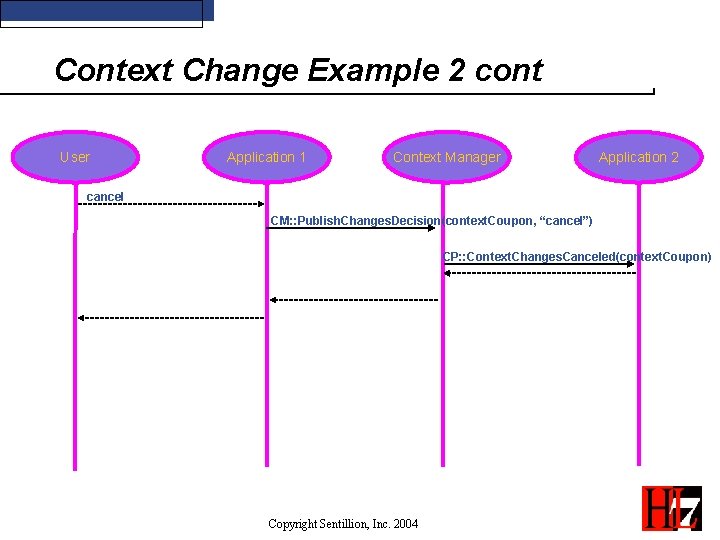
Context Change Example 2 cont User Application 1 Context Manager Application 2 cancel CM: : Publish. Changes. Decision(context. Coupon, “cancel”) CP: : Context. Changes. Canceled(context. Coupon) Copyright Sentillion, Inc. 2004
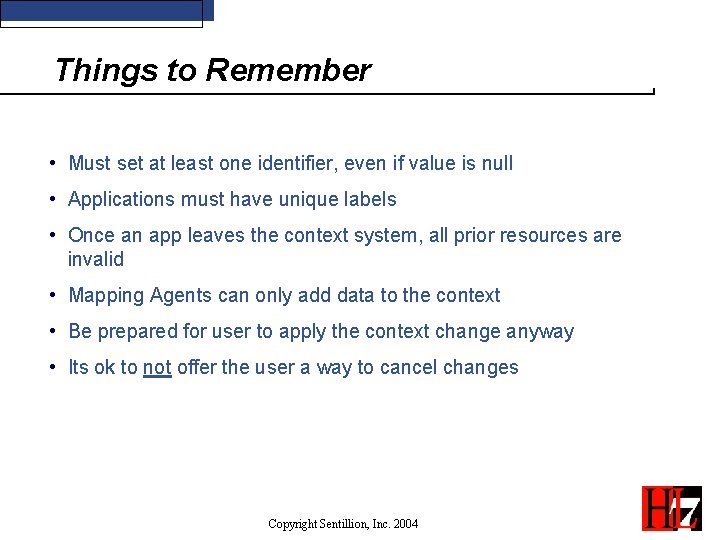
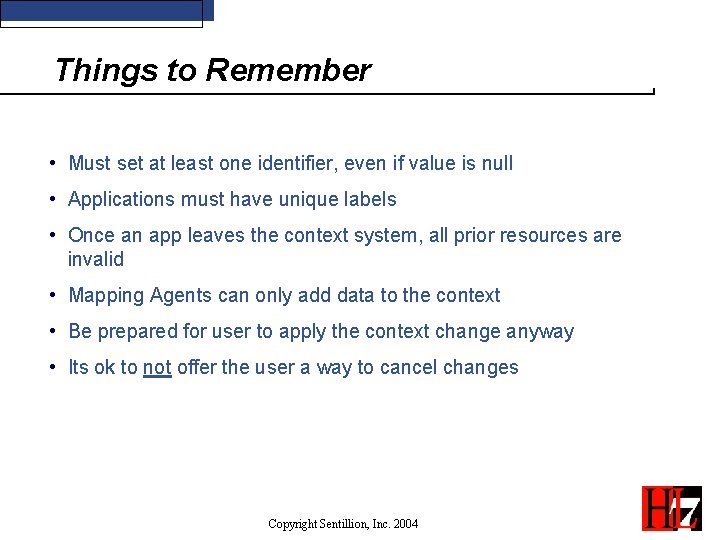
Things to Remember • Must set at least one identifier, even if value is null • Applications must have unique labels • Once an app leaves the context system, all prior resources are invalid • Mapping Agents can only add data to the context • Be prepared for user to apply the context change anyway • Its ok to not offer the user a way to cancel changes Copyright Sentillion, Inc. 2004
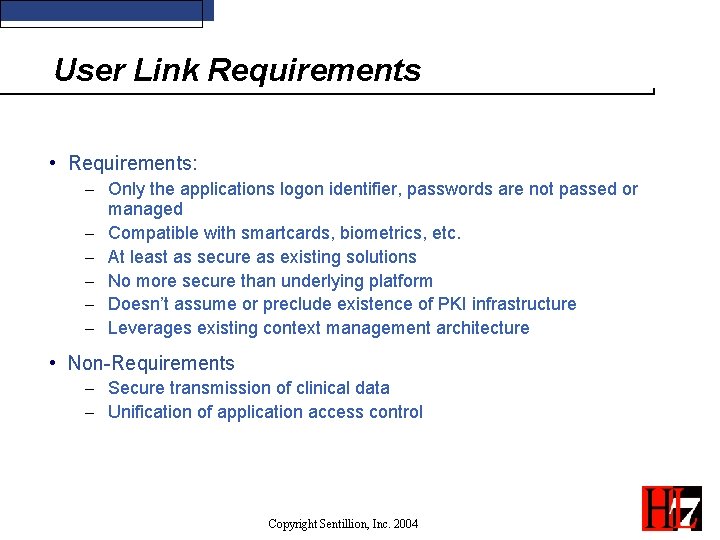
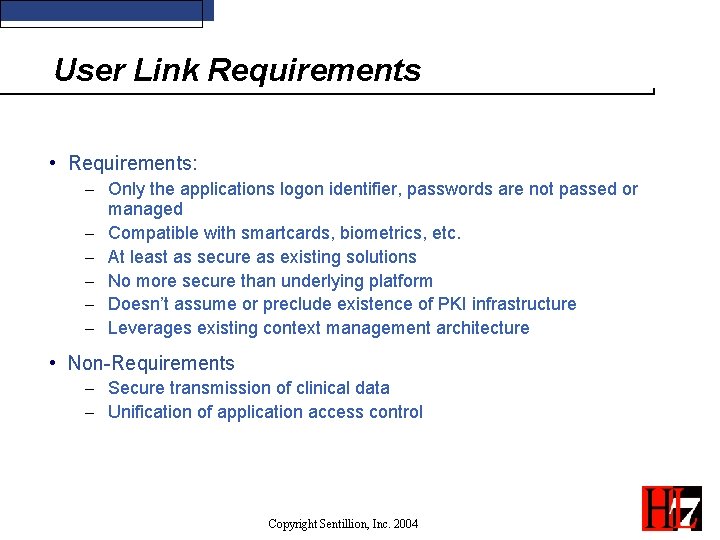
User Link Requirements • Requirements: - Only the applications logon identifier, passwords are not passed or managed - Compatible with smartcards, biometrics, etc. - At least as secure as existing solutions - No more secure than underlying platform - Doesn’t assume or preclude existence of PKI infrastructure - Leverages existing context management architecture • Non-Requirements - Secure transmission of clinical data - Unification of application access control Copyright Sentillion, Inc. 2004
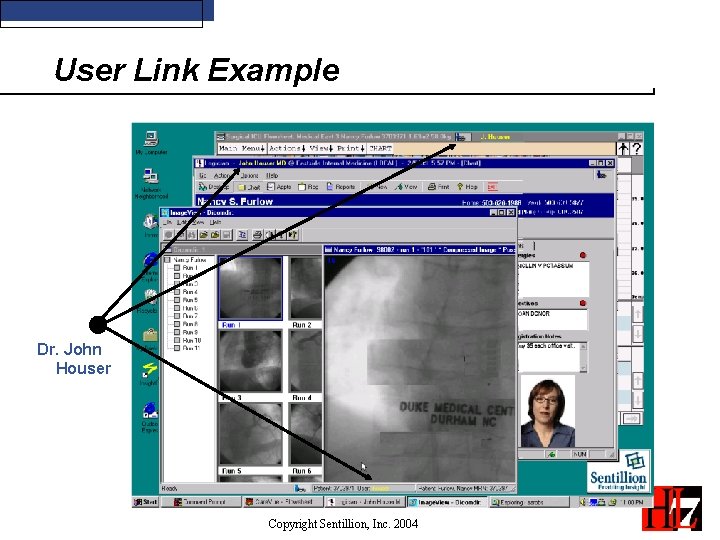
User Link Example Dr. John Houser Copyright Sentillion, Inc. 2004
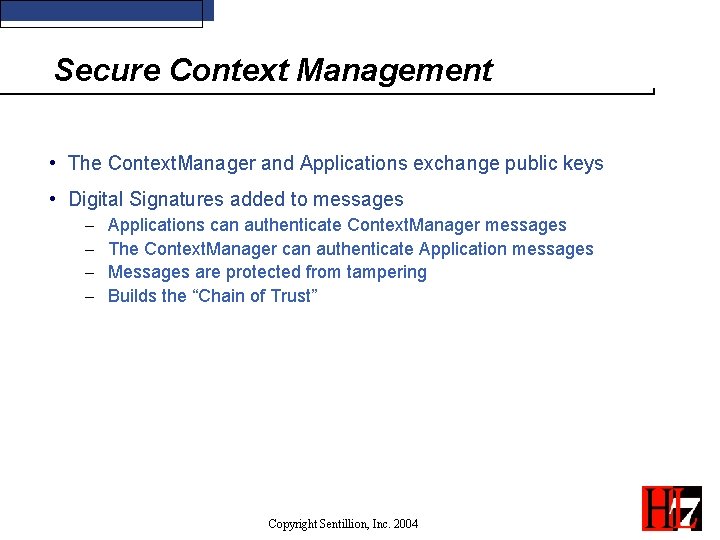
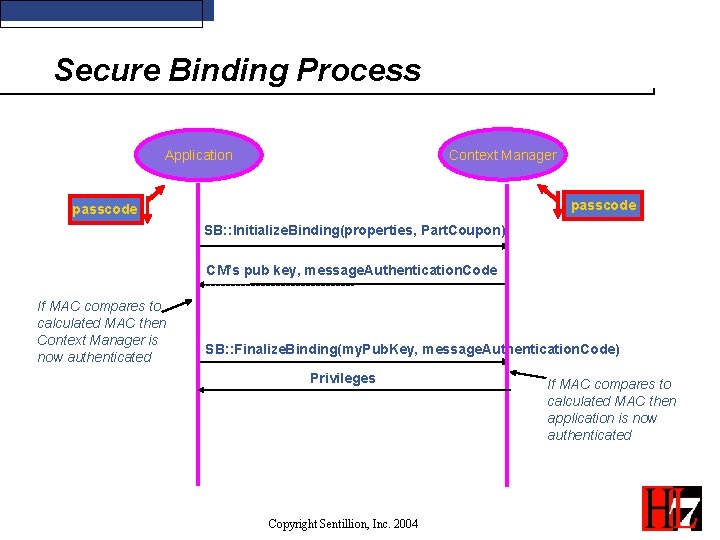
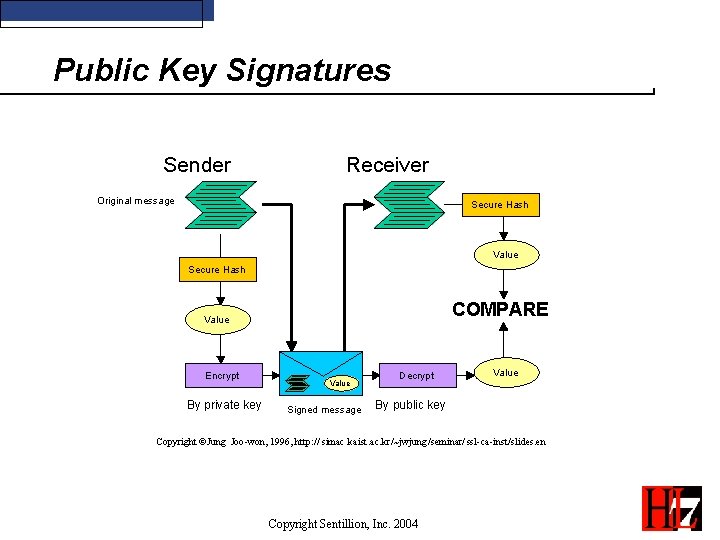
Secure Context Management • The Context. Manager and Applications exchange public keys • Digital Signatures added to messages - Applications can authenticate Context. Manager messages The Context. Manager can authenticate Application messages Messages are protected from tampering Builds the “Chain of Trust” Copyright Sentillion, Inc. 2004
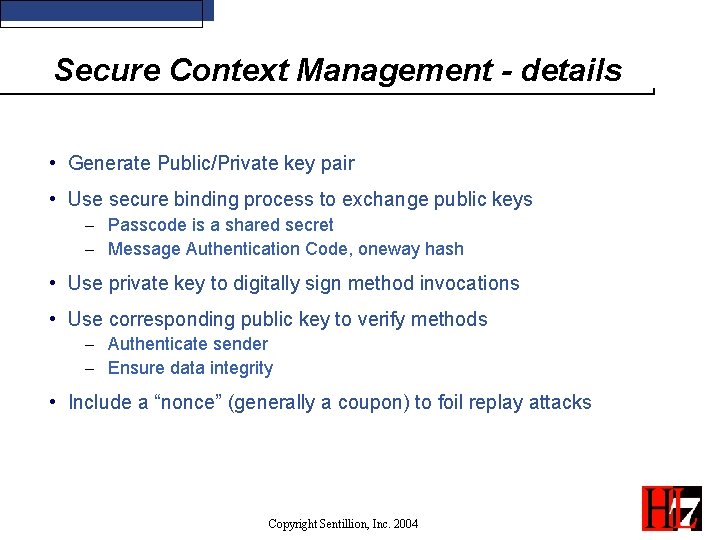
Secure Context Management - details • Generate Public/Private key pair • Use secure binding process to exchange public keys - Passcode is a shared secret - Message Authentication Code, oneway hash • Use private key to digitally sign method invocations • Use corresponding public key to verify methods - Authenticate sender - Ensure data integrity • Include a “nonce” (generally a coupon) to foil replay attacks Copyright Sentillion, Inc. 2004
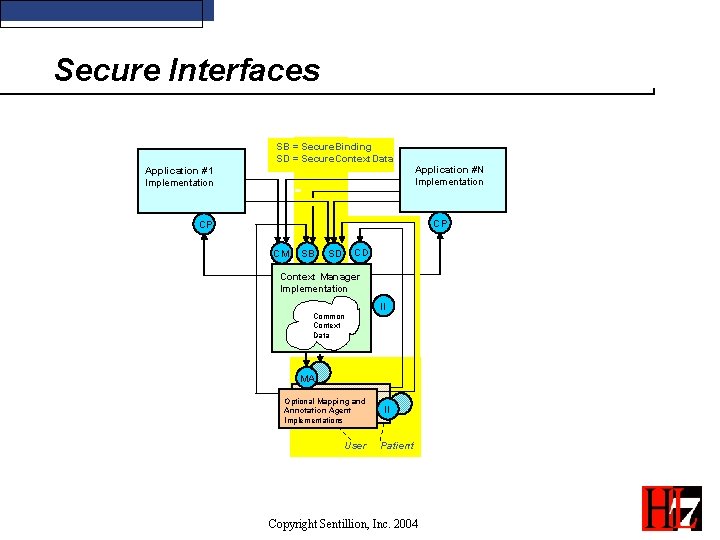
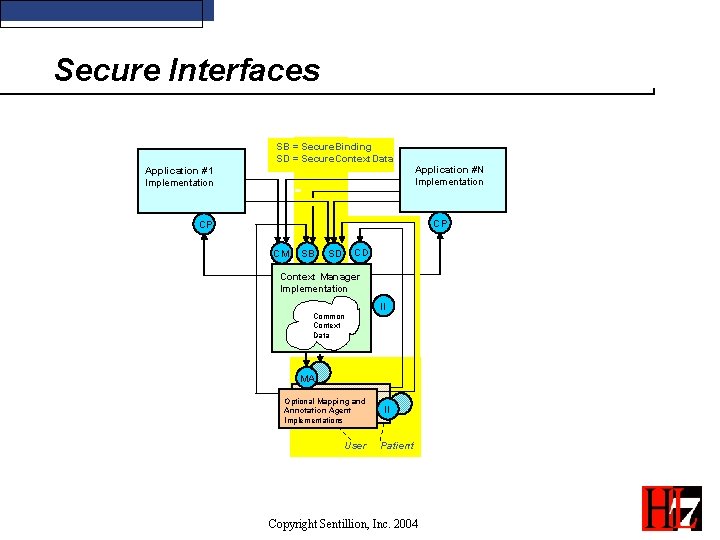
Secure Interfaces SB = Secure. Binding SD = Secure. Context. Data Application #N Implementation Application #1 Implementation CP CP CM SB CD SD Context Manager Implementation Common Context Data II MA Optional Mapping and Annotation Agent Implementations User II Patient Copyright Sentillion, Inc. 2004
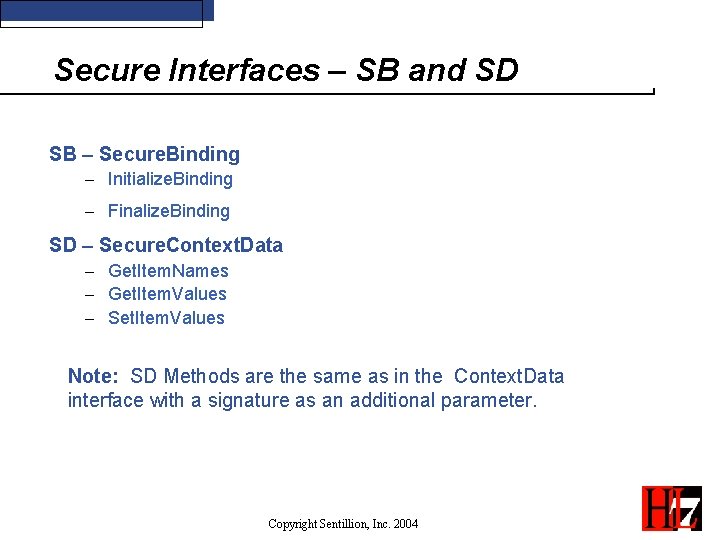
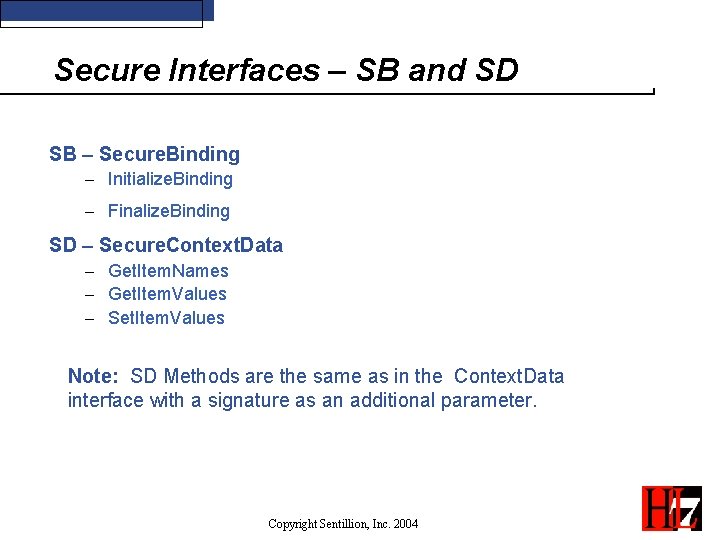
Secure Interfaces – SB and SD SB – Secure. Binding - Initialize. Binding - Finalize. Binding SD – Secure. Context. Data - Get. Item. Names - Get. Item. Values - Set. Item. Values Note: SD Methods are the same as in the Context. Data interface with a signature as an additional parameter. Copyright Sentillion, Inc. 2004
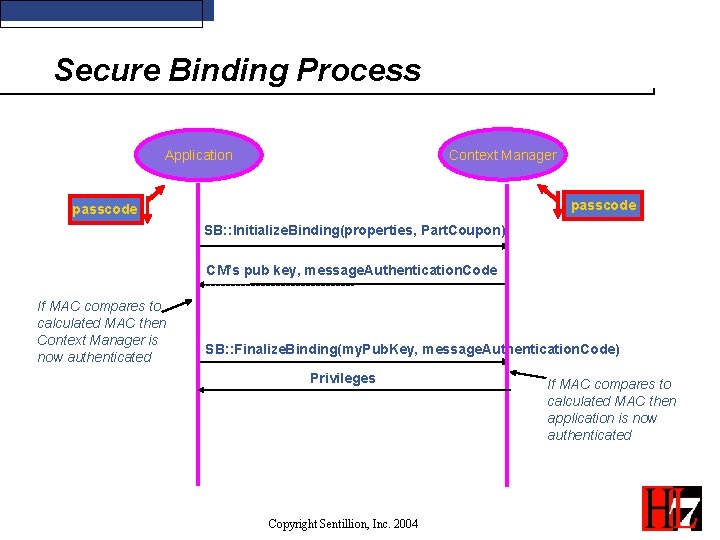
Secure Binding Process Context Manager Application passcode SB: : Initialize. Binding(properties, Part. Coupon) CM’s pub key, message. Authentication. Code If MAC compares to calculated MAC then Context Manager is now authenticated SB: : Finalize. Binding(my. Pub. Key, message. Authentication. Code) Privileges Copyright Sentillion, Inc. 2004 If MAC compares to calculated MAC then application is now authenticated
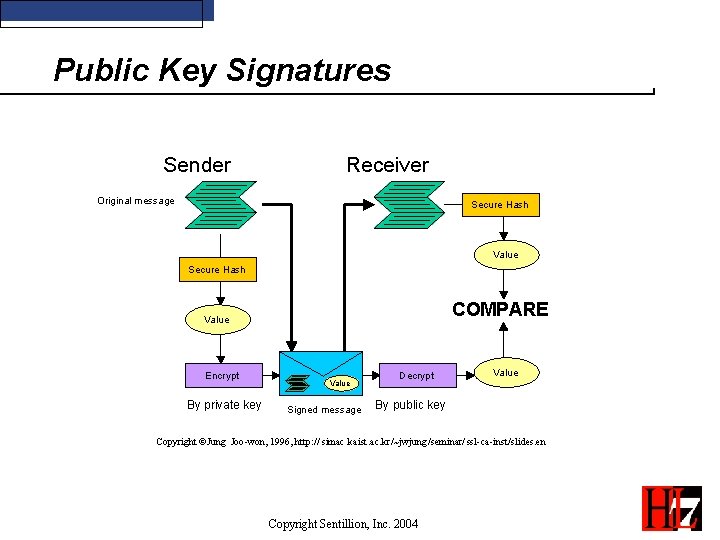
Public Key Signatures Sender Receiver Original message Secure Hash Value Secure Hash COMPARE Value Encrypt By private key Value Signed message Decrypt Value By public key Copyright ©Jung Joo-won, 1996, http: // simac. kaist. ac. kr/~jwjung/seminar/ ssl-ca-inst/slides. en Copyright Sentillion, Inc. 2004
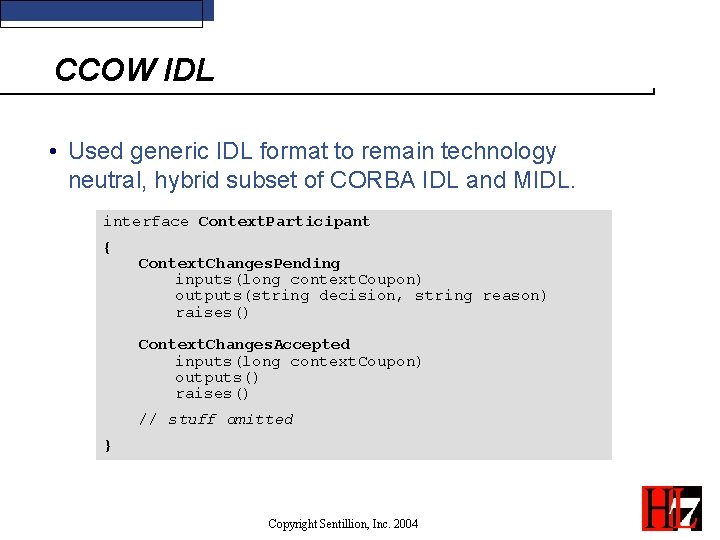
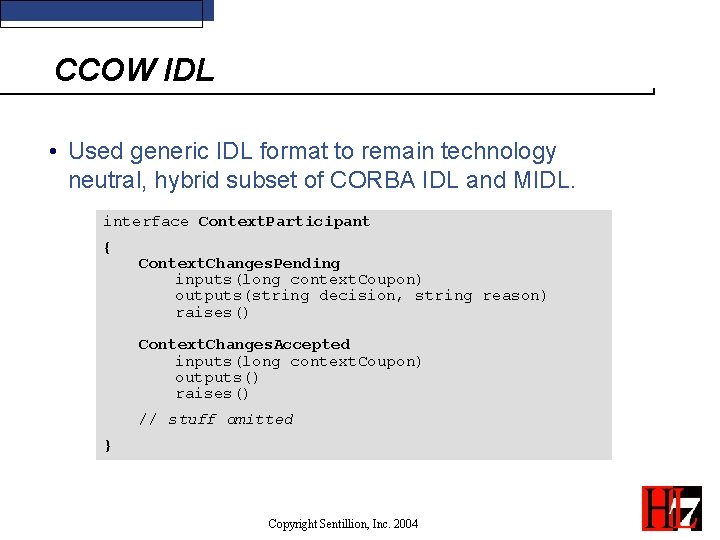
CCOW IDL • Used generic IDL format to remain technology neutral, hybrid subset of CORBA IDL and MIDL. interface Context. Participant { Context. Changes. Pending inputs(long context. Coupon) outputs(string decision, string reason) raises() Context. Changes. Accepted inputs(long context. Coupon) outputs() raises() // stuff omitted } Copyright Sentillion, Inc. 2004
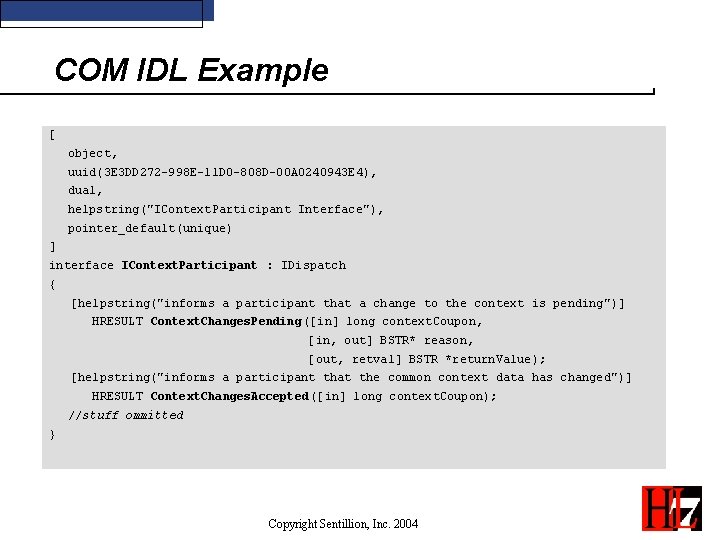
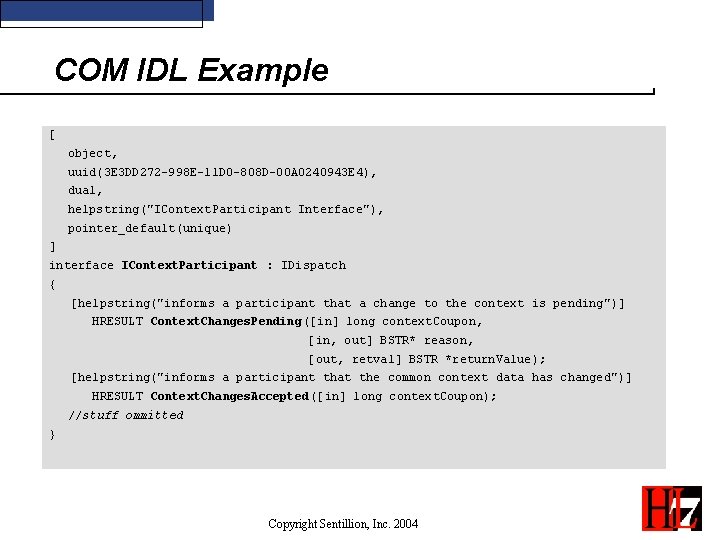
COM IDL Example [ object, uuid(3 E 3 DD 272 -998 E-11 D 0 -808 D-00 A 0240943 E 4), dual, helpstring("IContext. Participant Interface"), pointer_default(unique) ] interface IContext. Participant : IDispatch { [helpstring("informs a participant that a change to the context is pending")] HRESULT Context. Changes. Pending([in] long context. Coupon, [in, out] BSTR* reason, [out, retval] BSTR *return. Value); [helpstring("informs a participant that the common context data has changed")] HRESULT Context. Changes. Accepted([in] long context. Coupon); //stuff ommitted } Copyright Sentillion, Inc. 2004
COM Components • COM component prog ids in the Windows Registry: - CCOW. Context. Manager - CCOW. Mapping. Agent_[subject] - Ex: CCOW. Mapping. Agent_Patient - CCOW. Annotation. Agent_[subject] - Ex: CCOW. Mapping. Agent_Certificate - CCOW. Action. Agent_[subject] (version 1. 4) - Ex: CCOW. Action. Agent_Authenticate Copyright Sentillion, Inc. 2004
Web IDL Mapping • Encoded URL Example: http: //app. Address. com? interface=Context. Participant&method=Context Changes. Pending&context. Coupon=42 Copyright Sentillion, Inc. 2004
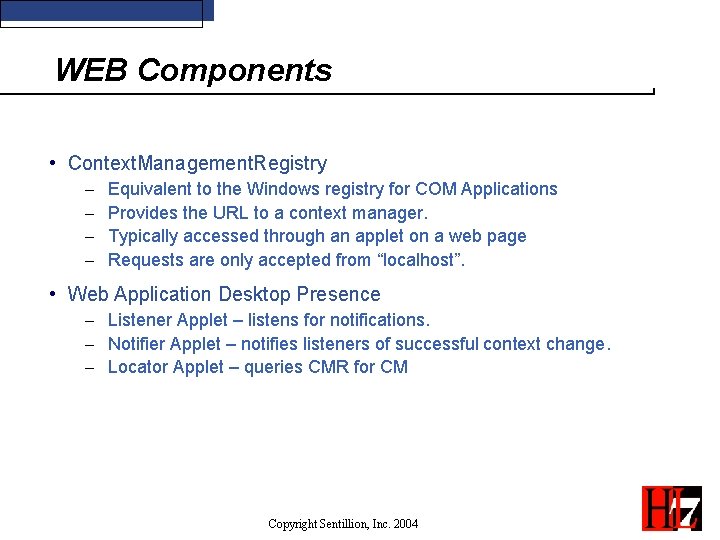
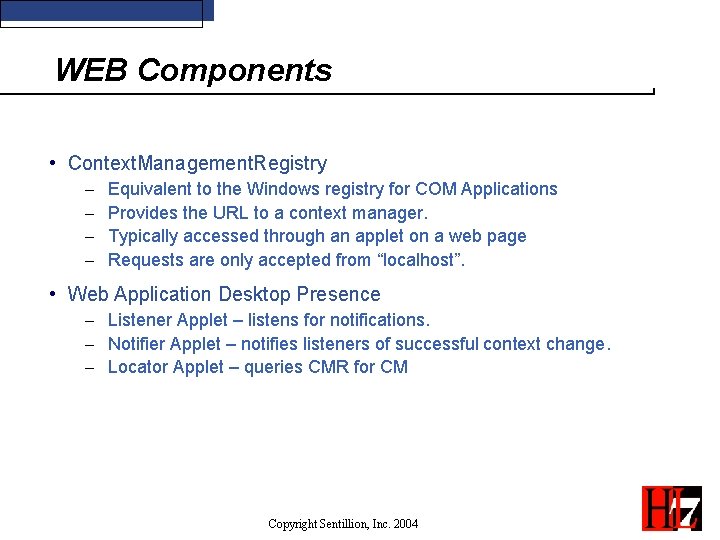
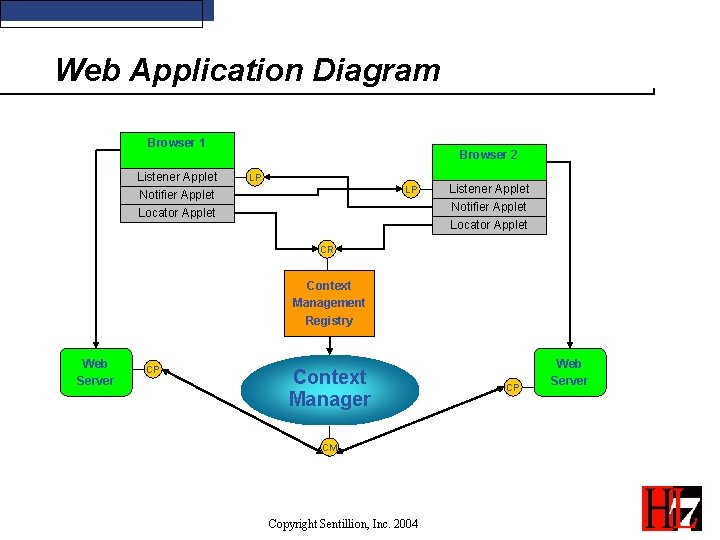
WEB Components • Context. Management. Registry - Equivalent to the Windows registry for COM Applications Provides the URL to a context manager. Typically accessed through an applet on a web page Requests are only accepted from “localhost”. • Web Application Desktop Presence - Listener Applet – listens for notifications. - Notifier Applet – notifies listeners of successful context change. - Locator Applet – queries CMR for CM Copyright Sentillion, Inc. 2004
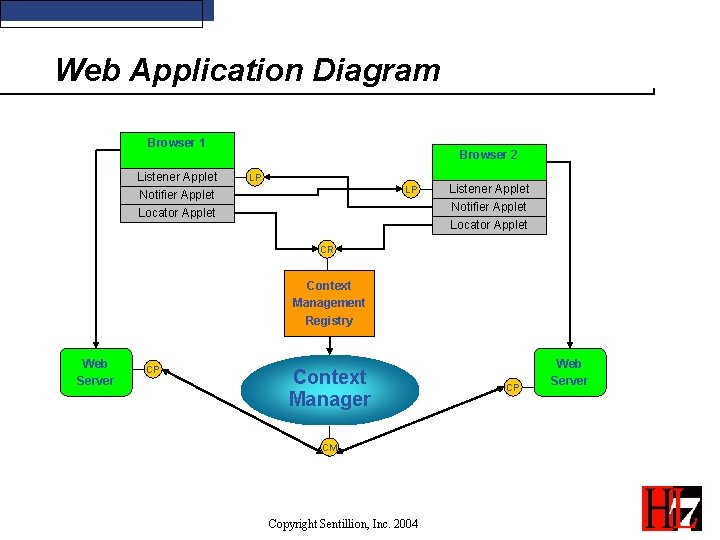
Web Application Diagram Browser 1 Listener Applet Notifier Applet Locator Applet Browser 2 LP LP Listener Applet Notifier Applet Locator Applet CR Context Management Registry Web Server CP Context Manager CM Copyright Sentillion, Inc. 2004 CP Web Server
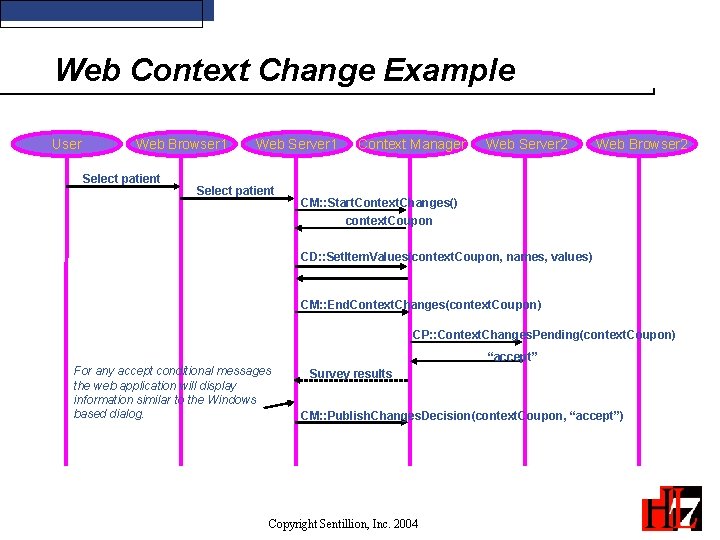
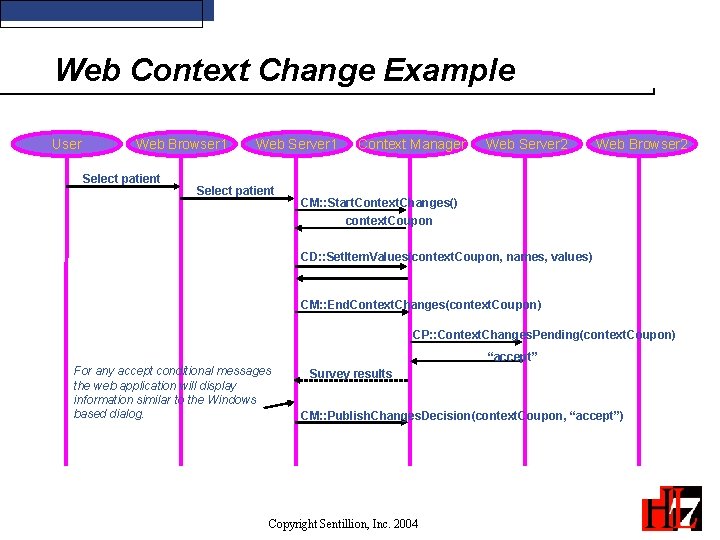
Web Context Change Example User Web Browser 1 Select patient Web Server 1 Select patient Context Manager Web Server 2 Web Browser 2 CM: : Start. Context. Changes() context. Coupon CD: : Set. Item. Values(context. Coupon, names, values) CM: : End. Context. Changes(context. Coupon) CP: : Context. Changes. Pending(context. Coupon) “accept” For any accept conditional messages the web application will display information similar to the Windows based dialog. Survey results CM: : Publish. Changes. Decision(context. Coupon, “accept”) Copyright Sentillion, Inc. 2004
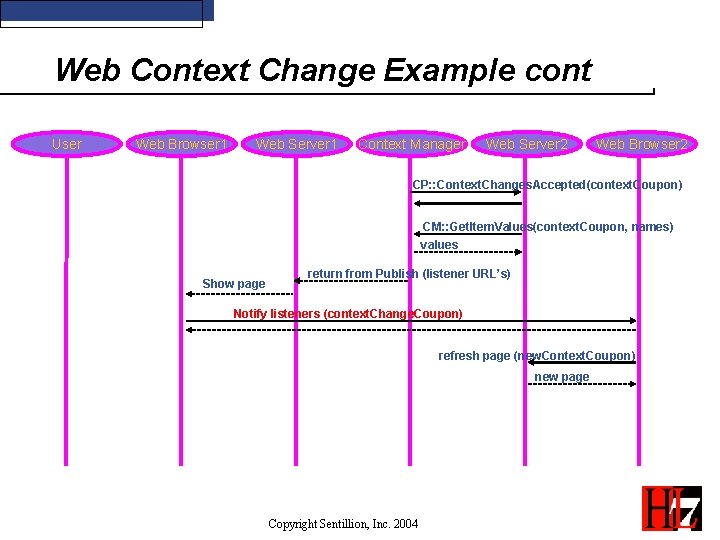
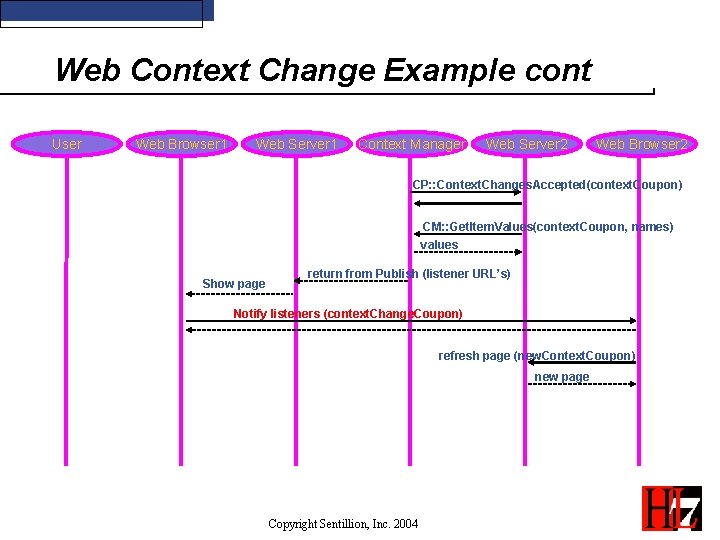
Web Context Change Example cont User Web Browser 1 Web Server 1 Context Manager Web Server 2 Web Browser 2 CP: : Context. Changes. Accepted(context. Coupon) CM: : Get. Item. Values(context. Coupon, names) values Show page return from Publish (listener URL’s) Notify listeners (context. Change. Coupon) refresh page (new. Context. Coupon) new page Copyright Sentillion, Inc. 2004
Context Actions Overview • A Context Action is a request by one application for another application to perform a context sensitive action, e. g. reauthenticate the user. • The Context. Manager brokers the communication. • Actions do not set the context data. No other participant is informed of the Action. • The instigator receives the action response as return values. • Actions are implemented by Action Agents and use the same interface definitions as Mapping and Annotation Agents. Copyright Sentillion, Inc. 2004
Context Actions Design Goal • Reuse existing CCOW infrastructure • Support thin client computing devices • Actions may require user input, determined at runtime • Must support both COM and Web technology mappings • Must support security • Must allow for mapping of both inputs and outputs • Anonymity between action requestor and action implementer. Copyright Sentillion, Inc. 2004
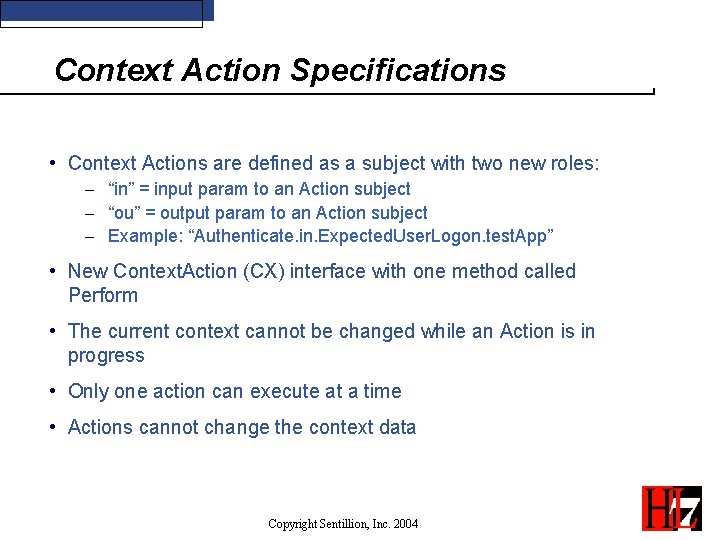
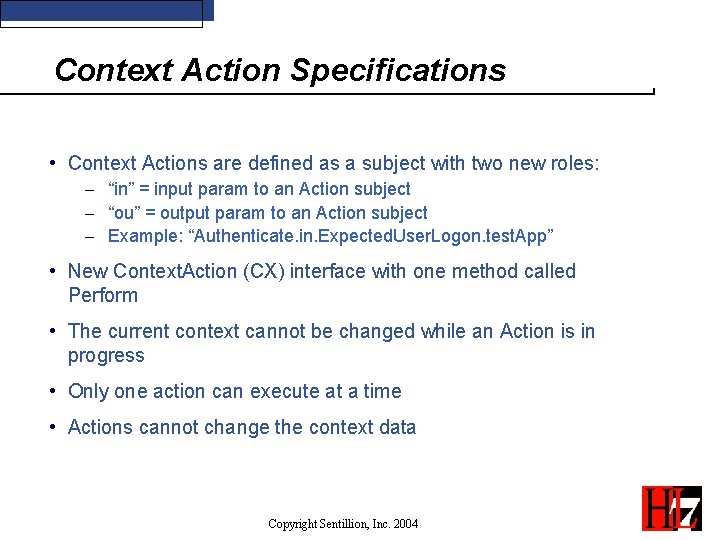
Context Action Specifications • Context Actions are defined as a subject with two new roles: - “in” = input param to an Action subject - “ou” = output param to an Action subject - Example: “Authenticate. in. Expected. User. Logon. test. App” • New Context. Action (CX) interface with one method called Perform • The current context cannot be changed while an Action is in progress • Only one action can execute at a time • Actions cannot change the context data Copyright Sentillion, Inc. 2004
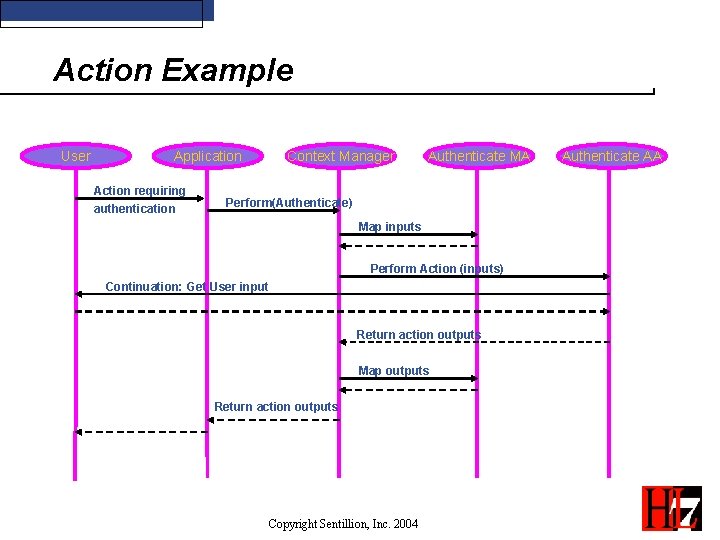
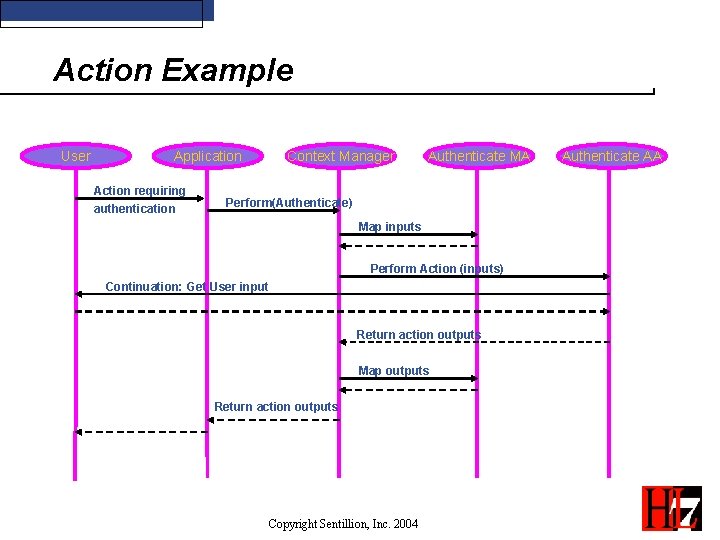
Action Example User Application Action requiring authentication Context Manager Authenticate MA Perform(Authenticate) Map inputs Perform Action (inputs) Continuation: Get User input Return action outputs Map outputs Return action outputs Copyright Sentillion, Inc. 2004 Authenticate AA
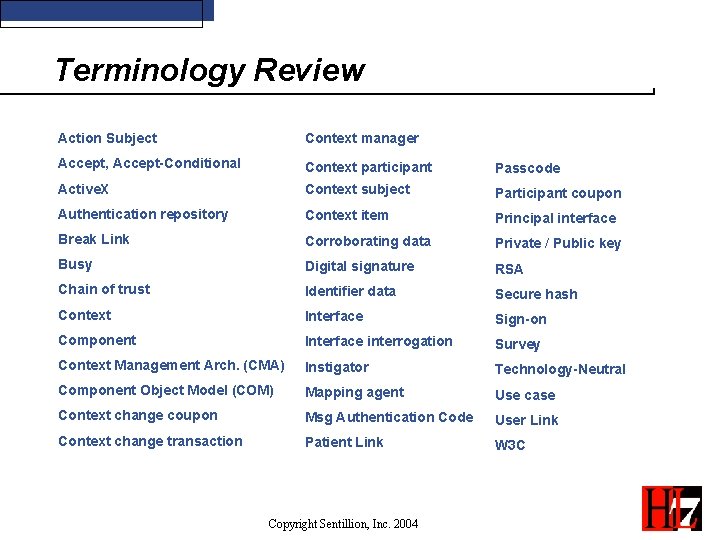
Terminology Review Action Subject Context manager Accept, Accept-Conditional Context participant Passcode Active. X Context subject Participant coupon Authentication repository Context item Principal interface Break Link Corroborating data Private / Public key Busy Digital signature RSA Chain of trust Identifier data Secure hash Context Interface Sign-on Component Interface interrogation Survey Context Management Arch. (CMA) Instigator Technology-Neutral Component Object Model (COM) Mapping agent Use case Context change coupon Msg Authentication Code User Link Context change transaction Patient Link W 3 C Copyright Sentillion, Inc. 2004
More HL 7 CCOW Information • Web Sites: - www. hl 7. org - www. sentillion. com • List server - Ccow@lists. hl 7. org (see HL 7 web site to join) • Co-Chairs - Robert Seliger, Sentillion, robs@sentillion. com - Barry Royer, Siemens, barry. royer@smed. com - Michael Russel MD, russe 004@mc. duke. edu Copyright Sentillion, Inc. 2004