Assembly Language for IntelBased Computers 4 th Edition
Assembly Language for Intel-Based Computers, 4 th Edition Kip R. Irvine Chapter 2: IA-32 Processor Architecture Slides prepared by Kip R. Irvine Revision date: 09/25/2002 • Chapter corrections (Web) Assembly language sources (Web) • Printing a slide show (c) Pearson Education, 2002. All rights reserved. You may modify and copy this slide show for your personal use, or for use in the classroom, as long as this copyright statement, the author's name, and the title are not changed.
Chapter Overview • General Concepts • IA-32 Processor Architecture • IA-32 Memory Management Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 2
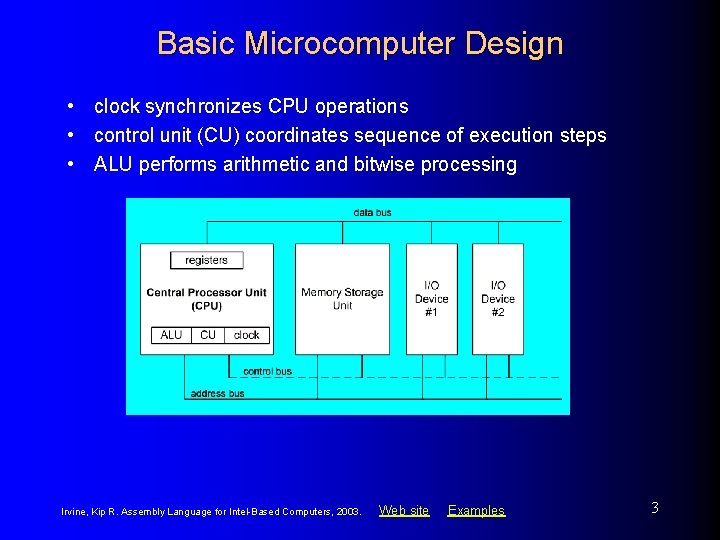
Basic Microcomputer Design • clock synchronizes CPU operations • control unit (CU) coordinates sequence of execution steps • ALU performs arithmetic and bitwise processing Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 3
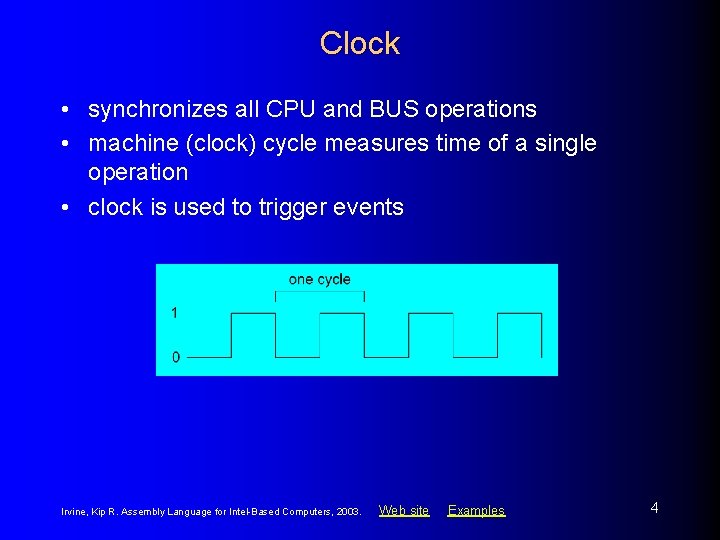
Clock • synchronizes all CPU and BUS operations • machine (clock) cycle measures time of a single operation • clock is used to trigger events Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 4
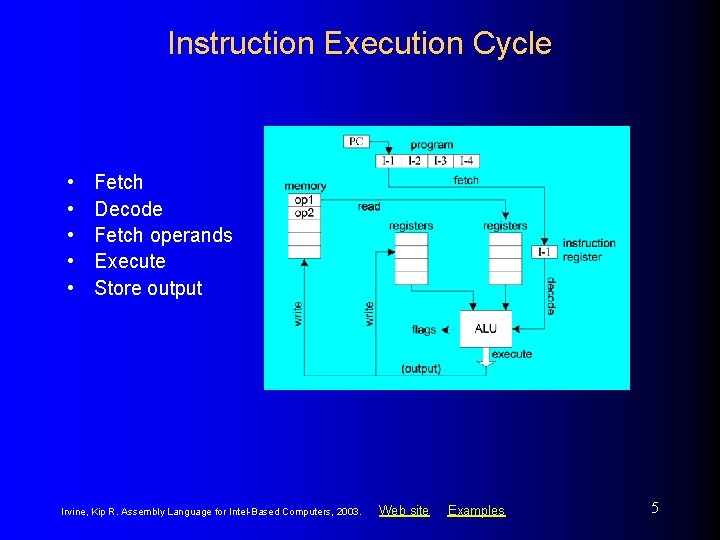
Instruction Execution Cycle • • • Fetch Decode Fetch operands Execute Store output Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 5
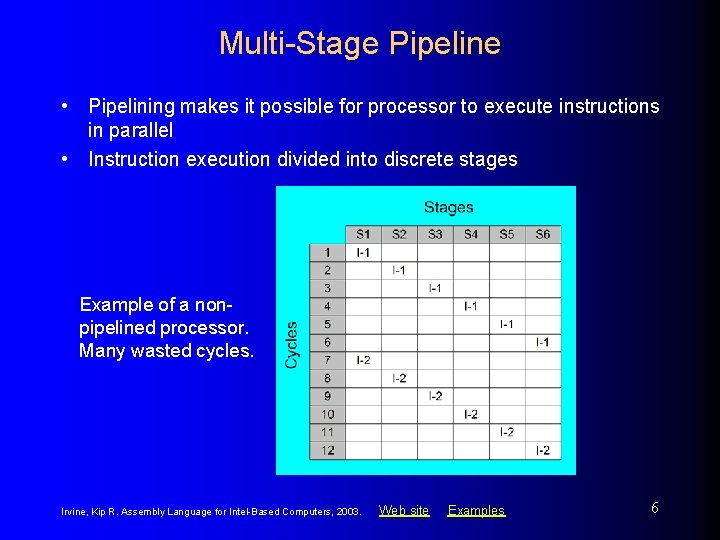
Multi-Stage Pipeline • Pipelining makes it possible for processor to execute instructions in parallel • Instruction execution divided into discrete stages Example of a nonpipelined processor. Many wasted cycles. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 6
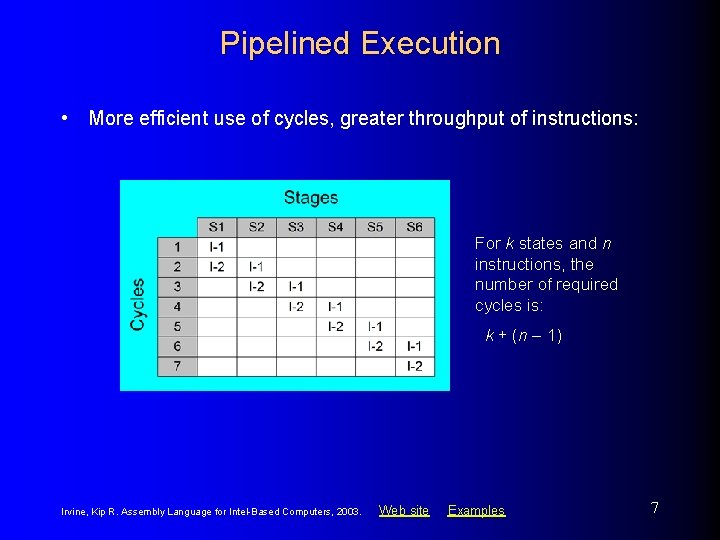
Pipelined Execution • More efficient use of cycles, greater throughput of instructions: For k states and n instructions, the number of required cycles is: k + (n – 1) Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 7
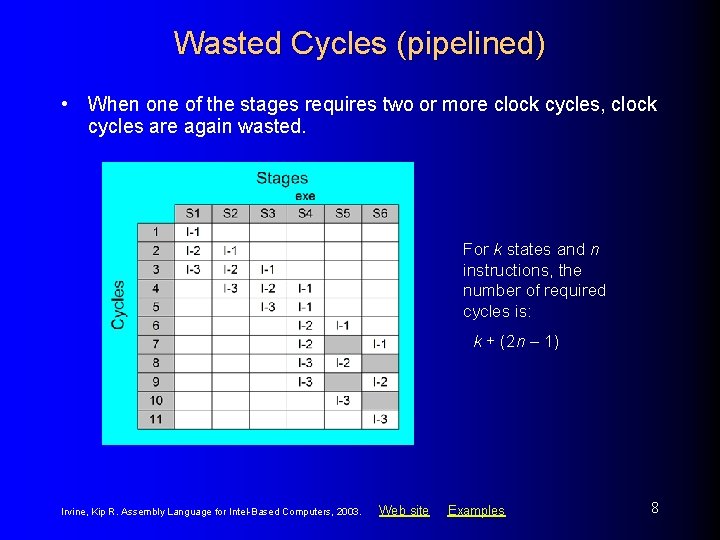
Wasted Cycles (pipelined) • When one of the stages requires two or more clock cycles, clock cycles are again wasted. For k states and n instructions, the number of required cycles is: k + (2 n – 1) Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 8
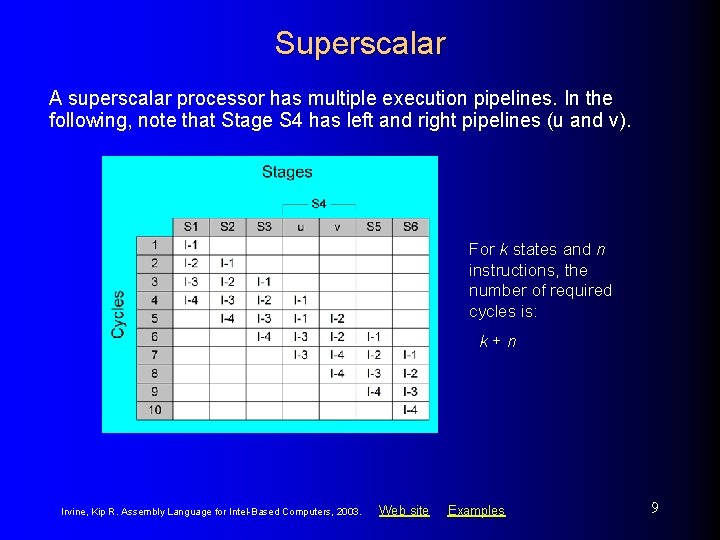
Superscalar A superscalar processor has multiple execution pipelines. In the following, note that Stage S 4 has left and right pipelines (u and v). For k states and n instructions, the number of required cycles is: k+n Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 9
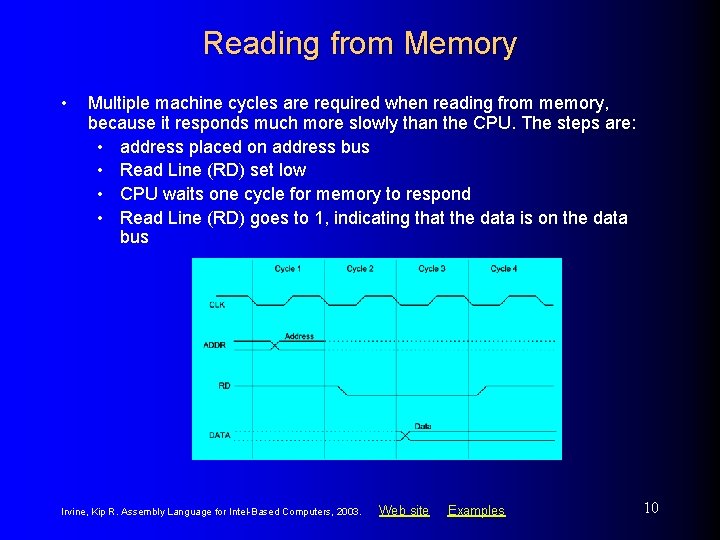
Reading from Memory • Multiple machine cycles are required when reading from memory, because it responds much more slowly than the CPU. The steps are: • address placed on address bus • Read Line (RD) set low • CPU waits one cycle for memory to respond • Read Line (RD) goes to 1, indicating that the data is on the data bus Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 10
Cache Memory • High-speed expensive static RAM both inside and outside the CPU. • Level-1 cache: inside the CPU • Level-2 cache: outside the CPU • Cache hit: when data to be read is already in cache memory • Cache miss: when data to be read is not in cache memory. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 11
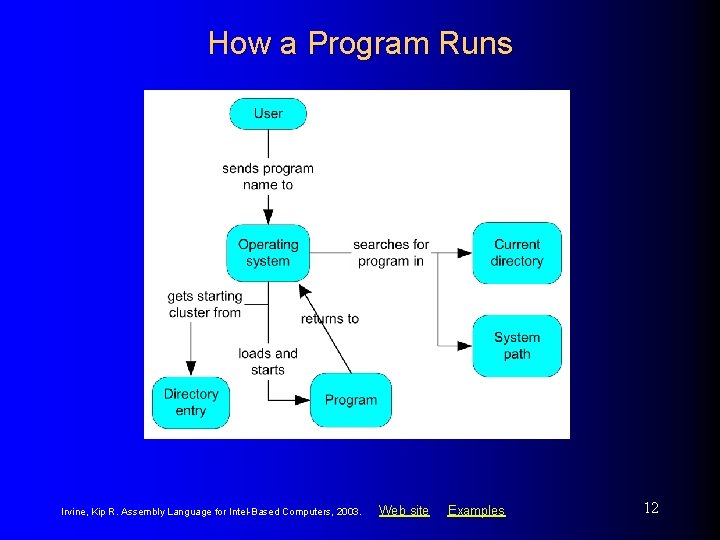
How a Program Runs Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 12
Multitasking • OS can run multiple programs at the same time. • Multiple threads of execution within the same program. • Scheduler utility assigns a given amount of CPU time to each running program. • Rapid switching of tasks • gives illusion that all programs are running at once • the processor must support task switching. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 13
IA-32 Processor Architecture • Modes of operation • Basic execution environment • Floating-point unit Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 14
Modes of Operation • Protected mode • native mode (Windows, Linux) • Real-address mode • native MS-DOS • System management mode • power management, system security, diagnostics • Virtual-8086 mode • hybrid of Protected • each program has its own 8086 computer Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 15
Basic Execution Environment • • • Addressable memory General-purpose registers Index and base registers Specialized register uses Status flags Floating-point, MMX, XMM registers Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 16
Addressable Memory • Protected mode • 4 GB • 32 -bit address • Real-address and Virtual-8086 modes • 1 MB space • 20 -bit address Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 17
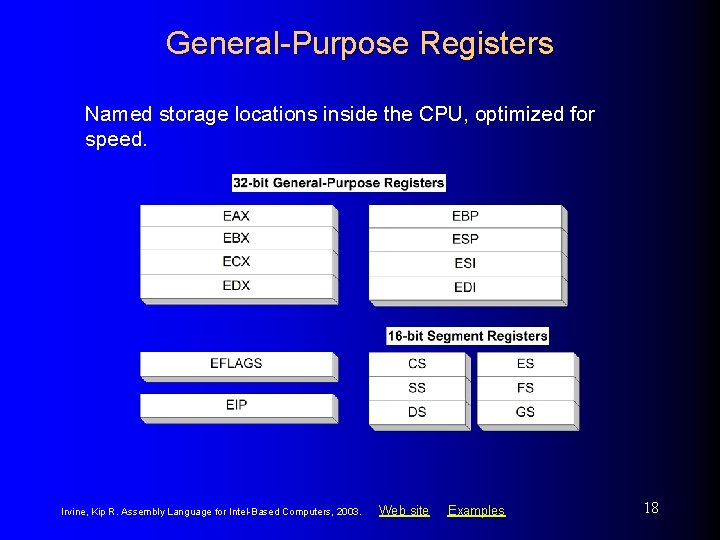
General-Purpose Registers Named storage locations inside the CPU, optimized for speed. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 18
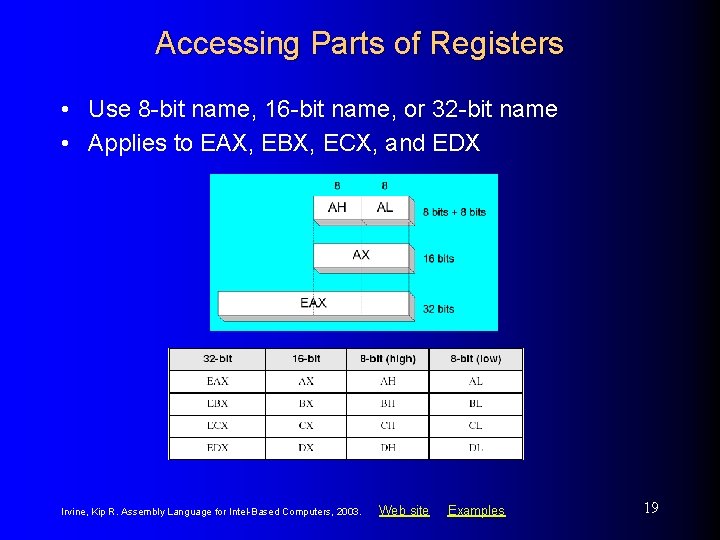
Accessing Parts of Registers • Use 8 -bit name, 16 -bit name, or 32 -bit name • Applies to EAX, EBX, ECX, and EDX Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 19
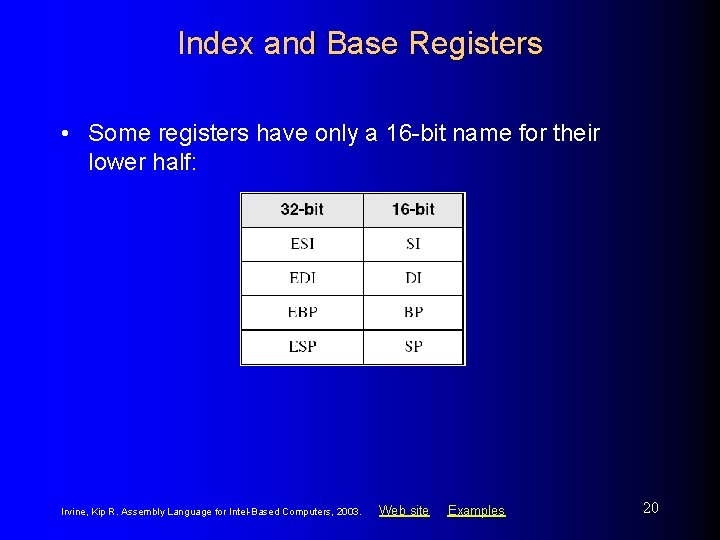
Index and Base Registers • Some registers have only a 16 -bit name for their lower half: Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 20
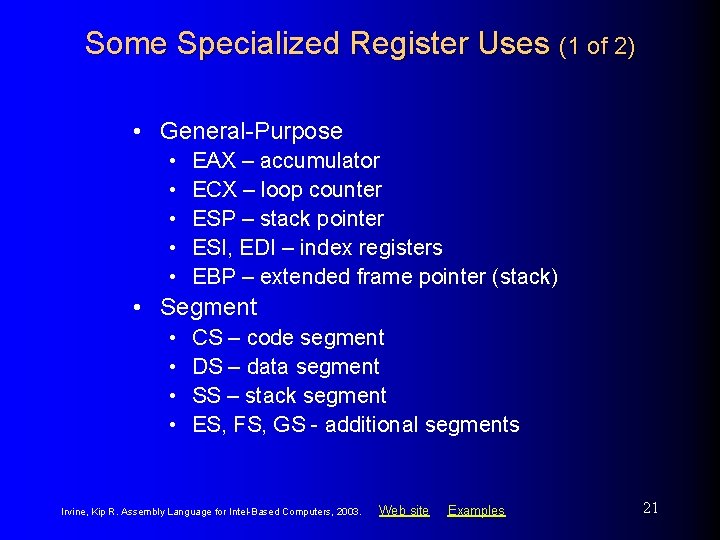
Some Specialized Register Uses (1 of 2) • General-Purpose • • • EAX – accumulator ECX – loop counter ESP – stack pointer ESI, EDI – index registers EBP – extended frame pointer (stack) • Segment • • CS – code segment DS – data segment SS – stack segment ES, FS, GS - additional segments Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 21
Some Specialized Register Uses (2 of 2) • EIP – instruction pointer • EFLAGS • status and control flags • each flag is a single binary bit Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 22
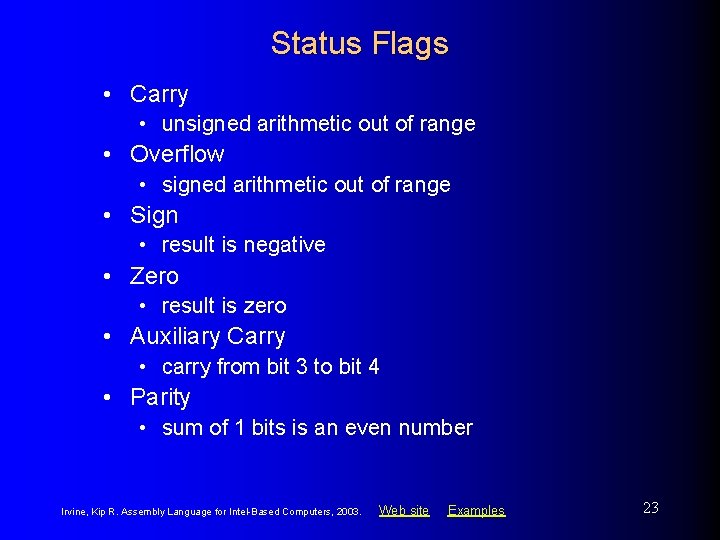
Status Flags • Carry • unsigned arithmetic out of range • Overflow • signed arithmetic out of range • Sign • result is negative • Zero • result is zero • Auxiliary Carry • carry from bit 3 to bit 4 • Parity • sum of 1 bits is an even number Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 23
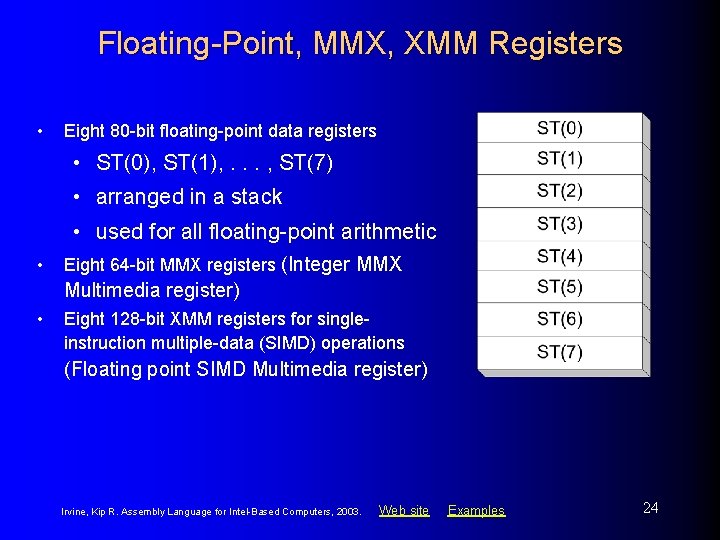
Floating-Point, MMX, XMM Registers • Eight 80 -bit floating-point data registers • ST(0), ST(1), . . . , ST(7) • arranged in a stack • used for all floating-point arithmetic • Eight 64 -bit MMX registers (Integer MMX Multimedia register) • Eight 128 -bit XMM registers for singleinstruction multiple-data (SIMD) operations (Floating point SIMD Multimedia register) Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 24
IA-32 Memory Management • • • Real-address mode Calculating linear addresses Protected mode Multi-segment model Paging Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 25
Real-Address mode • 1 MB RAM maximum addressable • Application programs can access any area of memory • Single tasking Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 26
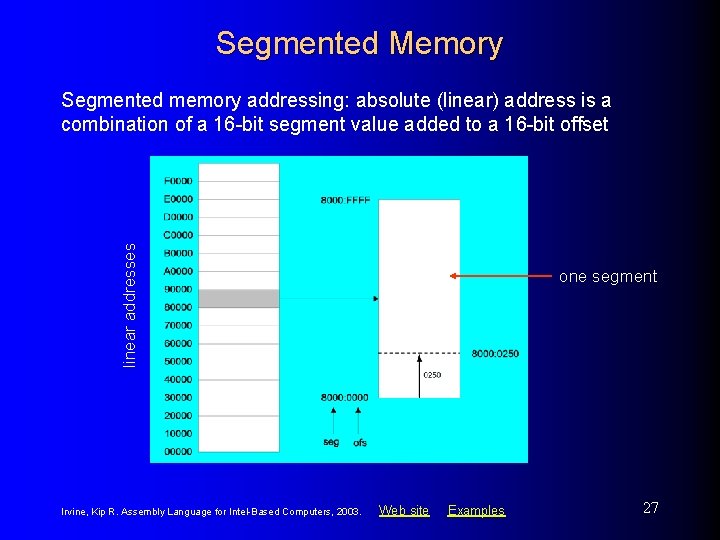
Segmented Memory linear addresses Segmented memory addressing: absolute (linear) address is a combination of a 16 -bit segment value added to a 16 -bit offset Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. one segment Web site Examples 27
Memory map for 8086 microprocessor • Some memory locations are marked reserved and others dedicated. • The dedicated locations are used for processing of specific system interrupts and the reset function. • Intel has also reserved several locations for future hardware and software products. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 28
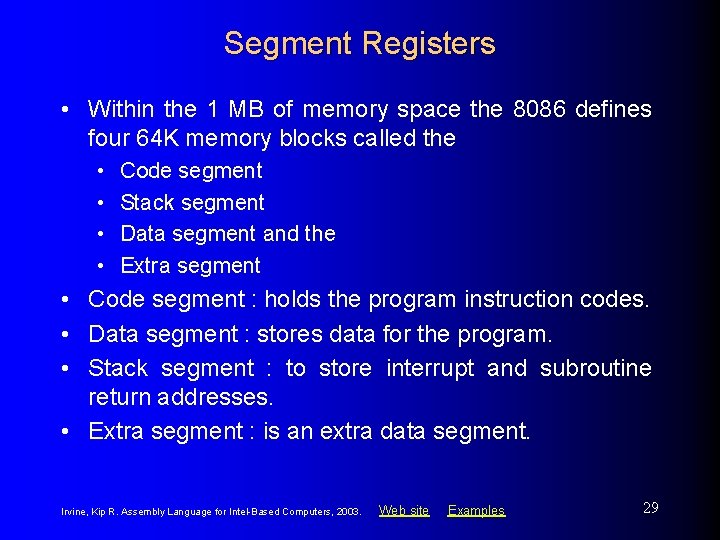
Segment Registers • Within the 1 MB of memory space the 8086 defines four 64 K memory blocks called the • • Code segment Stack segment Data segment and the Extra segment • Code segment : holds the program instruction codes. • Data segment : stores data for the program. • Stack segment : to store interrupt and subroutine return addresses. • Extra segment : is an extra data segment. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 29
Addressing • The concept of segmented memory is unique one. • Older generation microprocessors like 8 bit 8085 could access only one 64 K byte segment, called linear addressing. • Linear Addressing : the program instructions, data and the subroutine stack all had to share the same memory. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 30
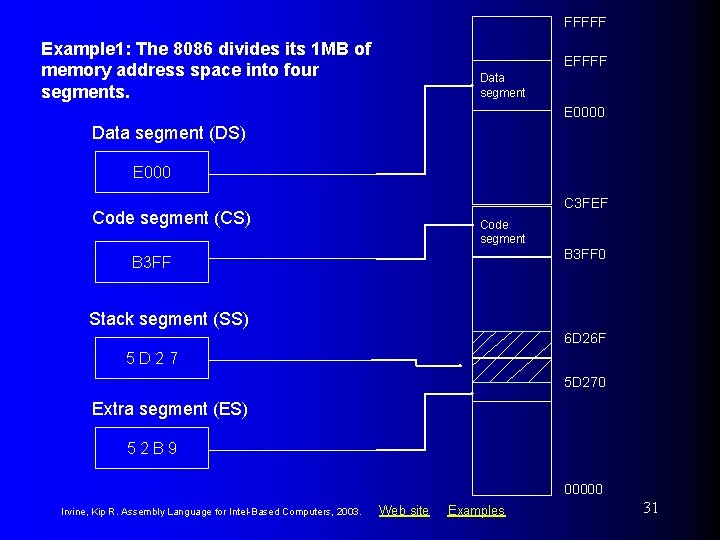
FFFFF Example 1: The 8086 divides its 1 MB of memory address space into four segments. EFFFF Data segment E 0000 Data segment (DS) E 000 C 3 FEF Code segment (CS) Code segment B 3 FF 0 B 3 FF Stack segment (SS) 6 D 26 F 5 D 270 Extra segment (ES) 52 B 9 00000 Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 31
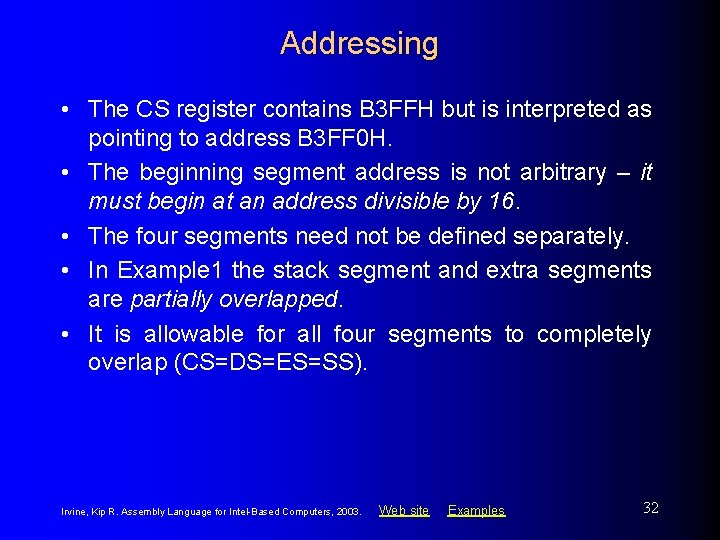
Addressing • The CS register contains B 3 FFH but is interpreted as pointing to address B 3 FF 0 H. • The beginning segment address is not arbitrary – it must begin at an address divisible by 16. • The four segments need not be defined separately. • In Example 1 the stack segment and extra segments are partially overlapped. • It is allowable for all four segments to completely overlap (CS=DS=ES=SS). Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 32
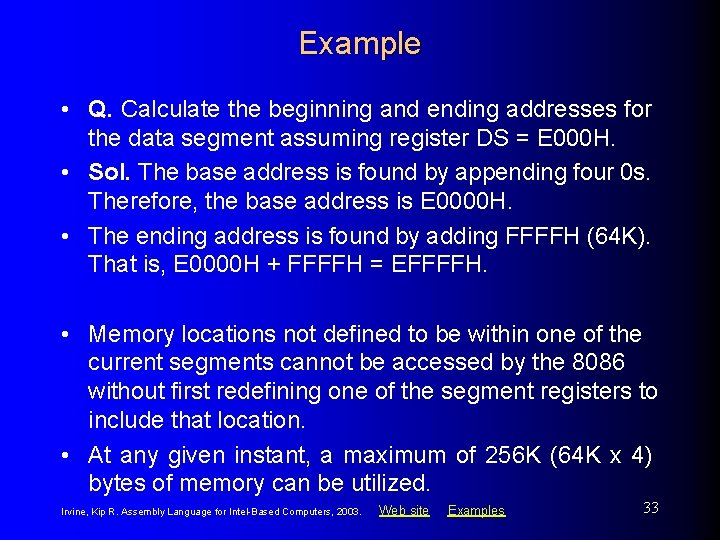
Example • Q. Calculate the beginning and ending addresses for the data segment assuming register DS = E 000 H. • Sol. The base address is found by appending four 0 s. Therefore, the base address is E 0000 H. • The ending address is found by adding FFFFH (64 K). That is, E 0000 H + FFFFH = EFFFFH. • Memory locations not defined to be within one of the current segments cannot be accessed by the 8086 without first redefining one of the segment registers to include that location. • At any given instant, a maximum of 256 K (64 K x 4) bytes of memory can be utilized. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 33
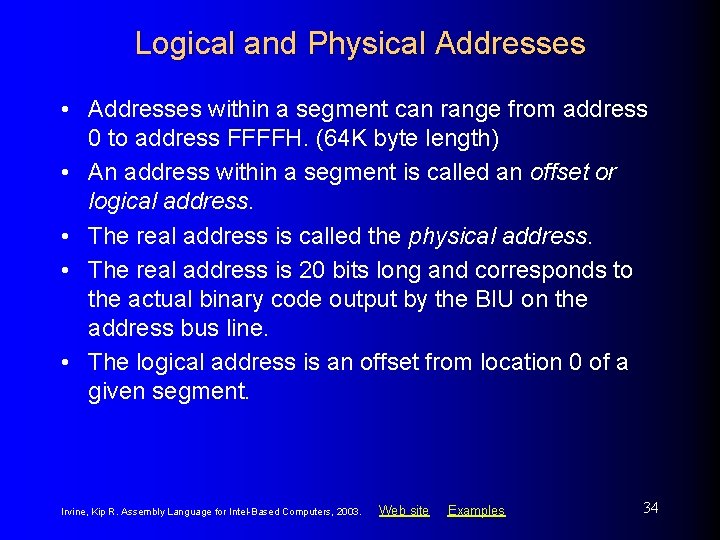
Logical and Physical Addresses • Addresses within a segment can range from address 0 to address FFFFH. (64 K byte length) • An address within a segment is called an offset or logical address. • The real address is called the physical address. • The real address is 20 bits long and corresponds to the actual binary code output by the BIU on the address bus line. • The logical address is an offset from location 0 of a given segment. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 34
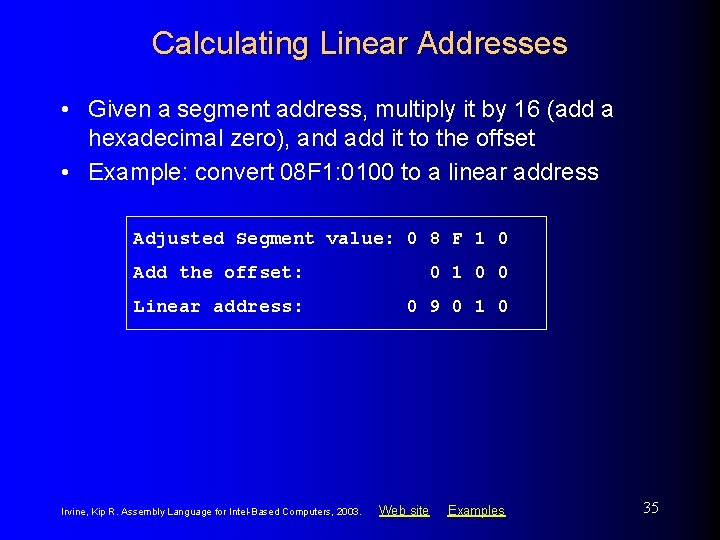
Calculating Linear Addresses • Given a segment address, multiply it by 16 (add a hexadecimal zero), and add it to the offset • Example: convert 08 F 1: 0100 to a linear address Adjusted Segment value: 0 8 F 1 0 Add the offset: 0 1 0 0 Linear address: 0 9 0 1 0 Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 35
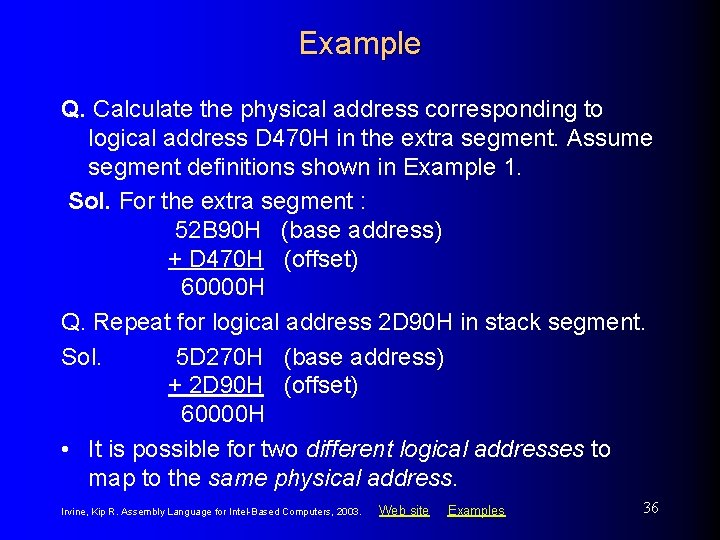
Example Q. Calculate the physical address corresponding to logical address D 470 H in the extra segment. Assume segment definitions shown in Example 1. Sol. For the extra segment : 52 B 90 H (base address) + D 470 H (offset) 60000 H Q. Repeat for logical address 2 D 90 H in stack segment. Sol. 5 D 270 H (base address) + 2 D 90 H (offset) 60000 H • It is possible for two different logical addresses to map to the same physical address. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 36
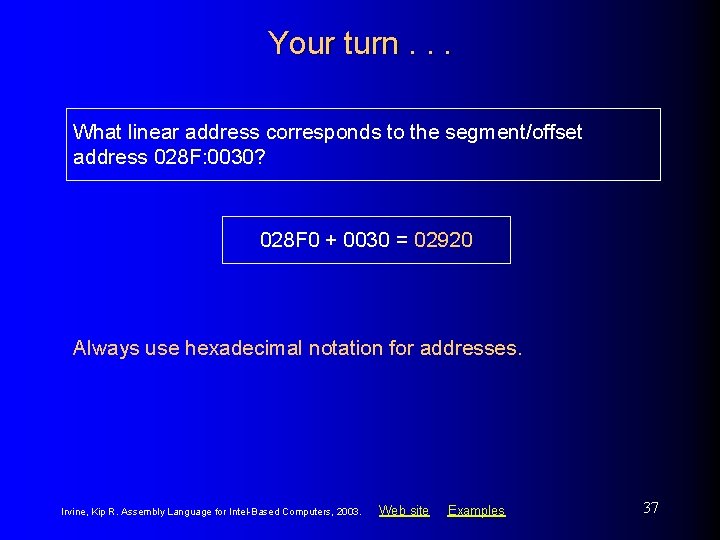
Your turn. . . What linear address corresponds to the segment/offset address 028 F: 0030? 028 F 0 + 0030 = 02920 Always use hexadecimal notation for addresses. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 37
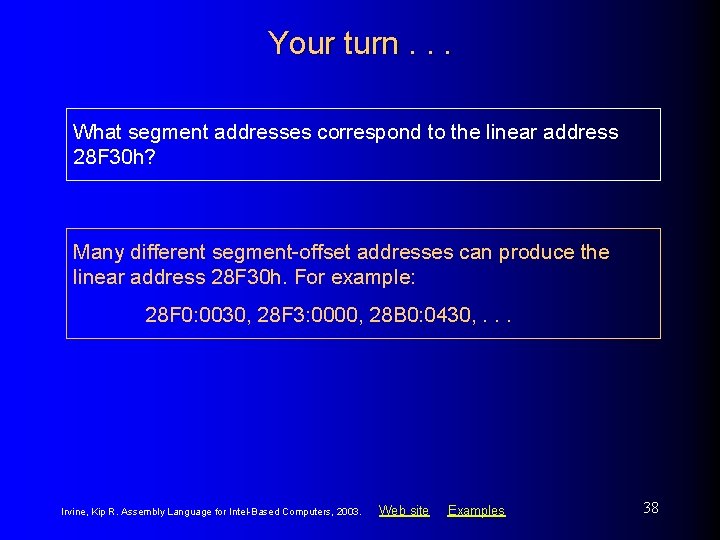
Your turn. . . What segment addresses correspond to the linear address 28 F 30 h? Many different segment-offset addresses can produce the linear address 28 F 30 h. For example: 28 F 0: 0030, 28 F 3: 0000, 28 B 0: 0430, . . . Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 38
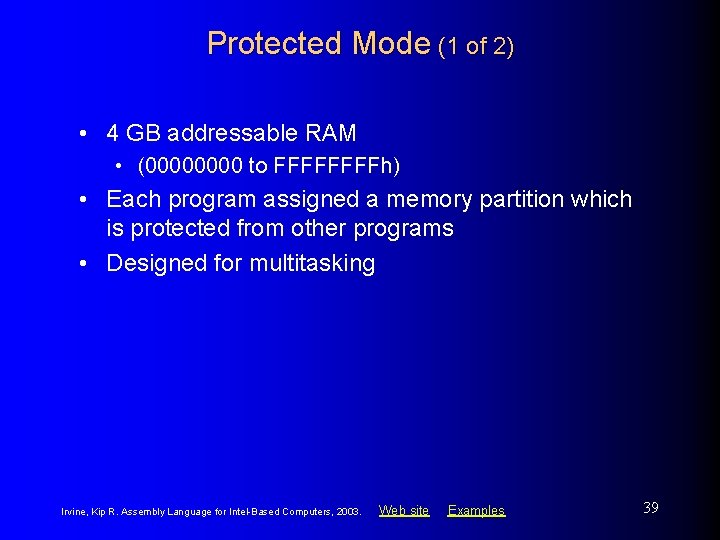
Protected Mode (1 of 2) • 4 GB addressable RAM • (0000 to FFFFh) • Each program assigned a memory partition which is protected from other programs • Designed for multitasking Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 39
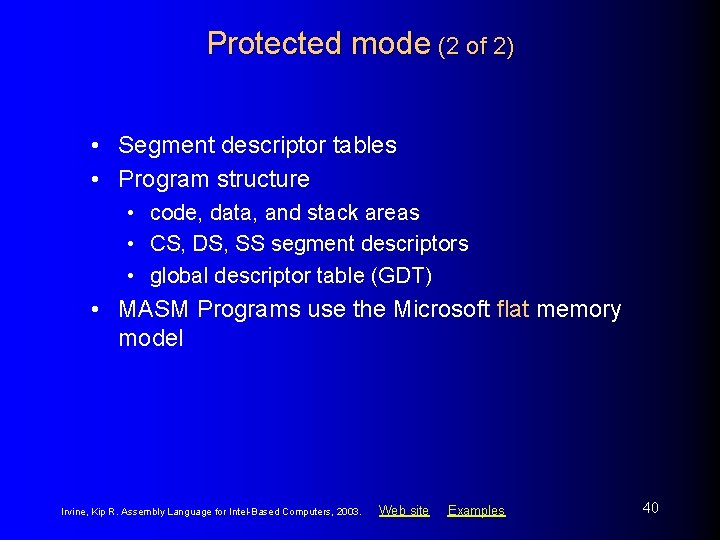
Protected mode (2 of 2) • Segment descriptor tables • Program structure • code, data, and stack areas • CS, DS, SS segment descriptors • global descriptor table (GDT) • MASM Programs use the Microsoft flat memory model Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 40
Segmentation • Protected Mode Memory Segments. • Protected mode segments can be as small as a single byte or as large as 4 GB. • Each memory segment is assigned a protection level. • Just six segments can be active at a given time • Segments can readily be swapped out to disk to support virtual memory. • Status bits indicate if the selected memory segment is actually present in memory. • Segments can be marked as read-only to protect code and data. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 41
Selectors and Descriptors • In order to specify a protected mode memory segment, its starting address, size and attributes must be known. • Now referred to as selectors, the segment registers are used to point to an entry in a descriptor table. • Each entry or descriptor in this table is eight bytes long. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 42
Descriptor Tables • Three descriptor tables : • The Global Descriptor Table (GDT) : Entries in this table describe segments that may be available to all tasks in the system. • The Local Descriptor Table (LDT) : Entries in this table describe segments associated with a given task. Each task have a separate LDT. • The Interrupt Descriptor Table (IDT) : Entries in this table point to the starting addresses of up to 256 different interrupt service routines. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 43
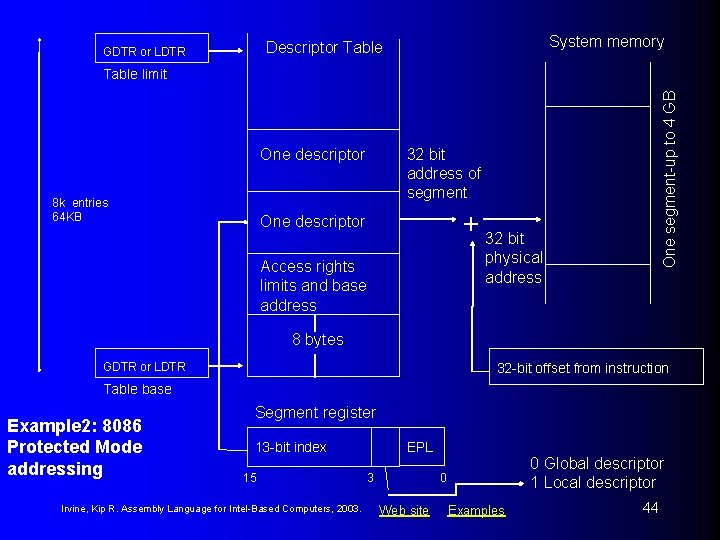
System memory Descriptor Table GDTR or LDTR One descriptor 8 k entries 64 KB One segment-up to 4 GB Table limit 32 bit address of segment + 32 bit One descriptor physical address Access rights limits and base address 8 bytes GDTR or LDTR 32 -bit offset from instruction Table base Example 2: 8086 Protected Mode addressing Segment register 13 -bit index 15 Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. EPL 3 0 Global descriptor 1 Local descriptor 0 Web site Examples 44
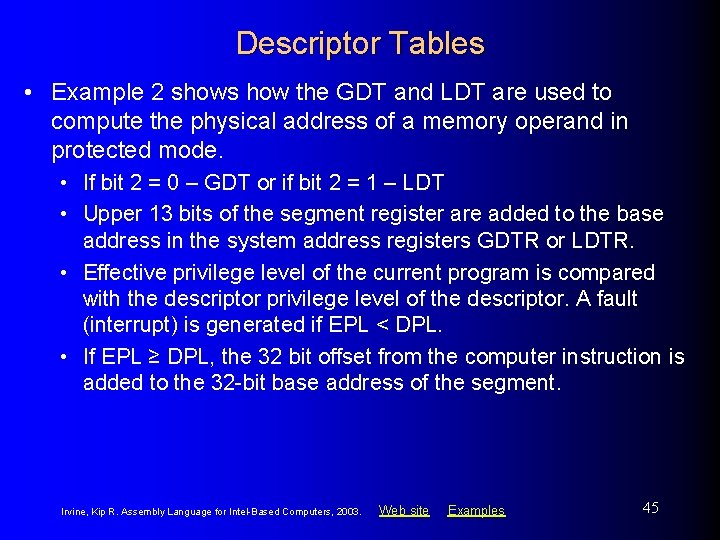
Descriptor Tables • Example 2 shows how the GDT and LDT are used to compute the physical address of a memory operand in protected mode. • If bit 2 = 0 – GDT or if bit 2 = 1 – LDT • Upper 13 bits of the segment register are added to the base address in the system address registers GDTR or LDTR. • Effective privilege level of the current program is compared with the descriptor privilege level of the descriptor. A fault (interrupt) is generated if EPL < DPL. • If EPL ≥ DPL, the 32 bit offset from the computer instruction is added to the 32 -bit base address of the segment. Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 45
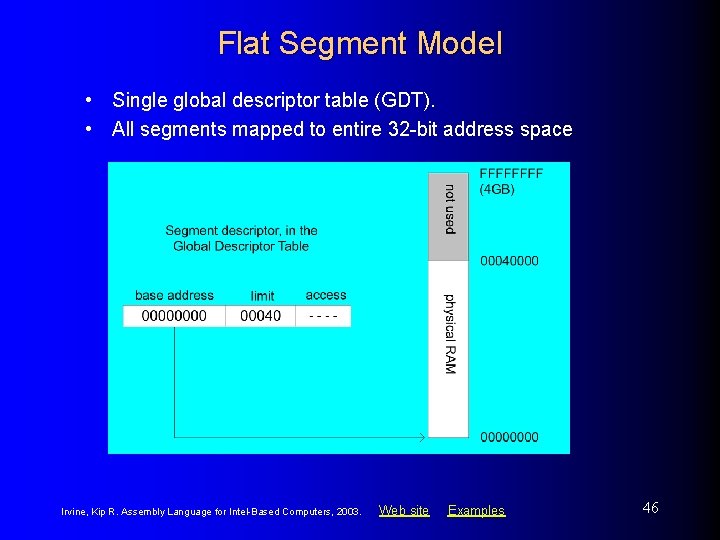
Flat Segment Model • Single global descriptor table (GDT). • All segments mapped to entire 32 -bit address space Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 46
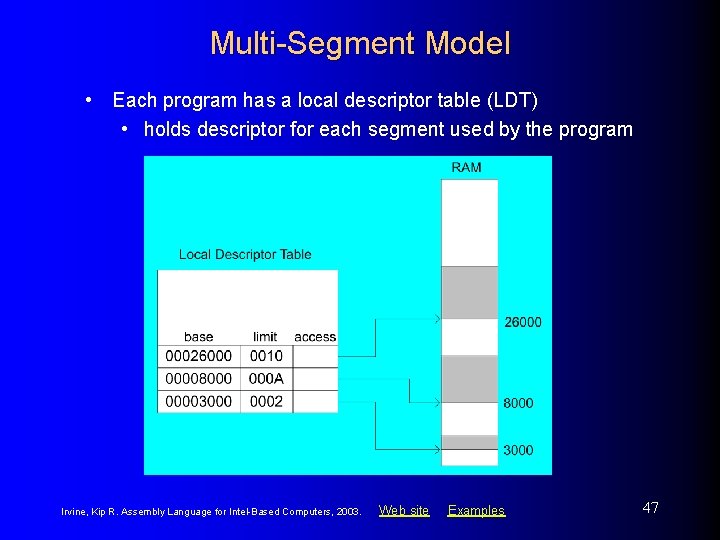
Multi-Segment Model • Each program has a local descriptor table (LDT) • holds descriptor for each segment used by the program Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 47
Paging • Supported directly by the CPU • Divides each segment into 4096 -byte blocks called pages • Sum of all programs can be larger than physical memory • Part of running program is in memory, part is on disk • Virtual memory manager (VMM) – OS utility that manages the loading and unloading of pages • Page fault – issued by CPU when a page must be loaded from disk Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 48
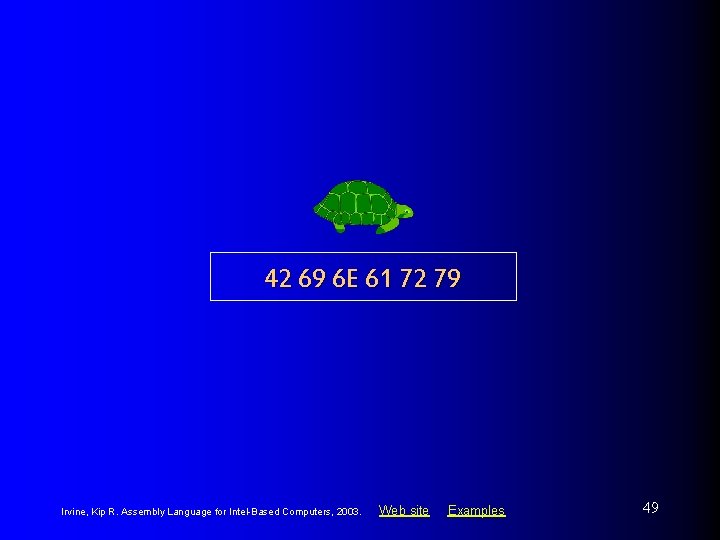
42 69 6 E 61 72 79 Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. Web site Examples 49
- Slides: 49