Network Security Security of Internet Mobility Tuomas Aura
Network Security: Security of Internet Mobility Tuomas Aura T-110. 5241 Network security Aalto University, Nov-Dec 2014
Outline Mobile IPv 6 Return routability test Address and identifier ownership Cryptographically generated IPv 6 addresses 2
Mobile IPv 6
! Why is Mobile IP(v 6) not used? Mobility in the IP layer was supposed to be a generic solution to all mobility, but it is not widely used IPv 6 deployment slowed than expected Too narrow view of what is mobility: Changing IP address (handover between WLAN APs, DHCP allocating a different address) – only this is solved by Mobile IP(v 6) Shared IP address (hosts behind a NAT) Multihoming (wired+wireless+cellular interfaces, and thus several IP addresses coming and going) Failover (duplicated nodes, e. g. telecom signaling points) Delay tolerance (device sleeping, no signal) Stateless protocols have taken over HTTP, REST, TLS tolerate connection failure and changing IP address Applications are not designed to depend on long-living TCP connections 5
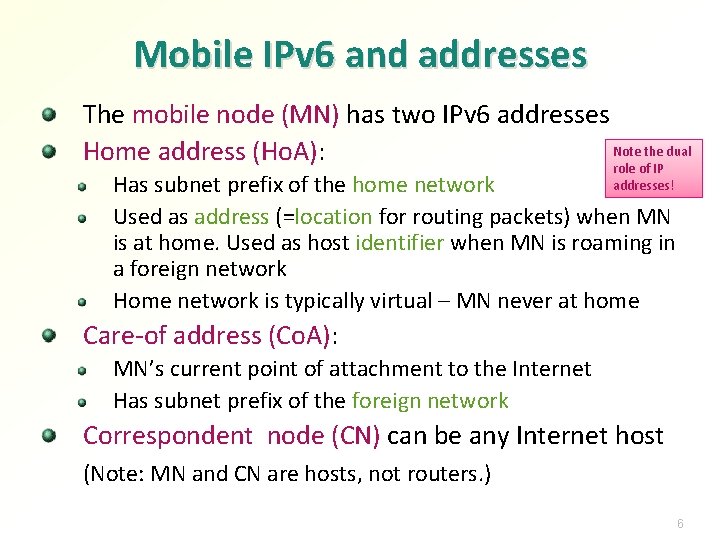
Mobile IPv 6 and addresses The mobile node (MN) has two IPv 6 addresses Note the dual Home address (Ho. A): role of IP addresses! Has subnet prefix of the home network Used as address (=location for routing packets) when MN is at home. Used as host identifier when MN is roaming in a foreign network Home network is typically virtual – MN never at home Care-of address (Co. A): MN’s current point of attachment to the Internet Has subnet prefix of the foreign network Correspondent node (CN) can be any Internet host (Note: MN and CN are hosts, not routers. ) 6
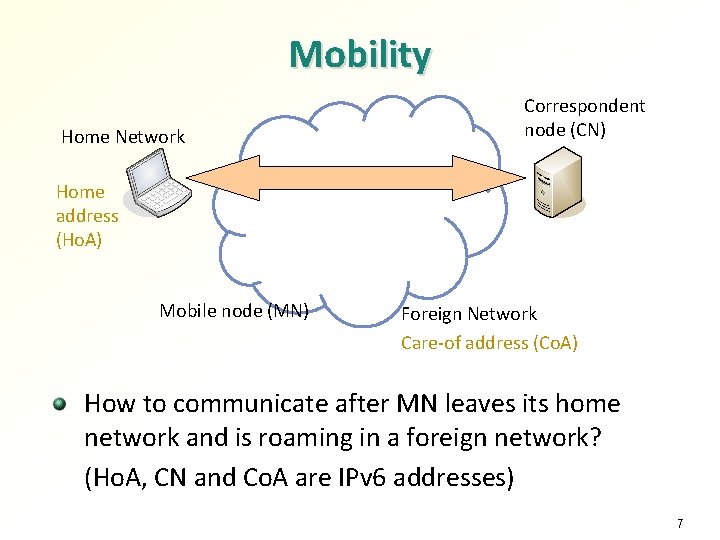
Mobility Home Network Correspondent node (CN) Home address (Ho. A) Mobile node (MN) Foreign Network Care-of address (Co. A) How to communicate after MN leaves its home network and is roaming in a foreign network? (Ho. A, CN and Co. A are IPv 6 addresses) 7
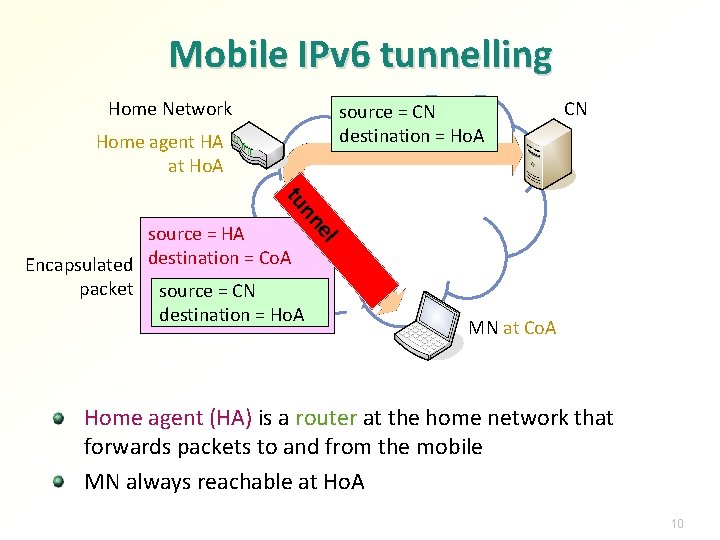
Mobile IPv 6 tunnelling Home Network source = CN destination = Ho. A Home agent HA at Ho. A CN e nn tu l source = HA Encapsulated destination = Co. A packet source = CN destination = Ho. A MN at Co. A Home agent (HA) is a router at the home network that forwards packets to and from the mobile MN always reachable at Ho. A 10
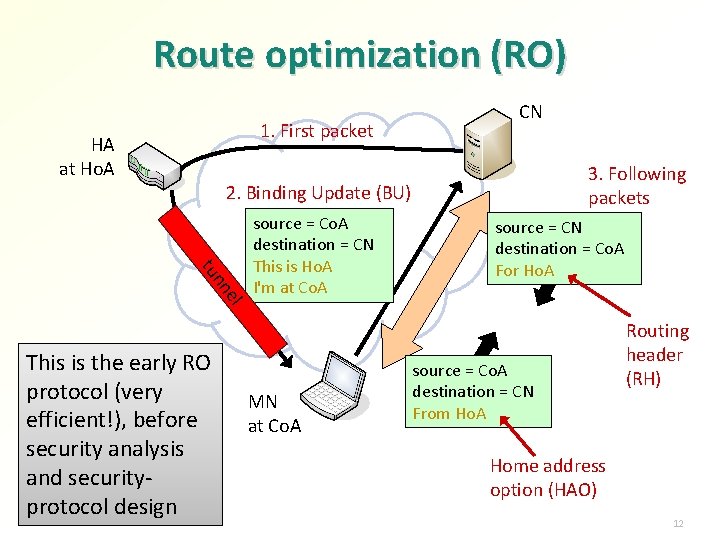
Route optimization (RO) 1. First packet HA at Ho. A CN 3. Following packets 2. Binding Update (BU) tu el nn This is the early RO protocol (very efficient!), before security analysis and securityprotocol design source = Co. A destination = CN This is Ho. A I'm at Co. A MN at Co. A source = CN destination = Co. A For Ho. A source = Co. A destination = CN From Ho. A Routing header (RH) Home address option (HAO) 12
How the MIPv 6 security protocol was developed: threats and protection mechanisms 17
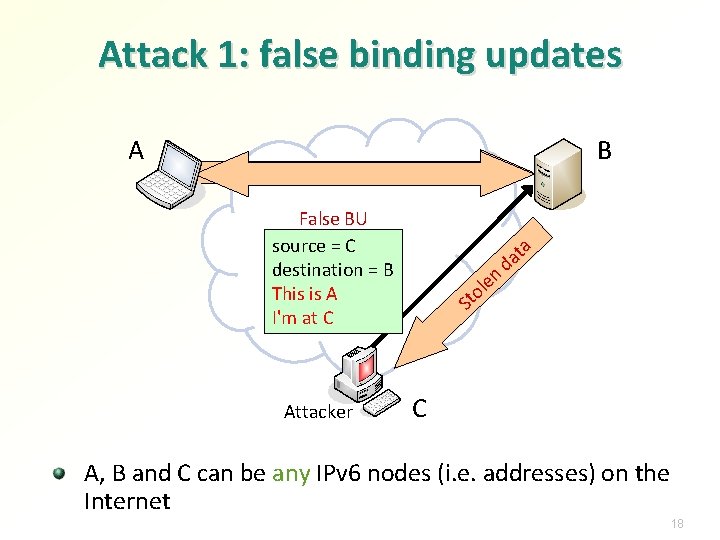
Attack 1: false binding updates A B False BU source = C destination = B This is A I'm at C Attacker n e ol St ta a d C A, B and C can be any IPv 6 nodes (i. e. addresses) on the Internet 18
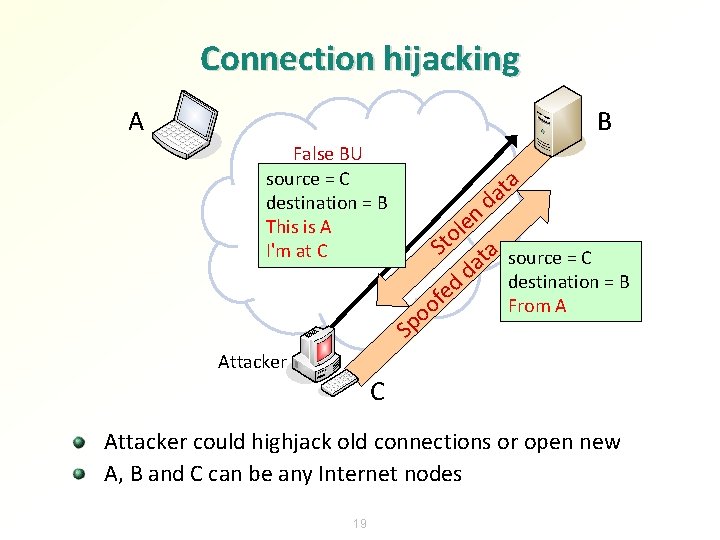
Connection hijacking A B False BU source = C destination = B This is A I'm at C a t a d en l o t S ta source = C a d destination = B ed f From A o o p S Attacker C Attacker could highjack old connections or open new A, B and C can be any Internet nodes 19
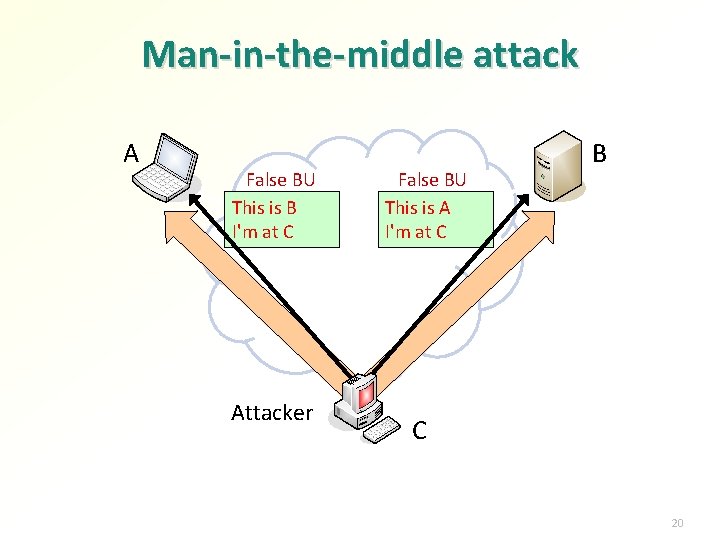
Man-in-the-middle attack A False BU This is B I'm at C Attacker False BU This is A I'm at C B C 20
If no security measures added Attacker anywhere on the Internet can hijack connection between any two Internet nodes, or spoof such a connection Attacker must know the IPv 6 addresses of the target nodes, though 21
BU authentication MN and HA trust each other and can have a secure tunnel between them. Authenticating BUs to CN is the problem The obvious solution is strong cryptographic authentication of BUs Problem: there is no global system for authenticating any Internet node 22
Authentication without infrastructure? How authenticate messages between any two IPv 6 nodes, without introducing new security infrastructure? Set requirements to the right level: Internet with Mobile IPv 6 deployed must be as secure as before it → no general-purpose strong authentication needed Some IP-layer infrastructure is available: IPv 6 addresses Routing infrastructure Surprisingly, both can be used for BU authentication: Cryptographically generated addresses (CGA) Routing-based “weak” authentication, called return routability 23
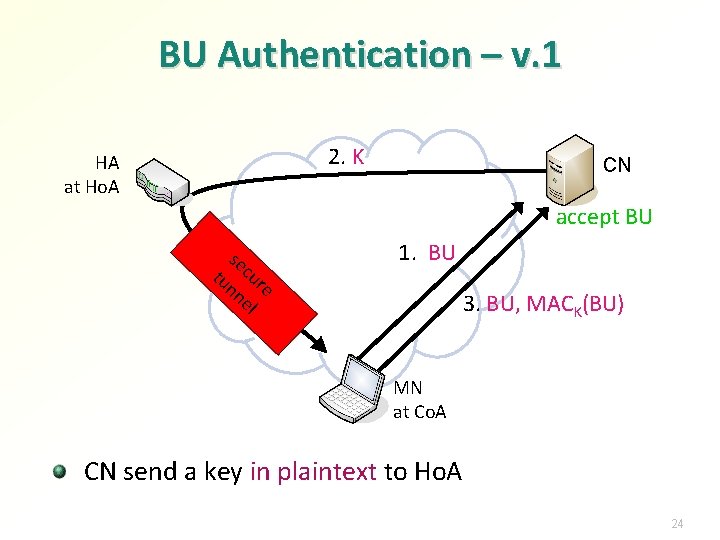
BU Authentication – v. 1 2. K HA at Ho. A CN accept BU se tu cur nn e el 1. BU 3. BU, MACK(BU) MN at Co. A CN send a key in plaintext to Ho. A 24
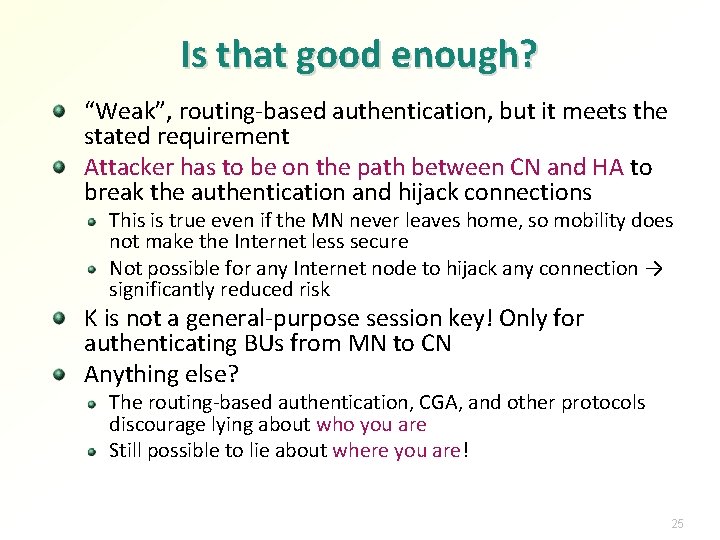
Is that good enough? “Weak”, routing-based authentication, but it meets the stated requirement Attacker has to be on the path between CN and HA to break the authentication and hijack connections This is true even if the MN never leaves home, so mobility does not make the Internet less secure Not possible for any Internet node to hijack any connection → significantly reduced risk K is not a general-purpose session key! Only for authenticating BUs from MN to CN Anything else? The routing-based authentication, CGA, and other protocols discourage lying about who you are Still possible to lie about where you are! 25
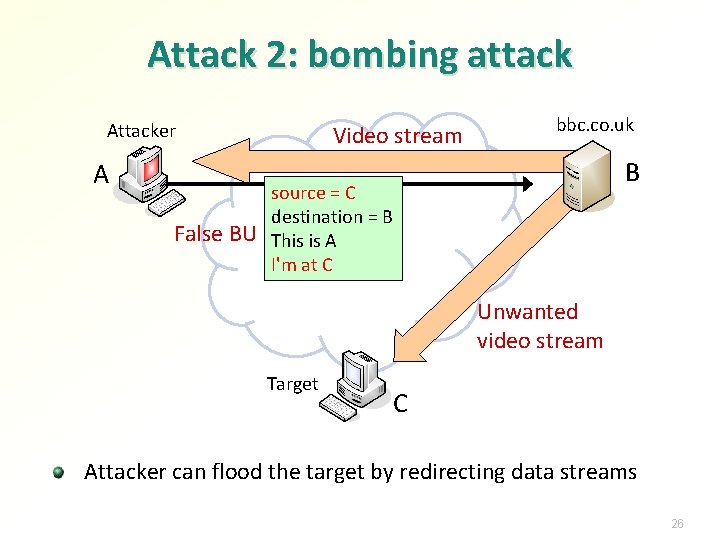
Attack 2: bombing attack Attacker A False BU Video stream bbc. co. uk B source = C destination = B This is A I'm at C Unwanted video stream Target C Attacker can flood the target by redirecting data streams 26
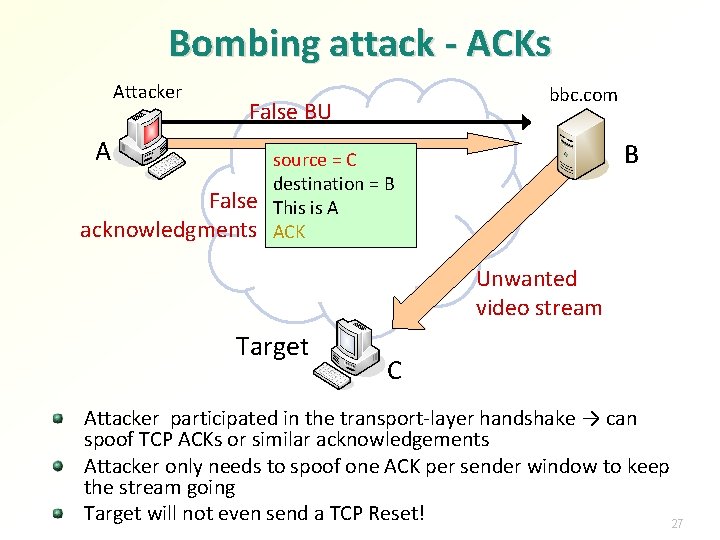
Bombing attack - ACKs Attacker A A bbc. com False BU False acknowledgments B source = C destination = B This is A ACK Unwanted video stream Target C Attacker participated in the transport-layer handshake → can spoof TCP ACKs or similar acknowledgements Attacker only needs to spoof one ACK per sender window to keep the stream going Target will not even send a TCP Reset! 27
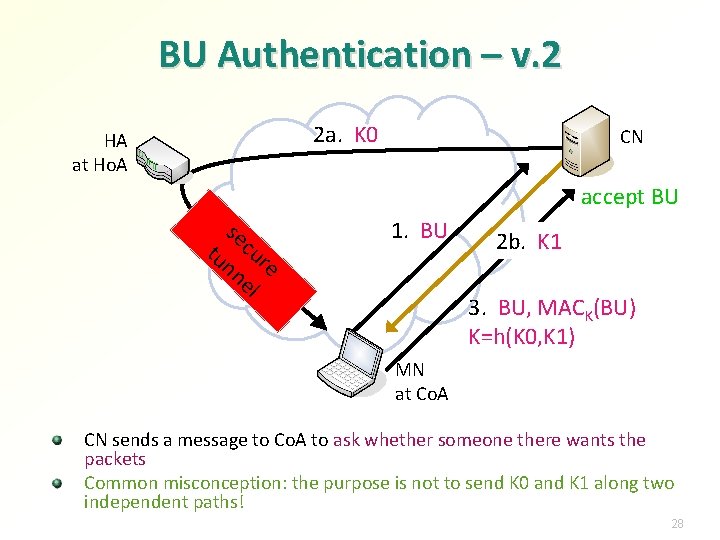
BU Authentication – v. 2 2 a. K 0 HA at Ho. A CN accept BU se tu cur nn e el 1. BU 2 b. K 1 3. BU, MACK(BU) K=h(K 0, K 1) MN at Co. A CN sends a message to Co. A to ask whether someone there wants the packets Common misconception: the purpose is not to send K 0 and K 1 along two independent paths! 28
Is that good enough? Not possible to lie about identity or location; all information in BUs is true Almost ready, but we still need to consider standard denial of service attacks against the BU protocol 29
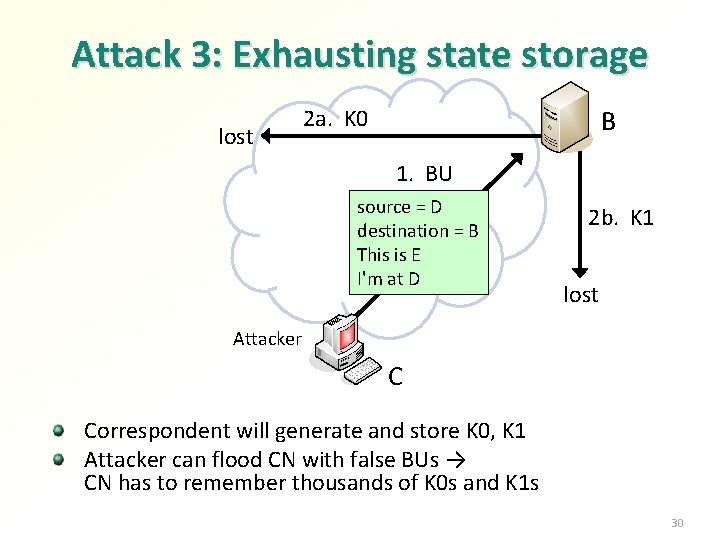
Attack 3: Exhausting state storage lost 2 a. K 0 B 1. BU source = D destination = B This is E I'm at D 2 b. K 1 lost Attacker C Correspondent will generate and store K 0, K 1 Attacker can flood CN with false BUs → CN has to remember thousands of K 0 s and K 1 s 30
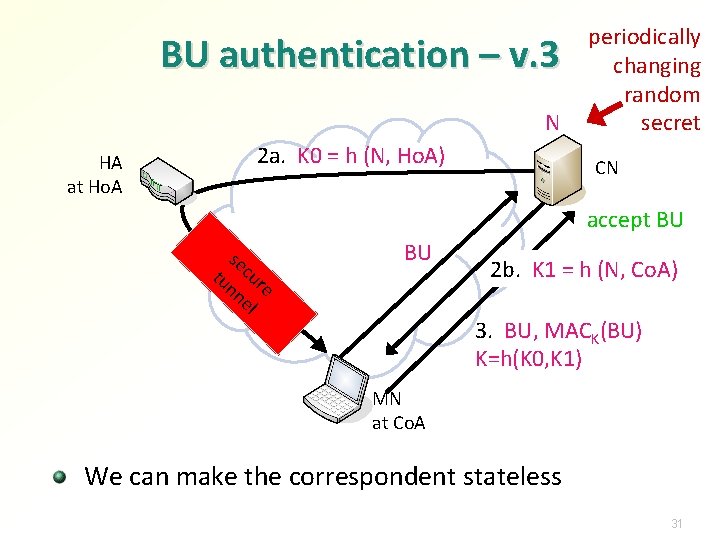
BU authentication – v. 3 N HA at Ho. A 2 a. K 0 = h (N, Ho. A) periodically changing random secret CN accept BU se tu cur nn e el 1. BU 2 b. K 1 = h (N, Co. A) 3. BU, MACK(BU) K=h(K 0, K 1) MN at Co. A We can make the correspondent stateless 31
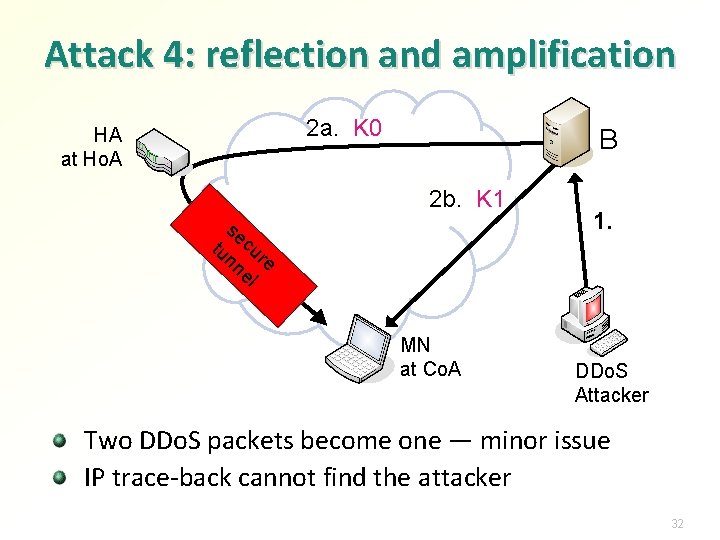
Attack 4: reflection and amplification 2 a. K 0 HA at Ho. A B 2 b. K 1 se tu cur nn e el MN at Co. A 1. DDo. S Attacker Two DDo. S packets become one — minor issue IP trace-back cannot find the attacker 32
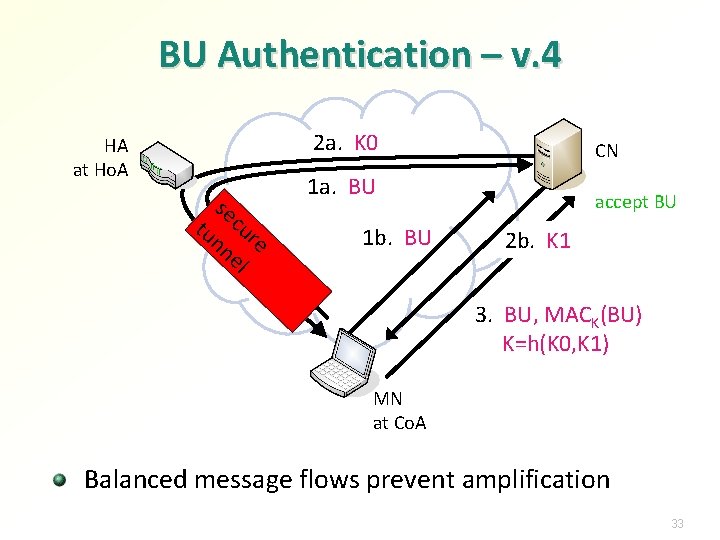
BU Authentication – v. 4 2 a. K 0 HA at Ho. A se tu cur nn e el CN 1 a. BU 1 b. BU accept BU 2 b. K 1 3. BU, MACK(BU) K=h(K 0, K 1) MN at Co. A Balanced message flows prevent amplification 33
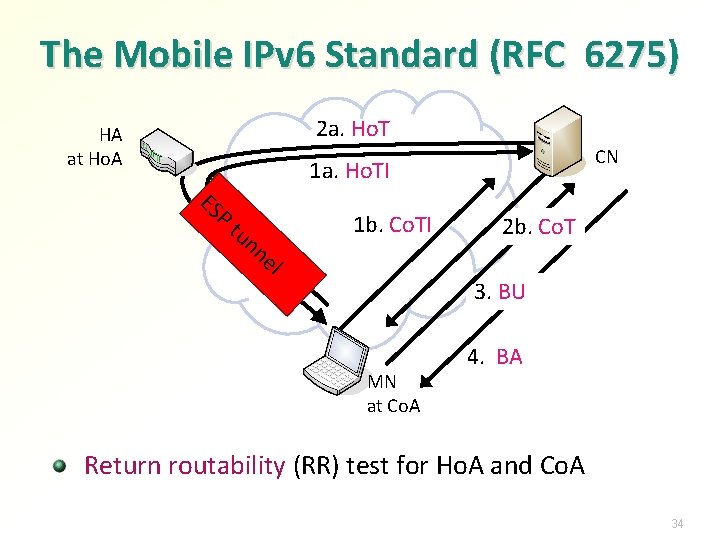
The Mobile IPv 6 Standard (RFC 6275) 2 a. Ho. T HA at Ho. A CN ES 1 a. Ho. TI P tu nn 1 b. Co. TI el 2 b. Co. T 3. BU MN at Co. A 4. BA Return routability (RR) test for Ho. A and Co. A 34
Bombing attacks in general General problem with mobility, multihoming, failover etc. 36
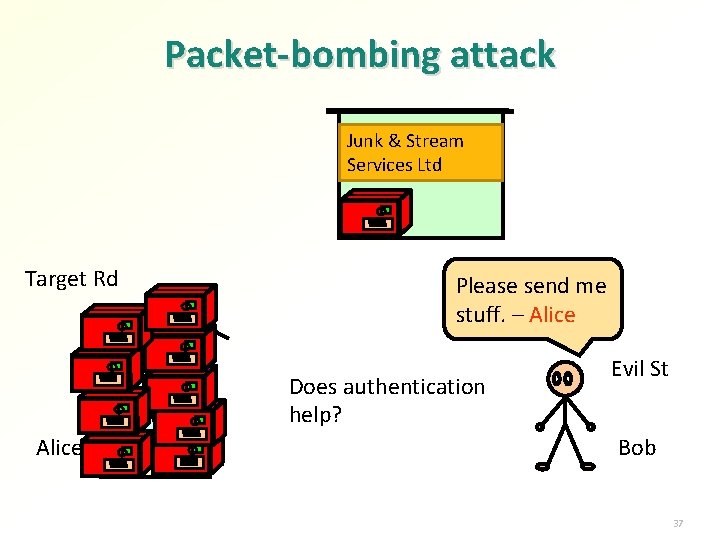
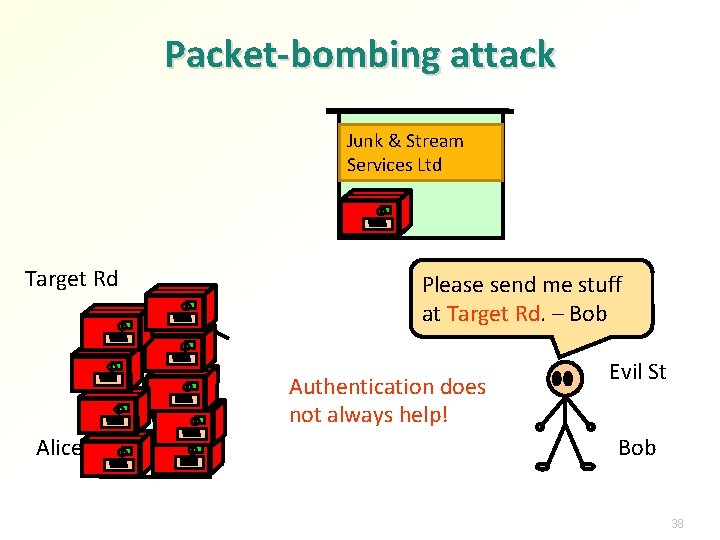
Packet-bombing attack Junk & Stream Services Ltd Target Rd Please send me stuff. – Alice Does authentication help? Alice Evil St Bob 37
Packet-bombing attack Junk & Stream Services Ltd Target Rd Please send me stuff at Target Rd. – Bob Authentication does not always help! Alice Evil St Bob 38
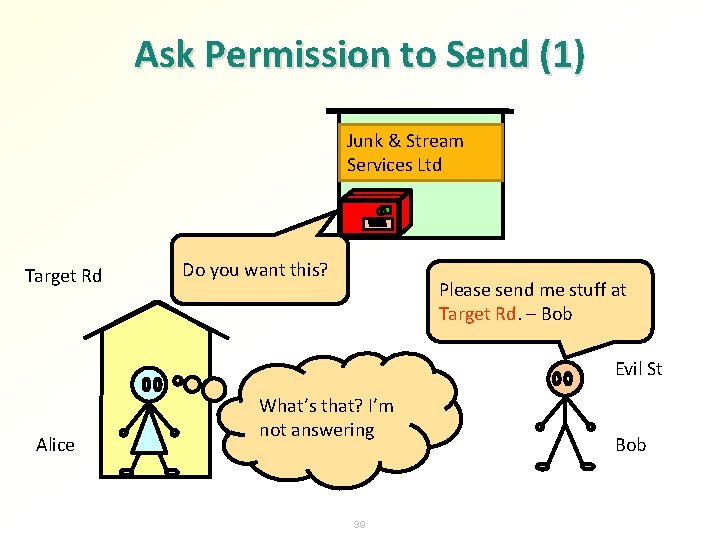
Ask Permission to Send (1) Junk & Stream Services Ltd Target Rd Do you want this? Please send me stuff at Target Rd. – Bob Evil St Alice What’s that? I’m not answering 39 Bob
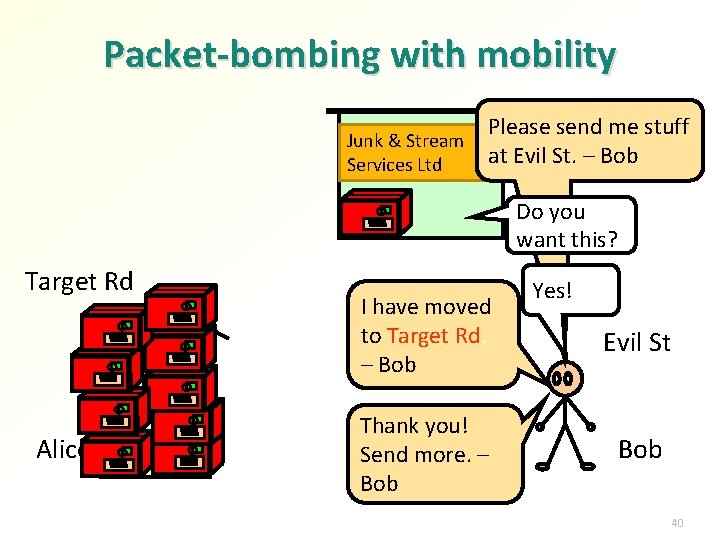
Packet-bombing with mobility Junk & Stream Services Ltd Please send me stuff at Evil St. – Bob Do you want this? Target Rd Alice I have moved to Target Rd. – Bob Thank you! Send more. – Bob Yes! Evil St Bob 40
Address ownership and squating General problem with addresses and identifiers
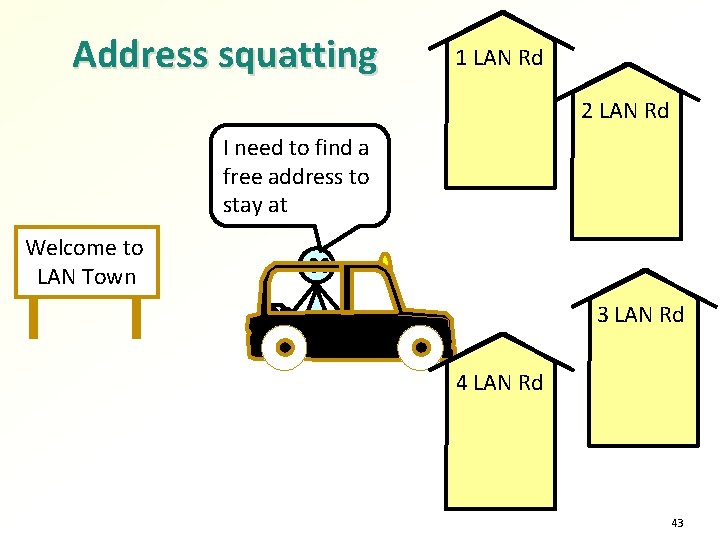
Address squatting 1 LAN Rd 2 LAN Rd I need to find a free address to stay at Welcome to LAN Town 3 LAN Rd 43
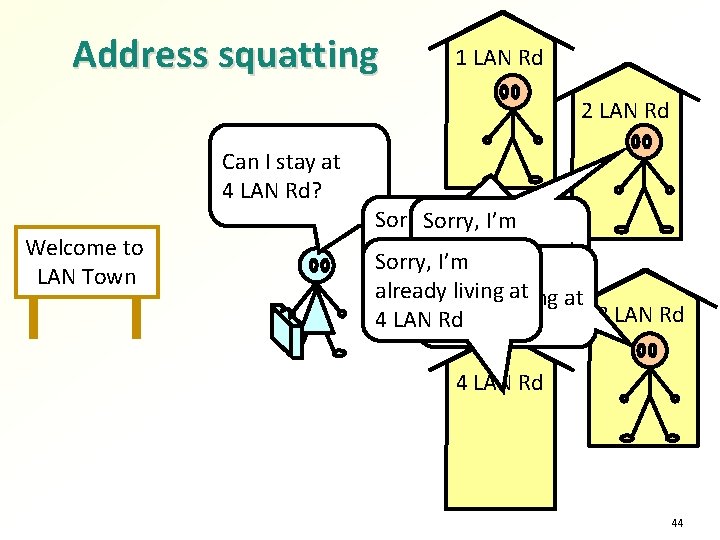
Address squatting 1 LAN Rd 2 LAN Rd Can I stay at 1 LAN Rd? 2 3 4 Welcome to LAN Town Sorry, I’m already living at at already Sorry, I’m 1 LAN 2 Rd LAN Rd already living at at already 3 LAN Rd 4 LAN 3 Rd LAN Rd 44
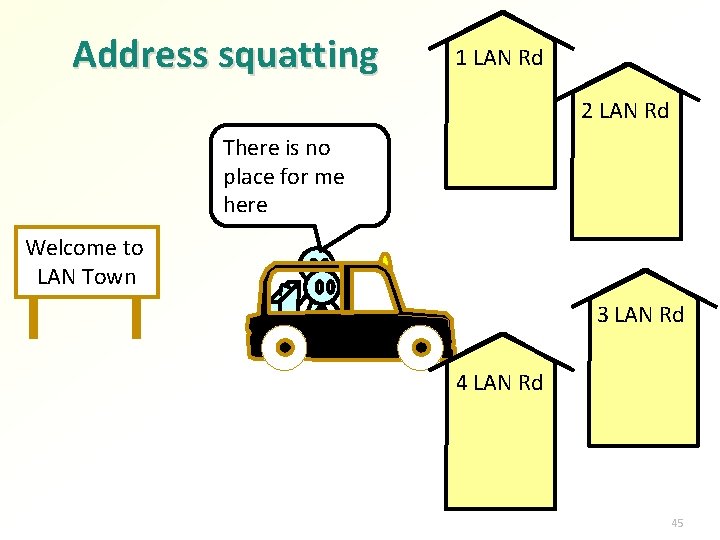
Address squatting 1 LAN Rd 2 LAN Rd There is no place for me here Welcome to LAN Town 3 LAN Rd 45
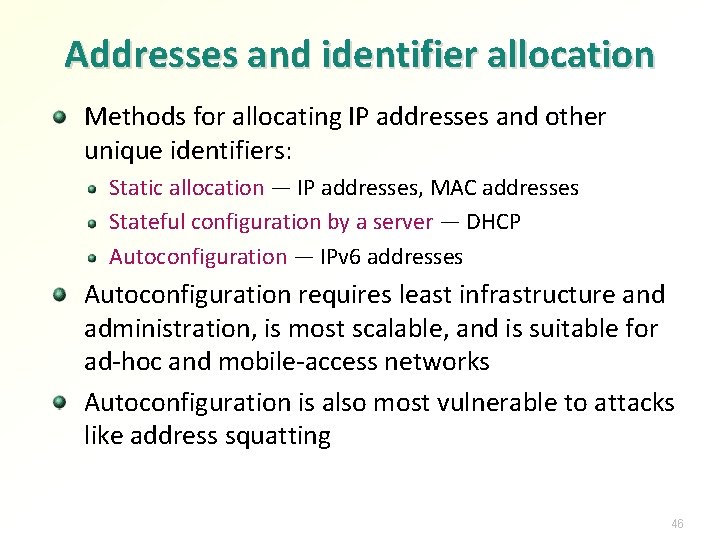
Addresses and identifier allocation Methods for allocating IP addresses and other unique identifiers: Static allocation — IP addresses, MAC addresses Stateful configuration by a server — DHCP Autoconfiguration — IPv 6 addresses Autoconfiguration requires least infrastructure and administration, is most scalable, and is suitable for ad-hoc and mobile-access networks Autoconfiguration is also most vulnerable to attacks like address squatting 46
IPv 6 addresses 47
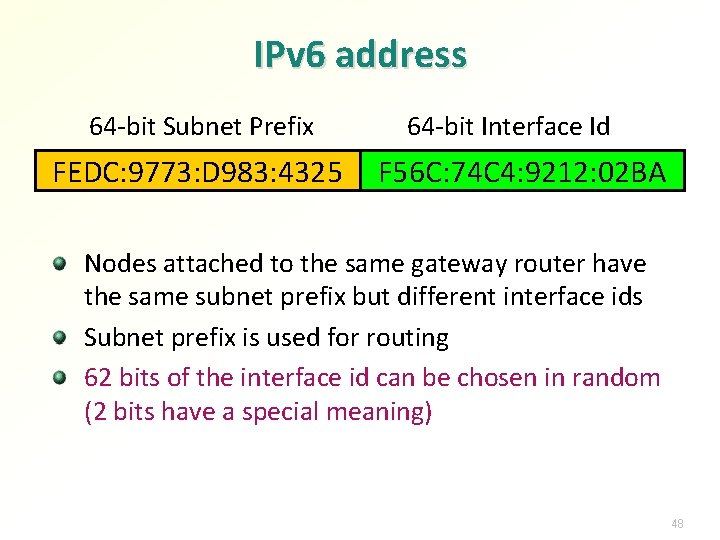
IPv 6 address 64 -bit Subnet Prefix FEDC: 9773: D 983: 4325 64 -bit Interface Id F 56 C: 74 C 4: 9212: 02 BA Nodes attached to the same gateway router have the same subnet prefix but different interface ids Subnet prefix is used for routing 62 bits of the interface id can be chosen in random (2 bits have a special meaning) 48
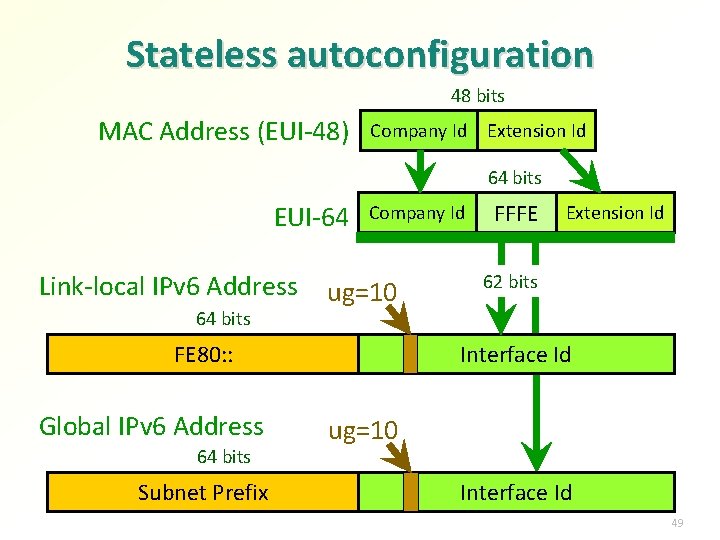
Stateless autoconfiguration 48 bits MAC Address (EUI-48) Company Id Extension Id 64 bits EUI-64 Link-local IPv 6 Address 64 bits Company Id ug=10 FE 80: : Global IPv 6 Address 64 bits Subnet Prefix FFFE Extension Id 62 bits Interface Id ug=10 Interface Id 49
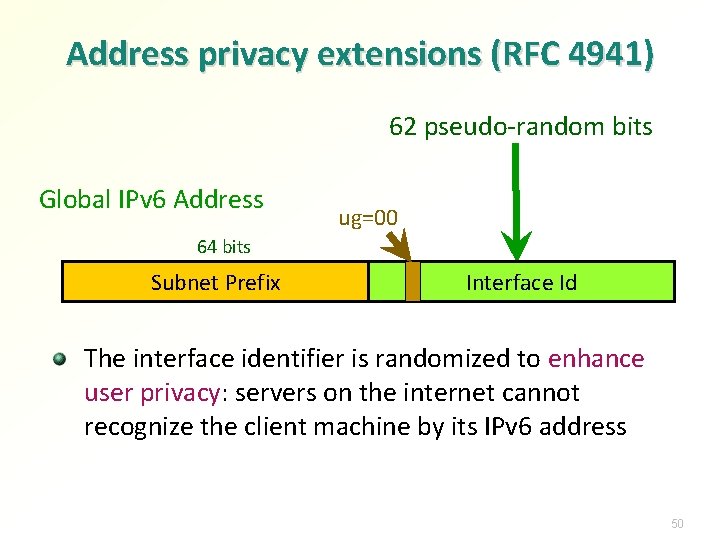
Address privacy extensions (RFC 4941) 62 pseudo-random bits Global IPv 6 Address ug=00 64 bits Subnet Prefix Interface Id The interface identifier is randomized to enhance user privacy: servers on the internet cannot recognize the client machine by its IPv 6 address 50
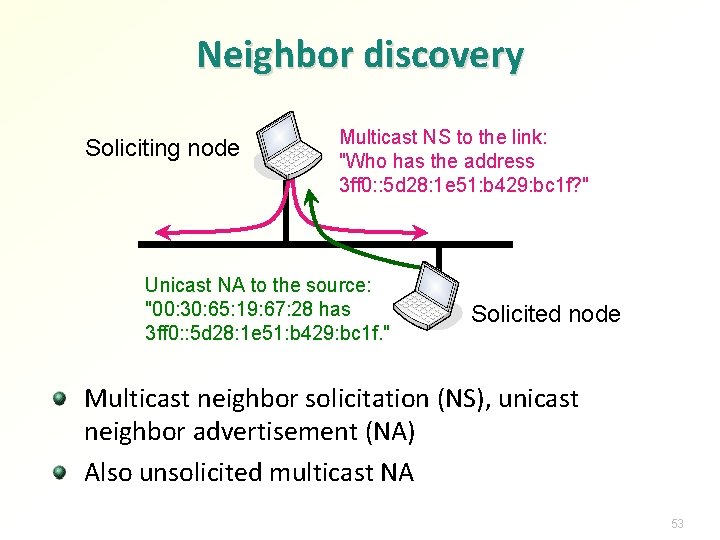
Neighbor discovery Soliciting node Multicast NS to the link: "Who has the address 3 ff 0: : 5 d 28: 1 e 51: b 429: bc 1 f? " Unicast NA to the source: "00: 30: 65: 19: 67: 28 has 3 ff 0: : 5 d 28: 1 e 51: b 429: bc 1 f. " Solicited node Multicast neighbor solicitation (NS), unicast neighbor advertisement (NA) Also unsolicited multicast NA 53
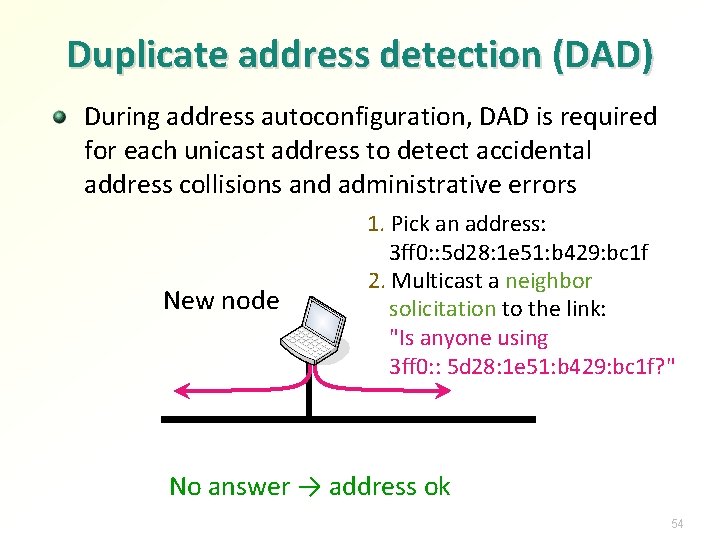
Duplicate address detection (DAD) During address autoconfiguration, DAD is required for each unicast address to detect accidental address collisions and administrative errors New node 1. Pick an address: 3 ff 0: : 5 d 28: 1 e 51: b 429: bc 1 f 2. Multicast a neighbor solicitation to the link: "Is anyone using 3 ff 0: : 5 d 28: 1 e 51: b 429: bc 1 f? " No answer → address ok 54
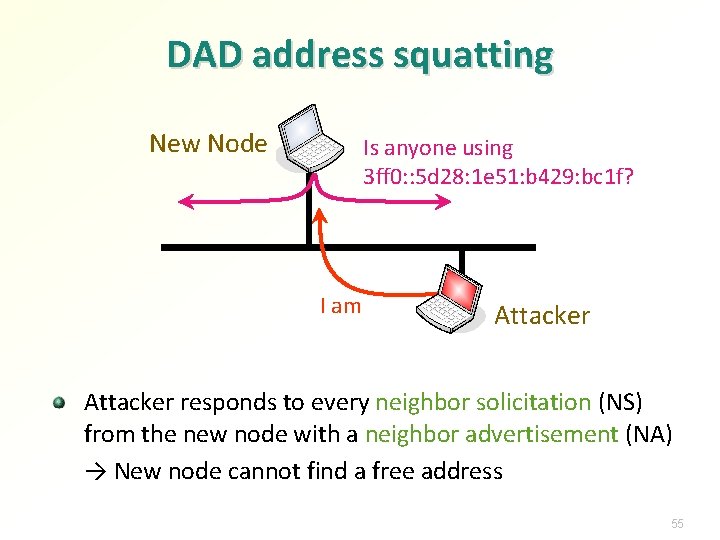
DAD address squatting New Node Is anyone using 3 ff 0: : 5 d 28: 1 e 51: b 429: bc 1 f? I am Attacker responds to every neighbor solicitation (NS) from the new node with a neighbor advertisement (NA) → New node cannot find a free address 55
Cryptographically generated addresses (CGA)
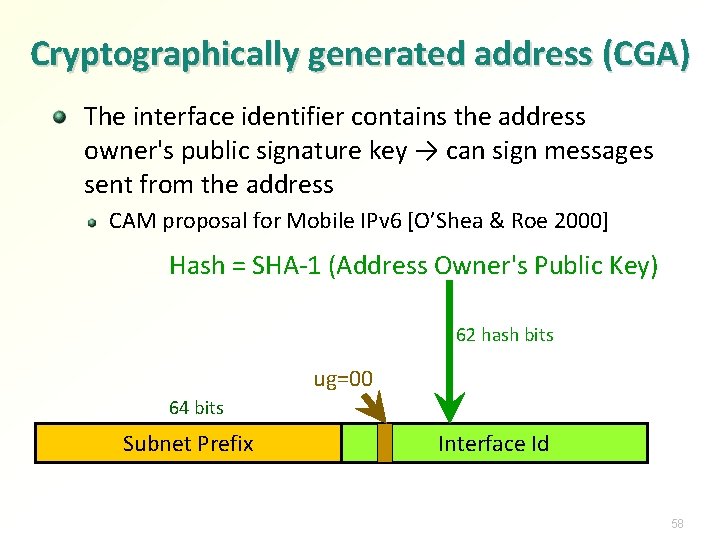
Cryptographically generated address (CGA) The interface identifier contains the address owner's public signature key → can sign messages sent from the address CAM proposal for Mobile IPv 6 [O’Shea & Roe 2000] Hash = SHA-1 (Address Owner's Public Key) 62 hash bits ug=00 64 bits Subnet Prefix Interface Id 58
Proof of address ownership Node sends the public key and a signed message from the CGA address Receiver Recomputes the hash of the public key Compares the hash with the interface id of the source address Verifies the signature using the public key → Receiver knows that the message was sent by the owner of the source address CGA-signing can prevent spoofing of IP-layer signaling messages such as neighbor advertisements 59
Hash extension The hash in CGA is at most 62 hash bits → vulnerable to brute-force attacks in the foreseeable future Moore’s law (one variation): CPU speed doubles every 18 months → one bit of hash strength lost → in about 30 years, CGA might be useless Already too weak for strong authentication but still ok for Do. S protection Solution: Increase artificially the cost of a brute-force attack Cost of creating a CGA will increase by the same factor Allow CGA creator to decide how much extra strength is needed Cost of using CGA (signing and verifying) will stay constant 61
![Standard CGA address format [RFC 3972] Hash 1 = SHA-1 (Public Key, Modifier, Subnet Standard CGA address format [RFC 3972] Hash 1 = SHA-1 (Public Key, Modifier, Subnet](http://slidetodoc.com/presentation_image_h2/35456accab0c40dbf56ca88f28955e70/image-48.jpg)
Standard CGA address format [RFC 3972] Hash 1 = SHA-1 (Public Key, Modifier, Subnet Prefix, Collision Count) Security Parameter (Sec) 64 bits Subnet Prefix 59 hash bits 3 bits Interface Id ug=00 Hash 2 = SHA-1 (Public Key, Modifier, 0, 0) = 000… 000 xxx…xxx 2 Modifier must be chosen so that Hash 2 begins with 16*Sec zero bits. 62
CGA limitations DNS names must be mapped to IP addresses → CGA-based authentication prevents spoofing of source IP addresses; it does not prevent DNS spoofing Authenticates the interface identifiers only, not the subnet prefix (=location in the network topology) CGA-based authentication prevents spoofing of someone else’s IP address. An attacker can generate a new address with any subnet prefix. CGA does not prove that the node or address exists Attacks against link layer may be just as bad 64
CGA advantages Authentication of an IP address without a PKI or other security infrastructure With Secure DNS, gives strong host authentication Without Secure DNS, prevents many Do. S attacks Particularly suitable for authenticating IP-layer signaling 65
Exercises Based on the historical flaws in Mobile IPv 6, are there any potential security problems in dynamic DNS? Does Secure DNS solve these problems? Could a SIP INVITE specify a false destination for a data stream? How could this be prevented? Design a more efficient binding-update protocol for Mobile IPv 6 assuming a global PKI is available How could the return-routability test for the care-of address (Co. A RR) be optimized if the mobile is opening a TCP connection? What are the advantages and disadvantages? What problems arise if the mobile node can automatically pick a home agent in any network that has one? 73
Exercises Why cannot CGA-based authentication prevent all IP sourceaddress spoofing? Can CGA-based authentication prevent IP source-address spoofing in DDo. S attacks? Why? What would be the advantages and limitations of using CGAbased authentication with IPSec? Design cryptographically generated MAC addresses for Ethernet. How would they be used? How to use CGA-based authentication with IPSec? What are the benefits and limitations? 74
- Slides: 52