Network Security Security of Internet Mobility Tuomas Aura
Network Security: Security of Internet Mobility Tuomas Aura T-110. 5241 Network security Aalto University, Nov-Dec 2011
Outline Mobile IPv 6 Spoofed bindings, bombing attack Return routability test 2
Mobile IPv 6
Mobile IPv 6 and addresses The mobile node (MN) has two IPv 6 addresses Home address (Ho. A): Subnet prefix of the home network Used as address when MN is at home. Used as node identifier when MN is roaming in a foreign network Home network may be virtual – MN never at home. Care-of address (Co. A): MN’s current point of attachment to the Internet Subnet prefix of the foreign network Correspondent node (CN) can be any Internet host (Note: MN and CN are hosts, not routers. ) 5
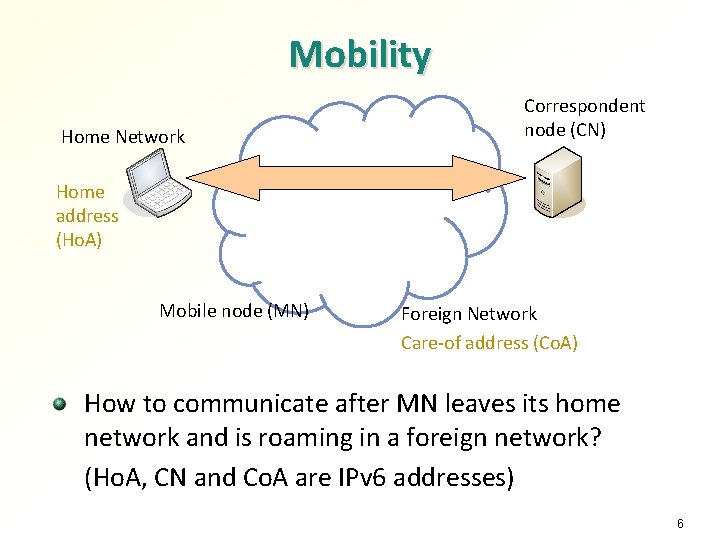
Mobility Home Network Correspondent node (CN) Home address (Ho. A) Mobile node (MN) Foreign Network Care-of address (Co. A) How to communicate after MN leaves its home network and is roaming in a foreign network? (Ho. A, CN and Co. A are IPv 6 addresses) 6
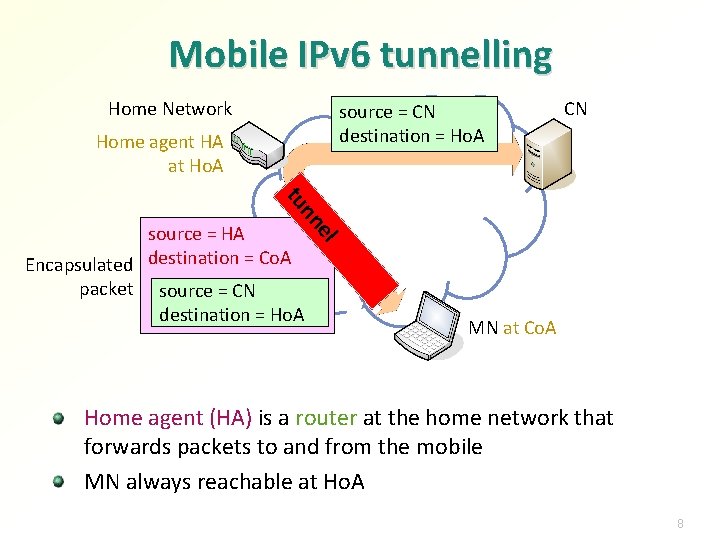
Mobile IPv 6 tunnelling Home Network source = CN destination = Ho. A Home agent HA at Ho. A CN e nn tu l source = HA Encapsulated destination = Co. A packet source = CN destination = Ho. A MN at Co. A Home agent (HA) is a router at the home network that forwards packets to and from the mobile MN always reachable at Ho. A 8
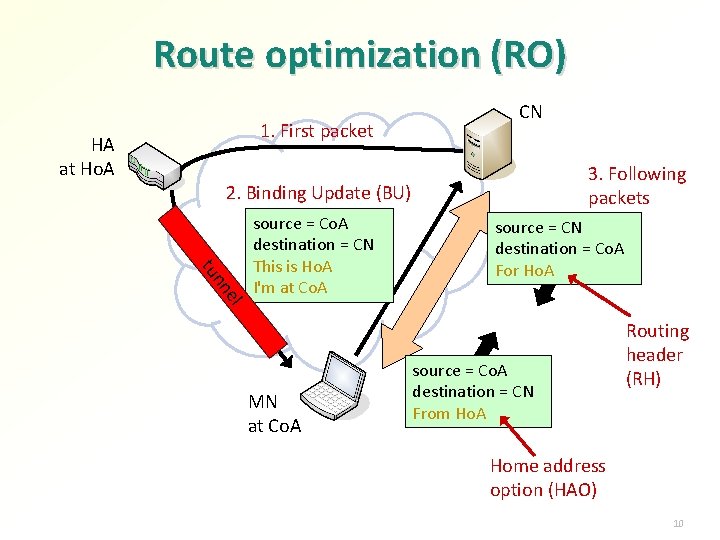
Route optimization (RO) 1. First packet HA at Ho. A CN 3. Following packets 2. Binding Update (BU) tu el nn source = Co. A destination = CN This is Ho. A I'm at Co. A MN at Co. A source = CN destination = Co. A For Ho. A source = Co. A destination = CN From Ho. A Routing header (RH) Home address option (HAO) 10

Threats and protection mechanisms All weaknesses shown here have been addresses in the RFC 15
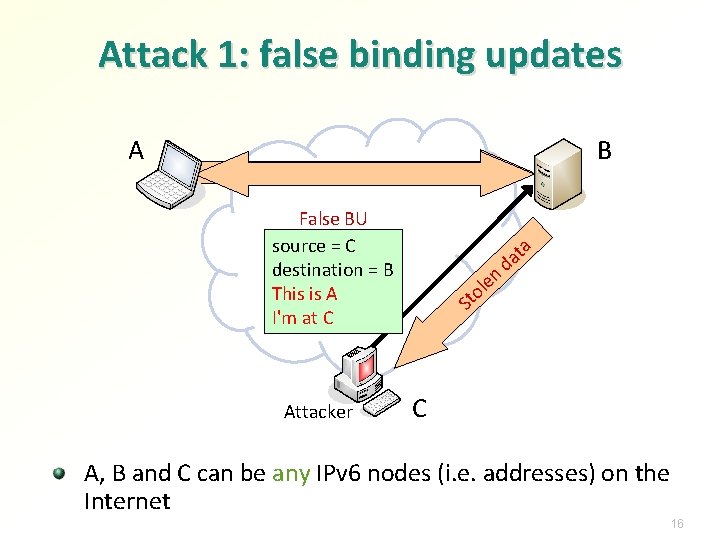
Attack 1: false binding updates A B False BU source = C destination = B This is A I'm at C Attacker n e ol St ta a d C A, B and C can be any IPv 6 nodes (i. e. addresses) on the Internet 16
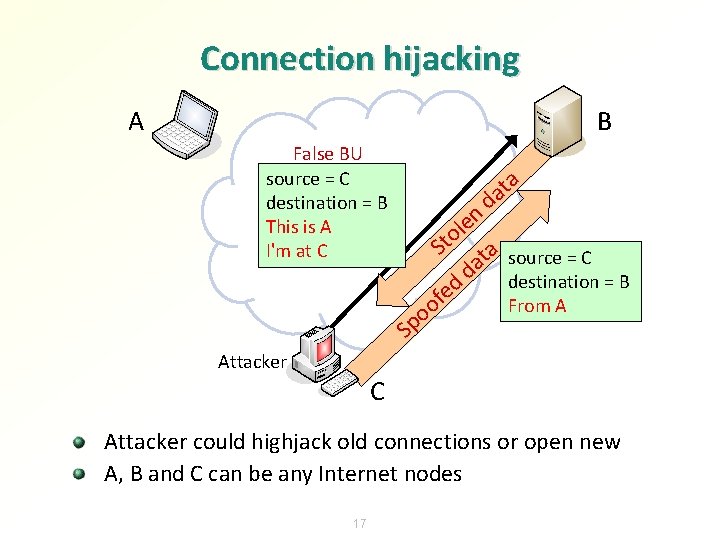
Connection hijacking A B False BU source = C destination = B This is A I'm at C a t a d en l o t S ta source = C a d destination = B ed f From A o o p S Attacker C Attacker could highjack old connections or open new A, B and C can be any Internet nodes 17
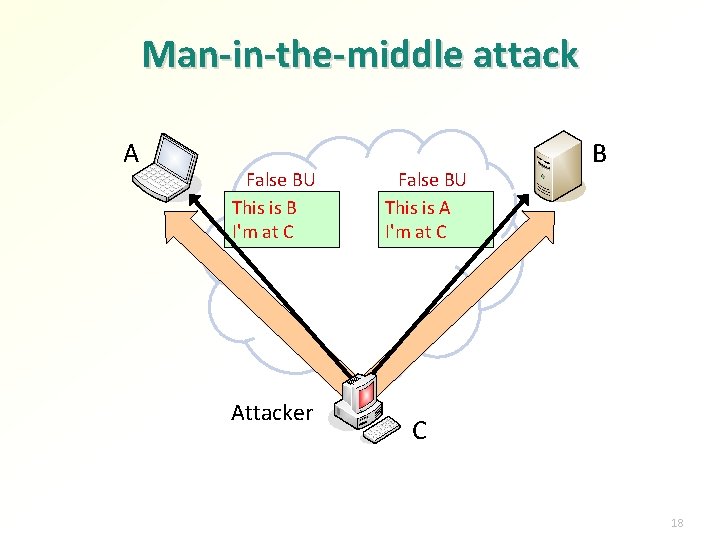
Man-in-the-middle attack A False BU This is B I'm at C Attacker False BU This is A I'm at C B C 18
If no security measures added Attacker anywhere on the Internet can hijack connection between any two Internet nodes, or spoof such a connection Attacker must know the IPv 6 addresses of the target nodes, though 19
BU authentication MN and HA trust each other and can have a secure tunnel between them. Authenticating BUs to CN is the problem The obvious solution is strong cryptographic authentication of BUs Problem: there is no global system for authenticating any Internet node 20
Authentication without infrastructure? How authenticate messages between any two IPv 6 nodes, without introducing new security infrastructure? Set requirements to the right level: Internet with Mobile IPv 6 deployed must be as secure as before it → no general-purpose strong authentication needed Some IP-layer infrastructure is available: IPv 6 addresses Routing infrastructure Surprisingly, both can be used for BU authentication: Cryptographically generated addresses (CGA) Routing-based “weak” authentication, called return routability 21
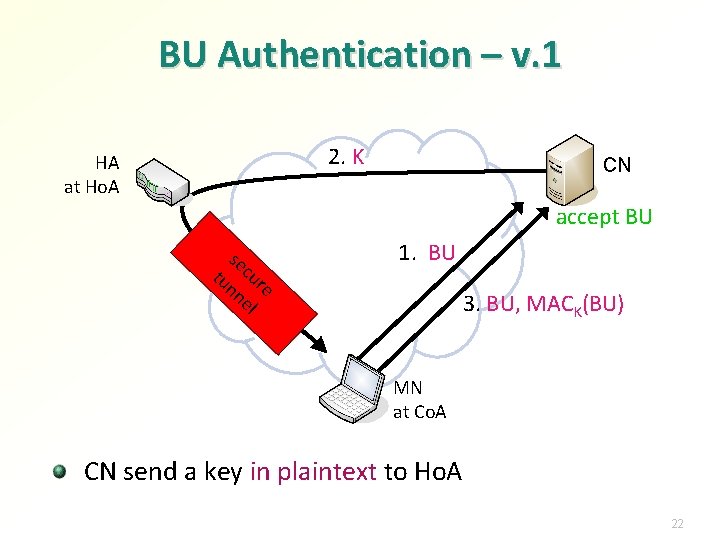
BU Authentication – v. 1 2. K HA at Ho. A CN accept BU se tu cur nn e el 1. BU 3. BU, MACK(BU) MN at Co. A CN send a key in plaintext to Ho. A 22
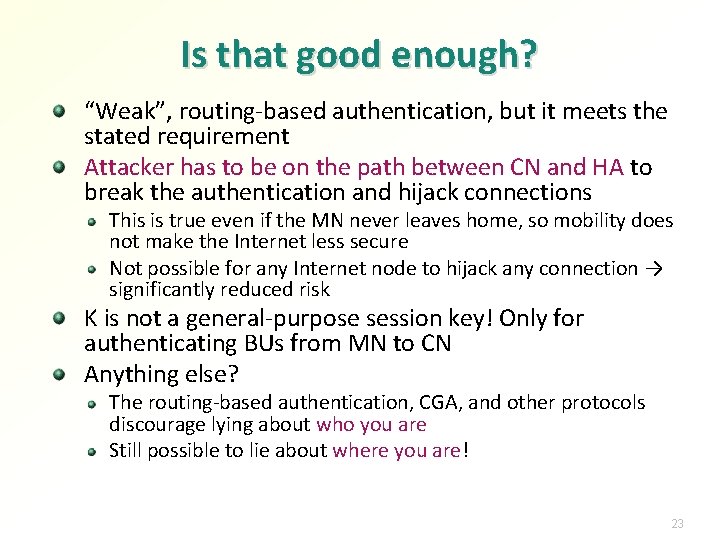
Is that good enough? “Weak”, routing-based authentication, but it meets the stated requirement Attacker has to be on the path between CN and HA to break the authentication and hijack connections This is true even if the MN never leaves home, so mobility does not make the Internet less secure Not possible for any Internet node to hijack any connection → significantly reduced risk K is not a general-purpose session key! Only for authenticating BUs from MN to CN Anything else? The routing-based authentication, CGA, and other protocols discourage lying about who you are Still possible to lie about where you are! 23
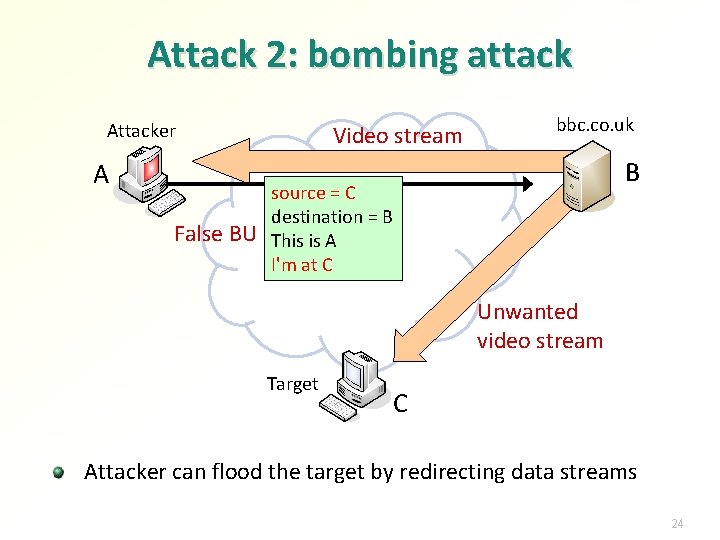
Attack 2: bombing attack Attacker A False BU Video stream bbc. co. uk B source = C destination = B This is A I'm at C Unwanted video stream Target C Attacker can flood the target by redirecting data streams 24
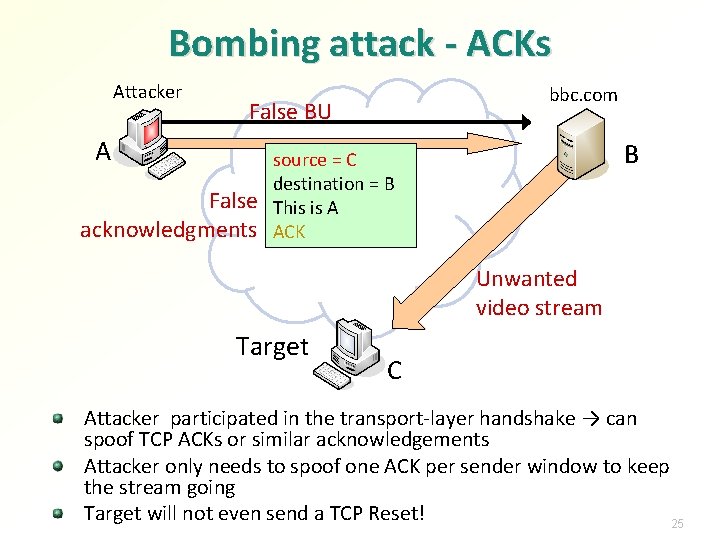
Bombing attack - ACKs Attacker A A bbc. com False BU False acknowledgments B source = C destination = B This is A ACK Unwanted video stream Target C Attacker participated in the transport-layer handshake → can spoof TCP ACKs or similar acknowledgements Attacker only needs to spoof one ACK per sender window to keep the stream going Target will not even send a TCP Reset! 25
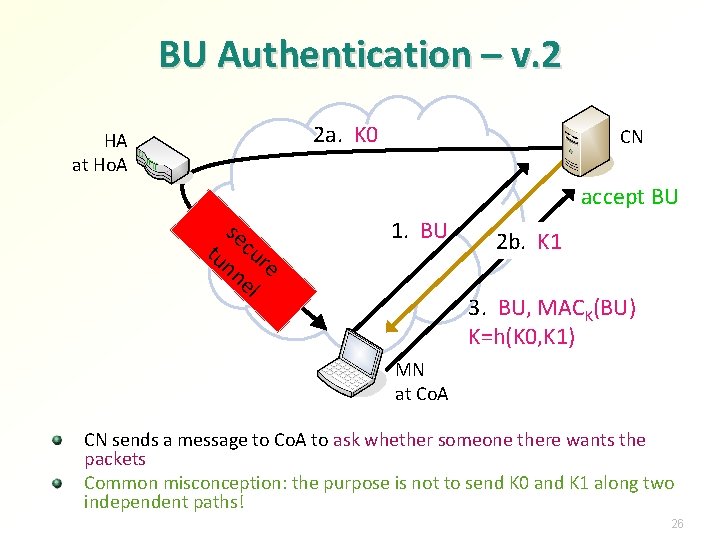
BU Authentication – v. 2 2 a. K 0 HA at Ho. A CN accept BU se tu cur nn e el 1. BU 2 b. K 1 3. BU, MACK(BU) K=h(K 0, K 1) MN at Co. A CN sends a message to Co. A to ask whether someone there wants the packets Common misconception: the purpose is not to send K 0 and K 1 along two independent paths! 26
Is that good enough? Not possible to lie about identity or location; all information in BUs is true Almost ready, but we still need to consider standard denial of service attacks against the BU protocol 27
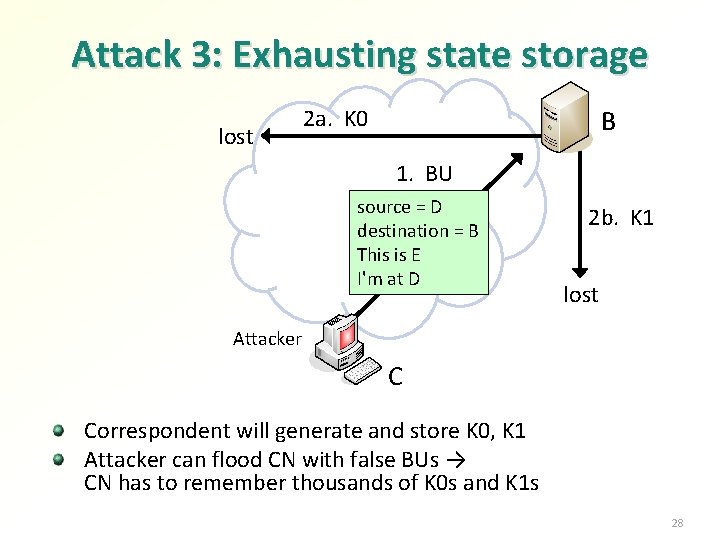
Attack 3: Exhausting state storage lost 2 a. K 0 B 1. BU source = D destination = B This is E I'm at D 2 b. K 1 lost Attacker C Correspondent will generate and store K 0, K 1 Attacker can flood CN with false BUs → CN has to remember thousands of K 0 s and K 1 s 28
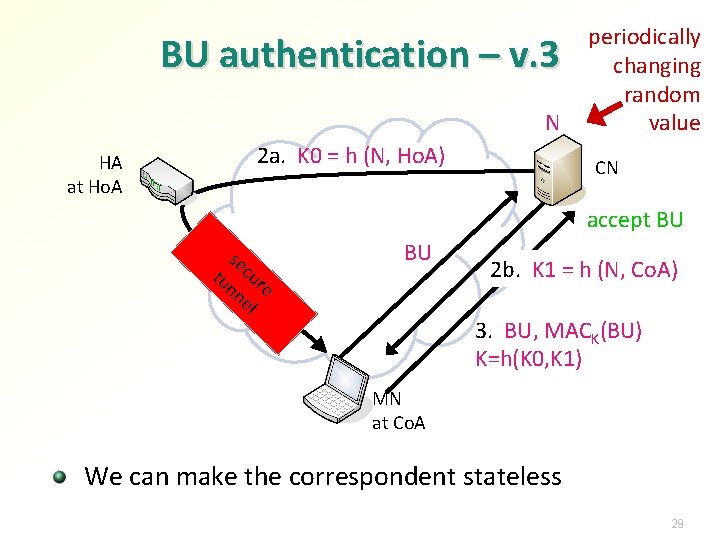
BU authentication – v. 3 N HA at Ho. A 2 a. K 0 = h (N, Ho. A) periodically changing random value CN accept BU se tu cur nn e el 1. BU 2 b. K 1 = h (N, Co. A) 3. BU, MACK(BU) K=h(K 0, K 1) MN at Co. A We can make the correspondent stateless 29
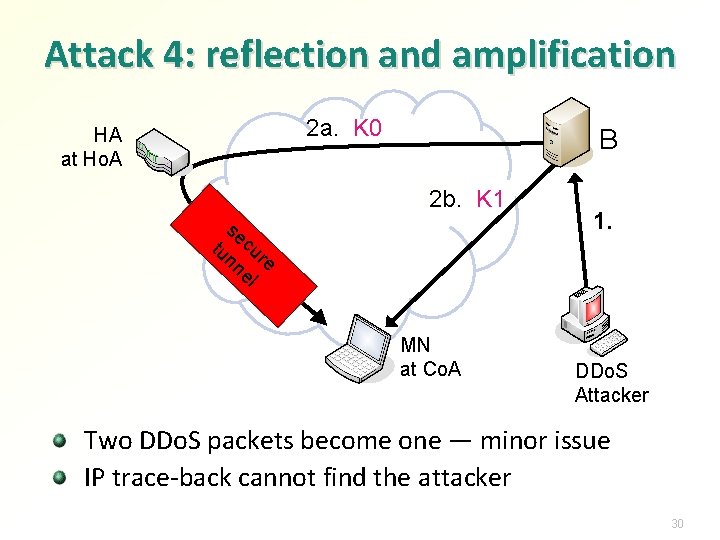
Attack 4: reflection and amplification 2 a. K 0 HA at Ho. A B 2 b. K 1 se tu cur nn e el MN at Co. A 1. DDo. S Attacker Two DDo. S packets become one — minor issue IP trace-back cannot find the attacker 30
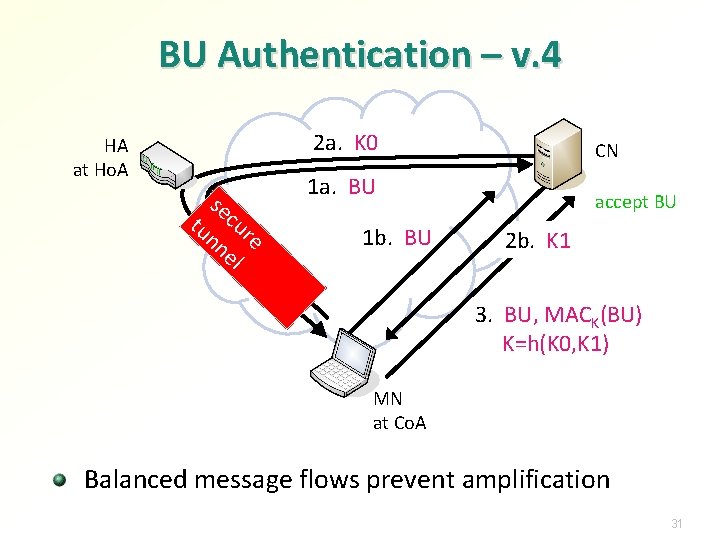
BU Authentication – v. 4 2 a. K 0 HA at Ho. A se tu cur nn e el CN 1 a. BU 1 b. BU accept BU 2 b. K 1 3. BU, MACK(BU) K=h(K 0, K 1) MN at Co. A Balanced message flows prevent amplification 31
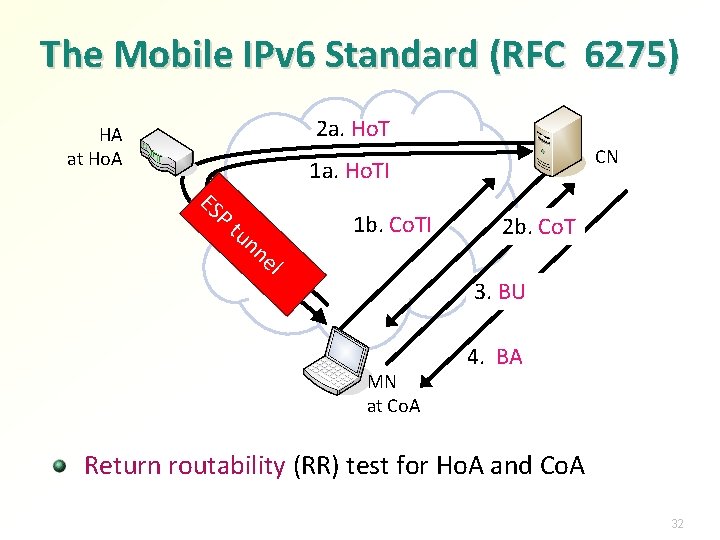
The Mobile IPv 6 Standard (RFC 6275) 2 a. Ho. T HA at Ho. A CN ES 1 a. Ho. TI P tu nn 1 b. Co. TI el 2 b. Co. T 3. BU MN at Co. A 4. BA Return routability (RR) test for Ho. A and Co. A 32
Puzzle of the day Compare identity protection in PGP Kerberos TLS + username and password in web form TLS + HTTP Digest Authentication EAP-TLS PEAP-MSCHAP 2 IPsec. 1. Can a passive sniffer learn the identities of the authenticating parties? 2. What about active attackers? 3. Does one side in the protocol have an advantage? 34
Exercises Based on the historical flaws in Mobile IPv 6, are there any potential security problems in dynamic DNS? Does Secure DNS solve these problems? Could a SIP INVITE specify a false destination for a data stream? How could this be prevented? Design a more efficient binding-update protocol for Mobile IPv 6 assuming a global PKI is available How could the return-routability test for the care-of address (Co. A RR) be optimized if the mobile is opening a TCP connection? What are the advantages and disadvantages? What problems arise if mobile node can automatically pick a home agent in any network? 35
- Slides: 27