Lecture 1 BASIC NETWORK CONCEPTS PGT 307 PROGRAMMING
Lecture 1: BASIC NETWORK CONCEPTS PGT 307: PROGRAMMING FOR NETWORKING norfazlin@unimap. edu. my ©The Mc. Graw-Hill Companies, Inc.
Networks “ v A group of computers and devices connected in some ways so as to be able v to exchange data. Each of the devices on the network can be “ thought of as a node, each node has a unique address.
Node “ v Each machine on a network is called a node can be computers, routers, bridges, gateways, dumb terminals, printers etc “ Nodes that are fully functional computers are also called hosts.
Address v Every network node has an address, a series of bytes that uniquely identify it. Eg: 204. 160. 241. 98 v The more bytes there are in each address, the more addresses there available and the more devices that can be connected to the network simultaneously. v Some networks also provide names that humans can more easily remember than numbers. Eg: www. javasoft. com, corresponding to the above numeric address.
Packet v All modern computer networks are packet switched networks: v Data traveling on the network is broken into chunks called packets and each packet is handled separately. v Each packet contains information about who sent it and where it's going.
Protocols “ v A protocol is a precise set of rules defining how computers communicate: the format of addresses, how data is split v into packets, and so on.
Protocols v There are many different protocols defining different aspects of network communication. v Roles: addressing and routing of messages, error detection and recovery, sequence and flow controls. v Specification: consists of the syntax, which defines the kinds and formats of the messages exchanged, and the semantic, which specifies the action taken by each entity when specific events occur. v Example: HTTP protocol for communication between web browsers and servers. v Open, published protocol standards allow software and equipment from different vendors to communicate with one another
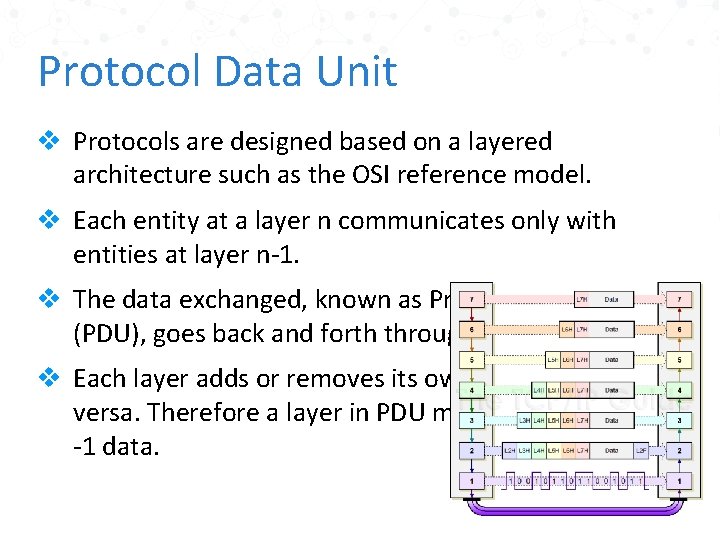
Protocol Data Unit v Protocols are designed based on a layered architecture such as the OSI reference model. v Each entity at a layer n communicates only with entities at layer n-1. v The data exchanged, known as Protocol Data Unit (PDU), goes back and forth through the layers. v Each layer adds or removes its own header and viceversa. Therefore a layer in PDU may become a layer n -1 data.
Layers of a Network Sending data across a network is a complex operation that must be carefully tuned There are several different layer models, each organized to fit the needs of a particular kind of network.
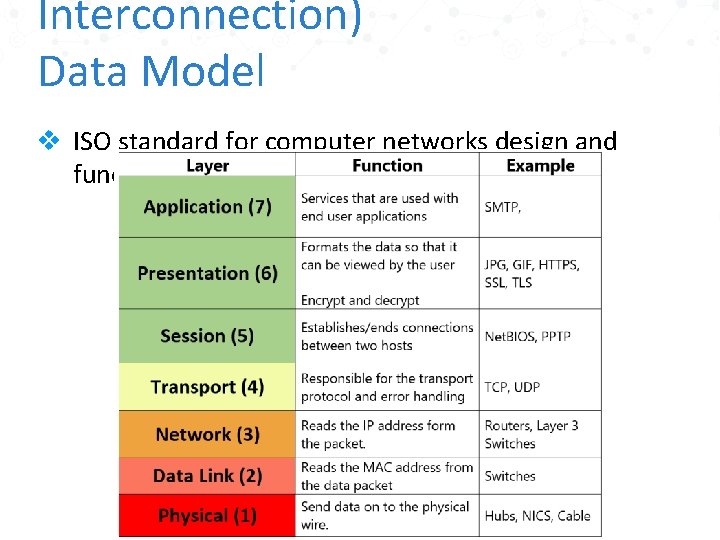
Interconnection) Data Model v ISO standard for computer networks design and functioning.
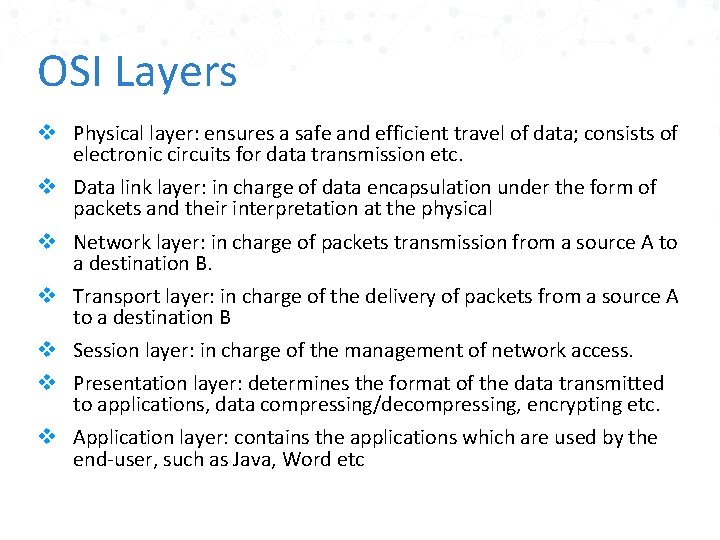
OSI Layers v Physical layer: ensures a safe and efficient travel of data; consists of electronic circuits for data transmission etc. v Data link layer: in charge of data encapsulation under the form of packets and their interpretation at the physical v Network layer: in charge of packets transmission from a source A to a destination B. v Transport layer: in charge of the delivery of packets from a source A to a destination B v Session layer: in charge of the management of network access. v Presentation layer: determines the format of the data transmitted to applications, data compressing/decompressing, encrypting etc. v Application layer: contains the applications which are used by the end-user, such as Java, Word etc
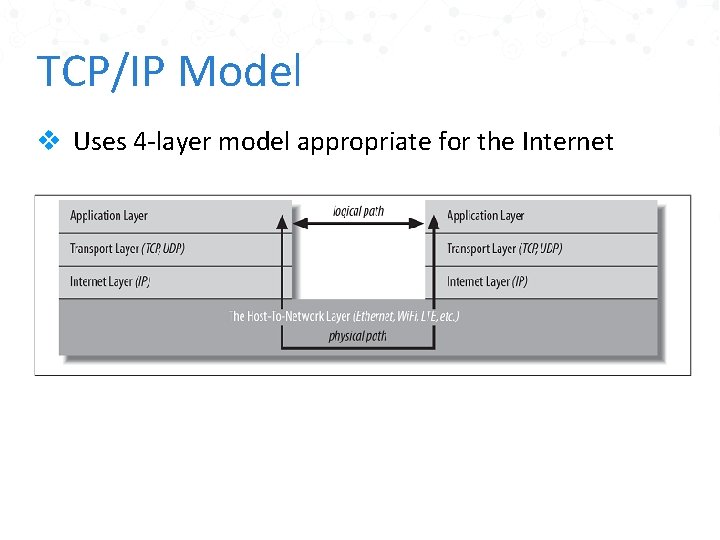
TCP/IP Model v Uses 4 -layer model appropriate for the Internet
TCP/IP: The Host-to-Network Layer v Also known as the link layer, data link layer, or network interface layer. v The host-to-network layer defines how a particular network interface (eg: Ethernet card, Wi. Fi antenna) sends IP datagrams over its physical connection to the local network and the world.
TCP/IP: The Internet Layer v Defines how bits and bytes of data are organized into the larger groups called packets, and the addressing scheme by which different machines find each other. DATAGRAMS ● Data is sent across the internet layer in packets called datagrams. ● Each IP datagram contains a header between 20 and 60 bytes long and a payload that contains up to 65, 515 bytes of data.
TCP/IP: The Transport Layer v Responsible for ensuring that packets are received in the order they were sent v Making sure that no data is lost or corrupted.
TCP/IP: The Application Layer v The layer that delivers data to the user is called the application layer. v Decides what to do with the data after it is transferred.
IP, TCP, and UDP IP: Internet protocol TCP: Transmission Control Protocol UDP: User Datagram Protocol
Internet Protocol v Designed to allow multiple routes between any two points to route packets of data around damaged routers. v The IP protocol provides two main functionality: è Decomposition of the initial information flow into packets of standardized size, and reassembling at the destination. è Routing of a packet through successive networks, from the source machine to the destination identified by its IP address. v The IP protocol does not request for connection (connectionless) before sending data and does not make any error detection.
Internet Protocol Functions v Decompose the initial data (to be sent) into datagrams. v Each datagram will have a header including, the IP address and the port number of the destination. v Datagrams are then sent to selected gateways, e. g IP routers, connected at the same time to the local network and to an IP service provider network. v Datagrams are transferred from gateways to gateways until they arrived at their final destination.
Transmission Control Protocol (TCP) v Since there are multiple routes between two points, and since the quickest path between two points may change over time as a function of network traffic and other factors), the packets that make up a particular data stream may not all take the same route. v They may not arrive in the order they were sent, if they even arrive at all. v TCP provides by using IP packets a basic service that does guarantee safe delivery: è error detection è safe data transmission è assurance that data are received in the correct order
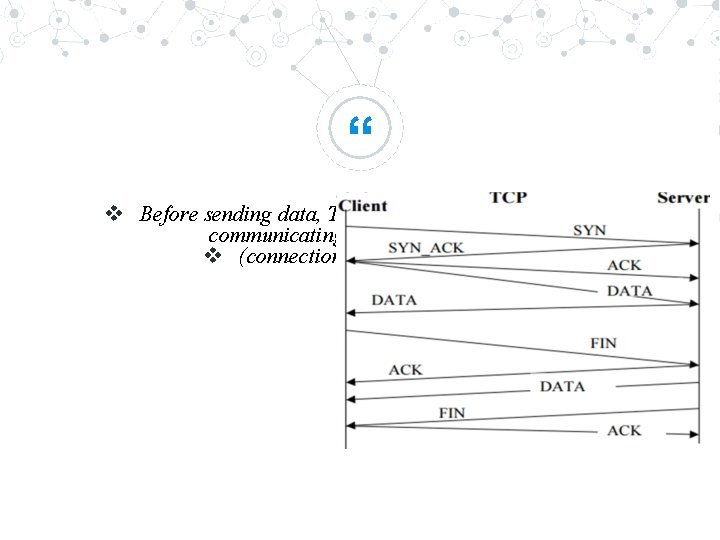
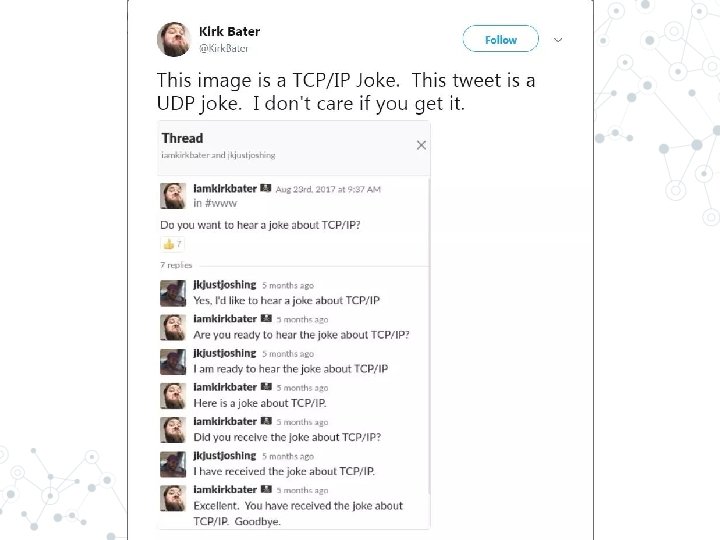
“ v Before sending data, TCP requires that the computers communicating establish a connection v (connection-oriented protocol)
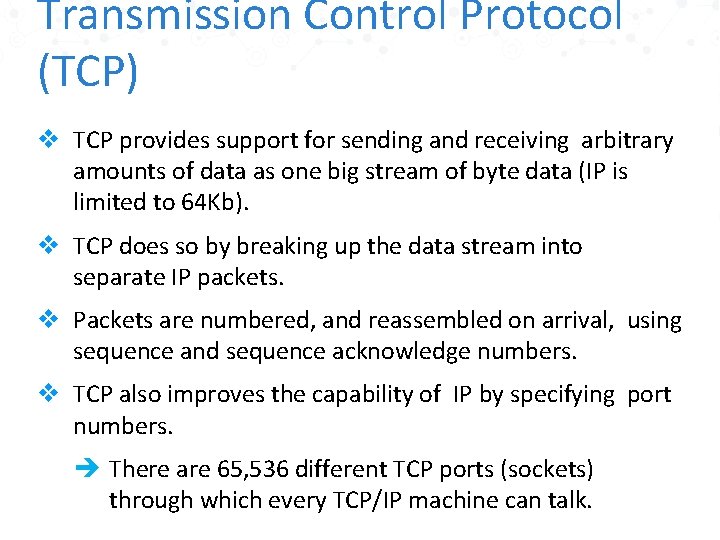
Transmission Control Protocol (TCP) v TCP provides support for sending and receiving arbitrary amounts of data as one big stream of byte data (IP is limited to 64 Kb). v TCP does so by breaking up the data stream into separate IP packets. v Packets are numbered, and reassembled on arrival, using sequence and sequence acknowledge numbers. v TCP also improves the capability of IP by specifying port numbers. è There are 65, 536 different TCP ports (sockets) through which every TCP/IP machine can talk.
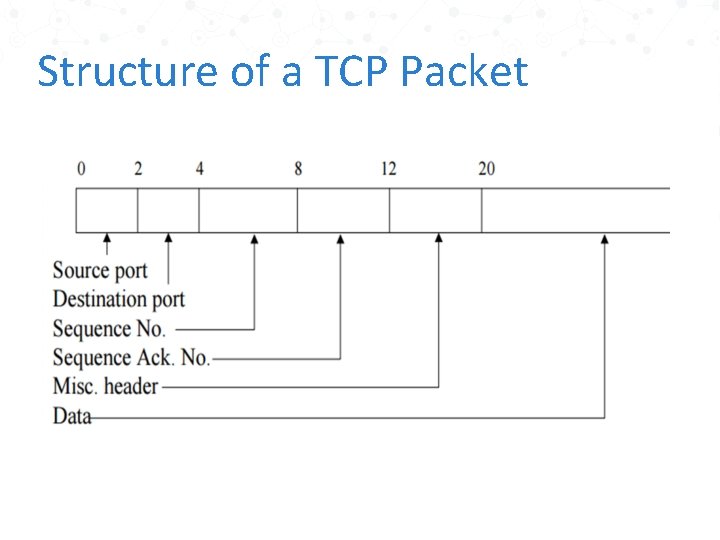
Structure of a TCP Packet
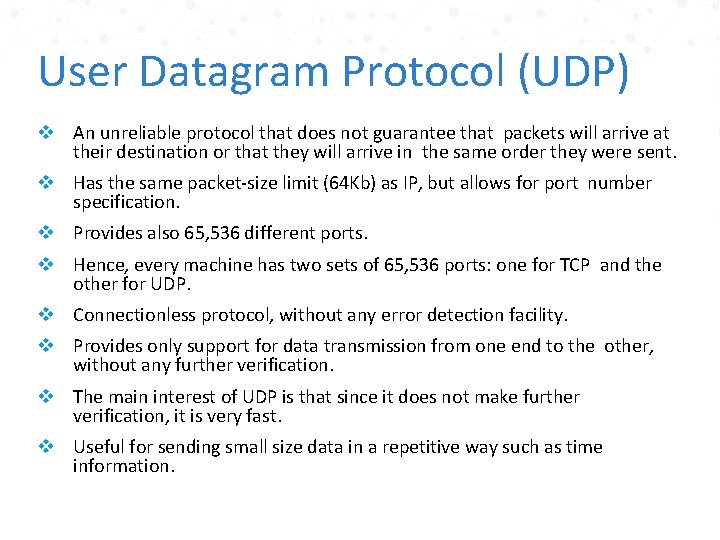
User Datagram Protocol (UDP) v An unreliable protocol that does not guarantee that packets will arrive at their destination or that they will arrive in the same order they were sent. v Has the same packet-size limit (64 Kb) as IP, but allows for port number specification. v Provides also 65, 536 different ports. v Hence, every machine has two sets of 65, 536 ports: one for TCP and the other for UDP. v Connectionless protocol, without any error detection facility. v Provides only support for data transmission from one end to the other, without any further verification. v The main interest of UDP is that since it does not make further verification, it is very fast. v Useful for sending small size data in a repetitive way such as time information.
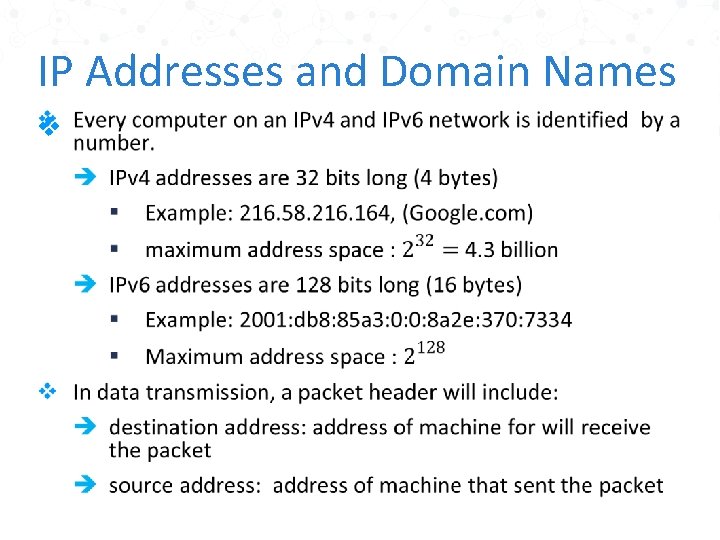
IP Addresses and Domain Names v
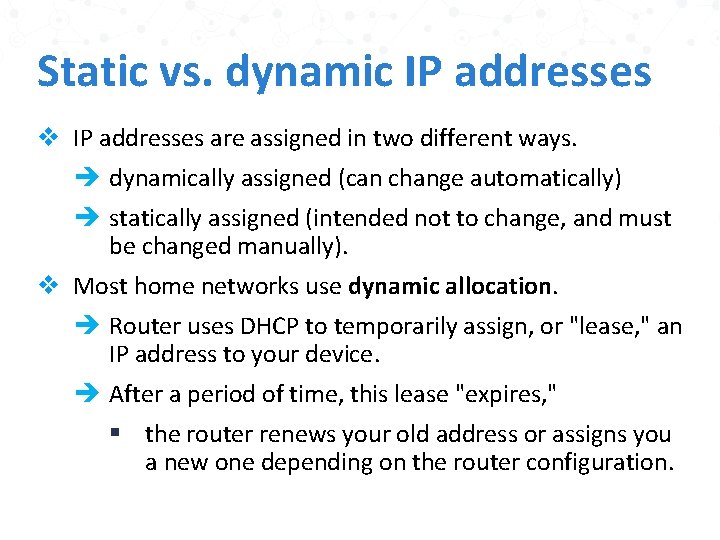
Static vs. dynamic IP addresses v IP addresses are assigned in two different ways. è dynamically assigned (can change automatically) è statically assigned (intended not to change, and must be changed manually). v Most home networks use dynamic allocation. è Router uses DHCP to temporarily assign, or "lease, " an IP address to your device. è After a period of time, this lease "expires, " § the router renews your old address or assigns you a new one depending on the router configuration.
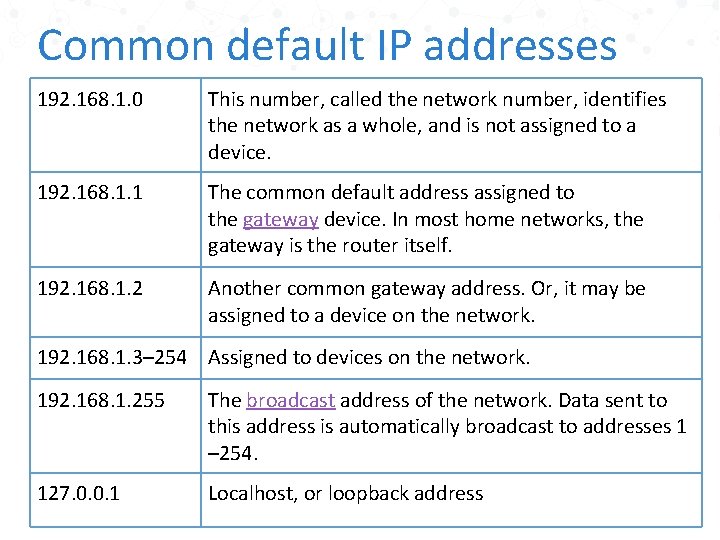
Common default IP addresses 192. 168. 1. 0 This number, called the network number, identifies the network as a whole, and is not assigned to a device. 192. 168. 1. 1 The common default address assigned to the gateway device. In most home networks, the gateway is the router itself. 192. 168. 1. 2 Another common gateway address. Or, it may be assigned to a device on the network. 192. 168. 1. 3– 254 Assigned to devices on the network. 192. 168. 1. 255 The broadcast address of the network. Data sent to this address is automatically broadcast to addresses 1 – 254. 127. 0. 0. 1 Localhost, or loopback address
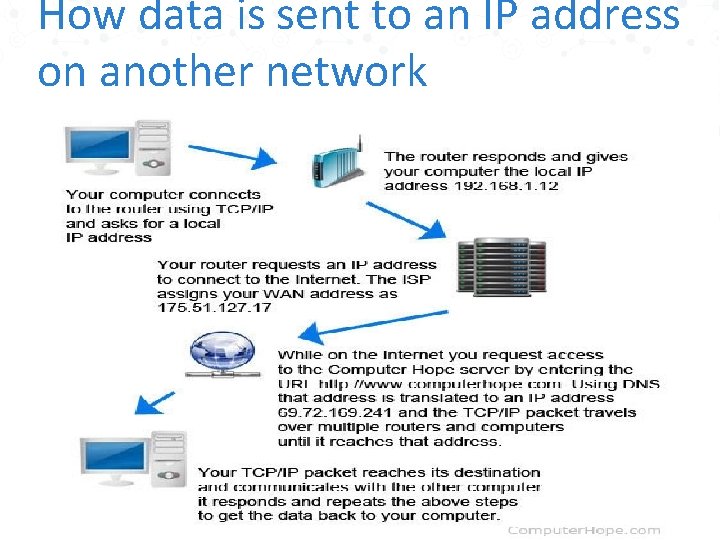
How data is sent to an IP address on another network
Domain Name System (DNS) v To translate hostnames that humans can remember (like www. math. hcmuns. edu. vn) into numeric Internet addresses (like 203. 162. 44. 37). v Mnemonic textual addresses are provided to facilitate the manipulation of internet addresses. v DNS servers are responsible for translating mnemonic textual Internet addresses into hard numeric Internet addresses.
Ports v Each computer with an IP address has several thousand logical ports. v Each port is identified by a number between 1 and 65, 535. Each port can be allocated to a particular service. v An IP address identifies a host machine on the Internet. v An IP port will identify a specific application running on an Internet host machine. v A port is identified by a number, the port number. v The number of ports is not functionally limited, in contrast to serial communications where only 4 ports are allowed. v There are some port numbers which are dedicated for specific applications.
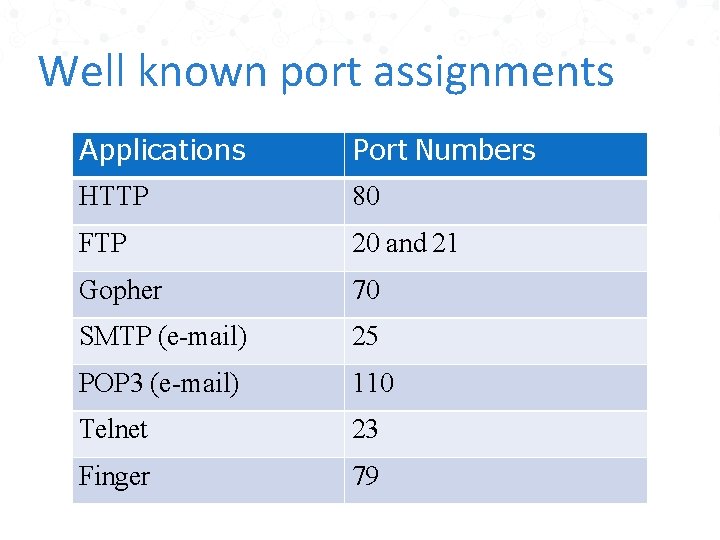
Well known port assignments Applications Port Numbers HTTP 80 FTP 20 and 21 Gopher 70 SMTP (e-mail) 25 POP 3 (e-mail) 110 Telnet 23 Finger 79
Classes of IP Address v IP addresses can be divided into 5 classes but we will focus on the 3 commonly used classes: è class A, class B, class C. v Subnet è A group of devices/hosts in a network segment. è All the hosts have the same prefix. è E. g: all device that starts with 192. 128. 2. X are in the same subnet. v Address Range: the first octet
Classes of IP Address v Class C address block specifies the first three bytes of the address; Eg: 199. 1. 32. v Class B address block only specifies the first two bytes of the addresses an organization may use; Eg: 167. 1. v Class A address block only specifies the first byte of the address range—for instance, 18—and therefore has room for over 16 million nodes. v Note: Each octet in IPv 4 must be between 0 to 254 only.
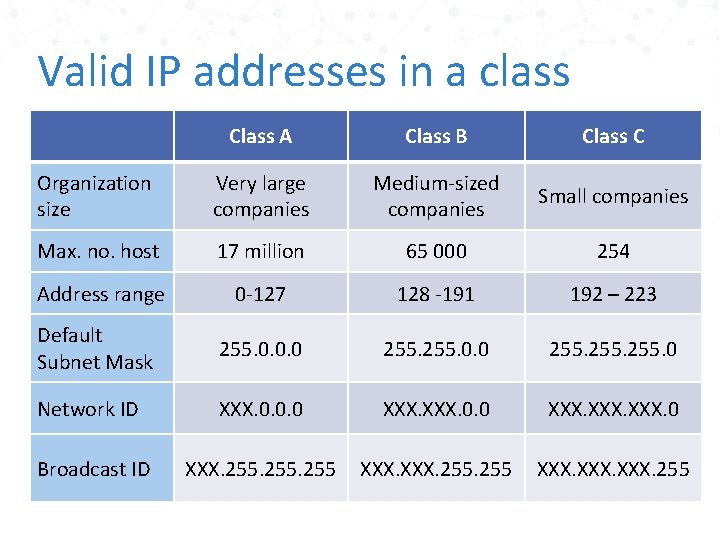
Valid IP addresses in a class Class A Class B Class C Organization size Very large companies Medium-sized companies Small companies Max. no. host 17 million 65 000 254 Address range 0 -127 128 -191 192 – 223 Default Subnet Mask 255. 0. 0. 0 255. 0 Network ID XXX. 0. 0. 0 XXX. 0 Broadcast ID XXX. 255 XXX. 255
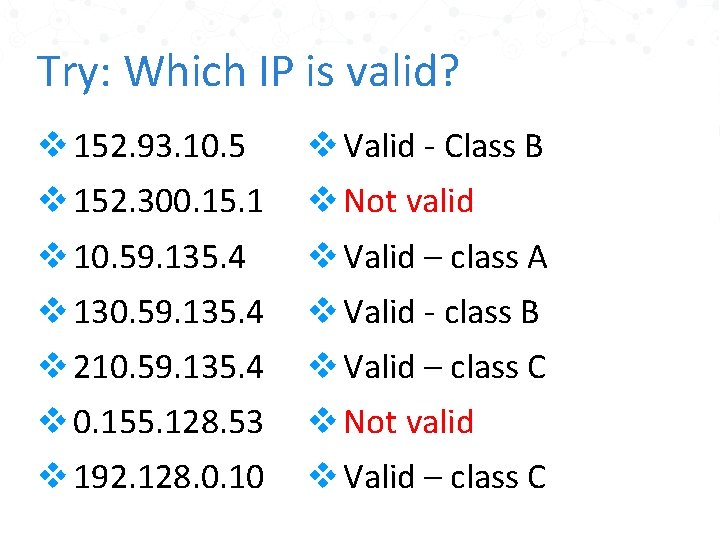
Try: Which IP is valid? v 152. 93. 10. 5 v Valid - Class B v 152. 300. 15. 1 v Not valid v 10. 59. 135. 4 v Valid – class A v 130. 59. 135. 4 v Valid - class B v 210. 59. 135. 4 v Valid – class C v 0. 155. 128. 53 v Not valid v 192. 128. 0. 10 v Valid – class C
Network Address Translation (NAT) v Because of the increasing scarcity of and demand for raw IP addresses, most networks today use Network Address Translation (NAT). v In NAT-based networks most nodes only have local, non-routable addresses selected from either 10. x. x. x, 172. 16. x. x to 172. 31. x. x, or 192. 168. x. x. v The routers that connect the local networks to the ISP translate these local addresses to a much smaller set of routable addresses.
Firewalls v The hardware and software that sit between the Internet and the local network, checking all the data that comes in or out to make sure it's kosher, is called a firewall. v Filtering is usually based on network addresses and ports. v For example, all traffic coming from the Class C network 193. 28. 25. x may be rejected because you had bad experiences with hackers from that network in the past.
Proxy Servers v If a firewall prevents hosts on a network from making direct connections to the outside world, a proxy server can act as a go-between. v Thus, a machine that is prevented from connecting to the external network by a firewall would make a request for a web page from the local proxy server instead of requesting the web page directly from the remote web server.
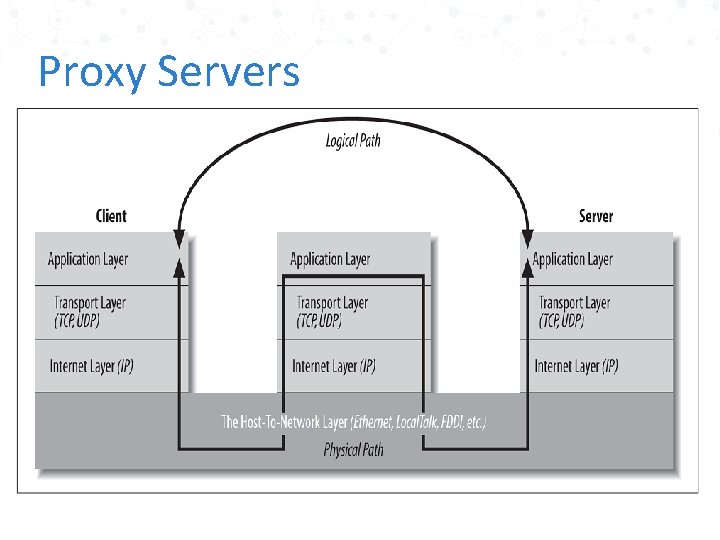
Proxy Servers
The Client/Server Model v Most modern network programming is based on a client/server model. v In most cases, a server primarily sends data while a client primarily receives it, but it is rare for one program to send or receive exclusively. v A more reliable distinction is that a client initiates a conversation while a server waits for clients to start conversations with it.
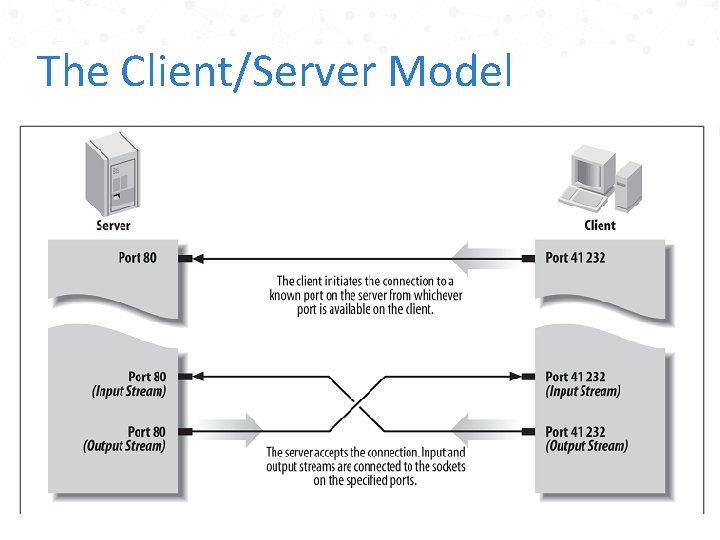
The Client/Server Model
Peer-to-peer v Not all applications fit easily into a client/server model. v For instance, in networked games, it seems likely that both players will send data back and forth roughly equally. v These sorts of connections are called peer-to-peer.

Internet Standards of application layer network programming and network protocols produced by standards organizations
Internet Engineering Task Force (IETF) v IETF is a relatively informal, democratic body open to participation by any interested party based on “rough consensus and running code” v IETF standards include TCP/IP, MIME, and SMTP. v Before something can become an IETF standard, it must actually exist and work.
World Wide Web Consortium (W 3 C) v Vendor organization, controlled by duespaying member corporations, that explicitly excludes participation by individuals. v Tries to define standards in advance of implementation v W 3 C standards include HTTP, HTML, and XML

THANK YOU
- Slides: 47