CSC 382 Computer Security Introduction to UNIX Programming
![Structure of a UNIX command #command [[ - ] option(s)] [option argument(s)] [command argument(s)] Structure of a UNIX command #command [[ - ] option(s)] [option argument(s)] [command argument(s)]](https://slidetodoc.com/presentation_image_h/0ad94690cd7f84d74f224eee0bb0f5a2/image-10.jpg)
![Obtaining Help with man [options][-s section] command-list # man ls User Commands ls(1) NAME Obtaining Help with man [options][-s section] command-list # man ls User Commands ls(1) NAME](https://slidetodoc.com/presentation_image_h/0ad94690cd7f84d74f224eee0bb0f5a2/image-15.jpg)
![printargs. c $ cat >printargs. c #include <stdio. h> int main(int argc, char *argv[]) printargs. c $ cat >printargs. c #include <stdio. h> int main(int argc, char *argv[])](https://slidetodoc.com/presentation_image_h/0ad94690cd7f84d74f224eee0bb0f5a2/image-29.jpg)
- Slides: 30
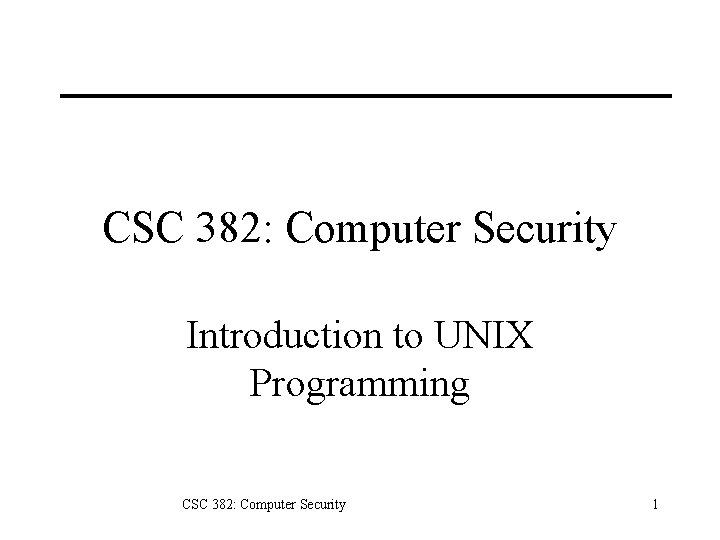
CSC 382: Computer Security Introduction to UNIX Programming CSC 382: Computer Security 1
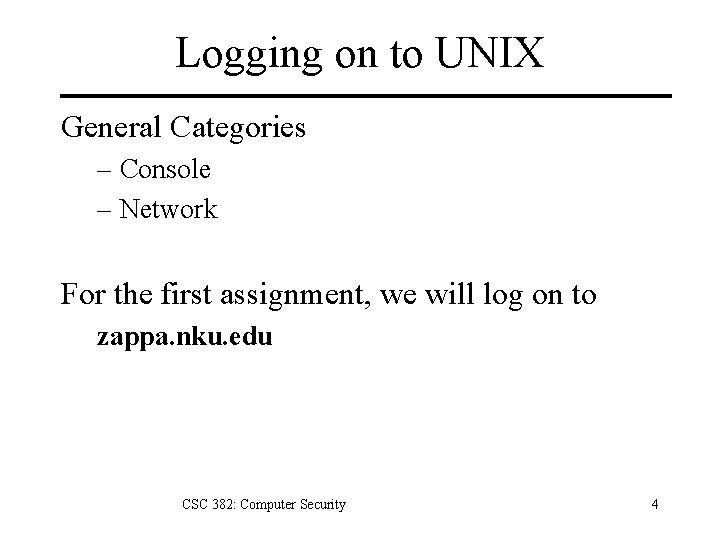
Topics 1. 2. 3. 4. 5. What is UNIX? Logging on. Basic Commands. The UNIX Shell Compiling on UNIX CSC 382: Computer Security 2
What is UNIX? UNIX: : /yoo'niks/ [In the authors' words, "A weak pun on Multics"] n. (also `Unix') An interactive time-sharing system originally invented in 1969 by Ken Thompson after Bell Labs left the Multics project, originally so he could play games on his scavenged PDP-7. Dennis Ritchie, the inventor of C, is considered a co-author of the system. CSC 382: Computer Security 3
Logging on to UNIX General Categories – Console – Network For the first assignment, we will log on to zappa. nku. edu CSC 382: Computer Security 4
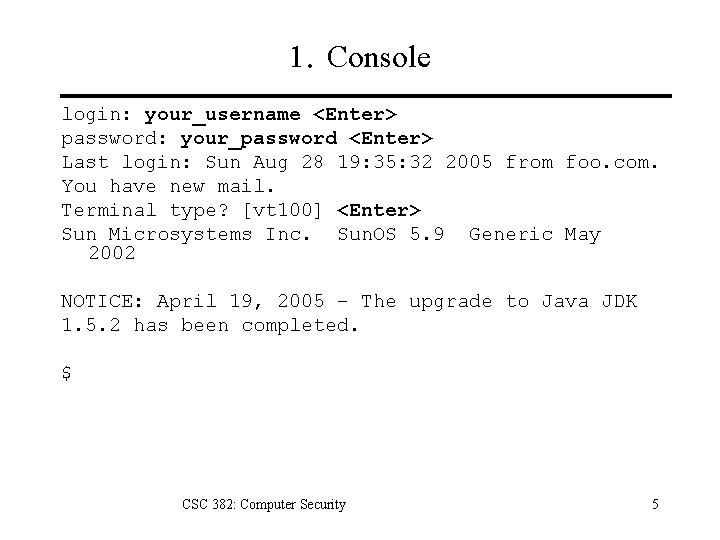
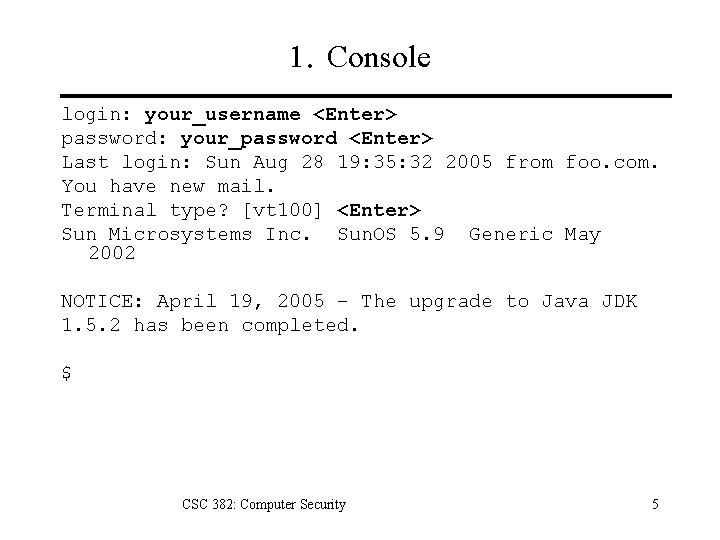
1. Console login: your_username <Enter> password: your_password <Enter> Last login: Sun Aug 28 19: 35: 32 2005 from foo. com. You have new mail. Terminal type? [vt 100] <Enter> Sun Microsystems Inc. Sun. OS 5. 9 Generic May 2002 NOTICE: April 19, 2005 – The upgrade to Java JDK 1. 5. 2 has been completed. $ CSC 382: Computer Security 5
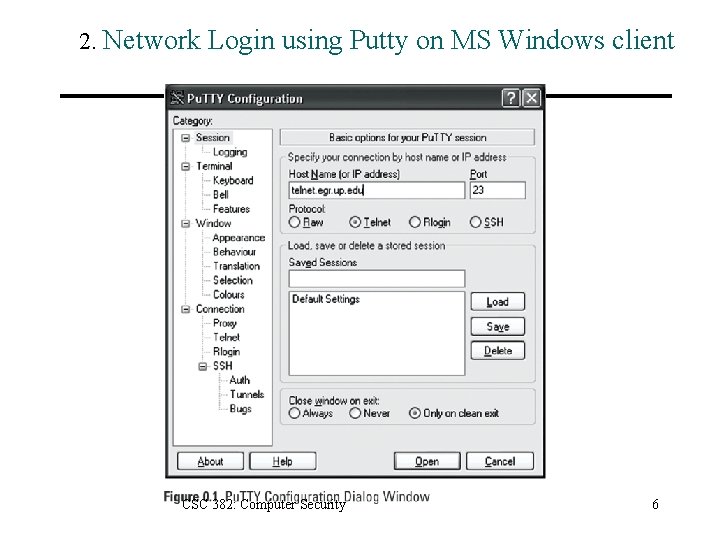
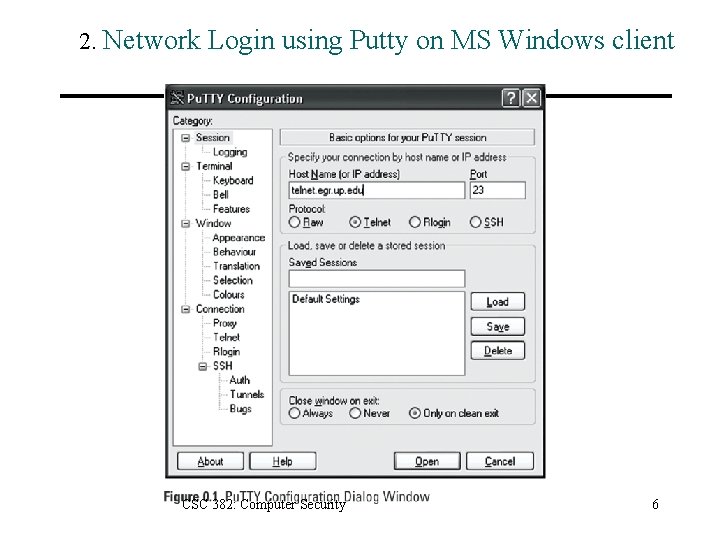
2. Network Login using Putty on MS Windows client CSC 382: Computer Security 6
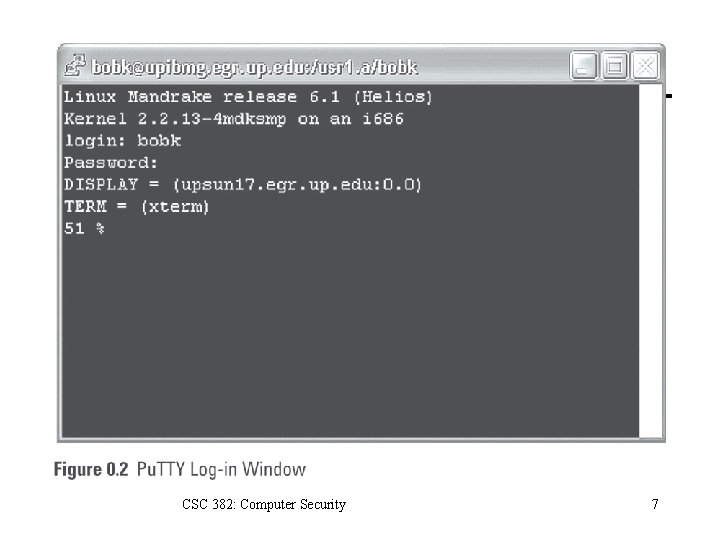
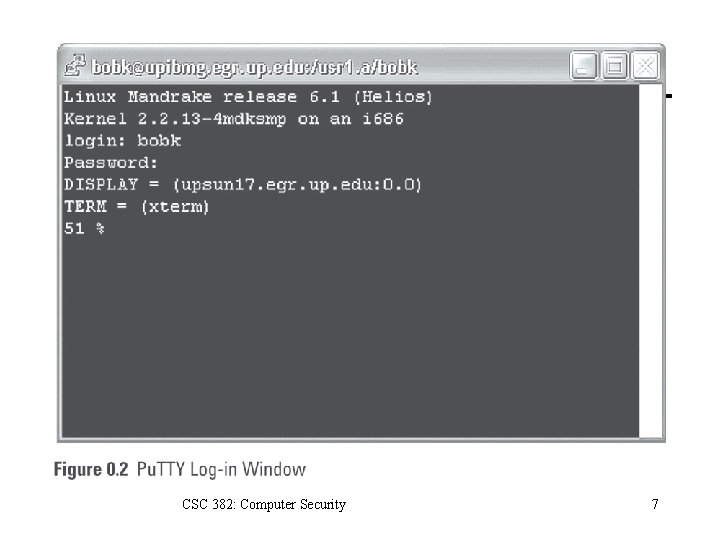
CSC 382: Computer Security 7
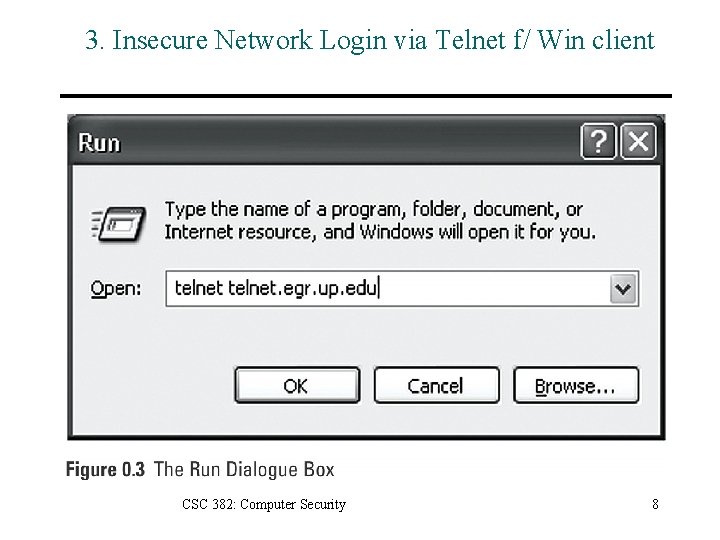
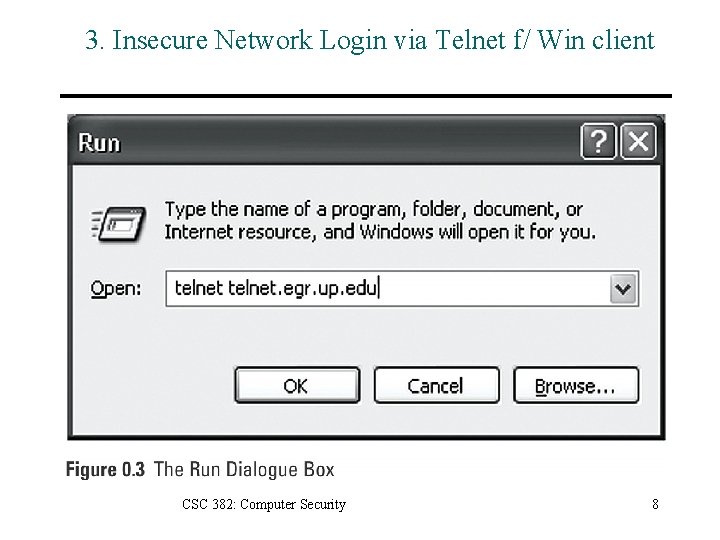
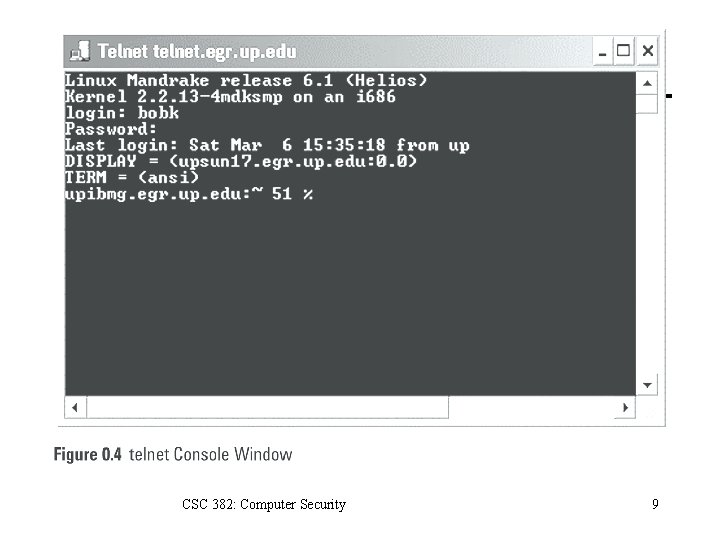
3. Insecure Network Login via Telnet f/ Win client CSC 382: Computer Security 8
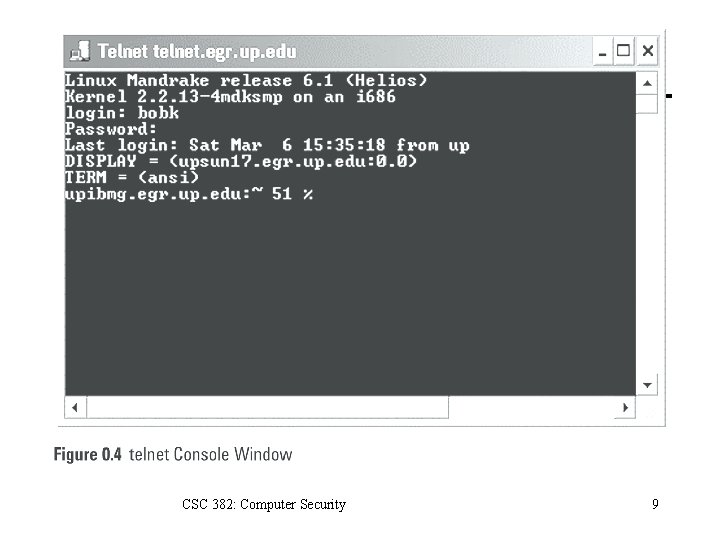
CSC 382: Computer Security 9
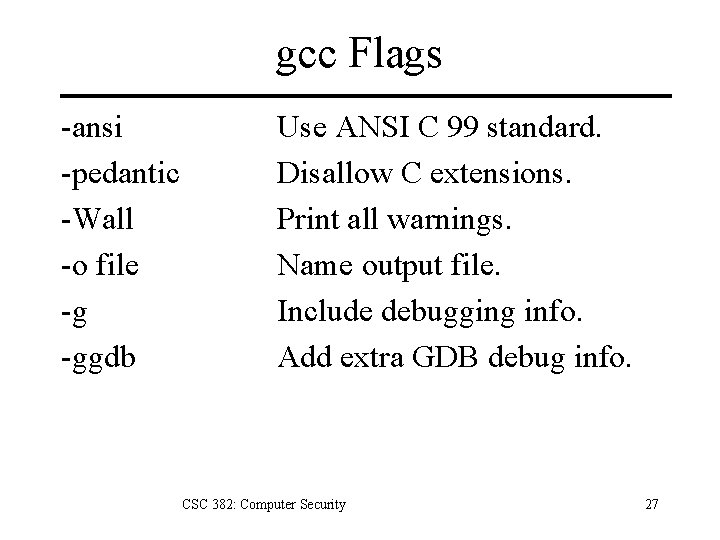
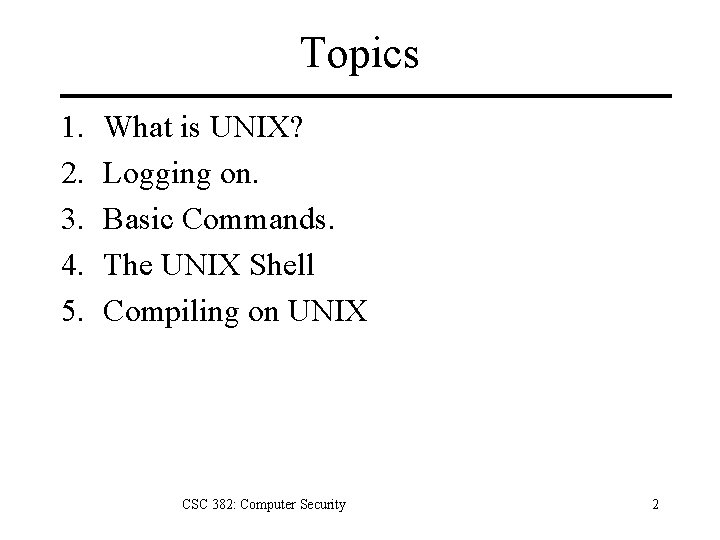
![Structure of a UNIX command command options option arguments command arguments Structure of a UNIX command #command [[ - ] option(s)] [option argument(s)] [command argument(s)]](https://slidetodoc.com/presentation_image_h/0ad94690cd7f84d74f224eee0bb0f5a2/image-10.jpg)
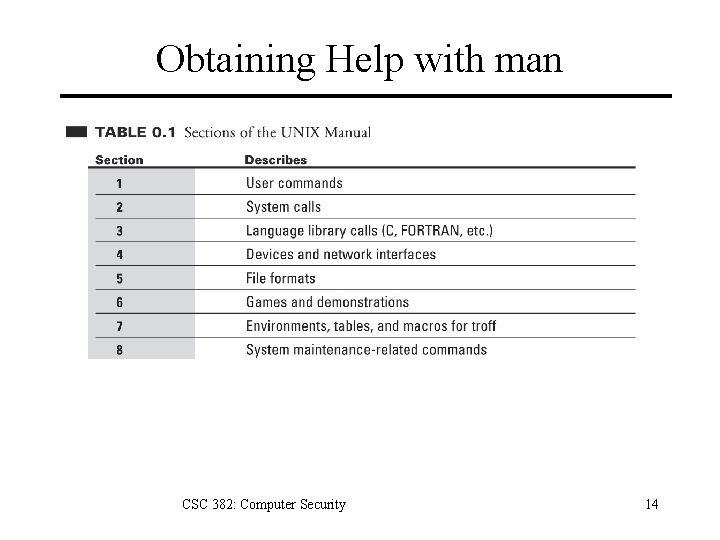
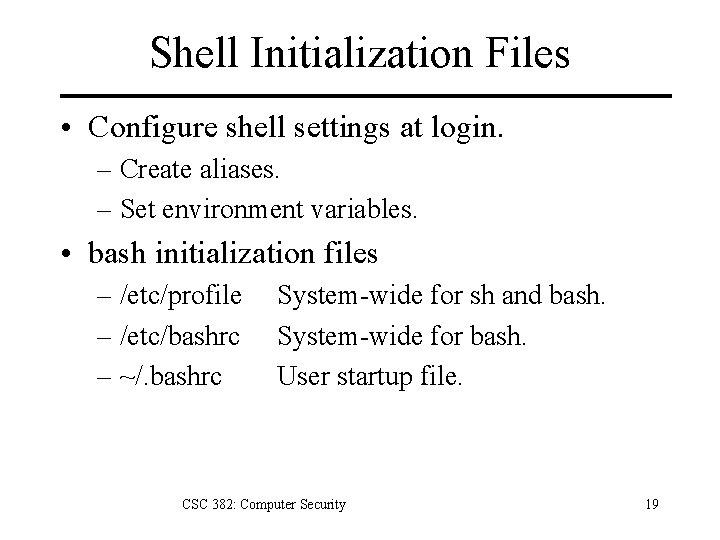
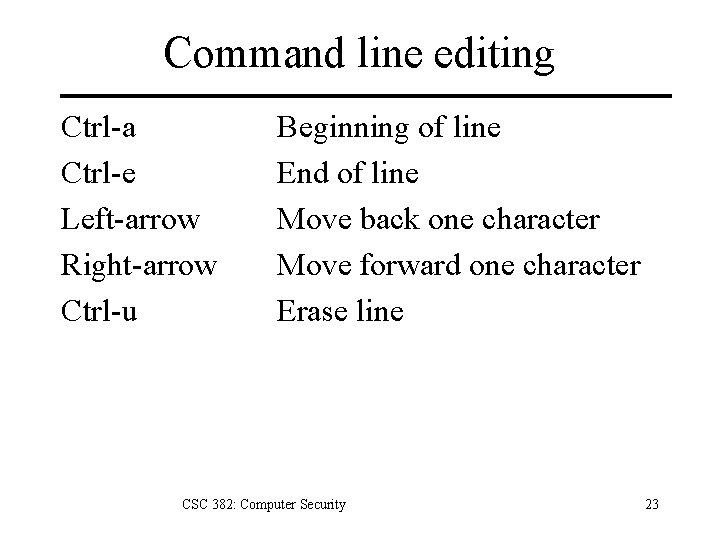
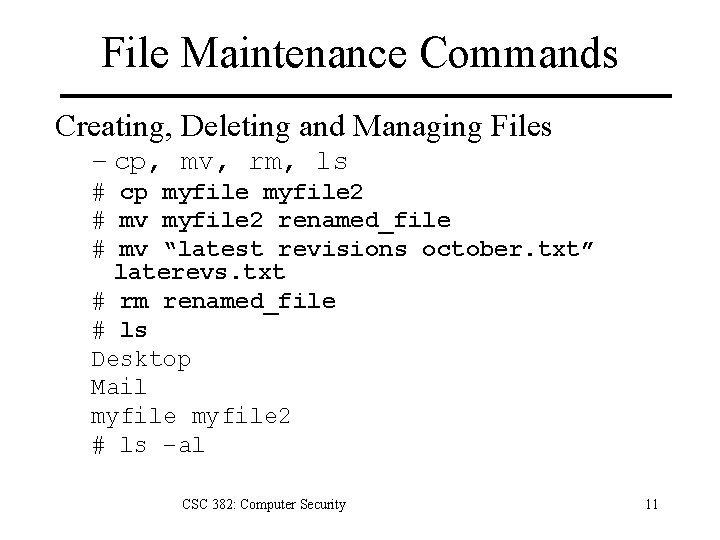
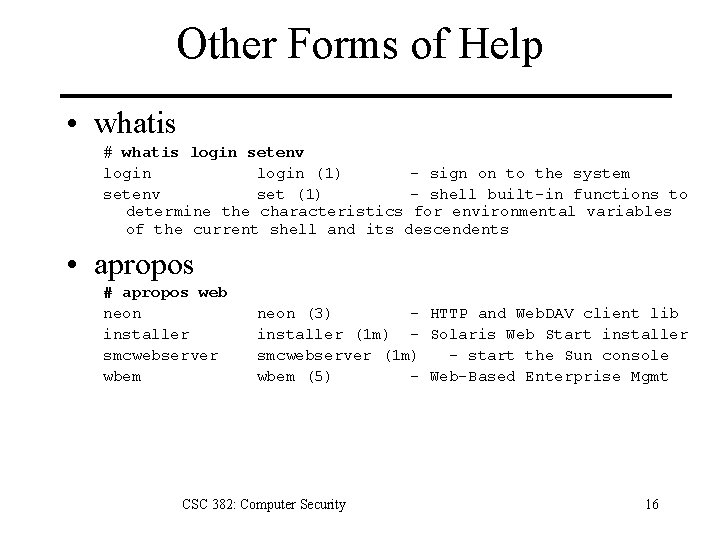
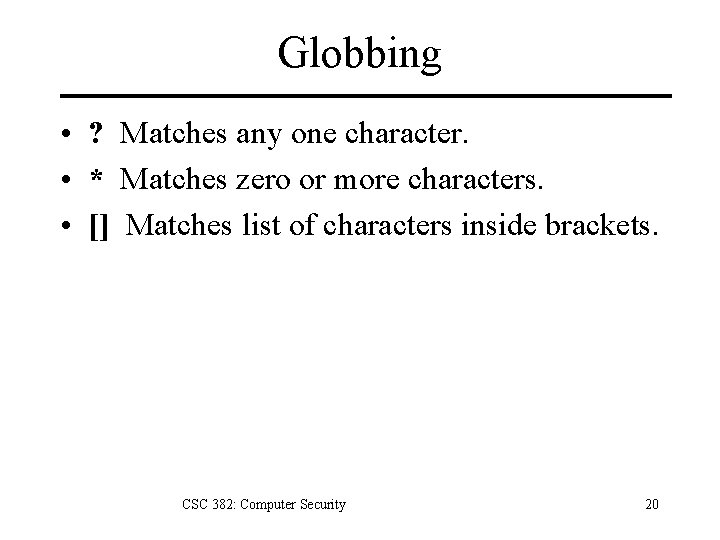
Structure of a UNIX command #command [[ - ] option(s)] [option argument(s)] [command argument(s)] Examples: • • $ $ ls ls ls lpr -la m* -Pspr -n 3 proposal. ps CSC 382: Computer Security 10
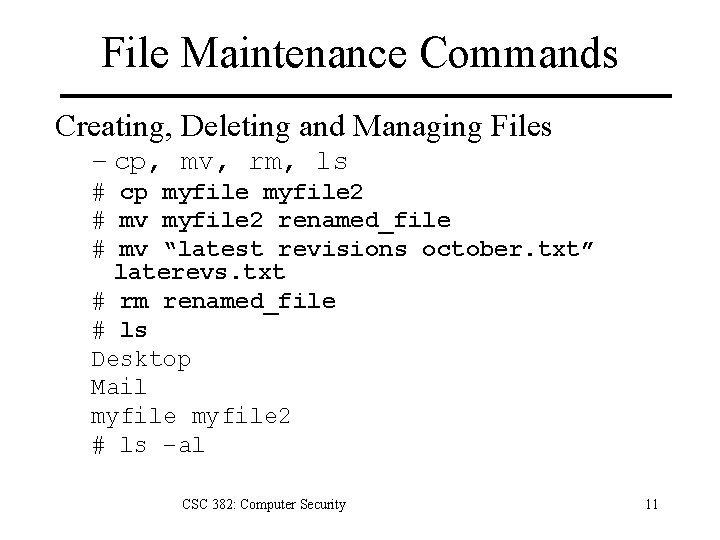
File Maintenance Commands Creating, Deleting and Managing Files – cp, mv, rm, ls # cp myfile 2 # mv myfile 2 renamed_file # mv “latest revisions october. txt” laterevs. txt # rm renamed_file # ls Desktop Mail myfile 2 # ls –al CSC 382: Computer Security 11
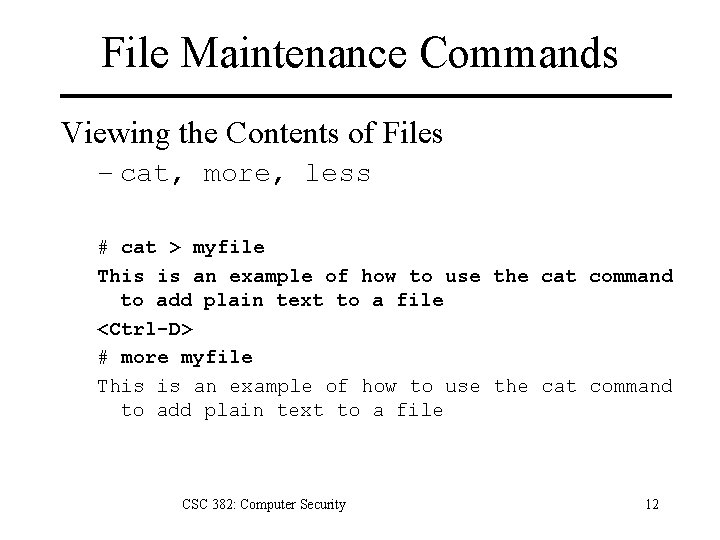
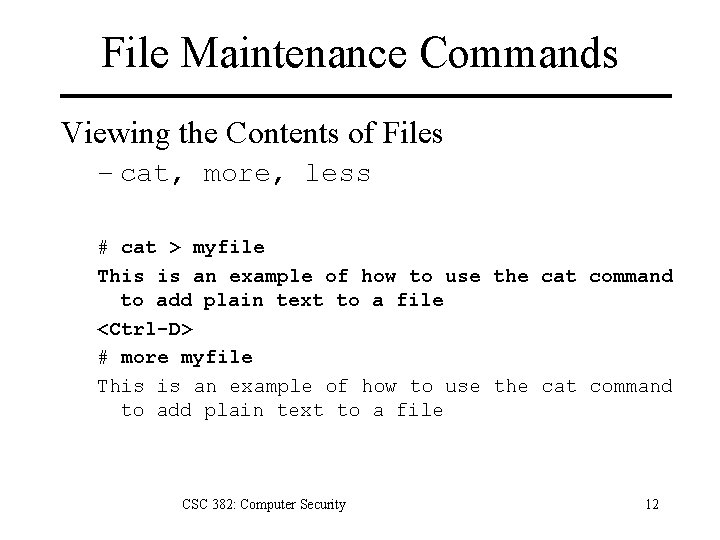
File Maintenance Commands Viewing the Contents of Files – cat, more, less # cat > myfile This is an example of how to use the cat command to add plain text to a file <Ctrl-D> # more myfile This is an example of how to use the cat command to add plain text to a file CSC 382: Computer Security 12
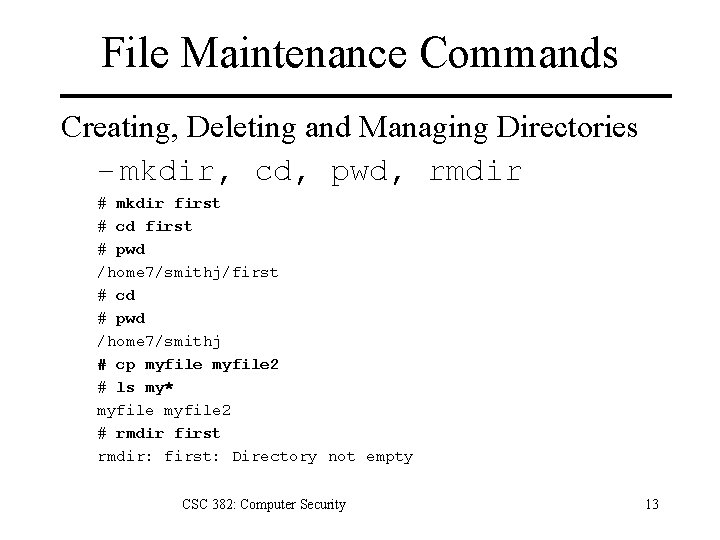
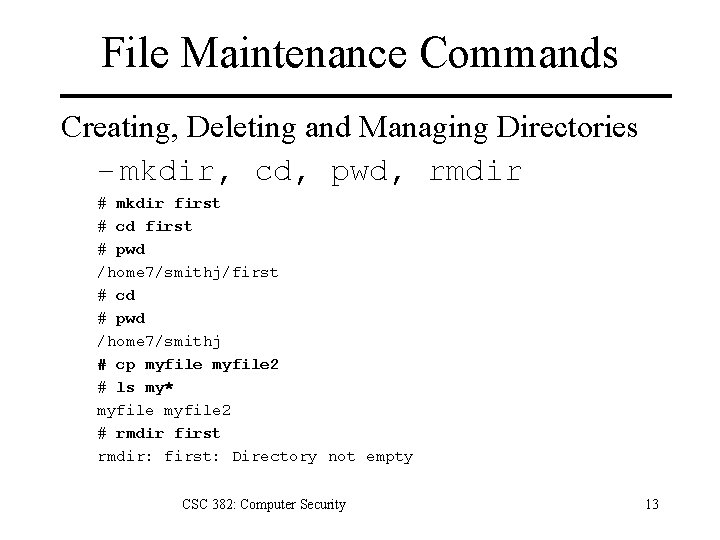
File Maintenance Commands Creating, Deleting and Managing Directories – mkdir, cd, pwd, rmdir # mkdir first # cd first # pwd /home 7/smithj/first # cd # pwd /home 7/smithj # cp myfile 2 # ls my* myfile 2 # rmdir first rmdir: first: Directory not empty CSC 382: Computer Security 13
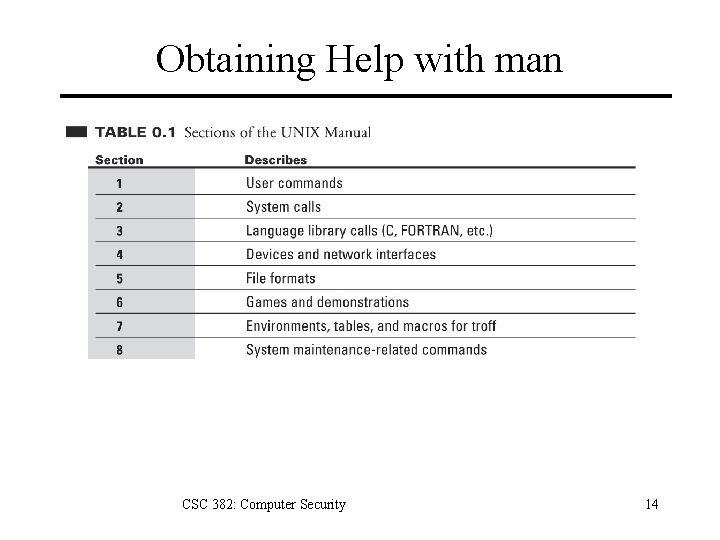
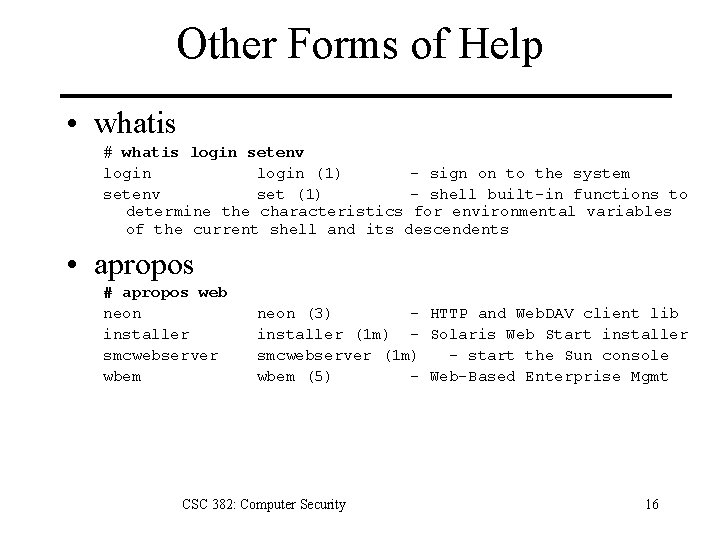
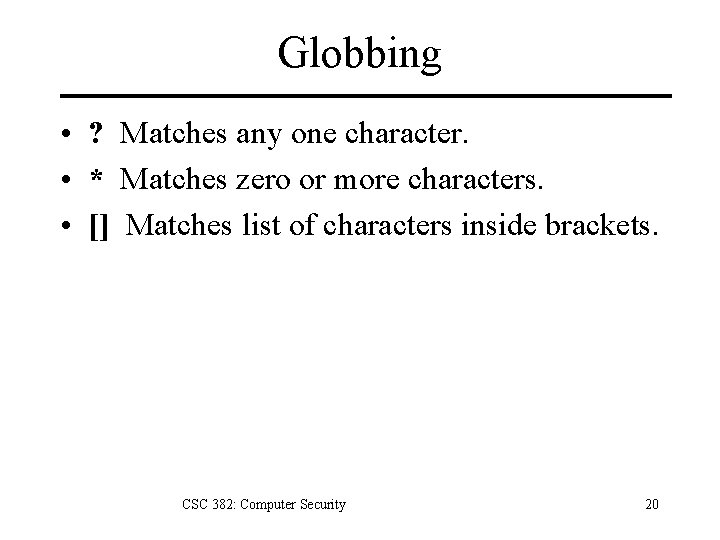
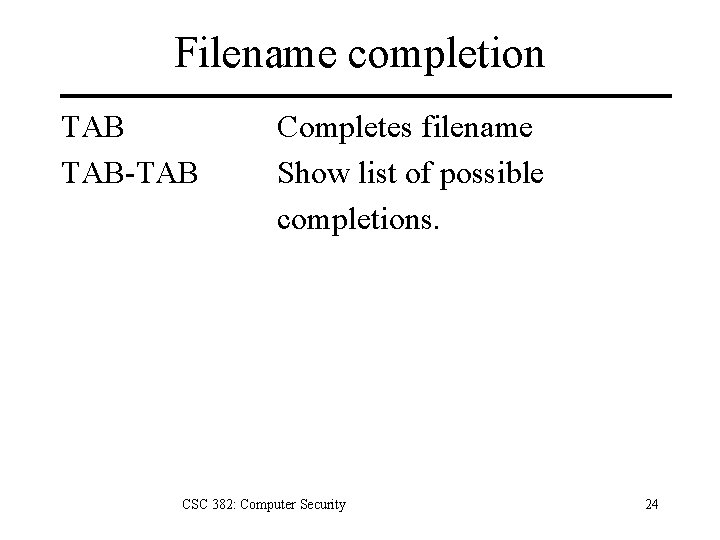
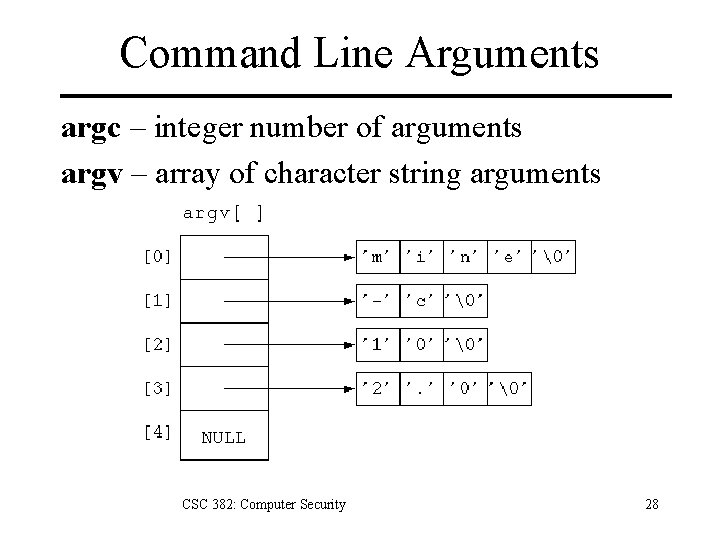
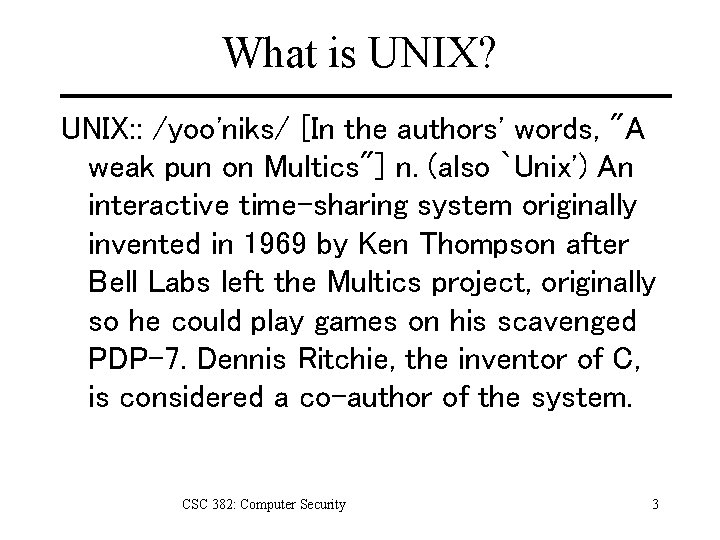
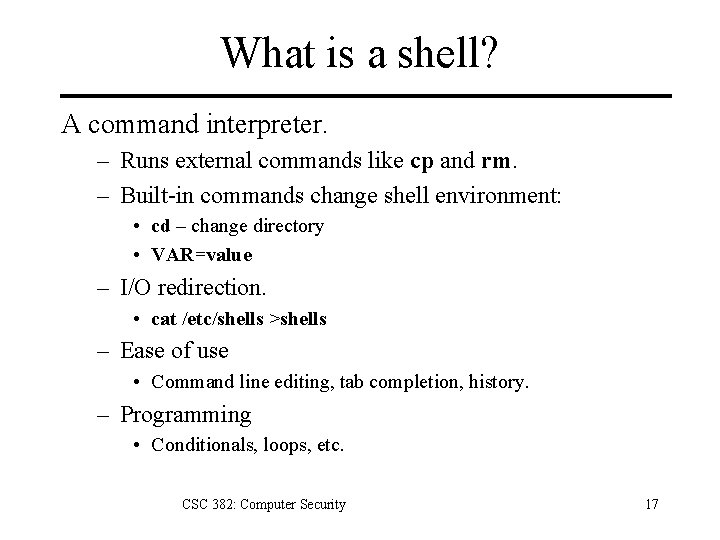
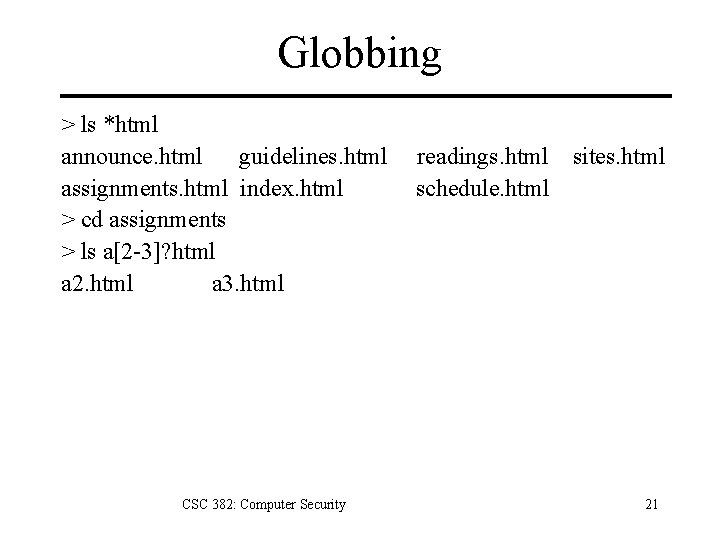
Obtaining Help with man CSC 382: Computer Security 14
![Obtaining Help with man optionss section commandlist man ls User Commands ls1 NAME Obtaining Help with man [options][-s section] command-list # man ls User Commands ls(1) NAME](https://slidetodoc.com/presentation_image_h/0ad94690cd7f84d74f224eee0bb0f5a2/image-15.jpg)
Obtaining Help with man [options][-s section] command-list # man ls User Commands ls(1) NAME ls - list contents of directory SYNOPSIS /usr/bin/ls [-a. Abc. Cdf. Fghil. Lmnopqr. Rstux 1@] [file. . . ] /usr/xpg 4/bin/ls [-a. Abc. Cdf. Fghil. Lmnopqr. Rstux 1@] [file. . . ] DESCRIPTION For each file that is a directory, ls lists the contents of the directory. For each file that is an ordinary file, ls repeats its name and any other information requested. The output is sorted alphabetically by default. When no argument is given, the current directory is listed. … CSC 382: Computer Security 15
Other Forms of Help • whatis # whatis login setenv login (1) - sign on to the system setenv set (1) - shell built-in functions to determine the characteristics for environmental variables of the current shell and its descendents • apropos # apropos web neon installer smcwebserver wbem neon (3) - HTTP and Web. DAV client lib installer (1 m) - Solaris Web Start installer smcwebserver (1 m) - start the Sun console wbem (5) - Web-Based Enterprise Mgmt CSC 382: Computer Security 16
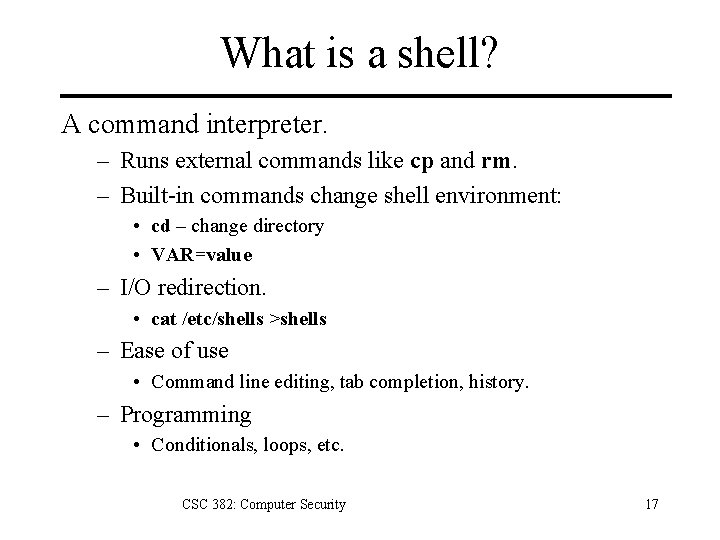
What is a shell? A command interpreter. – Runs external commands like cp and rm. – Built-in commands change shell environment: • cd – change directory • VAR=value – I/O redirection. • cat /etc/shells >shells – Ease of use • Command line editing, tab completion, history. – Programming • Conditionals, loops, etc. CSC 382: Computer Security 17
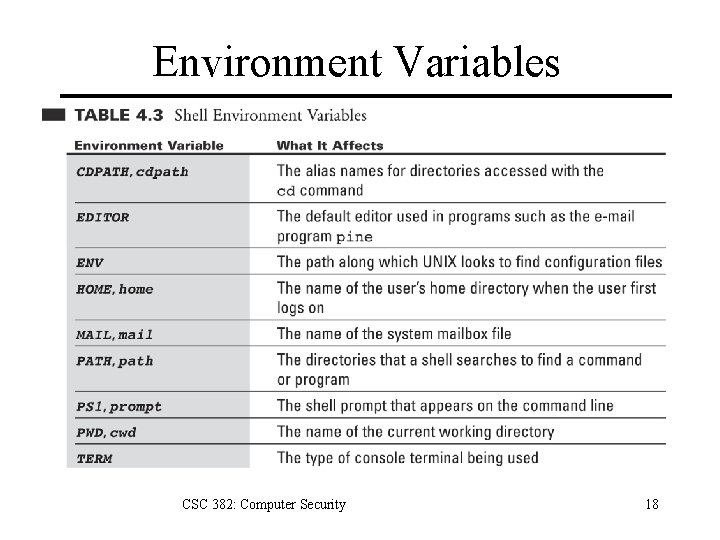
Environment Variables CSC 382: Computer Security 18
Shell Initialization Files • Configure shell settings at login. – Create aliases. – Set environment variables. • bash initialization files – /etc/profile – /etc/bashrc – ~/. bashrc System-wide for sh and bash. System-wide for bash. User startup file. CSC 382: Computer Security 19
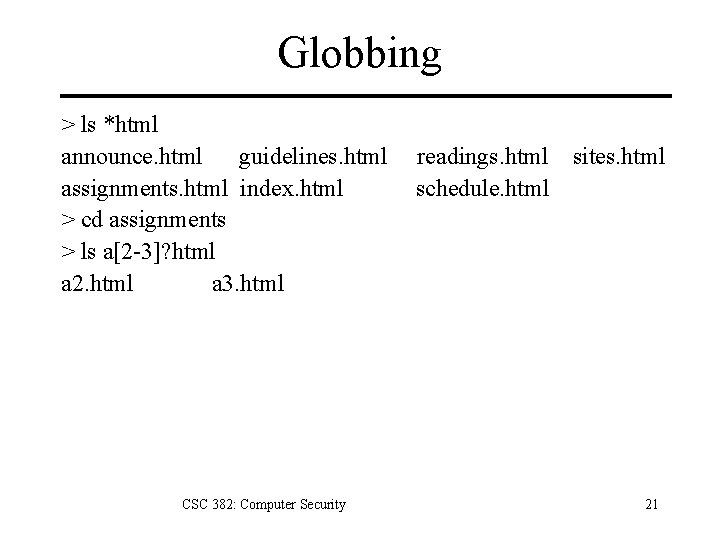
Globbing • ? Matches any one character. • * Matches zero or more characters. • [] Matches list of characters inside brackets. CSC 382: Computer Security 20
Globbing > ls *html announce. html guidelines. html readings. html sites. html assignments. html index. html schedule. html > cd assignments > ls a[2 -3]? html a 2. html a 3. html CSC 382: Computer Security 21
Command History Up-arrow Previous command Down-arrow Next command history List old commands !! Previous command !# Command # !$ Last arg of previous command CSC 382: Computer Security 22
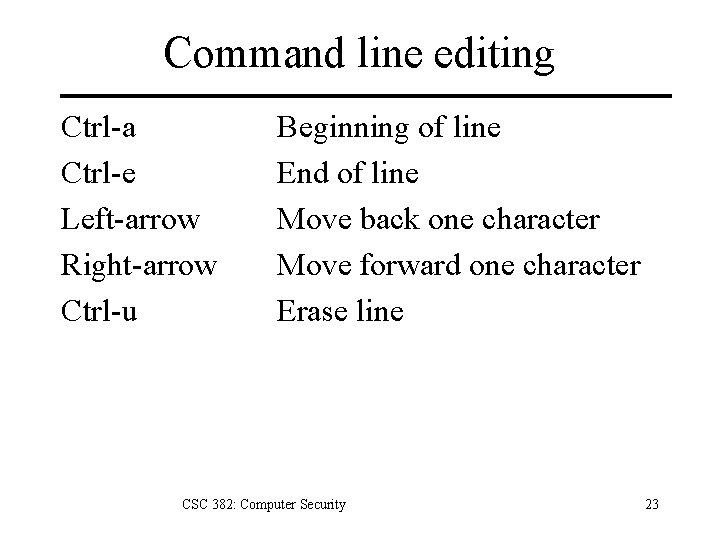
Command line editing Ctrl-a Ctrl-e Left-arrow Right-arrow Ctrl-u Beginning of line End of line Move back one character Move forward one character Erase line CSC 382: Computer Security 23
Filename completion TAB-TAB Completes filename Show list of possible completions. CSC 382: Computer Security 24
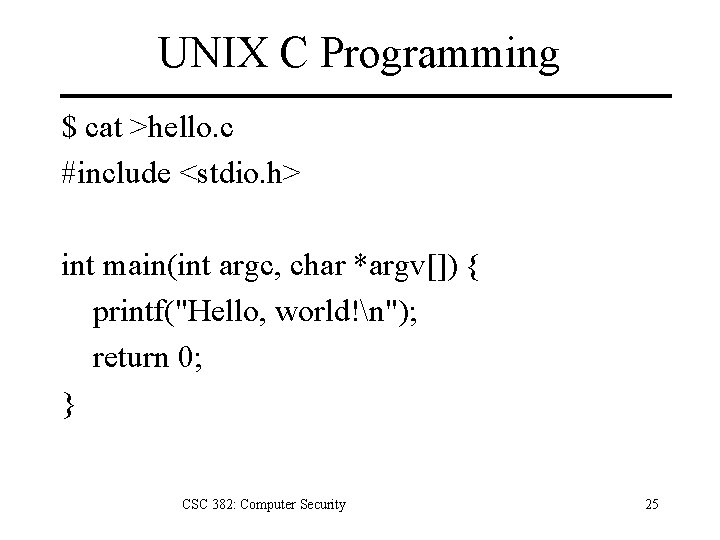
UNIX C Programming $ cat >hello. c #include <stdio. h> int main(int argc, char *argv[]) { printf("Hello, world!n"); return 0; } CSC 382: Computer Security 25
UNIX C Programming $ gcc –o hello. c $. /hello Hello, world! CSC 382: Computer Security 26
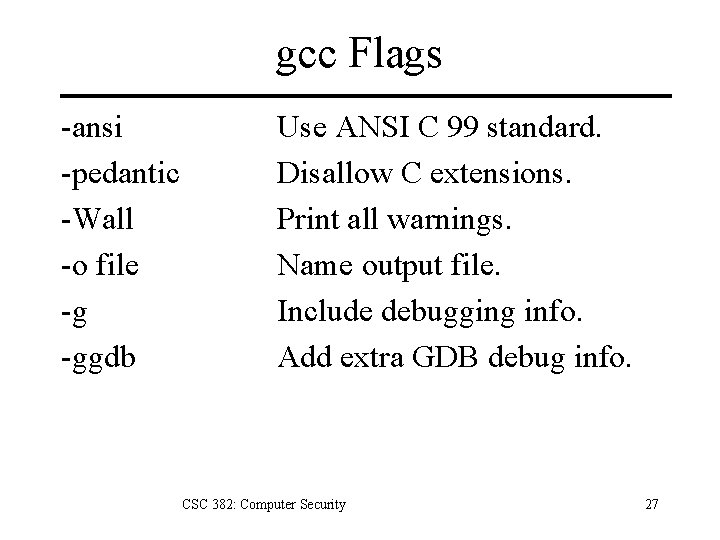
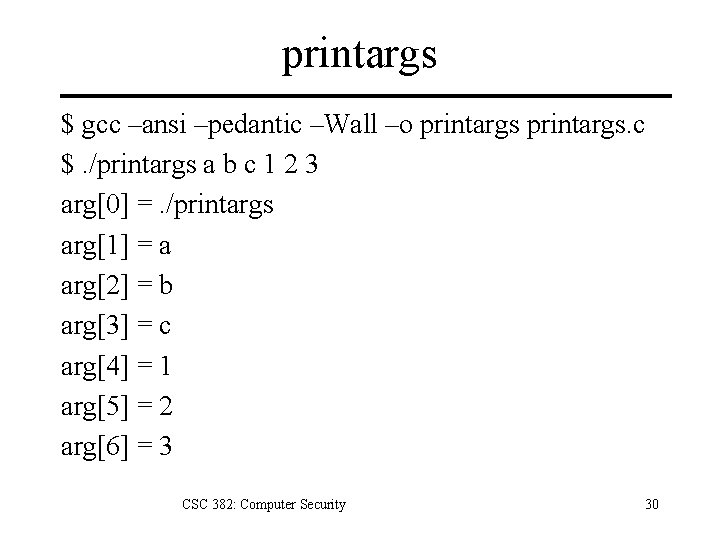
gcc Flags -ansi -pedantic -Wall -o file -g -ggdb Use ANSI C 99 standard. Disallow C extensions. Print all warnings. Name output file. Include debugging info. Add extra GDB debug info. CSC 382: Computer Security 27
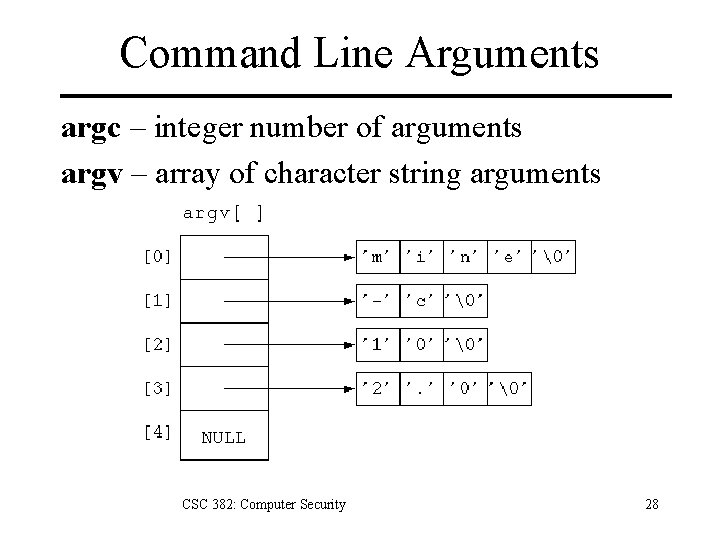
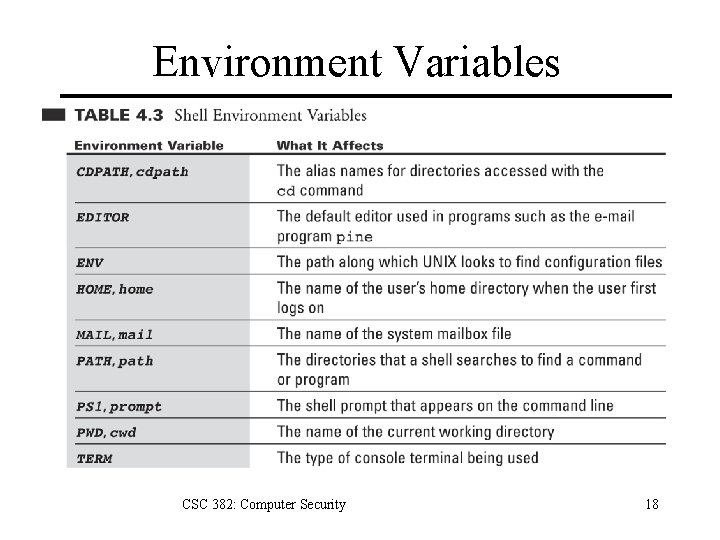
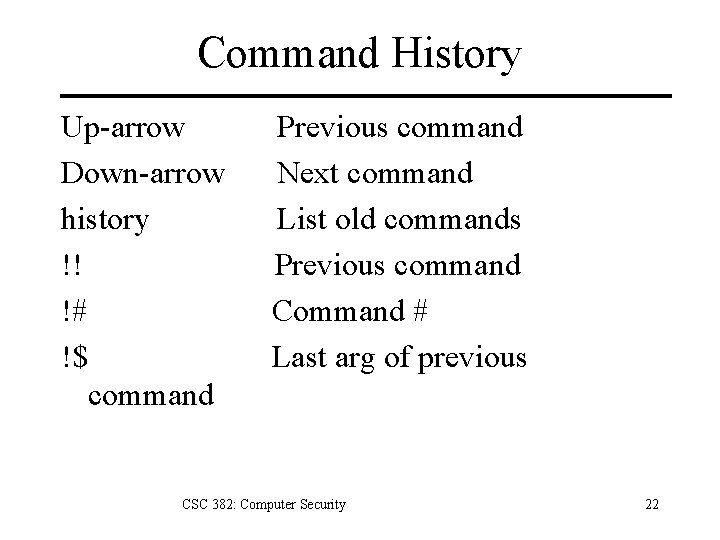
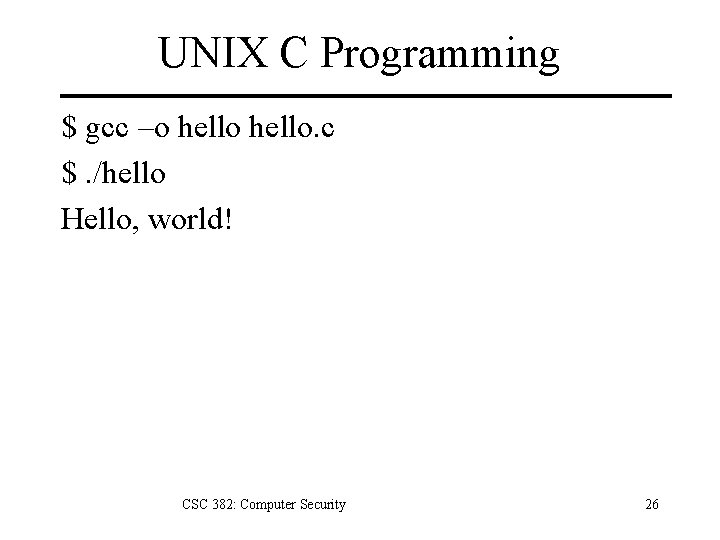
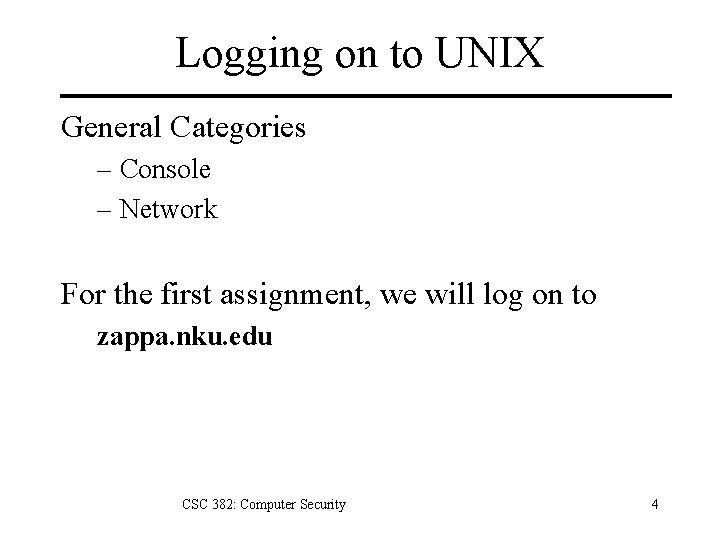
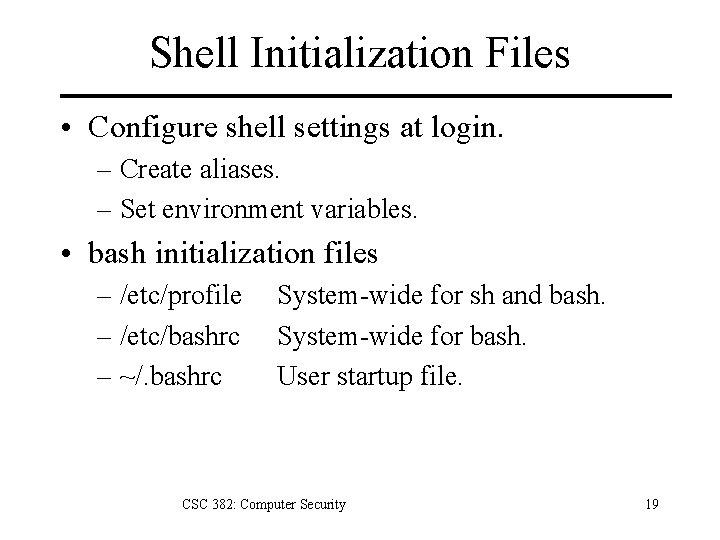
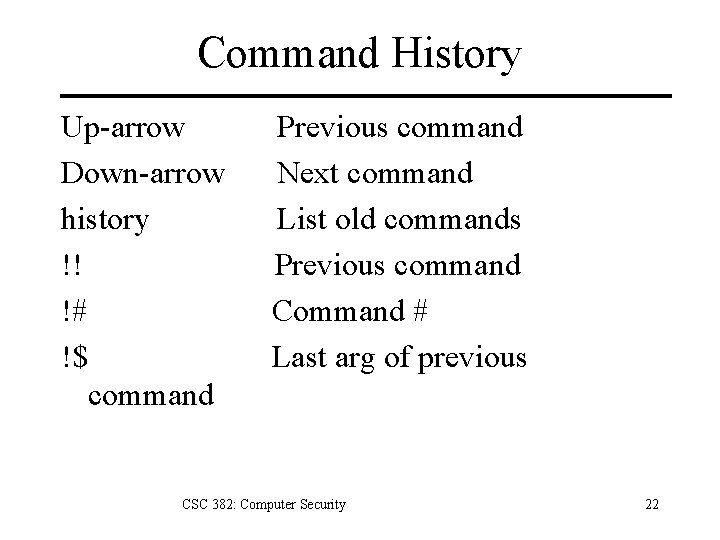
Command Line Arguments argc – integer number of arguments argv – array of character string arguments CSC 382: Computer Security 28
![printargs c cat printargs c include stdio h int mainint argc char argv printargs. c $ cat >printargs. c #include <stdio. h> int main(int argc, char *argv[])](https://slidetodoc.com/presentation_image_h/0ad94690cd7f84d74f224eee0bb0f5a2/image-29.jpg)
printargs. c $ cat >printargs. c #include <stdio. h> int main(int argc, char *argv[]) { int i; for(i=0; i<argc; i++) printf("arg[%d] = %sn", i, argv[i]); return 0; } CSC 382: Computer Security 29
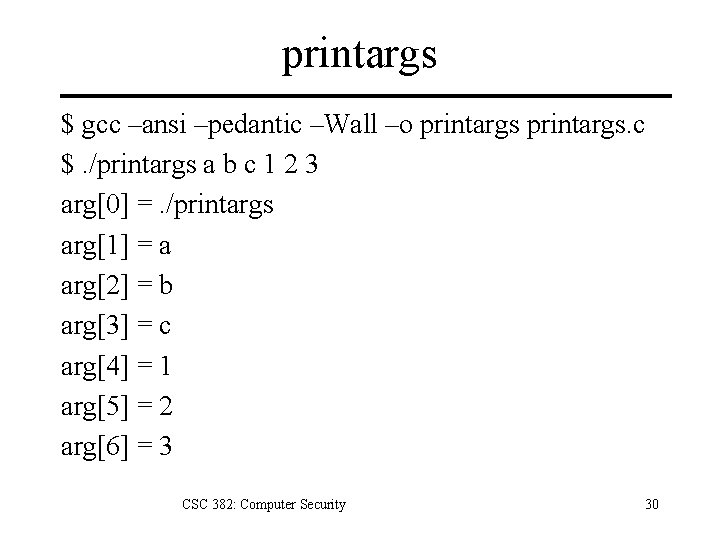
printargs $ gcc –ansi –pedantic –Wall –o printargs. c $. /printargs a b c 1 2 3 arg[0] =. /printargs arg[1] = a arg[2] = b arg[3] = c arg[4] = 1 arg[5] = 2 arg[6] = 3 CSC 382: Computer Security 30