METAMORPHIC SOFTWARE FOR GOOD AND EVIL Wing Wong

- Slides: 62
METAMORPHIC SOFTWARE FOR GOOD AND EVIL Wing Wong & Mark Stamp November 20, 2006
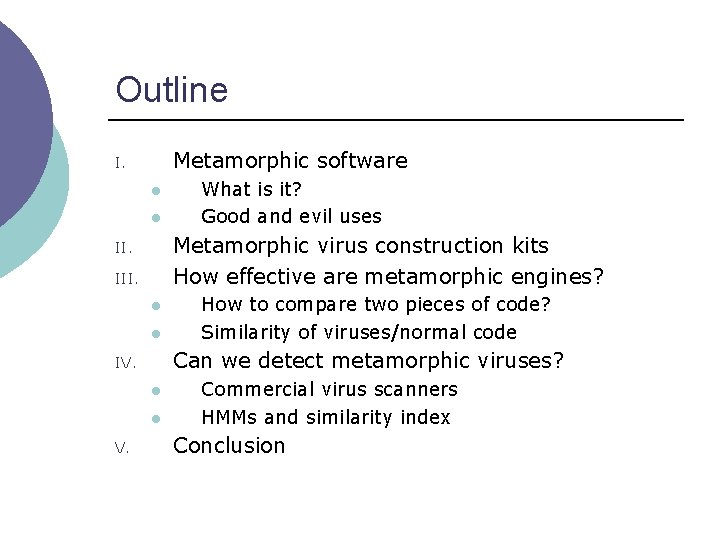
Outline Metamorphic software I. l l Metamorphic virus construction kits How effective are metamorphic engines? II. III. l l How to compare two pieces of code? Similarity of viruses/normal code Can we detect metamorphic viruses? IV. l l V. What is it? Good and evil uses Commercial virus scanners HMMs and similarity index Conclusion
PART I Metamorphic Software
What is Metamorphic Software? ¡ Software is metamorphic provided l l All copies do the same thing Internal structure differs Today almost all software is cloned ¡ “Good” metamorphic software… ¡ l ¡ Mitigate buffer overflow attacks “Bad” metamorphic software… l Avoid virus/worm signature detection
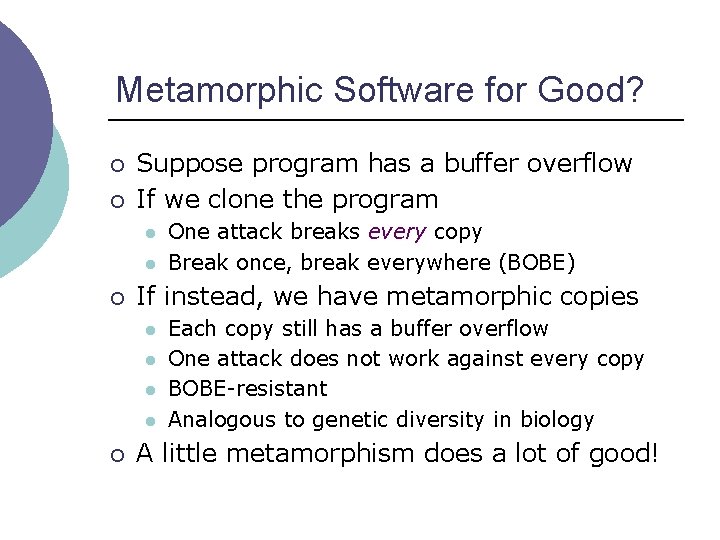
Metamorphic Software for Good? ¡ ¡ Suppose program has a buffer overflow If we clone the program l l ¡ If instead, we have metamorphic copies l l ¡ One attack breaks every copy Break once, break everywhere (BOBE) Each copy still has a buffer overflow One attack does not work against every copy BOBE-resistant Analogous to genetic diversity in biology A little metamorphism does a lot of good!
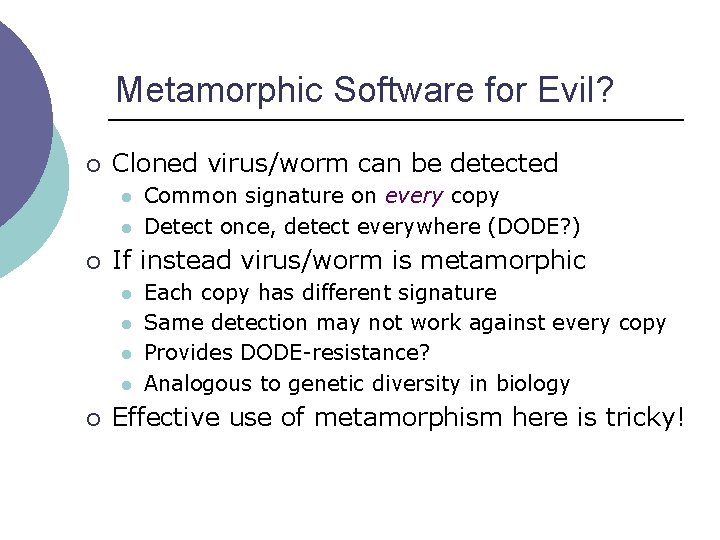
Metamorphic Software for Evil? ¡ Cloned virus/worm can be detected l l ¡ If instead virus/worm is metamorphic l l ¡ Common signature on every copy Detect once, detect everywhere (DODE? ) Each copy has different signature Same detection may not work against every copy Provides DODE-resistance? Analogous to genetic diversity in biology Effective use of metamorphism here is tricky!
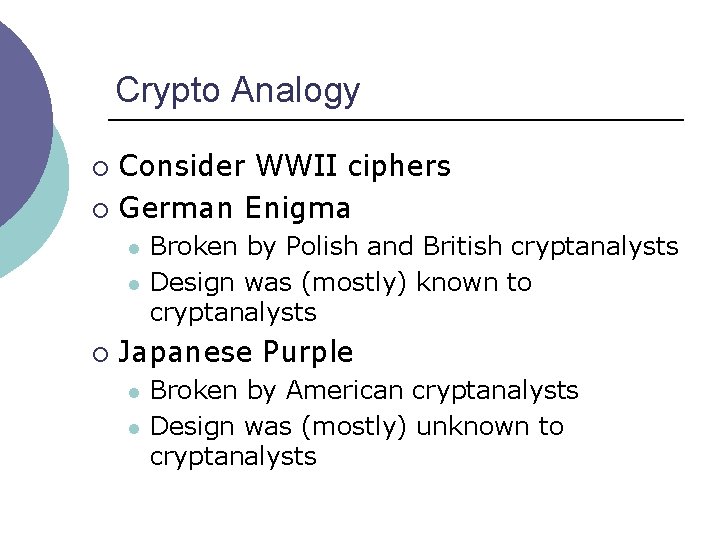
Crypto Analogy Consider WWII ciphers ¡ German Enigma ¡ l l ¡ Broken by Polish and British cryptanalysts Design was (mostly) known to cryptanalysts Japanese Purple l l Broken by American cryptanalysts Design was (mostly) unknown to cryptanalysts
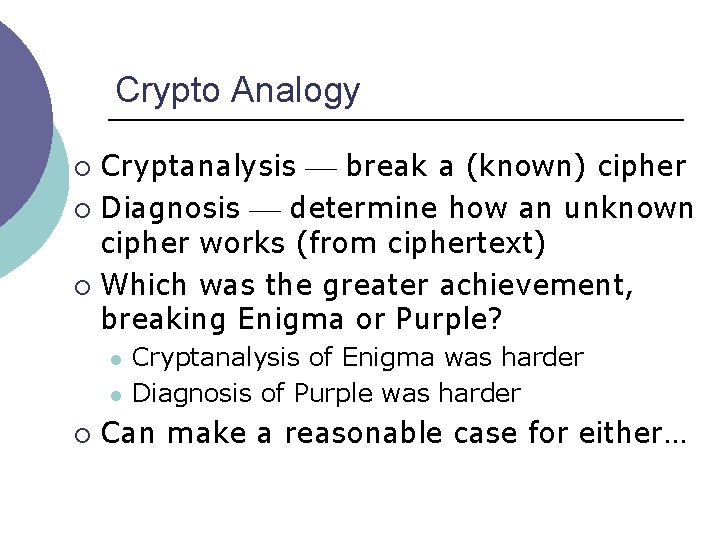
Crypto Analogy Cryptanalysis break a (known) cipher ¡ Diagnosis determine how an unknown cipher works (from ciphertext) ¡ Which was the greater achievement, breaking Enigma or Purple? ¡ l l ¡ Cryptanalysis of Enigma was harder Diagnosis of Purple was harder Can make a reasonable case for either…
Crypto Analogy What does this have to do with metamorphic software? ¡ Suppose the good guys generate metamorphic copies of software ¡ Bad guys can attack individual copies ¡ Can bad guys attack all copies? ¡ l l If they can diagnose our metamorphic generator, maybe But that’s a diagnosis problem…
Crypto Analogy ¡ What about case where bad guys write metamorphic code? l ¡ Do good guys need to solve diagnosis problem? l ¡ ¡ ¡ Metamorphic viruses, for example If so, good guys are in trouble Not if good guys “only” need to detect the metamorphic code (not diagnose) Not claiming the good guys job is easy Just claiming that there is hope…
Virus Evolution ¡ Viruses first appeared in the 1980 s l ¡ Viruses must avoid signature detection l ¡ Fred Cohen Virus can alter its “appearance” Techniques employed l l l encryption polymorphic metamorphic
Virus Evolution - Encryption ¡ Virus consists of l l ¡ Different encryption key l ¡ decrypting module (decryptor) encrypted virus body different virus body signature Weakness l decryptor can be detected
Virus Evolution – Polymorphism Try to hide signature of decryptor ¡ Can use code emulator to decrypt putative virus dynamically ¡ Decrypted virus body is constant ¡ l Once (partially) decrypted, signature detection is possible
Virus Evolution – Metamorphism ¡ ¡ Change virus body Mutation techniques: l l l permutation of subroutines insertion of garbage/jump instructions substitution of instructions
PART II Virus Construction Kits
Virus Construction Kits – PS-MPC ¡ According to Peter Szor: “… PS-MPC [Phalcon/Skism Mass. Produced Code generator] uses a generator that effectively works as a code-morphing engine…… the viruses that PS-MPC generates are not [only] polymorphic, but their decryption routines and structures change in variants…”
Virus Construction Kits – G 2 ¡ From the documentation of G 2 (Second Generation virus generator): “… different viruses may be generated from identical configuration files…”
Virus Construction Kits – NGVCK ¡ From the documentation for NGVCK (Next Generation Virus Creation Kit): “… all created viruses are completely different in structure and opcode…… impossible to catch all variants with one or more scanstrings. …… nearly 100% variability of the entire code” ¡ Oh, really?
PART III How Effective Are Metamorphic Engines?
How We Compare Two Pieces of Code
Virus Families – Test Data ¡ Four generators, 45 viruses l l ¡ 20 viruses by NGVCK 10 viruses by G 2 10 viruses by VCL 32 5 viruses by MPCGEN 20 normal utility programs from the Cygwin bin directory
Similarity within Virus Families – Results
Similarity within Virus Families – Results
Similarity within Virus Families – Results
Similarity within Virus Families – Results
Similarity within Virus Families – Results
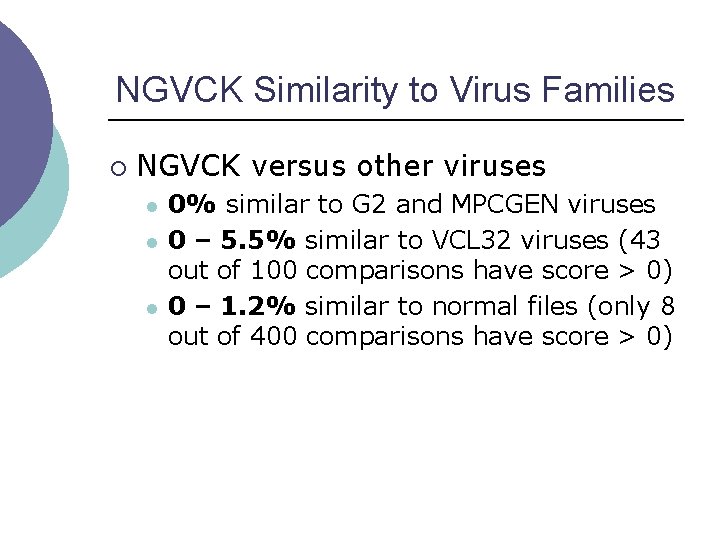
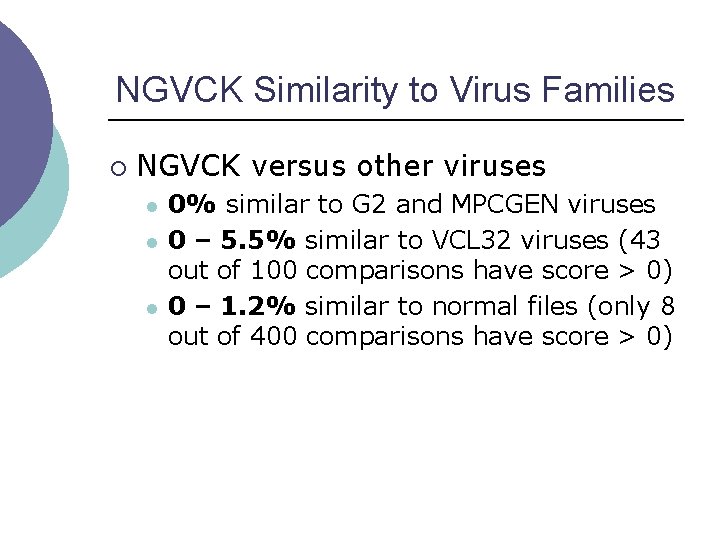
NGVCK Similarity to Virus Families ¡ NGVCK versus other viruses l l l 0% similar to G 2 and MPCGEN viruses 0 – 5. 5% similar to VCL 32 viruses (43 out of 100 comparisons have score > 0) 0 – 1. 2% similar to normal files (only 8 out of 400 comparisons have score > 0)
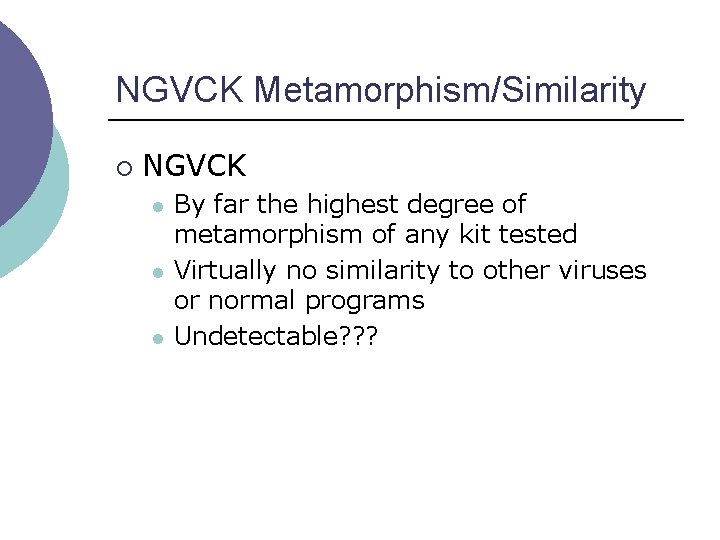
NGVCK Metamorphism/Similarity ¡ NGVCK l l l By far the highest degree of metamorphism of any kit tested Virtually no similarity to other viruses or normal programs Undetectable? ? ?
PART IV Can Metamorphic Viruses Be Detected?
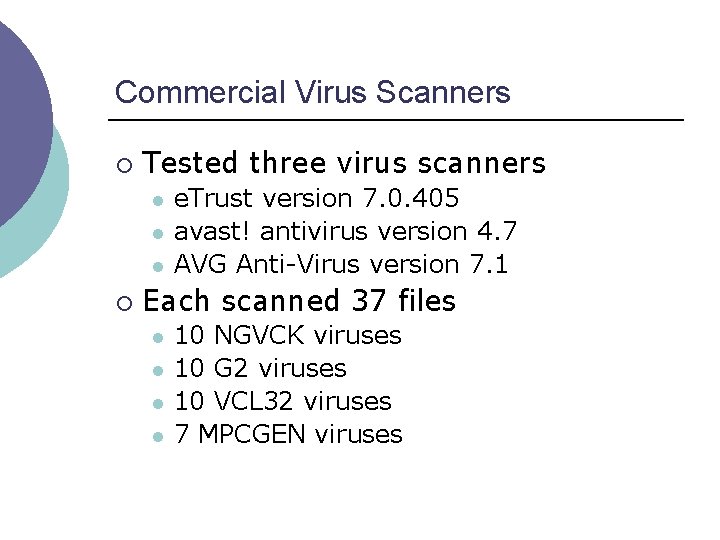
Commercial Virus Scanners ¡ Tested three virus scanners l l l ¡ e. Trust version 7. 0. 405 avast! antivirus version 4. 7 AVG Anti-Virus version 7. 1 Each scanned 37 files l l 10 NGVCK viruses 10 G 2 viruses 10 VCL 32 viruses 7 MPCGEN viruses
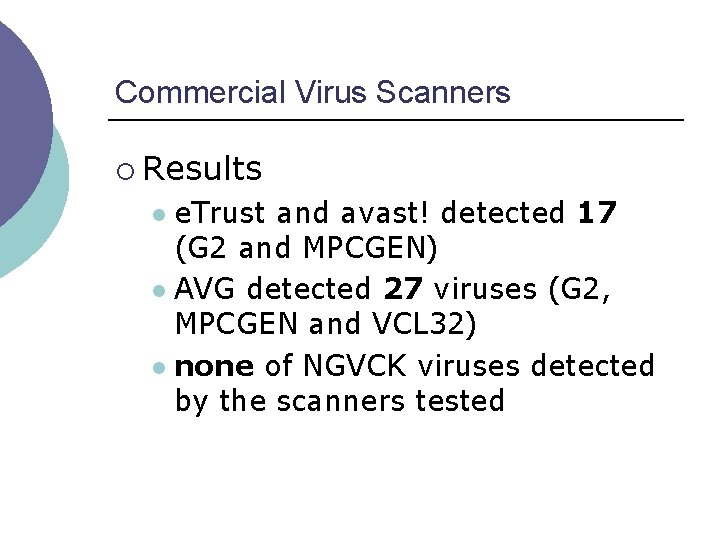
Commercial Virus Scanners ¡ Results e. Trust and avast! detected 17 (G 2 and MPCGEN) l AVG detected 27 viruses (G 2, MPCGEN and VCL 32) l none of NGVCK viruses detected by the scanners tested l
Virus Detection with HMMs ¡ Use hidden Markov models (HMMs) to represent statistical properties of a set of metamorphic virus variants l l Train the model on family of metamorphic viruses Use trained model to determine whether a given program is similar to the viruses the HMM represents
Virus Detection with HMMs – Data ¡ Data set l ¡ Comparison set l l ¡ 200 NGVCK viruses (160 for training, 40 for testing) 40 normal exes from Cygwin 25 other “non-family” viruses (G 2, MPCGEN and VCL 32) 25 HMM models generated and tested
Virus Detection with HMMs – Methodology
Virus Detection with HMMs – Results
Virus Detection with HMMs – Results ¡ Detect some other viruses “for free”
Virus Detection with HMMs ¡ Summary of experimental results l l All normal programs distinguished VCL 32 viruses had scores close to NGVCK family viruses With proper threshold, 17 HMM models had 100% detection rate and 10 models had 0% false positive rate No significant difference in performance between HMMs with 3 or more hidden states
Virus Detection with HMMs – Trained Models Converged probabilities in HMM matrices may give insight into the features of the represented viruses ¡ We observe ¡ l l ¡ opcodes grouped into “hidden” states most opcodes in one state only What does this mean? l We are not sure…
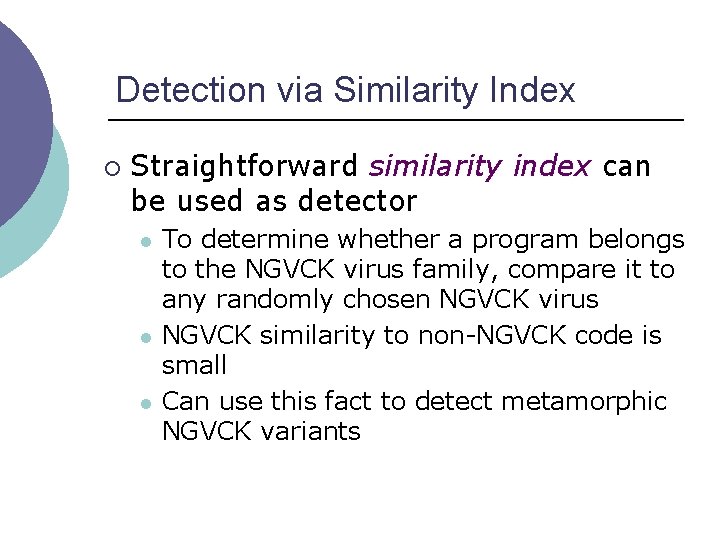
Detection via Similarity Index ¡ Straightforward similarity index can be used as detector l l l To determine whether a program belongs to the NGVCK virus family, compare it to any randomly chosen NGVCK virus NGVCK similarity to non-NGVCK code is small Can use this fact to detect metamorphic NGVCK variants
Detection via Similarity Index
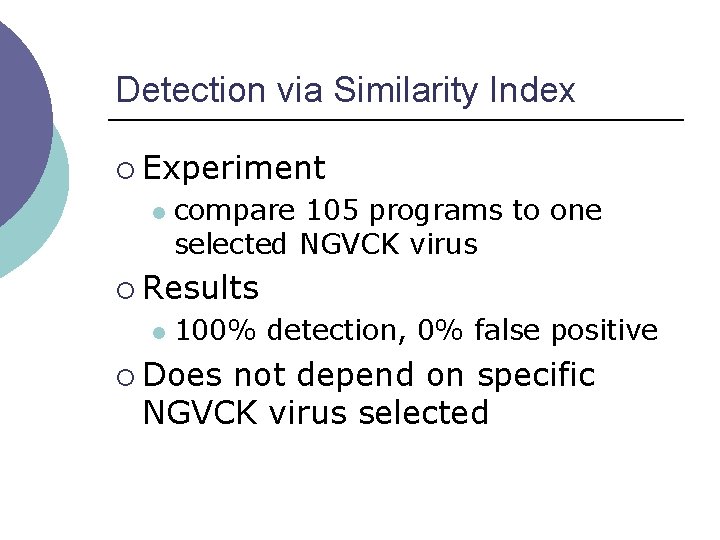
Detection via Similarity Index ¡ Experiment l compare 105 programs to one selected NGVCK virus ¡ Results l 100% detection, 0% false positive ¡ Does not depend on specific NGVCK virus selected
PART V Conclusion
Conclusion ¡ Metamorphic generators vary a lot l l l ¡ NGVCK has highest metamorphism (10% similarity on average) Other generators far less effective (60% similarity on average) Normal files 35% similar, on average But, NGVCK viruses can be detected! l NGVCK viruses too different from other viruses and normal programs
Conclusion NGVCK viruses not detected by commercial scanners we tested ¡ Hidden Markov model (HMM) detects NGVCK (and other) viruses with high accuracy ¡ NGVCK viruses also detectable by similarity index ¡
Conclusion ¡ All metamorphic viruses tested were detectable because l l ¡ High similarity within family and/or Too different from normal programs Effective use of metamorphism by virus/worm requires l l A high degree of metamorphism and similarity to other programs This is not trivial!
The Bottom Line ¡ Metamorphism for “good” l l ¡ Buffer overflow mitigation, BOBEresistance A little metamorphism does a lot of good Metamorphism for “evil” l l l For example, try to evade virus/worm signature detection Requires high degree of metamorphism and similarity to normal programs Not impossible, but not easy…
The Bottom Line All-too-often in security, the advantage lies with the bad guys ¡ For metamorphic software, perhaps the inherent advantage lies with the good guys ¡
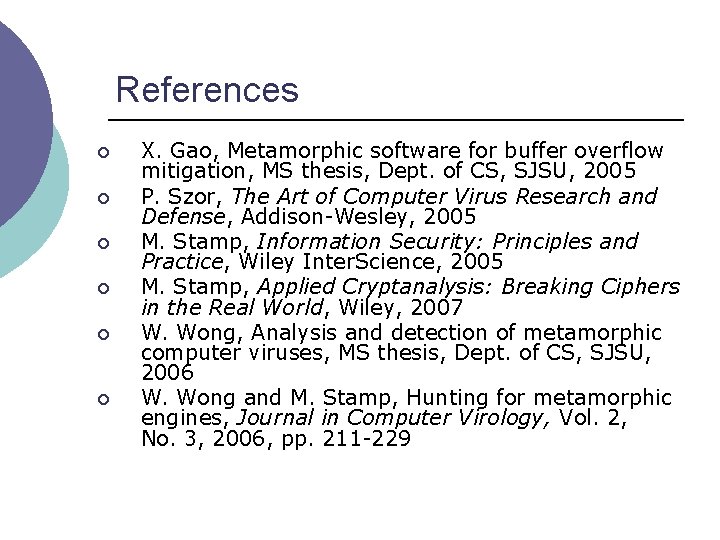
References ¡ ¡ ¡ X. Gao, Metamorphic software for buffer overflow mitigation, MS thesis, Dept. of CS, SJSU, 2005 P. Szor, The Art of Computer Virus Research and Defense, Addison-Wesley, 2005 M. Stamp, Information Security: Principles and Practice, Wiley Inter. Science, 2005 M. Stamp, Applied Cryptanalysis: Breaking Ciphers in the Real World, Wiley, 2007 W. Wong, Analysis and detection of metamorphic computer viruses, MS thesis, Dept. of CS, SJSU, 2006 W. Wong and M. Stamp, Hunting for metamorphic engines, Journal in Computer Virology, Vol. 2, No. 3, 2006, pp. 211 -229
Appendix Bonus Material
Hidden Markov Models (HMMs) ¡ ¡ ¡ state machines transitions between states have fixed probabilities each state has a probability distribution for observing a set of observation symbols states = features of the input data transition and the observation probabilities = statistical properties of features can “train” an HMM to represent a set of data (in the form of observation sequences)
HMM Example – the Occasionally Dishonest Casino
HMM Example – the Occasionally Dishonest Casino ¡ ¡ ¡ 2 states: fair/loaded The switch between dice is a Markov process Outcomes of a roll have different probabilities in each state If we can only see a sequence of rolls, the state sequence is hidden want to understand the underlying Markov process from the observations
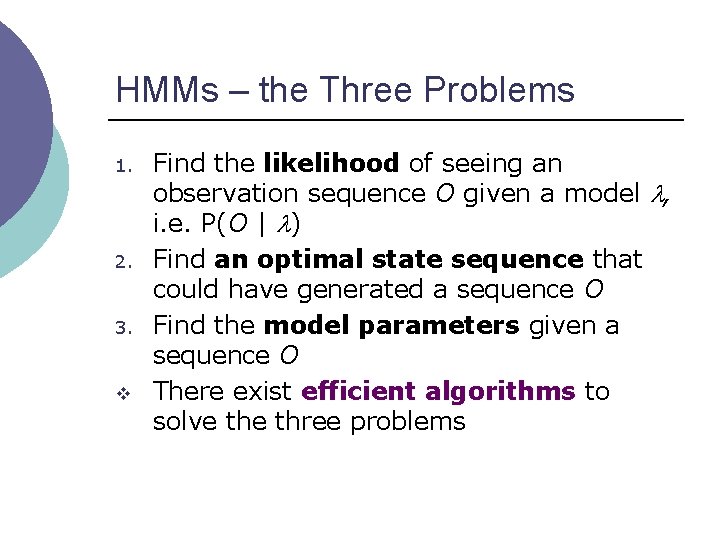
HMMs – the Three Problems 1. 2. 3. v Find the likelihood of seeing an observation sequence O given a model , i. e. P(O | ) Find an optimal state sequence that could have generated a sequence O Find the model parameters given a sequence O There exist efficient algorithms to solve three problems
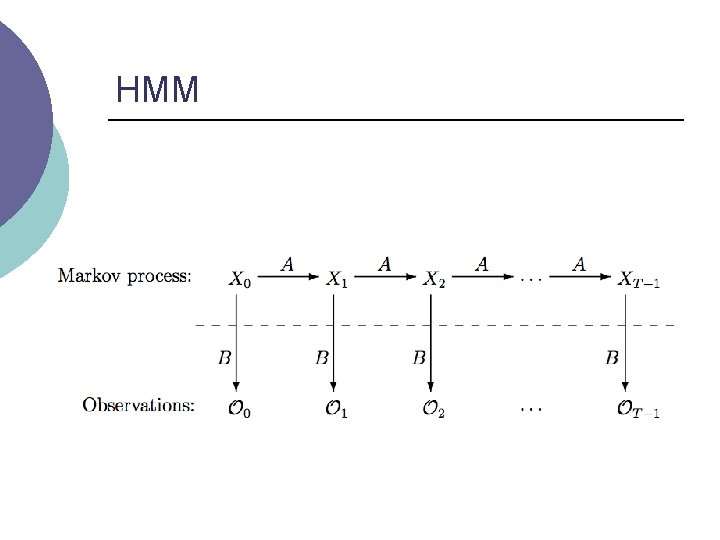
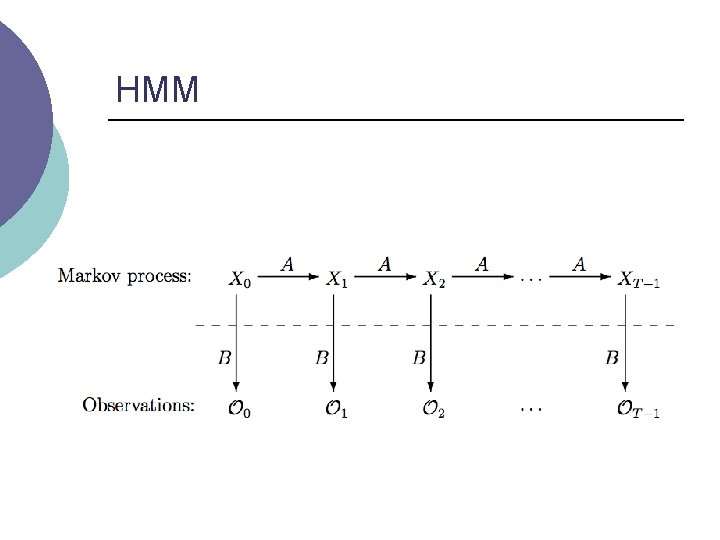
HMM
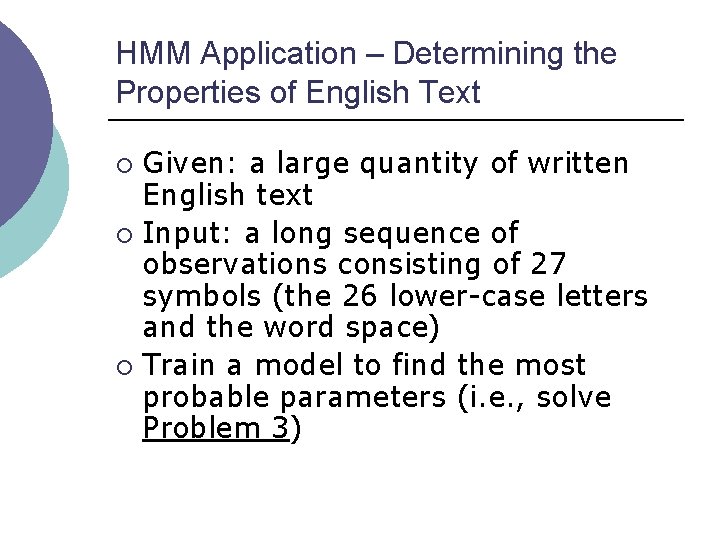
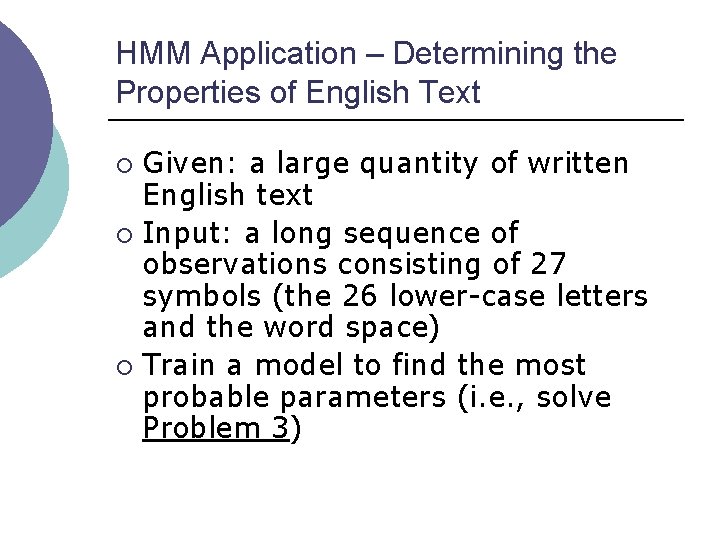
HMM Application – Determining the Properties of English Text Given: a large quantity of written English text ¡ Input: a long sequence of observations consisting of 27 symbols (the 26 lower-case letters and the word space) ¡ Train a model to find the most probable parameters (i. e. , solve Problem 3) ¡
HMM Application – Initial and Final Observation Probability Distributions
HMM Application - Results ¡ ¡ Observation probabilities converged, each letter belongs to one of the two hidden states The two states correspond to consonants and vowels Can use trained model to score any unknown sequence of letters to determine whether it corresponds to English text. (i. e. Problem 1) Note: l l no a priori assumption was made HMM effectively recovered the statistically significant feature inherent in English
HMM Application - Results Probabilities can be sensibly interpreted for up to n = 12 hidden states ¡ Trained model could be used to detect English text, even if the text is “disguised” by, say, a simple substitution cipher or similar transformation ¡

HMMs – The Trained Models
HMMs – Run Time of Training Process ¡ 5 to 38 minutes, depending on number of states N.
HMMs – Run Time of Classifying Process ¡ 0. 008 to 0. 4 milliseconds, depending on N and number of opcodes T.
AVG Anti-Virus Scanning Result