1 2 CODEBREAKER UNCLASSIFIED 1 CYBER RESEARCH AND

1

2
CODEBREAKER: (UNCLASSIFIED) 1. CYBER RESEARCH AND PASSWORD CRACKING 2. EXPERIMENTATION WITH COMMERCIAL OF THE SHELF (COTS) - SINGLE BOARD COMPUTERS (SBC) 3. HAVING FUN AND DEVELOPING CYBERSECURITY KNOWLEDGE LARRY LEIBROCK 5 MARCH 2020 3
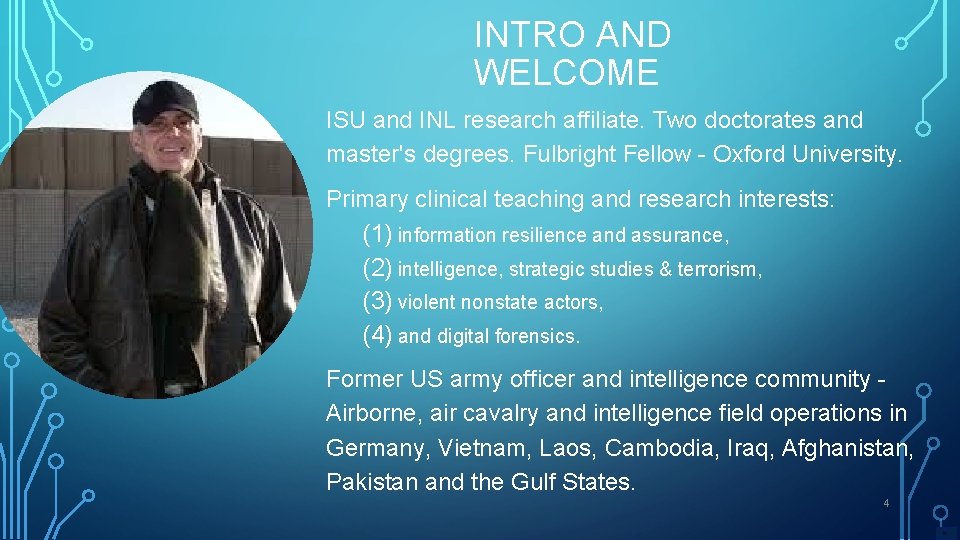
INTRO AND WELCOME ISU and INL research affiliate. Two doctorates and master's degrees. Fulbright Fellow - Oxford University. Primary clinical teaching and research interests: (1) information resilience and assurance, (2) intelligence, strategic studies & terrorism, (3) violent nonstate actors, (4) and digital forensics. Former US army officer and intelligence community Airborne, air cavalry and intelligence field operations in Germany, Vietnam, Laos, Cambodia, Iraq, Afghanistan, Pakistan and the Gulf States. 4
NOTICES • Anytime. DISCLAIMER – Stop and ask. AND questions. • Take everything with a grain of salt - Cum grano salis • I am not speaking for any USG or academic institution, whatsoever. • • I speak for me – my facts – my opinions – my evidence Idaho Computer Laws Title 18, chapter 22 commission of cyber crime – You are hereby cautioned 5
INTERSECTIONS - PHILOSOPHY, DIGITAL SECURITY TECHNOLOGIES AND TRADECRAFT • 6
DISCUSSION PLAN üIntroduce audience to case questioning and active learning discussion pedagogy üBrief discourse concerning passwords ‘aka’ credentials üDiscuss utility of a Single Board Computer (SBC) as a personal research tool for cyber threat intelligence as emerging tradecraft üHaving fun by my making use of the Feynman Learning Technique: 1. Choose a concept you want to learn and teach 2. Pretend you are teaching it to a high school student 3. Identify gaps in your explanation; back to the source material, to better understand it. 4. Teach, learn review and simplify 7
‘You should question everything. Every stripe, every star, every idea, every word spoke, everything’. – Ernest Gaines, 1993 8
CASE QUESTIONING METHOD AND DISCUSSION • Protocol – Let us will treat this as a case discussion – We (me) – pose some questions – you think, respond. • Situation You are recent university graduate - You are working at a US National Lab. You are riding in an airplane to a technical conference. You are seated next to your supervisor – “she asks you the following…. Can you give me a short, informal tutorial concerning information technology passwords with some salient concepts and how can 9 I
OVERVIEW OF PASSWORDS • If we hear the term ‘password’ your first associations might be ‘logging-in’ to a digital device, e-mail encryption, secure website access, using smart cards for banking applications or code breaking during World War II with the attack against the German Enigma encryption machine • Question – is this first association with passwords, correct? • Passwords are the most common form of authentication in our digital lives. 10
SOME SALIENT CONFUSION – THE TERM OF ART – ‘PASSWORD’ • Logging on, signing in, or signing on) is the process by which an individual gains access to a computer system by identifying and authenticating themselves. The user credentials are typically some form of "username" and a matching "password" Password – memorized secret to claim your identity • Passcode – a 4 - to 6 -digit password used to grant access to the device, similar to the code you use for an ATM bank card or a debit card • Passphrase – long passwords, a memorized secret consisting of a sequence of words or other text separated by spaces • Personal identification number (PIN) – be numeric the permissible characters are constrained to 11
PASSWORDS - NIST TERMS IN NIST SPECIAL PUBLICATION 800 -63 REV. 3 • Passwords are tokens that provide proof of digital identity. The online persona of a subject or object, and a single definition is widely debated. • The term persona is apropos as a subject or object may represent themselves online - in many ways. examples ‘good Larry, bad Larry, no Larry’. • Passwords serve as digital identity is the unique representation of a subject engaged in an online transaction. A digital identity is always unique in the context of a digital service • Jeremy Grant, head of NSTIC initiative (the US Dept. of Commerce - National Strategy for Trusted Identities in Cyberspace), declared "Passwords are a disaster 12
PASSWORDS - NIST TERMS IN NIST SPECIAL PUBLICATION 800 -63 REV. 3 • Passwords employed by modern ‘operating systems’ serve as both a reference and monitor to grant or restrict privileges for: services, controls and limitations of access for both security/authentication mechanisms and data managed by the operating systems. • Question – Is there a problem with this construct 13
PASSWORDS AS AUTHENTICATORS The classic paradigm for password/authentication systems identifies 3 factors as the cornerstones of authentication: 1. 2. Something you know (e. g. , a password). 3. Something you are or possess (e. g. , a fingerprint, face -print or other biometric data). 14 Something you have (e. g. , an ID badge or a cryptographic key).
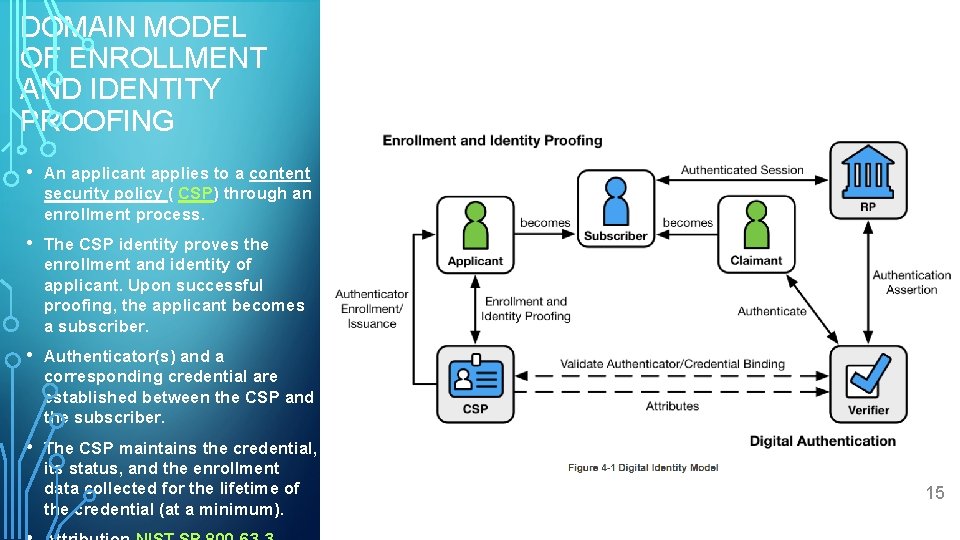
DOMAIN MODEL OF ENROLLMENT AND IDENTITY PROOFING • An applicant applies to a content security policy ( CSP) through an enrollment process. • The CSP identity proves the enrollment and identity of applicant. Upon successful proofing, the applicant becomes a subscriber. • Authenticator(s) and a corresponding credential are established between the CSP and the subscriber. • The CSP maintains the credential, its status, and the enrollment data collected for the lifetime of the credential (at a minimum). 15
PASSWORDS • Memorized Secret - A type of authenticator comprised of a character string intended to be memorized or memorable by the user (subscriber), permitting the subscriber to demonstrate something they know as part of an authentication process. • This artifact is intended to support authentication which serves to verify the identity of a user, process, or device, as the prerequisite to allowing access to a system’s resources. • Question – are passwords, conceptualized as memorized secrets a useful ‘artifact’? 16
PASSWORDS AS UGLY BABIES • The problem with passwords is that, for them to be effective, they need to be an uncommon word, of eight letters or more and not used anywhere else. However, memorizing fifty or more passwords is difficult. It is very difficult to have complex and unique passwords for as many sites as required. It is understandable that people reuse them - because they are required to use so many passwords. • According to Microsoft for a password to be effective, it needs to meet the following criteria: (1) changed every 60 days, (2) at least 8 characters long(3) Use both upper and lower case characters (4) contain a combination of alphanumeric characters and symbols (5) Unique (only used for this particular account/website) Using these minimum requirements means that there at least 2 x 1014 different possibilities. • A PC running a freely distributed brute force password cracker can attempt eight million passwords a second, meaning it would take ~ 315 days to break a password. However, a high -end computer with 25 GPUs was recently found to achieve 350 billion passwords a second, 17 which would only take ~ 10 minutes to break passwords.
“SOMETIMES WE MUST ADMIT THAT OUR CREATIONS ARE REALLY UGLY BABIES – BUT REMEMBER THESE BABIES, HAVE OUR FACES” - GENERAL STANLEY MCCRYSTAL 18
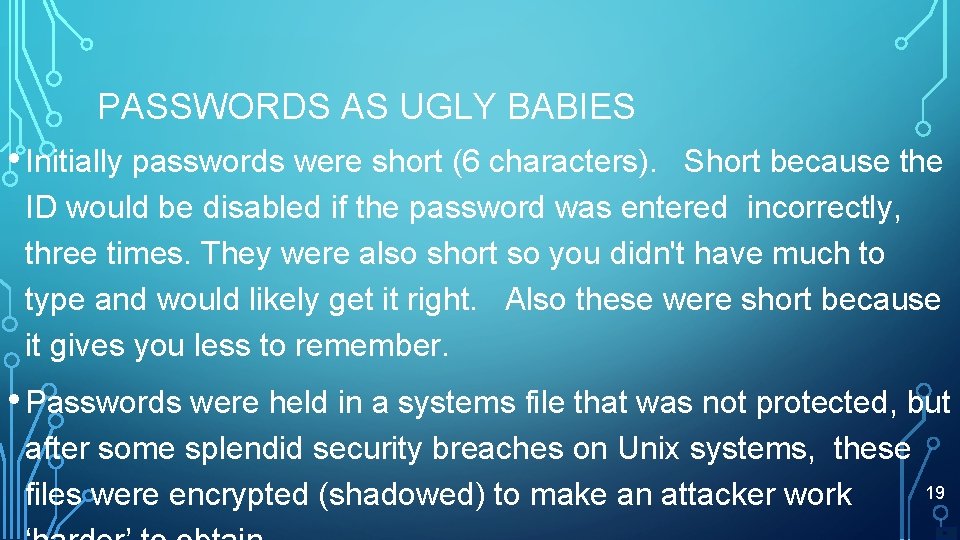
PASSWORDS AS UGLY BABIES • Initially passwords were short (6 characters). Short because the ID would be disabled if the password was entered incorrectly, three times. They were also short so you didn't have much to type and would likely get it right. Also these were short because it gives you less to remember. • Passwords were held in a systems file that was not protected, but after some splendid security breaches on Unix systems, these files were encrypted (shadowed) to make an attacker work 19
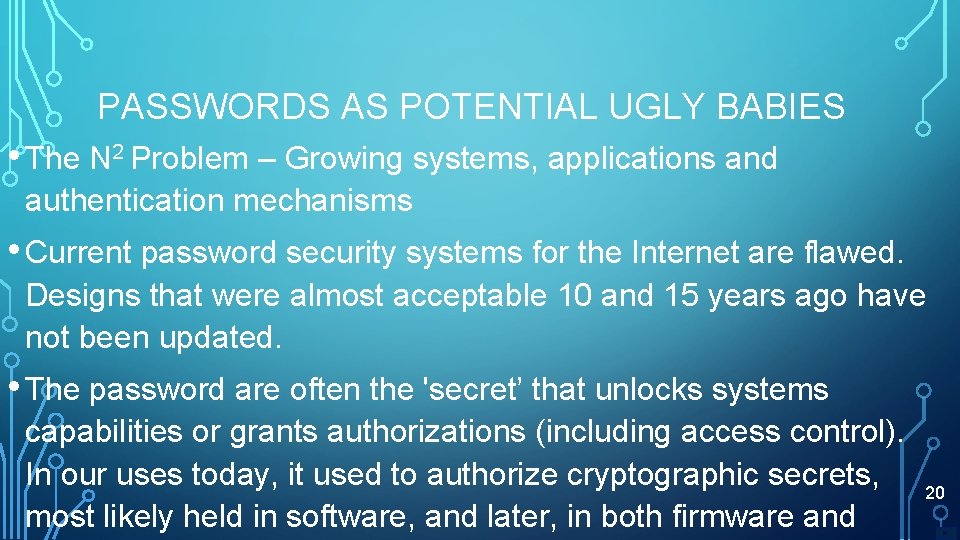
PASSWORDS AS POTENTIAL UGLY BABIES • The N 2 Problem – Growing systems, applications and authentication mechanisms • Current password security systems for the Internet are flawed. Designs that were almost acceptable 10 and 15 years ago have not been updated. • The password are often the 'secret’ that unlocks systems capabilities or grants authorizations (including access control). In our uses today, it used to authorize cryptographic secrets, most likely held in software, and later, in both firmware and 20
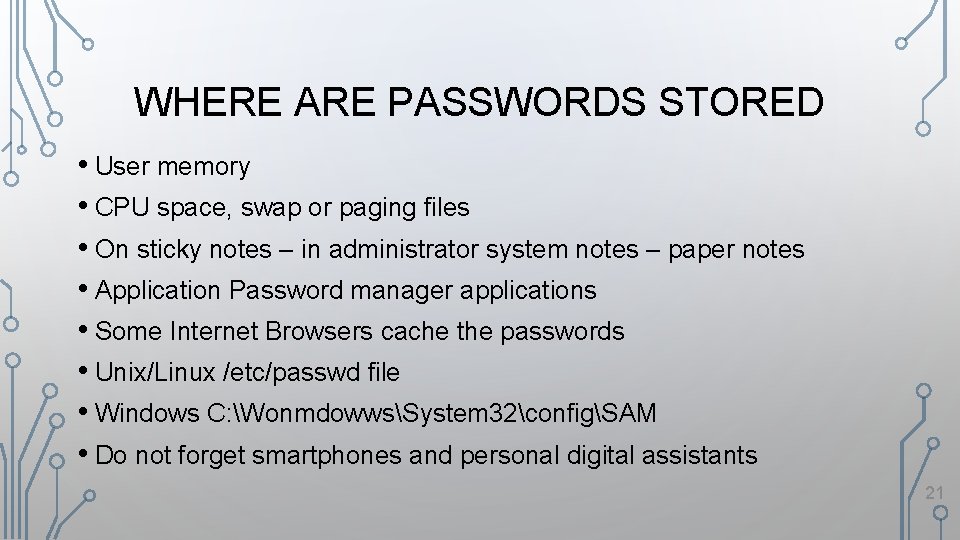
WHERE ARE PASSWORDS STORED • User memory • CPU space, swap or paging files • On sticky notes – in administrator system notes – paper notes • Application Password manager applications • Some Internet Browsers cache the passwords • Unix/Linux /etc/passwd file • Windows C: WonmdowwsSystem 32configSAM • Do not forget smartphones and personal digital assistants 21
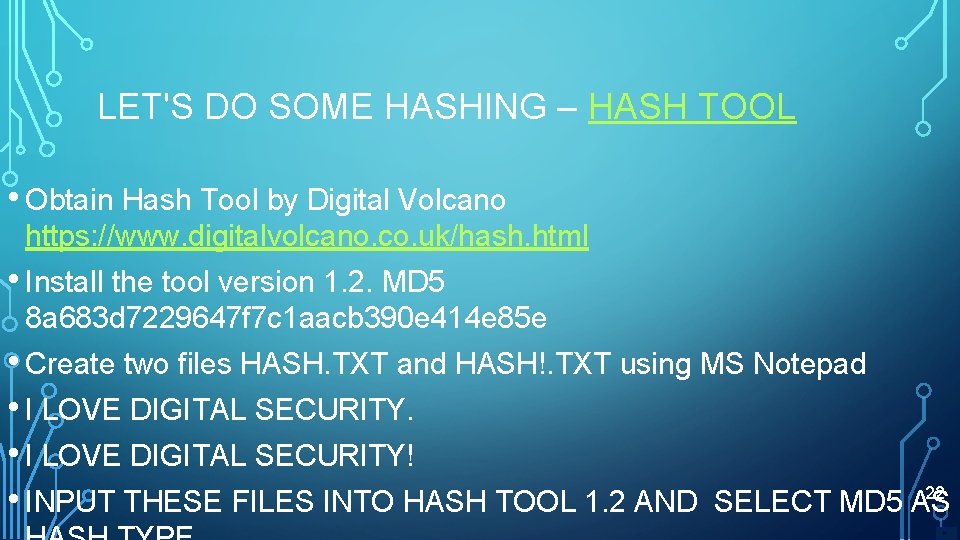
LET'S DO SOME HASHING – HASH TOOL • Obtain Hash Tool by Digital Volcano https: //www. digitalvolcano. co. uk/hash. html • Install the tool version 1. 2. MD 5 8 a 683 d 7229647 f 7 c 1 aacb 390 e 414 e 85 e • Create two files HASH. TXT and HASH!. TXT using MS Notepad • I LOVE DIGITAL SECURITY! 22 • INPUT THESE FILES INTO HASH TOOL 1. 2 AND SELECT MD 5 AS
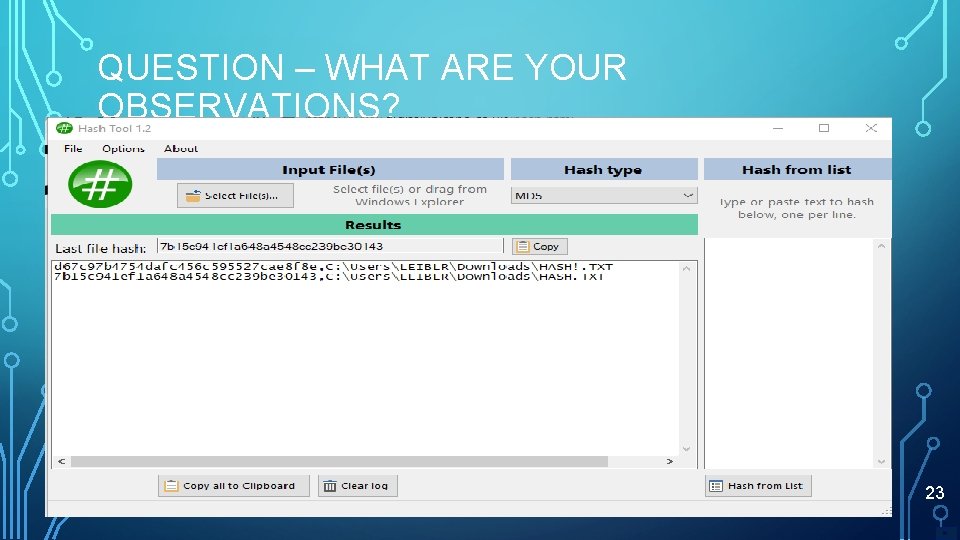
QUESTION – WHAT ARE YOUR OBSERVATIONS? 23
HASHING TECHNOLOGY IS CENTRAL TO PASSWORD TECHNOLOGY • A hash function is function that can be used to map data of arbitrary size to fixed-size values. The values returned by a hash function are called hash values, hash codes, digests, or simply hashes. The values are used to index a fixed-size table called a hash table. • Use of a hash function to index a hash table is called hashing or scatter storage addressing. 24
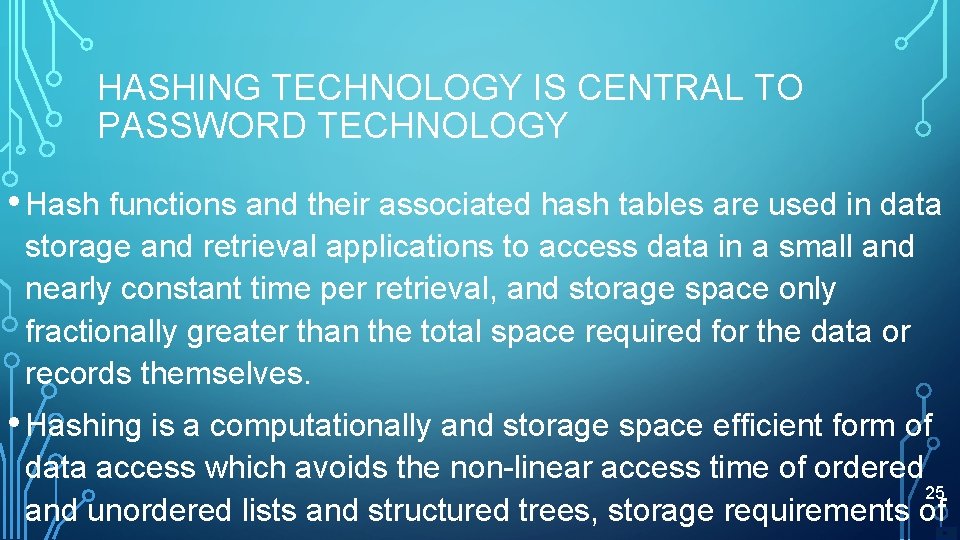
HASHING TECHNOLOGY IS CENTRAL TO PASSWORD TECHNOLOGY • Hash functions and their associated hash tables are used in data storage and retrieval applications to access data in a small and nearly constant time per retrieval, and storage space only fractionally greater than the total space required for the data or records themselves. • Hashing is a computationally and storage space efficient form of data access which avoids the non-linear access time of ordered 25 and unordered lists and structured trees, storage requirements of
26
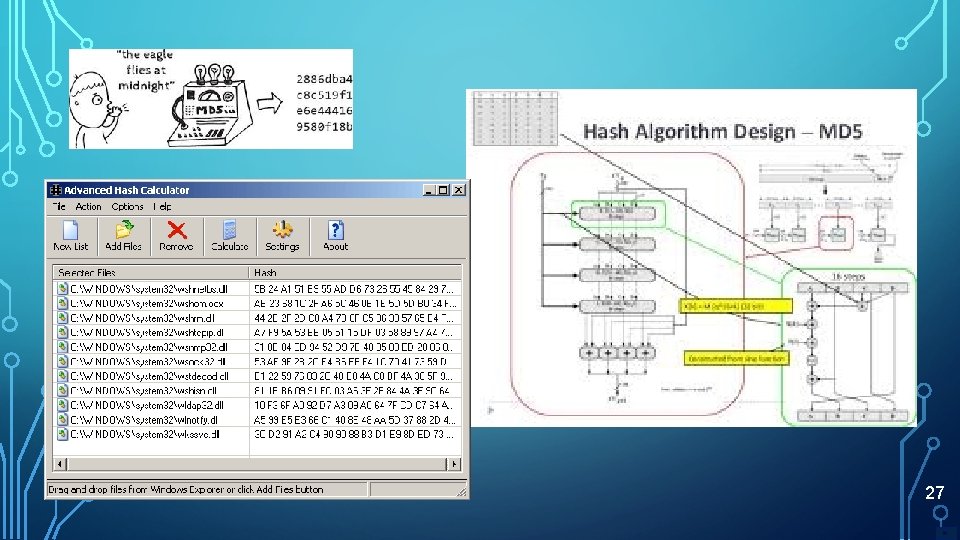
27
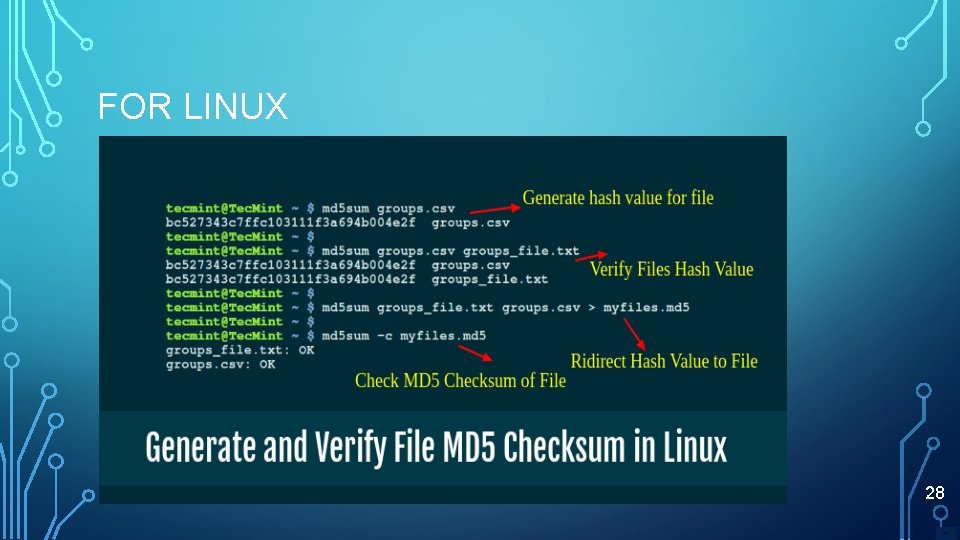
FOR LINUX 28
SO WHAT? • Hashing performs a one-way transformation on a password, turning the password into another String, called the hashed password. “One-way” means that it is practically impossible (but there is one way) to go the other way - to turn the hashed password back into the original password. 29
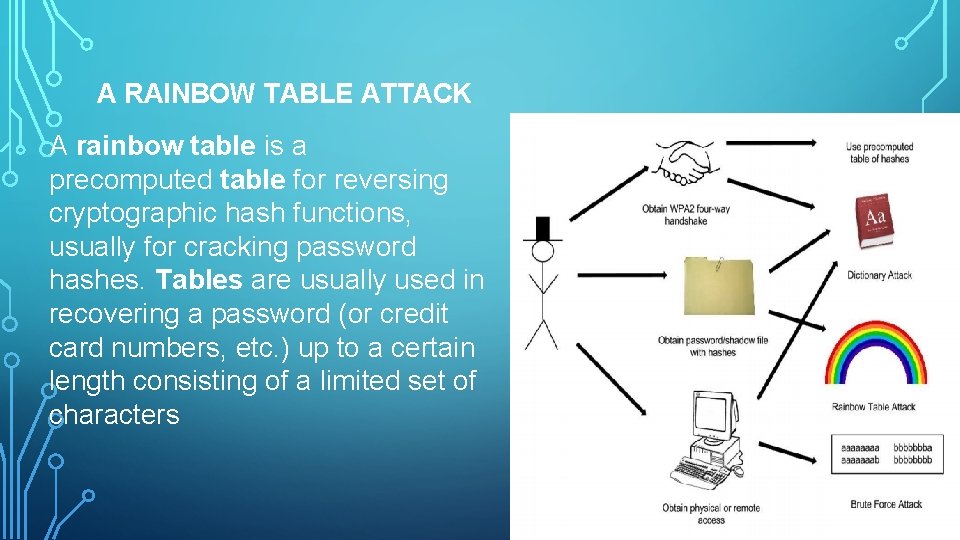
A RAINBOW TABLE ATTACK A rainbow table is a precomputed table for reversing cryptographic hash functions, usually for cracking password hashes. Tables are usually used in recovering a password (or credit card numbers, etc. ) up to a certain length consisting of a limited set of characters 30
HYPOTHETICAL DEFINITION OF SECURE PASSWORDS • A password cryptosystem is secure, if the bestknown attack is to try all possible keys – ‘time to solution’ • Password - cryptosystem is insecure, if any shortcut attack is known • By this definition, an insecure system might be 31
TIME FOR CRITICAL THINKING HYPOTHESES 32
HYPOTHESES: A USEFUL THOUGHT EXPERIMENT SIDEBAR FOR CYBER RESEARCHERS • Question - What are hypotheses? • A hypothesis is an idea that you then test through study and experimentation. A hypothesis is something more than a wild guess but less than a proven theory. • Digital technologies are creating new opportunities, individuals particularly cyber researchers should experiment to learn both what is possible and what people want. Most companies are relying on empowered, agile individual working in teams to conduct these experiments based on hypotheses. 33
SOME HYPOTHESES AND PROBLEMS WITH CREDENTIALS/PASSWORDS • HO 1 Use of passwords have solved the critical problems with cybersecurity today. • HO 2 – Passwords in social media applications enable the use to share information with both our family and friends. We share names, places you went on vacation, names of dogs and cats and other animals, even grandparents’ names and locations. That is all good. • HO 3 – One great feature of password is inability to conduct spear phishing. Malicious actors are not able to mimic the look and feel of a real company website and ask the user in a communications email for his user ID to help “solve a problem. ” 34
HO 1 USE OF PASSWORDS HAVE SOLVED THE CRITICAL PROBLEMS WITH CYBERSECURITY TODAY • Evidence # 1 - The Protected Voices initiative was launched by the FBI to help safeguard against online "foreign influence" operations along with cybersecurity threats. • Evidence # 2 - You aren't using one of the world's top 100 worst passwords • Evidence # 3 - Multiple layers of security are always a good thing. Adding extra user verification steps such as biometrics (a fingerprint) or tokens (hardware security keys or software authenticator app codes) into the mix will lock your accounts and services. • Evidence # 4 - The 2019 Top Vulnerabilities used by Cybercriminals • Evidence # 5 - Federal Cybersecurity: America’s Data at Risk – Subcommittee on investigations – US Senate 35
36
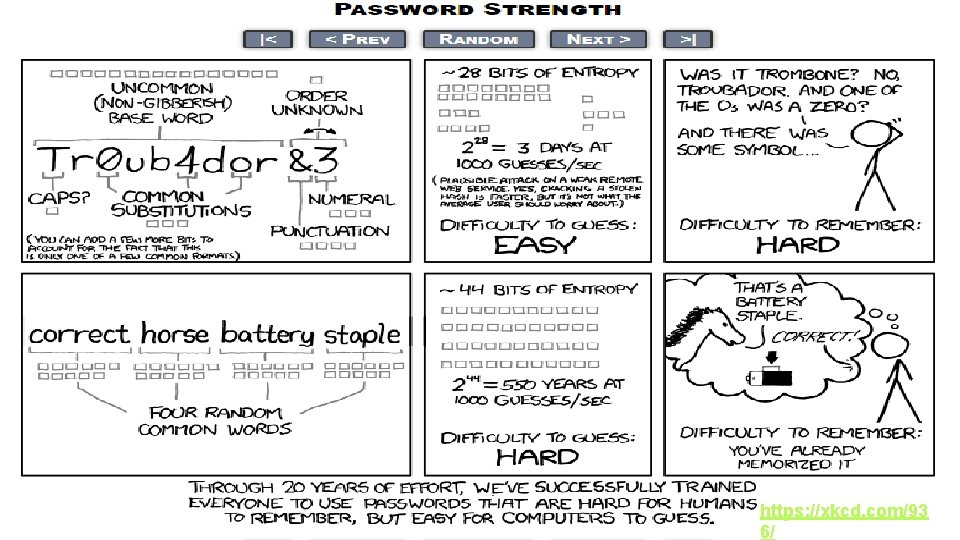
37 https: //xkcd. com/93 6/
HO 2 – PASSWORDS IN SOCIAL MEDIA APPLICATIONS ENABLE THE USE TO SHARE INFORMATION WITH BOTH OUR FAMILY AND FRIENDS. WE SHARE NAMES, PLACES YOU WENT ON VACATION, NAMES OF DOGS AND CATS AND OTHER ANIMALS, EVEN GRANDPARENTS’ NAMES AND LOCATIONS. THAT IS ALL GOOD. • Evidence # 1 = Roughly half of government and military employee passwords are weak. After conducting a thorough analysis of the 2012 Linked. In data dump to identify trends in user password strength, Watch. Guard's Threat Lab team found that half of all passwords associated with ". mil" and ". gov" email address domains within the database were objectively weak. Of the 355, 023 government and military account passwords within the database. The most common passwords used by these accounts included “ First Name, Family Name, Address, Twitter Name, 123456, " "password, " "linkedin, " "sunshine, " and "111111”. • Evidence # 2 - More than 75 percent of malware attacks are delivered over the social email and web. Making use of password compromises • Evidence # 3 - Cyber criminals continue to rely on malicious emails or 38
HO 3 – ONE GREAT FEATURE OF PASSWORD IS INABILITY TO CONDUCT SPEAR PHISHING. MALICIOUS ACTORS ARE NOT ABLE TO MIMIC THE LOOK AND FEEL OF A REAL COMPANY WEBSITE AND ASK THE USER IN A COMMUNICATIONS EMAIL FOR HIS USER ID TO HELP “SOLVE A PROBLEM. ” • The fraudulent practice of sending emails ostensibly from a known or trusted sender in order to induce targeted individuals to reveal confidential information. Spear phishing represents a serious threat for every industry. • Drivers • • Rising events of spear phishing attacks is propelling the severity of attacks • • Surging adoption of digitization in the industry verticals is contributing of the growth of the market • Surging acquisition of Bring Your Own Device (BYOD) policy in organizations is fueling the growth of the market Absence of knowledge and understanding of current threats and cyber-attacks is retraining the growth of the market Various organizations has raised concerns regarding outsourcing of security services which is 39
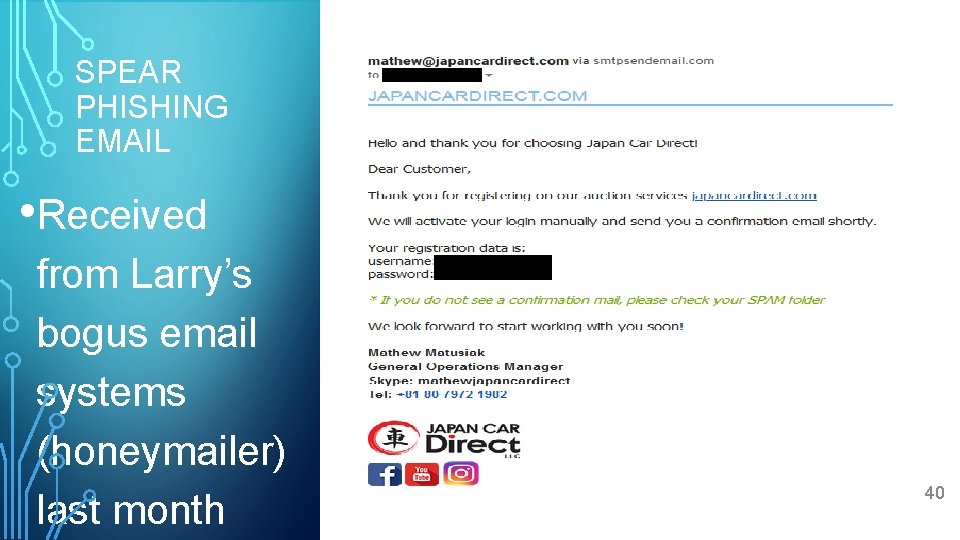
SPEAR PHISHING EMAIL • Received from Larry’s bogus email systems (honeymailer) last month 40
HO 4 – INTRINSICALLY PASSWORD ARTIFACTS ARE STORED IN CRYPTOGRAPHICALLY ‘SECURE’ REPOSITORIES IN BOTH SOFTWARE AND HARDWARE AND ARE NOT SUBJECT TO COMPROMISE. • Some devices have hard coded hashed passwords in firmware and/or hardware. • The specious observation of successful attacks against ‘legacy hash/password’ implementations • Network sniffing is the process of intercepting data packets sent over a network. This can be done by the specialized software program or hardware equipment. Sniffing can be used to; Capture sensitive data such as login credentials Eavesdrop on chat messages Capture files have been transmitted over a network. Many computer protocols are vulnerable to password/credential sniffing i. e Telnet, Rlogin, HTTP, SMTP, NNTP, POP, 41

42
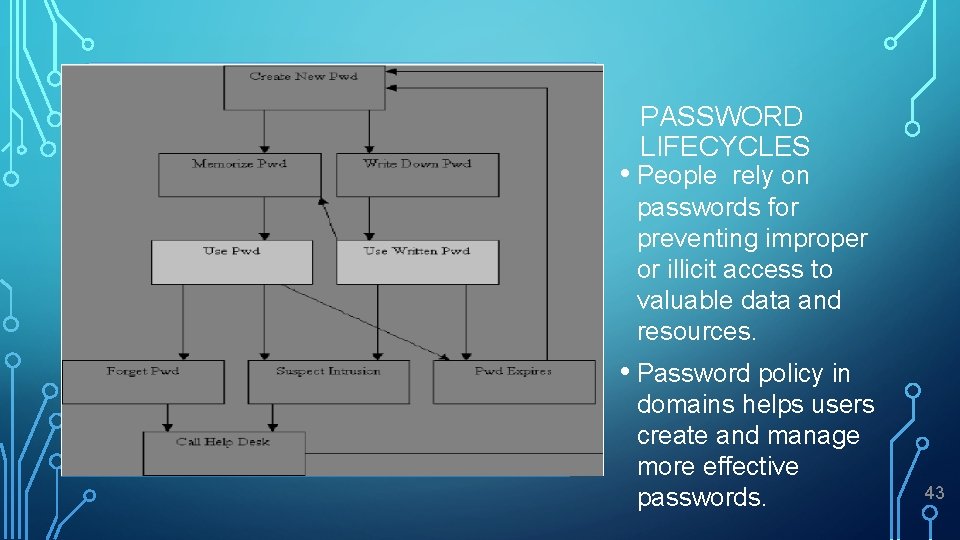
PASSWORD LIFECYCLES • People rely on passwords for preventing improper or illicit access to valuable data and resources. • Password policy in domains helps users create and manage more effective passwords. 43
44
HAVING FUN BY MY MAKING USE OF THE FEYNMAN LEARNING TECHNIQUE: 1. Choose a concept you want to learn about 2. Pretend you are teaching it to a student in grade 6 3. Identify gaps in your explanations; Go back to the source material, to better understand it. 4. Review and simplify 45
CIA AS DESIRED ATTRIBUTES • Confidentiality, Integrity and Availability • Confidentiality: prevent unauthorized reading of information • Integrity: prevent unauthorized writing of information • Availability: data is available in a timely manner when needed • Availability is a “new” security concern • Due to denial of service (Do. S) threats 46
CRYPTANALYSIS ATTACKS • Eve wants to recover password, credential key or plaintext • Eve is not bound by any rules • For example, Eve might attack the implementation, not the algorithm itself • She might use “side channel” info, etc. 47

48
HOW ARE WE GOING TO PERFORM THE FEYNMAN EXPERIMENT? 49
DISCUSS UTILITY OF A SINGLE BOARD COMPUTER (SBC) AS A PERSONAL RESEARCH TOOL FOR CYBER THREAT INTELLIGENCE AS EMERGING TRADECRAFT 50
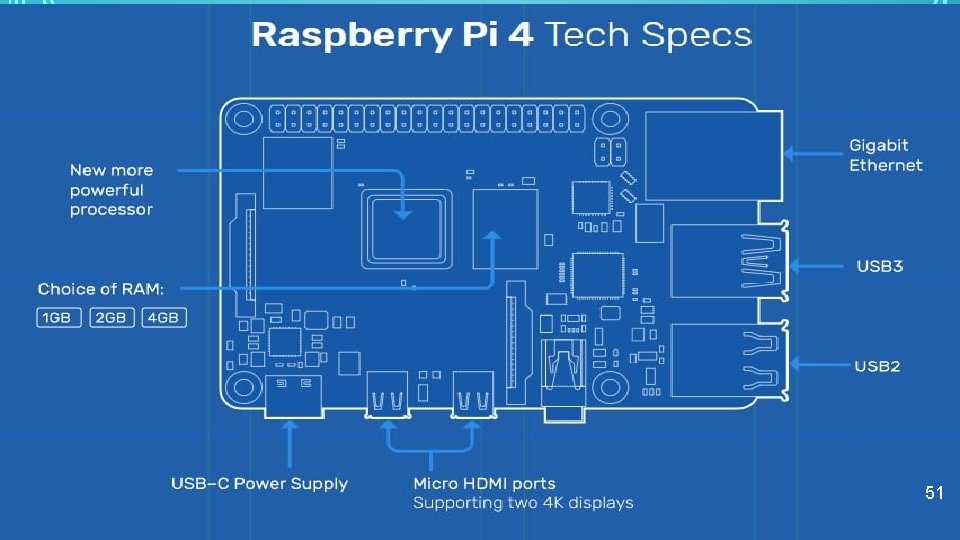
51
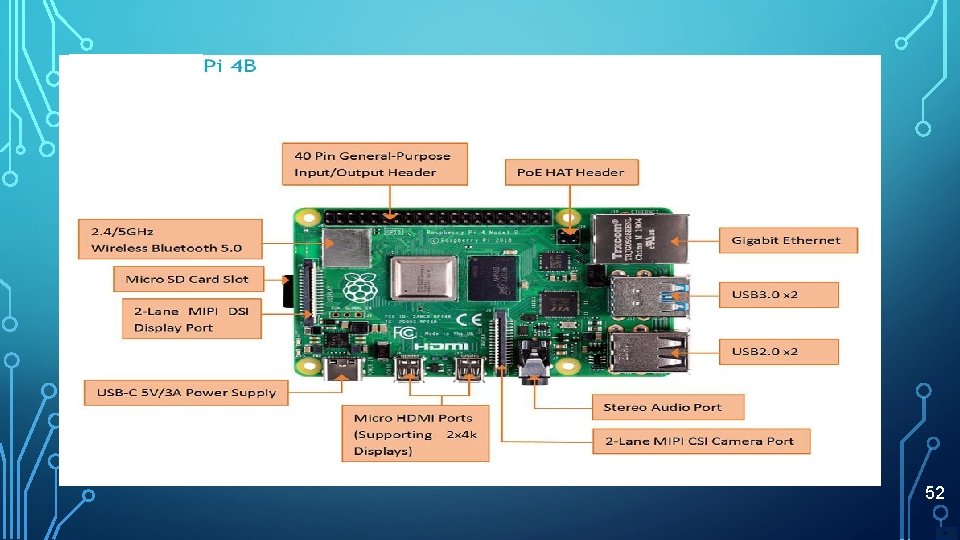
52
HEADLESS KALI LINUX SETUP ON RASPBERRY PI 4 53
HTTPS: //WWW. YOUTUBE. COM/WATCH? V=7 R 10 QN_UCH 0 Caution = Recommend you do not have this in your luggage – TSA has zero sense of humor. 54
ONLINE DEMOS FOR CRACKING PASSWORDS • Kali Linux 2020. 1 | The Linux Distro For Cyber Reliance Researchers • How to Crack Password using John The Ripper Tool | Crack Linux, Windows, Zip, md 5 Password • Generating Rainbow Tables With Rainbow. Crack • Wi-Fi hacking WPA-WPA 2 using aircrack-ng in Kali linux 55
PASSWORD BREAKING - QUICK AND DIRTY • Use Kali Linux – John • commands cp /etc/shadow. / then cp /etc/password. / then unshadow passwd shadow > phashes finally john phashes • John the Ripper makes use of its list 3, 500 passwords. • You can build your own 56
LARRY’S SPECIAL 10 PASSWORD LIST (~4 TO 5 % OF ALL ACCOUNTS – ATTRIBUTED OCCUPYTHEWEB 123456, 654321, sunshine, qwerty, iloveyou, admin, user, !@#$%^&* password 1 +_)(*&^% 57
EXHAUSTIVE KEY SEARCH • How can Eve attack a ciphered key? • https: //www. tunnelsup. com/getting-started-cracking-password-hashes/ • Download the password hash file bundle from the Kore. Logic 2012 DEFCON challenge. Or use this mirror. • She can simply try all possible keys and test each to see if it is correct • Exhaustive key search • To prevent an exhaustive key search, a cryptosystem must have a large keyspace • Must be too many keys for Eve to try them all in any reasonable amount of time • • • Resources http: //www. openwall. com/john/doc/EXAMPLES. shtml 58
USING WIRESHARK TO CAPTURE DATA PACKETS AS THEY ARE TRANSMITTED OVER HTTP PROTOCOL • How to Capture Passwords with Wireshark • We will sniff the network using Wireshark, then login to a web application that does not use secure communication. We will login to a web application on http: //www. techpanda. org/ • The login address is admin@google. com , and the password is Password 2010. • Note: we will login to the web app for demonstration purposes only. The technique can also sniff data packets from other computers that are on the same network as the one that you are using to sniff. The sniffing is not only limited to techpanda. org, but also 59 sniffs all HTTP and other protocols data packets.
BEYOND EXHAUSTIVE SEARCH • A large keyspace is necessary for security • But a large keyspace is not enough • Shortcut attacks might exist • We have seen many examples of shortcut attacks, i. e. social media artifacts, affiliations, keyloggers • In cryptography we can (almost) never prove that no shortcut attack exists • This makes cyber research interesting… 60

CROWPI- COMPACT RASPBERRY PI EDUCATIONAL KIT 61
THIS DOCUMENT SHOWS THE APPROXIMATE AMOUNT OF TIME REQUIRED FOR A COMPUTER OR A CLUSTER OF COMPUTERS TO GUESS VARIOUS PASSWORDS. HTTP: //WWW. LOCKDOWN. CO. UK/? PG=COMBI&S=ARTIC LES 62
PASSWORD CYBER THREAT INTELLIGENCE TOOLS 1. Introduction to the 10 Most Popular Password Cracking Tools 2. Know top worst passwords 3. John the Ripper 4. Crowpi 5. Portable Cracking Rig 6. 25 -GPU cluster cracks every standard Windows password in <6 hours (350 billion passwords a second 7. Building a Hacking Kit with Raspberry Pi and Kali Linux 63

64
ARE PASSWORDS AN EXEMPLAR OF A FAILED TECHNOLOGY? 65
OK – WHAT CAN WE DO! – 13 CONSIDERATIONS 1. Critically reappraise your assumptions concerning ‘trust’ in your digital lives. Segregate professional, personal email, end-to-end encrypted emails and onetime anonymous email accounts 2. Assume both your password credentials are compromised on your digital systems, make use of virtual private networks (VPNs) in all open networks – i. e. Starbucks, Burger King, Mc. Donalds etc. 3. Assume malicious actors know you, your social media and your online buyer history i. e Web Cache ‘hooking’. 4. 5. 6. Consider use of password vaults or strong encrypted password managers Consider dual device authentication – smart phones 66 Never buy/use written password books – sorry Amazon – no sale for these particular items -
7. 8. 9. OK – WHAT CAN WE DO! – 13 CONSIDERATIONS Use robust passwords generators and randomly ‘substantively’ change passwords Multiple accounts – multiple passwords Never return digital storage media to vendors, resellers or donation institutions whatsoever 10. Never share your passwords i. e. wives, family, significant others, 11. For your devices – invest and use biometric authentication – understand wiping procedures 12. Enact USB or Smartcard security keys and encrypted data 13. Use Google Alerts for notice of your account compromises – immediately change 67 associated password
• Password Skills and Practice is critical skill for Professional Cyberwarriors • Password cracking tools exist for legitimate system admin checks, pen testing etc 68
• Introduction • Used case method to support interactions • Examined Password as a failing technology • Alice, Bob and Eve Password Needs and Attacks • Discussed Key Searches • Reviewed SBC Raspberry Pi 4 – with Kali and Wireshark • 13 Ideas for ‘What we can do about 69
YOUR CRITIQUE AND QUESTIONS 70
- Slides: 70