Chapter 5 Database and Cloud Security Databases Structured
Chapter 5 Database and Cloud Security
Databases Structured collection of data stored for use by one or more applications Contains the relationships between data items and groups of data items Can sometimes contain sensitive data that needs to be secured Database management system (DBMS) • Suite of programs for constructing and maintaining the database • Offers ad hoc query facilities to multiple users and applications Query language: Provides a uniform interface to the database Organizational databases tend to concentrate sensitive information in a single logical system. Examples include: • Corporate financial data • Confidential phone records • Customer and employee information, such as name, Social Security number, bank account information, credit card information • Proprietary product information • Health care information and medical records
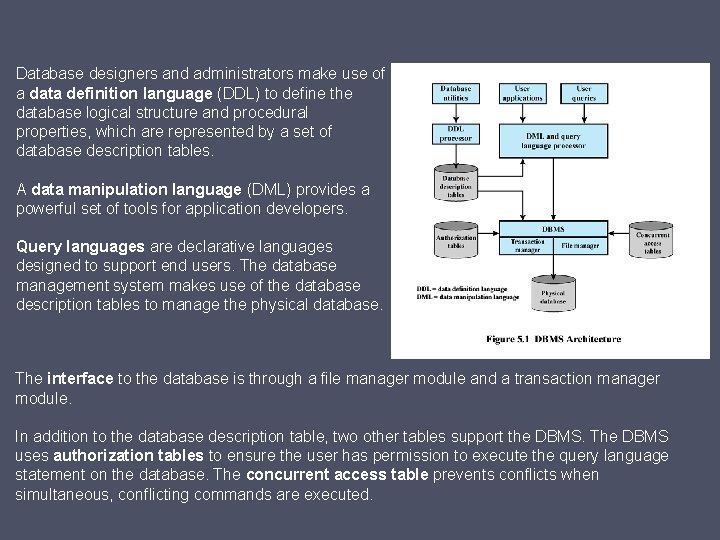
Database designers and administrators make use of a data definition language (DDL) to define the database logical structure and procedural properties, which are represented by a set of database description tables. A data manipulation language (DML) provides a powerful set of tools for application developers. Query languages are declarative languages designed to support end users. The database management system makes use of the database description tables to manage the physical database. The interface to the database is through a file manager module and a transaction manager module. In addition to the database description table, two other tables support the DBMS. The DBMS uses authorization tables to ensure the user has permission to execute the query language statement on the database. The concurrent access table prevents conflicts when simultaneous, conflicting commands are executed.
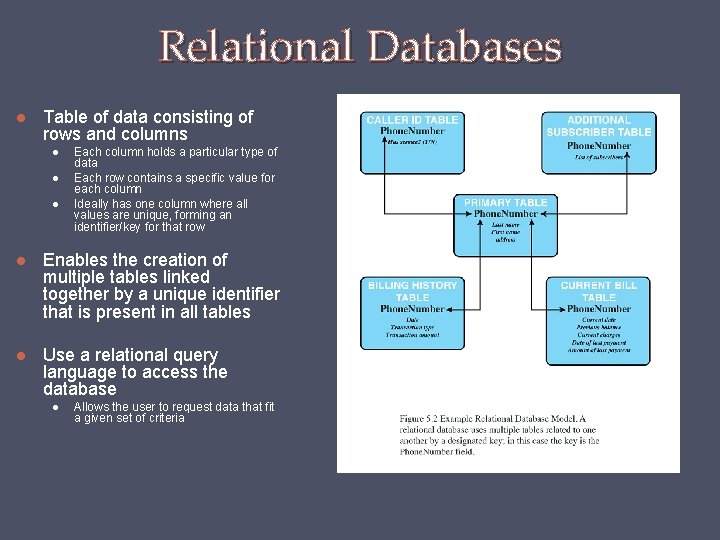
Relational Databases Table of data consisting of rows and columns Each column holds a particular type of data Each row contains a specific value for each column Ideally has one column where all values are unique, forming an identifier/key for that row Enables the creation of multiple tables linked together by a unique identifier that is present in all tables Use a relational query language to access the database Allows the user to request data that fit a given set of criteria
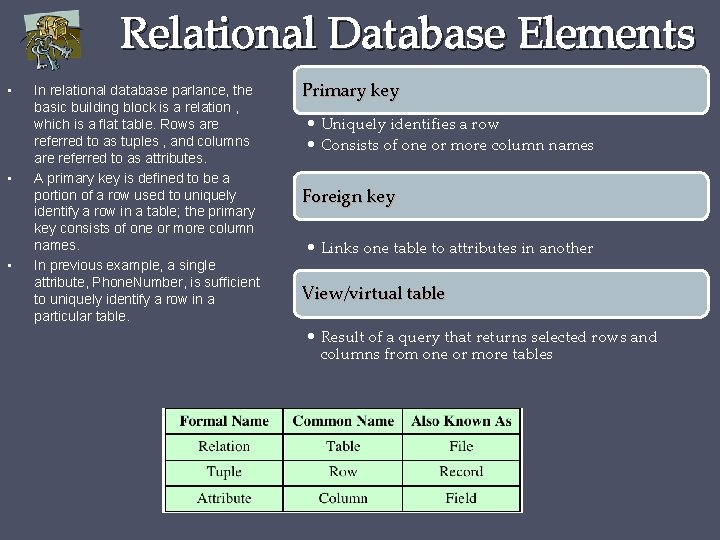
Relational Database Elements • • • In relational database parlance, the basic building block is a relation , which is a flat table. Rows are referred to as tuples , and columns are referred to as attributes. A primary key is defined to be a portion of a row used to uniquely identify a row in a table; the primary key consists of one or more column names. In previous example, a single attribute, Phone. Number, is sufficient to uniquely identify a row in a particular table. Primary key • Uniquely identifies a row • Consists of one or more column names Foreign key • Links one table to attributes in another View/virtual table • Result of a query that returns selected rows and columns from one or more tables
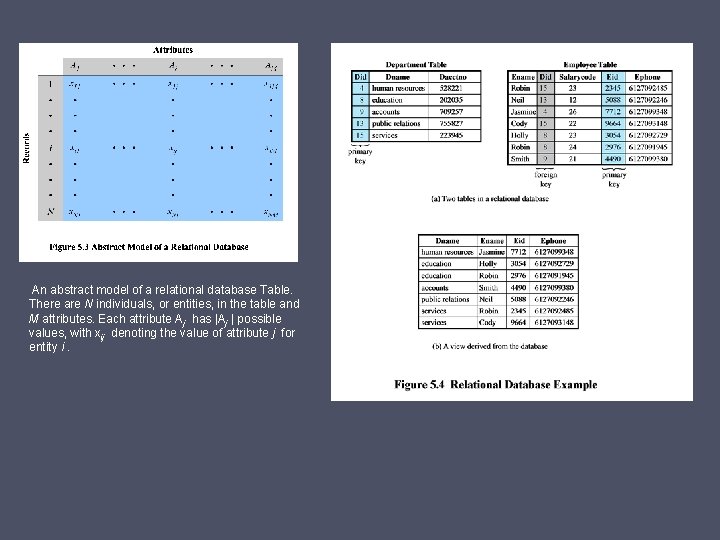
An abstract model of a relational database Table. There are N individuals, or entities, in the table and M attributes. Each attribute Aj has |Aj | possible values, with xij denoting the value of attribute j for entity i.
Structured Query Language (SQL) Standardized language to define schema, manipulate, and query data in a relational database Several similar versions of ANSI/ISO standard All follow the same basic syntax and semantics SQL statements can be used to: • Create tables • Insert and delete data in tables • Create views • Retrieve data with query statements
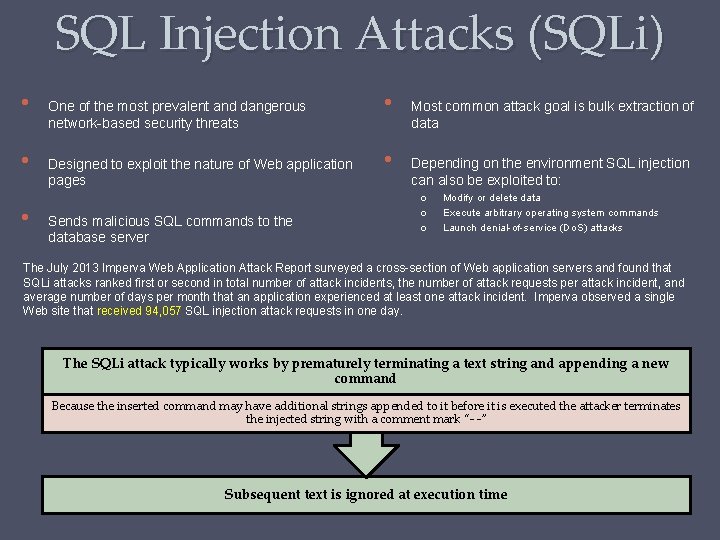
SQL Injection Attacks (SQLi) • • • One of the most prevalent and dangerous network-based security threats Designed to exploit the nature of Web application pages Sends malicious SQL commands to the database server • • Most common attack goal is bulk extraction of data Depending on the environment SQL injection can also be exploited to: o o o Modify or delete data Execute arbitrary operating system commands Launch denial-of-service (Do. S) attacks The July 2013 Imperva Web Application Attack Report surveyed a cross-section of Web application servers and found that SQLi attacks ranked first or second in total number of attack incidents, the number of attack requests per attack incident, and average number of days per month that an application experienced at least one attack incident. Imperva observed a single Web site that received 94, 057 SQL injection attack requests in one day. The SQLi attack typically works by prematurely terminating a text string and appending a new command Because the inserted command may have additional strings appended to it before it is executed the attacker terminates the injected string with a comment mark “- -” Subsequent text is ignored at execution time
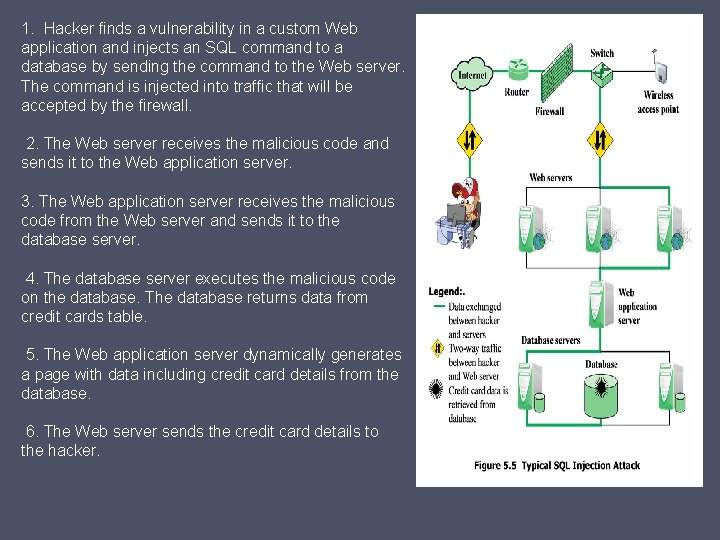
1. Hacker finds a vulnerability in a custom Web application and injects an SQL command to a database by sending the command to the Web server. The command is injected into traffic that will be accepted by the firewall. 2. The Web server receives the malicious code and sends it to the Web application server. 3. The Web application server receives the malicious code from the Web server and sends it to the database server. 4. The database server executes the malicious code on the database. The database returns data from credit cards table. 5. The Web application server dynamically generates a page with data including credit card details from the database. 6. The Web server sends the credit card details to the hacker.
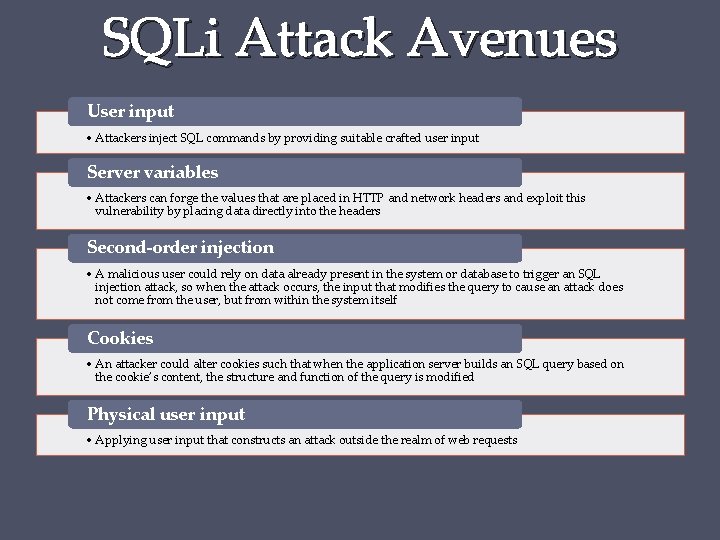
SQLi Attack Avenues User input • Attackers inject SQL commands by providing suitable crafted user input Server variables • Attackers can forge the values that are placed in HTTP and network headers and exploit this vulnerability by placing data directly into the headers Second-order injection • A malicious user could rely on data already present in the system or database to trigger an SQL injection attack, so when the attack occurs, the input that modifies the query to cause an attack does not come from the user, but from within the system itself Cookies • An attacker could alter cookies such that when the application server builds an SQL query based on the cookie’s content, the structure and function of the query is modified Physical user input • Applying user input that constructs an attack outside the realm of web requests
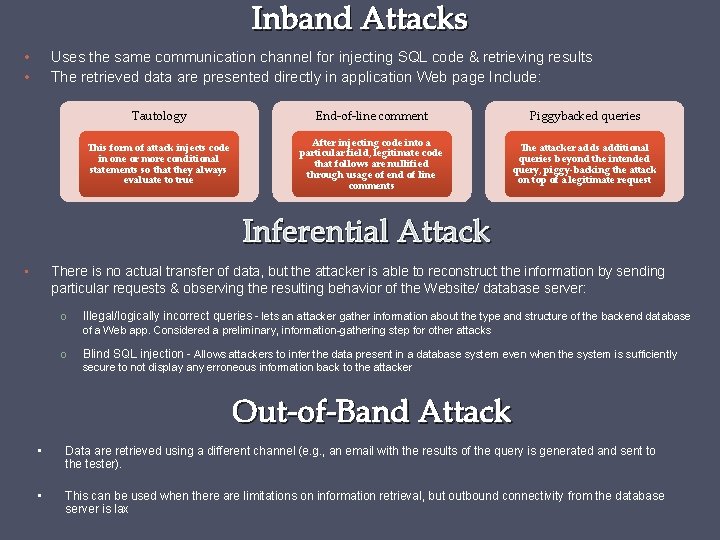
Inband Attacks • • Uses the same communication channel for injecting SQL code & retrieving results The retrieved data are presented directly in application Web page Include: Tautology End-of-line comment Piggybacked queries This form of attack injects code in one or more conditional statements so that they always evaluate to true After injecting code into a particular field, legitimate code that follows are nullified through usage of end of line comments The attacker adds additional queries beyond the intended query, piggy-backing the attack on top of a legitimate request Inferential Attack • There is no actual transfer of data, but the attacker is able to reconstruct the information by sending particular requests & observing the resulting behavior of the Website/ database server: o Illegal/logically incorrect queries - lets an attacker gather information about the type and structure of the backend database o Blind SQL injection - Allows attackers to infer the data present in a database system even when the system is sufficiently of a Web app. Considered a preliminary, information-gathering step for other attacks secure to not display any erroneous information back to the attacker Out-of-Band Attack • Data are retrieved using a different channel (e. g. , an email with the results of the query is generated and sent to the tester). • This can be used when there are limitations on information retrieval, but outbound connectivity from the database server is lax
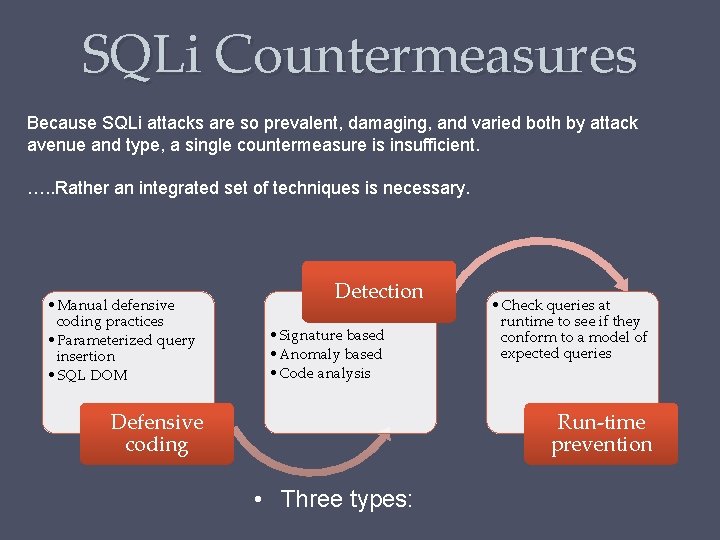
SQLi Countermeasures Because SQLi attacks are so prevalent, damaging, and varied both by attack avenue and type, a single countermeasure is insufficient. …. . Rather an integrated set of techniques is necessary. • Manual defensive coding practices • Parameterized query insertion • SQL DOM Detection • Signature based • Anomaly based • Code analysis Defensive coding • Check queries at runtime to see if they conform to a model of expected queries Run-time prevention • Three types:
SQL Access Controls Database access control system determines If the user has access to the entire database or just portions of it. What access rights the user has (create, insert, delete, update, read, write). • Centralized administration - Small number of privileged users may grant and revoke access rights • Ownership-based administration - The creator of a table may grant and revoke access rights to the table • Decentralized administration - The owner of the table may grant and revoke authorization rights to other users, allowing them to grant and revoke access rights to the table • Two commands for managing access rights: • Grant o Used to grant one or more access rights or can be used to assign a user to a role • Revoke • o Revokes the access rights Typical access rights are: • Select / Insert / Update / Delete /References • As with any access control system, a database access control system distinguishes different access rights, including create, insert, delete, update, read, and write. Some DBMSs provide considerable control over the granularity of access rights. • Access rights can be determined based on the contents of a table entry. For example, in a personnel database, some users may be limited to seeing salary information only up to a certain maximum value and a department manager may only be allowed to view salary information for employees in his or her department.
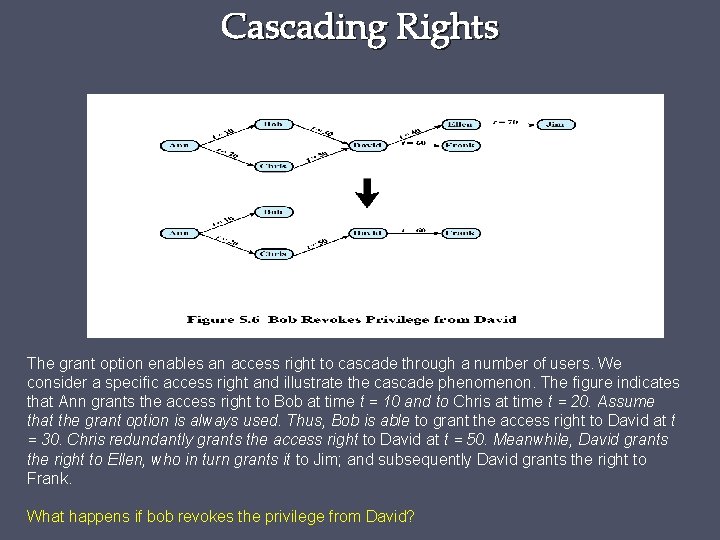
Cascading Rights The grant option enables an access right to cascade through a number of users. We consider a specific access right and illustrate the cascade phenomenon. The figure indicates that Ann grants the access right to Bob at time t = 10 and to Chris at time t = 20. Assume that the grant option is always used. Thus, Bob is able to grant the access right to David at t = 30. Chris redundantly grants the access right to David at t = 50. Meanwhile, David grants the right to Ellen, who in turn grants it to Jim; and subsequently David grants the right to Frank. What happens if bob revokes the privilege from David?
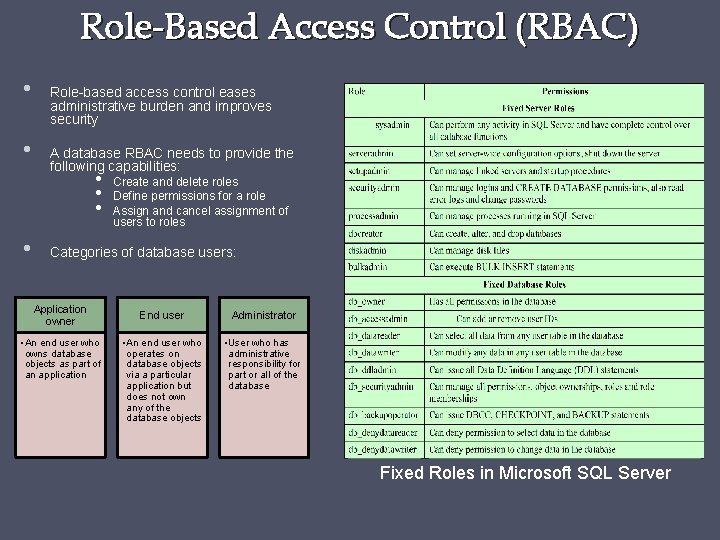
Role-Based Access Control (RBAC) • • Role-based access control eases administrative burden and improves security A database RBAC needs to provide the following capabilities: • • Create and delete roles Define permissions for a role Assign and cancel assignment of users to roles Categories of database users: Application owner • An end user who owns database objects as part of an application End user Administrator • An end user who operates on database objects via a particular application but does not own any of the database objects • User who has administrative responsibility for part or all of the database Fixed Roles in Microsoft SQL Server
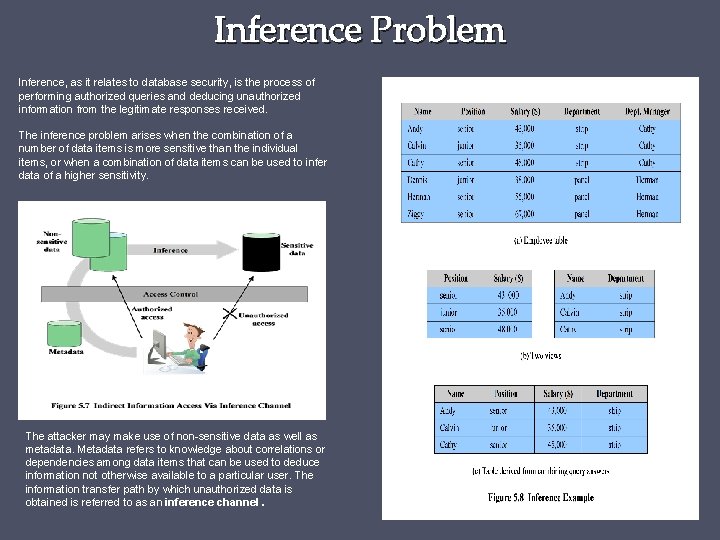
Inference Problem Inference, as it relates to database security, is the process of performing authorized queries and deducing unauthorized information from the legitimate responses received. The inference problem arises when the combination of a number of data items is more sensitive than the individual items, or when a combination of data items can be used to infer data of a higher sensitivity. The attacker may make use of non-sensitive data as well as metadata. Metadata refers to knowledge about correlations or dependencies among data items that can be used to deduce information not otherwise available to a particular user. The information transfer path by which unauthorized data is obtained is referred to as an inference channel.
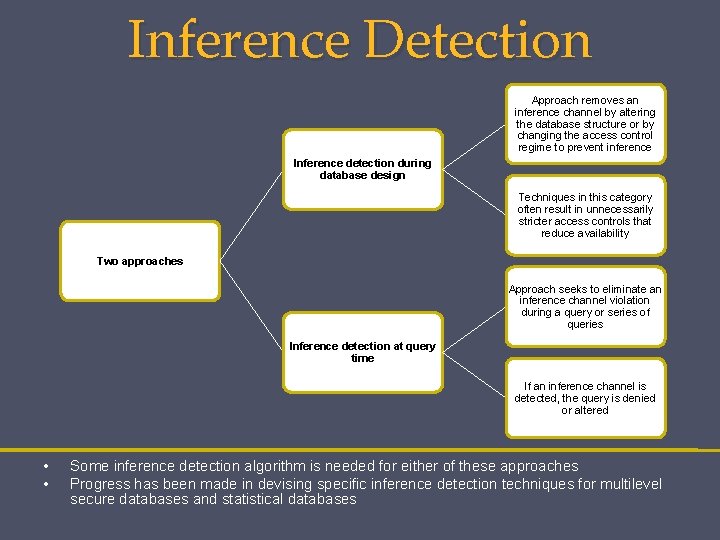
Inference Detection Approach removes an inference channel by altering the database structure or by changing the access control regime to prevent inference Inference detection during database design Techniques in this category often result in unnecessarily stricter access controls that reduce availability Two approaches Approach seeks to eliminate an inference channel violation during a query or series of queries Inference detection at query time If an inference channel is detected, the query is denied or altered • • Some inference detection algorithm is needed for either of these approaches Progress has been made in devising specific inference detection techniques for multilevel secure databases and statistical databases
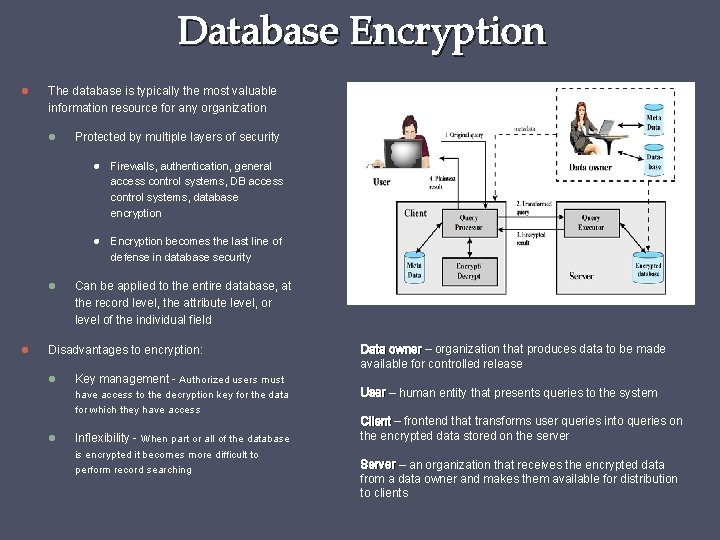
Database Encryption The database is typically the most valuable information resource for any organization Protected by multiple layers of security Firewalls, authentication, general access control systems, DB access control systems, database encryption Encryption becomes the last line of defense in database security Can be applied to the entire database, at the record level, the attribute level, or level of the individual field Disadvantages to encryption: Key management - Authorized users must have access to the decryption key for the data for which they have access Data owner – organization that produces data to be made available for controlled release Inflexibility - When part or all of the database is encrypted it becomes more difficult to perform record searching User – human entity that presents queries to the system Client – frontend that transforms user queries into queries on the encrypted data stored on the server Server – an organization that receives the encrypted data from a data owner and makes them available for distribution to clients
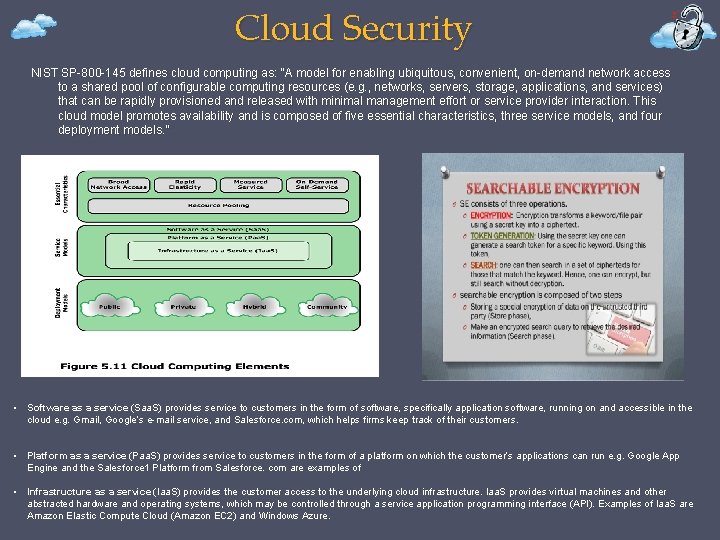
Cloud Security NIST SP-800 -145 defines cloud computing as: “A model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources (e. g. , networks, servers, storage, applications, and services) that can be rapidly provisioned and released with minimal management effort or service provider interaction. This cloud model promotes availability and is composed of five essential characteristics, three service models, and four deployment models. ” • Software as a service (Saa. S) provides service to customers in the form of software, specifically application software, running on and accessible in the cloud e. g. Gmail, Google’s e-mail service, and Salesforce. com, which helps firms keep track of their customers. • Platform as a service (Paa. S) provides service to customers in the form of a platform on which the customer’s applications can run e. g. Google App Engine and the Salesforce 1 Platform from Salesforce. com are examples of • Infrastructure as a service (Iaa. S) provides the customer access to the underlying cloud infrastructure. Iaa. S provides virtual machines and other abstracted hardware and operating systems, which may be controlled through a service application programming interface (API). Examples of Iaa. S are Amazon Elastic Compute Cloud (Amazon EC 2) and Windows Azure.
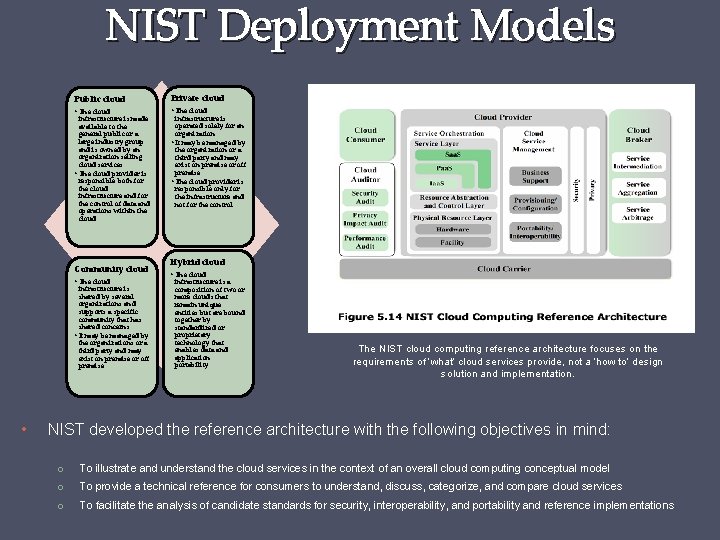
NIST Deployment Models Public cloud Private cloud • The cloud infrastructure is made available to the general public or a large industry group and is owned by an organization selling cloud services • The cloud provider is responsible both for the cloud infrastructure and for the control of data and operations within the cloud Community cloud • The cloud infrastructure is shared by several organizations and supports a specific community that has shared concerns • It may be managed by the organizations or a third party and may exist on premise or off premise • infrastructure is operated solely for an organization • It may be managed by the organization or a third party and may exist on premise or off premise • The cloud provider is responsible only for the infrastructure and not for the control Hybrid cloud • The cloud infrastructure is a composition of two or more clouds that remain unique entities but are bound together by standardized or proprietary technology that enables data and application portability The NIST cloud computing reference architecture focuses on the requirements of ‘what’ cloud services provide, not a ‘how to’ design solution and implementation. NIST developed the reference architecture with the following objectives in mind: o To illustrate and understand the cloud services in the context of an overall cloud computing conceptual model o To provide a technical reference for consumers to understand, discuss, categorize, and compare cloud services o To facilitate the analysis of candidate standards for security, interoperability, and portability and reference implementations
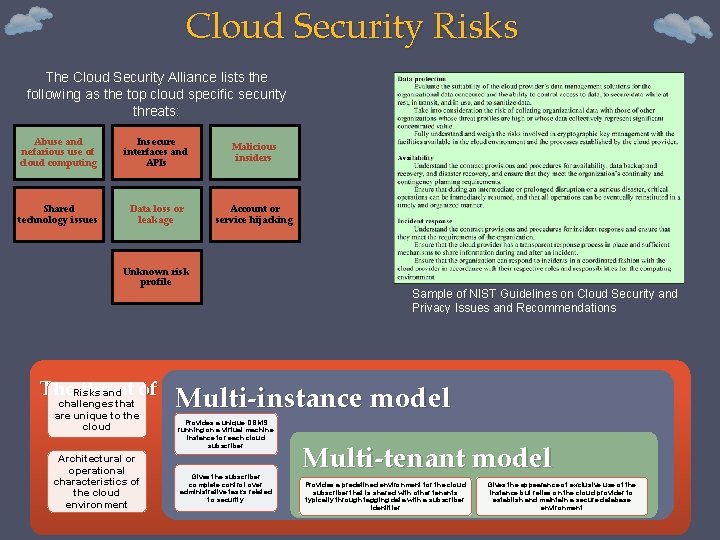
Cloud Security Risks The Cloud Security Alliance lists the following as the top cloud specific security threats: Abuse and nefarious use of cloud computing Insecure interfaces and APIs Malicious insiders Shared technology issues Data loss or leakage Account or service hijacking Unknown risk profile Sample of NIST Guidelines on Cloud Security and Privacy Issues and Recommendations The. Risks threat of data compromise increases in the cloud and challenges that are unique to the cloud Architectural or operational characteristics of the cloud environment Multi-instance model Provides a unique DBMS running on a virtual machine instance for each cloud subscriber Gives the subscriber complete control over administrative tasks related to security Multi-tenant model Provides a predefined environment for the cloud subscriber that is shared with other tenants typically through tagging data with a subscriber identifier Gives the appearance of exclusive use of the instance but relies on the cloud provider to establish and maintain a secure database environment
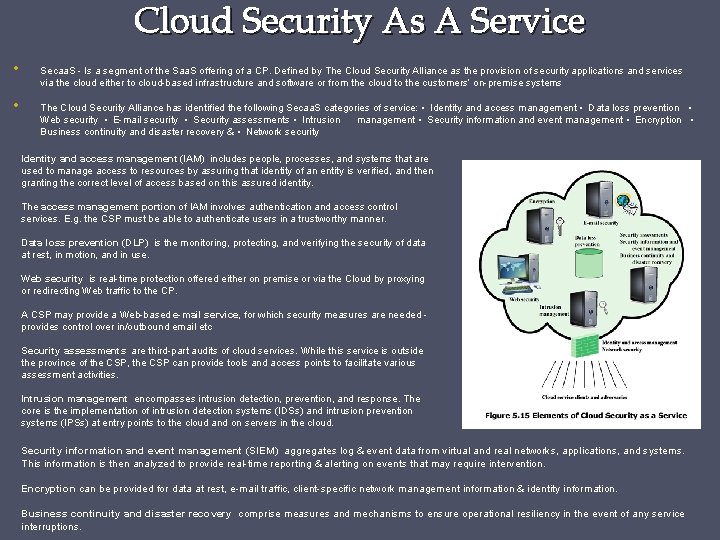
Cloud Security As A Service • • Secaa. S - Is a segment of the Saa. S offering of a CP. Defined by The Cloud Security Alliance as the provision of security applications and services via the cloud either to cloud-based infrastructure and software or from the cloud to the customers’ on-premise systems The Cloud Security Alliance has identified the following Secaa. S categories of service: • Identity and access management • Data loss prevention • Web security • E-mail security • Security assessments • Intrusion management • Security information and event management • Encryption • Business continuity and disaster recovery & • Network security Identity and access management (IAM) includes people, processes, and systems that are used to manage access to resources by assuring that identity of an entity is verified, and then granting the correct level of access based on this assured identity. The access management portion of IAM involves authentication and access control services. E. g. the CSP must be able to authenticate users in a trustworthy manner. Data loss prevention (DLP) is the monitoring, protecting, and verifying the security of data at rest, in motion, and in use. Web security is real-time protection offered either on premise or via the Cloud by proxying or redirecting Web traffic to the CP. A CSP may provide a Web-based e-mail service, for which security measures are needed provides control over in/outbound email etc Security assessments are third-part audits of cloud services. While this service is outside the province of the CSP, the CSP can provide tools and access points to facilitate various assessment activities. Intrusion management encompasses intrusion detection, prevention, and response. The core is the implementation of intrusion detection systems (IDSs) and intrusion prevention systems (IPSs) at entry points to the cloud and on servers in the cloud. Security information and event management (SIEM) aggregates log & event data from virtual and real networks, applications, and systems. This information is then analyzed to provide real-time reporting & alerting on events that may require intervention. Encryption can be provided for data at rest, e-mail traffic, client-specific network management information & identity information. Business continuity and disaster recovery comprise measures and mechanisms to ensure operational resiliency in the event of any service interruptions.
Chapter 6 Malicious Software
![Malware [SOUP 13] defines malware as: “a program that is inserted into a system, Malware [SOUP 13] defines malware as: “a program that is inserted into a system,](http://slidetodoc.com/presentation_image_h/24db5f537f37a2b19c8c1f4138f17c41/image-24.jpg)
Malware [SOUP 13] defines malware as: “a program that is inserted into a system, usually covertly, with the intent of compromising the confidentiality, integrity, or availability of the victim’s data, applications, or operating system or otherwise annoying or disrupting the victim. ” Hence, we are concerned with the threat malware poses to application programs, to utility programs, such as editors and compilers, and to kernel-level programs. We are also concerned with its use on compromised or malicious Web sites and servers, or in especially crafted spam e-mails or other messages, which aim to trick users into revealing sensitive personal information. Malware Terminology
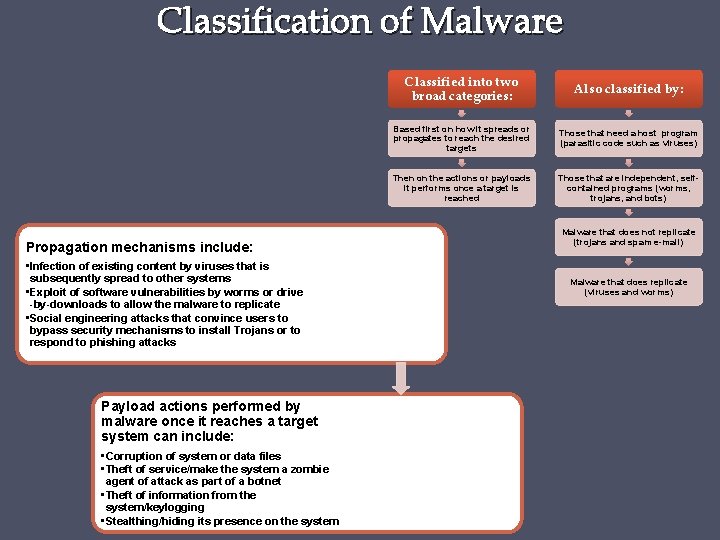
Classification of Malware Propagation mechanisms include: • Infection of existing content by viruses that is subsequently spread to other systems • Exploit of software vulnerabilities by worms or drive -by-downloads to allow the malware to replicate • Social engineering attacks that convince users to bypass security mechanisms to install Trojans or to respond to phishing attacks Payload actions performed by malware once it reaches a target system can include: • Corruption of system or data files • Theft of service/make the system a zombie agent of attack as part of a botnet • Theft of information from the system/keylogging • Stealthing/hiding its presence on the system Classified into two broad categories: Also classified by: Based first on how it spreads or propagates to reach the desired targets Those that need a host program (parasitic code such as viruses) Then on the actions or payloads it performs once a target is reached Those that are independent, selfcontained programs (worms, trojans, and bots) Malware that does not replicate (trojans and spam e-mail) Malware that does replicate (viruses and worms)
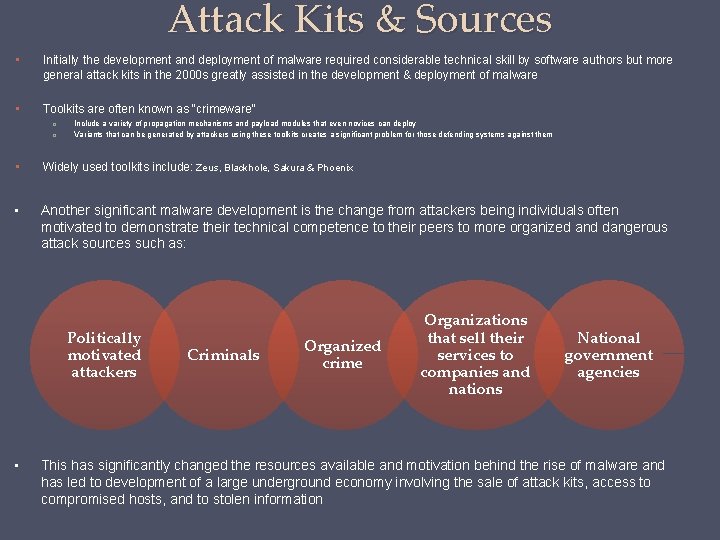
Attack Kits & Sources • Initially the development and deployment of malware required considerable technical skill by software authors but more general attack kits in the 2000 s greatly assisted in the development & deployment of malware • Toolkits are often known as “crimeware” o o Include a variety of propagation mechanisms and payload modules that even novices can deploy Variants that can be generated by attackers using these toolkits creates a significant problem for those defending systems against them • Widely used toolkits include: Zeus, Blackhole, Sakura & Phoenix • Another significant malware development is the change from attackers being individuals often motivated to demonstrate their technical competence to their peers to more organized and dangerous attack sources such as: Politically motivated attackers • Criminals Organized crime Organizations that sell their services to companies and nations National government agencies This has significantly changed the resources available and motivation behind the rise of malware and has led to development of a large underground economy involving the sale of attack kits, access to compromised hosts, and to stolen information
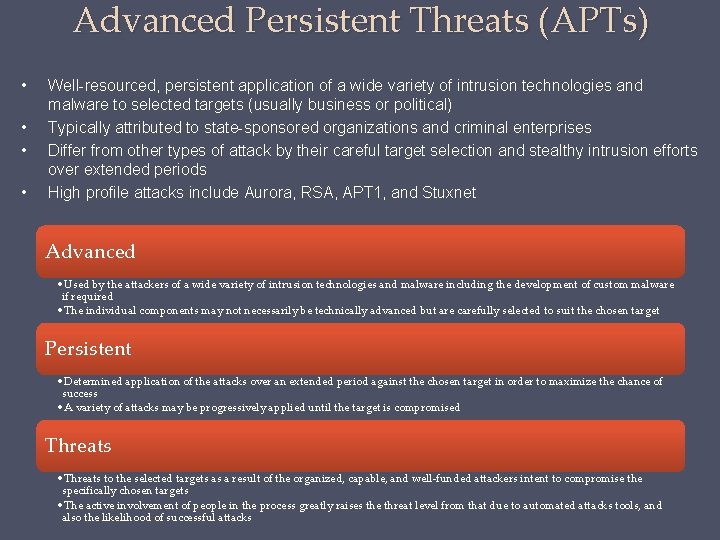
Advanced Persistent Threats (APTs) • • Well-resourced, persistent application of a wide variety of intrusion technologies and malware to selected targets (usually business or political) Typically attributed to state-sponsored organizations and criminal enterprises Differ from other types of attack by their careful target selection and stealthy intrusion efforts over extended periods High profile attacks include Aurora, RSA, APT 1, and Stuxnet Advanced • Used by the attackers of a wide variety of intrusion technologies and malware including the development of custom malware if required • The individual components may not necessarily be technically advanced but are carefully selected to suit the chosen target Persistent • Determined application of the attacks over an extended period against the chosen target in order to maximize the chance of success • A variety of attacks may be progressively applied until the target is compromised Threats • Threats to the selected targets as a result of the organized, capable, and well-funded attackers intent to compromise the specifically chosen targets • The active involvement of people in the process greatly raises the threat level from that due to automated attacks tools, and also the likelihood of successful attacks
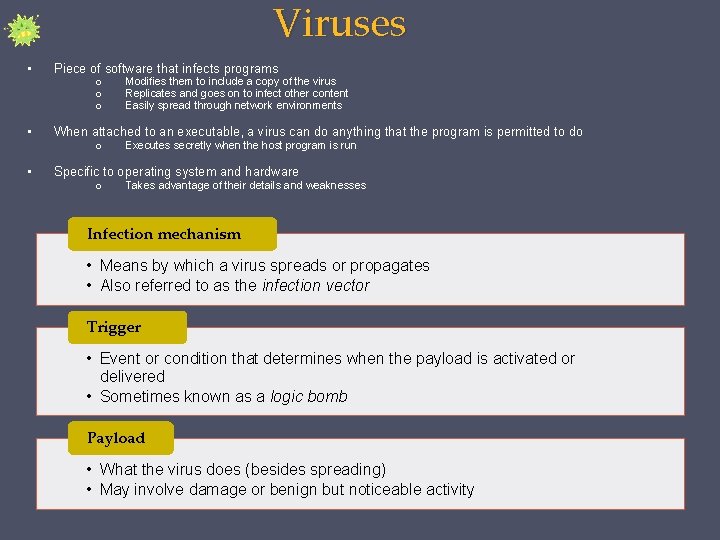
Viruses • Piece of software that infects programs • When attached to an executable, a virus can do anything that the program is permitted to do • Specific to operating system and hardware o o o Modifies them to include a copy of the virus Replicates and goes on to infect other content Easily spread through network environments Executes secretly when the host program is run Takes advantage of their details and weaknesses Infection mechanism • Means by which a virus spreads or propagates • Also referred to as the infection vector Trigger • Event or condition that determines when the payload is activated or delivered • Sometimes known as a logic bomb Payload • What the virus does (besides spreading) • May involve damage or benign but noticeable activity
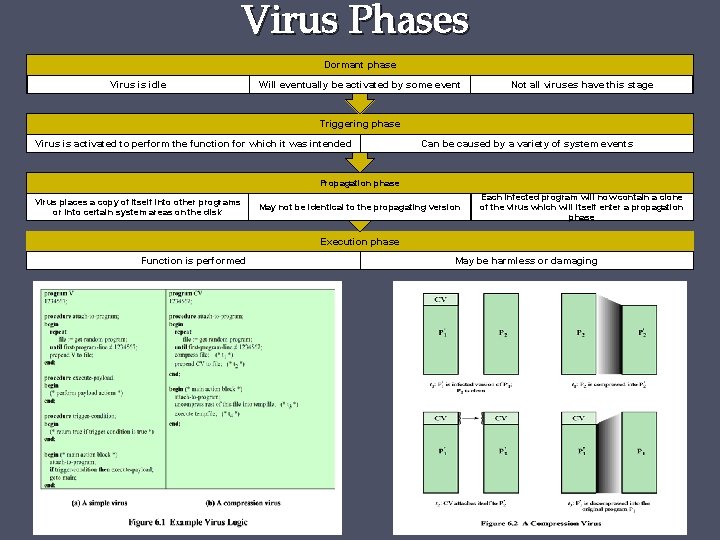
Virus Phases Dormant phase Virus is idle Will eventually be activated by some event Not all viruses have this stage Triggering phase Virus is activated to perform the function for which it was intended Can be caused by a variety of system events Propagation phase Virus places a copy of itself into other programs or into certain system areas on the disk May not be identical to the propagating version Each infected program will now contain a clone of the virus which will itself enter a propagation phase Execution phase Function is performed May be harmless or damaging
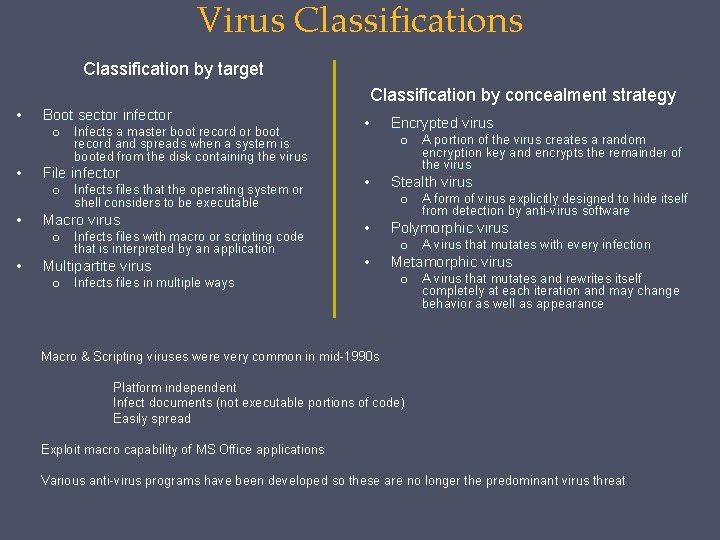
Virus Classification by target Classification by concealment strategy • Boot sector infector o • File infector o • Infects files that the operating system or shell considers to be executable Macro virus o • Infects a master boot record or boot record and spreads when a system is booted from the disk containing the virus Infects files with macro or scripting code that is interpreted by an application Multipartite virus o • Encrypted virus o • Stealth virus o • • Infects files in multiple ways A portion of the virus creates a random encryption key and encrypts the remainder of the virus A form of virus explicitly designed to hide itself from detection by anti-virus software Polymorphic virus o A virus that mutates with every infection o A virus that mutates and rewrites itself completely at each iteration and may change behavior as well as appearance Metamorphic virus Macro & Scripting viruses were very common in mid-1990 s Platform independent Infect documents (not executable portions of code) Easily spread Exploit macro capability of MS Office applications Various anti-virus programs have been developed so these are no longer the predominant virus threat
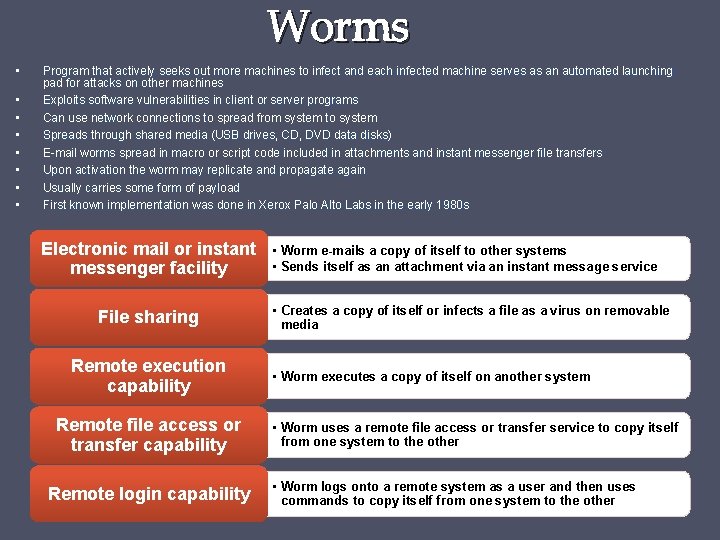
Worms • • Program that actively seeks out more machines to infect and each infected machine serves as an automated launching pad for attacks on other machines Exploits software vulnerabilities in client or server programs Can use network connections to spread from system to system Spreads through shared media (USB drives, CD, DVD data disks) E-mail worms spread in macro or script code included in attachments and instant messenger file transfers Upon activation the worm may replicate and propagate again Usually carries some form of payload First known implementation was done in Xerox Palo Alto Labs in the early 1980 s Electronic mail or instant messenger facility File sharing Remote execution capability Remote file access or transfer capability Remote login capability • Worm e-mails a copy of itself to other systems • Sends itself as an attachment via an instant message service • Creates a copy of itself or infects a file as a virus on removable media • Worm executes a copy of itself on another system • Worm uses a remote file access or transfer service to copy itself from one system to the other • Worm logs onto a remote system as a user and then uses commands to copy itself from one system to the other
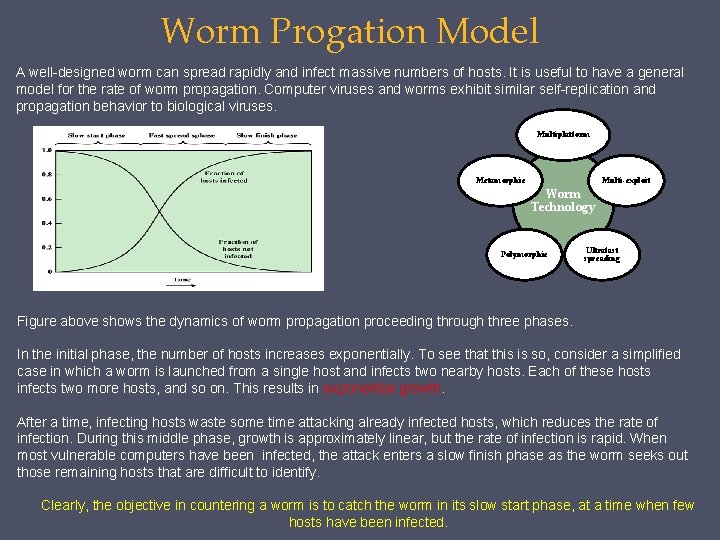
Worm Progation Model A well-designed worm can spread rapidly and infect massive numbers of hosts. It is useful to have a general model for the rate of worm propagation. Computer viruses and worms exhibit similar self-replication and propagation behavior to biological viruses. Multiplatform Metamorphic Multi-exploit Worm Technology Polymorphic Ultrafast spreading Figure above shows the dynamics of worm propagation proceeding through three phases. In the initial phase, the number of hosts increases exponentially. To see that this is so, consider a simplified case in which a worm is launched from a single host and infects two nearby hosts. Each of these hosts infects two more hosts, and so on. This results in exponential growth. After a time, infecting hosts waste some time attacking already infected hosts, which reduces the rate of infection. During this middle phase, growth is approximately linear, but the rate of infection is rapid. When most vulnerable computers have been infected, the attack enters a slow finish phase as the worm seeks out those remaining hosts that are difficult to identify. Clearly, the objective in countering a worm is to catch the worm in its slow start phase, at a time when few hosts have been infected.
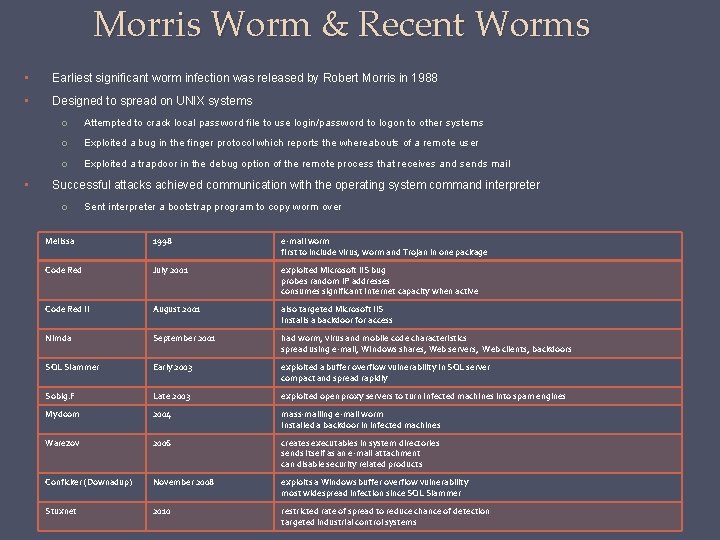
Morris Worm & Recent Worms • Earliest significant worm infection was released by Robert Morris in 1988 • Designed to spread on UNIX systems • o Attempted to crack local password file to use login/password to logon to other systems o Exploited a bug in the finger protocol which reports the whereabouts of a remote user o Exploited a trapdoor in the debug option of the remote process that receives and sends mail Successful attacks achieved communication with the operating system command interpreter o Sent interpreter a bootstrap program to copy worm over Melissa 1998 e-mail worm first to include virus, worm and Trojan in one package Code Red July 2001 exploited Microsoft IIS bug probes random IP addresses consumes significant Internet capacity when active Code Red II August 2001 also targeted Microsoft IIS installs a backdoor for access Nimda September 2001 had worm, virus and mobile code characteristics spread using e-mail, Windows shares, Web servers, Web clients, backdoors SQL Slammer Early 2003 exploited a buffer overflow vulnerability in SQL server compact and spread rapidly Sobig. F Late 2003 exploited open proxy servers to turn infected machines into spam engines Mydoom 2004 mass-mailing e-mail worm installed a backdoor in infected machines Warezov 2006 creates executables in system directories sends itself as an e-mail attachment can disable security related products Conficker (Downadup) November 2008 exploits a Windows buffer overflow vulnerability most widespread infection since SQL Slammer Stuxnet 2010 restricted rate of spread to reduce chance of detection targeted industrial control systems
Worm Countermeasures • • Considerable overlap in techniques for dealing with viruses and worms Once a worm is resident on a machine anti-virus software can be used to detect and possibly remove it Perimeter network activity and usage monitoring can form the basis of a worm defense Worm defense approaches include: o o o Signature-based worm scan filtering Filter-based worm containment Payload-classification-based worm containment Threshold random walk (TRW) scan detection Rate limiting Rate halting
Mobile Code • • • Programs that can be shipped unchanged to a variety of platforms Transmitted from a remote system to a local system and then executed on the local system Often acts as a mechanism for a virus, worm, or Trojan horse Takes advantage of vulnerabilities to perform its own exploits Popular vehicles include Java applets, Active. X, Java. Script and VBScript • • • First Mobile phone exploit was the Cabir worm in 2004, then Lasco and Comm. Warrior in 2005 Communicate through Bluetooth wireless connections or MMS where target was smartphone Can completely disable the phone, delete data on the phone, or force the device to send costly messages Comm. Warrior replicates by means of Bluetooth to other phones, sends itself as an MMS file to contacts and as an auto reply to incoming text messages • • Social Engineering still used to “Trick” users to assist in the compromise of their own systems Spam Unsolicited bulk e-mail Trojan horse Mobile phone trojans Program or utility containing harmful hidden code First appeared in 2004 (Skuller) Used to accomplish functions that the attacker could not accomplish directly Target is the smartphone Significant carrier of malware Used for phishing attacks
Drive by Downloads & Clickjacking • • • Drive by downloads exploit browser vulnerabilities to download and installs malware on the system when the user views a Web page controlled by the attacker In most cases does not actively propagate Spreads when users visit the malicious Web page • • Clickjacking is also known as a user-interface (UI) redress attack Using a similar technique, keystrokes can also be hijacked o • A user can be led to believe they are typing in the password to their email or bank account, but are instead typing into an invisible frame controlled by the attacker Vulnerability used by an attacker to collect an infected user’s clicks o The attacker can force the user to do a variety of things from adjusting the user’s computer setters to unwittingly sending the user to Web sites that might have malicious code o By taking advantage of Adobe Flash or Java. Script an attacker could even place a button under or over a legitimate button making it difficult for users to detect o A typical attack uses multiple transparent or opaque layers to trick a user into clicking on a button or link on another page when they were intending to click on the top level page o The attacker is hijacking clicks meant for one page and routing them to another page
Payload System Corruption • Real-world damage • Causes damage to physical equipment o Chernobyl virus rewrites BIOS code • Stuxnet worm o Targets specific industrial control system software • There are concerns about using sophisticated targeted malware for industrial sabotage • Logic bomb • Code embedded in the malware that is set to “explode” when certain conditions are met • A bot takes over another Internet attached computer and uses that computer to launch or manage attacks • • Botnet - collection of bots capable of acting in a coordinated manner • Remote Control Facility distinguishes a bot from a worm • Worm propagates itself and activates itself • Bot is initially controlled from some central facility • Typical means of implementing the remote control facility is on an IRC server Uses: Distributed denial-of-service (DDo. S) attacks, Spamming, Sniffing traffic, Keylogging, Spreading new malware, Installing advertisement add-ons and browser helper objects (BHOs), Attacking IRC chat networks, Manipulating online polls/games • Bots join a specific channel on this server and treat incoming messages as commands • More recent botnets use covert communication channels via protocols such as HTTP • Distributed control mechanisms use peer-to-peer protocols to avoid a single point of failure
Payload – Information Theft, Keyloggers and Spyware Keylogger • Captures keystrokes to allow attacker to monitor sensitive information • Typically uses some form of filtering mechanism that only returns information close to keywords (“login”, “password”) Spyware • Subverts the compromised machine to allow monitoring of a wide range of activity on the system • Monitoring history and content of browsing activity • Redirecting certain Web page requests to fake sites • Dynamically modifying data exchanged between the browser and certain Web sites of interest • Exploits social engineering to leverage the user’s trust by masquerading as communication from a trusted source • Include a URL in a spam e-mail that links to a fake Web site that mimics the login page of a banking, gaming, or similar site • Suggests that urgent action is required by the user to authenticate their account • Attacker exploits the account using the captured credentials • Spear-phishing • Recipients are carefully researched by the attacker. E-mail is crafted to specifically suit its recipient, often quoting a range of information to convince them of its authenticity
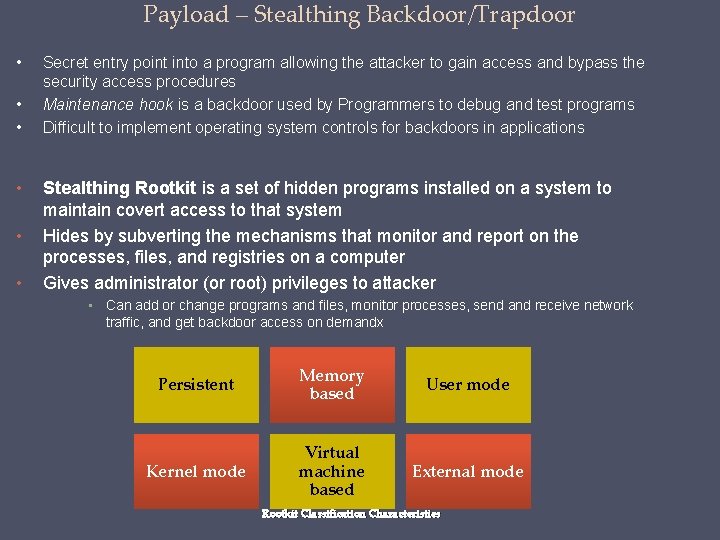
Payload – Stealthing Backdoor/Trapdoor • • • Secret entry point into a program allowing the attacker to gain access and bypass the security access procedures Maintenance hook is a backdoor used by Programmers to debug and test programs Difficult to implement operating system controls for backdoors in applications Stealthing Rootkit is a set of hidden programs installed on a system to maintain covert access to that system Hides by subverting the mechanisms that monitor and report on the processes, files, and registries on a computer Gives administrator (or root) privileges to attacker • Can add or change programs and files, monitor processes, send and receive network traffic, and get backdoor access on demandx Persistent Memory based User mode Kernel mode Virtual machine based External mode Rootkit Classification Characteristics
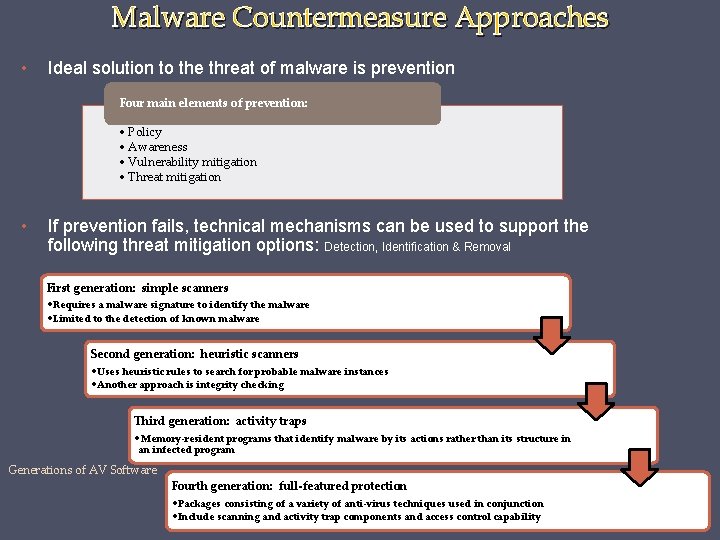
Malware Countermeasure Approaches • Ideal solution to the threat of malware is prevention Four main elements of prevention: • Policy • Awareness • Vulnerability mitigation • Threat mitigation • If prevention fails, technical mechanisms can be used to support the following threat mitigation options: Detection, Identification & Removal First generation: simple scanners • Requires a malware signature to identify the malware • Limited to the detection of known malware Second generation: heuristic scanners • Uses heuristic rules to search for probable malware instances • Another approach is integrity checking Third generation: activity traps • Memory-resident programs that identify malware by its actions rather than its structure in an infected program Generations of AV Software Fourth generation: full-featured protection • Packages consisting of a variety of anti-virus techniques used in conjunction • Include scanning and activity trap components and access control capability
Generic Decryption (GD) • Enables AV program to detect complex polymorphic viruses & malware while maintaining fast scanning speeds • Executable files are run through a GD scanner which contains the following elements: • CPU emulator: A software-based virtual computer. Instructions in an executable file are interpreted by the emulator rather than executed on the underlying processor. The emulator includes software versions of all registers and other processor hardware, so that the underlying processor is unaffected by programs interpreted on the emulator. • Virus signature scanner: A module that scans the target code looking for known malware signatures. • Emulation control module: Controls the execution of the target code. • At the start of each simulation, emulator begins interpreting instructions in the target code, one at a time. Thus, if the code includes a decryption routine that decrypts and hence exposes the malware, that code is interpreted. • In effect, the malware does the work for the anti-virus program by exposing itself. Periodically, the control module interrupts interpretation to scan the target code for malware signatures. • During interpretation, the target code can cause no damage to the actual personal computer environment, because it is being interpreted in a completely controlled environment. • The most difficult design issue with a GD scanner is to determine how long to run each interpretation
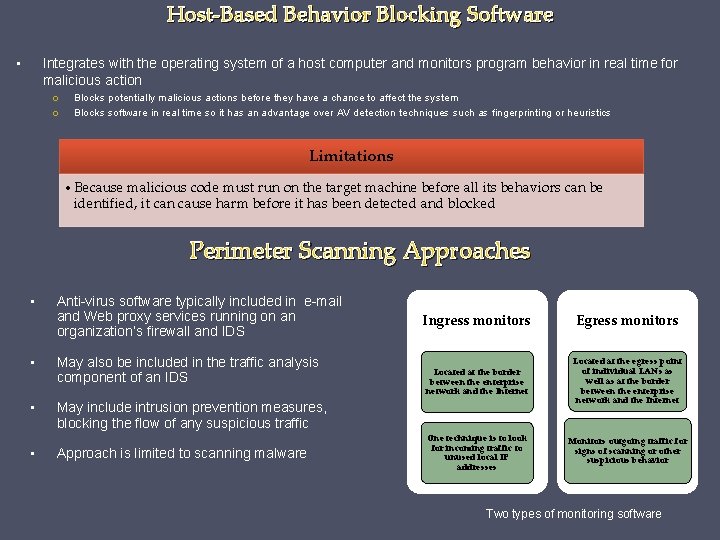
Host-Based Behavior Blocking Software • Integrates with the operating system of a host computer and monitors program behavior in real time for malicious action o o Blocks potentially malicious actions before they have a chance to affect the system Blocks software in real time so it has an advantage over AV detection techniques such as fingerprinting or heuristics Limitations • Because malicious code must run on the target machine before all its behaviors can be identified, it can cause harm before it has been detected and blocked Perimeter Scanning Approaches • Anti-virus software typically included in e-mail and Web proxy services running on an organization’s firewall and IDS • May also be included in the traffic analysis component of an IDS • May include intrusion prevention measures, blocking the flow of any suspicious traffic • Approach is limited to scanning malware Ingress monitors Egress monitors Located at the border between the enterprise network and the Internet Located at the egress point of individual LANs as well as at the border between the enterprise network and the Internet One technique is to look for incoming traffic to unused local IP addresses Monitors outgoing traffic for signs of scanning or other suspicious behavior Two types of monitoring software
Finally, Lab today 2. Information Gathering Techniques 2. 1 Open Web Information Gathering 2. 1. 1 Google Hacking 2. 2 Netcraft & Goohost 2. 2. 1 Netcraft 2. 2. 2 Goohost 2. 2. 3 Whois Reconnaissance 2. 3 OWASP Joomla! Vulnerability Scanner 2. 3. 1 Joomla! Command Line Scan 2. 3. 3 WPScan-Wordpress Security Scanner 2. 3. 4 Plecost 2. 3. 5 What. Web 2. 3. 6 Blind. Elephant-Web Application Fingerprinter 2. 3. 7 Intrusion Detection Systems Detection 2. 4 Snort for sniffing and logging packets 2. 4. 1 Snort Overview 2. 4. 2 Run Snort in Sniffer Mode 2. 4. 3 Run Snort in Packet Logger Mode 2. 4. 4 Running snort in network intrusion detection system mode 2. 4. 5 Setting Alert Rules 2. 5 Homework: How to Change Your MAC Address 2. 5. 1 How to change your MAC address on Windows 2. 5. 2 How to change your MAC address on Linux 2. 6 Documentation of Penetration Tests
- Slides: 44