Chapter 6 Database Security Integrity for databases record
Chapter 6 – Database Security Integrity for databases: record integrity, data correctness, update integrity u Security for databases: access control, inference, and aggregation u Multilevel secure databases: partitioned, cryptographically sealed, filtered u
Introduction to Databases Database – collection of data and set of rules that organize the data by specifying certain relationships among the data u Database administrator (DBA) u Database management system (DBMS) – database manager, frontend u
Introduction to Databases Records – contain related group of data u Fields (elements) – elementary data items u Schema – logical structure of database u Subschema – view into database u
Introduction to Databases u Relational • Rows (relation); columns (attributes) • DB 2, Oracle, Access u Hierarchical • IMS u Object-oriented
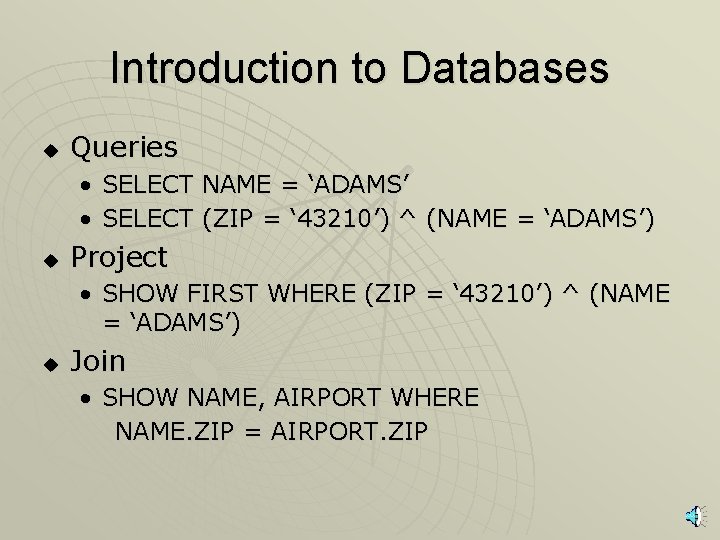
Introduction to Databases u Queries • SELECT NAME = ‘ADAMS’ • SELECT (ZIP = ‘ 43210’) ^ (NAME = ‘ADAMS’) u Project • SHOW FIRST WHERE (ZIP = ‘ 43210’) ^ (NAME = ‘ADAMS’) u Join • SHOW NAME, AIRPORT WHERE NAME. ZIP = AIRPORT. ZIP
Advantages of Using Databases Shared access u Minimal redundancy u Data consistency u Data integrity u Controlled access u
Security Requirements Physical database integrity u Logical database integrity u Element integrity u Auditability u Access control u User authentication u Availability u
Integrity of the Database Users must be able to trust the accuracy of the data values u Updates are performed by authorized individuals u Integrity is the responsibility of the DBMS, the OS, and the computing system manager u Must be able to reconstruct the database at the point of a failure u
Element Integrity Correctness or accuracy of elements u Field checks u Access control u Maintain a change log – list every change made to the database u
Auditability & Access Control Desirable to generate an audit record of all access to the database (reads/writes) u Pass-through problem – accessing a record or element without transferring the data received to the user (no reads/writes) u Databases separated logically by user access privileges u
Other Security Requirements User Authentication u Integrity u Confidentiality u Availability u
Reliability and Integrity Database integrity u Element accuracy u u Some protection from OS • File access • Data integrity checks
Two-Phase Update Failure of computing system in middle of modifying data u Intent Phase – gather resources needed for update; write commit flag to the database u Update Phase – make permanent changes u
Redundancy / Internal Consistency u Error detection / Correction codes (parity bits, Hamming codes, CRCs) u Shadow fields u Log of user accesses and changes
Concurrency/Consistency u u u Access by two users sharing the same database must be constrained (lock) Monitors –check entered values to ensure consistency with rest of DB Range Comparisons State Constraints – describes condition of database (unique employee #) Transition Constraints – conditions before changes are applied to DB
- Slides: 15