Resourcebased Attacks Attacking Networks ResourceBased Attacks Resourcebased attacks
Resource-based Attacks
Attacking Networks Resource-Based Attacks • Resource-based attacks are designed to gain access to additional resources for the attacker. • Basically, taking over machines in order to set up illicit servers on them.
Attacking Networks Resource-Based Attacks • Some resource-based attack examples -
Attacking Networks Resource-Based Attacks • Data storage (ftp) servers to store files (e. g. illicit copies of software and media). – Warez.
Attacking Networks Resource-Based Attacks • Message (IRC) servers to host chat sessions.
Attacking Networks Resource-Based Attacks • Mail servers to send spam.
Attacking Networks Resource-Based Attacks • Computers from which to launch subsequent attacks (zombies, bots).
Attacking Networks Resource-Based Attacks • Resource-based attacks typically are intrusion attacks. • That is, the attacker gains control of the computer in order to set up their desired illicit server(s).
Data-based Attacks
Attacking Networks Data-Based Attacks • Data-based attacks are designed to steal or modify data. • Basically, high-tech theft and fraud. • These are also intrusion-based attacks, so the attacker can gain access to the data to steal or alter it.
Attacking Networks Data-Based Attacks • Recent thefts of credit card data from a credit card purchase processing firm are high profile data-based attacks. • The attackers stole large number of credit card numbers, and possibly other data that can be used for fraudulent purchases or possibly identity theft.
Reconnaissance
Attacking Networks Reconnaissance • Before mounting an exploit, an attacker needs reconnaissance - they need to know what attacks will work on their intended targets. – Or, viewed alternately, which servers are vulnerable to their chosen attack(s).
Attacking Networks Port Scanning • Port scanning is part of that reconnaissance. • The purpose of port scanning is to see which, if any, services a computer is offering.
Attacking Networks Port Scanning • In port scanning, 1. the attacker runs a program that attempts to open a connection on each of the ports of a potential victim machine. 2. The program sees which ports respond.
Attacking Networks Port Scanning • Those ports that respond represent services that the computer is offering over the network.
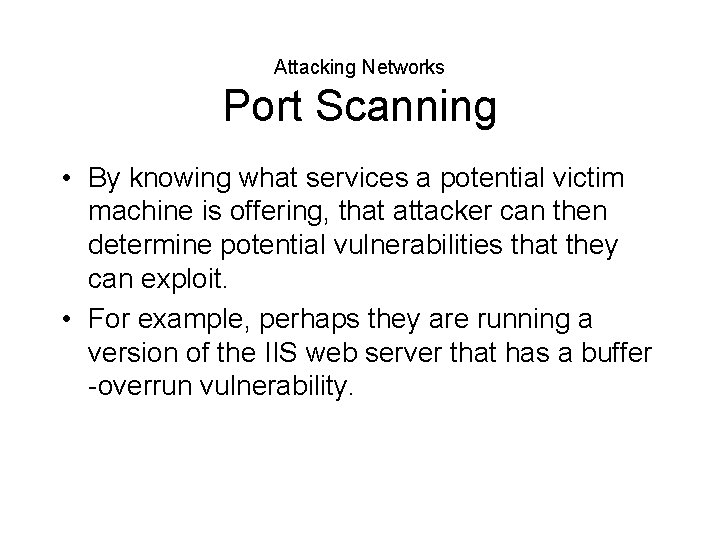
Attacking Networks Port Scanning • By knowing what services a potential victim machine is offering, that attacker can then determine potential vulnerabilities that they can exploit. • For example, perhaps they are running a version of the IIS web server that has a buffer -overrun vulnerability.
Sniffing
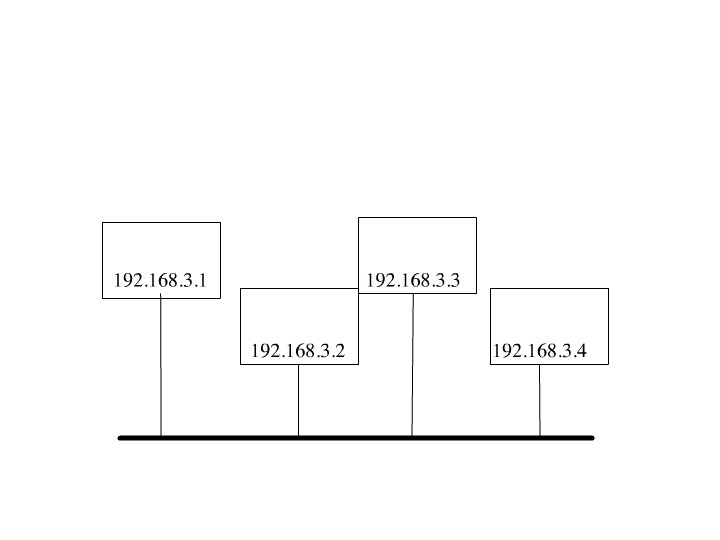
Attacking Networks Sniffing • One major security vulnerability is the digital network equivalent of eavesdropping or wiretapping - sniffing. • On many common types of networks, all of the computers on the local network see all of the packets on that network. • Ethernet, the most common type of non-wireless network, can have this property.
Attacking Networks Sniffing • A computer on the local network can engage in sniffing. • Sniffing is capturing a copy of the packets that are on the local network. • The packets can then be analyzed for useful data, – User IDs and passwords, – Technical information that might be useful for an attack – Other valuable information, e. g. credit card numbers, keys for access to software.
Module Eight Worms
Worms • As discussed previously, worms are malicious software that is used to attack computers. • Although a worm can be spread in other manners, they are most at home on computer networks.
Worms Sniffing • Many modern worms install sniffers once they have taken over a victim computer.
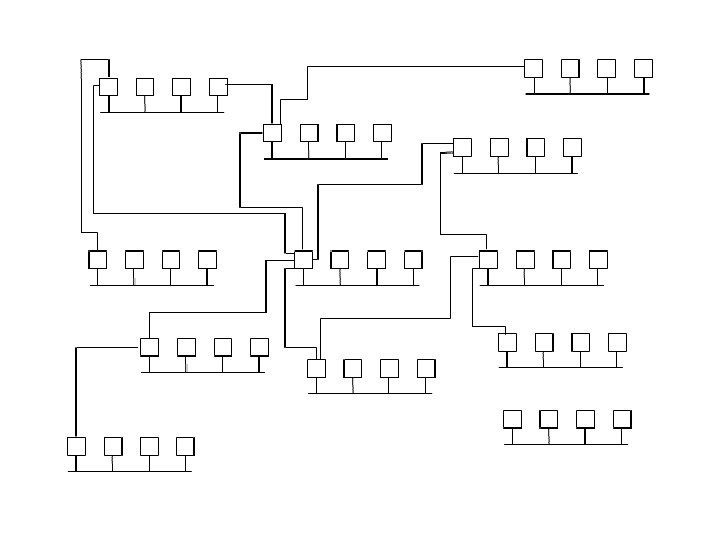
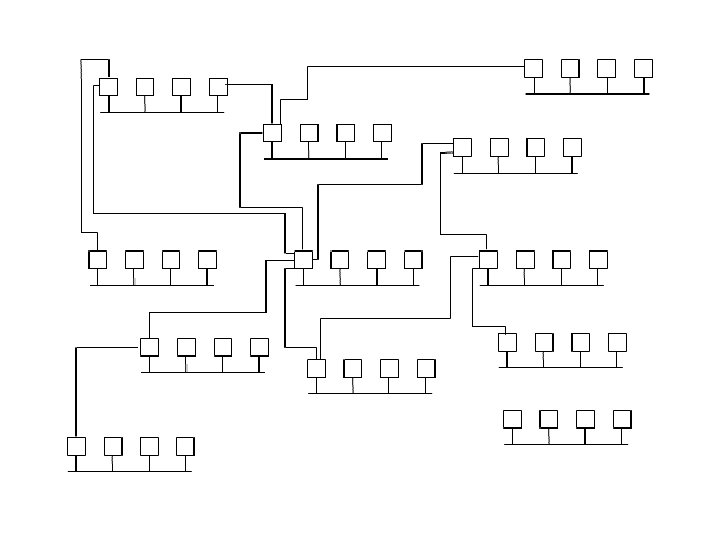
Worms Infecting New Machines • They can find other machines to infect, either – By targeting IP addresses at random, or – Attacking specific machines or networks. • The speed of modern computers and networks allow worms to target very large numbers of potential victims.
The Slammer Worm
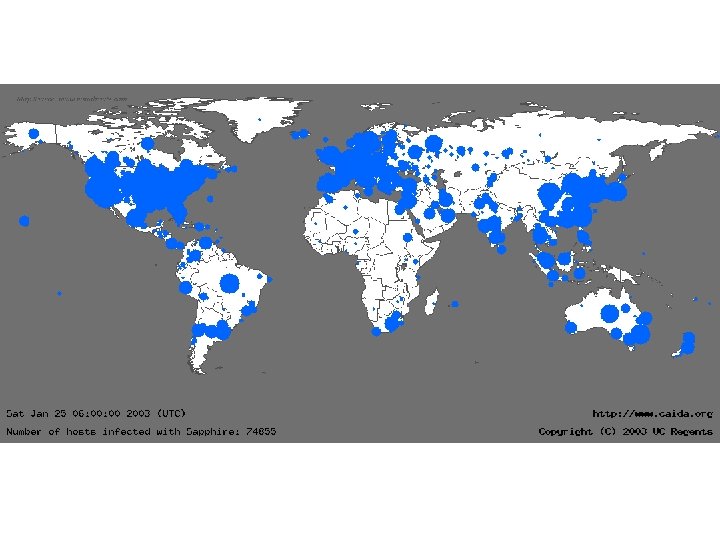
Worms Slammer Worm • The Slammer worm was first seen in January 2003. – It attacked computers running a Microsoft database server. – It exploited a buffer overflow in the database software to propagate.
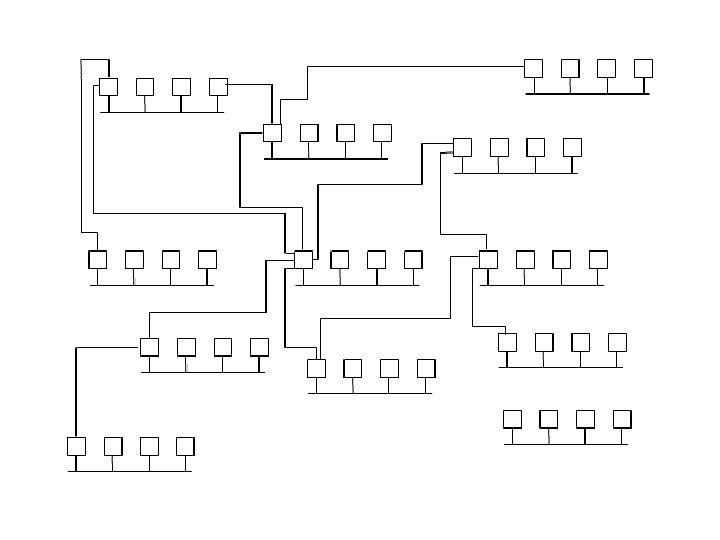
Worms Slammer Worm • Infected machines randomly scanned the Internet, looking for servers that responded to UDP port 1434. – When it found one, it sent the bufferoverflowing message.
Worms Slammer Worm • Not only did the random scanning help the worm spread rapidly, all of the scanning traffic had the side-effect of causing denial of service attacks.
Worms Slammer Worm • The vulnerability the Slammer Worm exploited was not new at the time. – The vulnerability had been publicly known, and a patch available since the previous summer (2002). • Systems that were infected by the worm had not been patched. – Roughly speaking, patching is modifying the software to close the vulnerability.
Worms Slammer Worm • The worm did not have a malicious payload. • But, it still had substantial effects – The worm infected computers at Ohio's Davis. Besse nuclear plant, disrupting plant safety systems. • Operators believed that a firewall would keep them safe. – Airline flights were cancelled. – ATM service was disrupted.
Worms Slammer Worm • The Slammer worm spread through the entire Internet in 10 minutes, infecting ~90% of all vulnerable servers.
- Slides: 38