CS 419579 Cyber Attacks Defense NSA Codebreaker Task
CS 419/579 Cyber Attacks & Defense NSA Codebreaker Task 4 and 5 12/3/19
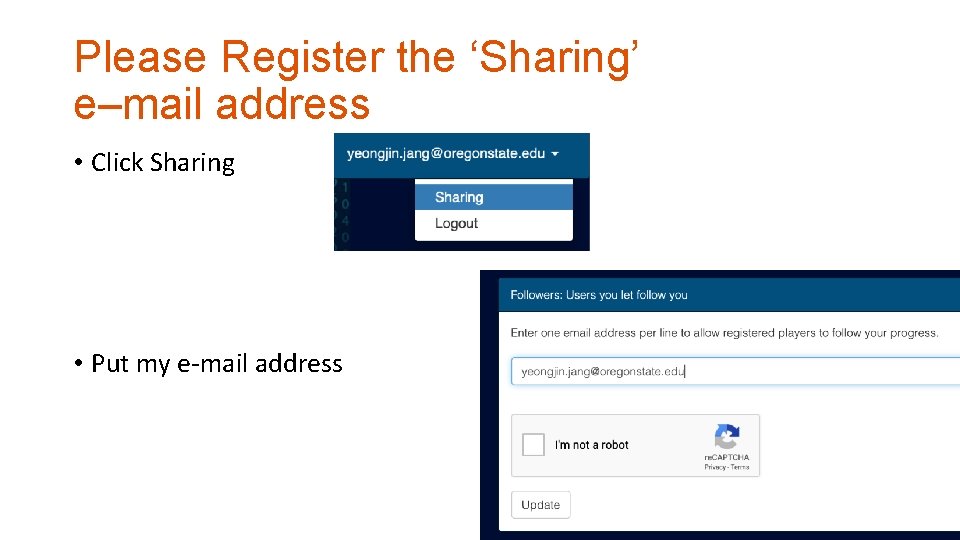
Please Register the ‘Sharing’ e–mail address • Click Sharing • Put my e-mail address
Contents • Task 1— 3 • Database file: client. DB. db • Android Studio • Android Virtual Device • Java / Javac • Jadx
Database File • Please obtain client. DB. db from Task 3 • You can open the database file using • https: //sqlitebrowser. org/
Installing Android Studio • https: //developer. android. com/studio • Download and install!
Installing Android Virtual Device (AVD) • Run Android Studio • Create a new application (We will not use it at all though) • Why an AVD? The app is built for x 86, not ARM, so it will never run on your phone. .
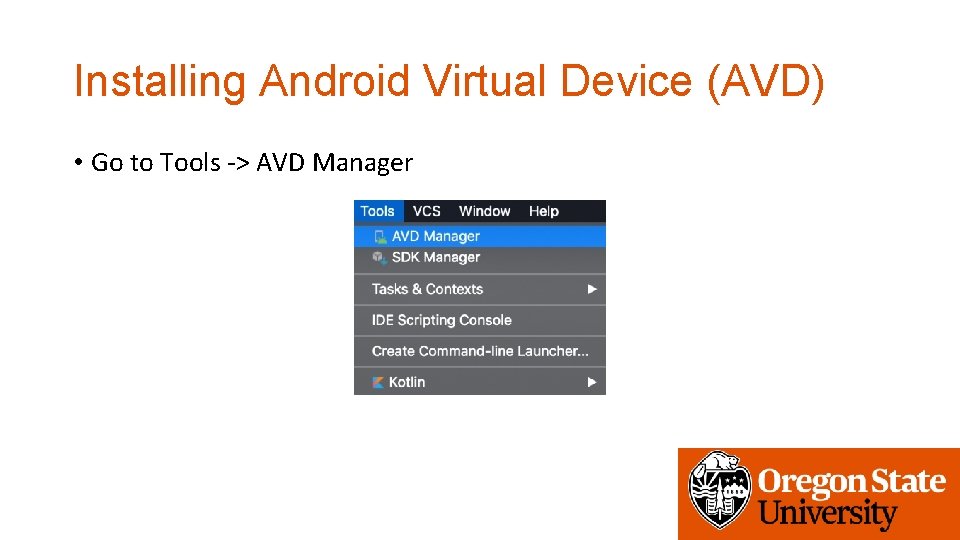
Installing Android Virtual Device (AVD) • Go to Tools -> AVD Manager
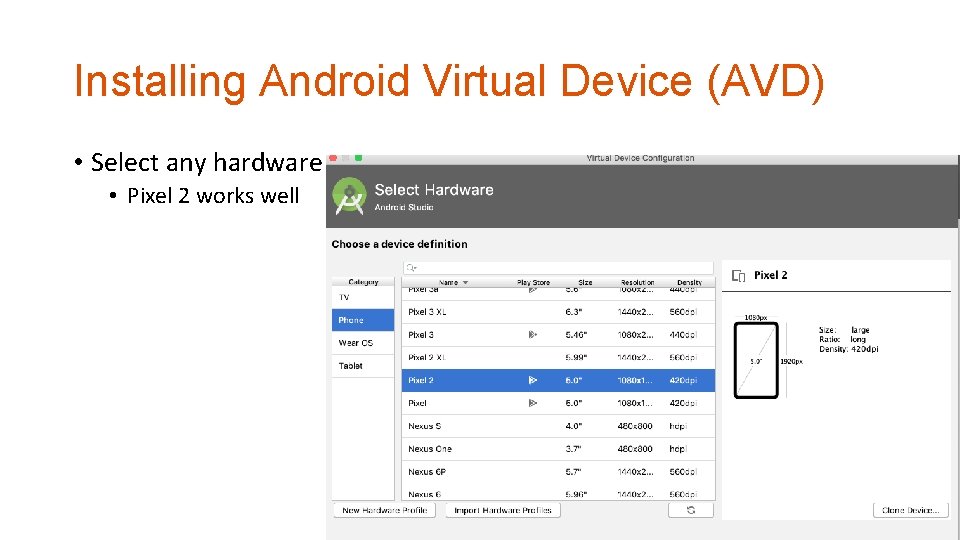
Installing Android Virtual Device (AVD) • Select any hardware • Pixel 2 works well
Installing Android Virtual Device (AVD) • Install Android Q SDK by clicking ‘Download’
Installing Android Virtual Device (AVD) • Accept the term and • Install SDK…

Create an AVD • Clicking Finish will finalize the AVD creation
Launch an AVD • Clicking the ‘Play’ button will do that. .
Running AVD • Now you have an AVD

Installing Terror. Time • Download Version 2 from the Codebreaker Website

Locate platform-tools/adb • On Mac: ~/Library/Android/sdk/platform-tools • On Linux: ~/Android/Sdk/platform-tools • Or run find ~ | grep platform-tools • On Windows: • C: Users[your user]App. DataLocalAndroidsdkplatform-tools
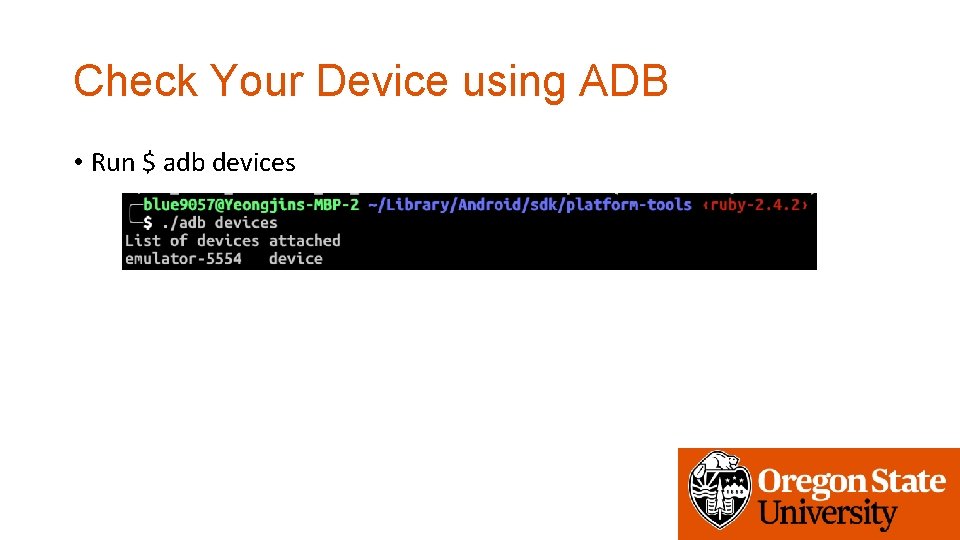
Check Your Device using ADB • Run $ adb devices

Install the app using adb • $ adb install ~/Download/terror. Time. apk • You may uninstall the app by running • $ adb uninstall com. badguy. terrortime
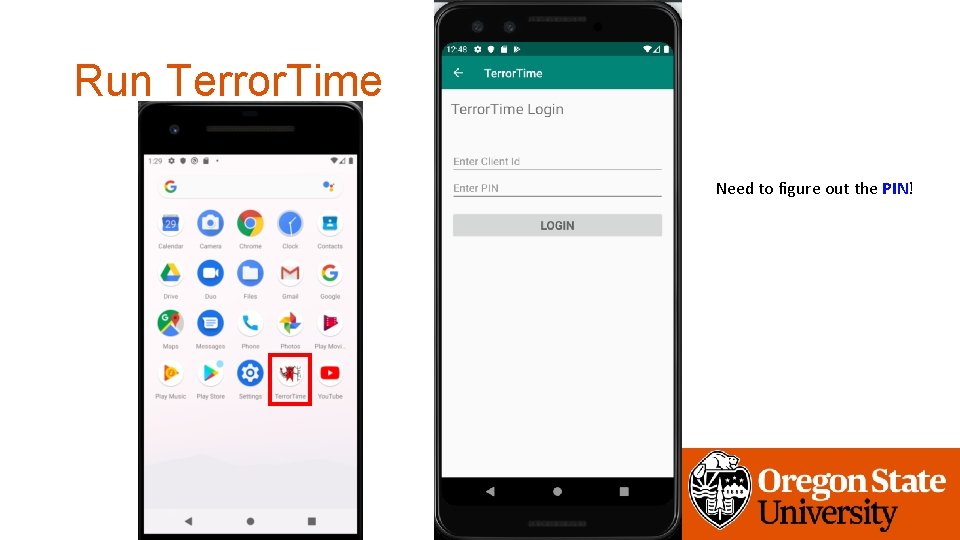
Run Terror. Time Need to figure out the PIN!

Inject client. DB. db to the app • Download client. DB. db
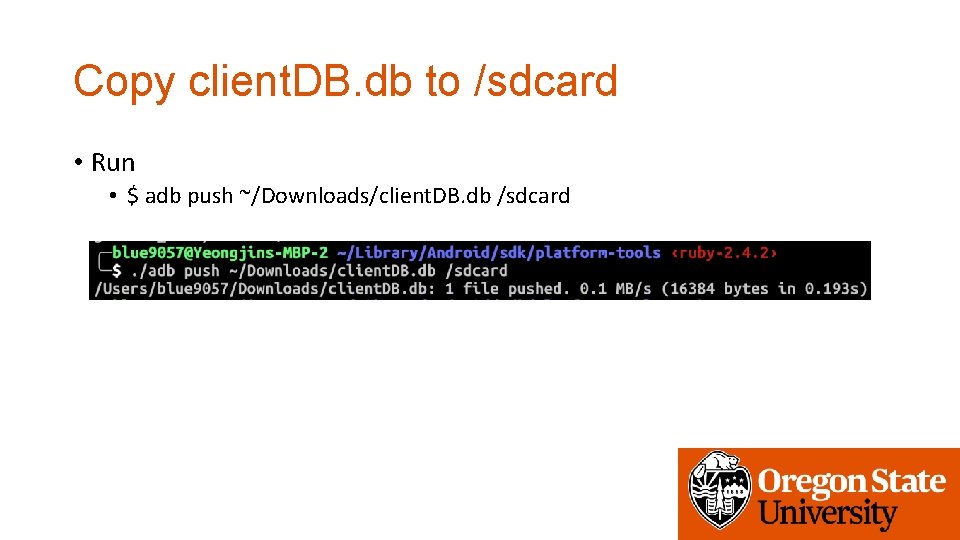
Copy client. DB. db to /sdcard • Run • $ adb push ~/Downloads/client. DB. db /sdcard
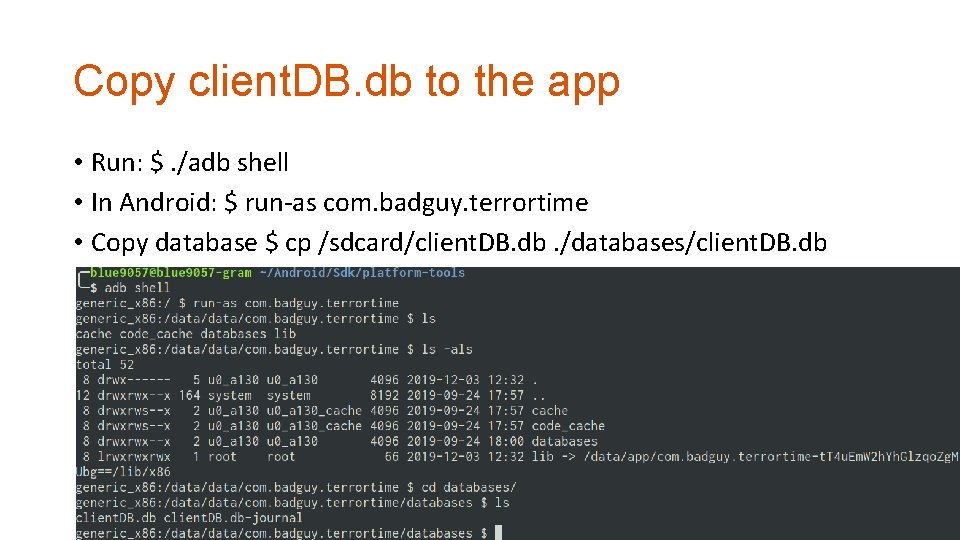
Copy client. DB. db to the app • Run: $. /adb shell • In Android: $ run-as com. badguy. terrortime • Copy database $ cp /sdcard/client. DB. db. /databases/client. DB. db
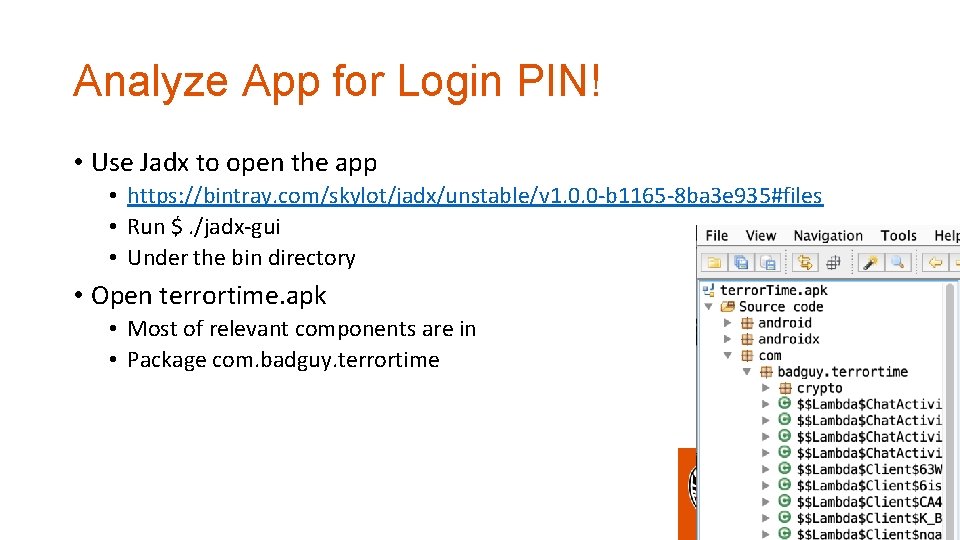
Analyze App for Login PIN! • Use Jadx to open the app • https: //bintray. com/skylot/jadx/unstable/v 1. 0. 0 -b 1165 -8 ba 3 e 935#files • Run $. /jadx-gui • Under the bin directory • Open terrortime. apk • Most of relevant components are in • Package com. badguy. terrortime

Reverse Enginnering 101 • Interpret the meaning of Symbols • Now you want to login to the service • There is a symbol Login. Activity!!! • And then you want to know what is the PIN for login • • • Login. Activity internally uses ‘Client’ Client has lots of methods, but get. Check. Pin() get. Encrypted. Pin() PIN seems relevant!
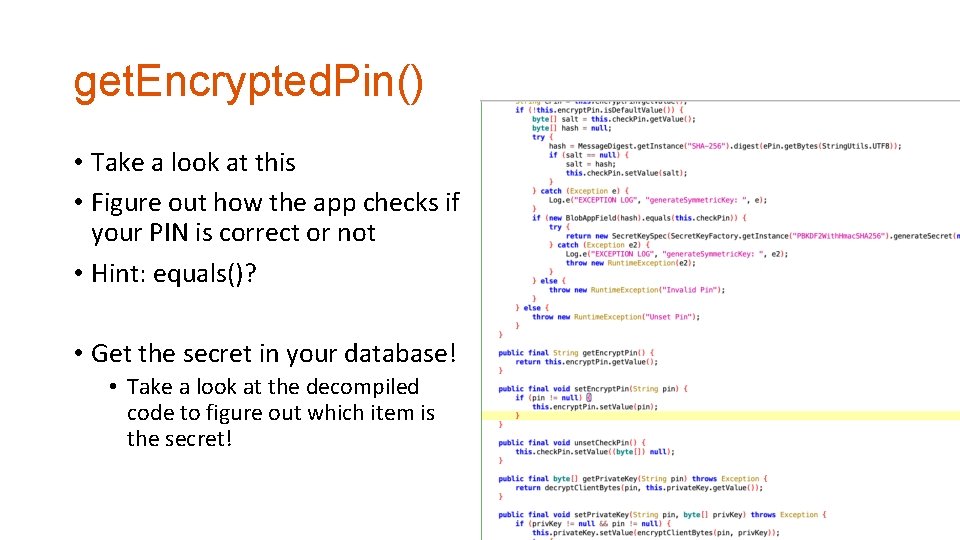
get. Encrypted. Pin() • Take a look at this • Figure out how the app checks if your PIN is correct or not • Hint: equals()? • Get the secret in your database! • Take a look at the decompiled code to figure out which item is the secret!

SHA 256 • A cryptographic hash algorithm • Secure Hash Algorithm (SHA) 256 -bit • https: //en. wikipedia. org/wiki/SHA-2 • One-way function • Easy to get a digest (result of the hash) • Very difficult to get the input for generating a specific digest • Example • SHA-256(‘A’) == ca 978112 ca 1 bbdcafac 231 b 39 a 23 dc 4 da 786 eff 8147 c 4 e 72 b 9807785 afee 48 bb
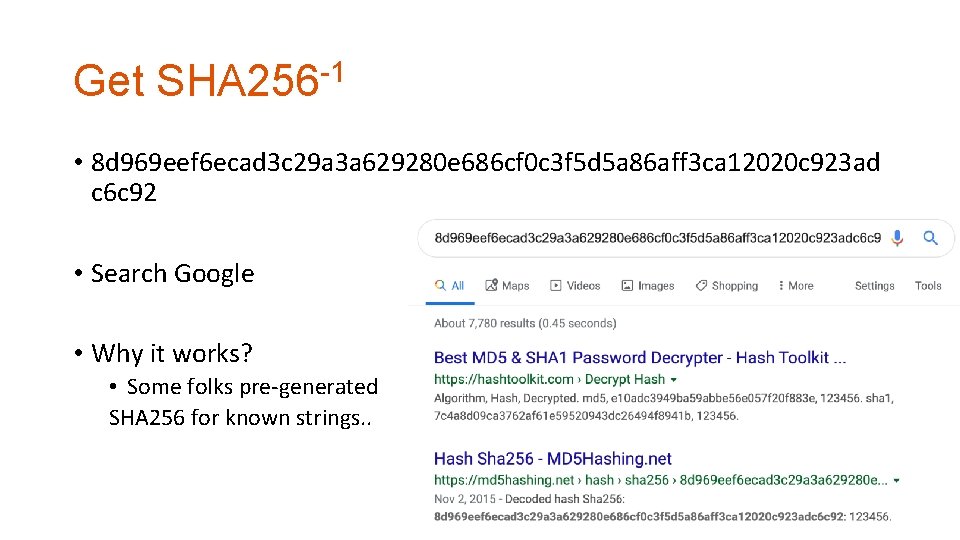
Get SHA 256 -1 • 8 d 969 eef 6 ecad 3 c 29 a 3 a 629280 e 686 cf 0 c 3 f 5 d 5 a 86 aff 3 ca 12020 c 923 ad c 6 c 92 • Search Google • Why it works? • Some folks pre-generated SHA 256 for known strings. .

After getting PIN • Login and read messages!
Task 5 • Finding a vulnerability in a Python Compiled file… • PYC, no source code, but don’t worry, we have • UNCOMPYLE!!!
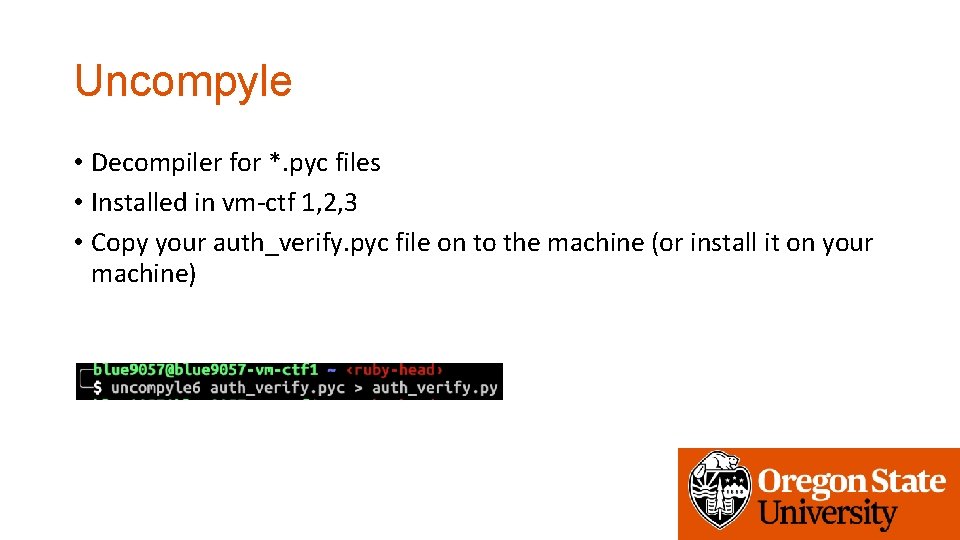
Uncompyle • Decompiler for *. pyc files • Installed in vm-ctf 1, 2, 3 • Copy your auth_verify. pyc file on to the machine (or install it on your machine)
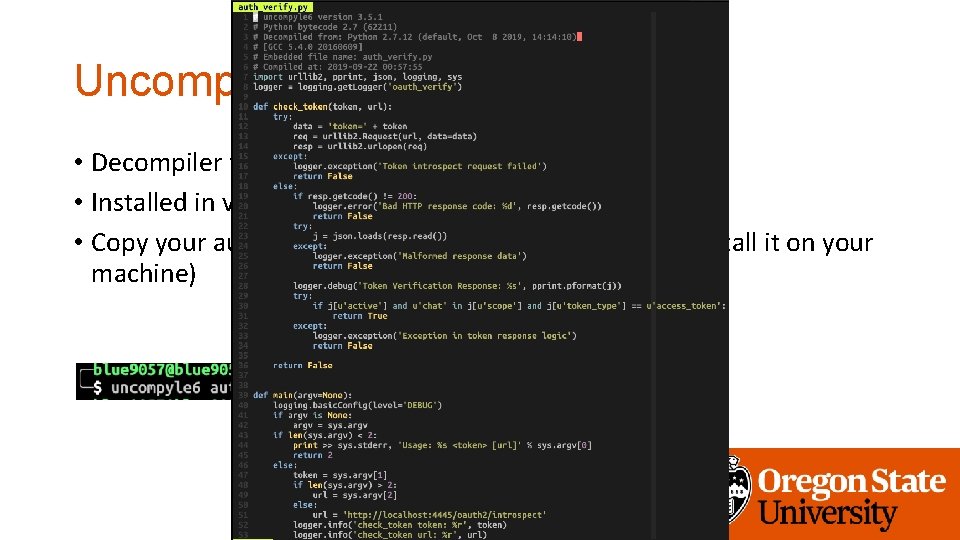
Uncompyle • Decompiler for *. pyc files • Installed in vm-ctf 1, 2, 3 • Copy your auth_verify. pyc file on to the machine (or install it on your machine)
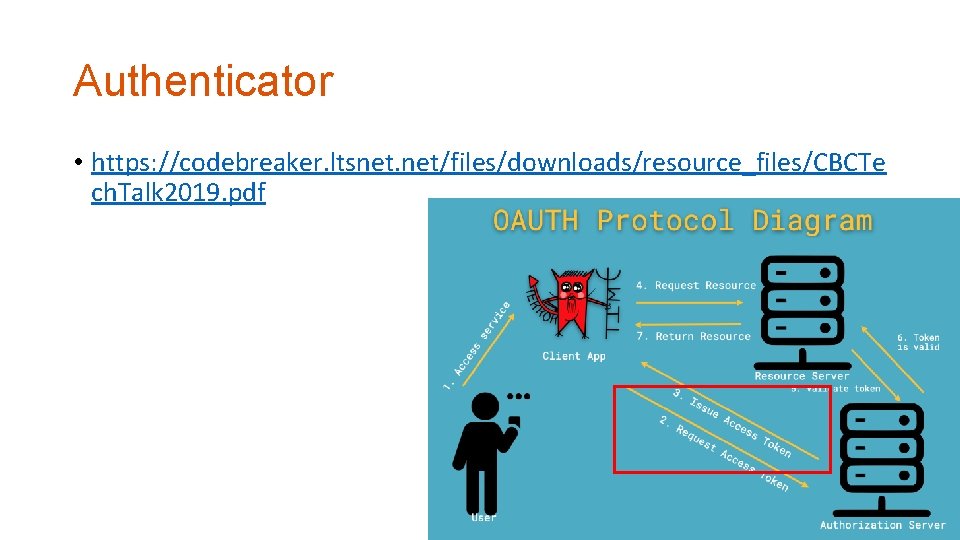
Authenticator • https: //codebreaker. ltsnet. net/files/downloads/resource_files/CBCTe ch. Talk 2019. pdf
Find the Vulnerability in the Code! • Question: • Can you login to the server with other user name? • The app uses a bespoke application of the OAUTH protocol to authorize and authenticate Terror. Time users to the chat service. Our intelligence indicates that individual terrorists are provided phones with Terror. Time installed and preregistered to them. They simply need to enter their username and secret PIN to access the chat service, which uses OAUTH behind the scenes to generate a unique token that is used for authentication. This is a non-standard way of using the protocol, but they believe it to be superior to normal password-based authentication since a unique token is used per login vs. a static password. Whether that is indeed the case is up to you to analyze and assess for possible vulnerabilities. Our forensics team recovered a deleted file from the terrorist's hard drive that may aid in your analysis.
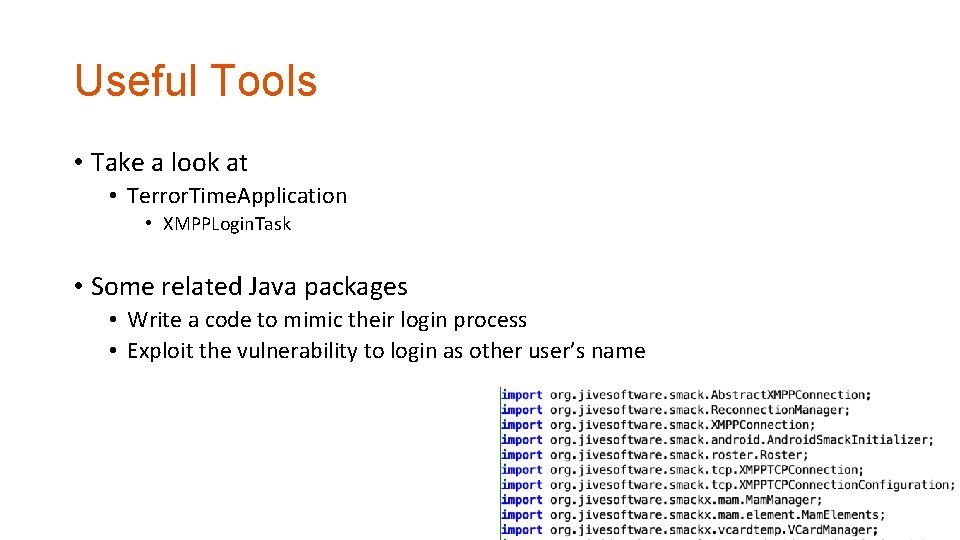
Useful Tools • Take a look at • Terror. Time. Application • XMPPLogin. Task • Some related Java packages • Write a code to mimic their login process • Exploit the vulnerability to login as other user’s name

Assignment Dues • Week 6 late: 12/10 14: 10 • Week 7: 12/6 14: 10 • Week 7 late: 12/12 14: 10 • Codebreaker: 12/12 23: 59 • Your grade will be available on 12/13
- Slides: 34