Baseband Attacks Remote Exploitation of Memory Corruption in
Baseband Attacks: Remote Exploitation of Memory Corruption in Cellular Protocol Stacks Ralf-Philipp Weinmann University of Luxwembourg WOOT ‘ 12 Syssec Lab. 김은수

Mobile Security v Application Security – Malwares – Browser / App Vulnerability v OS Security Application Layer Software Security – Kernel Vulnerability v Cellular Network Security – Location tracking – Eavesdropping / Caller spoofing – Over-billing / Free data channel Network Security How about Baseband layer security? 2
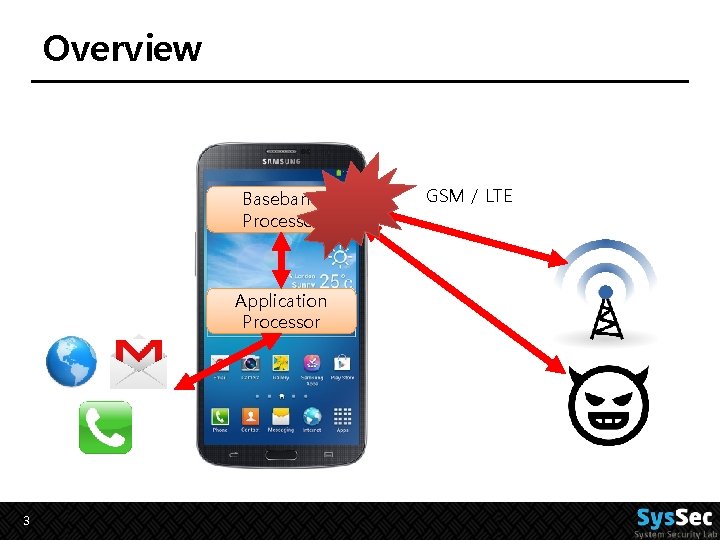
Overview Baseband Processor Application Processor 3 GSM / LTE
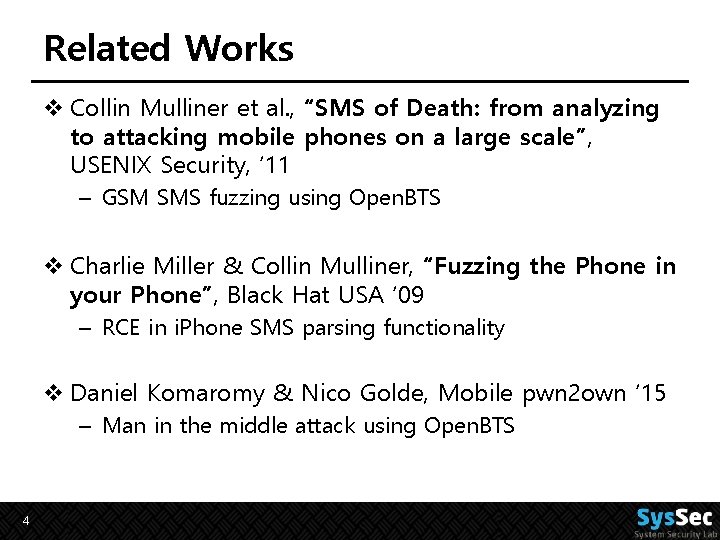
Related Works v Collin Mulliner et al. , “SMS of Death: from analyzing to attacking mobile phones on a large scale”, USENIX Security, ‘ 11 – GSM SMS fuzzing using Open. BTS v Charlie Miller & Collin Mulliner, “Fuzzing the Phone in your Phone”, Black Hat USA ‘ 09 – RCE in i. Phone SMS parsing functionality v Daniel Komaromy & Nico Golde, Mobile pwn 2 own ‘ 15 – Man in the middle attack using Open. BTS 4

Smartphone architecture 5

GSM Layers Call, SMS, … Location update Radio channel Data-link Layer Physical Layer 6
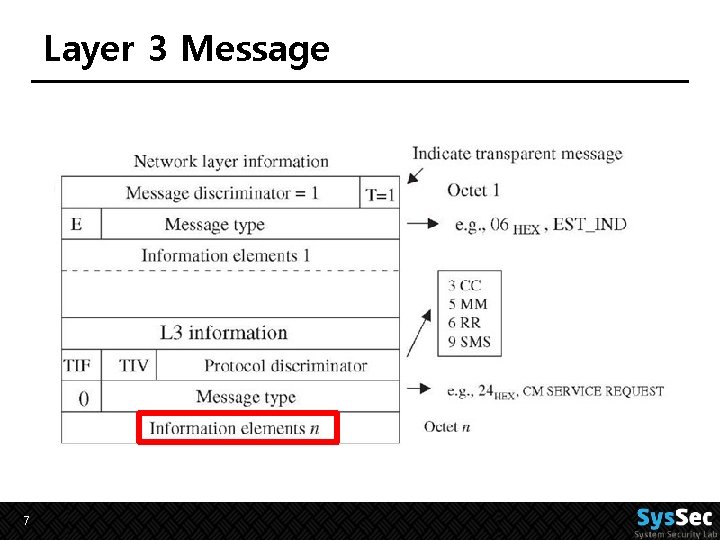
Layer 3 Message 7
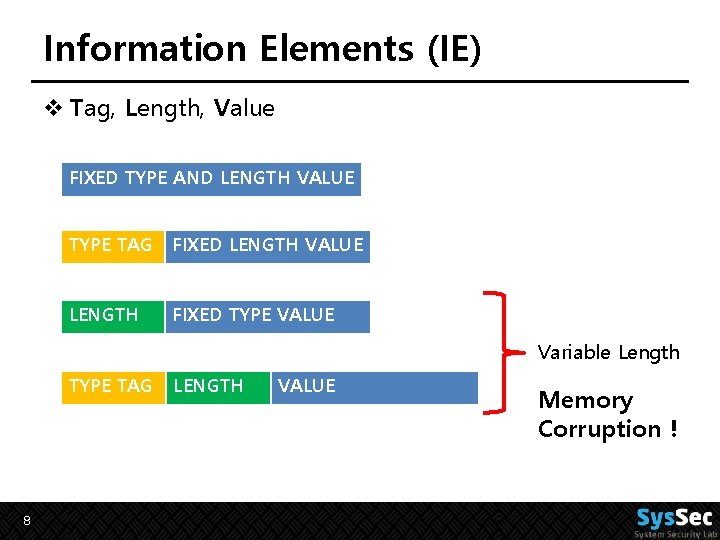
Information Elements (IE) v Tag, Length, Value FIXED TYPE AND LENGTH VALUE TYPE TAG FIXED LENGTH VALUE LENGTH FIXED TYPE VALUE Variable Length TYPE TAG 8 LENGTH VALUE Memory Corruption !
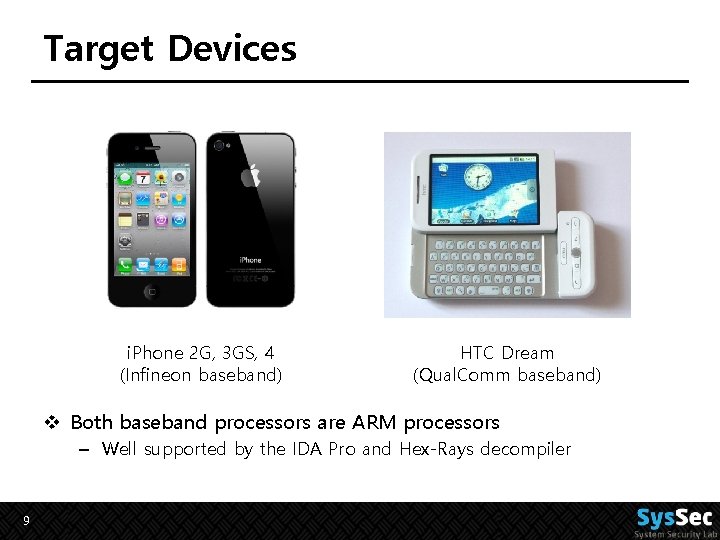
Target Devices i. Phone 2 G, 3 GS, 4 (Infineon baseband) HTC Dream (Qual. Comm baseband) v Both baseband processors are ARM processors – Well supported by the IDA Pro and Hex-Rays decompiler 9
Analysis v Fuzzing is not sufficient – Difficult to find causes of crashes v Baseband source code is not available – Reverse-engineer the firmware binary for updates v Useful tools – – Qual. Comm’s QXDM IDA Pro disassembler Hex-Rays decompiler Bin. Diff v Find Vulnerabilities! 10
Exploit Mitigations v No Stack Canary v No Heap Hardening v No Data Execution Prevention v No Address Space Layout Randomization 11
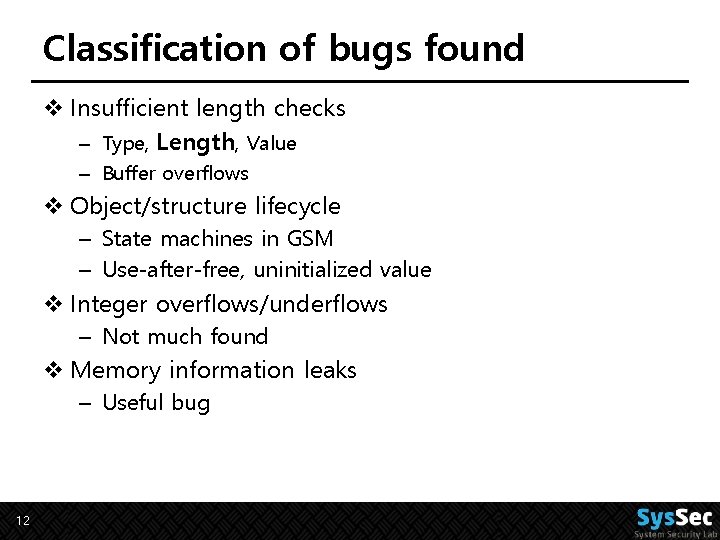
Classification of bugs found v Insufficient length checks – Type, Length, Value – Buffer overflows v Object/structure lifecycle – State machines in GSM – Use-after-free, uninitialized value v Integer overflows/underflows – Not much found v Memory information leaks – Useful bug 12
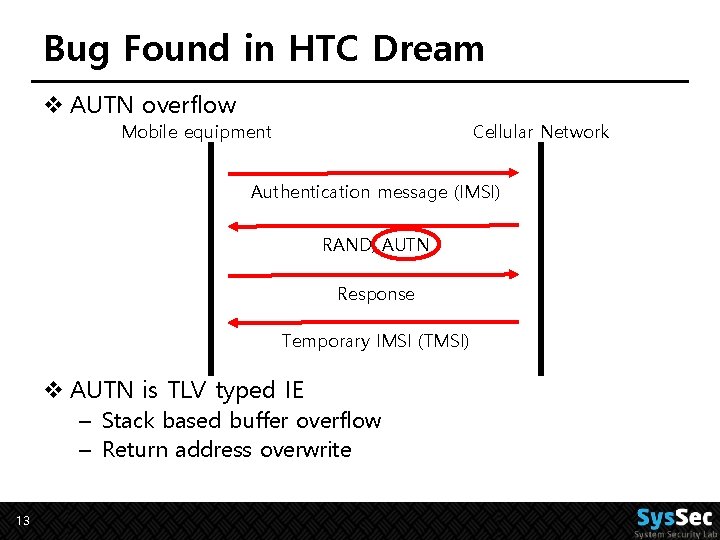
Bug Found in HTC Dream v AUTN overflow Mobile equipment Cellular Network Authentication message (IMSI) RAND, AUTN Response Temporary IMSI (TMSI) v AUTN is TLV typed IE – Stack based buffer overflow – Return address overwrite 13
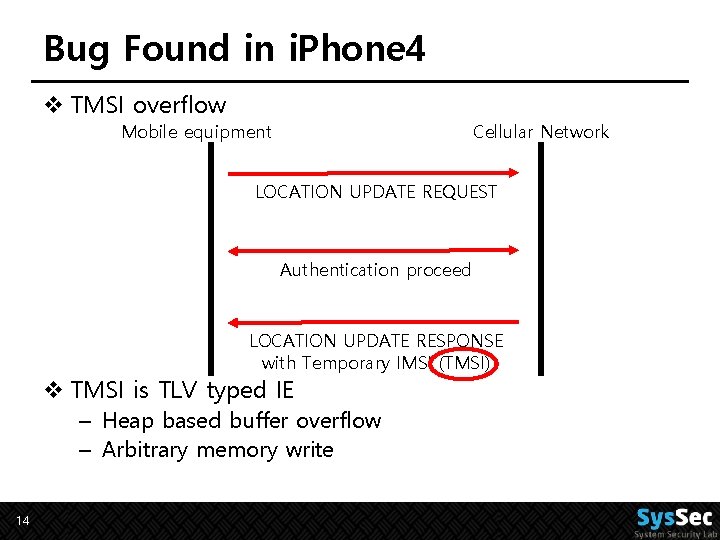
Bug Found in i. Phone 4 v TMSI overflow Mobile equipment Cellular Network LOCATION UPDATE REQUEST Authentication proceed LOCATION UPDATE RESPONSE with Temporary IMSI (TMSI) v TMSI is TLV typed IE – Heap based buffer overflow – Arbitrary memory write 14
From Bugs to Exploits v Make the phone perform an unexpected action v Force Auto-answer functionality – The phone automatically pick up an incoming call – Setup using AT command 15
Attack v Open. BTS – – – Open source Cellular Infrastructure Supports Universal Software Radio Peripheral Can build a Fake Base station Nearby phones will attach No auth on Base station v Target device fingerprinting – International Mobile Station Equipment Identity (IMEISV) – AA-BBBBBB-CCCCCC(serial #)-DD(software version) 16
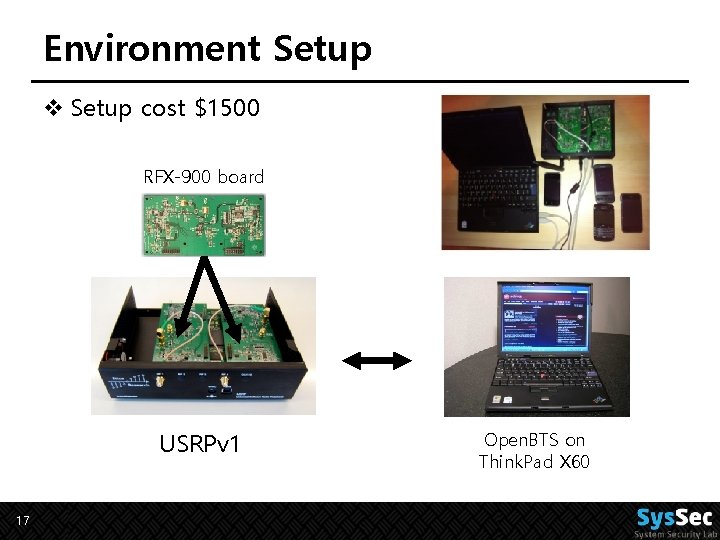
Environment Setup v Setup cost $1500 RFX-900 board USRPv 1 17 Open. BTS on Think. Pad X 60
Impact v Monitor the voice and other connections v Billing Issues v Brick by writing NVRAM v Affect the applications layer 18
Conclusion v Found many memory corruptions in baseband v Baseband layer can be exploited – With only $1500 equipments v 3 G would be also vulnerable to similar method – More complicated protocols – More bugs v Need code audit and hardenings 19
Appendix. LTE baseband Attack v LTE Protocols – More security features (mutual authentication) – Complicated protocols – Hard to reverse-engineering (Qual. Comm Hexagon) v Found some bugs… – But no exploitable bugs yet. v Open. LTE 20

Thank You! syssec@kaist. ac. kr 21
- Slides: 21