Spring 2017 Software Defined Networking William Brockelsby Ph
Spring 2017 Software Defined Networking William Brockelsby Ph. D Student – NC State Computer Science Senior Systems Engineer – Juniper Networks wjbrocke@ncsu. edu
Background • • • 1998 - Started at NC State 1999 - Part time “Res. Net” network technician 2002 - Bachelors in CSC 2003 - CSC graduate student 2004 - Software engineer at NC State 2005 - Network engineer at NC State 2006 - Masters in CSC 2009 - Senior network engineer at Duke University Health System 2010 - Lead network architect at NC State 2015 - CSC part-time Ph. D student 2016 - Senior systems engineer at Juniper Networks
SDN Review • What is SDN? – One answer: Separation of control plane from forwarding plane* [1] • Why SDN? – Policy Driven Networking – Automation • Faster Time to Service • Faster Time to Revenue – Reduced Complexity – Improve Reliability by Minimizing Human Error [3]
SDN Approaches • Flow table/pipeline abstraction – Forwarding plane: table(s) with match+action – Control plane: Controller(s) populate tables with match+action – Open. Flow [1] – P 4: Programming Protocol-Independent Packet Processors [2] • Overlay – Forwarding plane: Tunnel Encap/Decap (VXLAN, GRE, etc) – Control Plane: EVPN (RFC 7209), Open. Contrail, etc
SDN Approaches • Additional Approaches – Compromise between centralized and traditional (distributed) control plane (what happens to an Open. Flow switch if the controller is lost? ) – I 2 RS – Interface to the Routing System: allows external software to interact with the RIB. Classic routing protocols can co-exist with this setup. – PCEP – Path Computation Element (PCE) Protocol: permits the centralized computation and distribution of paths (traffic engineering tunnels) across an MPLS network with a global view.
Open. Flow Challenges • Proactive vs Reactive • v. Switches (OVS, Lagopus, etc) – Excellent Support; Lower Performance* • Hardware Switches – Mapping table abstraction onto ASICs is difficult – Flow table capacity varies widely by platform – OF specification contains many optional components – Some actions are implemented in software – Pipelines: A chain of tables to help minimize Cartesian product explosion • Support is often limited
Open. Flow “App Store” • Early Idea – Community develops applications for Open. Flow environments – These are uploaded to an “app store” like interface – Other interested parties can download network applications: • Firewalls • Load balancers • Traffic engineering systems • We faced challenges, although some examples exist
P 4: Programming Protocol-Independent Packet Processors • http: //p 4. org - A “Programming Language” for Packet Processors • Define headers and associated fields • Define a parser : returns parsed representations of incoming packets based on headers/fields • Match+Action Tables – operate on the parsed representation – size is specified by programmer – actions: modify field, add/remove header, counters/meta data • Control Function: specifies the sequence of tables a packet visits • Permits packet cloning and recirculation
P 4: Programming Protocol-Independent Packet Processors • P 4 source code file is compiled by a P 4 compiler and loaded onto processor • The compiler can be provided by a vendor to avoid disclosing intellectual property associated with the underlying ASIC • The compiler generates an API that can be used at runtime to populate the tables with matches and actions (eliminates the need for Open. Flow) • An Open. Flow agent could call the P 4 API to provide backwards compatibility
Overlay Networks • Built on top of another network referred to as an underlay • Level of indirection with many benefits such as: – The ability to support multi-tenancy and isolation on shared infrastructure – Add features not natively supported on the underlay (ex: IPv 6 or MPLS) • Tunnels have been around for years, how is this SDN? – Networks can be created rapidly on demand by software – Tunnels can be steered onto tunnels by software (how? ) – One way to implement service chaining (NFV)
Overlay Network Challenges • Overhead of additional headers (VXLAN, GRE, etc) – Less of a concern in the LAN and Data Center – Header parsing – Hardware (Switch/NIC) offload • Disconnect between overlay and underlay – ECMP hashing (local decision) can lead to hot spots • Source IP, Destination IP, Protocol, Source Port, Destination Port • VXLAN – entropy in UDP source port, destination port is 4789 (IANA) – Underlay is blind (can’t enforce policies or make optimal decisions)
Software Forwarding Enhancements • Data Plane Development Kit (DPDK) – Originally developed by Intel – Now an open source BSD licensed project – http: //dpdk. org – Library and NIC controller for packet processing in software – Provides an abstraction layer for software forwarding to maximize performance across platforms • Lockless queues • Enhanced buffer management • Poll mode drivers (no interrupt overhead)
Software Forwarding Enhancements • Fast Data Project – Linux Foundation Project – http: //fd. io – Leverages DPDK – Adds Vector Packet Processing • Instead of reading a single packet, grab a vector of packets • Packets enter a packet parsing graph where different nodes handle different protocols • All applicable packets in the vector are processed within a given graph node before moving onto the next node • Improves performance on software processors
Software Forwarding Enhancements • Hardware Offload – NIC checksum offload (IP, TCP, UDP) in hardware – ethtool --show-offload eth 0 • Tunneling Hardware Offloads (major NIC vendors) – VXLAN, NVGRE offload
Network Functions Virtualization • What is a network function? • How are network functions typically deployed? What is the problem? • What about performance and scale? • Local vs centralized deployment options?
SDN Application - Network Functions Virtualization
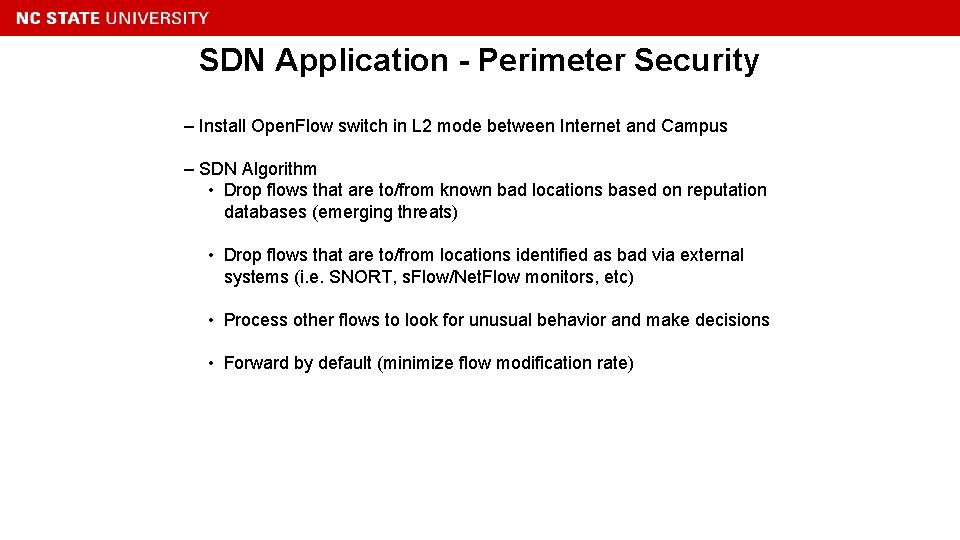
SDN Application - Perimeter Security – Install Open. Flow switch in L 2 mode between Internet and Campus – SDN Algorithm • Drop flows that are to/from known bad locations based on reputation databases (emerging threats) • Drop flows that are to/from locations identified as bad via external systems (i. e. SNORT, s. Flow/Net. Flow monitors, etc) • Process other flows to look for unusual behavior and make decisions • Forward by default (minimize flow modification rate)
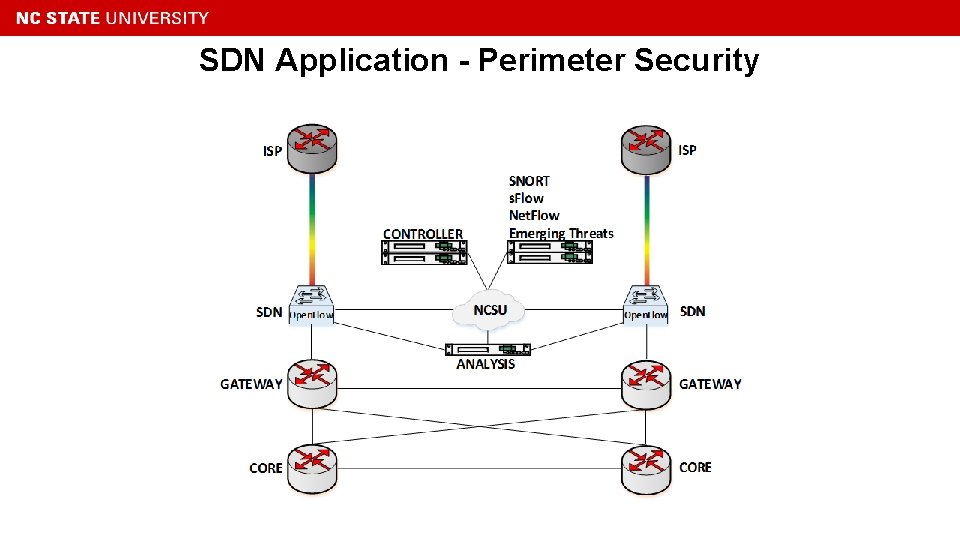
SDN Application - Perimeter Security
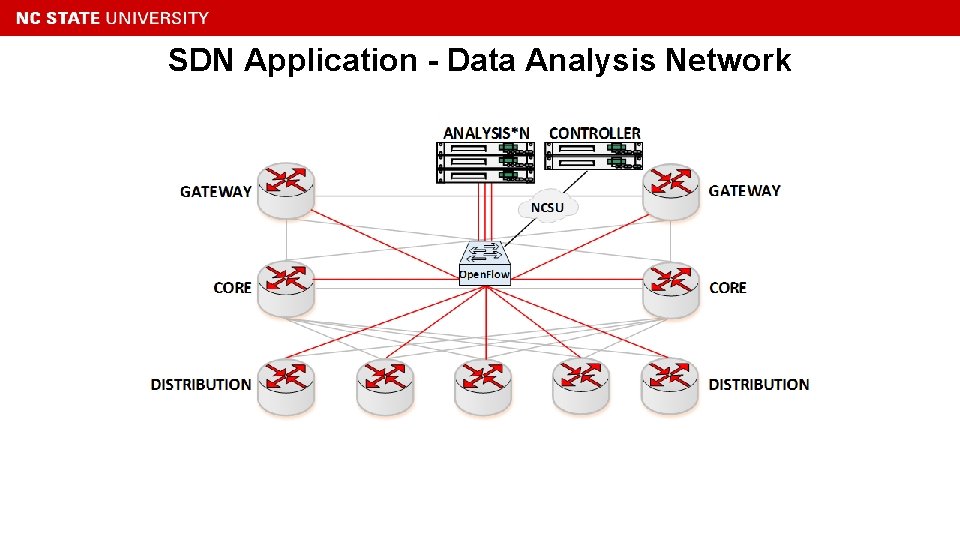
SDN Application - Data Analysis Network
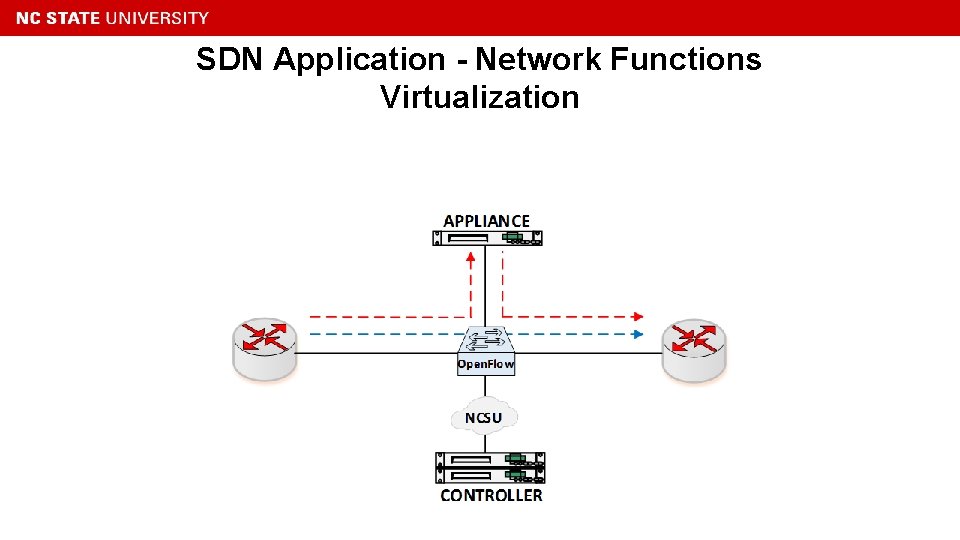
SDN Application - Network Functions Virtualization
![References [1] Mc. Keown, N. , Anderson, T. , Balakrishnan, H. , Parulkar, G. References [1] Mc. Keown, N. , Anderson, T. , Balakrishnan, H. , Parulkar, G.](http://slidetodoc.com/presentation_image/2077909a84b4145eabb349cc7fa8dd63/image-21.jpg)
References [1] Mc. Keown, N. , Anderson, T. , Balakrishnan, H. , Parulkar, G. , Peterson, L. , Rexford, J. , . . . & Turner, J. (2008). Open. Flow: enabling innovation in campus networks. ACM SIGCOMM Computer Communication Review, 38(2), 69 74. [2] Bosshart, P. , Daly, D. , Gibb, G. , Izzard, M. , Mc. Keown, N. , Rexford, J. , . . . & Walker, D. (2014). P 4: Programming protocol-independent packet processors. ACM SIGCOMM Computer Communication Review, 44(3), 87 -95. [3] Mushi, M. J. (2016). Factoring Human Workflow in Network Reliability Engineering. Ph. D Dissertation, North Carolina State University

Juniper Networks SDN Overview Open. Contrail, North. Star William Brockelsby
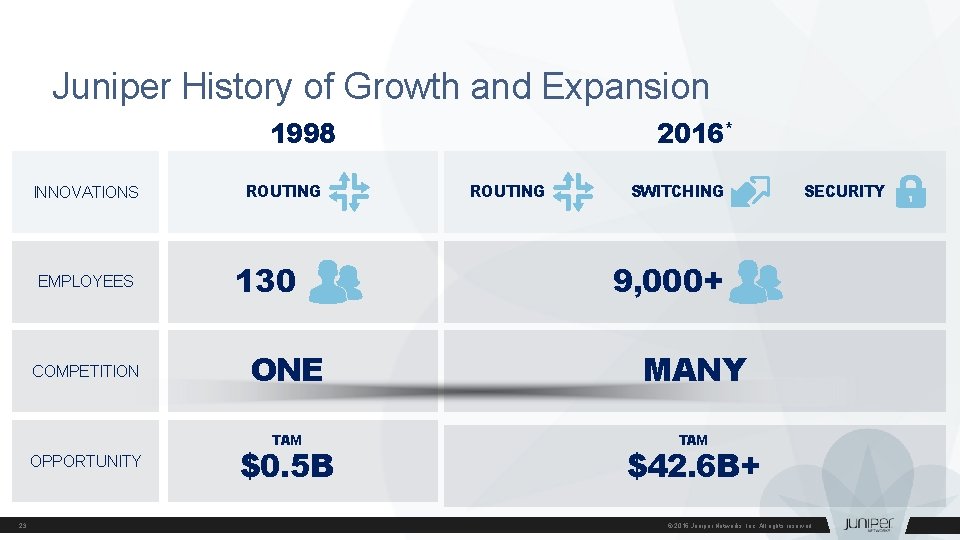
Juniper History of Growth and Expansion 1998 INNOVATIONS EMPLOYEES COMPETITION OPPORTUNITY 23 ROUTING 130 2016* ROUTING SWITCHING 9, 000+ ONE MANY TAM $0. 5 B SECURITY $42. 6 B+ © 2016 Juniper Networks, Inc. All rights reserved.
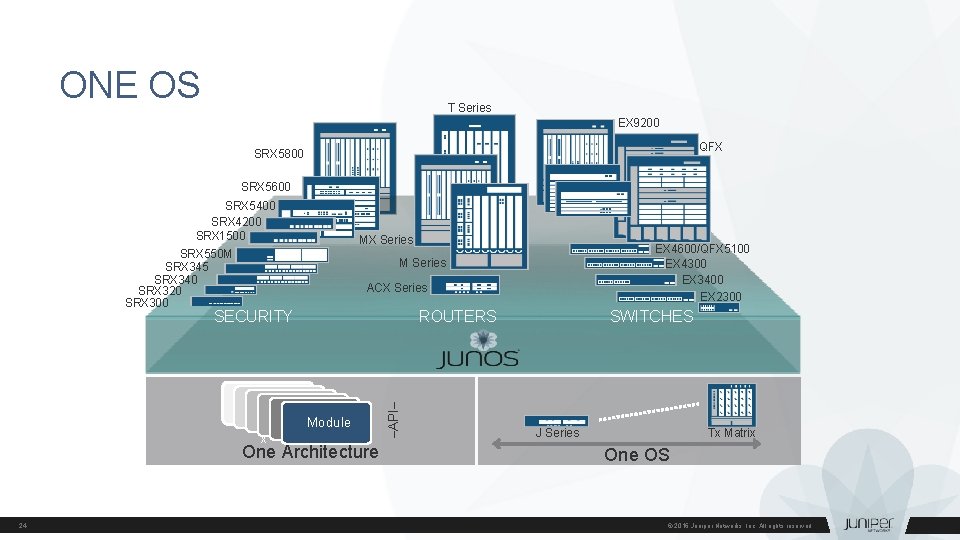
ONE OS T Series EX 9200 QFX SRX 5800 SRX 5600 SRX 5400 SRX 4200 SRX 1500 SRX 550 M SRX 345 SRX 340 SRX 320 SRX 300 MX Series ACX Series ROUTERS Module One Architecture 24 –API– SECURITY x EX 4600/QFX 5100 EX 4300 EX 3400 EX 2300 M Series SWITCHES J Series Tx Matrix One OS © 2016 Juniper Networks, Inc. All rights reserved.
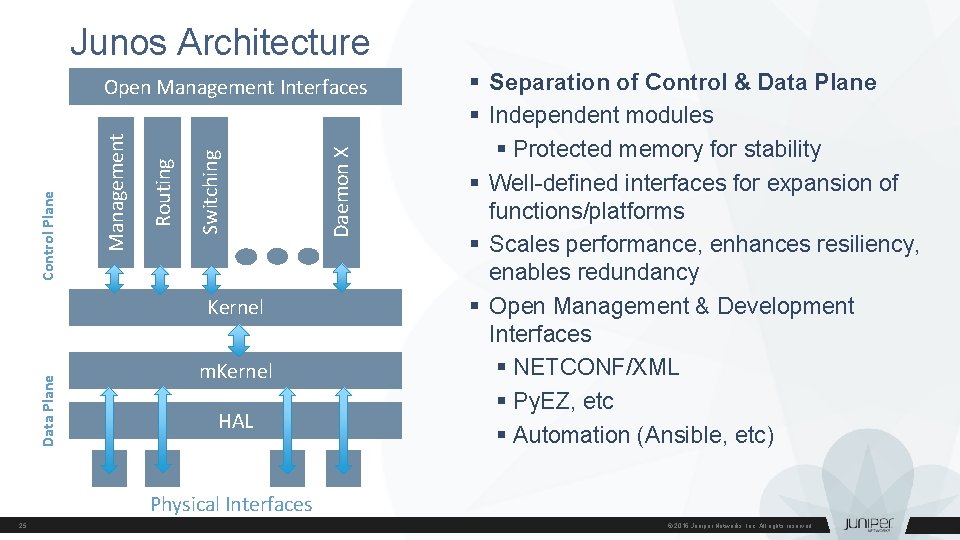
Junos Architecture Data Plane Kernel m. Kernel HAL Daemon X Switching Routing Management Control Plane Open Management Interfaces § Separation of Control & Data Plane § Independent modules § Protected memory for stability § Well-defined interfaces for expansion of functions/platforms § Scales performance, enhances resiliency, enables redundancy § Open Management & Development Interfaces § NETCONF/XML § Py. EZ, etc § Automation (Ansible, etc) Physical Interfaces 25 © 2016 Juniper Networks, Inc. All rights reserved.

Open. Contrail
What is Open. Contrail? • Open. Contrail is an Apache 2. 0 -licensed project • Provides all components needed for Network Virtualization: • • SDN Controller v. Router Analytics engine Published Northbound APIs • Most widely deployed commercial SDN Controller as voted by Open. Stack • More information can be found at www. opencontrail. org 27 © 2016 Juniper Networks, Inc. All rights reserved.
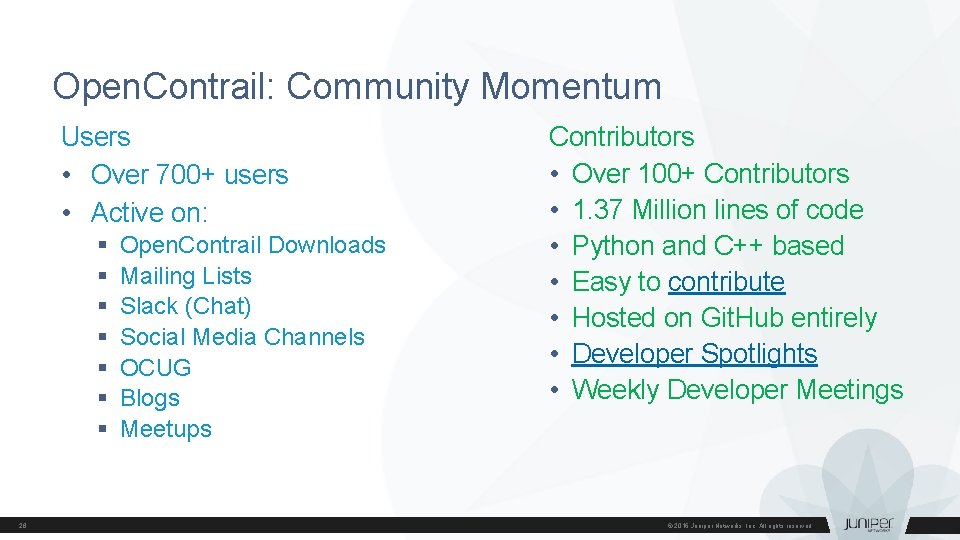
Open. Contrail: Community Momentum Users • Over 700+ users • Active on: § § § § 28 Open. Contrail Downloads Mailing Lists Slack (Chat) Social Media Channels OCUG Blogs Meetups Contributors • Over 100+ Contributors • 1. 37 Million lines of code • Python and C++ based • Easy to contribute • Hosted on Git. Hub entirely • Developer Spotlights • Weekly Developer Meetings © 2016 Juniper Networks, Inc. All rights reserved.
Open. Contrail: What is network virtualization • Independent of Physical Network Location or State – Logical Network across any server, any rack, any cluster, any data-center – Virtual Machines can migrate without requiring any reworking of security policies, load balancing, etc – New Workloads or Networks should not require provisioning of physical network – Nodes in Physical Network can fail without any disruption to Workload • Full Isolation for Multi-tenancy and Fault Tolerance – MAC and IP Addresses are completely private per tenant – Any failures or configuration errors by tenants do not affect other applications or tenants – Any failures in the virtual layer do not propagate to physical layer 29 © 2017 Juniper Networks, Inc. All rights reserved.
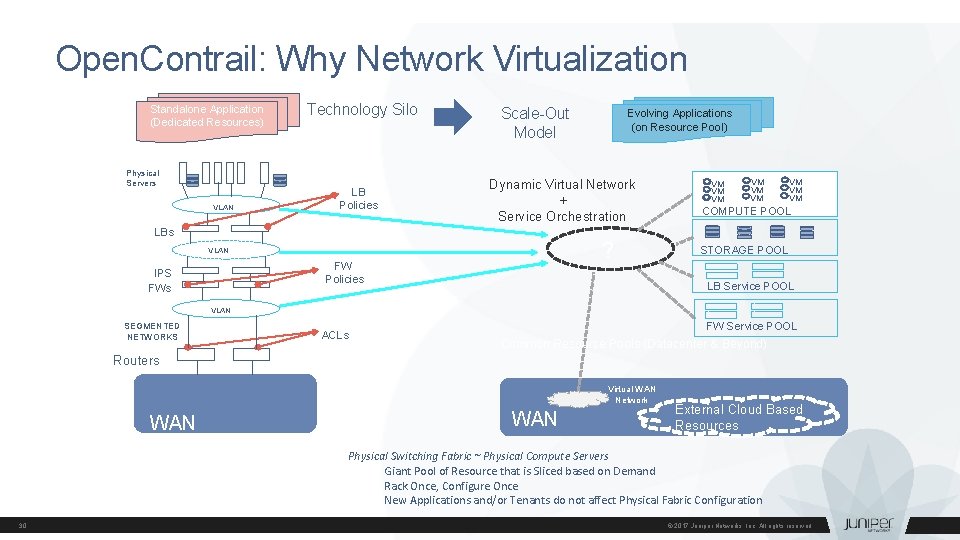
Open. Contrail: Why Network Virtualization Standalone Application (Dedicated Resources) Physical Servers VLAN Technology Silo LB Policies Scale-Out Model Dynamic Virtual Network + Service Orchestration LBs ? VLAN FW Policies IPS FWs Evolving Applications (on Resource Pool) VM VM VM COMPUTE POOL STORAGE POOL LB Service POOL VLAN SEGMENTED NETWORKS ACLs FW Service POOL Common Resource Pools (Datacenter & Beyond) Routers Virtual WAN Network WAN External Cloud Based Resources Physical Switching Fabric ~ Physical Compute Servers Giant Pool of Resource that is Sliced based on Demand Rack Once, Configure Once New Applications and/or Tenants do not affect Physical Fabric Configuration 30 © 2017 Juniper Networks, Inc. All rights reserved.
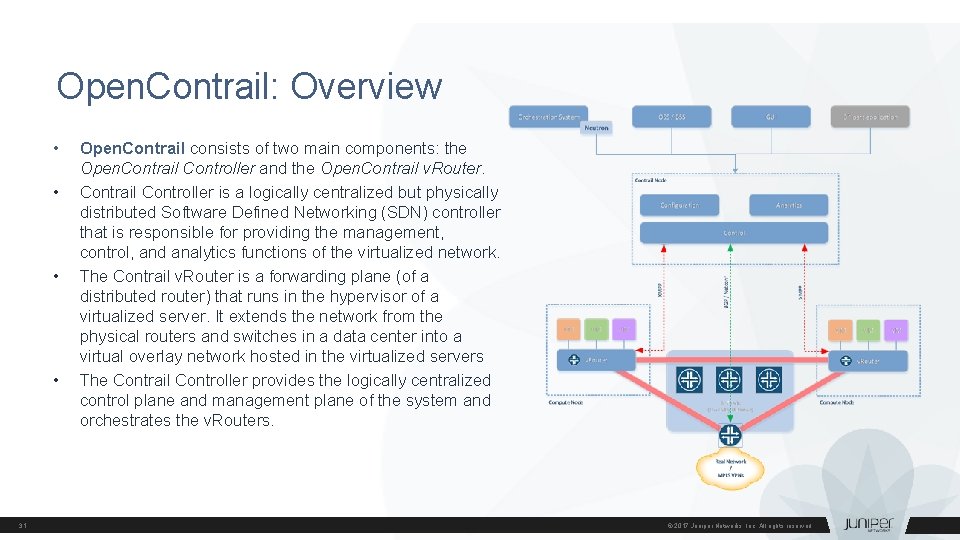
Open. Contrail: Overview • • 31 Open. Contrail consists of two main components: the Open. Contrail Controller and the Open. Contrail v. Router. Contrail Controller is a logically centralized but physically distributed Software Defined Networking (SDN) controller that is responsible for providing the management, control, and analytics functions of the virtualized network. The Contrail v. Router is a forwarding plane (of a distributed router) that runs in the hypervisor of a virtualized server. It extends the network from the physical routers and switches in a data center into a virtual overlay network hosted in the virtualized servers The Contrail Controller provides the logically centralized control plane and management plane of the system and orchestrates the v. Routers. © 2017 Juniper Networks, Inc. All rights reserved.
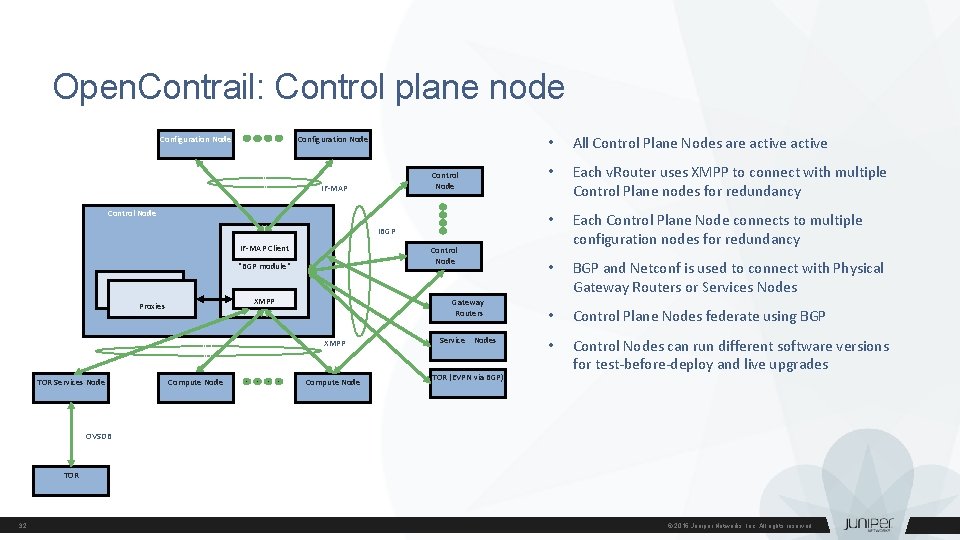
Open. Contrail: Control plane node Configuration Node Control Node IF-MAP Control Node IBGP IF-MAP Client Control Node "BGP module" XMPP Proxies Gateway Routers XMPP TOR Services Node Compute Node Service Nodes TOR (EVPN via BGP) • All Control Plane Nodes are active • Each v. Router uses XMPP to connect with multiple Control Plane nodes for redundancy • Each Control Plane Node connects to multiple configuration nodes for redundancy • BGP and Netconf is used to connect with Physical Gateway Routers or Services Nodes • Control Plane Nodes federate using BGP • Control Nodes can run different software versions for test-before-deploy and live upgrades OVSDB TOR 32 © 2016 Juniper Networks, Inc. All rights reserved.
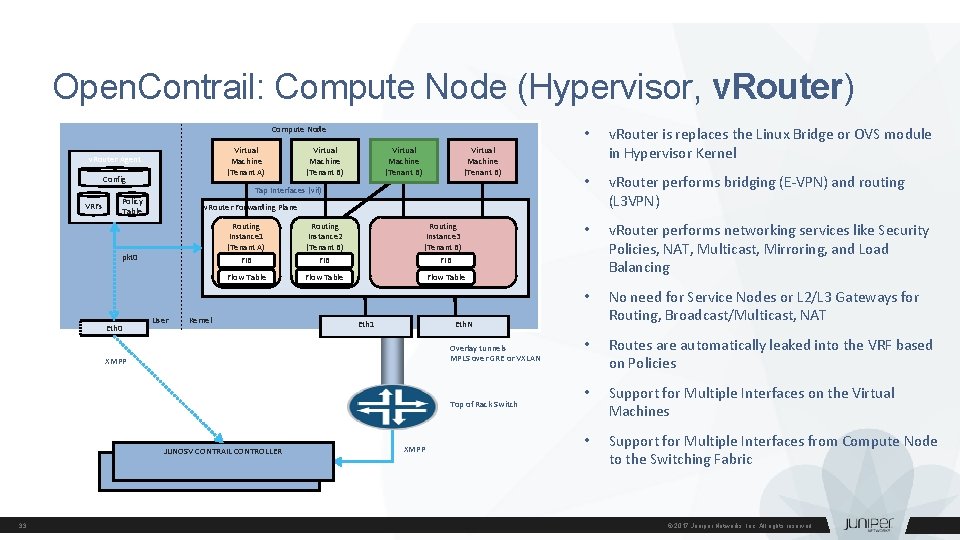
Open. Contrail: Compute Node (Hypervisor, v. Router) Compute Node Virtual Machine (Tenant A) v. Router Agent Config VRFs Virtual Machine (Tenant B) Tap Interfaces (vif) Policy Table User Routing Instance 1 (Tenant A) Routing Instance 2 (Tenant B) FIB Flow Table Kernel Routing Instance 3 (Tenant B) FIB • v. Router performs bridging (E-VPN) and routing (L 3 VPN) • v. Router performs networking services like Security Policies, NAT, Multicast, Mirroring, and Load Balancing • No need for Service Nodes or L 2/L 3 Gateways for Routing, Broadcast/Multicast, NAT • Routes are automatically leaked into the VRF based on Policies • Support for Multiple Interfaces on the Virtual Machines • Support for Multiple Interfaces from Compute Node to the Switching Fabric Flow Table Eth 1 Eth. N Overlay tunnels MPLS over GRE or VXLAN XMPP Top of Rack Switch JUNOSV CONTRAIL CONTROLLER 33 v. Router is replaces the Linux Bridge or OVS module in Hypervisor Kernel v. Router Forwarding Plane pkt 0 Eth 0 Virtual Machine (Tenant B) • XMPP © 2017 Juniper Networks, Inc. All rights reserved.
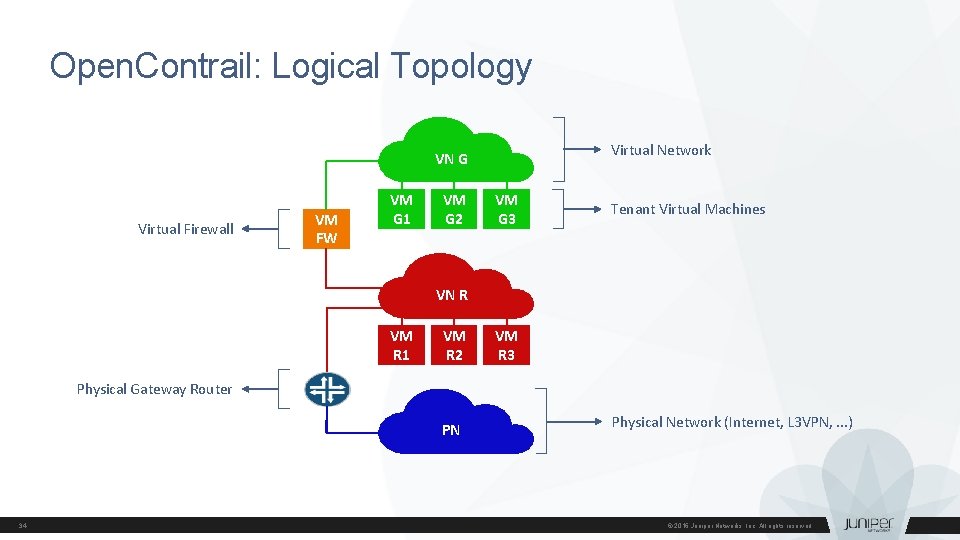
Open. Contrail: Logical Topology Virtual Network VN G Virtual Firewall VM FW VM G 1 VM G 2 VM G 3 Tenant Virtual Machines VN R VM R 1 VM R 2 VM R 3 Physical Gateway Router PN 34 Physical Network (Internet, L 3 VPN, . . . ) © 2016 Juniper Networks, Inc. All rights reserved.
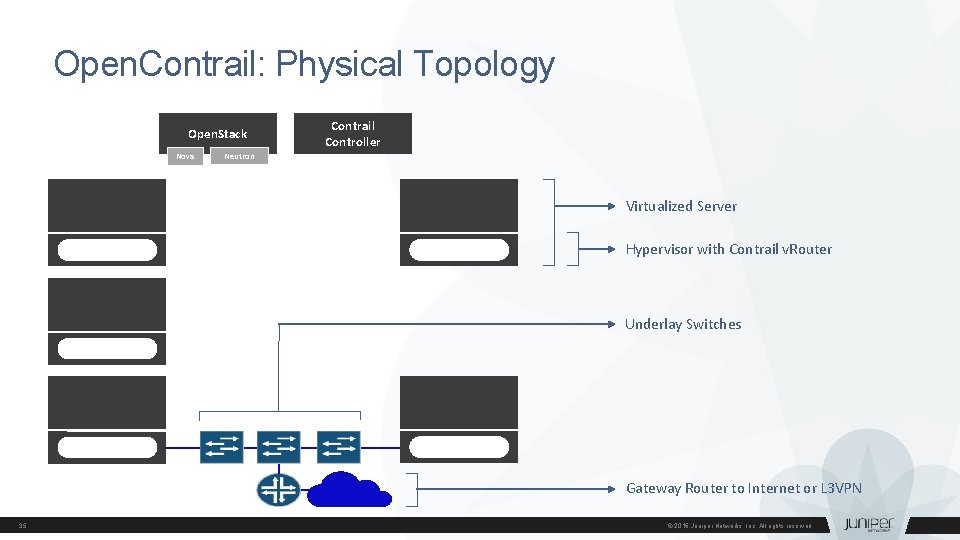
Open. Contrail: Physical Topology Open. Stack Nova Contrail Controller Neutron Virtualized Server Hypervisor with Contrail v. Router Underlay Switches Gateway Router to Internet or L 3 VPN 35 © 2016 Juniper Networks, Inc. All rights reserved.
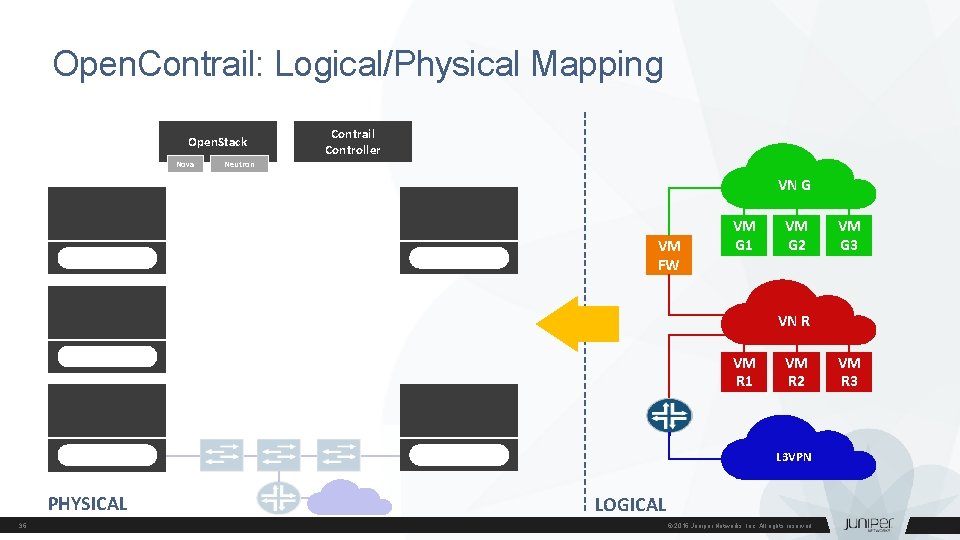
Open. Contrail: Logical/Physical Mapping Open. Stack Nova Contrail Controller Neutron VN G VM FW VM G 1 VM G 2 VM G 3 VN R VM R 1 VM R 2 VM R 3 L 3 VPN PHYSICAL 36 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
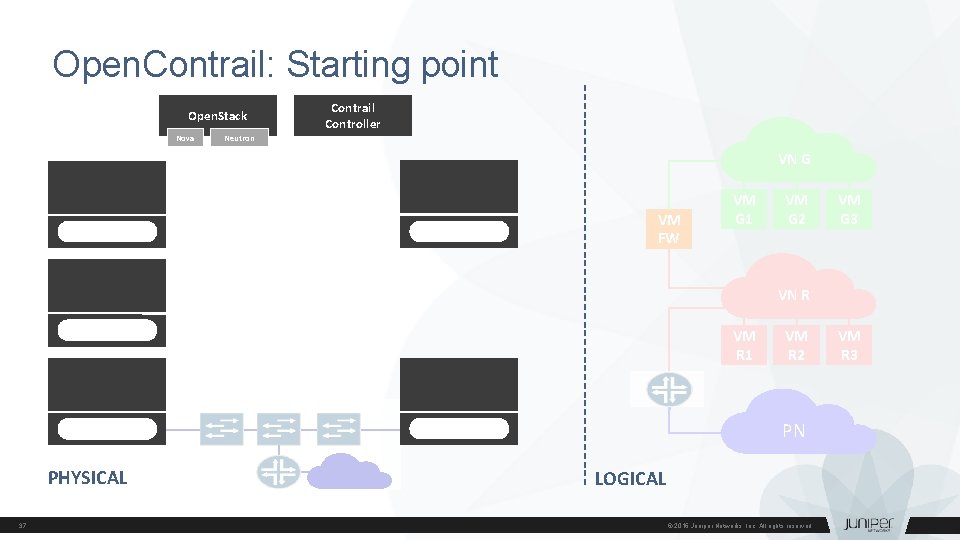
Open. Contrail: Starting point empty logical topology Open. Stack Nova Contrail Controller Neutron VN G VM FW VM G 1 VM G 2 VM G 3 VN R VM R 1 VM R 2 VM R 3 PN PHYSICAL 37 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
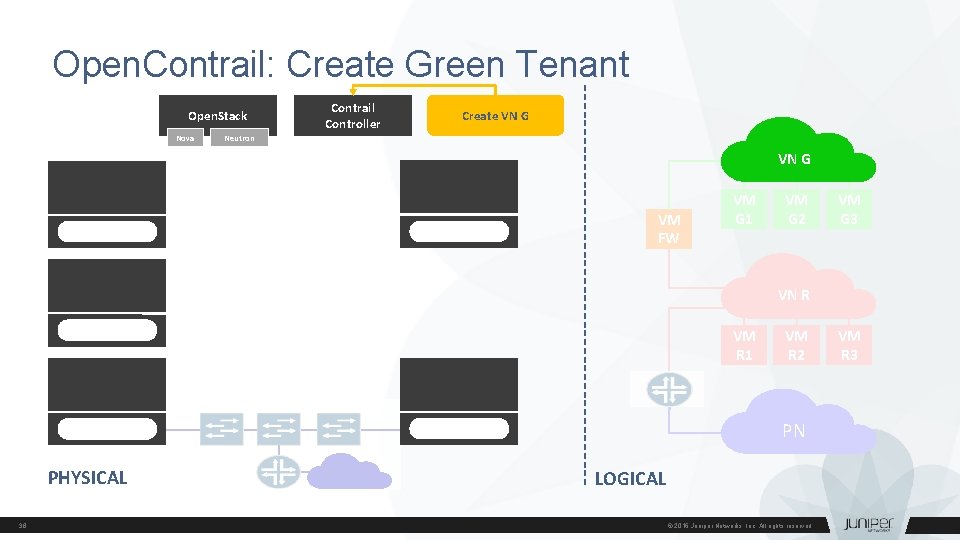
Open. Contrail: Create Green Tenant create virtual network "green" Open. Stack Nova Contrail Controller Create VN G Neutron VN G VM FW VM G 1 VM G 2 VM G 3 VN R VM R 1 VM R 2 VM R 3 PN PHYSICAL 38 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
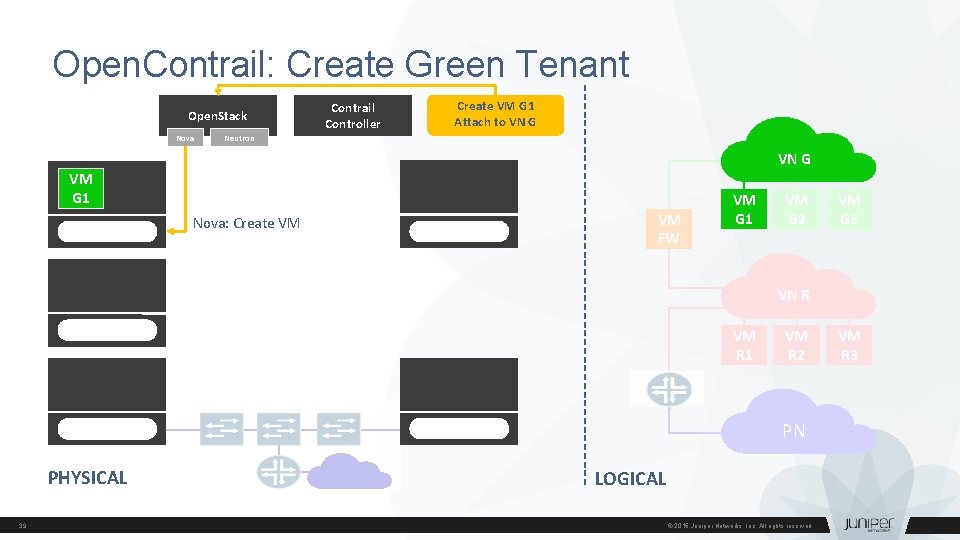
Open. Contrail: Create Green Tenant create virtual machine "g 1" Open. Stack Nova Contrail Controller Create VM G 1 Attach to VN G Neutron VN G VM G 1 Nova: Create VM VM FW VM G 1 VM G 2 VM G 3 VN R VM R 1 VM R 2 VM R 3 PN PHYSICAL 39 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
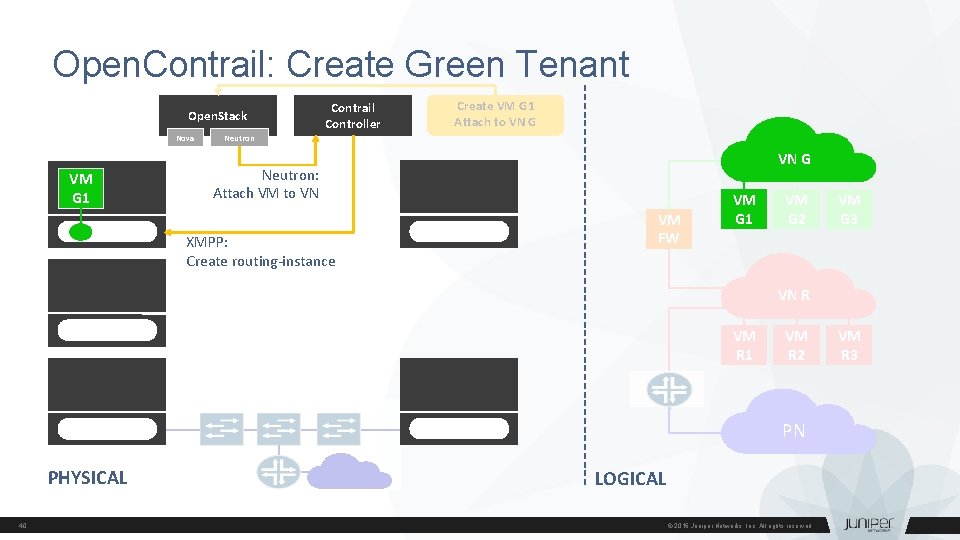
Open. Contrail: Create Green Tenant create virtual machine "g 1" Open. Stack Nova VM G 1 Contrail Controller Create VM G 1 Attach to VN G Neutron: Attach VM to VN XMPP: Create routing-instance VM FW VM G 1 VM G 2 VM G 3 VN R VM R 1 VM R 2 VM R 3 PN PHYSICAL 40 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
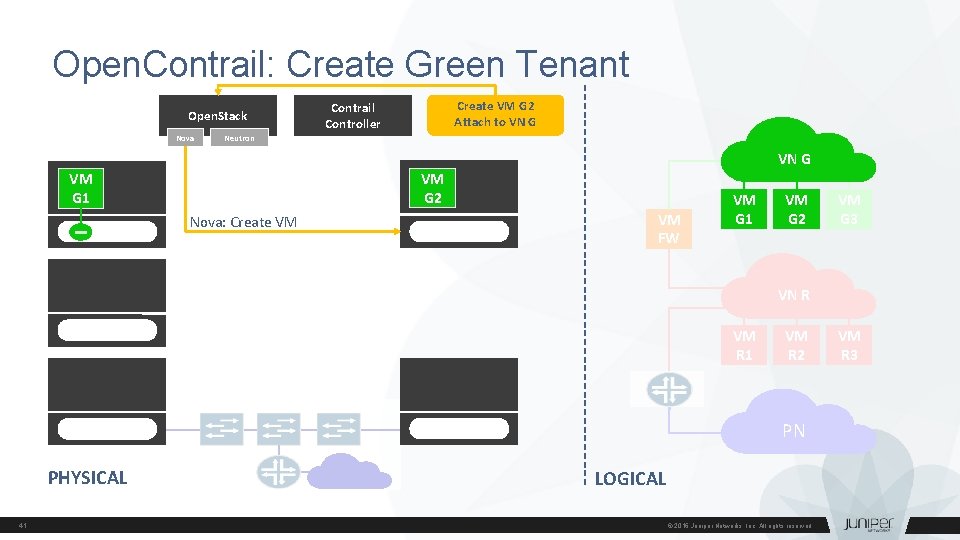
Open. Contrail: Create Green Tenant create virtual machine "g 2" Open. Stack Nova Create VM G 2 Attach to VN G Contrail Controller Neutron VN G VM G 2 VM G 1 Nova: Create VM VM FW VM G 1 VM G 2 VM G 3 VN R VM R 1 VM R 2 VM R 3 PN PHYSICAL 41 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
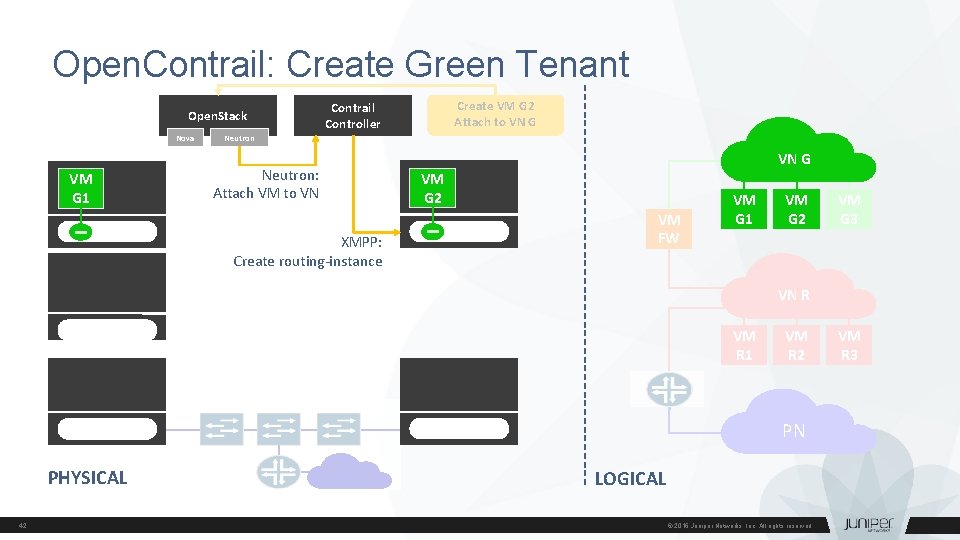
Open. Contrail: Create Green Tenant create virtual machine "g 2" Open. Stack Nova VM G 1 Create VM G 2 Attach to VN G Contrail Controller Neutron: Attach VM to VN XMPP: Create routing-instance VN G VM G 2 VM FW VM G 1 VM G 2 VM G 3 VN R VM R 1 VM R 2 VM R 3 PN PHYSICAL 42 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
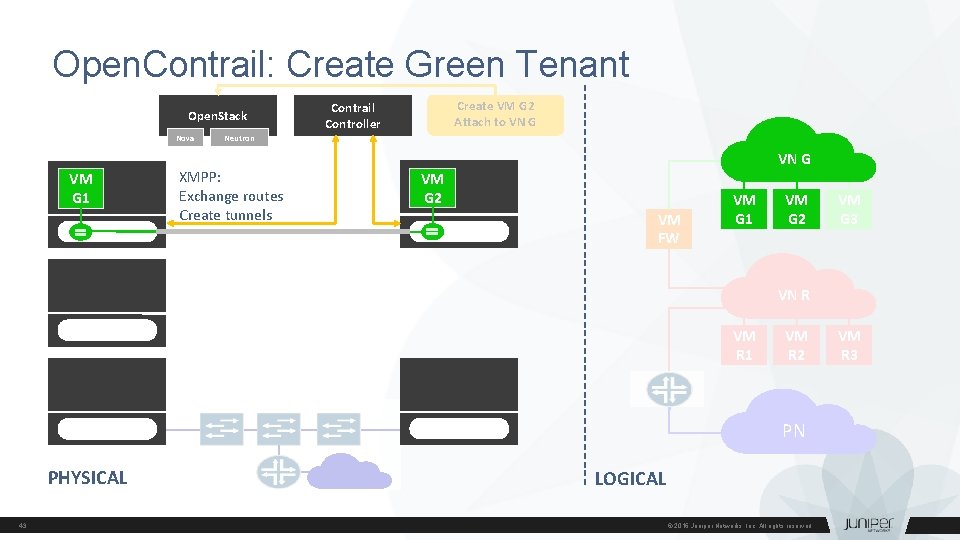
Open. Contrail: Create Green Tenant create virtual machine "g 2" Open. Stack Nova VM G 1 Create VM G 2 Attach to VN G Contrail Controller Neutron XMPP: Exchange routes Create tunnels VN G VM G 2 VM FW VM G 1 VM G 2 VM G 3 VN R VM R 1 VM R 2 VM R 3 PN PHYSICAL 43 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
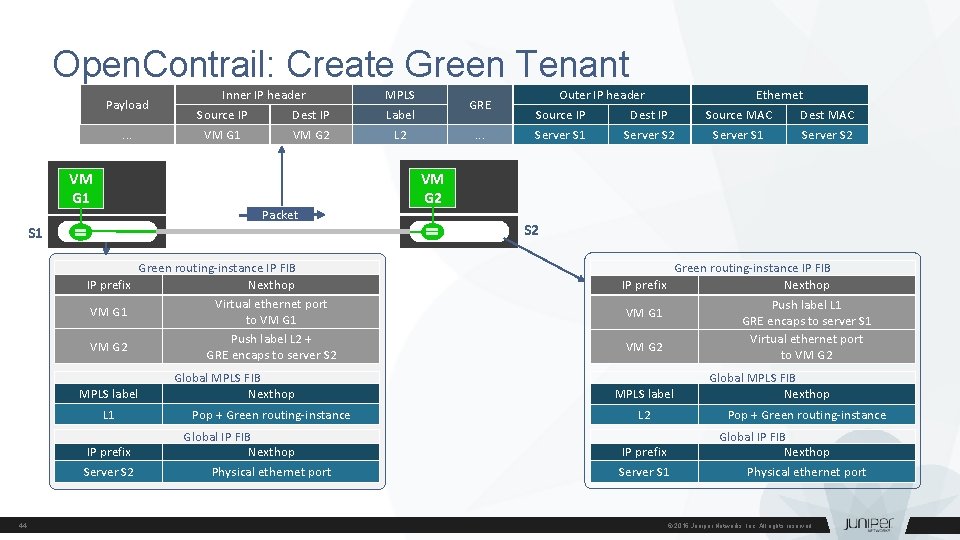
Open. Contrail: Create Green Tenant Inner IP header forwarding tables and encapsulation Payload. . . VM G 1 Source IP Dest IP MPLS Label VM G 1 VM G 2 L 2 Packet S 1 Green routing-instance IP FIB IP prefix Nexthop Virtual ethernet port VM G 1 to VM G 1 Push label L 2 + VM G 2 GRE encaps to server S 2 MPLS label L 1 IP prefix Server S 2 44 Global MPLS FIB Nexthop Pop + Green routing-instance Global IP FIB Nexthop Physical ethernet port GRE. . . Outer IP header Source IP Dest IP Server S 1 Server S 2 Ethernet Source MAC Dest MAC Server S 1 Server S 2 VM G 2 S 2 Green routing-instance IP FIB IP prefix Nexthop Push label L 1 VM G 1 GRE encaps to server S 1 Virtual ethernet port VM G 2 to VM G 2 MPLS label L 2 Global MPLS FIB Nexthop Pop + Green routing-instance IP prefix Server S 1 Global IP FIB Nexthop Physical ethernet port © 2016 Juniper Networks, Inc. All rights reserved.
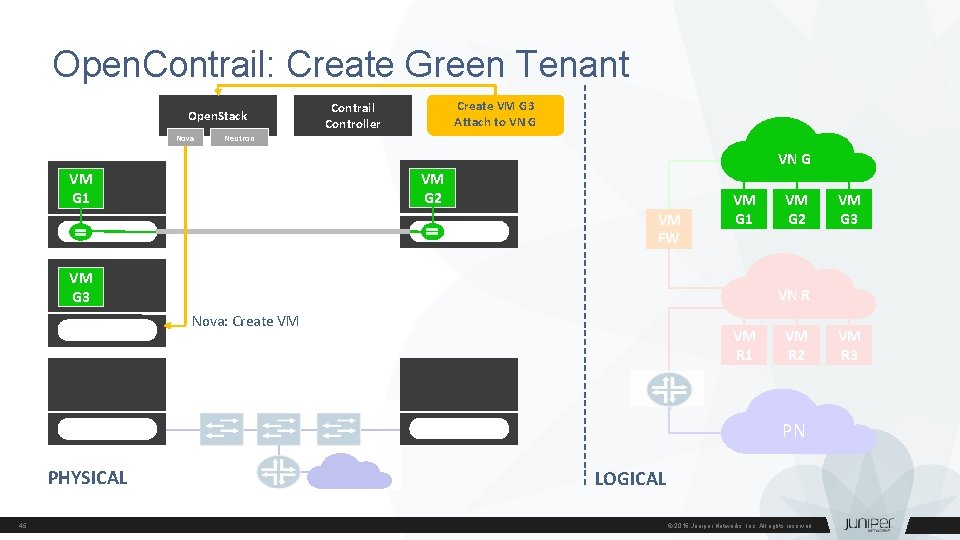
Open. Contrail: Create Green Tenant create virtual machine "g 3" Open. Stack Nova Create VM G 3 Attach to VN G Contrail Controller Neutron VN G VM G 2 VM G 1 VM FW VM G 1 VM G 3 VM G 2 VM G 3 VN R Nova: Create VM VM R 1 VM R 2 VM R 3 PN PHYSICAL 45 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
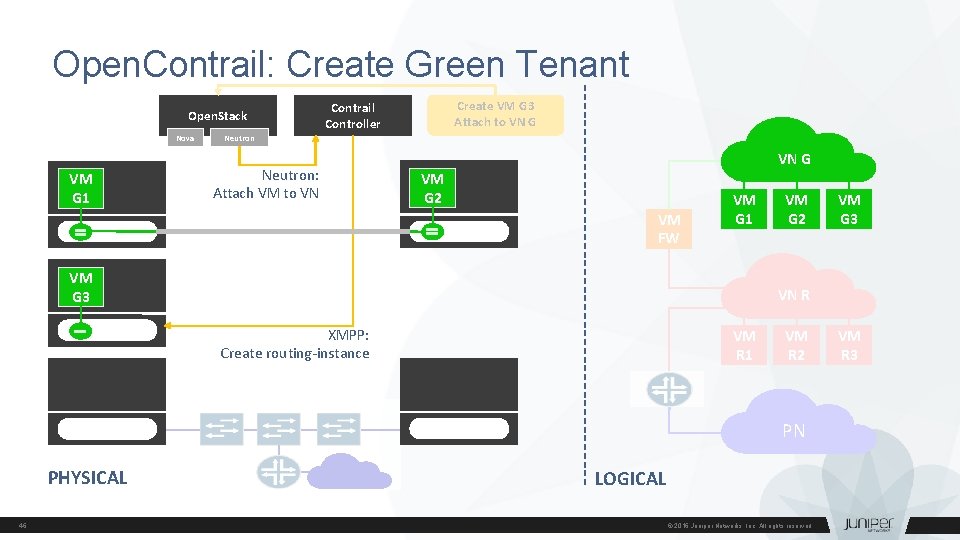
Open. Contrail: Create Green Tenant create virtual machine "g 3" Open. Stack Nova VM G 1 Create VM G 3 Attach to VN G Contrail Controller Neutron: Attach VM to VN VN G VM G 2 VM FW VM G 1 VM G 3 VM G 2 VM G 3 VN R XMPP: Create routing-instance VM R 1 VM R 2 VM R 3 PN PHYSICAL 46 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
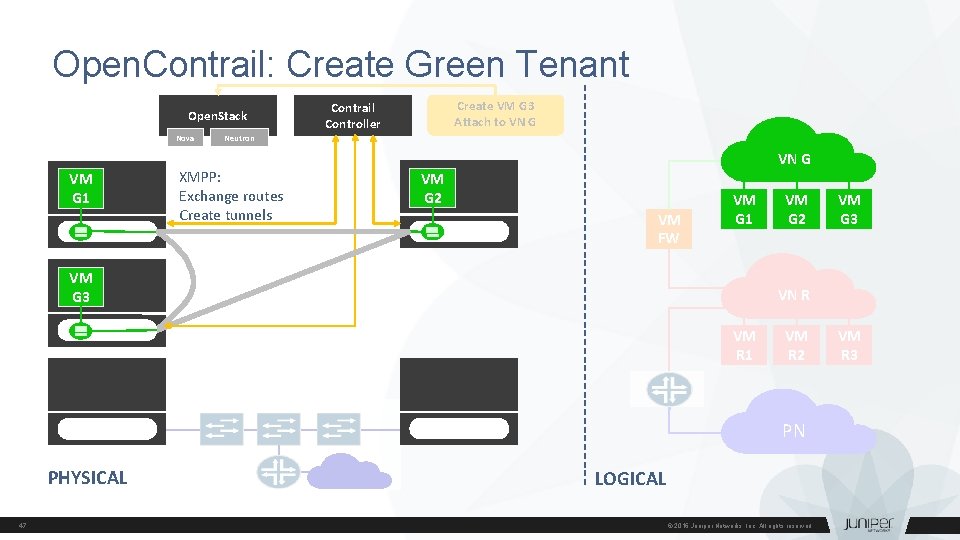
Open. Contrail: Create Green Tenant create virtual machine "g 3" Open. Stack Nova VM G 1 Create VM G 3 Attach to VN G Contrail Controller Neutron XMPP: Exchange routes Create tunnels VN G VM G 2 VM FW VM G 1 VM G 3 VM G 2 VM G 3 VN R VM R 1 VM R 2 VM R 3 PN PHYSICAL 47 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
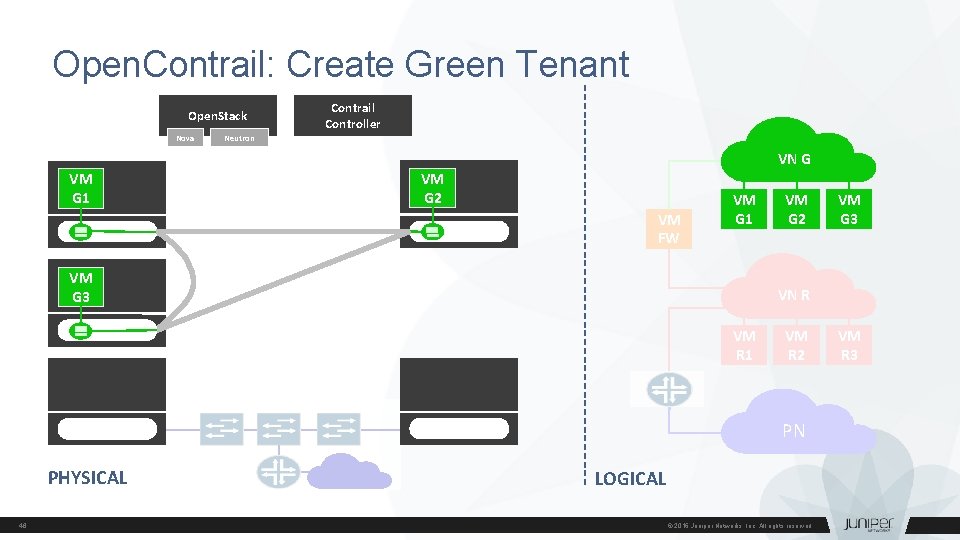
Open. Contrail: Create Green Tenant End state Open. Stack Nova Contrail Controller Neutron VN G VM G 1 VM G 2 VM FW VM G 1 VM G 3 VM G 2 VM G 3 VN R VM R 1 VM R 2 VM R 3 PN PHYSICAL 48 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
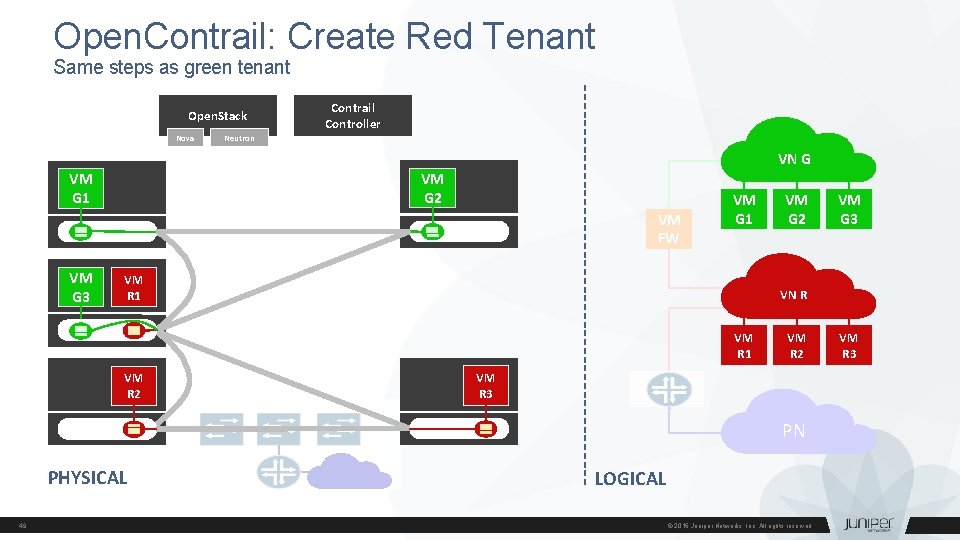
Open. Contrail: Create Red Tenant Same steps as green tenant Open. Stack Nova Contrail Controller Neutron VN G VM G 2 VM G 1 VM FW VM G 3 VM G 1 VM R 1 VM G 3 VN R VM R 1 VM R 2 VM G 2 VM R 3 PN PHYSICAL 49 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
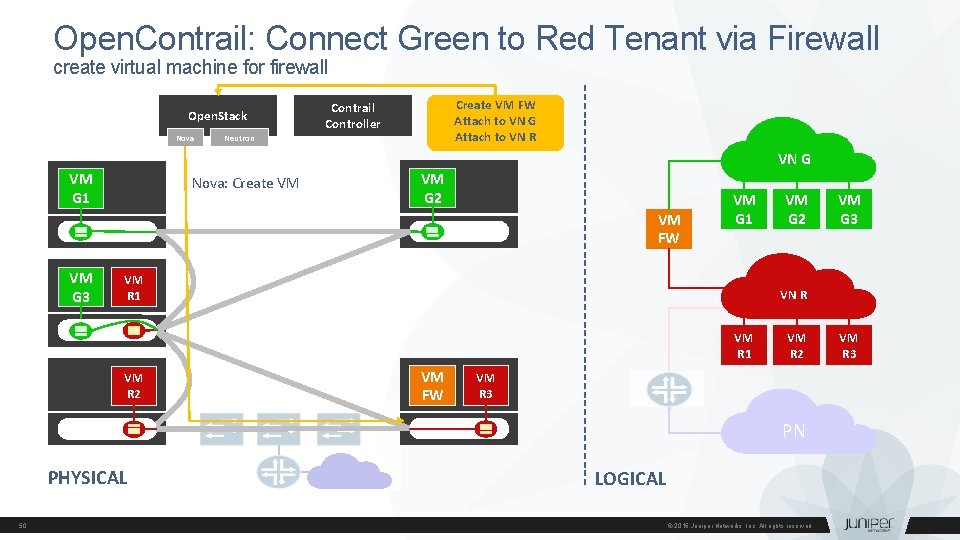
Open. Contrail: Connect Green to Red Tenant via Firewall create virtual machine for firewall Open. Stack Nova Create VM FW Attach to VN G Attach to VN R Contrail Controller Neutron VN G VM G 1 Nova: Create VM VM G 2 VM FW VM G 3 VM G 1 VM R 1 VM G 3 VN R VM R 1 VM R 2 VM G 2 VM FW VM R 2 VM R 3 PN PHYSICAL 50 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
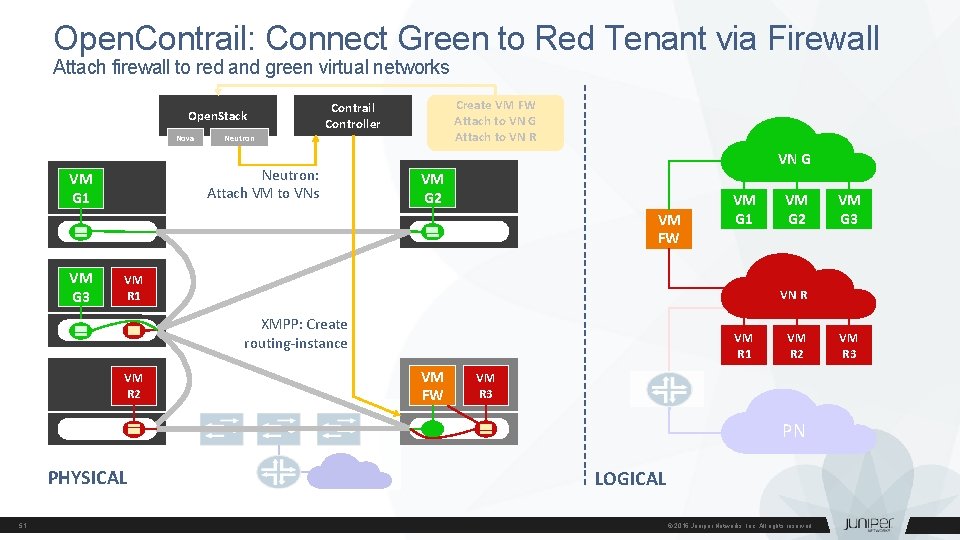
Open. Contrail: Connect Green to Red Tenant via Firewall Attach firewall to red and green virtual networks Open. Stack Nova Neutron: Attach VM to VNs VM G 1 Create VM FW Attach to VN G Attach to VN R Contrail Controller VN G VM G 2 VM FW VM G 3 VM G 1 VM R 1 VM G 3 VN R XMPP: Create routing-instance VM R 2 VM G 2 VM R 1 VM FW VM R 2 VM R 3 PN PHYSICAL 51 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
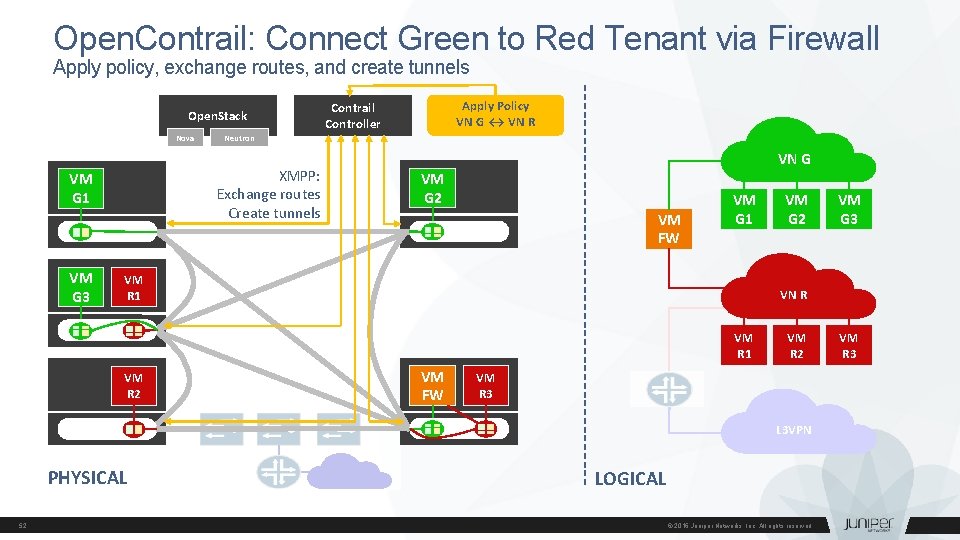
Open. Contrail: Connect Green to Red Tenant via Firewall Apply policy, exchange routes, and create tunnels Open. Stack Nova VM G 3 Neutron XMPP: Exchange routes Create tunnels VM G 1 Apply Policy VN G ↔ VN R Contrail Controller VN G VM G 2 VM FW VM G 1 VM R 1 VM G 3 VN R VM R 1 VM R 2 VM G 2 VM FW VM R 2 VM R 3 L 3 VPN PHYSICAL 52 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
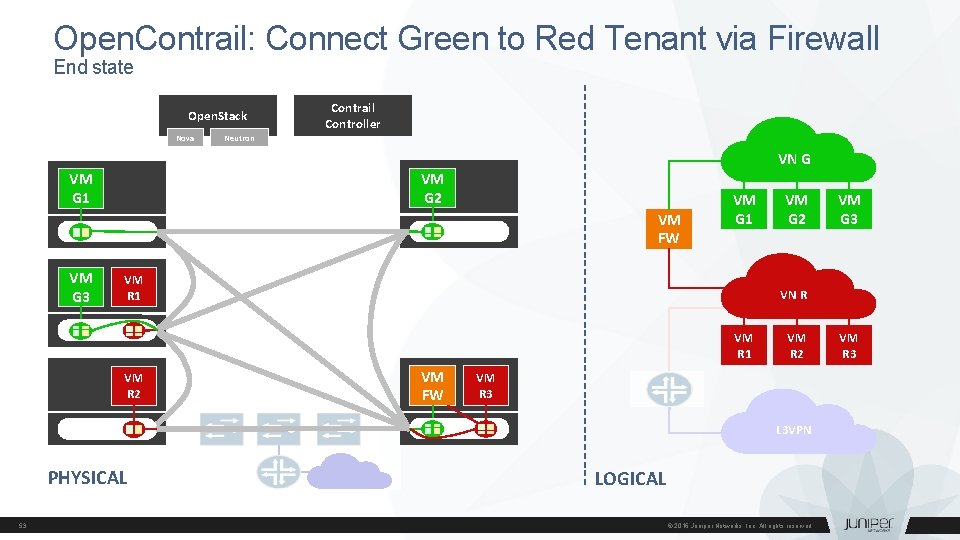
Open. Contrail: Connect Green to Red Tenant via Firewall End state Open. Stack Nova Contrail Controller Neutron VN G VM G 2 VM G 1 VM FW VM G 3 VM G 1 VM R 1 VM G 3 VN R VM R 1 VM R 2 VM G 2 VM FW VM R 2 VM R 3 L 3 VPN PHYSICAL 53 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
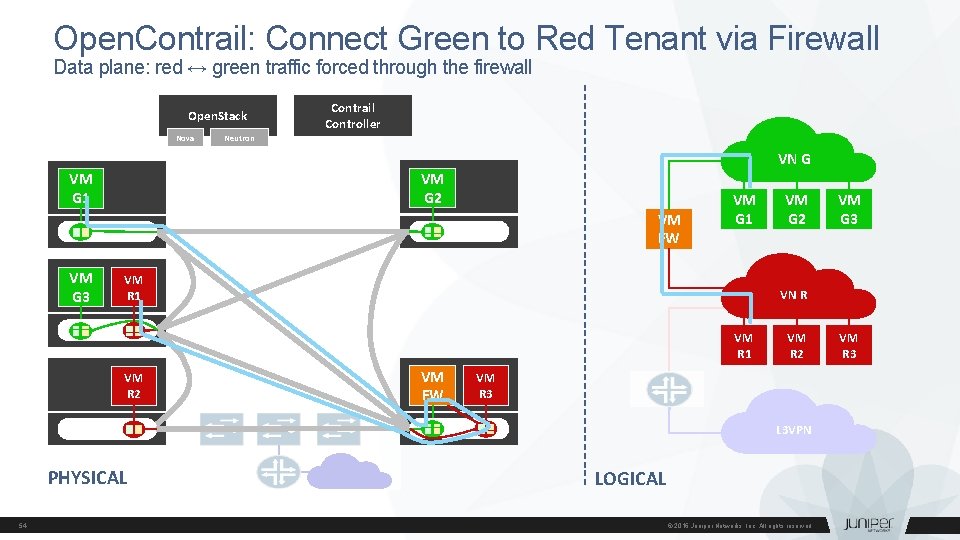
Open. Contrail: Connect Green to Red Tenant via Firewall Data plane: red ↔ green traffic forced through the firewall Open. Stack Nova Contrail Controller Neutron VN G VM G 2 VM G 1 VM FW VM G 3 VM G 1 VM R 1 VM G 3 VN R VM R 1 VM R 2 VM G 2 VM FW VM R 2 VM R 3 L 3 VPN PHYSICAL 54 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
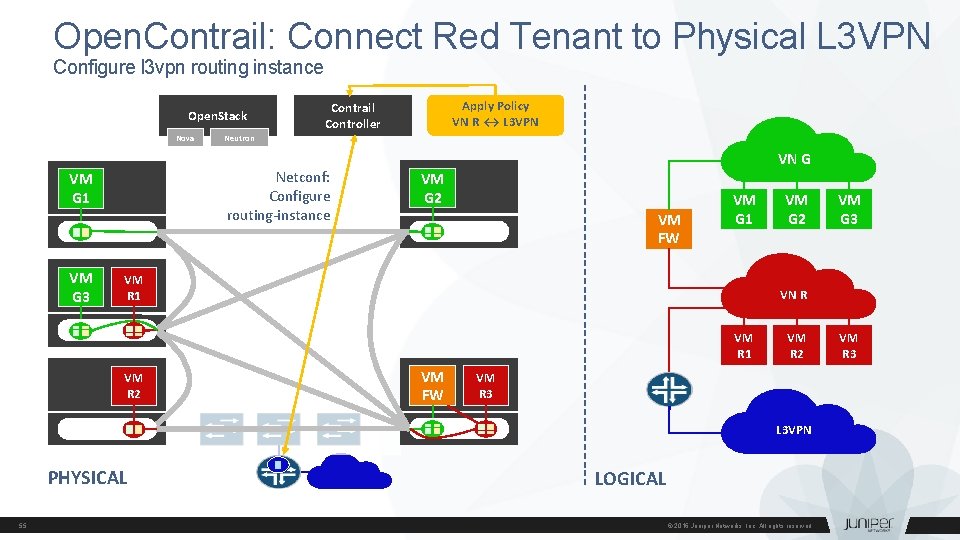
Open. Contrail: Connect Red Tenant to Physical L 3 VPN Configure l 3 vpn routing instance Open. Stack Nova VM G 3 Neutron Netconf: Configure routing-instance VM G 1 Apply Policy VN R ↔ L 3 VPN Contrail Controller VN G VM G 2 VM FW VM G 1 VM R 1 VM G 3 VN R VM R 1 VM R 2 VM G 2 VM FW VM R 2 VM R 3 L 3 VPN PHYSICAL 55 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
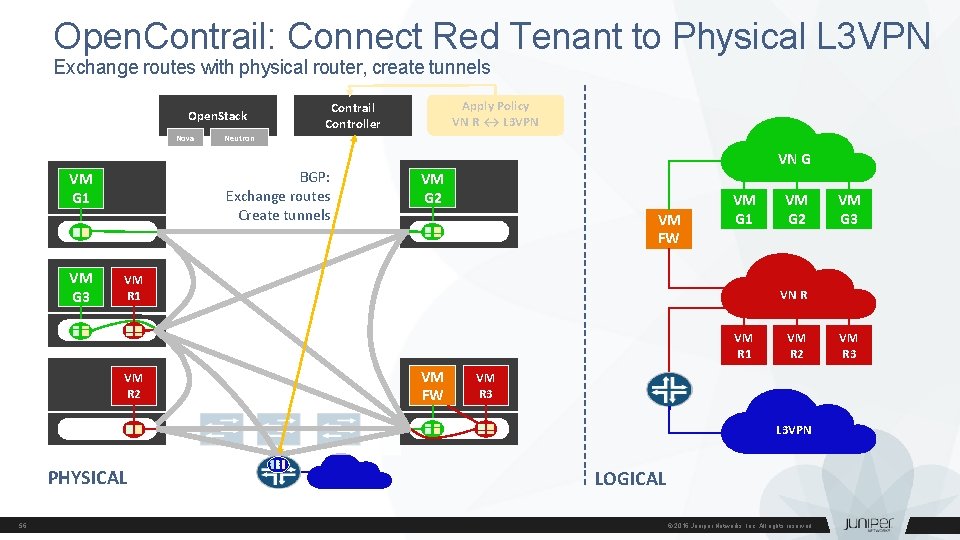
Open. Contrail: Connect Red Tenant to Physical L 3 VPN Exchange routes with physical router, create tunnels Open. Stack Nova VM G 3 Neutron BGP: Exchange routes Create tunnels VM G 1 Apply Policy VN R ↔ L 3 VPN Contrail Controller VN G VM G 2 VM FW VM G 1 VM R 1 VM G 3 VN R VM R 1 VM R 2 VM G 2 VM FW VM R 2 VM R 3 L 3 VPN PHYSICAL 56 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.
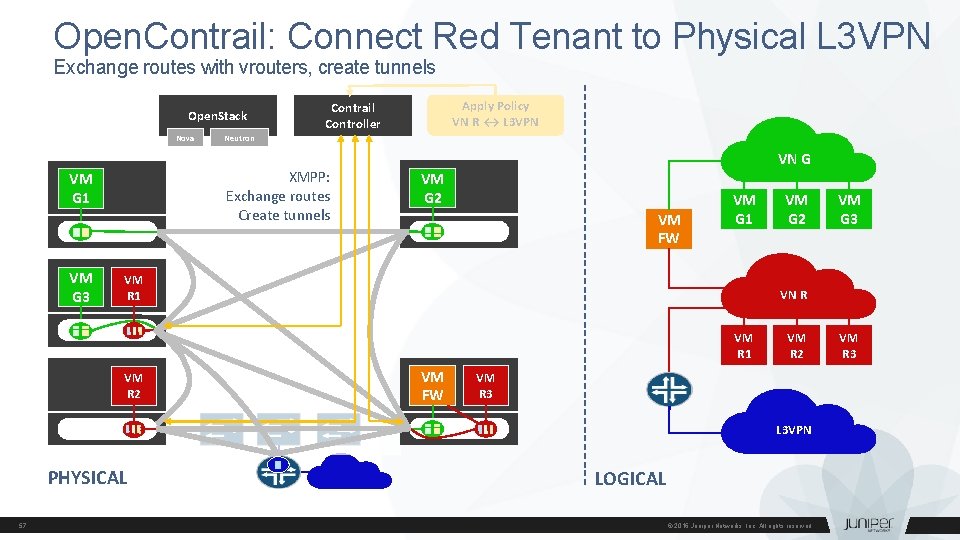
Open. Contrail: Connect Red Tenant to Physical L 3 VPN Exchange routes with vrouters, create tunnels Open. Stack Nova VM G 3 Neutron XMPP: Exchange routes Create tunnels VM G 1 Apply Policy VN R ↔ L 3 VPN Contrail Controller VN G VM G 2 VM FW VM G 1 VM R 1 VM G 3 VN R VM R 1 VM R 2 VM G 2 VM FW VM R 2 VM R 3 L 3 VPN PHYSICAL 57 LOGICAL © 2016 Juniper Networks, Inc. All rights reserved.

North. Star
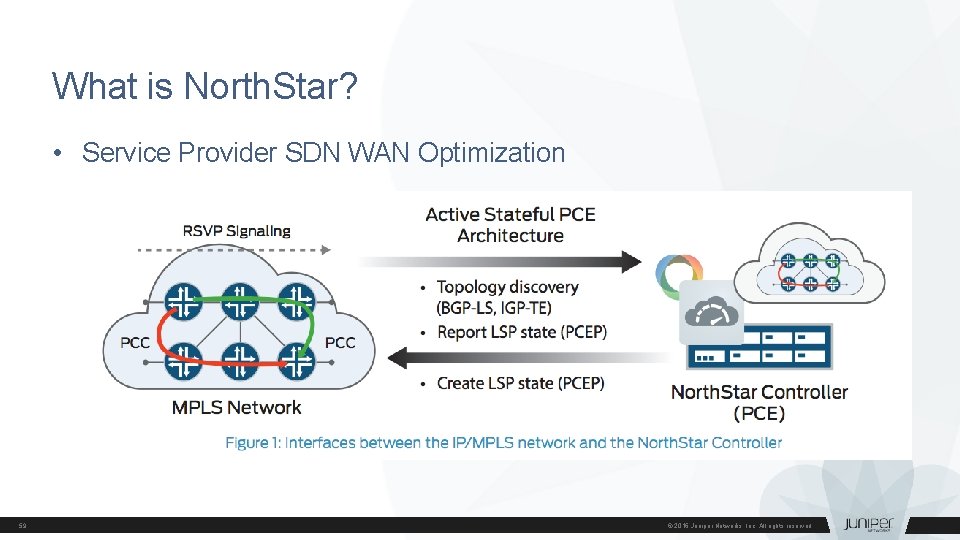
What is North. Star? • Service Provider SDN WAN Optimization 59 © 2016 Juniper Networks, Inc. All rights reserved.
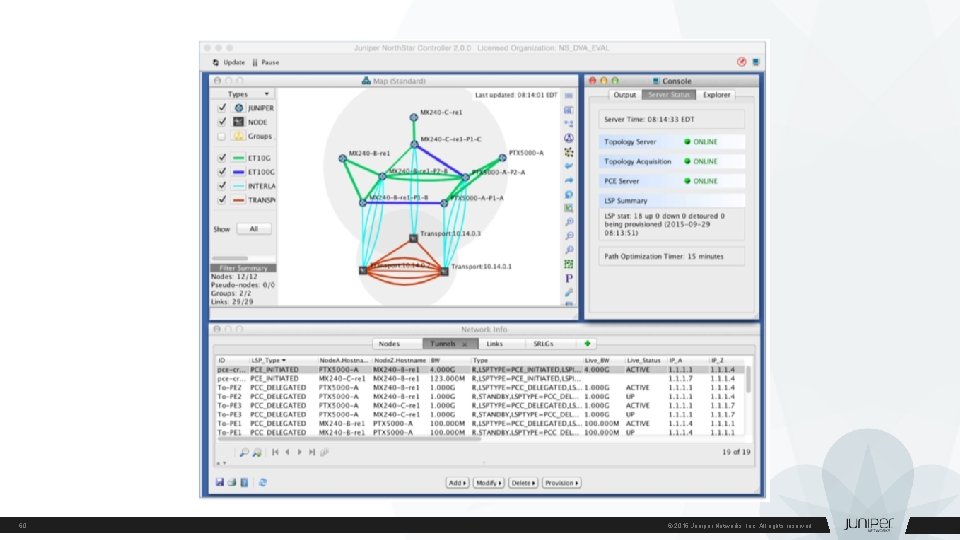
60 © 2016 Juniper Networks, Inc. All rights reserved.

NFX 250 – NFV Appliance
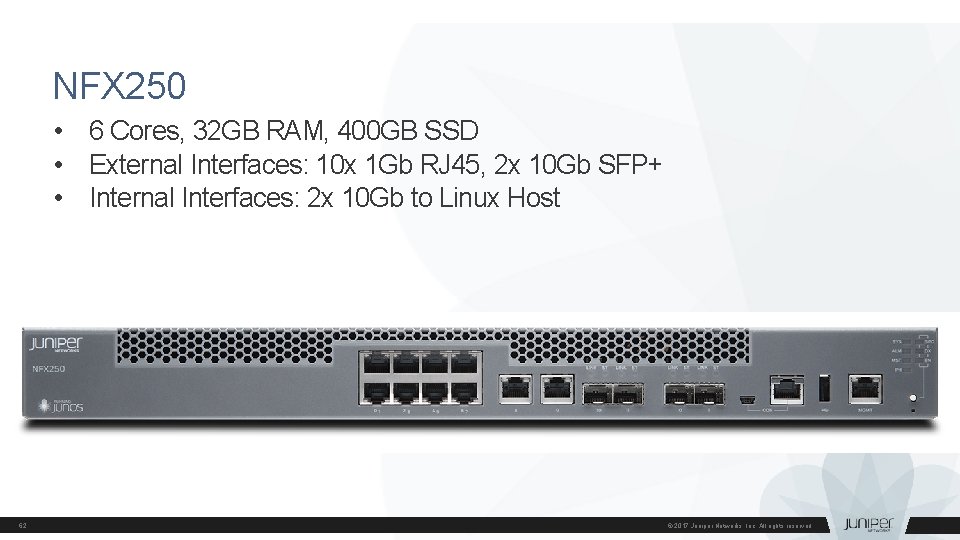
NFX 250 • 6 Cores, 32 GB RAM, 400 GB SSD • External Interfaces: 10 x 1 Gb RJ 45, 2 x 10 Gb SFP+ • Internal Interfaces: 2 x 10 Gb to Linux Host 62 © 2017 Juniper Networks, Inc. All rights reserved.
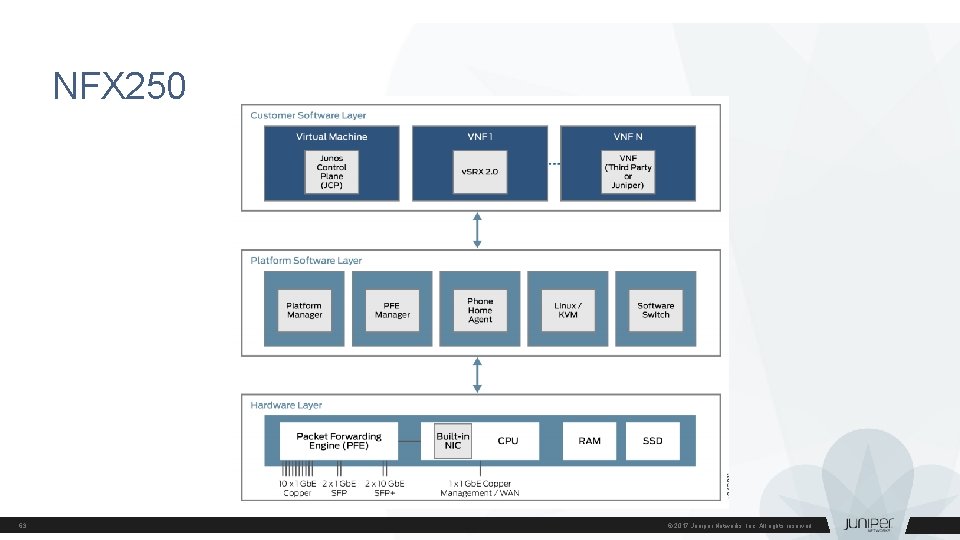
NFX 250 63 © 2017 Juniper Networks, Inc. All rights reserved.
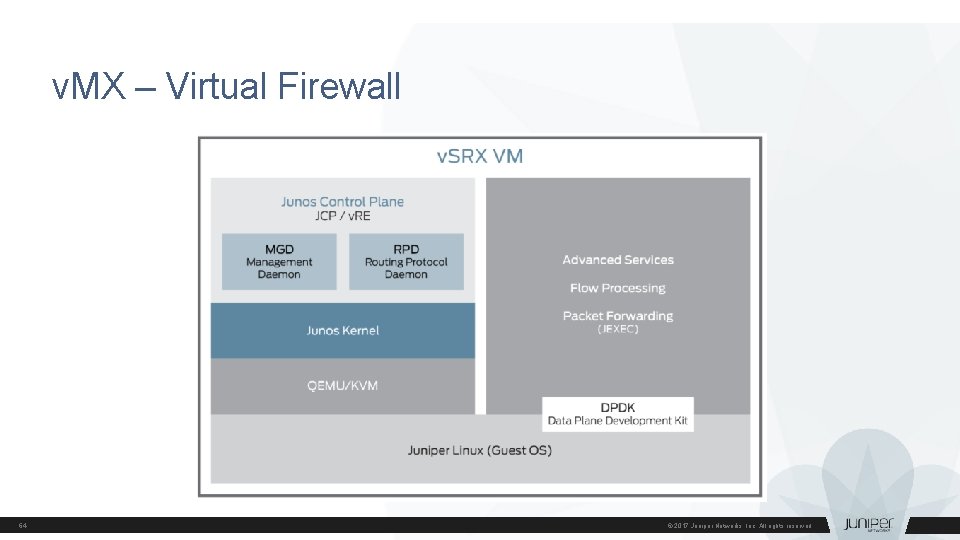
v. MX – Virtual Firewall 64 © 2017 Juniper Networks, Inc. All rights reserved.
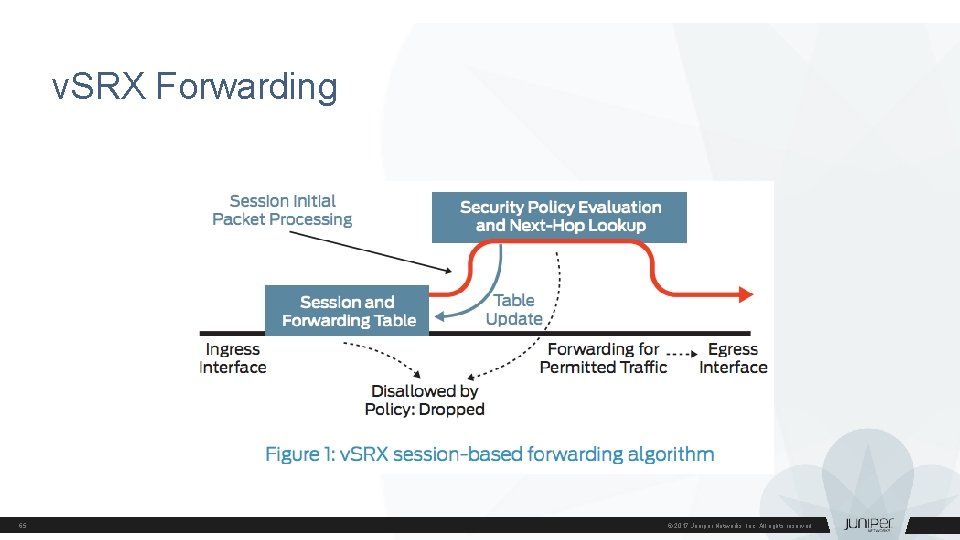
v. SRX Forwarding 65 © 2017 Juniper Networks, Inc. All rights reserved.
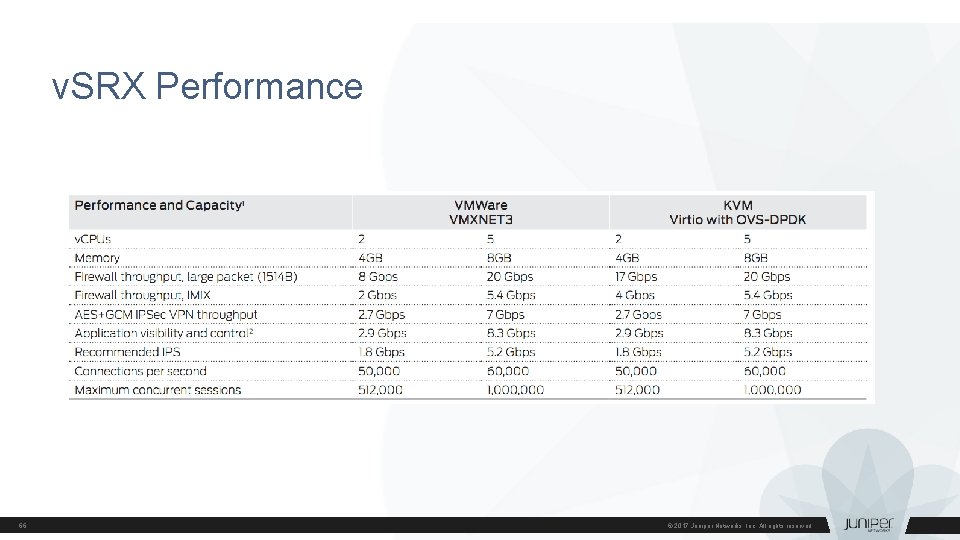
v. SRX Performance 66 © 2017 Juniper Networks, Inc. All rights reserved.
- Slides: 66