Identity Based Networking Terena Rhodes June 04 Eric
Identity Based Networking Terena Rhodes, June 04 Eric Marin EMEA Consulting Engineer Cisco Systems Emarin Terena IBNS © 2004 Cisco Systems, Inc. All rights reserved. 1
Port-Based Network Authentication • Have the client (a user or a device) request a service —in this case access to the network • Verify the client’s claim of identity—authentication • Reference the configured policies for the requesting client • Grant or deny the services as per the policy— authorization Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 2
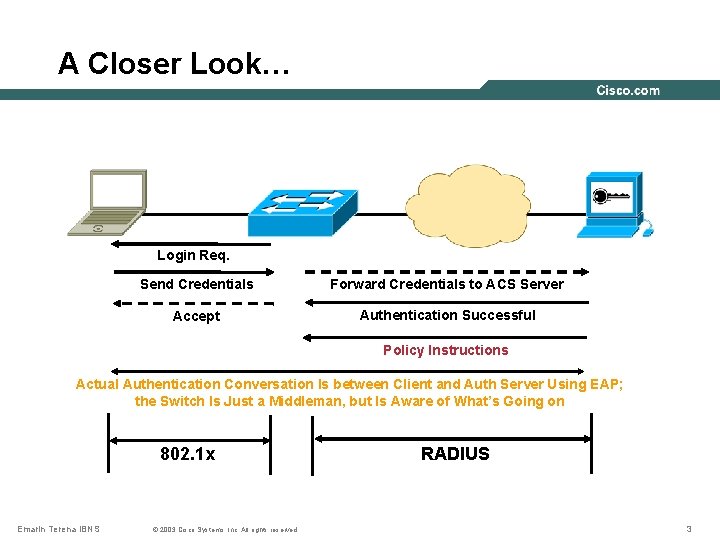
A Closer Look… Login Req. Send Credentials Forward Credentials to ACS Server Accept Authentication Successful Policy Instructions Actual Authentication Conversation Is between Client and Auth Server Using EAP; the Switch Is Just a Middleman, but Is Aware of What’s Going on 802. 1 x Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. RADIUS 3
Agenda • Protocols and Mechanisms behind 802. 1 x • Identity-Based Policy Enforcement • Understanding Microsoft Environments Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 4
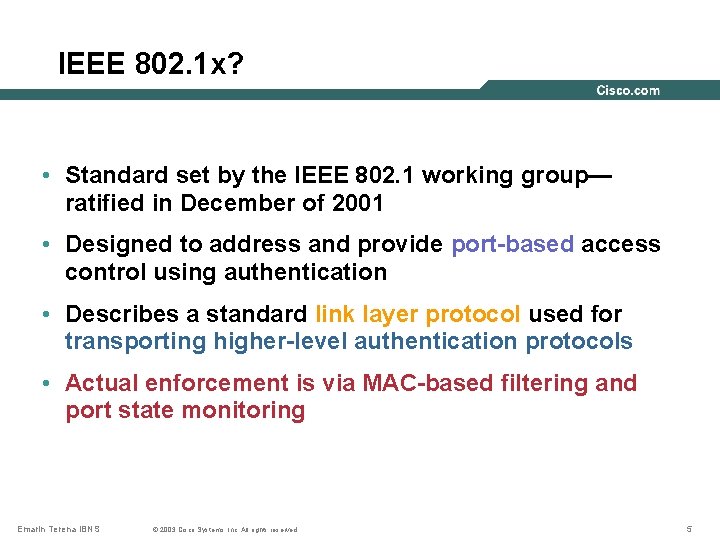
IEEE 802. 1 x? • Standard set by the IEEE 802. 1 working group— ratified in December of 2001 • Designed to address and provide port-based access control using authentication • Describes a standard link layer protocol used for transporting higher-level authentication protocols • Actual enforcement is via MAC-based filtering and port state monitoring Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 5
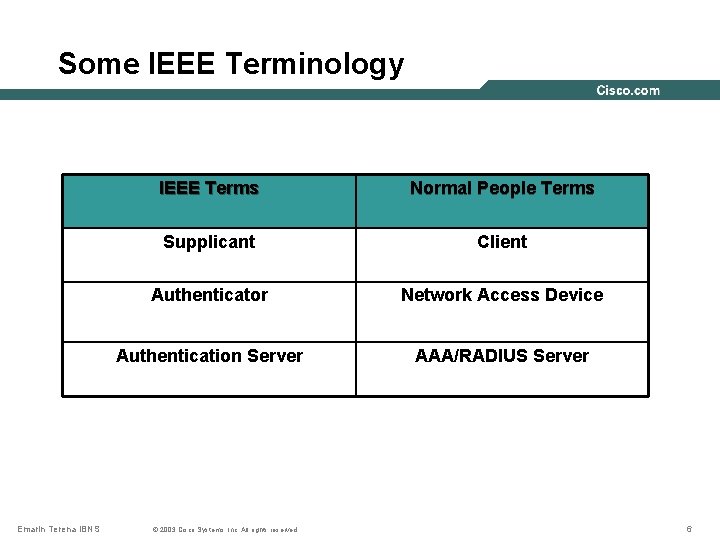
Some IEEE Terminology Emarin Terena IBNS IEEE Terms Normal People Terms Supplicant Client Authenticator Network Access Device Authentication Server AAA/RADIUS Server © 2003 Cisco Systems, Inc. All rights reserved. 6
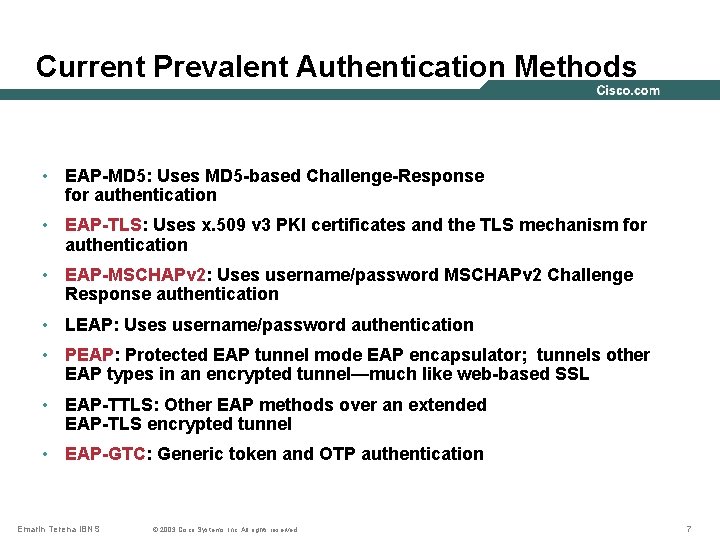
Current Prevalent Authentication Methods • EAP-MD 5: Uses MD 5 -based Challenge-Response for authentication • EAP-TLS: Uses x. 509 v 3 PKI certificates and the TLS mechanism for authentication • EAP-MSCHAPv 2: Uses username/password MSCHAPv 2 Challenge Response authentication • LEAP: Uses username/password authentication • PEAP: Protected EAP tunnel mode EAP encapsulator; tunnels other EAP types in an encrypted tunnel—much like web-based SSL • EAP-TTLS: Other EAP methods over an extended EAP-TLS encrypted tunnel • EAP-GTC: Generic token and OTP authentication Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 7

Agenda • Protocols and Mechanisms behind 802. 1 x • Identity-Based Policy Enforcement • Understanding Microsoft Environments Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 8
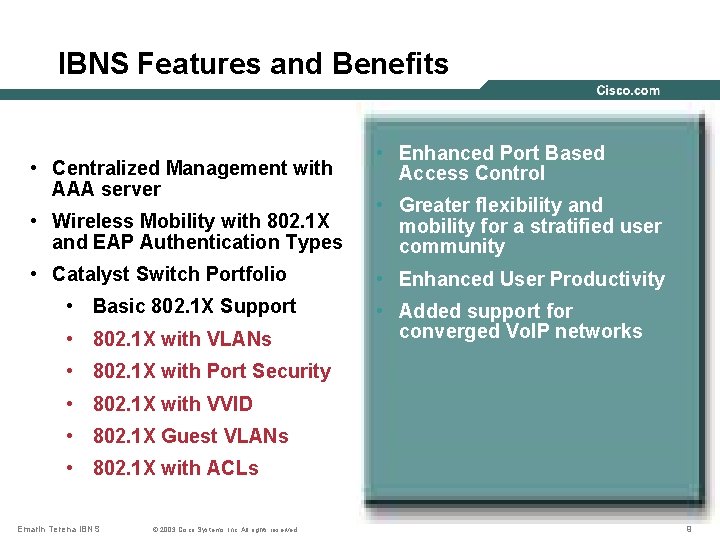
IBNS Features and Benefits • Centralized Management with AAA server • Enhanced Port Based Access Control • Wireless Mobility with 802. 1 X and EAP Authentication Types • Greater flexibility and mobility for a stratified user community • Catalyst Switch Portfolio • Enhanced User Productivity • Basic 802. 1 X Support • 802. 1 X with VLANs • Added support for converged Vo. IP networks • 802. 1 X with Port Security • 802. 1 X with VVID • 802. 1 X Guest VLANs • 802. 1 X with ACLs Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 9
Dynamic VLAN Assignment • Dynamic VLAN assignment based on identity • Allows VLAN assignment, by group, or individual, at the time of authentication • VLANs assigned by name—allows for more flexible VLAN management • Allows VLAN policies to be applied to groups of users (i. e. , VLAN Qo. S, VLAN ACLs, etc. ) Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 10
Dynamic VLAN Mechanism • RADIUS AV-Pairs used to send back VLAN configuration information to authenticator. • AV-Pair usage for VLANs is IEEE specified in the 802. 1 x standard. • AV-Pairs used – all are IETF standard: [64] Tunnel-Type – “VLAN” (13) [65] Tunnel-Medium-Type – “ 802” (6) [81] Tunnel-Private-Group-ID - <VLAN name> Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 11
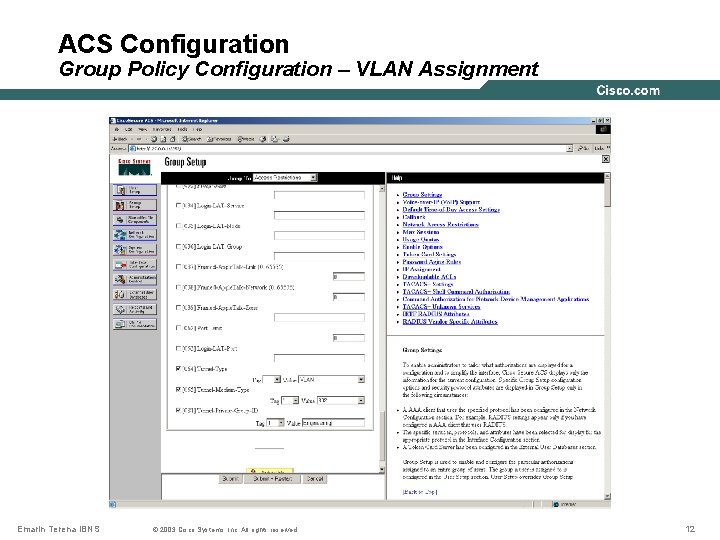
ACS Configuration Group Policy Configuration – VLAN Assignment Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 12
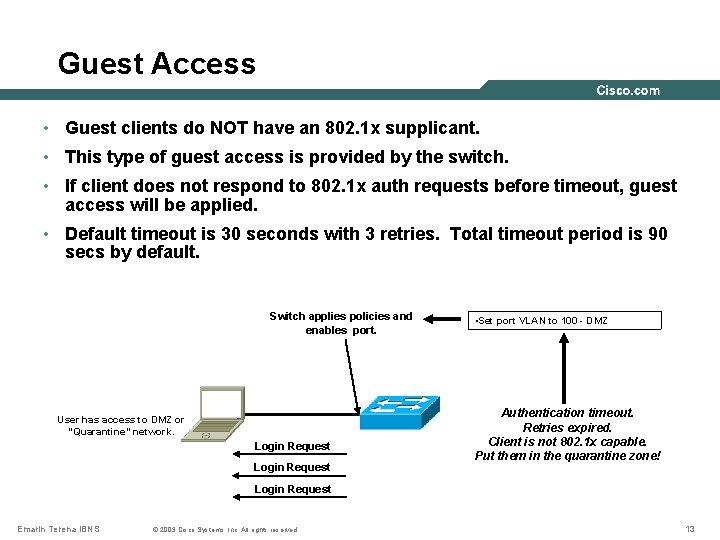
Guest Access • Guest clients do NOT have an 802. 1 x supplicant. • This type of guest access is provided by the switch. • If client does not respond to 802. 1 x auth requests before timeout, guest access will be applied. • Default timeout is 30 seconds with 3 retries. Total timeout period is 90 secs by default. Switch applies policies and enables port. User has access to DMZ or “Quarantine” network. Login Request • Set port VLAN to 100 - DMZ Authentication timeout. Retries expired. Client is not 802. 1 x capable. Put them in the quarantine zone! Login Request Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 13
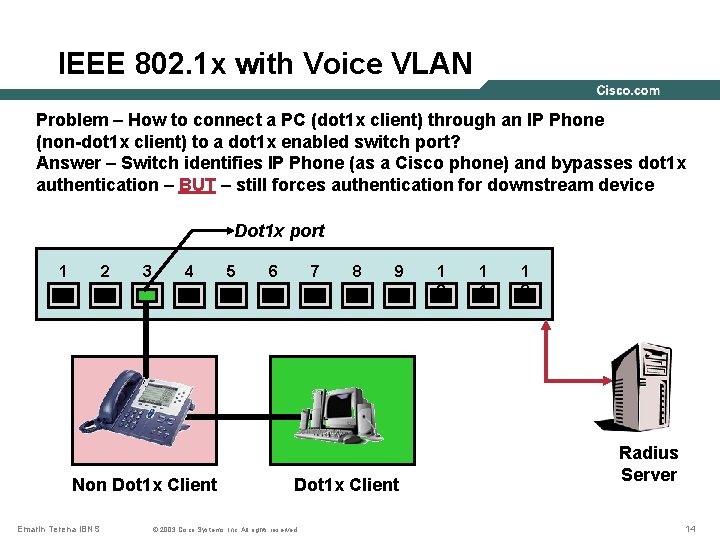
IEEE 802. 1 x with Voice VLAN Problem – How to connect a PC (dot 1 x client) through an IP Phone (non-dot 1 x client) to a dot 1 x enabled switch port? Answer – Switch identifies IP Phone (as a Cisco phone) and bypasses dot 1 x authentication – BUT – still forces authentication for downstream device Dot 1 x port 1 2 3 4 Non Dot 1 x Client Emarin Terena IBNS 5 6 7 8 9 Dot 1 x Client © 2003 Cisco Systems, Inc. All rights reserved. 1 0 1 1 1 2 Radius Server 14
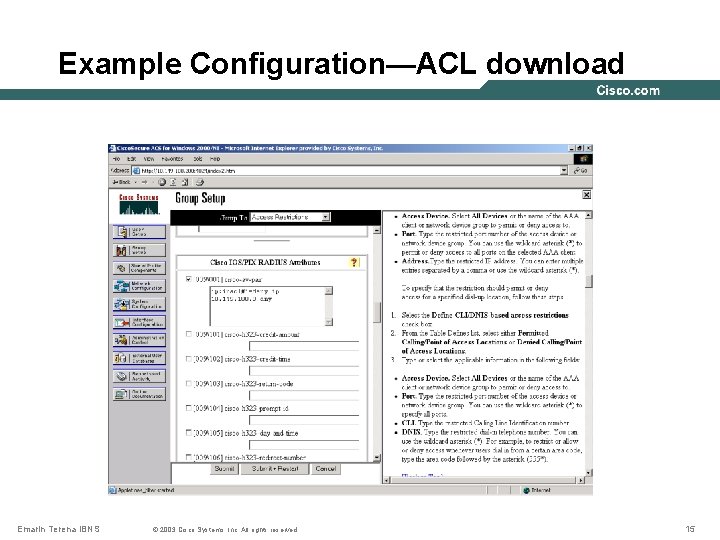
Example Configuration—ACL download Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 15
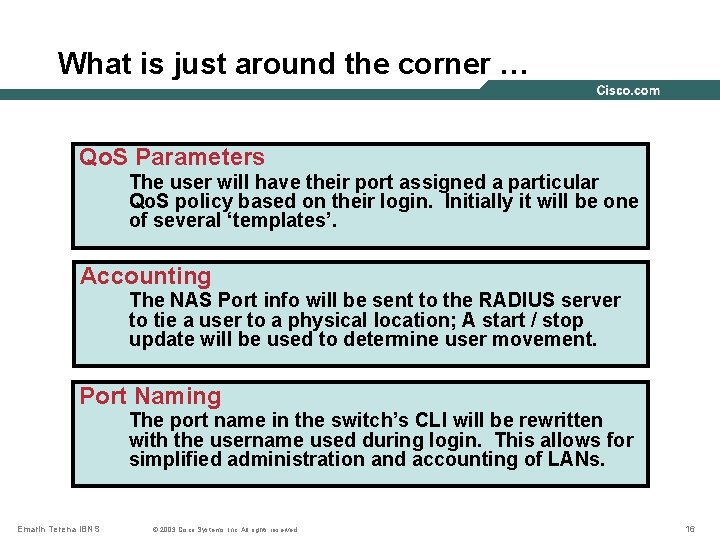
What is just around the corner … Qo. S Parameters The user will have their port assigned a particular Qo. S policy based on their login. Initially it will be one of several ‘templates’. Accounting The NAS Port info will be sent to the RADIUS server to tie a user to a physical location; A start / stop update will be used to determine user movement. Port Naming The port name in the switch’s CLI will be rewritten with the username used during login. This allows for simplified administration and accounting of LANs. Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 16
Agenda • Protocols and Mechanisms behind 802. 1 x • Identity-Based Policy Enforcement • Understanding Microsoft Environments Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 17
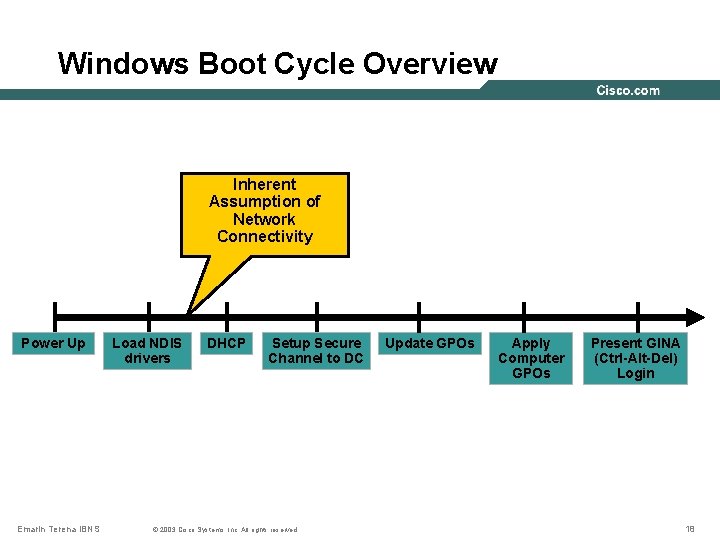
Windows Boot Cycle Overview Inherent Assumption of Network Connectivity Power Up Emarin Terena IBNS Load NDIS drivers DHCP Setup Secure Channel to DC © 2003 Cisco Systems, Inc. All rights reserved. Update GPOs Apply Computer GPOs Present GINA (Ctrl-Alt-Del) Login 18
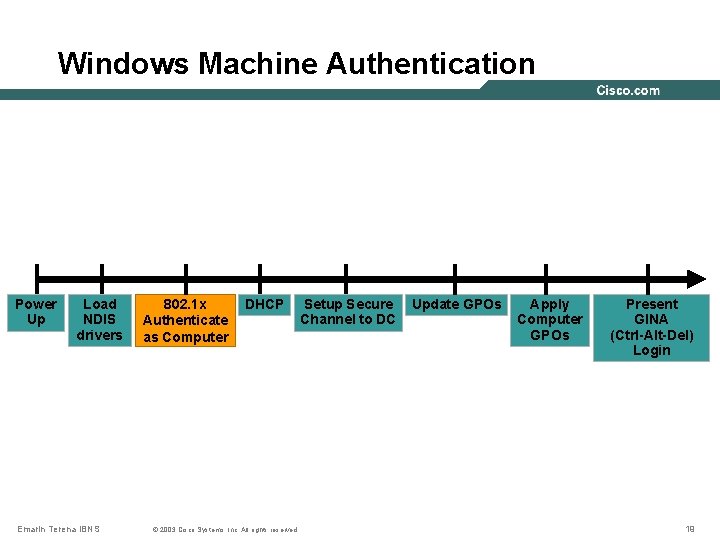
Windows Machine Authentication Power Up Load NDIS drivers Emarin Terena IBNS 802. 1 x Authenticate as Computer DHCP © 2003 Cisco Systems, Inc. All rights reserved. Setup Secure Channel to DC Update GPOs Apply Computer GPOs Present GINA (Ctrl-Alt-Del) Login 19
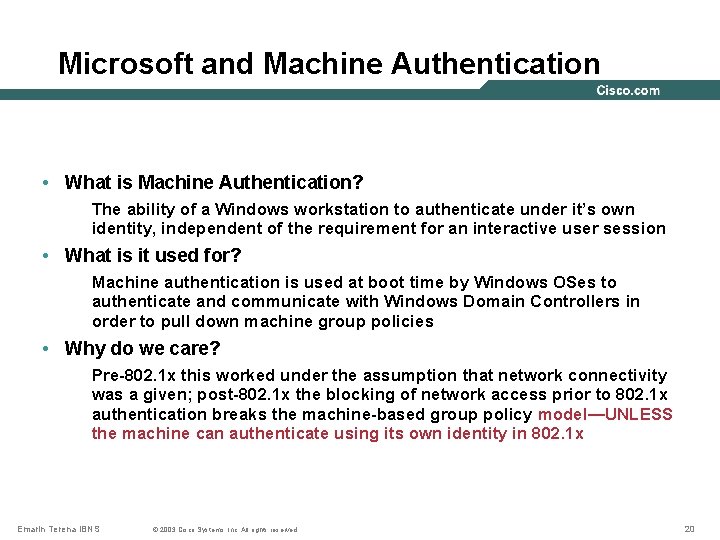
Microsoft and Machine Authentication • What is Machine Authentication? The ability of a Windows workstation to authenticate under it’s own identity, independent of the requirement for an interactive user session • What is it used for? Machine authentication is used at boot time by Windows OSes to authenticate and communicate with Windows Domain Controllers in order to pull down machine group policies • Why do we care? Pre-802. 1 x this worked under the assumption that network connectivity was a given; post-802. 1 x the blocking of network access prior to 802. 1 x authentication breaks the machine-based group policy model—UNLESS the machine can authenticate using its own identity in 802. 1 x Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 20
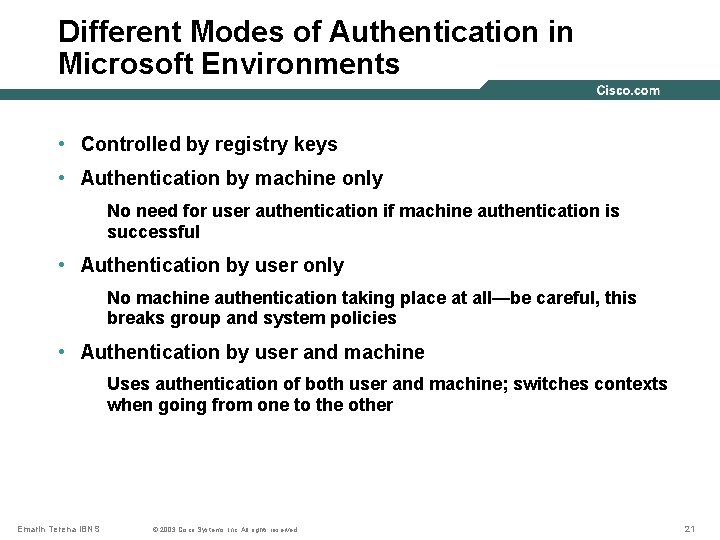
Different Modes of Authentication in Microsoft Environments • Controlled by registry keys • Authentication by machine only No need for user authentication if machine authentication is successful • Authentication by user only No machine authentication taking place at all—be careful, this breaks group and system policies • Authentication by user and machine Uses authentication of both user and machine; switches contexts when going from one to the other Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 21
Microsoft Issues with DHCP • DHCP is a parallel event, independent of 802. 1 x authentication • With wired interfaces a successful 802. 1 x authentication DOES NOT force an DHCP address discovery (no media-connect signal) • This produces a problem if not properly planned • DHCP starts once interface comes up • If 802. 1 x authentication takes too long, DHCP may time out… • Host may also be put into a different VLAN upon 802. 1 X authentication Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 22
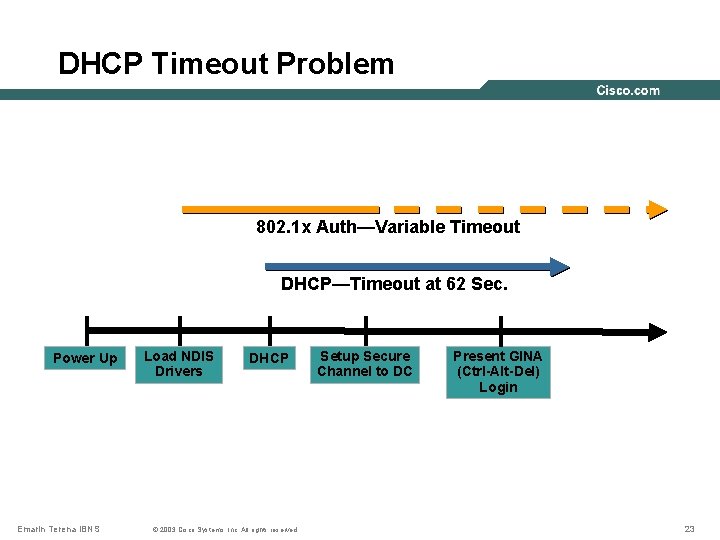
DHCP Timeout Problem 802. 1 x Auth—Variable Timeout DHCP—Timeout at 62 Sec. Power Up Emarin Terena IBNS Load NDIS Drivers DHCP © 2003 Cisco Systems, Inc. All rights reserved. Setup Secure Channel to DC Present GINA (Ctrl-Alt-Del) Login 23
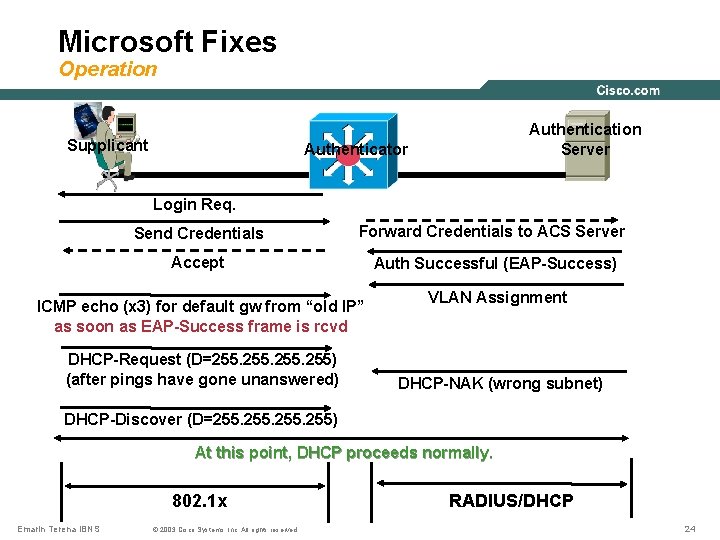
Microsoft Fixes Operation Supplicant Authentication Server Authenticator Login Req. Send Credentials Forward Credentials to ACS Server Accept Auth Successful (EAP-Success) ICMP echo (x 3) for default gw from “old IP” as soon as EAP-Success frame is rcvd DHCP-Request (D=255. 255) (after pings have gone unanswered) VLAN Assignment DHCP-NAK (wrong subnet) DHCP-Discover (D=255. 255) At this point, DHCP proceeds normally. 802. 1 x Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. RADIUS/DHCP 24
Conclusion • Situation gets better and better on the supplicant side • Authorization part of AAA gives IBN great extensibility • 802. 1 X being deployed more & more on switches • Also present on Cisco IOS routers combined with IPsec VPN access Emarin Terena IBNS © 2003 Cisco Systems, Inc. All rights reserved. 25
Questions? Emarin Terena IBNS © 2002, Cisco Systems, Inc. All rights reserved. © 2003 Cisco Systems, Inc. All rights reserved. 26
Emarin Terena IBNS © 2003, Cisco Systems, Inc. All rights reserved. © 2003 Cisco Systems, Inc. All rights reserved. 27
- Slides: 27