SCHOOL OF COMPUTING Cloud Vulnerability Scanner Anil Kumar
SCHOOL OF COMPUTING Cloud Vulnerability Scanner Anil Kumar Konasale Krishna Robert Ricci 1
SCHOOL OF COMPUTING Introduction Motivation Architecture and Design Evaluation and Results Limitations Future work 2
SCHOOL OF COMPUTING Introduction Motivation Architecture and Design Evaluation and Results Limitations Future work 3
Vulnerabilities. SCHOOL are OF COMPUTING everywhere!!! 4
SCHOOL OF COMPUTING 5
SCHOOL OF COMPUTING Introduction • It is important to identify and assess the vulnerabilities • Vulnerability Scanner Software application that assesses security vulnerabilities in networks or host systems and produces a set of scan results. 6
SCHOOL OF COMPUTING Vulnerability Assessment Known vulnerabilities in well known software 7
SCHOOL OF COMPUTING Introduction Motivation Architecture and Design Evaluation and Results Limitations Future work 8
SCHOOL OF COMPUTING Motivation Existing Vulnerability Scanners are • Not Accurate – False Negatives and False Positives • Disruptive – Service break-down, System crash etc… 9
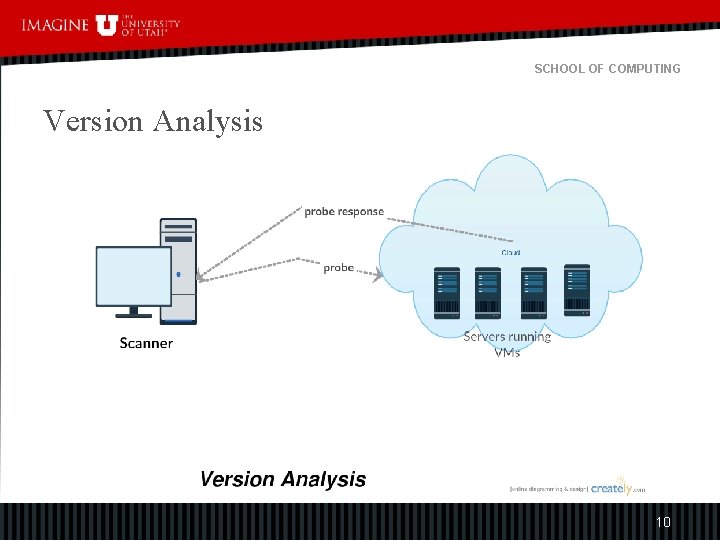
SCHOOL OF COMPUTING Version Analysis 10
SCHOOL OF COMPUTING Motivation • Version Analysis – System library versions are not revealed – Reveals only high-level protocol version, not implementation version – Version info is not accurate • 389/tcp open ldap Open. LDAP 2. 2. X - 2. 3. X False Positives 11
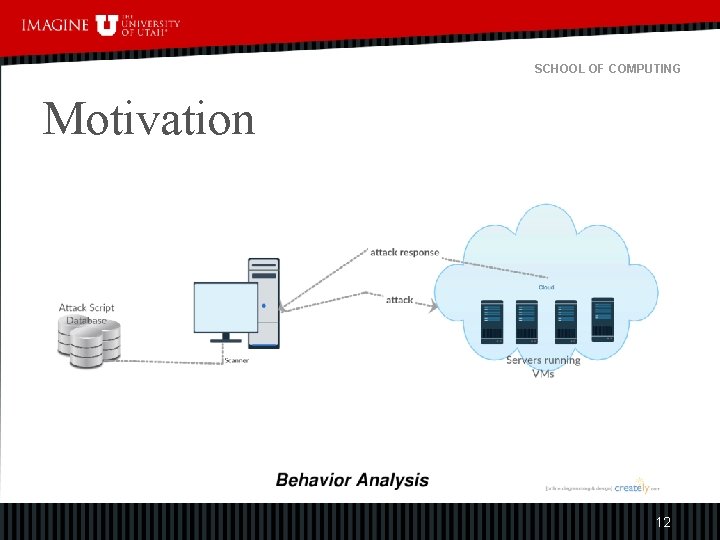
SCHOOL OF COMPUTING Motivation 12
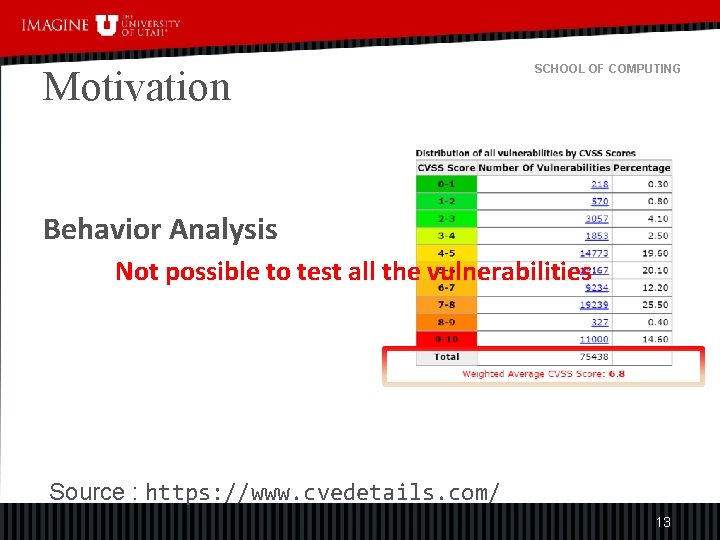
Motivation SCHOOL OF COMPUTING Behavior Analysis Not possible to test all the vulnerabilities Source : https: //www. cvedetails. com/ 13
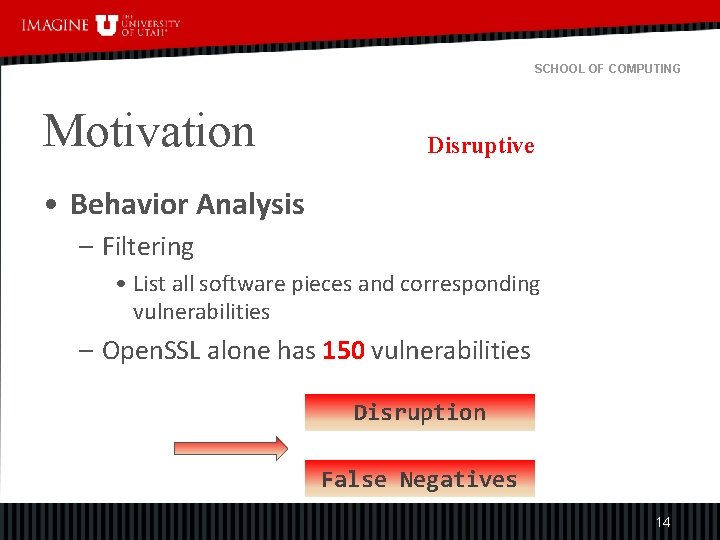
SCHOOL OF COMPUTING Motivation Disruptive • Behavior Analysis – Filtering • List all software pieces and corresponding vulnerabilities – Open. SSL alone has 150 vulnerabilities Disruption False Negatives 14
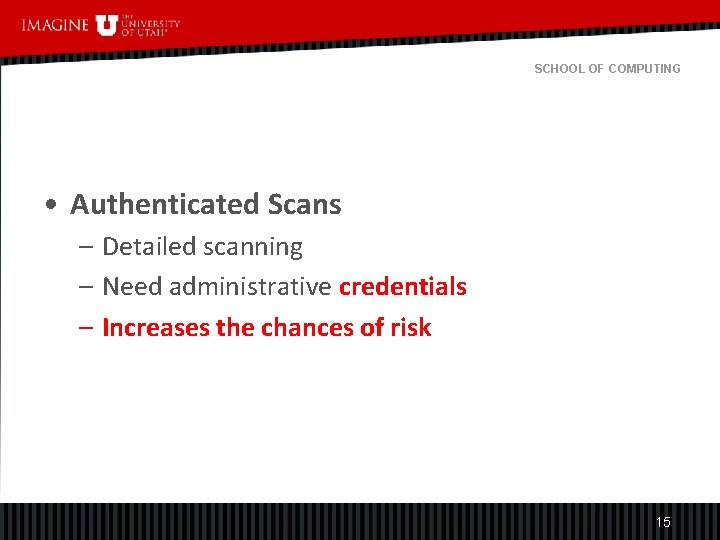
SCHOOL OF COMPUTING • Authenticated Scans – Detailed scanning – Need administrative credentials – Increases the chances of risk 15
SCHOOL OF COMPUTING Cloud Vulnerability Scanner(Vmi. CVS) A novel Virtual Machine Introspection(VMI) based Cloud Vulnerability Assessment Scanner 16
SCHOOL OF COMPUTING Vmi. CVS Non-disruptive And Accurate 17
SCHOOL OF COMPUTING Introduction Motivation Architecture and Design Evaluation and Results Limitations Future work 18
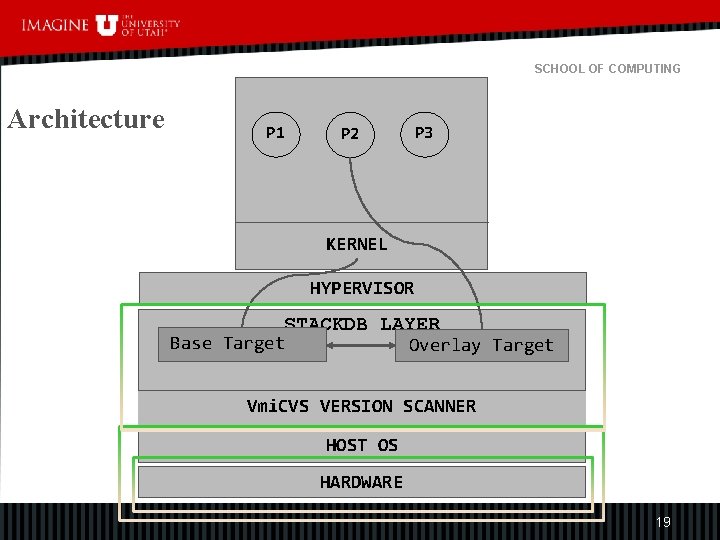
SCHOOL OF COMPUTING Architecture P 1 P 3 P 2 KERNEL HYPERVISOR STACKDB LAYER Base Target Overlay Target Vmi. CVS VERSION SCANNER HOST OS HARDWARE 19
SCHOOL OF COMPUTING Stackdb A VMI based debugging library to Monitor and control system through different targets 20
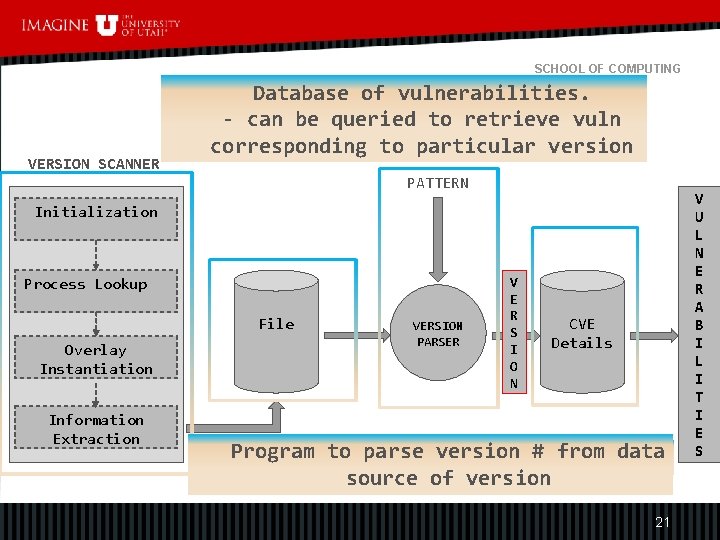
SCHOOL OF COMPUTING VERSION SCANNER Database of vulnerabilities. - can be queried to retrieve vuln Vmi. CVS Vulnerability Scanner corresponding to particular version PATTERN Initialization Process Lookup File Overlay Instantiation Information Extraction VERSION PARSER V E R S I O N CVE Details Program to parsedumps version # from data Version Scanner data source File containing dumped version data sourceversion of version containing number 21 V U L N E R A B I L I T I E S
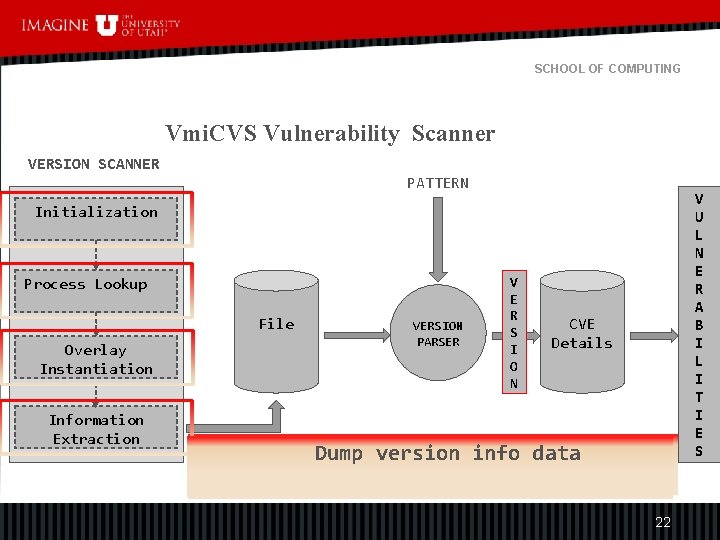
SCHOOL OF COMPUTING Vmi. CVS Vulnerability Scanner VERSION SCANNER PATTERN Initialization Process Lookup File Overlay Instantiation Information Extraction VERSION PARSER V E R S I O N CVE Details Initialize init_task retrieval and base Navigate and to Dump. Stackdb version info data target Get process targetenvironment from attach the desired to Base process target 22 V U L N E R A B I L I T I E S
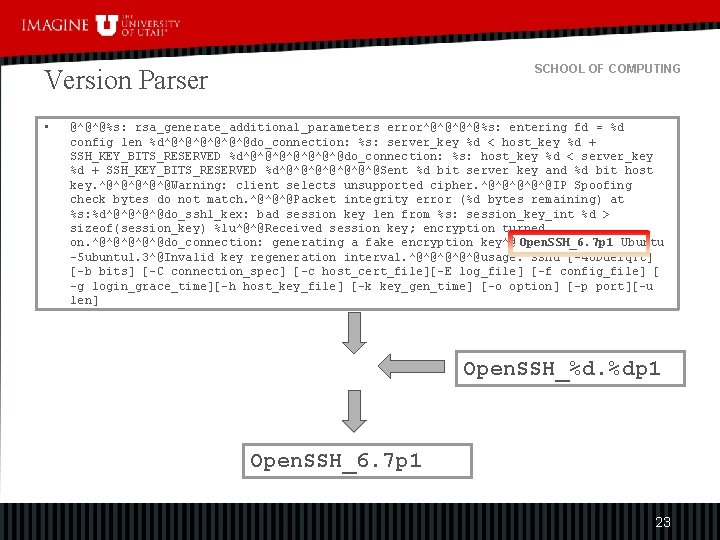
SCHOOL OF COMPUTING Version Parser • @^@^@%s: rsa_generate_additional_parameters error^@^@%s: entering fd = %d config len %d^@^@^@do_connection: %s: server_key %d < host_key %d + SSH_KEY_BITS_RESERVED %d^@^@^@^@do_connection: %s: host_key %d < server_key %d + SSH_KEY_BITS_RESERVED %d^@^@^@^@Sent %d bit server key and %d bit host key. ^@^@^@Warning: client selects unsupported cipher. ^@^@^@IP Spoofing check bytes do not match. ^@^@^@Packet integrity error (%d bytes remaining) at %s: %d^@^@do_ssh 1_kex: bad session key len from %s: session_key_int %d > sizeof(session_key) %lu^@^@Received session key; encryption turned on. ^@^@^@do_connection: generating a fake encryption key^@ Open. SSH_6. 7 p 1 Ubuntu -5 ubuntu 1. 3^@Invalid key regeneration interval. ^@^@^@usage: sshd [-46 Ddeiq. Tt] [-b bits] [-C connection_spec] [-c host_cert_file][-E log_file] [-f config_file] [ -g login_grace_time][-h host_key_file] [-k key_gen_time] [-o option] [-p port][-u len] Open. SSH_%d. %dp 1 Open. SSH_6. 7 p 1 23
SCHOOL OF COMPUTING Version Scanners a) Virtual Memory based Version Scanner b) Name based Version Scanner 24
SCHOOL OF COMPUTING Virtual Memory Based VS Dumps virtual memory pages of a process into a file for version extraction 25
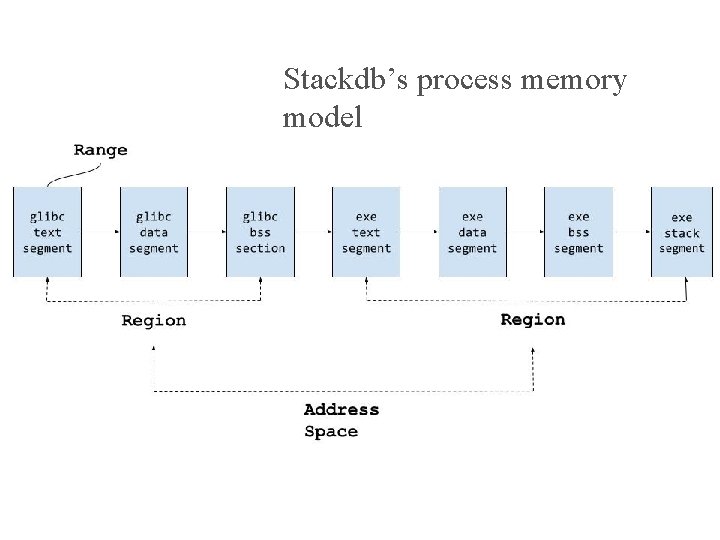
Stackdb’s process memory model SCHOOL OF COMPUTING 26
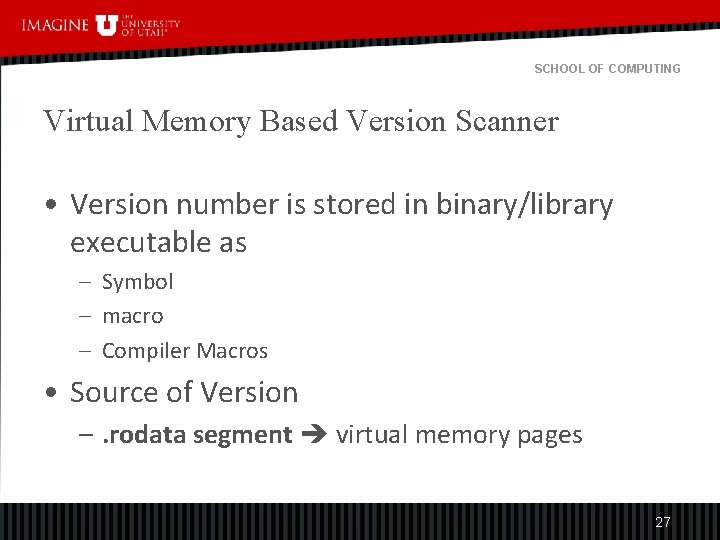
SCHOOL OF COMPUTING Virtual Memory Based Version Scanner • Version number is stored in binary/library executable as – Symbol – macro – Compiler Macros • Source of Version –. rodata segment virtual memory pages 27
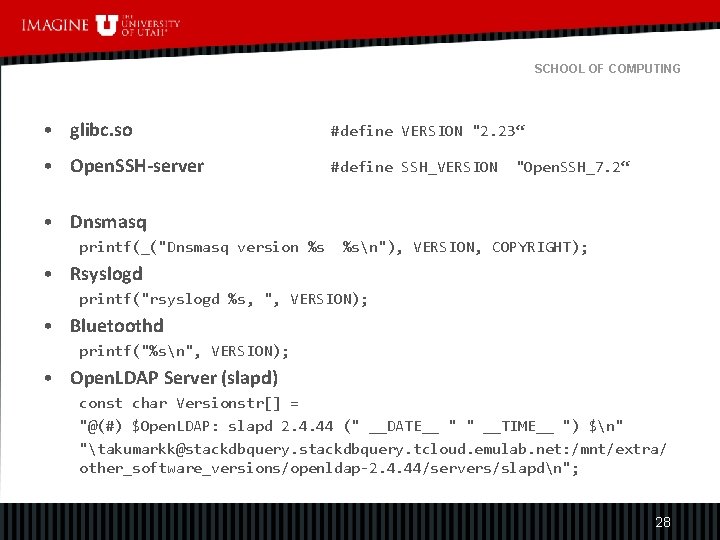
SCHOOL OF COMPUTING • glibc. so #define VERSION "2. 23“ • Open. SSH-server #define SSH_VERSION "Open. SSH_7. 2“ • Dnsmasq printf(_("Dnsmasq version %s %sn"), VERSION, COPYRIGHT); • Rsyslogd printf("rsyslogd %s, ", VERSION); • Bluetoothd printf("%sn", VERSION); • Open. LDAP Server (slapd) const char Versionstr[] = "@(#) $Open. LDAP: slapd 2. 4. 44 (" __DATE__ " " __TIME__ ") $n" "takumarkk@stackdbquery. tcloud. emulab. net: /mnt/extra/ other_software_versions/openldap-2. 4. 44/servers/slapdn"; 28
SCHOOL OF COMPUTING Name Based Version Scanner Scans version number from the filename of the shared library 29
SCHOOL OF COMPUTING Shared Library Versioning • Build Tools inserts version number in the filename of the shared library lib<name>. so. <major>. <minor>. <rls> PAPER : Library Interface Versioning in Solaris and Linux 30
SCHOOL OF COMPUTING libtool • Specify version number using – version-number or version-info <soname>. so. <current-age>. <revision> 31
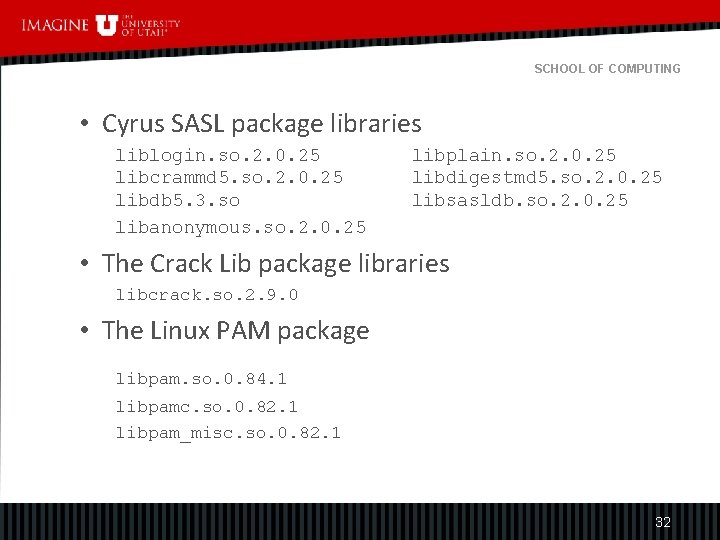
SCHOOL OF COMPUTING • Cyrus SASL package libraries liblogin. so. 2. 0. 25 libplain. so. 2. 0. 25 libcrammd 5. so. 2. 0. 25 libdigestmd 5. so. 2. 0. 25 libdb 5. 3. so libsasldb. so. 2. 0. 25 libanonymous. so. 2. 0. 25 • The Crack Lib package libraries libcrack. so. 2. 9. 0 • The Linux PAM package libpam. so. 0. 84. 1 libpamc. so. 0. 82. 1 libpam_misc. so. 0. 82. 1 32
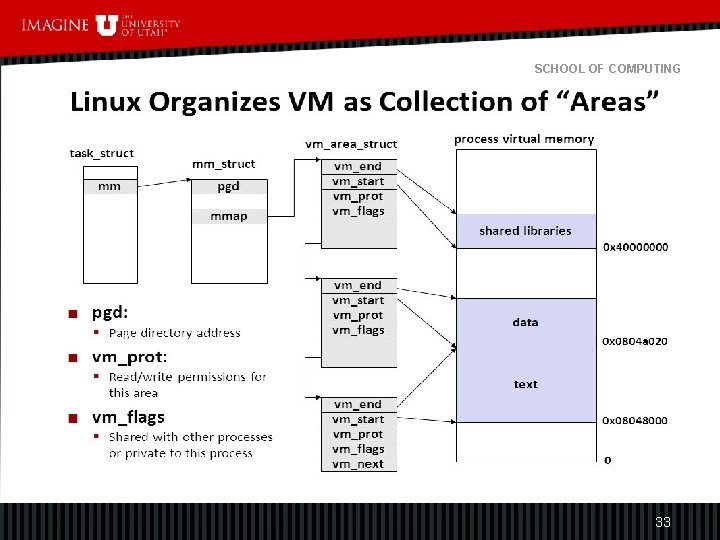
SCHOOL OF COMPUTING 33
SCHOOL OF COMPUTING Introduction Motivation Architecture and Design Evaluation and Results Limitations Future work 34
SCHOOL OF COMPUTING Evaluation • Comparison with nmap • Disruption • Name based VS versus Virtual Memory based VS 35
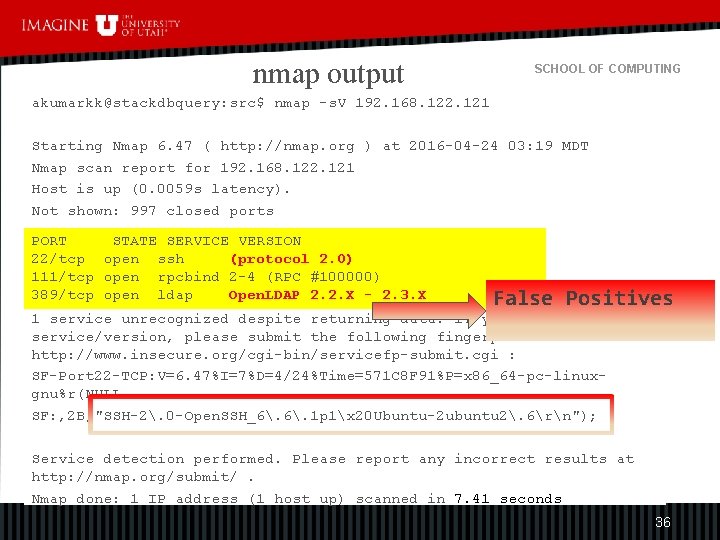
nmap output SCHOOL OF COMPUTING akumarkk@stackdbquery: src$ nmap -s. V 192. 168. 122. 121 Starting Nmap 6. 47 ( http: //nmap. org ) at 2016 -04 -24 03: 19 MDT Nmap scan report for 192. 168. 122. 121 Host is up (0. 0059 s latency). Not shown: 997 closed ports PORT STATE SERVICE VERSION 22/tcp open ssh (protocol 2. 0) 111/tcp open rpcbind 2 -4 (RPC #100000) 389/tcp open ldap Open. LDAP 2. 2. X - 2. 3. X False Positives 1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at http: //www. insecure. org/cgi-bin/servicefp-submit. cgi : SF-Port 22 -TCP: V=6. 47%I=7%D=4/24%Time=571 C 8 F 91%P=x 86_64 -pc-linuxgnu%r(NULL SF: , 2 B, "SSH-2. 0 -Open. SSH_6. 1 p 1x 20 Ubuntu-2 ubuntu 2. 6rn"); Service detection performed. Please report any incorrect results at http: //nmap. org/submit/. Nmap done: 1 IP address (1 host up) scanned in 7. 41 seconds 36
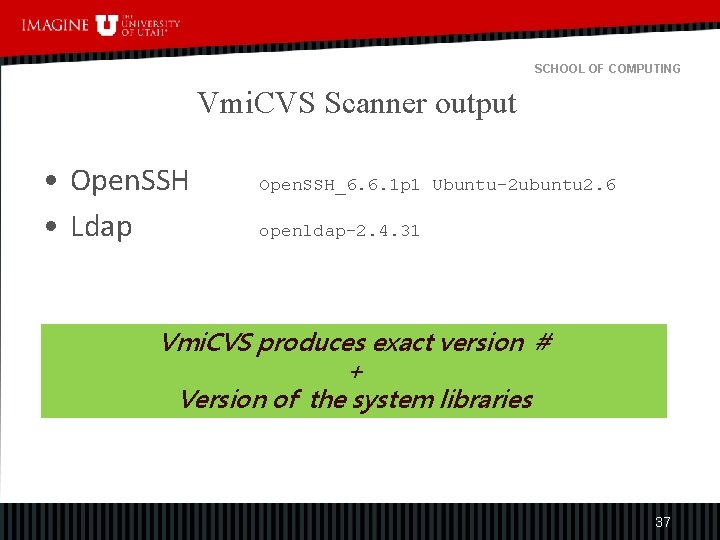
SCHOOL OF COMPUTING Vmi. CVS Scanner output • Open. SSH • Ldap Open. SSH_6. 6. 1 p 1 Ubuntu-2 ubuntu 2. 6 openldap-2. 4. 31 Vmi. CVS produces exact version # + Version of the system libraries 37
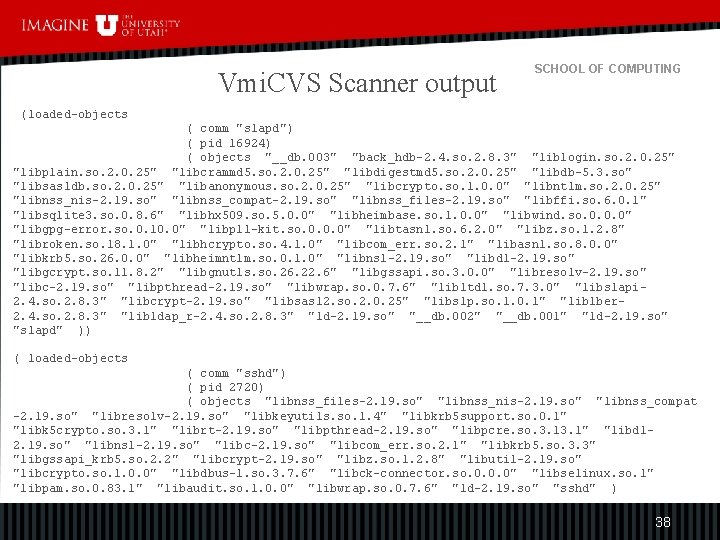
Vmi. CVS Scanner output SCHOOL OF COMPUTING (loaded-objects ( comm "slapd") ( pid 16924) ( objects "__db. 003" "back_hdb-2. 4. so. 2. 8. 3" "liblogin. so. 2. 0. 25" "libplain. so. 2. 0. 25" "libcrammd 5. so. 2. 0. 25" "libdigestmd 5. so. 2. 0. 25" "libdb-5. 3. so" "libsasldb. so. 2. 0. 25" "libanonymous. so. 2. 0. 25" "libcrypto. so. 1. 0. 0" "libntlm. so. 2. 0. 25" "libnss_nis-2. 19. so" "libnss_compat-2. 19. so" "libnss_files-2. 19. so" "libffi. so. 6. 0. 1" "libsqlite 3. so. 0. 8. 6" "libhx 509. so. 5. 0. 0" "libheimbase. so. 1. 0. 0" "libwind. so. 0. 0. 0" "libgpg-error. so. 0. 10. 0" "libp 11 -kit. so. 0. 0. 0" "libtasn 1. so. 6. 2. 0" "libz. so. 1. 2. 8" "libroken. so. 18. 1. 0" "libhcrypto. so. 4. 1. 0" "libcom_err. so. 2. 1" "libasn 1. so. 8. 0. 0" "libkrb 5. so. 26. 0. 0" "libheimntlm. so. 0. 1. 0" "libnsl-2. 19. so" "libdl-2. 19. so" "libgcrypt. so. 11. 8. 2" "libgnutls. so. 26. 22. 6" "libgssapi. so. 3. 0. 0" "libresolv-2. 19. so" "libc-2. 19. so" "libpthread-2. 19. so" "libwrap. so. 0. 7. 6" "libltdl. so. 7. 3. 0" "libslapi 2. 4. so. 2. 8. 3" "libcrypt-2. 19. so" "libsasl 2. so. 2. 0. 25" "libslp. so. 1. 0. 1" "liblber 2. 4. so. 2. 8. 3" "libldap_r-2. 4. so. 2. 8. 3" "ld-2. 19. so" "__db. 002" "__db. 001" "ld-2. 19. so" "slapd" )) ( loaded-objects ( comm "sshd") ( pid 2720) ( objects "libnss_files-2. 19. so" "libnss_nis-2. 19. so" "libnss_compat -2. 19. so" "libresolv-2. 19. so" "libkeyutils. so. 1. 4" "libkrb 5 support. so. 0. 1" "libk 5 crypto. so. 3. 1" "librt-2. 19. so" "libpthread-2. 19. so" "libpcre. so. 3. 1" "libdl 2. 19. so" "libnsl-2. 19. so" "libcom_err. so. 2. 1" "libkrb 5. so. 3. 3" "libgssapi_krb 5. so. 2. 2" "libcrypt-2. 19. so" "libz. so. 1. 2. 8" "libutil-2. 19. so" "libcrypto. so. 1. 0. 0" "libdbus-1. so. 3. 7. 6" "libck-connector. so. 0. 0. 0" "libselinux. so. 1" "libpam. so. 0. 83. 1" "libaudit. so. 1. 0. 0" "libwrap. so. 0. 7. 6" "ld-2. 19. so" "sshd" ) 38
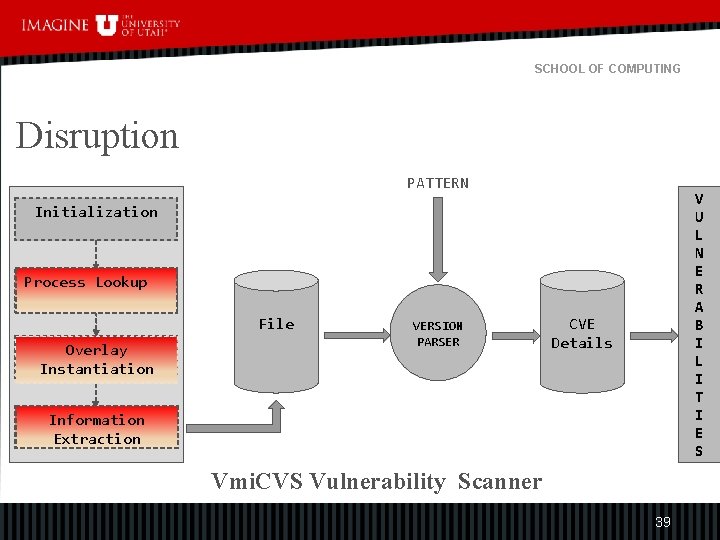
SCHOOL OF COMPUTING Disruption PATTERN V U L N E R A B I L I T I E S Initialization Process Lookup File Overlay Instantiation VERSION PARSER CVE Details Information Extraction Vmi. CVS Vulnerability Scanner 39
SCHOOL OF COMPUTING Disruption Pausing the Virtual Machine But Not harming 40
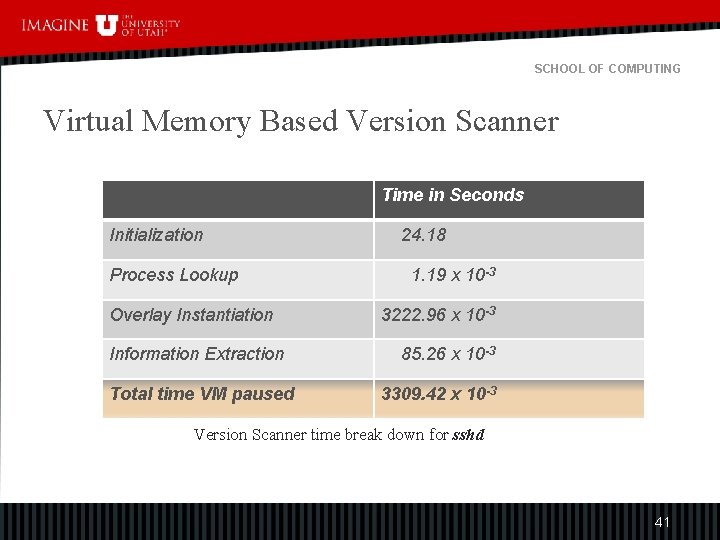
SCHOOL OF COMPUTING Virtual Memory Based Version Scanner Time in Seconds Initialization Process Lookup Overlay Instantiation Information Extraction Total time VM paused 24. 18 1. 19 x 10 -3 3222. 96 x 10 -3 85. 26 x 10 -3 3309. 42 x 10 -3 Version Scanner time break down for sshd 41
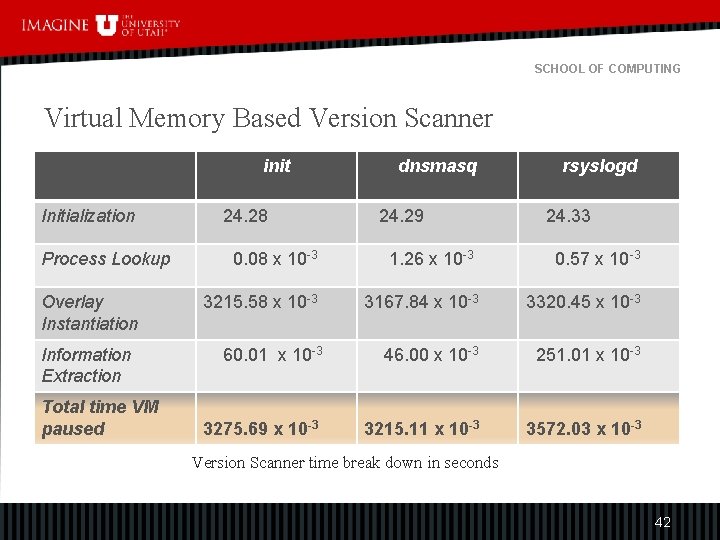
SCHOOL OF COMPUTING Virtual Memory Based Version Scanner init Initialization Process Lookup Overlay Instantiation Information Extraction Total time VM paused 24. 28 dnsmasq 24. 29 rsyslogd 24. 33 0. 08 x 10 -3 1. 26 x 10 -3 0. 57 x 10 -3 3215. 58 x 10 -3 3167. 84 x 10 -3 3320. 45 x 10 -3 60. 01 x 10 -3 46. 00 x 10 -3 251. 01 x 10 -3 3275. 69 x 10 -3 3215. 11 x 10 -3 3572. 03 x 10 -3 Version Scanner time break down in seconds 42
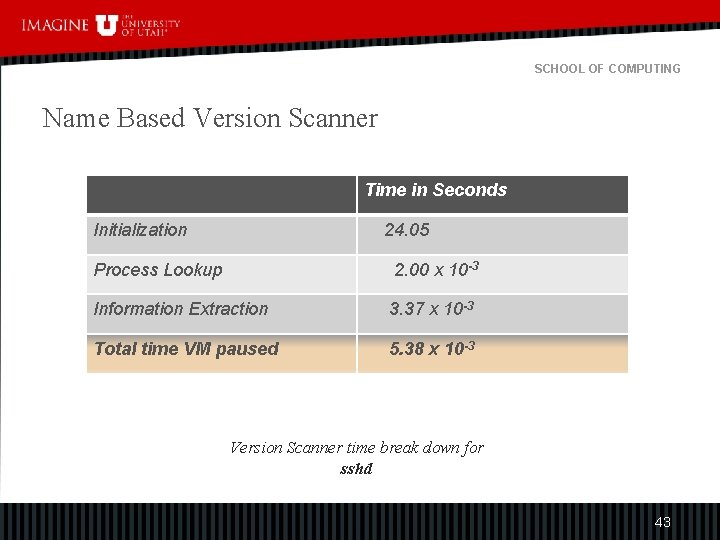
SCHOOL OF COMPUTING Name Based Version Scanner Time in Seconds Initialization 24. 05 Process Lookup 2. 00 x 10 -3 Information Extraction 3. 37 x 10 -3 Total time VM paused 5. 38 x 10 -3 Version Scanner time break down for sshd 43
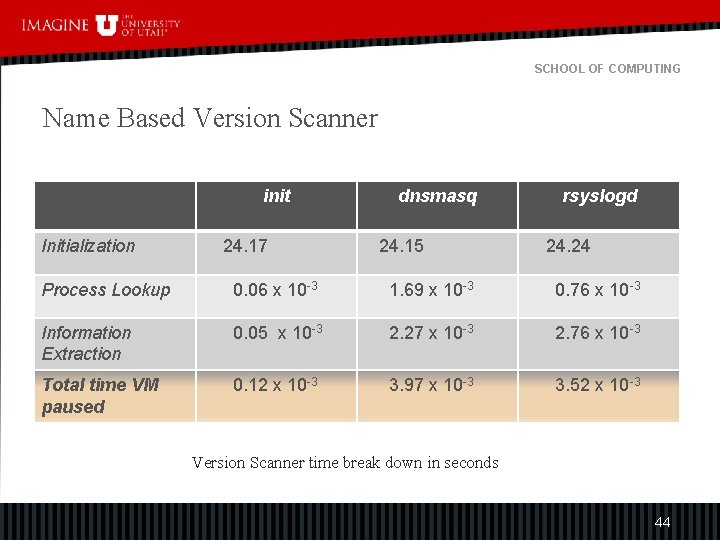
SCHOOL OF COMPUTING Name Based Version Scanner init Initialization 24. 17 dnsmasq 24. 15 rsyslogd 24. 24 Process Lookup 0. 06 x 10 -3 1. 69 x 10 -3 0. 76 x 10 -3 Information Extraction 0. 05 x 10 -3 2. 27 x 10 -3 2. 76 x 10 -3 Total time VM paused 0. 12 x 10 -3 3. 97 x 10 -3 3. 52 x 10 -3 Version Scanner time break down in seconds 44
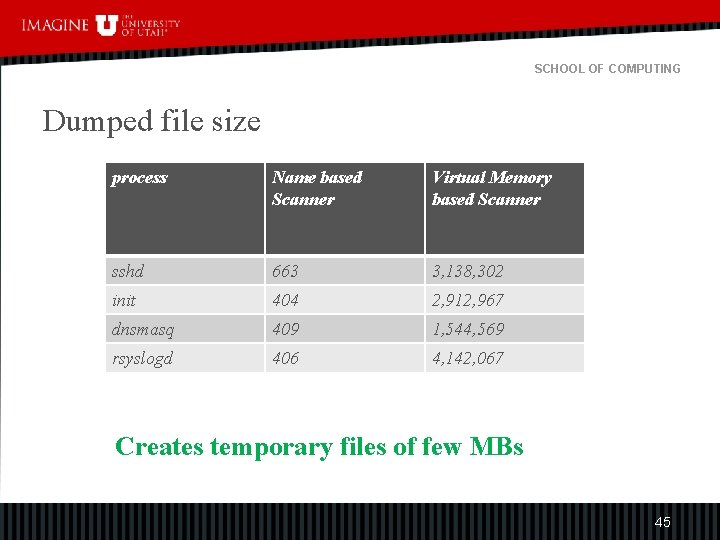
SCHOOL OF COMPUTING Dumped file size process Name based Scanner Virtual Memory based Scanner sshd 663 3, 138, 302 init 404 2, 912, 967 dnsmasq 409 1, 544, 569 rsyslogd 406 4, 142, 067 Creates temporary files of few MBs 45
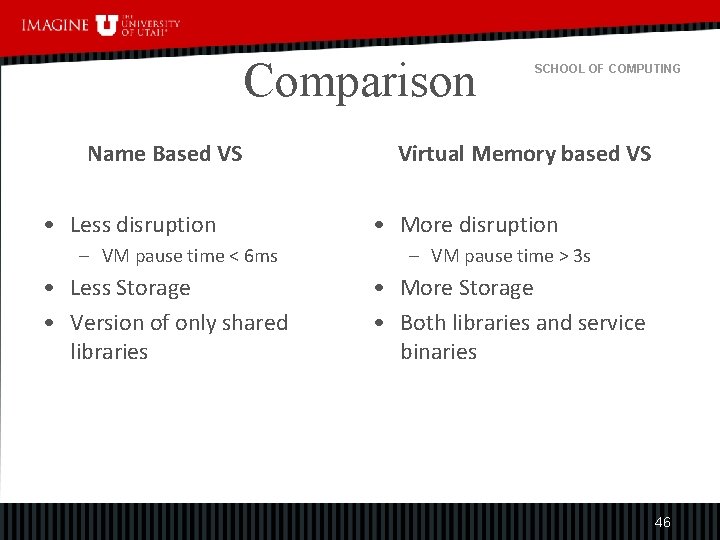
Comparison Name Based VS • Less disruption – VM pause time < 6 ms • Less Storage • Version of only shared libraries SCHOOL OF COMPUTING Virtual Memory based VS • More disruption – VM pause time > 3 s • More Storage • Both libraries and service binaries 46
SCHOOL OF COMPUTING Introduction Motivation Architecture and Design Evaluation and Results Limitations Future work 47
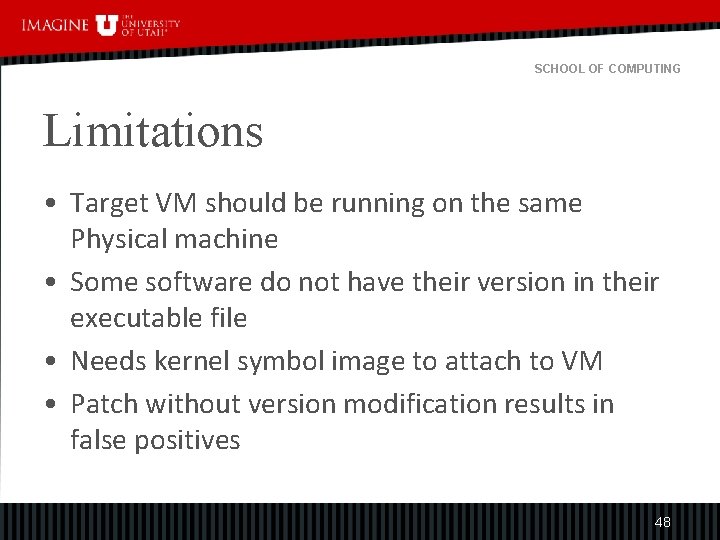
SCHOOL OF COMPUTING Limitations • Target VM should be running on the same Physical machine • Some software do not have their version in their executable file • Needs kernel symbol image to attach to VM • Patch without version modification results in false positives 48
SCHOOL OF COMPUTING Introduction Motivation Architecture and Design Evaluation and Results Limitations Future work 49
SCHOOL OF COMPUTING Future work • Further assessment to confirm the presence of vulnerabilities • Instead of dumping version info to file, parse according to version database • overlay instantiation can be optimized 50
SCHOOL OF COMPUTING Conclusion Vmi. CVS scanner produces Detailed Accurate results And Non-disruptive 51
SCHOOL OF COMPUTING Thank You 52
- Slides: 52