Reversible Data Hiding for PointSampled Geometry PENGCHENG WANG
Reversible Data Hiding for Point-Sampled Geometry PENG-CHENG WANG AND CHUNG-MING WANG JOURNAL OF INFORMATION SCIENCE AND ENGINEERING Vol. 23, pp. 1889 -1900, 2007 Reporter: 陳德祐 2008/2/22
Outline n n n Introduction Reversible Data Hiding Point-Sampled Geometry Proposed scheme Conclusions Comments 2
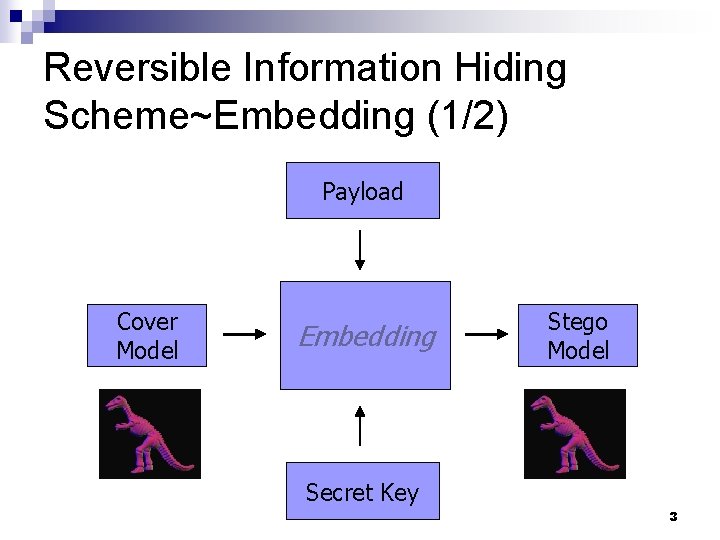
Reversible Information Hiding Scheme~Embedding (1/2) Payload Cover Model Embedding Stego Model Secret Key 3
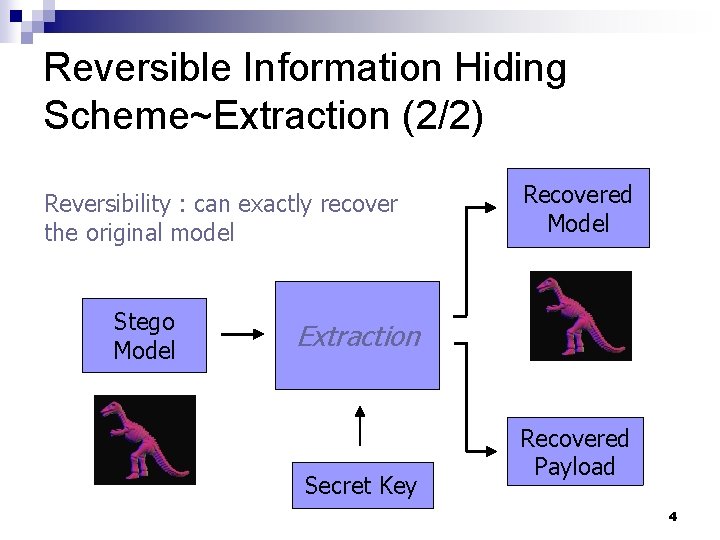
Reversible Information Hiding Scheme~Extraction (2/2) Reversibility : can exactly recover the original model Stego Model Recovered Model Extraction Secret Key Recovered Payload 4
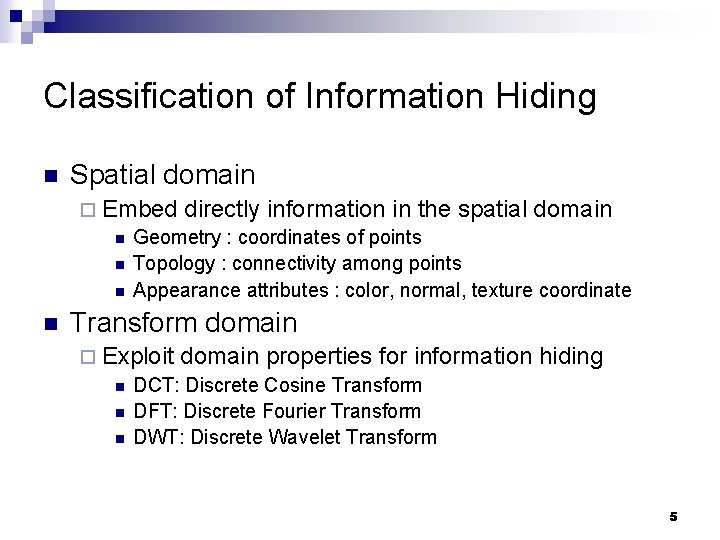
Classification of Information Hiding n Spatial domain ¨ Embed directly information in the spatial domain n Geometry : coordinates of points n Topology : connectivity among points n Appearance attributes : color, normal, texture coordinate n Transform domain ¨ Exploit domain properties for information n DCT: Discrete Cosine Transform n DFT: Discrete Fourier Transform n DWT: Discrete Wavelet Transform hiding 5
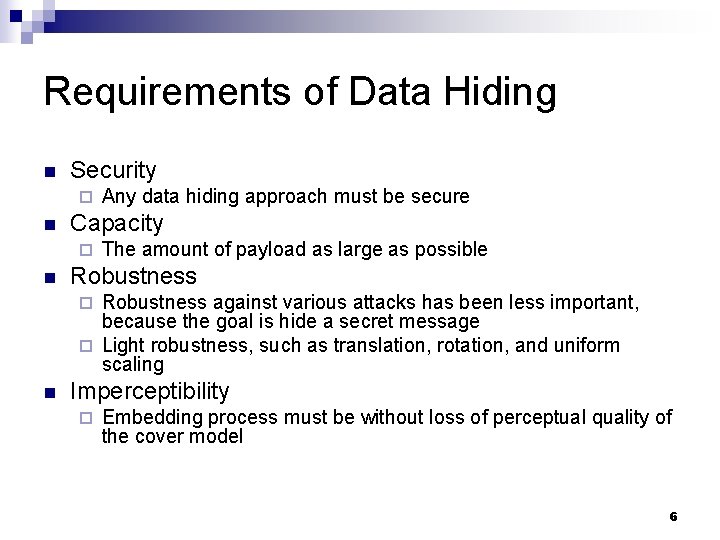
Requirements of Data Hiding n Security ¨ n Capacity ¨ n Any data hiding approach must be secure The amount of payload as large as possible Robustness against various attacks has been less important, because the goal is hide a secret message ¨ Light robustness, such as translation, rotation, and uniform scaling ¨ n Imperceptibility ¨ Embedding process must be without loss of perceptual quality of the cover model 6
3 D Models Representation Polygonal models n Point-sampled geometries n Parametric surfaces, e. g. non-uniform rational B-spline surfaces (NURBS) n Constructive solid geometry (CSG) n Voxels n Motion data n 7
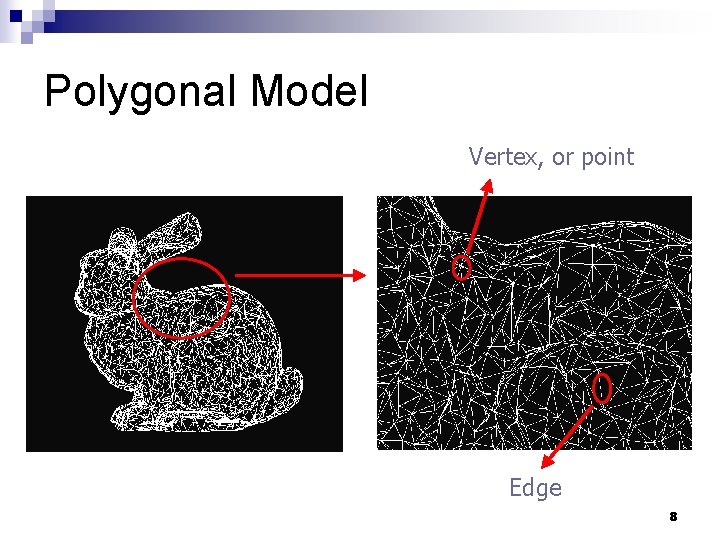
Polygonal Model Vertex, or point Edge 8
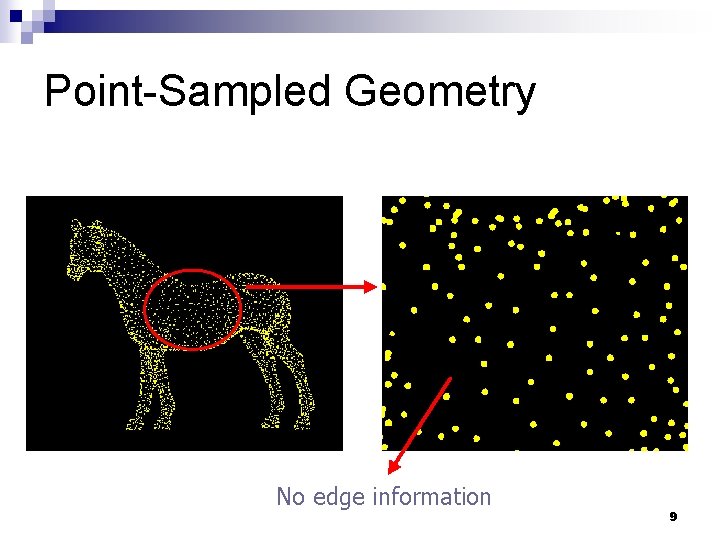
Point-Sampled Geometry No edge information 9
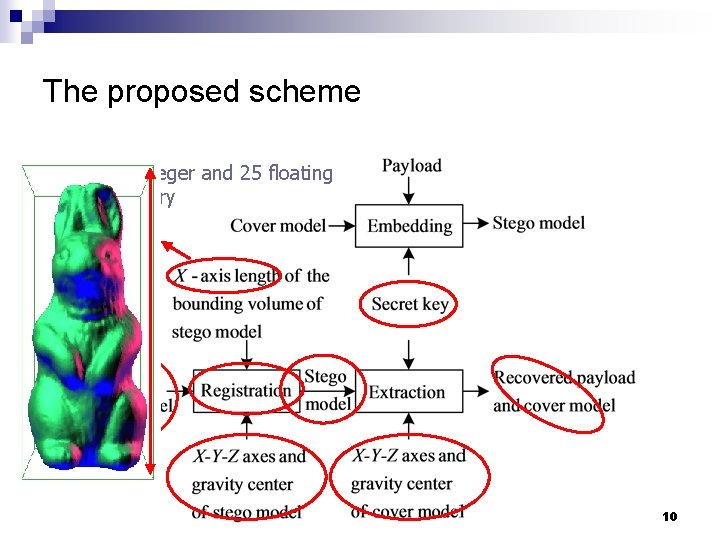
The proposed scheme Require one integer and 25 floating points of memory 10
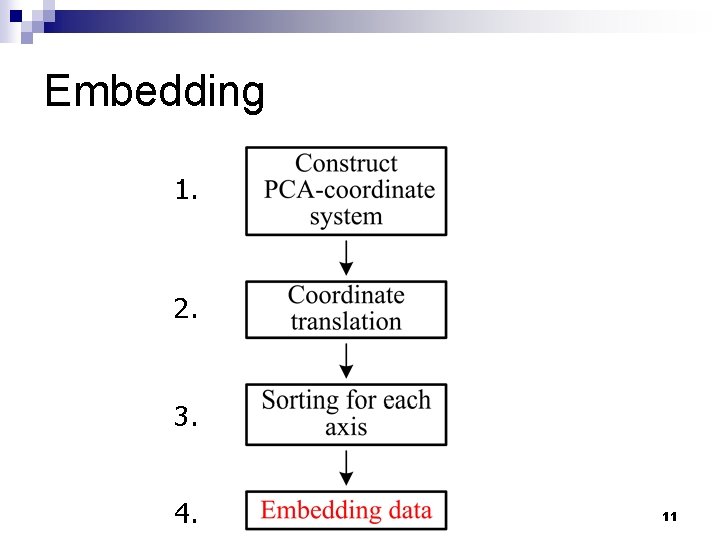
Embedding 1. 2. 3. 4. 11
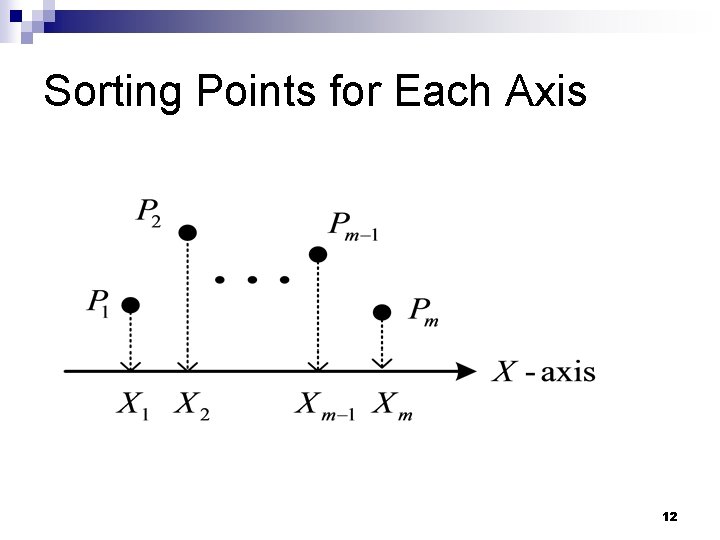
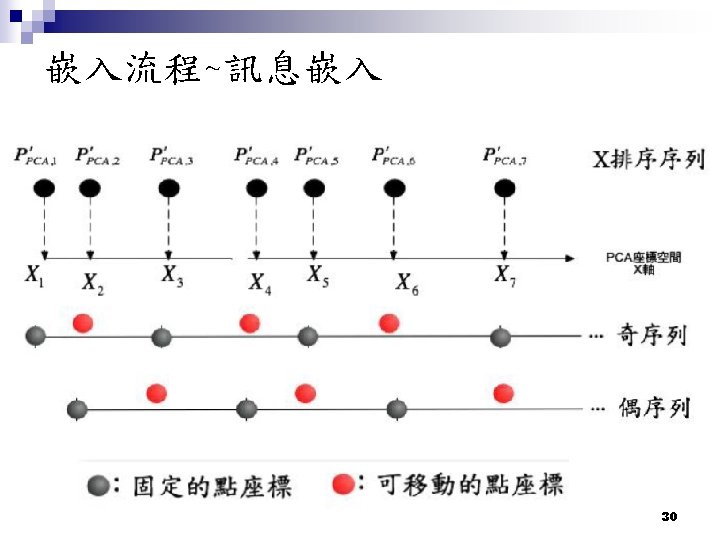
Sorting Points for Each Axis 12
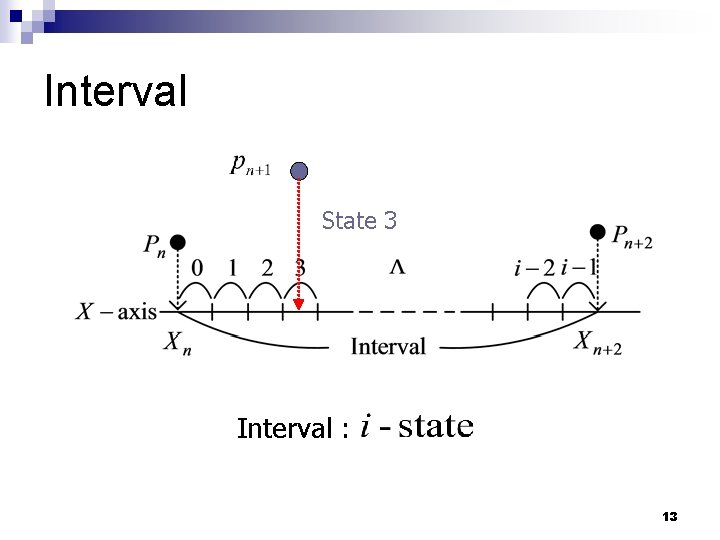
Interval State 3 Interval : 13
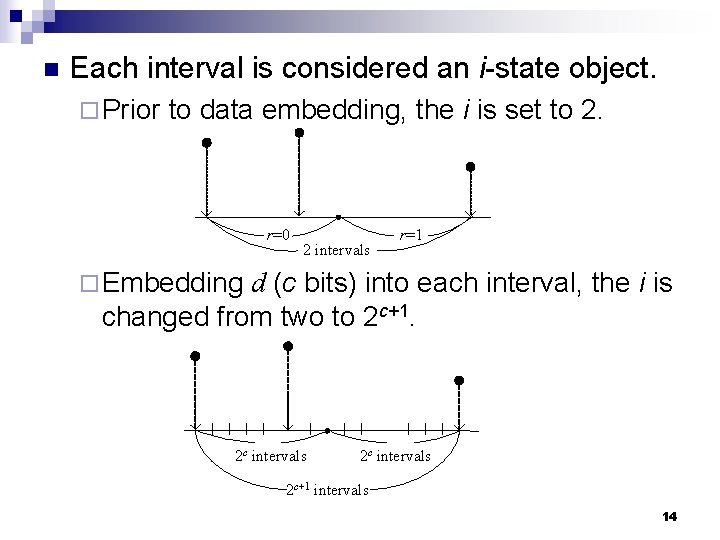
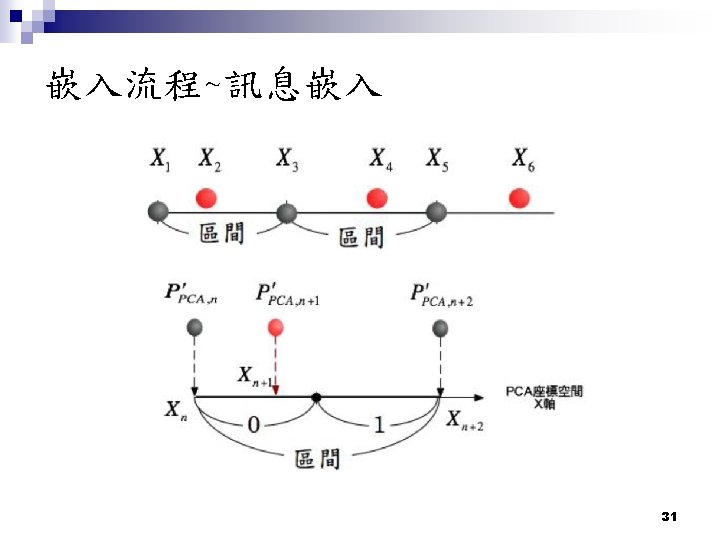
n Each interval is considered an i-state object. ¨ Prior to data embedding, the i is set to 2. r=0 2 intervals r=1 ¨ Embedding d (c bits) into each interval, the i is changed from two to 2 c+1. 2 c intervals 2 c+1 intervals 14
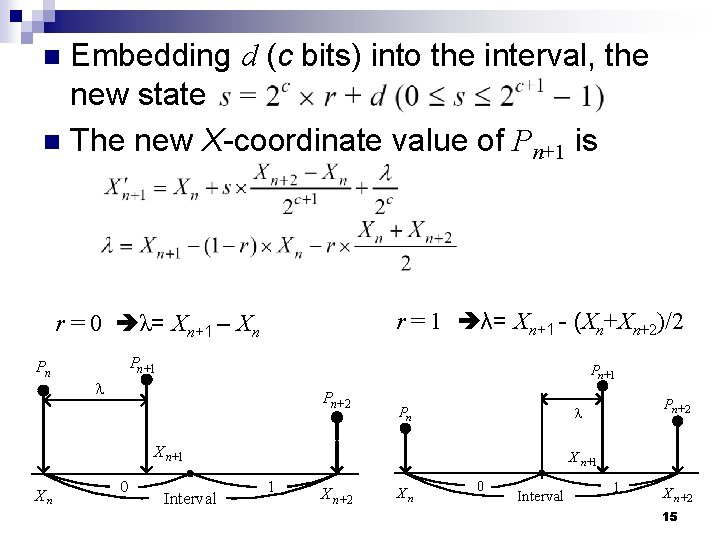
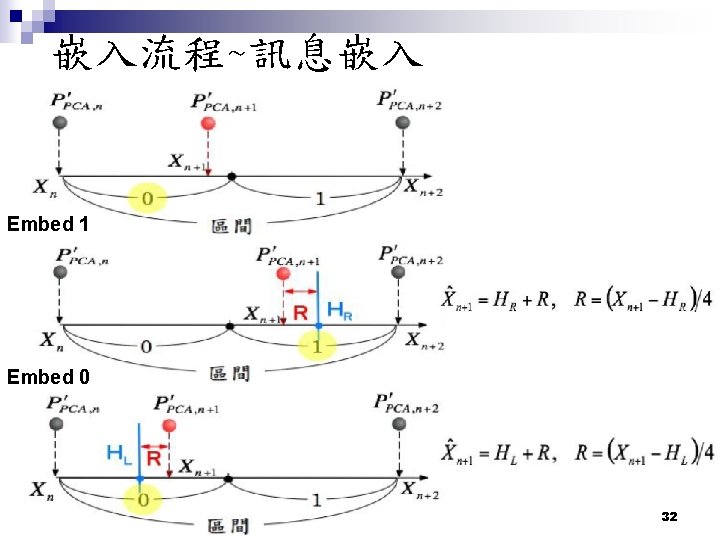
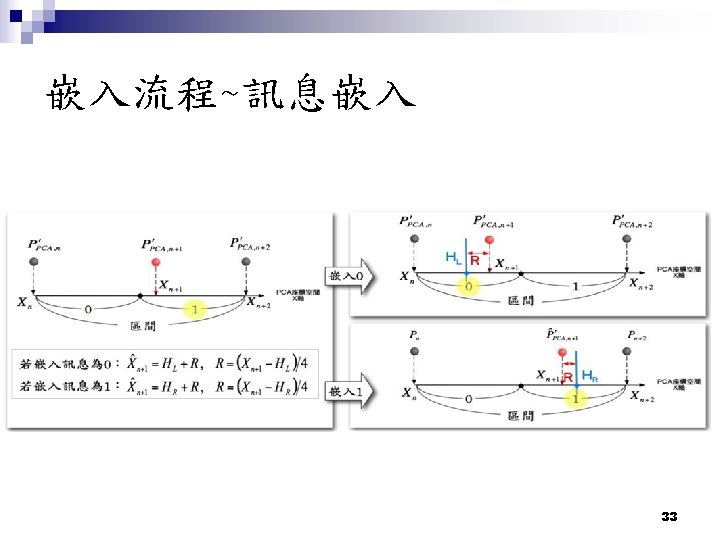
Embedding d (c bits) into the interval, the new state n The new X-coordinate value of Pn+1 is n r = 1 λ= Xn+1 - (Xn+Xn+2)/2 r = 0 λ= Xn+1 – Xn Pn Pn+1 l Pn+ 2 X n+1 Xn 0 Interval Pn + 2 l Pn X n +1 1 X n+ 2 Xn 0 Interval 1 X n+ 2 15
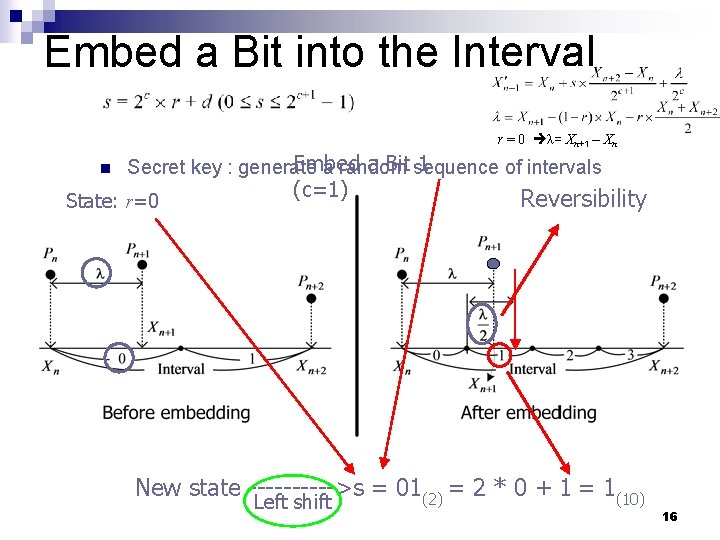
Embed a Bit into the Interval r = 0 λ= Xn+1 – Xn n Embed a Bit sequence 1 Secret key : generate a random of intervals State: r=0 (c=1) Reversibility New state ----->s = 01(2) = 2 * 0 + 1 = 1(10) Left shift 16
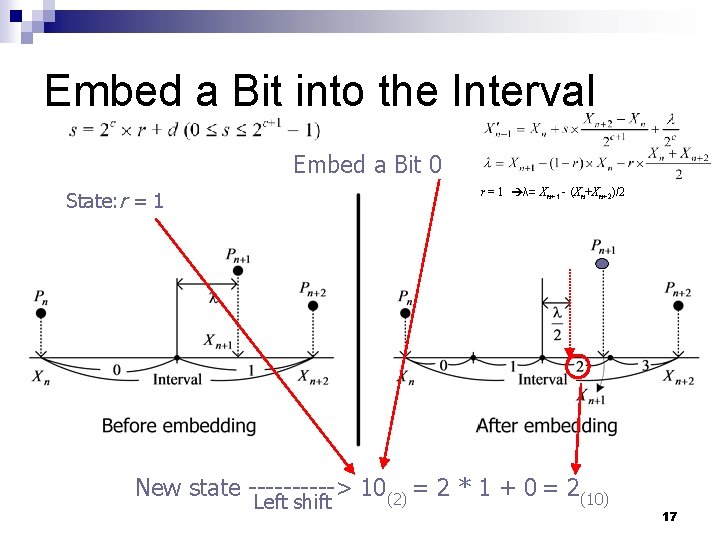
Embed a Bit into the Interval Embed a Bit 0 r = 1 λ= Xn+1 - (Xn+Xn+2)/2 State: r = 1 New state -----> 10(2) = 2 * 1 + 0 = 2(10) Left shift 17
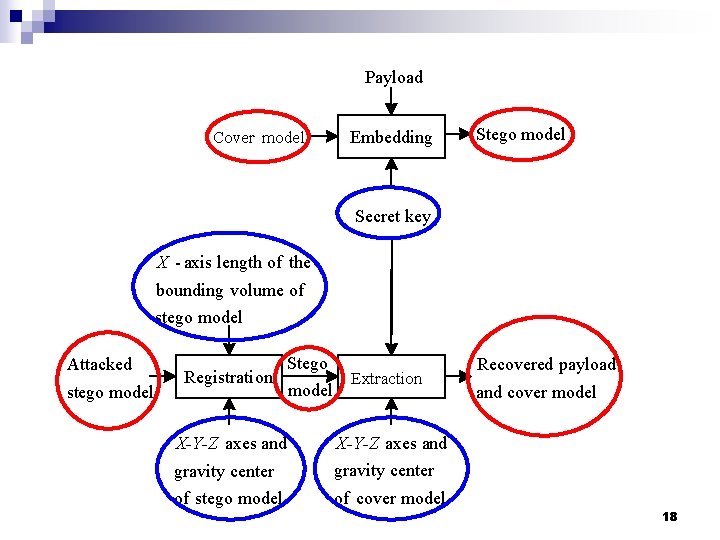
Payload Cover model Embedding Stego model Secret key X - axis length of the bounding volume of stego model Attacked stego model Registrati on Stego model Extraction X-Y-Z axes and gravity center of stego model of cover model Recovered payload and cover model 18
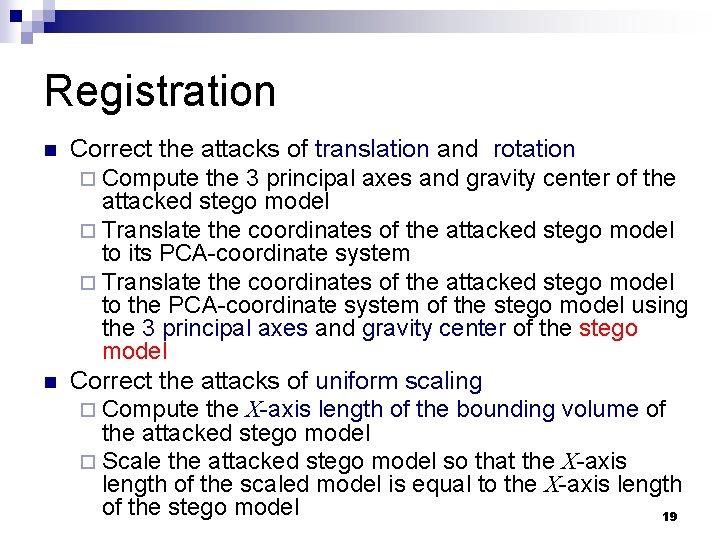
Registration n n Correct the attacks of translation and rotation ¨ Compute the 3 principal axes and gravity center of the attacked stego model ¨ Translate the coordinates of the attacked stego model to its PCA-coordinate system ¨ Translate the coordinates of the attacked stego model to the PCA-coordinate system of the stego model using the 3 principal axes and gravity center of the stego model Correct the attacks of uniform scaling ¨ Compute the X-axis length of the bounding volume of the attacked stego model ¨ Scale the attacked stego model so that the X-axis length of the scaled model is equal to the X-axis length of the stego model 19
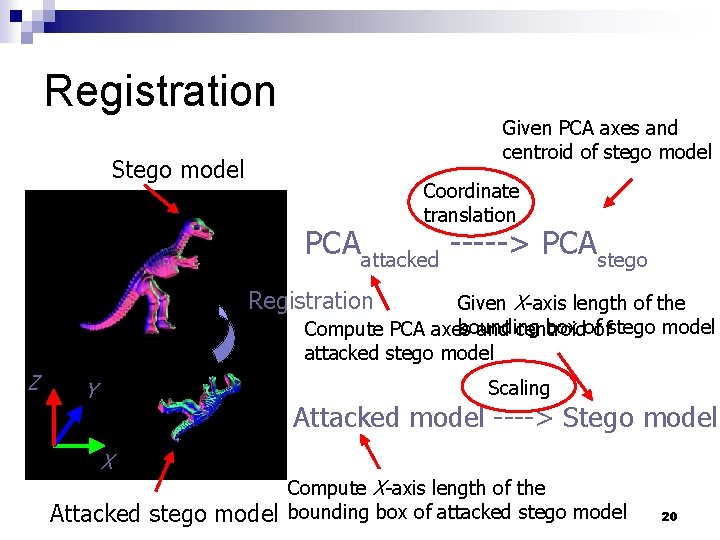
Registration Given PCA axes and centroid of stego model Stego model Coordinate translation PCAattacked -----> PCAstego Registration Given X-axis length of the bounding box ofofstego model Compute PCA axes and centroid attacked stego model Z Scaling Y Attacked model ----> Stego model X Attacked stego model Compute X-axis length of the bounding box of attacked stego model 20
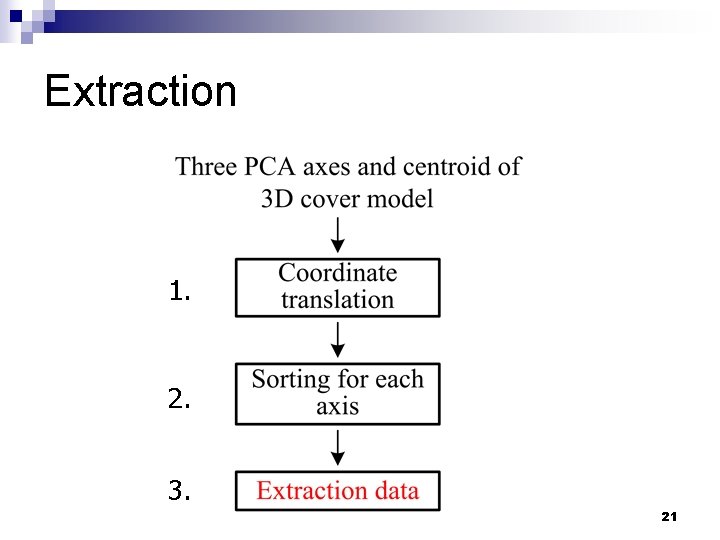
Extraction 1. 2. 3. 21
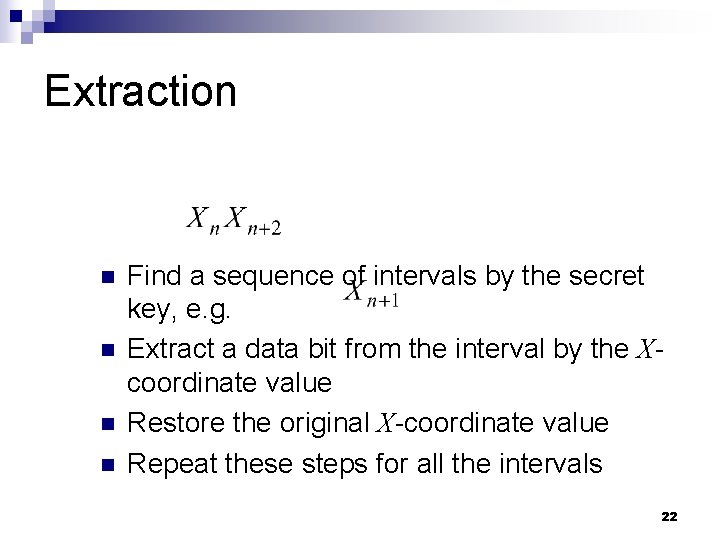
Extraction n n Find a sequence of intervals by the secret key, e. g. Extract a data bit from the interval by the Xcoordinate value Restore the original X-coordinate value Repeat these steps for all the intervals 22
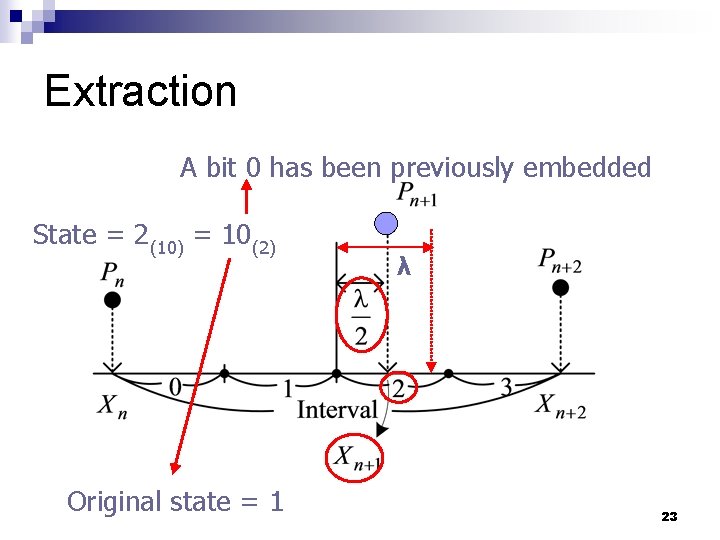
Extraction A bit 0 has been previously embedded State = 2(10) = 10(2) Original state = 1 λ 23
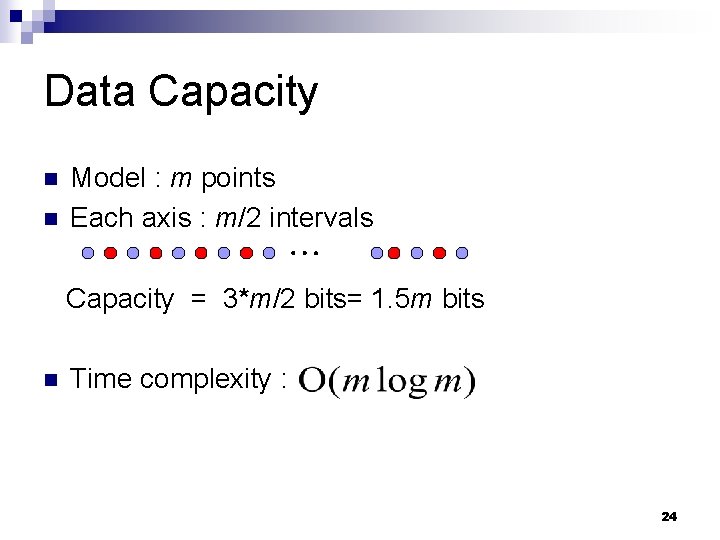
Data Capacity n n Model : m points Each axis : m/2 intervals Capacity = 3*m/2 bits= 1. 5 m bits n Time complexity : 24
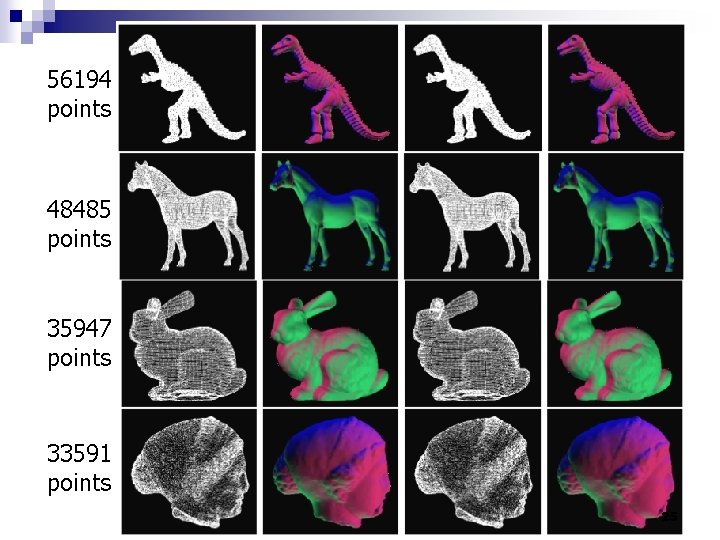
56194 points 48485 points 35947 points 33591 points 25
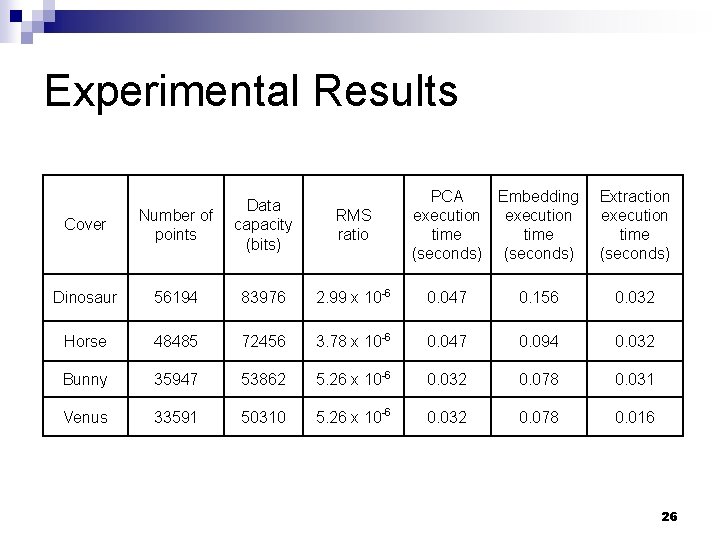
Experimental Results RMS ratio PCA execution time (seconds) Embedding execution time (seconds) Extraction execution time (seconds) Cover Number of points Data capacity (bits) Dinosaur 56194 83976 2. 99 x 10 -6 0. 047 0. 156 0. 032 Horse 48485 72456 3. 78 x 10 -6 0. 047 0. 094 0. 032 Bunny 35947 53862 5. 26 x 10 -6 0. 032 0. 078 0. 031 Venus 33591 50310 5. 26 x 10 -6 0. 032 0. 078 0. 016 26
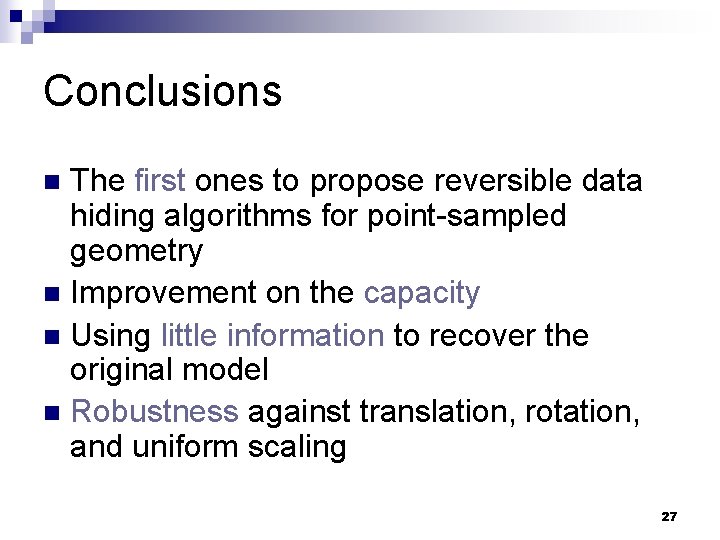
Conclusions The first ones to propose reversible data hiding algorithms for point-sampled geometry n Improvement on the capacity n Using little information to recover the original model n Robustness against translation, rotation, and uniform scaling n 27
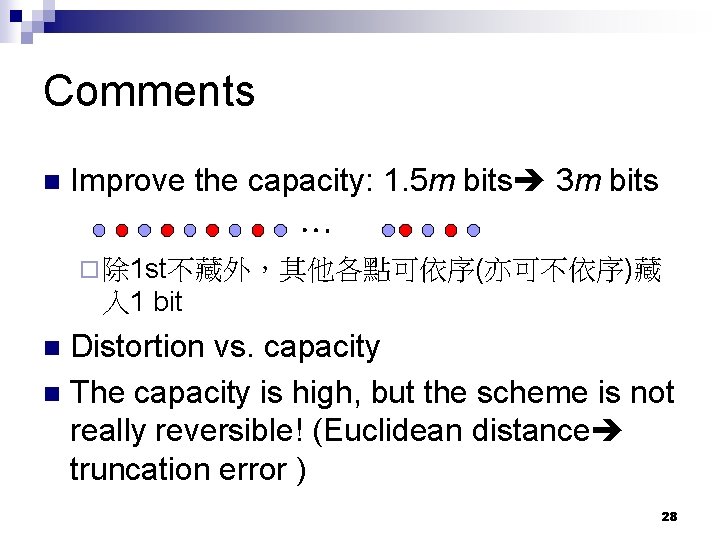
Comments n Improve the capacity: 1. 5 m bits 3 m bits ¨ 除 1 st不藏外,其他各點可依序(亦可不依序)藏 入 1 bit Distortion vs. capacity n The capacity is high, but the scheme is not really reversible! (Euclidean distance truncation error ) n 28
34
- Slides: 34