Double Linear Regression Prediction based Reversible Data Hiding
Double Linear Regression Prediction based Reversible Data Hiding in Encrypted Images Source: Multimedia Tools and Applications, Sep. 2020. Author: Fengyong Li, Hengjie Zhu, Jiang Yu, and Chuan Qin Speaker: Su Guodong Date: 2020/11/02 1
Outline • Introduction • Proposed scheme • Experiments • Conclusions 2
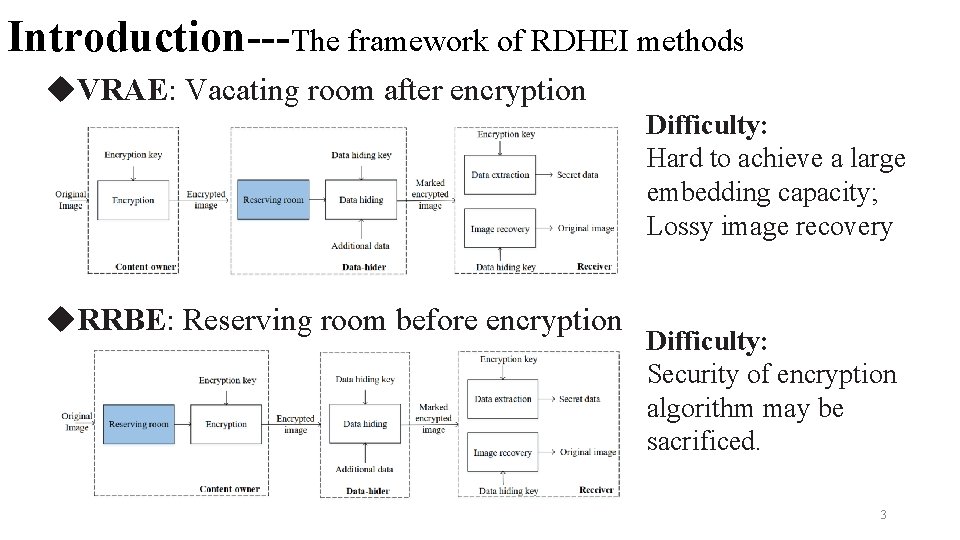
Introduction---The framework of RDHEI methods u. VRAE: Vacating room after encryption Difficulty: Hard to achieve a large embedding capacity; Lossy image recovery u. RRBE: Reserving room before encryption Difficulty: Security of encryption algorithm may be sacrificed. 3
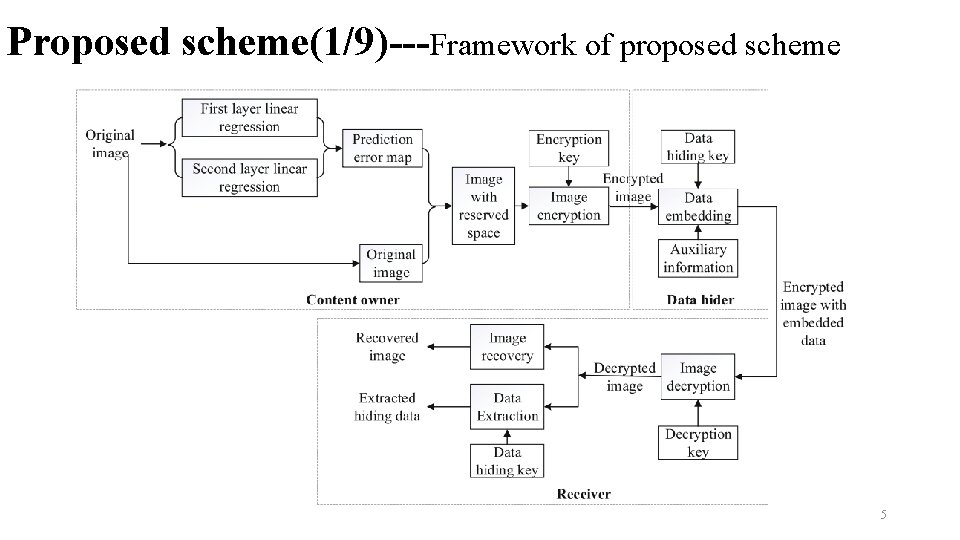
Proposed scheme(1/9)---Framework of proposed scheme 5
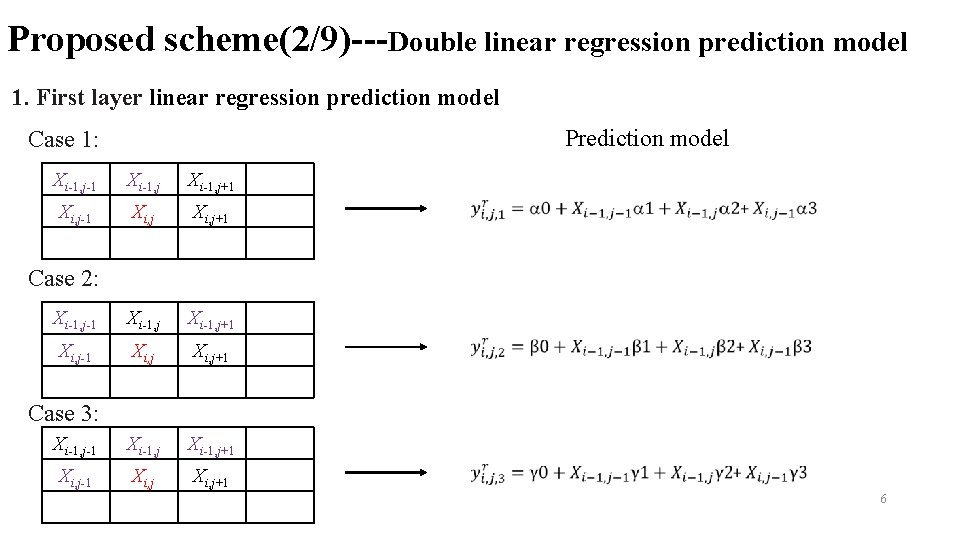
Proposed scheme(2/9)---Double linear regression prediction model 1. First layer linear regression prediction model Prediction model Case 1: Xi-1, j-1 Xi-1, j+1 Xi, j-1 Xi, j+1 Xi-1, j-1 Xi-1, j+1 Xi, j-1 Xi, j+1 Case 2: Case 3: 6
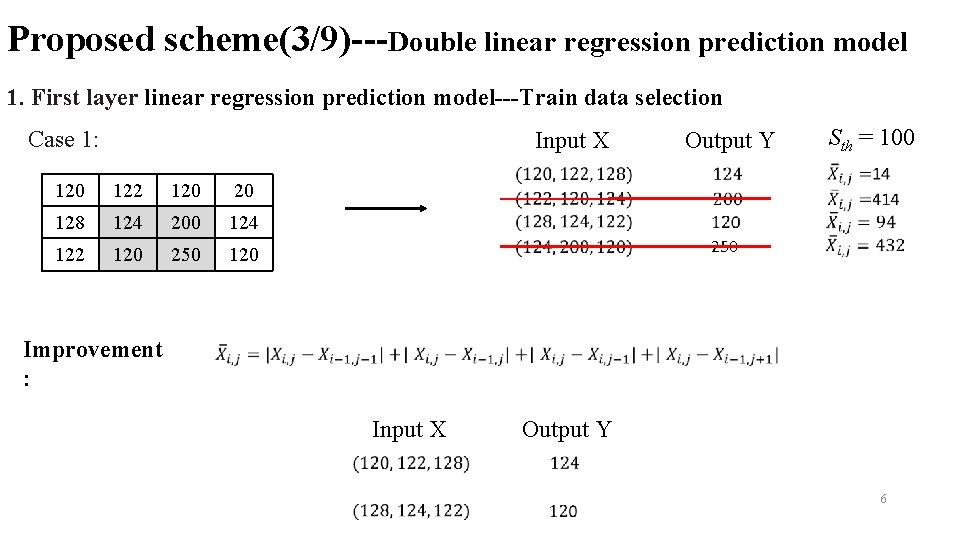
Proposed scheme(3/9)---Double linear regression prediction model 1. First layer linear regression prediction model---Train data selection Case 1: Input X 120 122 120 20 128 124 200 124 122 120 250 120 Improvement : Output Y 250 Sth = 100 Input X Output Y 6
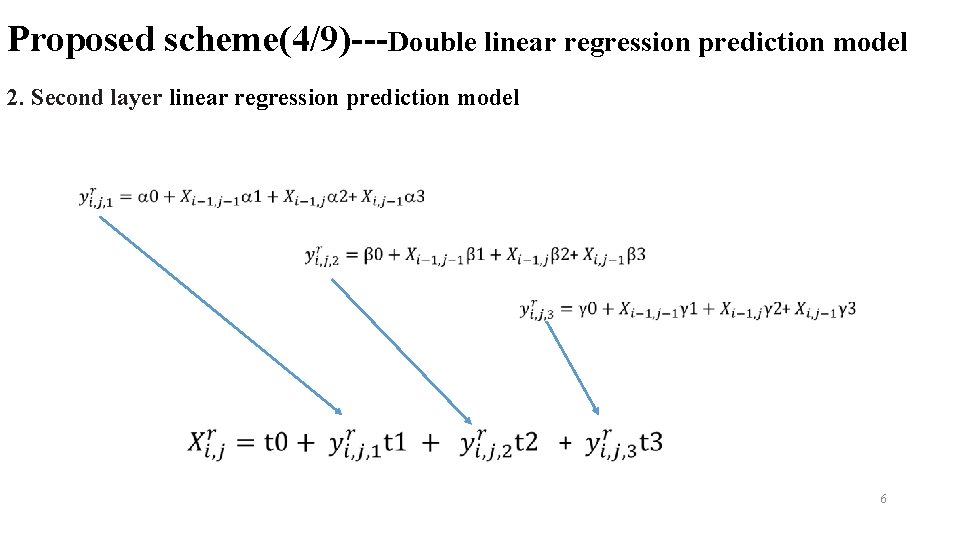
Proposed scheme(4/9)---Double linear regression prediction model 2. Second layer linear regression prediction model 6
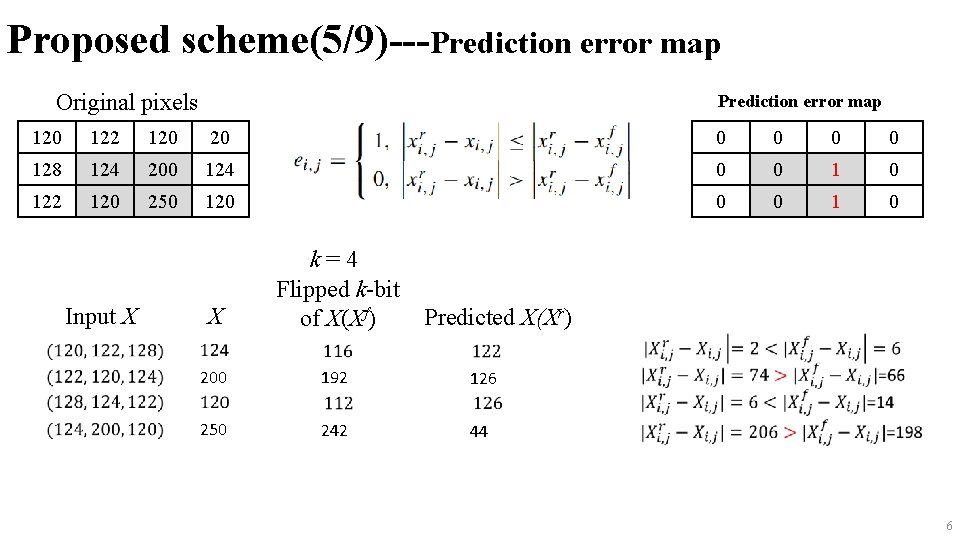
Proposed scheme(5/9)---Prediction error map Original pixels Prediction error map 120 122 120 20 0 0 128 124 200 124 0 0 122 120 250 120 0 0 1 0 Input X X k=4 Flipped k-bit of X(Xf) 200 192 126 250 242 44 Predicted X(Xr) 6
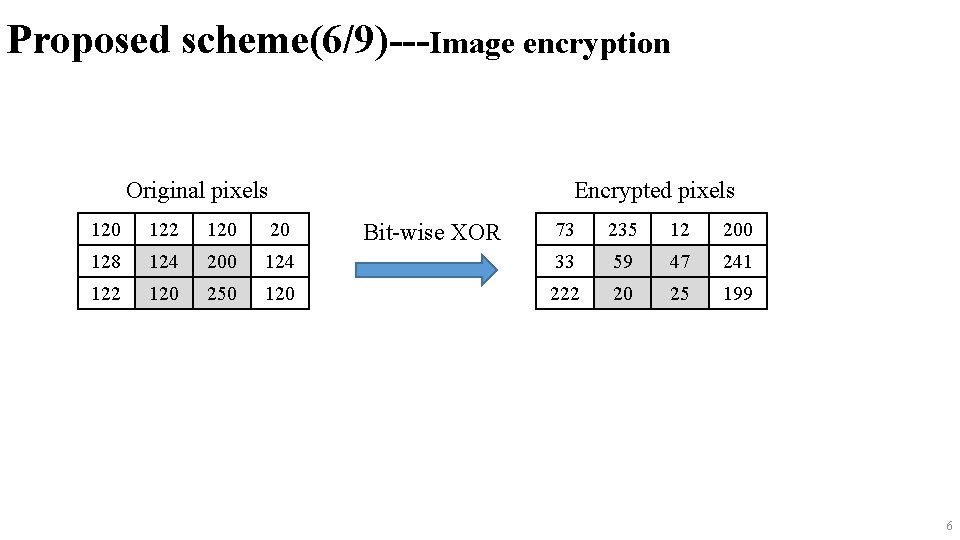
Proposed scheme(6/9)---Image encryption Encrypted pixels Original pixels 120 122 120 20 73 235 12 200 128 124 200 124 33 59 47 241 122 120 250 120 222 20 25 199 Bit-wise XOR 6
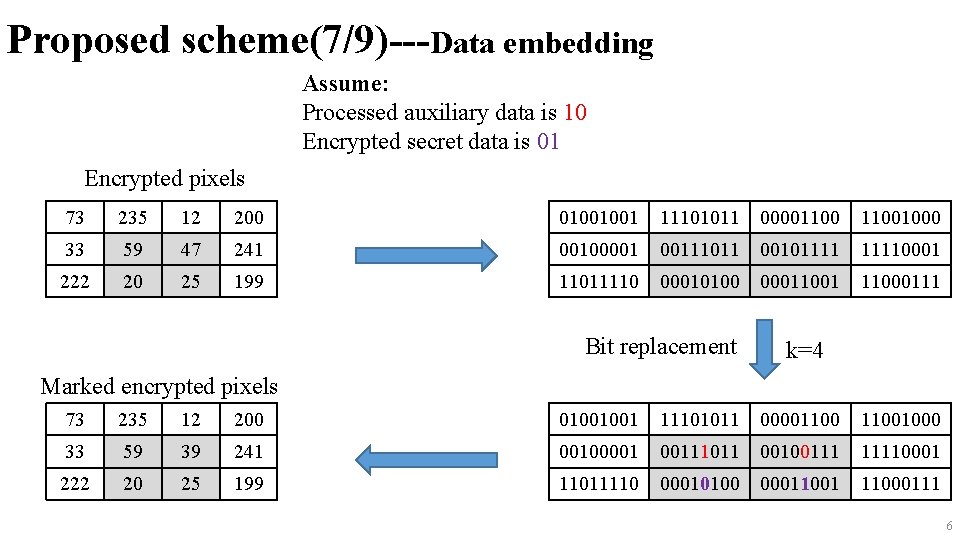
Proposed scheme(7/9)---Data embedding Assume: Processed auxiliary data is 10 Encrypted secret data is 01 Encrypted pixels 73 235 12 200 01001001 11101011 000011001000 33 59 47 241 00100001 00111011 001011110001 222 20 25 199 11011110 00010100 00011001 11000111 Bit replacement k=4 Marked encrypted pixels 73 235 12 200 01001001 11101011 000011001000 33 59 39 241 00100001 00111011 00100111 11110001 222 20 25 199 11011110 00010100 00011001 11000111 6
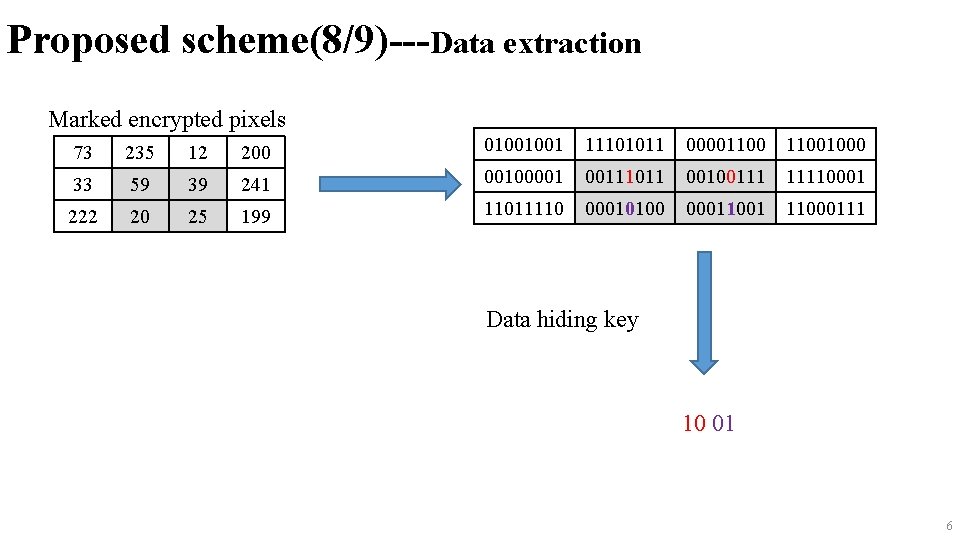
Proposed scheme(8/9)---Data extraction Marked encrypted pixels 73 235 12 200 01001001 11101011 000011001000 33 59 39 241 00100001 00111011 00100111 11110001 222 20 25 199 11011110 00010100 00011001 11000111 Data hiding key 10 01 6
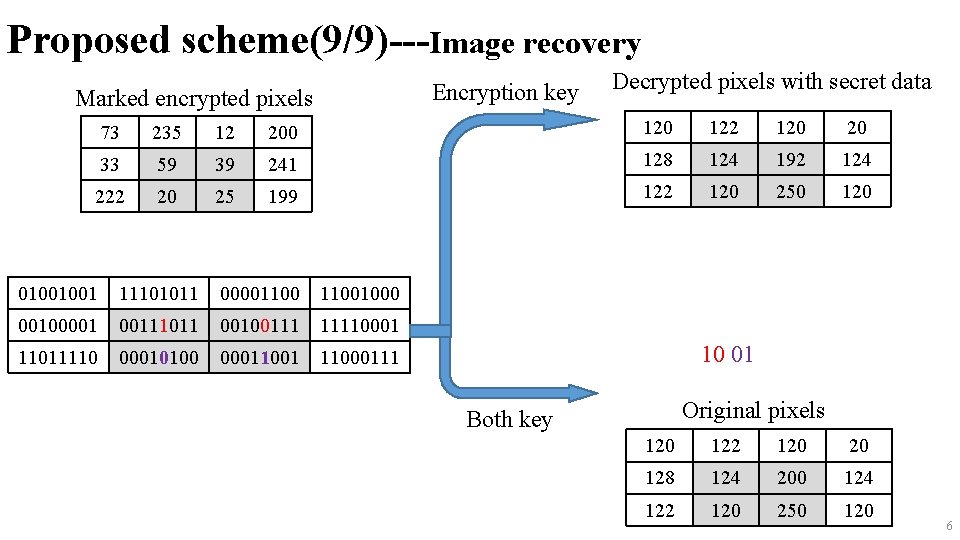
Proposed scheme(9/9)---Image recovery Encryption key Marked encrypted pixels Decrypted pixels with secret data 73 235 12 200 122 120 20 33 59 39 241 128 124 192 124 222 20 25 199 122 120 250 120 01001001 11101011 000011001000 00100001 00111011 00100111 11110001 11011110 00010100 00011001 11000111 10 01 Original pixels Both key 120 122 120 20 128 124 200 124 122 120 250 120 6
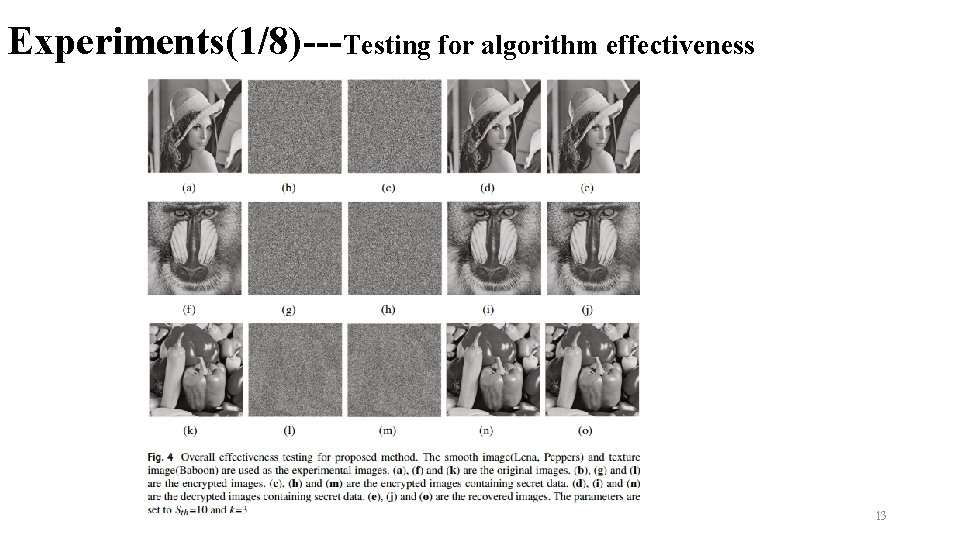
Experiments(1/8)---Testing for algorithm effectiveness 13
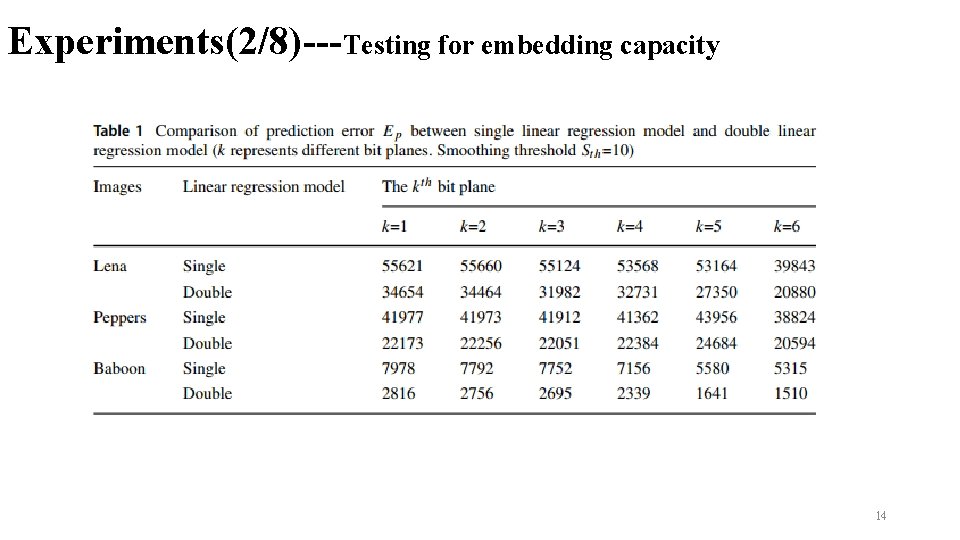
Experiments(2/8)---Testing for embedding capacity 14
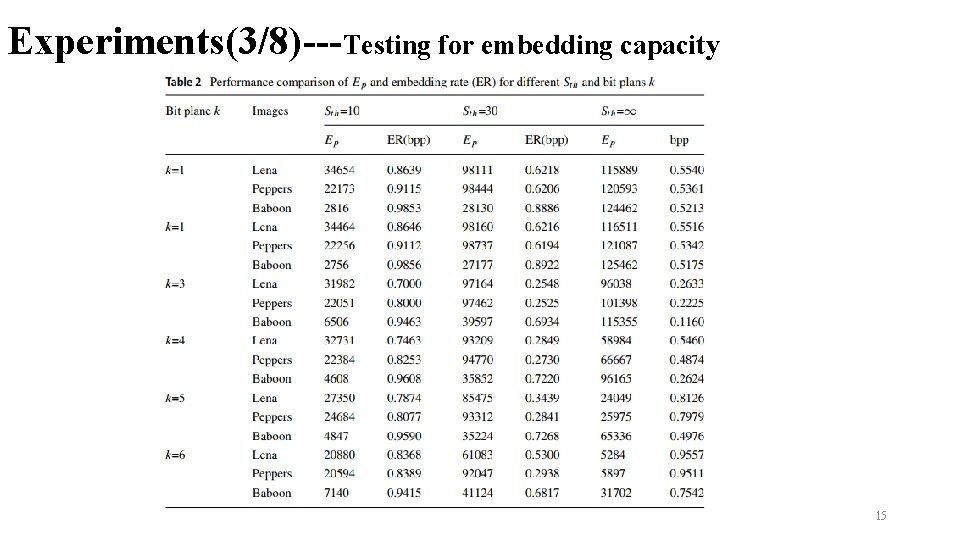
Experiments(3/8)---Testing for embedding capacity 15
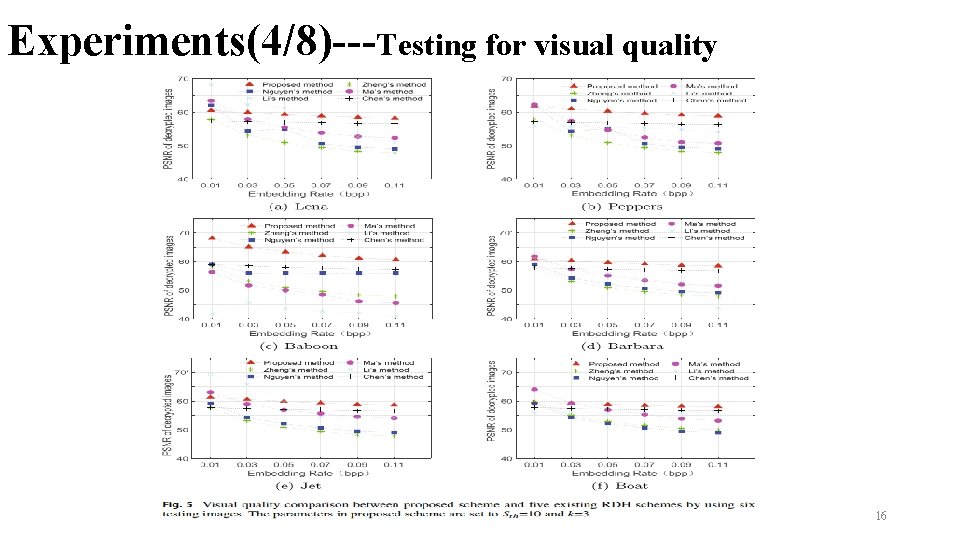
Experiments(4/8)---Testing for visual quality 16
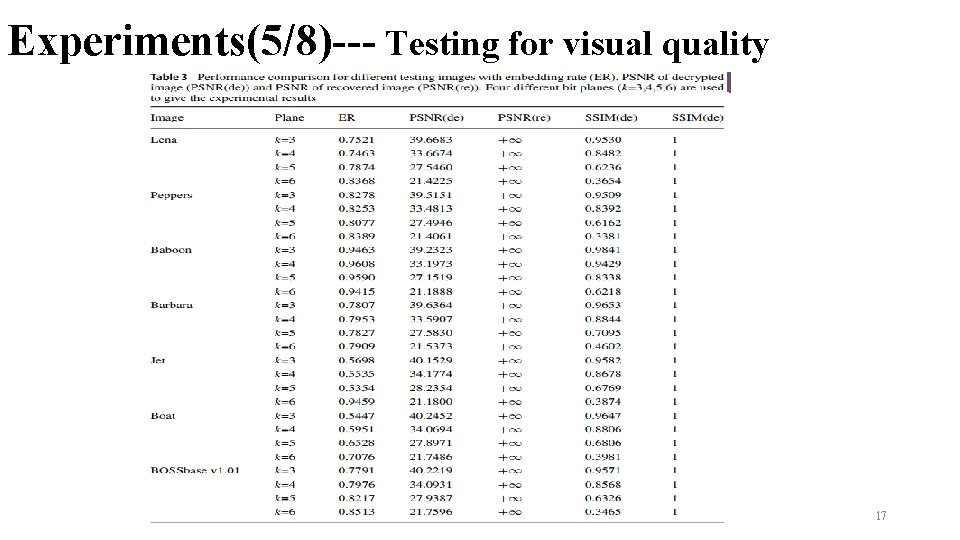
Experiments(5/8)--- Testing for visual quality 17
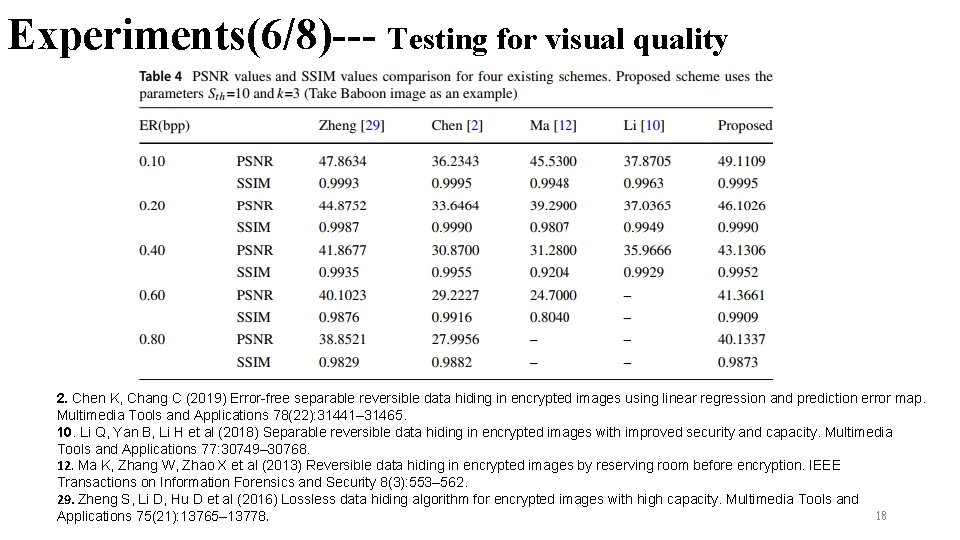
Experiments(6/8)--- Testing for visual quality 2. Chen K, Chang C (2019) Error-free separable reversible data hiding in encrypted images using linear regression and prediction error map. Multimedia Tools and Applications 78(22): 31441– 31465. 10. Li Q, Yan B, Li H et al (2018) Separable reversible data hiding in encrypted images with improved security and capacity. Multimedia Tools and Applications 77: 30749– 30768. 12. Ma K, Zhang W, Zhao X et al (2013) Reversible data hiding in encrypted images by reserving room before encryption. IEEE Transactions on Information Forensics and Security 8(3): 553– 562. 29. Zheng S, Li D, Hu D et al (2016) Lossless data hiding algorithm for encrypted images with high capacity. Multimedia Tools and 18 Applications 75(21): 13765– 13778.
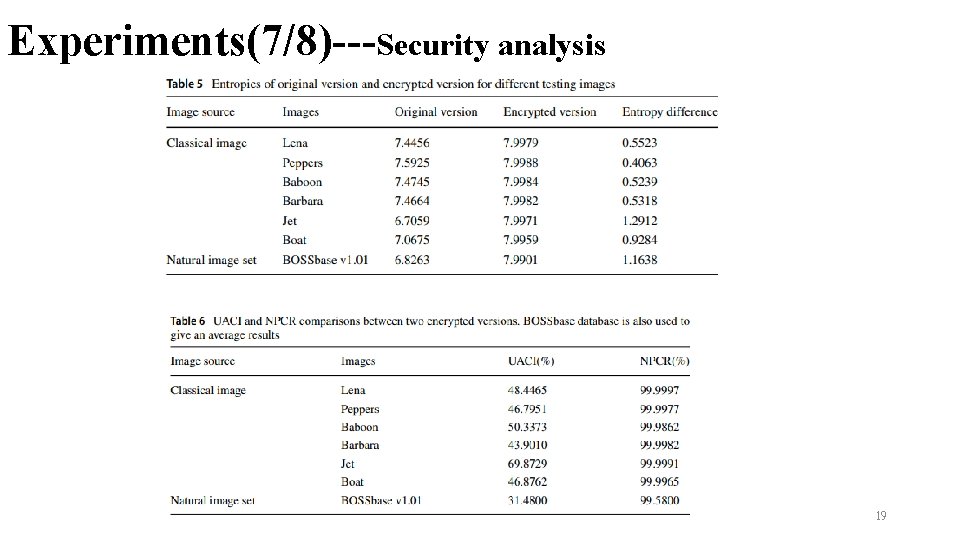
Experiments(7/8)---Security analysis 19
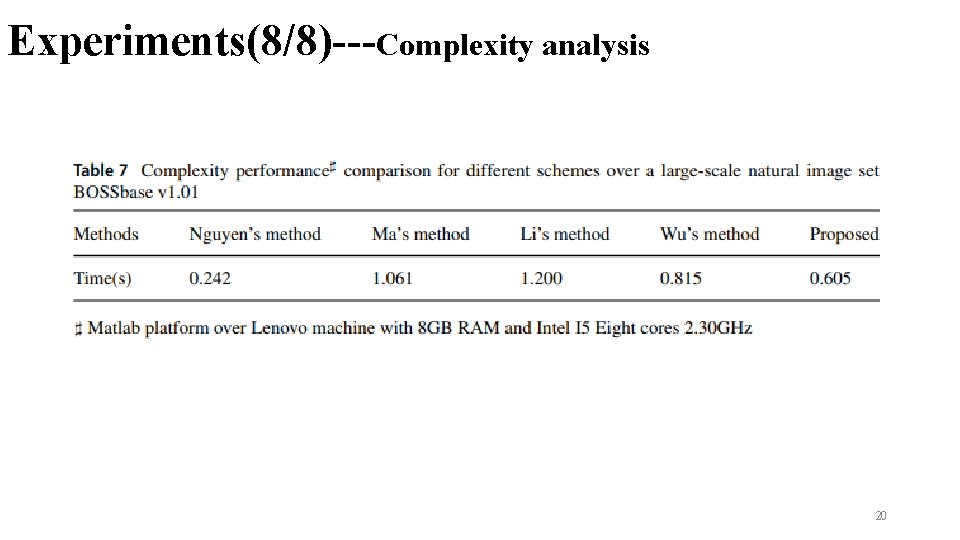
Experiments(8/8)---Complexity analysis 20
Conclusions ØDesign a double linear regression prediction model, which can further improve the prediction accuracy for the current pixe ØCompare to the existing solutions, our method has superior performance in terms of embedding capacity, visual quality and security performance 21
Thanks! 22
- Slides: 22