A Separable Reversible Data Hiding Scheme for Encrypted
A Separable Reversible Data Hiding Scheme for Encrypted Images Based on Tromino Scrambling and Adaptive Pixel Value Ordering u. Source : Signal Processing, Available online 7 July 2020, 107703 u. Authors : Min Long, Yu Zhao, Xiang Zhang and Fei Peng u. Speaker : Chia-Shou Shih u. Date : 2020/07/16 1
Outline �Introduction �Related work �Proposed method �Experimental results �Conclusions 2
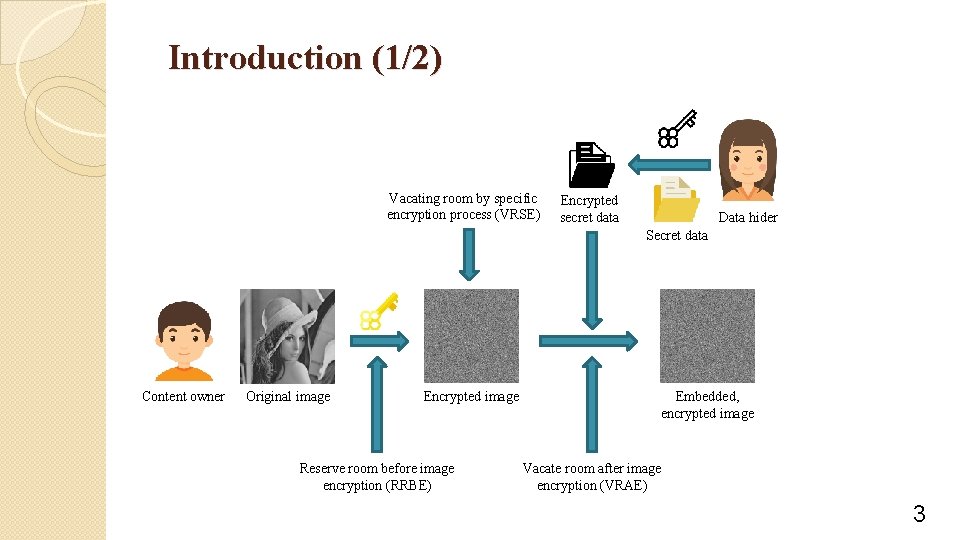
Introduction (1/2) Vacating room by specific encryption process (VRSE) Encrypted secret data Data hider Secret data Content owner Original image Encrypted image Reserve room before image encryption (RRBE) Embedded, encrypted image Vacate room after image encryption (VRAE) 3
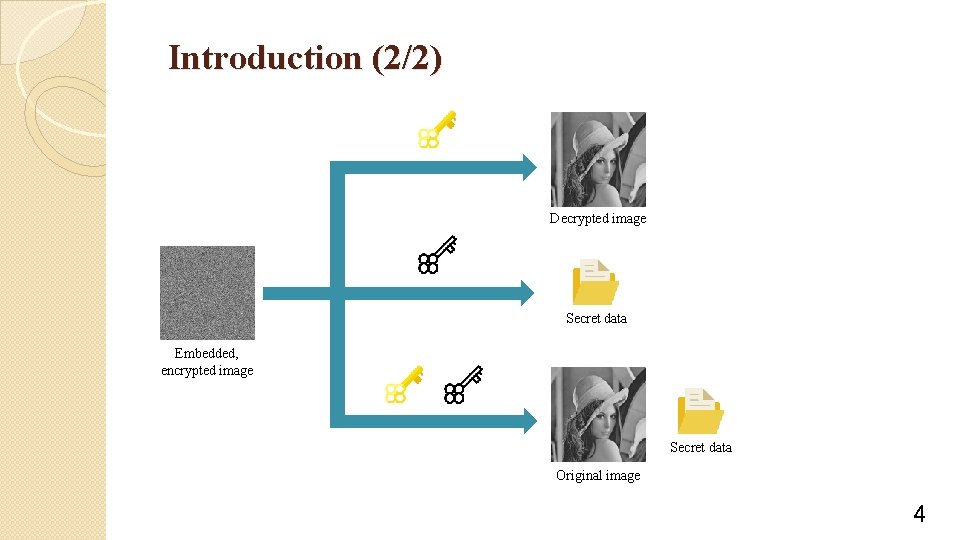
Introduction (2/2) Decrypted image Secret data Embedded, encrypted image Secret data Original image 4
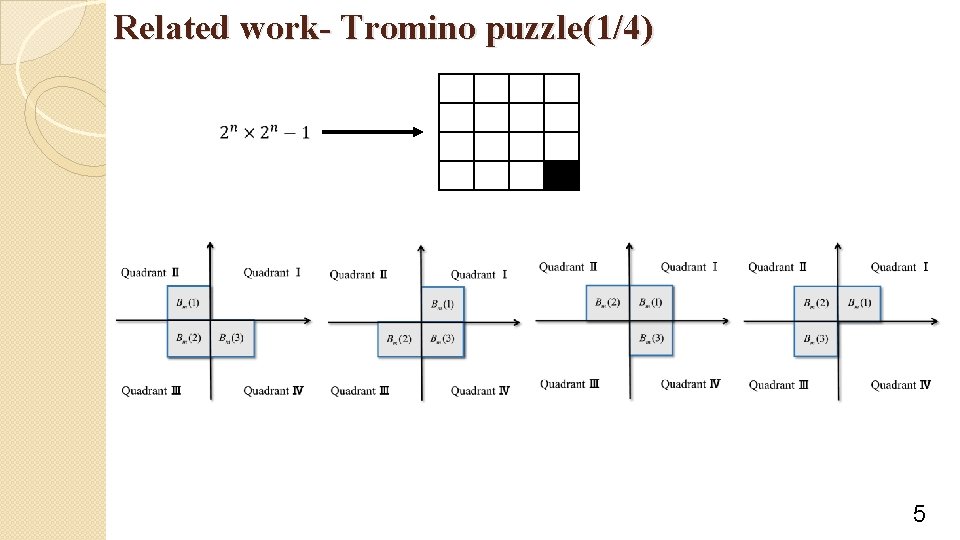
Related work- Tromino puzzle(1/4) 5
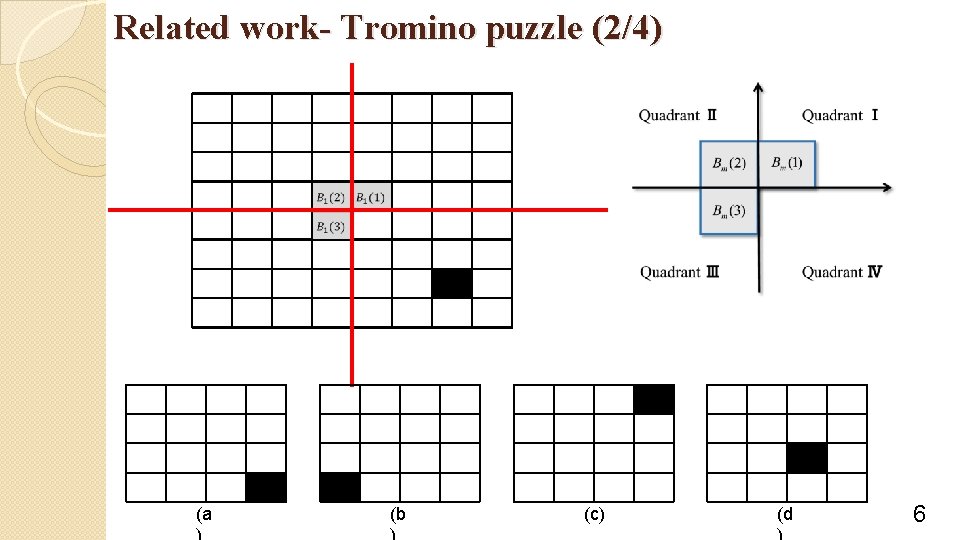
Related work- Tromino puzzle (2/4) (a (b (c) (d 6
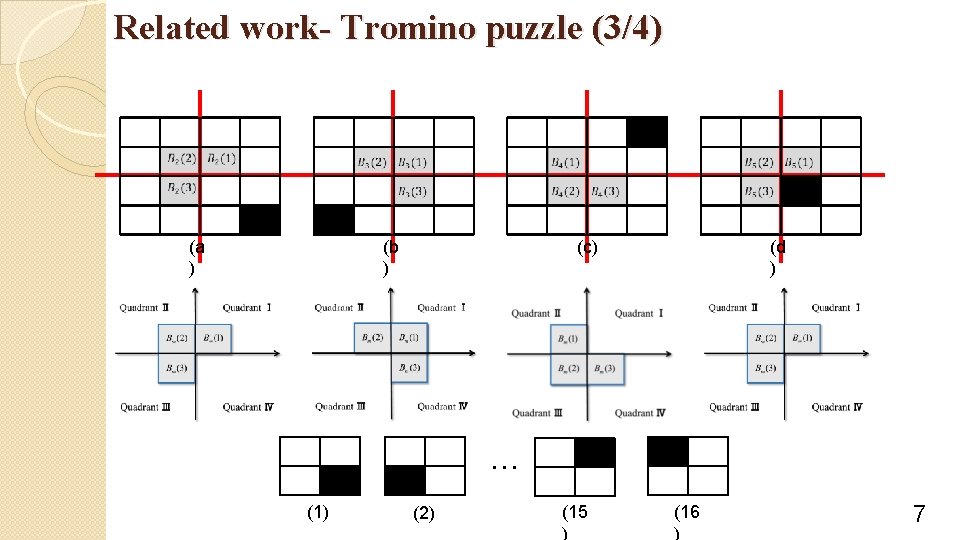
Related work- Tromino puzzle (3/4) (a ) (b ) (c) (d ) … (1) (2) (15 ) (16 ) 7
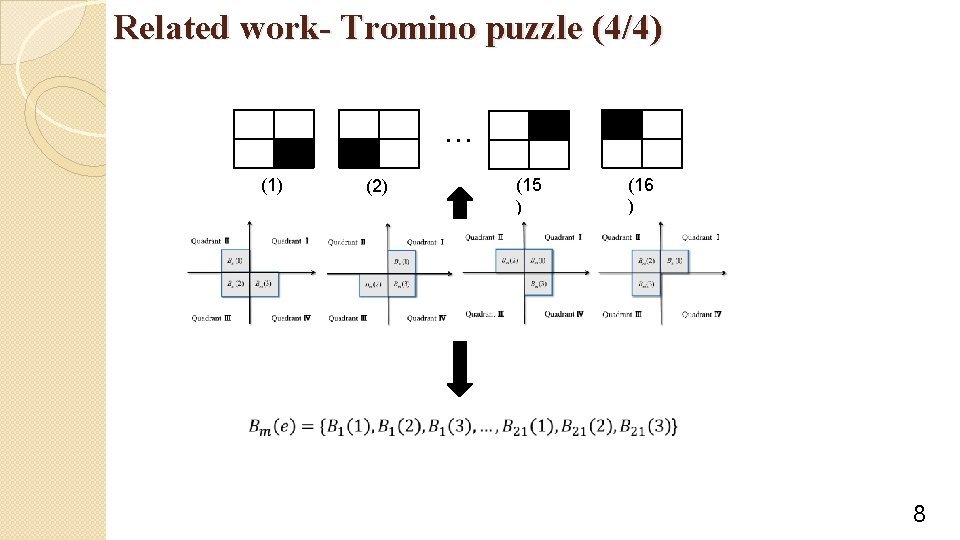
Related work- Tromino puzzle (4/4) … (1) (2) (15 ) (16 ) 8
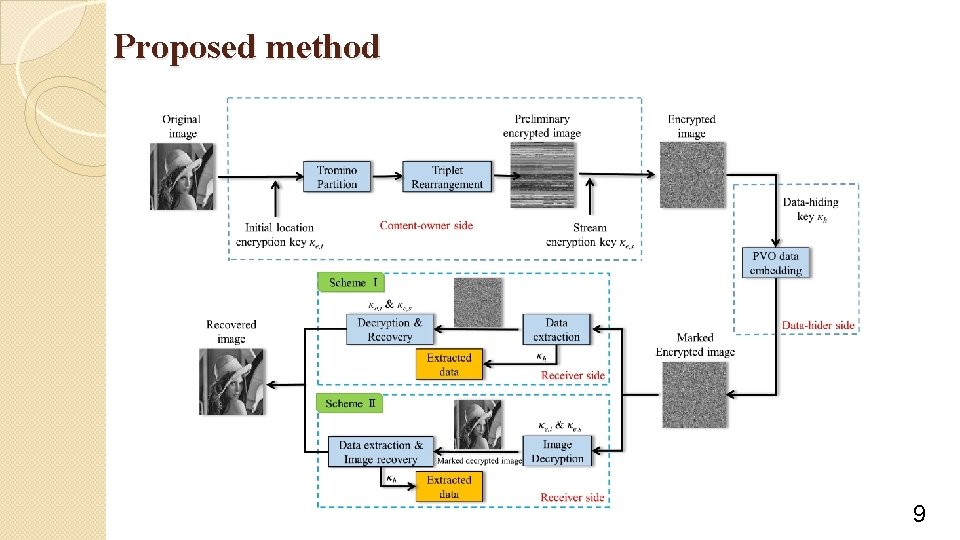
Proposed method 9
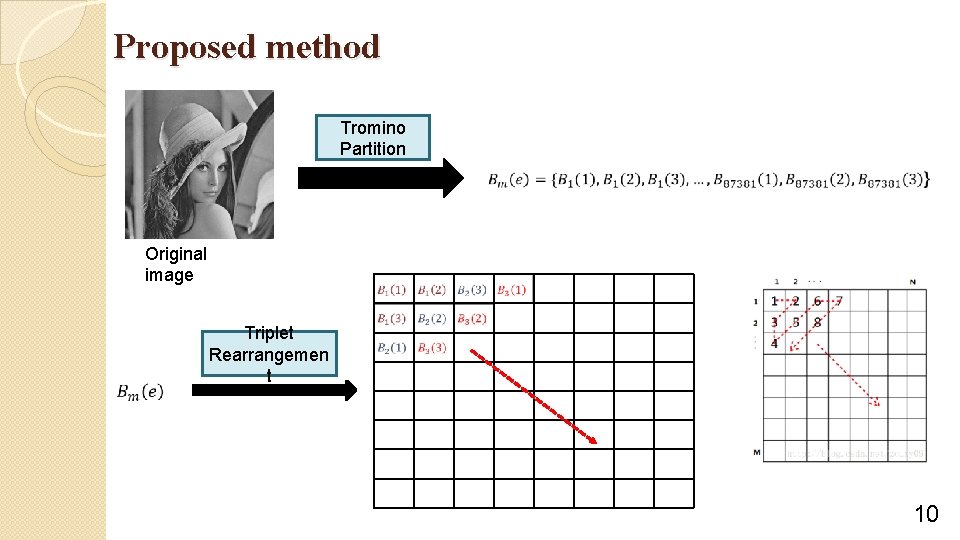
Proposed method Tromino Partition Original image Triplet Rearrangemen t 10
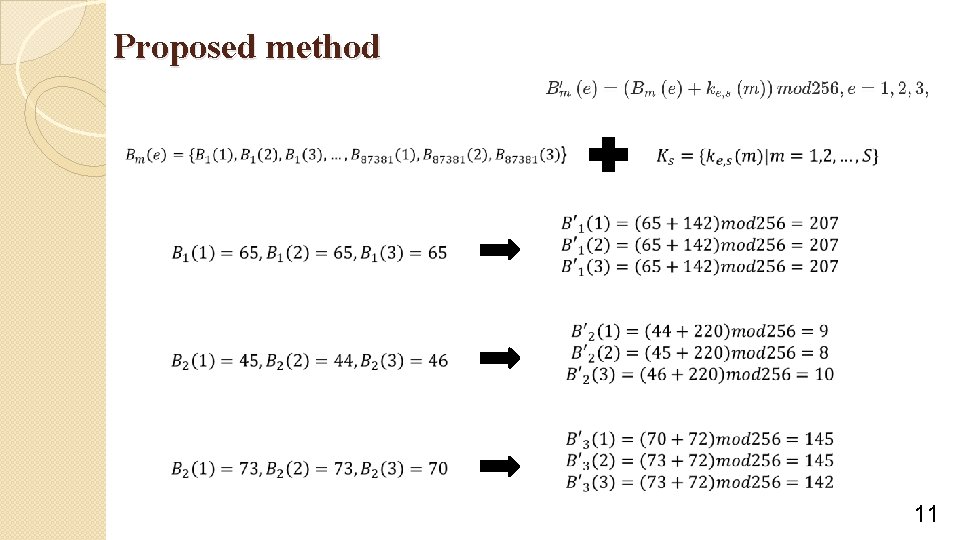
Proposed method 11
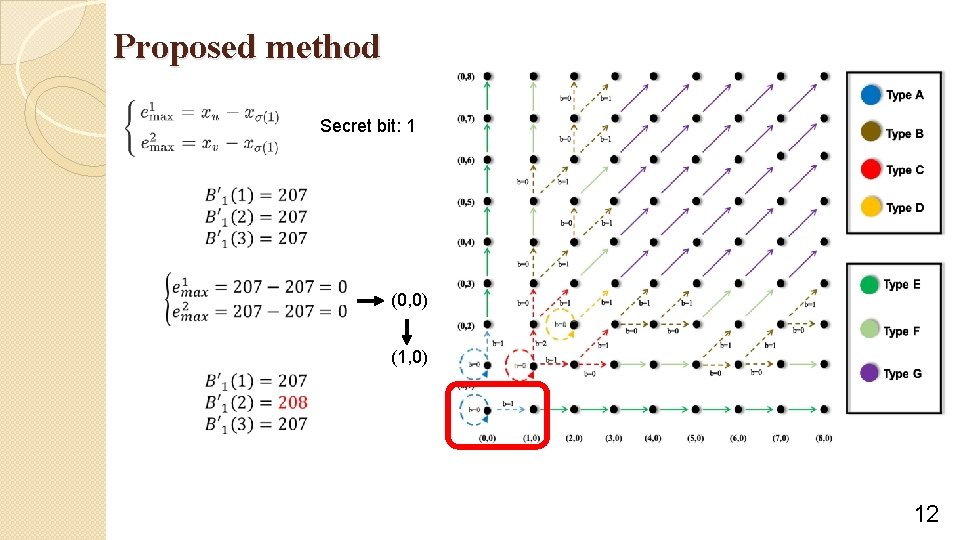
Proposed method Secret bit: 1 (0, 0) (1, 0) 12
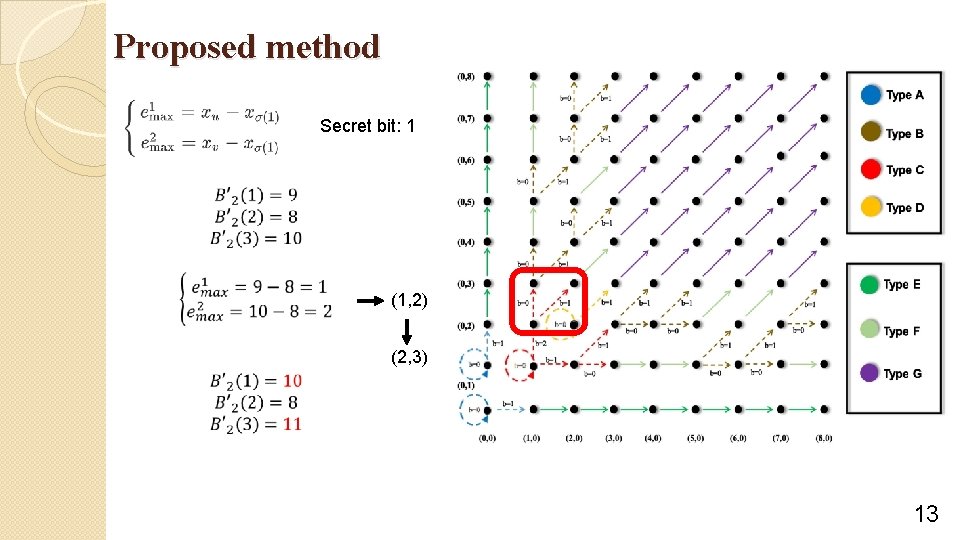
Proposed method Secret bit: 1 (1, 2) (2, 3) 13
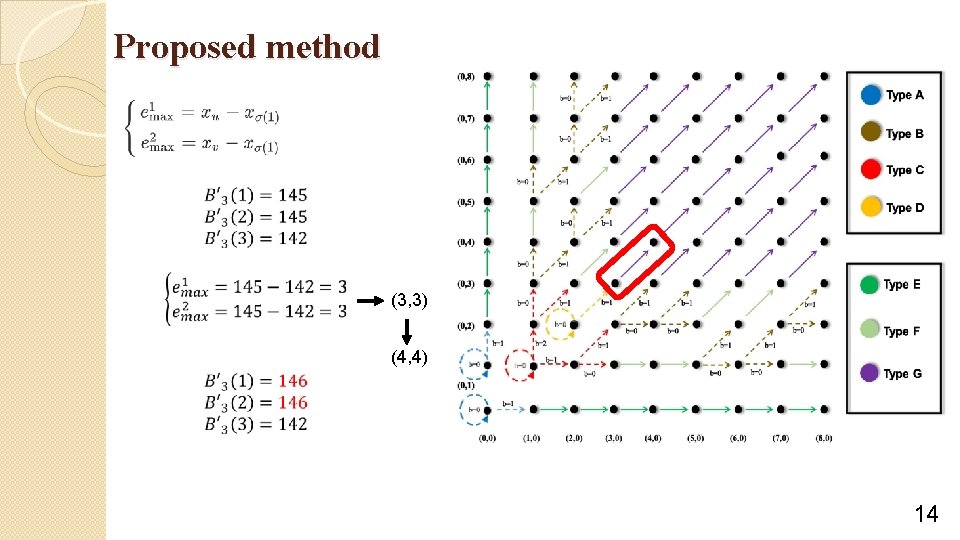
Proposed method (3, 3) (4, 4) 14
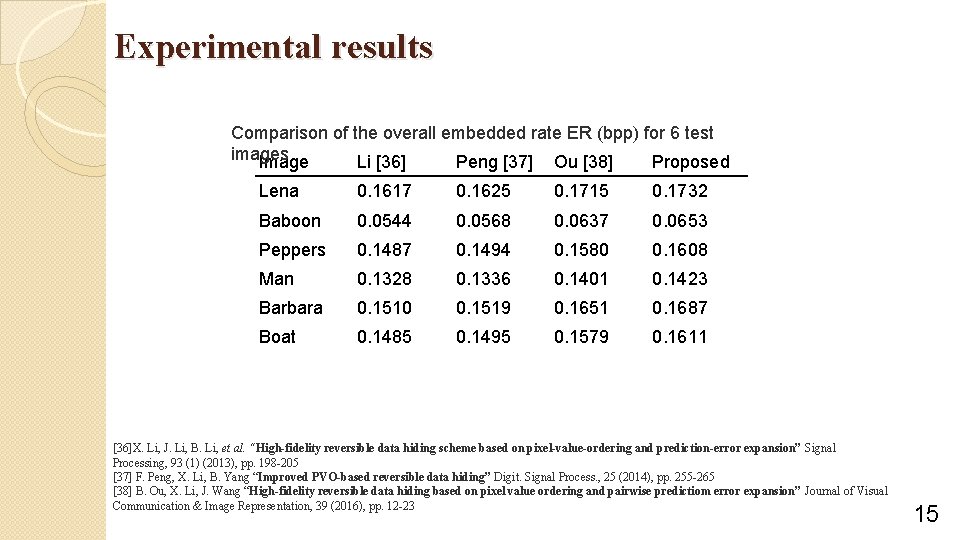
Experimental results Comparison of the overall embedded rate ER (bpp) for 6 test images Image Li [36] Peng [37] Ou [38] Proposed Lena 0. 1617 0. 1625 0. 1715 0. 1732 Baboon 0. 0544 0. 0568 0. 0637 0. 0653 Peppers 0. 1487 0. 1494 0. 1580 0. 1608 Man 0. 1328 0. 1336 0. 1401 0. 1423 Barbara 0. 1510 0. 1519 0. 1651 0. 1687 Boat 0. 1485 0. 1495 0. 1579 0. 1611 [36]X. Li, J. Li, B. Li, et al. “High-fidelity reversible data hiding scheme based on pixel-value-ordering and prediction-error expansion” Signal Processing, 93 (1) (2013), pp. 198 -205 [37] F. Peng, X. Li, B. Yang “Improved PVO-based reversible data hiding” Digit. Signal Process. , 25 (2014), pp. 255 -265 [38] B. Ou, X. Li, J. Wang “High-fidelity reversible data hiding based on pixel value ordering and pairwise predictiom error expansion” Journal of Visual Communication & Image Representation, 39 (2016), pp. 12 -23 15
![Experimental results Comparison of imperceptibility Image ER Li [36] Peng[37] Ou [38] Proposed Lena Experimental results Comparison of imperceptibility Image ER Li [36] Peng[37] Ou [38] Proposed Lena](http://slidetodoc.com/presentation_image_h/80ada52970ada4d9a7333925cfd8d45e/image-16.jpg)
Experimental results Comparison of imperceptibility Image ER Li [36] Peng[37] Ou [38] Proposed Lena 0. 0572 56. 6731 56. 5134 56. 7413 57. 3149 0. 1444 51. 8452 51. 8627 52. 5964 53. 1425 0. 1526 47. 5814 47. 7623 48. 3571 48. 9171 0. 0191 55. 7756 55. 6374 57. 1396 57. 4712 0. 0382 52. 1938 52. 2769 52. 9477 53. 2448 0. 0572 - - 48. 9313 49. 2430 0. 0382 57. 3421 57. 0264 57. 5438 58. 0488 0. 0763 52. 9122 52. 8334 53. 5208 53. 8914 0. 1444 50. 0537 50. 0457 50. 8826 51. 2340 0. 0382 55. 0477 54. 9317 55. 3784 56. 0442 0. 0763 50. 6229 50. 7475 51. 2275 52. 4178 0. 1444 47. 3154 47. 3958 47. 7339 47. 9451 0. 0382 58. 5324 58. 4154 58. 9412 59. 1574 0. 0763 54. 2167 54. 2232 54. 8036 54. 9963 0. 1444 50. 3437 50. 6144 51. 7340 52. 0047 0. 0382 56. 3541 56. 3417 56. 6140 57. 3081 0. 0763 51. 6478 51. 8431 52. 5127 53. 7432 0. 1444 48. 6742 48. 7364 49. 1127 50. 1169 Baboon Peppers Man Barbara Boat 16
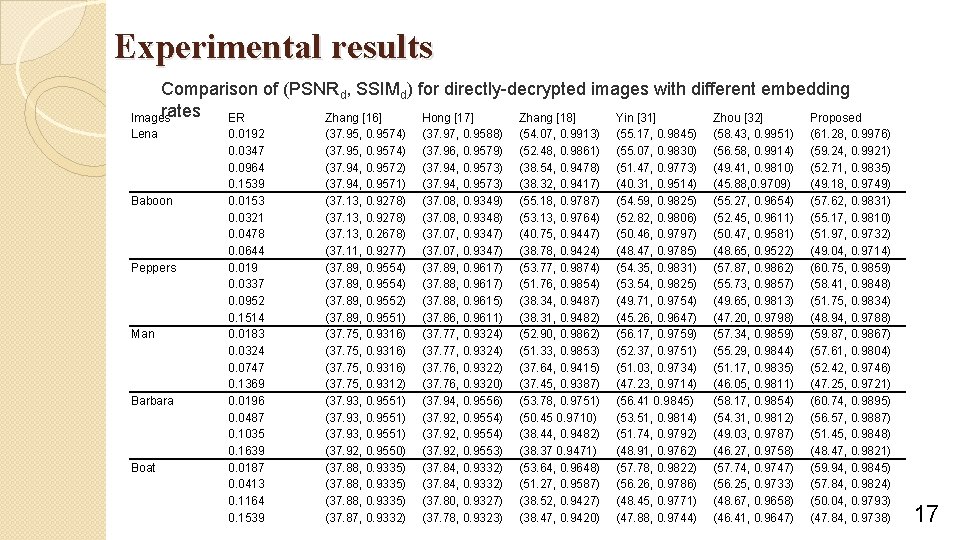
Experimental results Comparison of (PSNRd, SSIMd) for directly-decrypted images with different embedding rates ER Images Zhang [16] Hong [17] Zhang [18] Yin [31] Zhou [32] Proposed Lena Baboon Peppers Man Barbara Boat 0. 0192 0. 0347 0. 0964 0. 1539 0. 0153 0. 0321 0. 0478 0. 0644 0. 019 0. 0337 0. 0952 0. 1514 0. 0183 0. 0324 0. 0747 0. 1369 0. 0196 0. 0487 0. 1035 0. 1639 0. 0187 0. 0413 0. 1164 0. 1539 (37. 95, 0. 9574) (37. 94, 0. 9572) (37. 94, 0. 9571) (37. 13, 0. 9278) (37. 13, 0. 2678) (37. 11, 0. 9277) (37. 89, 0. 9554) (37. 89, 0. 9552) (37. 89, 0. 9551) (37. 75, 0. 9316) (37. 75, 0. 9312) (37. 93, 0. 9551) (37. 92, 0. 9550) (37. 88, 0. 9335) (37. 87, 0. 9332) (37. 97, 0. 9588) (37. 96, 0. 9579) (37. 94, 0. 9573) (37. 08, 0. 9349) (37. 08, 0. 9348) (37. 07, 0. 9347) (37. 89, 0. 9617) (37. 88, 0. 9615) (37. 86, 0. 9611) (37. 77, 0. 9324) (37. 76, 0. 9322) (37. 76, 0. 9320) (37. 94, 0. 9556) (37. 92, 0. 9554) (37. 92, 0. 9553) (37. 84, 0. 9332) (37. 80, 0. 9327) (37. 78, 0. 9323) (54. 07, 0. 9913) (52. 48, 0. 9861) (38. 54, 0. 9478) (38. 32, 0. 9417) (55. 18, 0. 9787) (53. 13, 0. 9764) (40. 75, 0. 9447) (38. 78, 0. 9424) (53. 77, 0. 9874) (51. 76, 0. 9854) (38. 34, 0. 9487) (38. 31, 0. 9482) (52. 90, 0. 9862) (51. 33, 0. 9853) (37. 64, 0. 9415) (37. 45, 0. 9387) (53. 78, 0. 9751) (50. 45 0. 9710) (38. 44, 0. 9482) (38. 37 0. 9471) (53. 64, 0. 9648) (51. 27, 0. 9587) (38. 52, 0. 9427) (38. 47, 0. 9420) (55. 17, 0. 9845) (55. 07, 0. 9830) (51. 47, 0. 9773) (40. 31, 0. 9514) (54. 59, 0. 9825) (52. 82, 0. 9806) (50. 46, 0. 9797) (48. 47, 0. 9785) (54. 35, 0. 9831) (53. 54, 0. 9825) (49. 71, 0. 9754) (45. 26, 0. 9647) (56. 17, 0. 9759) (52. 37, 0. 9751) (51. 03, 0. 9734) (47. 23, 0. 9714) (56. 41 0. 9845) (53. 51, 0. 9814) (51. 74, 0. 9792) (48. 91, 0. 9762) (57. 78, 0. 9822) (56. 26, 0. 9786) (48. 45, 0. 9771) (47. 88, 0. 9744) (58. 43, 0. 9951) (56. 58, 0. 9914) (49. 41, 0. 9810) (45. 88, 0. 9709) (55. 27, 0. 9654) (52. 45, 0. 9611) (50. 47, 0. 9581) (48. 65, 0. 9522) (57. 87, 0. 9862) (55. 73, 0. 9857) (49. 65, 0. 9813) (47. 20, 0. 9798) (57. 34, 0. 9859) (55. 29, 0. 9844) (51. 17, 0. 9835) (46. 05, 0. 9811) (58. 17, 0. 9854) (54. 31, 0. 9812) (49. 03, 0. 9787) (46. 27, 0. 9758) (57. 74, 0. 9747) (56. 25, 0. 9733) (48. 67, 0. 9658) (46. 41, 0. 9647) (61. 28, 0. 9976) (59. 24, 0. 9921) (52. 71, 0. 9835) (49. 18, 0. 9749) (57. 62, 0. 9831) (55. 17, 0. 9810) (51. 97, 0. 9732) (49. 04, 0. 9714) (60. 75, 0. 9859) (58. 41, 0. 9848) (51. 75, 0. 9834) (48. 94, 0. 9788) (59. 87, 0. 9867) (57. 61, 0. 9804) (52. 42, 0. 9746) (47. 25, 0. 9721) (60. 74, 0. 9895) (56. 57, 0. 9887) (51. 45, 0. 9848) (48. 47, 0. 9821) (59. 94, 0. 9845) (57. 84, 0. 9824) (50. 04, 0. 9793) (47. 84, 0. 9738) 17
![Experimental results [16] X. Zhang “Reversible data hiding in encrypted image” IEEE Signal Processing Experimental results [16] X. Zhang “Reversible data hiding in encrypted image” IEEE Signal Processing](http://slidetodoc.com/presentation_image_h/80ada52970ada4d9a7333925cfd8d45e/image-18.jpg)
Experimental results [16] X. Zhang “Reversible data hiding in encrypted image” IEEE Signal Processing Letters, 18 (4) (2011), pp. 255 -258 [17] W. Hong, T. Chen, H. Wu “An improved reversible data hiding in encrypted images using side match” IEEE Signal Processing Letters, 19 (4) (2012), pp. 199 -202 [18] X. Zhang “Separable reversible data hiding in encrypted Image” IEEE Signal Processing Letters, 7 (2) (2012), pp. 826 -832 [31] B. X. Yin, F. Chen, H. He, S. Yan “Separable reversible data hiding in encrypted image with classification Permutation” Proceedings of 2017 IEEE Third International Conference on Multimedia Big Data (2017), pp. 201 -204 [32] J. Zhou, W. Sun, L. Dong, et al. “Secure reversible image data hiding over encrypted domain via key modulation” IEEE Transactions on Circuits & Systems for Video Technology, 26 (3) (2016), pp. 441 -452 18
Conclusions �Tromino scrambling �Adaptive pixel value ordering 1
-END- 2
- Slides: 20