Reversible data hiding in encrypted images with additive
Reversible data hiding in encrypted images with additive and multiplicative public-key homomorphism Source: Signal Processing 2019 Authors: Bing Chen, Xiaotian Wu, Wei Lu, Honglin Ren Speaker: Keju Meng Date: 08/08/2019 1
Outline • • • Introduction Preliminaries Proposed schemes Experimental results Conclusions 2
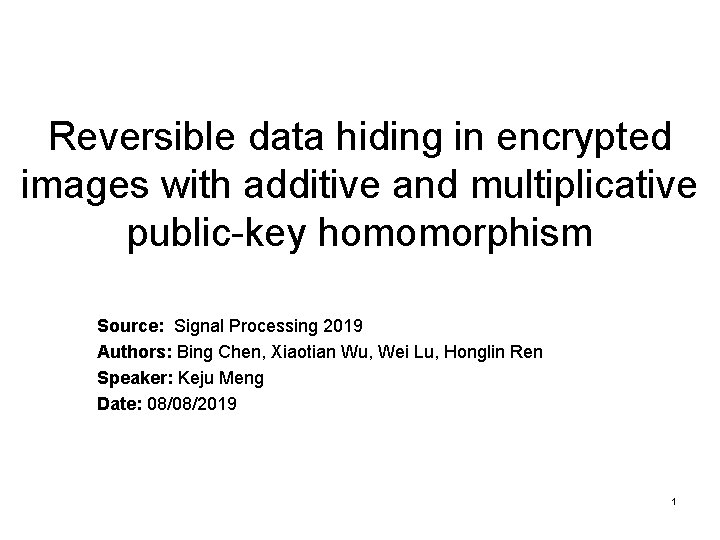
Introduction(1/2) 3
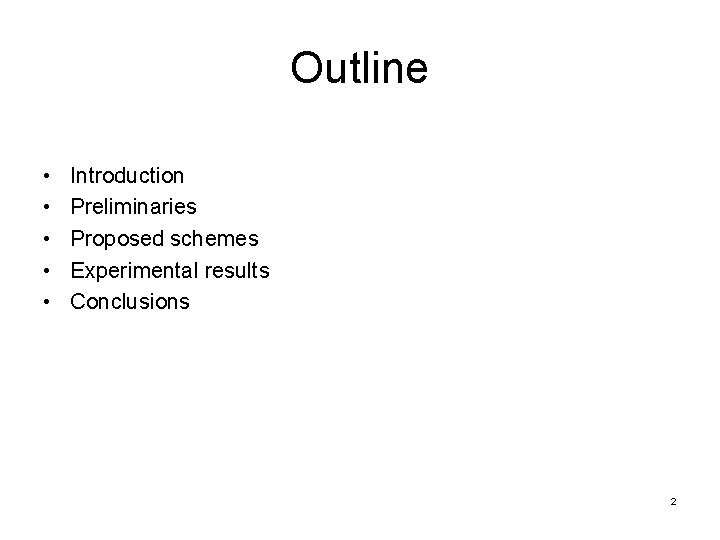
Introduction(2/2) 4
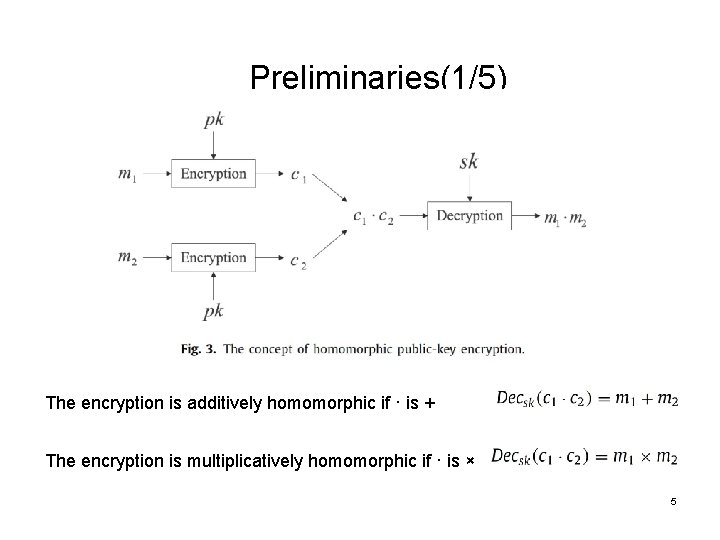
Preliminaries(1/5) The encryption is additively homomorphic if · is + The encryption is multiplicatively homomorphic if · is × 5

Preliminaries(2/5) Probabilistic encryption Dec(0) = 0 or 1 Dec(1) = 2 or 3 How to use the encryption to implement data hiding? Plaintext: 0 1 1 0 Ciphertext: 1 3 2 0 Secret stream: 1 0 1 1 Modified Ciphertext: 1 2 3 1 6
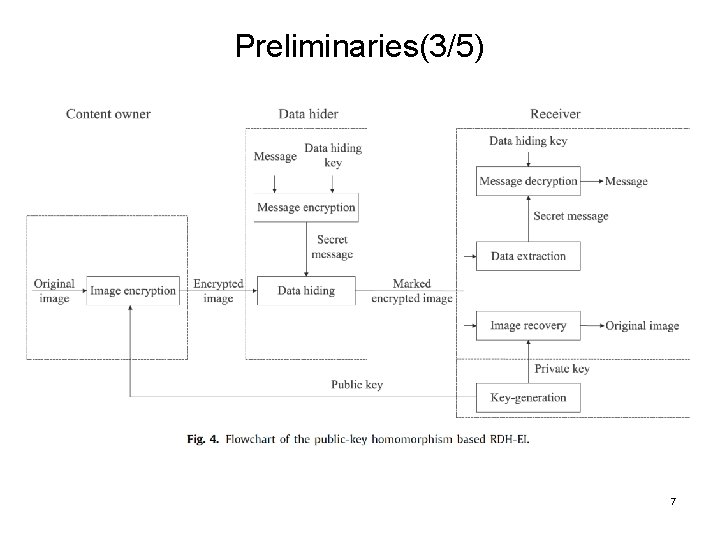
Preliminaries(3/5) 7
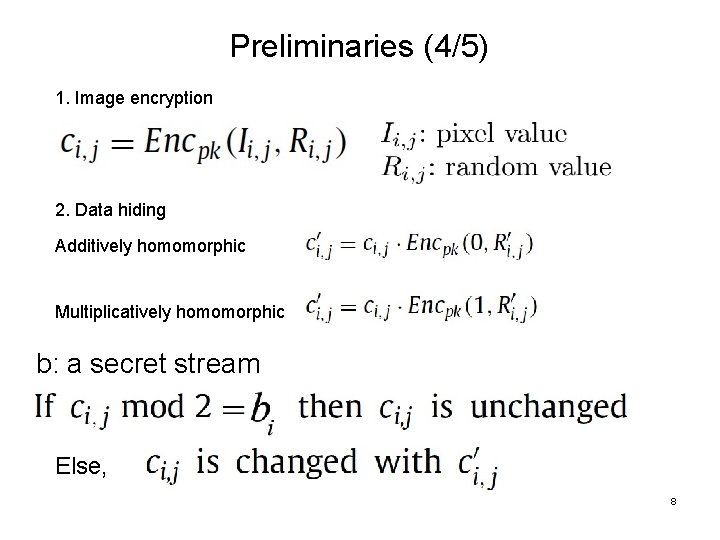
Preliminaries (4/5) 1. Image encryption 2. Data hiding Additively homomorphic Multiplicatively homomorphic b: a secret stream Else, 8
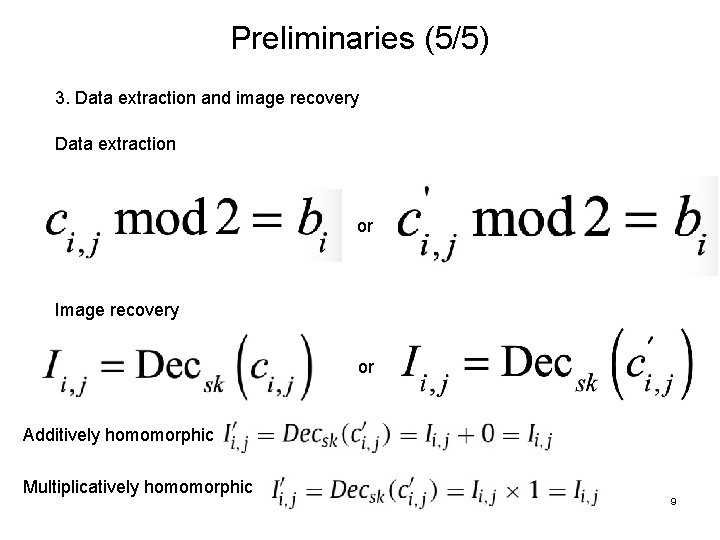
Preliminaries (5/5) 3. Data extraction and image recovery Data extraction or Image recovery or Additively homomorphic Multiplicatively homomorphic 9
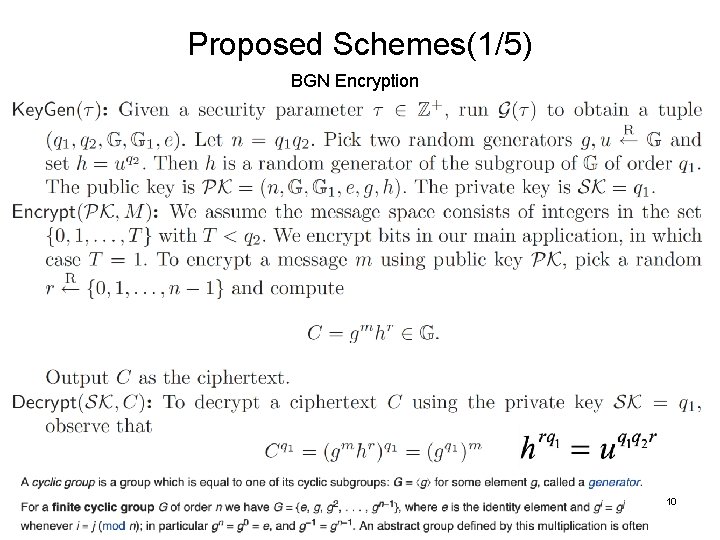
Proposed Schemes(1/5) BGN Encryption Boneh D, Goh E J, Nissim K. Evaluating 2 -DNF formulas on ciphertexts[C]//Theory of Cryptography Conference. Springer, Berlin, Heidelberg, 2005: 325 -341. 10
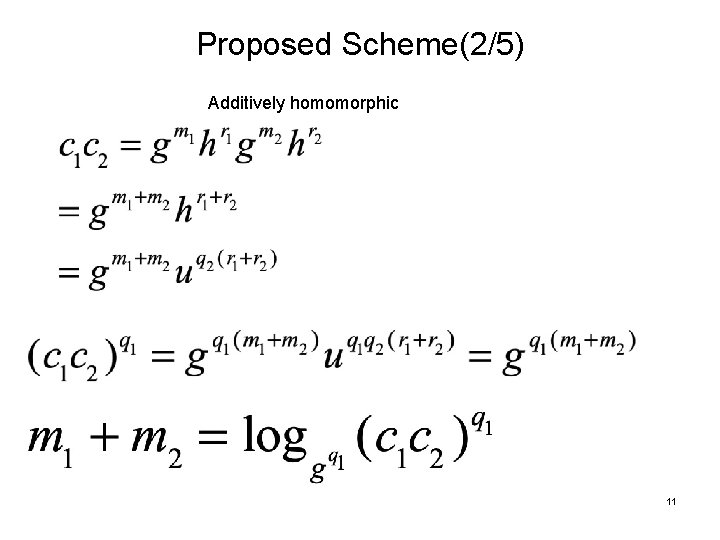
Proposed Scheme(2/5) Additively homomorphic 11
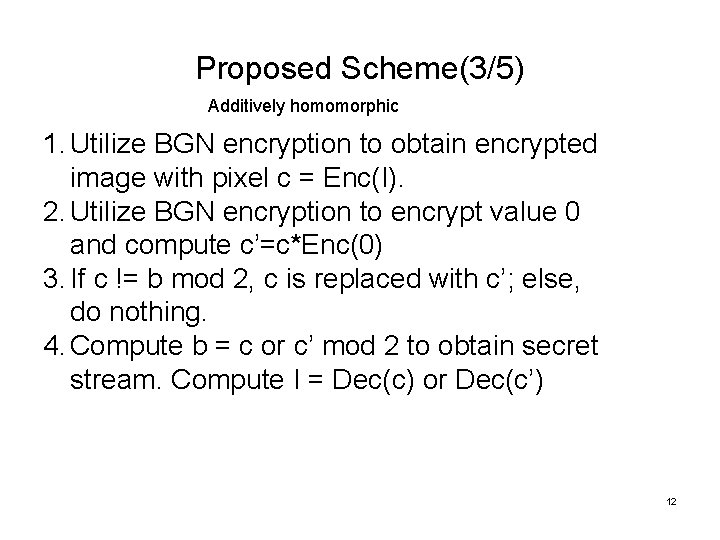
Proposed Scheme(3/5) Additively homomorphic 1. Utilize BGN encryption to obtain encrypted image with pixel c = Enc(I). 2. Utilize BGN encryption to encrypt value 0 and compute c’=c*Enc(0) 3. If c != b mod 2, c is replaced with c’; else, do nothing. 4. Compute b = c or c’ mod 2 to obtain secret stream. Compute I = Dec(c) or Dec(c’) 12
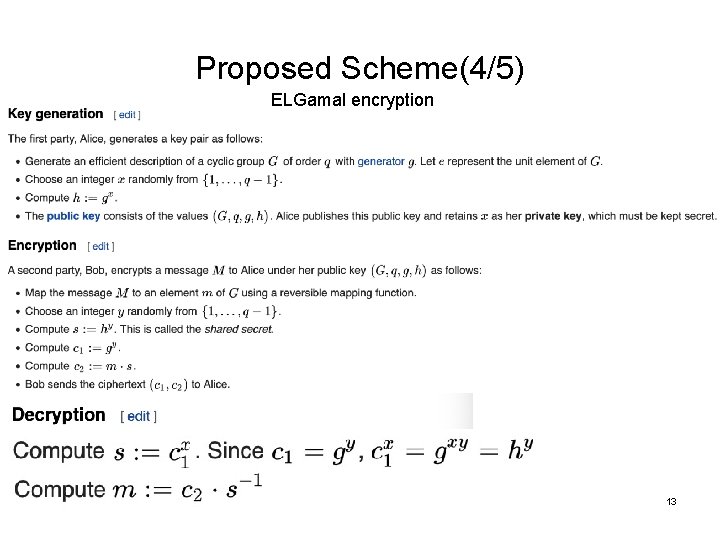
Proposed Scheme(4/5) ELGamal encryption 13

Proposed Scheme(5/5) Multiplicatively homomorphic 1. Utilize ELGamal encryption to obtain encrypted image with pixel c 1, c 2 = Enc(I). 2. Utilize ELGamal encryption to encrypt value 0 and compute c 1’= c 1 *Enc(1), c 2’= c 2*Enc(1) 3. If c 1 != b mod 2, c 1 c 2 are replaced with c 1, c 2 ; else, do nothing. 4. Compute b = c or c’ mod 2 to obtain secret stream. Compute I = Dec(c 1, c 2) or Dec(c 1’, c 2’) 14
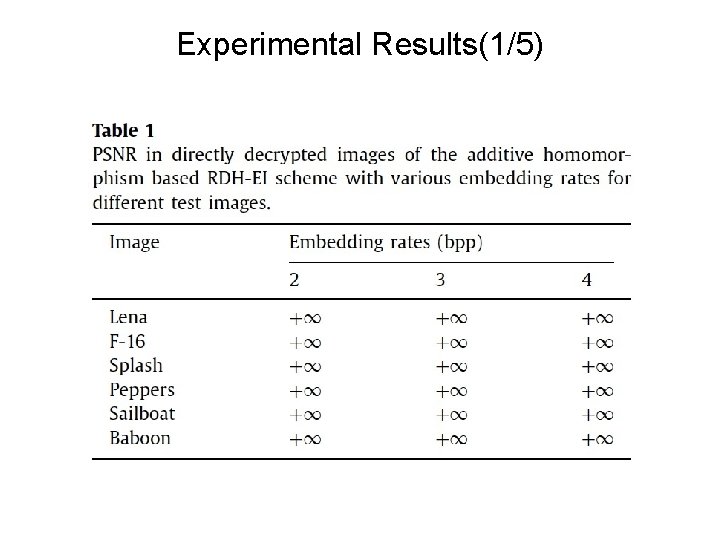
Experimental Results(1/5)
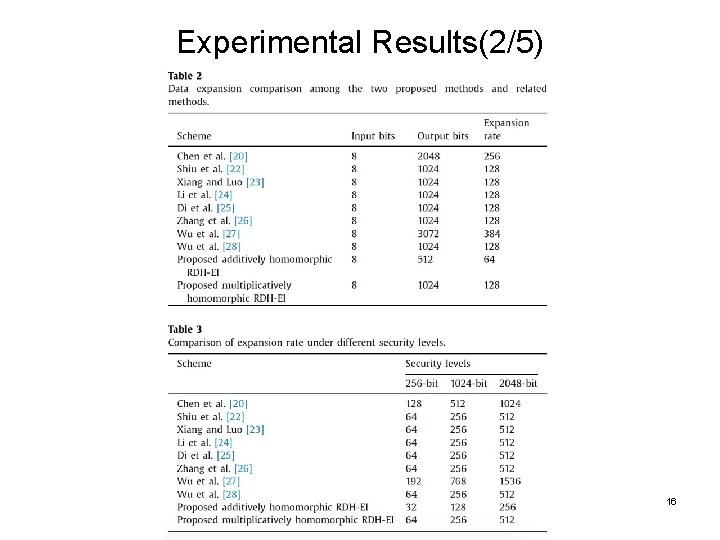
Experimental Results(2/5) 16
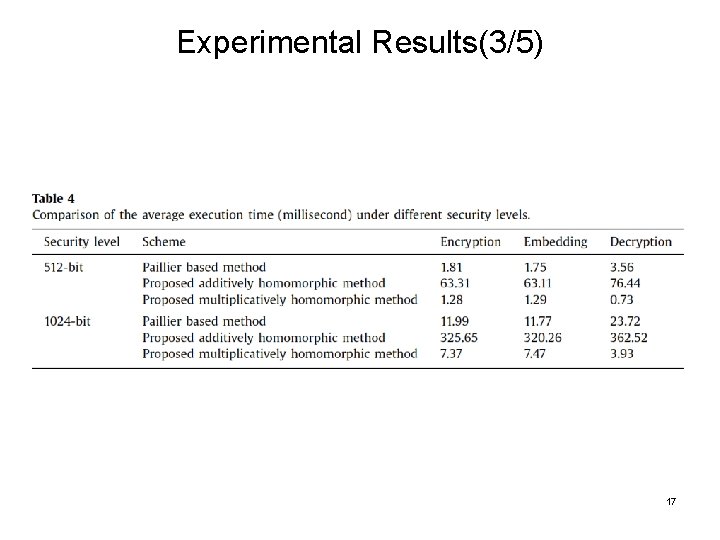
Experimental Results(3/5) 17
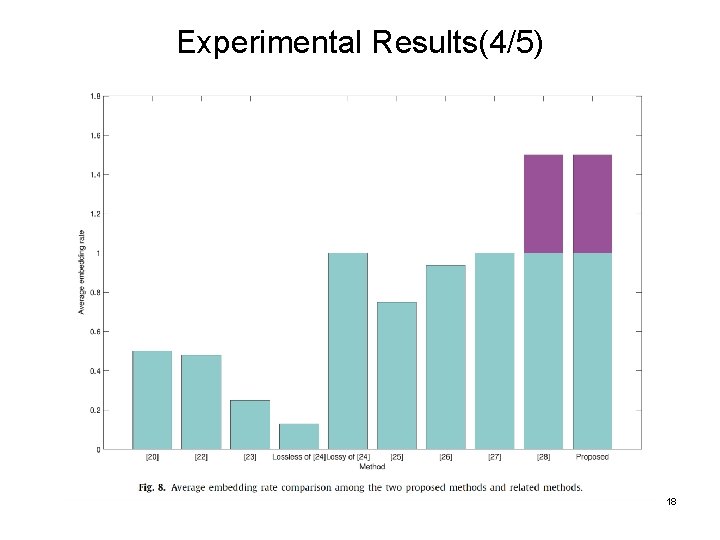
Experimental Results(4/5) 18
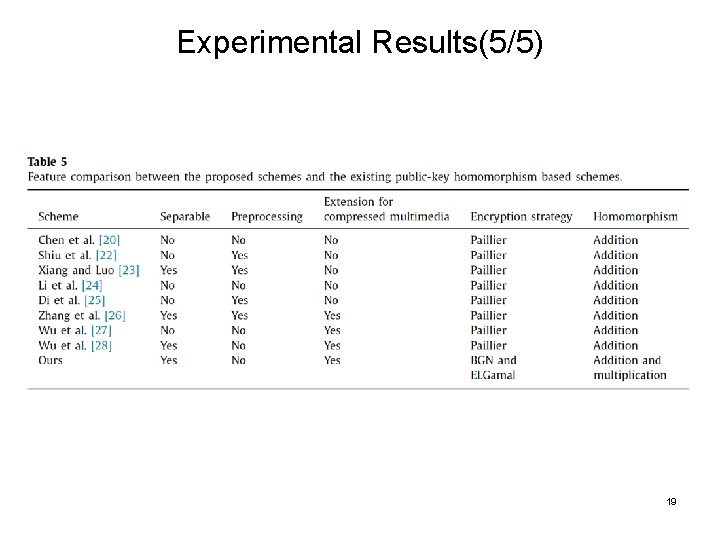
Experimental Results(5/5) 19
Conclusions • Two simple and efficient RDH-EI schemes are proposed. • How to reduce pixel expansion and improve embedding capacity? 20
- Slides: 20