Reversible Data Hiding in Encrypted Images using Chunk
Reversible Data Hiding in Encrypted Images using Chunk Encryption and Redundancy Matrix Representation Source: IEEE Transactions on Dependable and Secure Computing (2020, early access) Authors: Zi-Long Liu and Chi-Man Pun Speaker: Wang Xu Date: 2020/08/20
Outline • Introduction • Proposed method • Experiment results • Conclusions
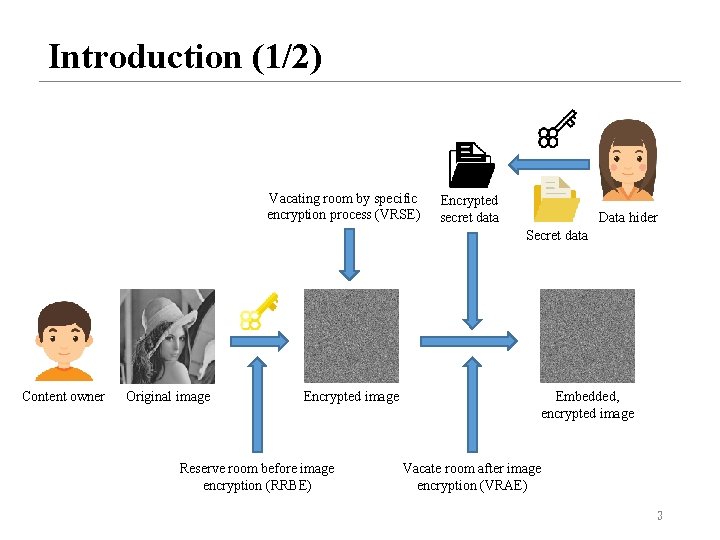
Introduction (1/2) Vacating room by specific encryption process (VRSE) Encrypted secret data Data hider Secret data Content owner Original image Encrypted image Reserve room before image encryption (RRBE) Embedded, encrypted image Vacate room after image encryption (VRAE) 3
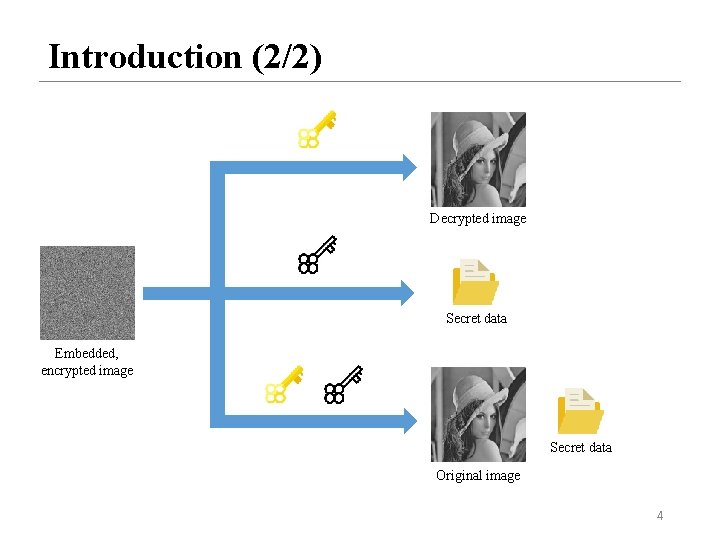
Introduction (2/2) Decrypted image Secret data Embedded, encrypted image Secret data Original image 4
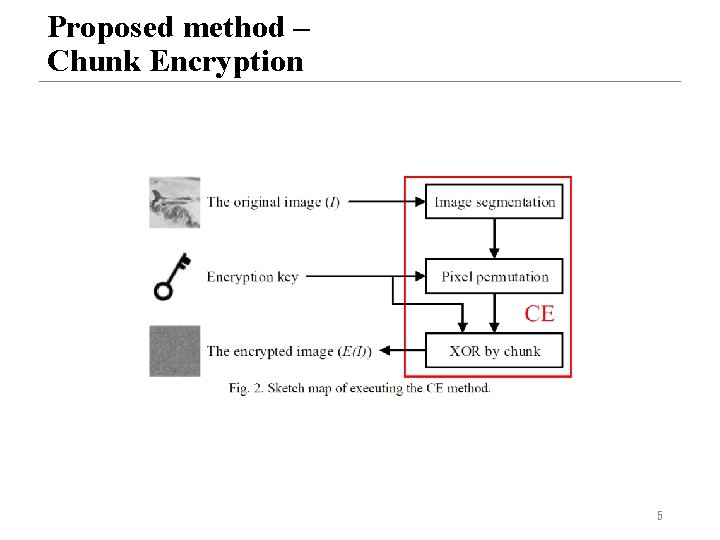
Proposed method – Chunk Encryption 5
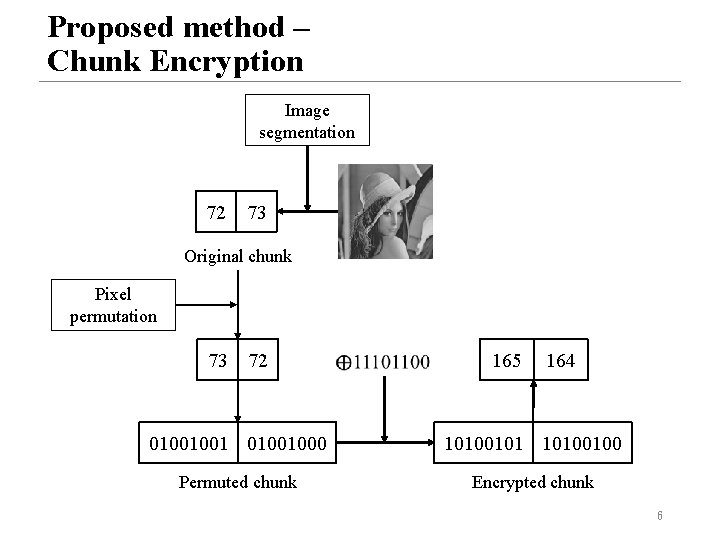
Proposed method – Chunk Encryption Image segmentation 72 73 Original chunk Pixel permutation 73 72 165 164 01001001000 10100101 10100100 Permuted chunk Encrypted chunk 6
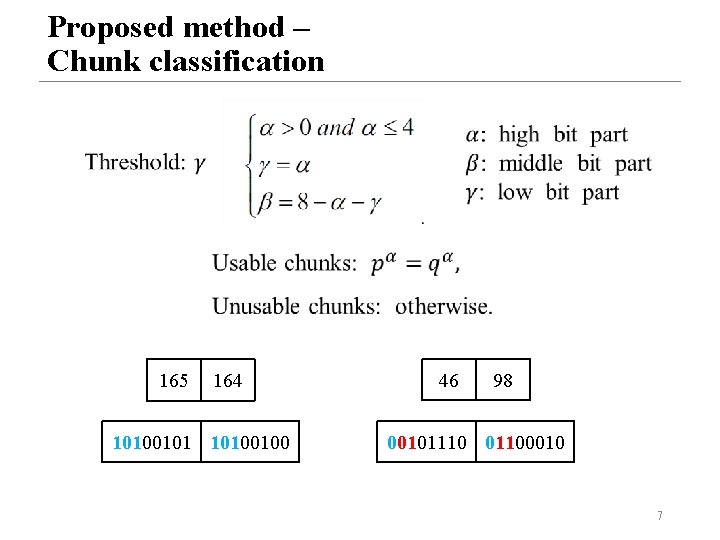
Proposed method – Chunk classification 165 164 10100101 10100100 46 98 00101110 01100010 7
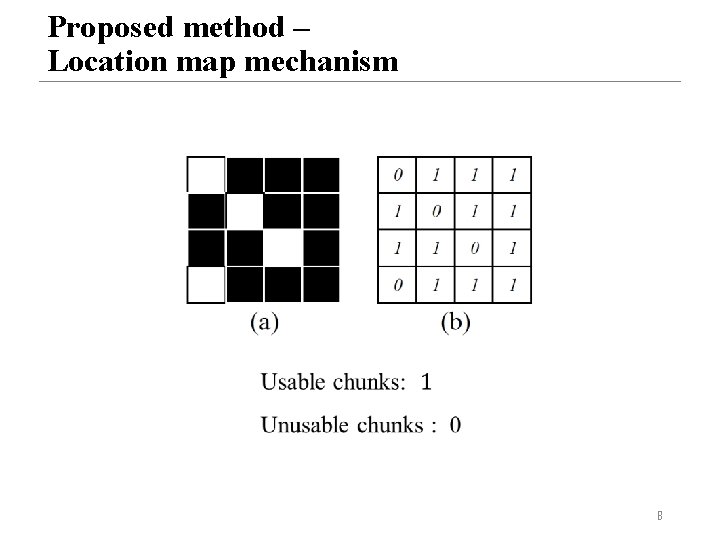
Proposed method – Location map mechanism 8
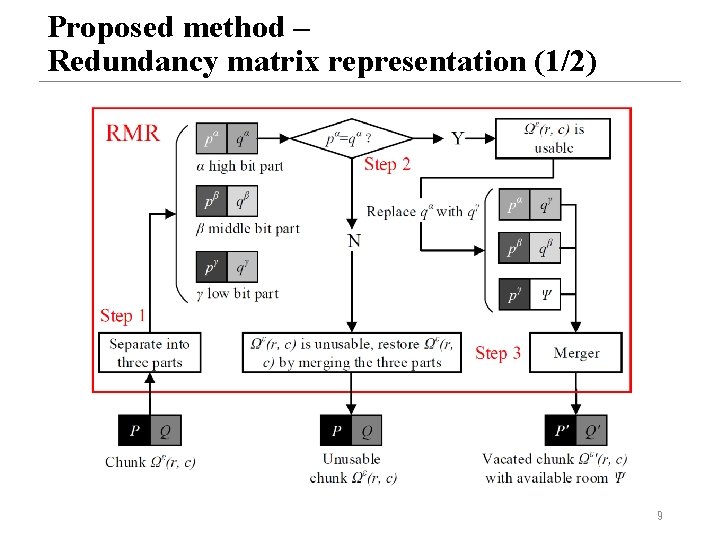
Proposed method – Redundancy matrix representation (1/2) 9
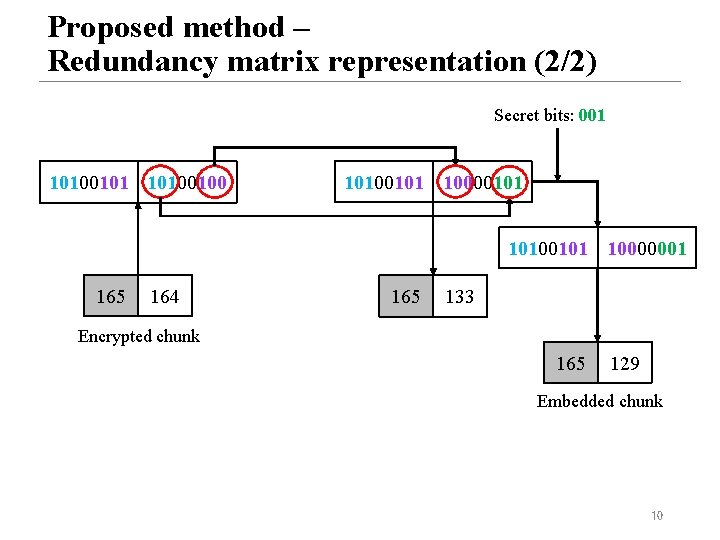
Proposed method – Redundancy matrix representation (2/2) Secret bits: 001 10100100 10100101 10000101 10100101 10000001 165 164 165 133 Encrypted chunk 165 129 Embedded chunk 10
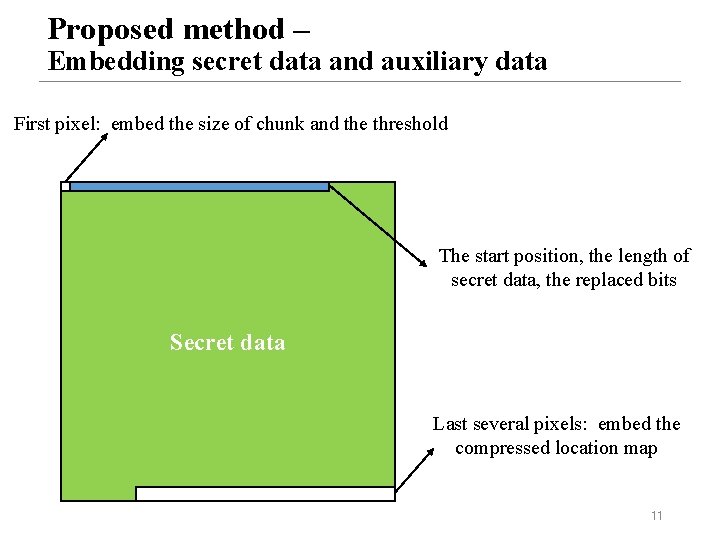
Proposed method – Embedding secret data and auxiliary data First pixel: embed the size of chunk and the threshold The start position, the length of secret data, the replaced bits Secret data Last several pixels: embed the compressed location map 11
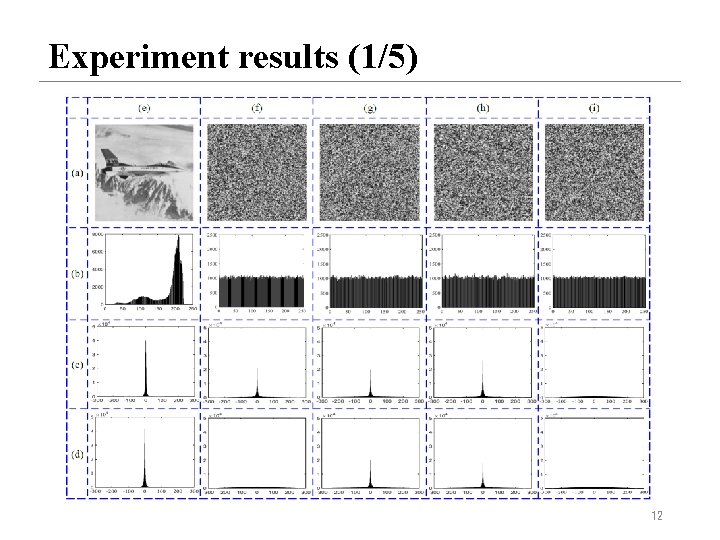
Experiment results (1/5) 12
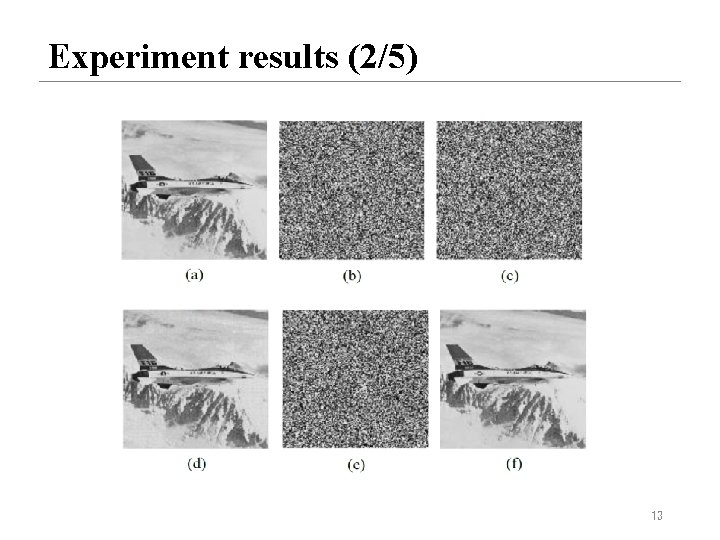
Experiment results (2/5) 13
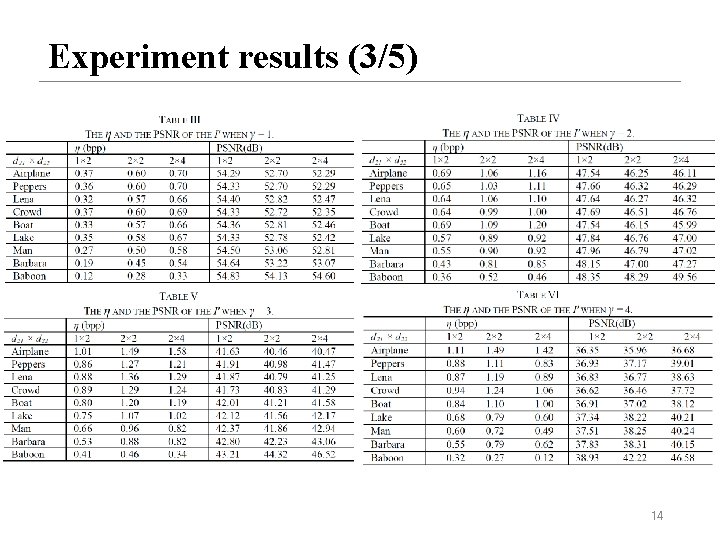
Experiment results (3/5) 14
![Experiment results (4/5) [17] X. Zhang, “Reversible data hiding in encrypted image, ” IEEE Experiment results (4/5) [17] X. Zhang, “Reversible data hiding in encrypted image, ” IEEE](http://slidetodoc.com/presentation_image_h2/e74af24442d974ea4ef27de0e3b62b68/image-15.jpg)
Experiment results (4/5) [17] X. Zhang, “Reversible data hiding in encrypted image, ” IEEE Signal Processing Letters, vol. 18, no. 4, pp. 255– 258, April 2011. [18] W. Hong, T. Chen, and H. Wu, “An improved reversible data hiding in encrypted images using side match, ” IEEE Signal Processing Letters, vol. 19, no. 4, pp. 199– 202, April 2012. [19] X. Zhang, “Separable reversible data hiding in encrypted image”, IEEE Trans. Inf. Forensics Security, vol. 7, no. 2, pp. 826– 832, Apr. 2012. [20] X. Zhang, J. Long, Z. Wang, and H. Cheng, “Lossless and reversible data hiding in encrypted images with public-key cryptography”, IEEE Trans. Circuits Syst. Video Technol. , vol. 26, no. 9, pp. 1622 -1631, Sep. 2016. [21] K. Ma, W. Zhang, X. Zhao, N. Yu, and F. Li, “Reversible data hiding in encrypted images by reserving room before encryption”, IEEE Trans. Inf. Forensics Security, vol. 8, no. 3, pp. 553 -562, Mar. 2013. [22] W. Zhang, K. Ma, and N. Yu, “Reversibility improved data hiding in encrypted images”, Signal Process. , vol. 94, pp. 118 -127, Jan. 2014. [23] X. Cao, L. Du, X. Wei, D. Meng, and X. Guo, “High capacity reversible data hiding in encrypted images by patch-level sparse representation”, IEEE Trans. Cybern. , vol. 46, no. 5, pp. 1132 -1143, May. 2016. [24] S. Yi, and Y. Zhou, “Binary-block embedding for reversible data hiding in encrypted images”, Signal Process. , Vol. 133, pp. 40 -51, Apr. 2017. [25] C. Qin, W. Zhang, F. Cao, X. Zhang, and C. -C. Chang, “Separable reversible data hiding in encrypted images via adaptive embedding strategy with block selection”, Signal Process. , Vol. 153, pp. 109 -122, Dec. 2018. [26] Q. Li, B. Yan, H. Li, and N. Chen, “Separable reversible data hiding in encrypted images with improved security and capacity”, Multimed Tools Appl. , 15 Vol. 77, no. 23, pp. 30749 -30768, Dec. 2018.
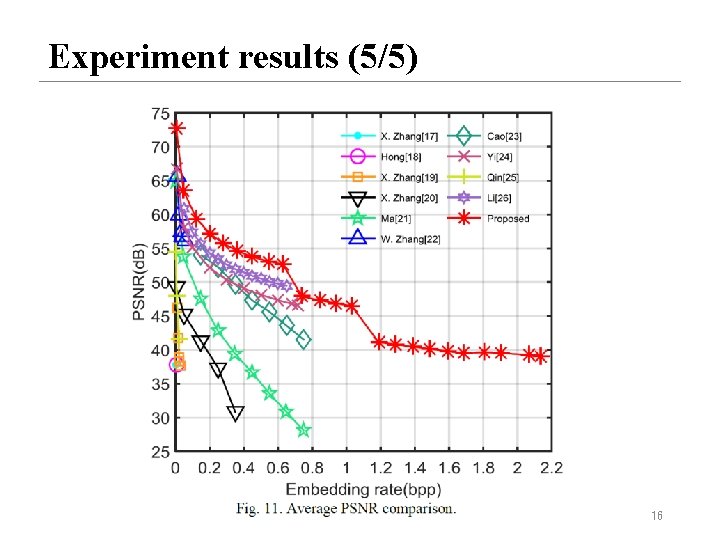
Experiment results (5/5) 16
Conclusions Ø Proposed the chunk encryption method and the redundancy matrix representation method. Ø The data extraction and image recovery are independent. Ø The performance outperforms other algorithms. 17
- Slides: 17