Encrypted Traffic Management Symantec SSL Visibility Appliance Remove

Encrypted Traffic Management Symantec SSL Visibility Appliance Remove security blind-spots with SSL Decryption/Visibility Bruce Marco, CISSP, Federal Systems Engineering Manager
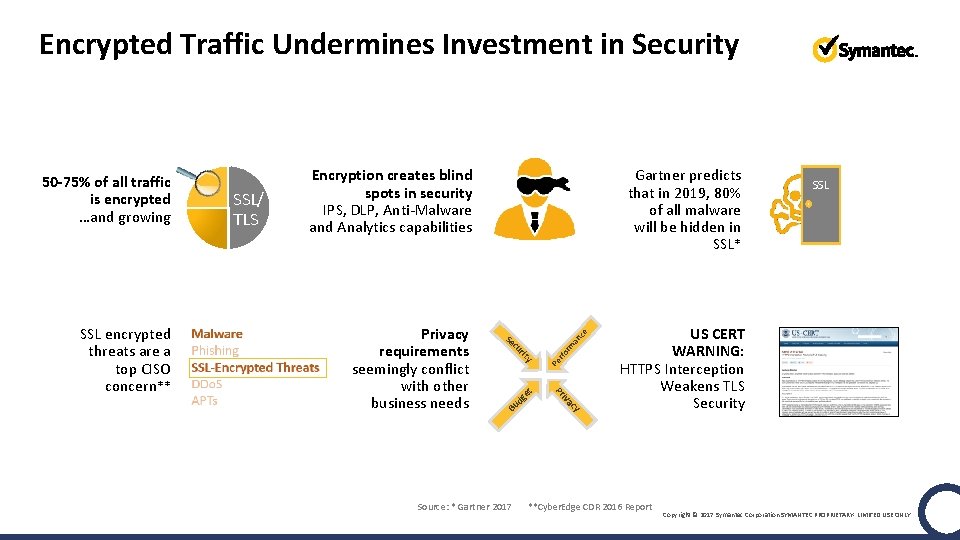
Encrypted Traffic Undermines Investment in Security ce y et B g ud y ac Source: * Gartner 2017 rit rm an cu rfo Se iv Privacy requirements seemingly conflict with other business needs Gartner predicts that in 2019, 80% of all malware will be hidden in SSL* Pr SSL encrypted threats are a top CISO concern** SSL/ TLS Encryption creates blind spots in security IPS, DLP, Anti-Malware and Analytics capabilities Pe 50 -75% of all traffic is encrypted …and growing SSL US CERT WARNING: HTTPS Interception Weakens TLS Security **Cyber. Edge CDR 2016 Report Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
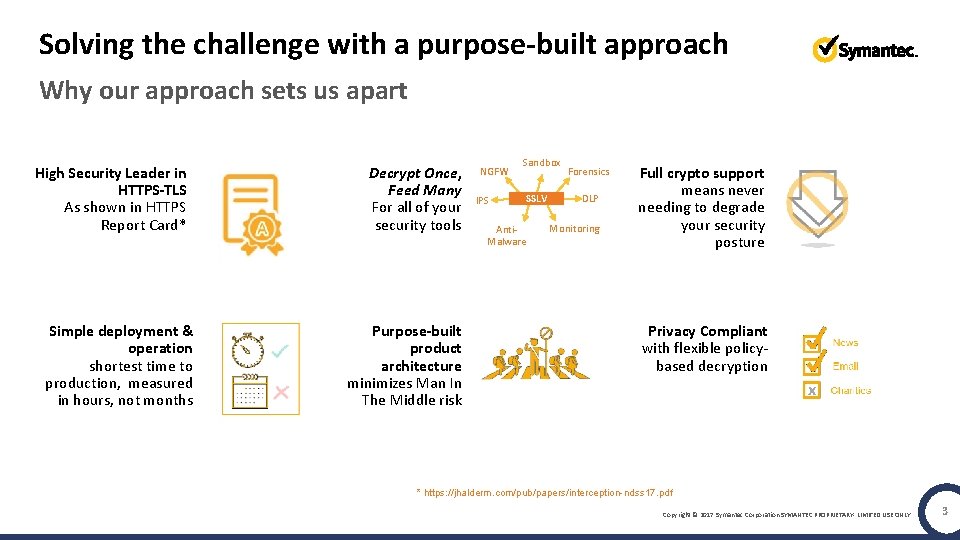
Solving the challenge with a purpose-built approach Why our approach sets us apart High Security Leader in HTTPS-TLS As shown in HTTPS Report Card* Simple deployment & operation shortest time to production, measured in hours, not months SSL Decrypt Once, Feed Many For all of your security tools Purpose-built product architecture minimizes Man In The Middle risk NGFW IPS Sandbox SSLV Anti. Malware Forensics DLP Monitoring Full crypto support means never needing to degrade your security posture Privacy Compliant with flexible policybased decryption x * https: //jhalderm. com/pub/papers/interception-ndss 17. pdf Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY 3
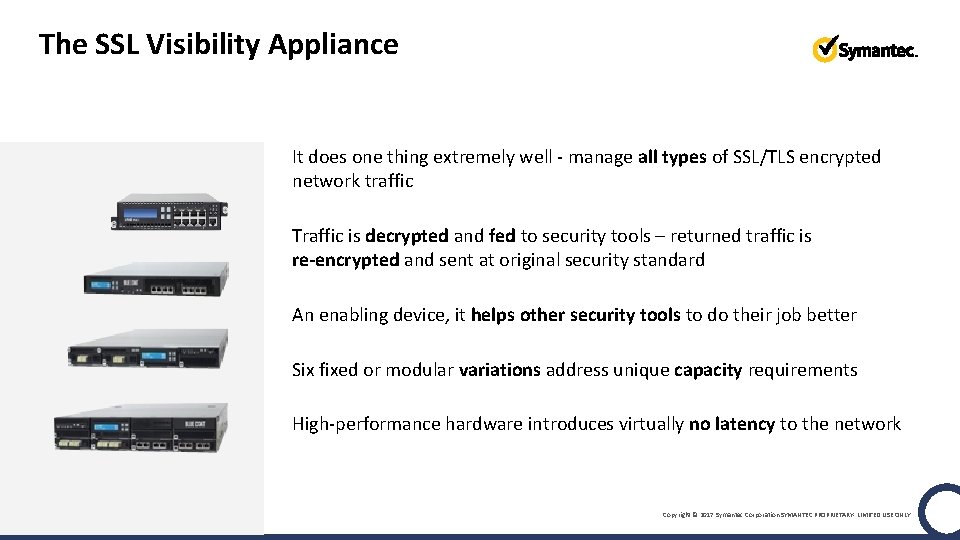
The SSL Visibility Appliance It does one thing extremely well - manage all types of SSL/TLS encrypted network traffic Traffic is decrypted and fed to security tools – returned traffic is re-encrypted and sent at original security standard An enabling device, it helps other security tools to do their job better Six fixed or modular variations address unique capacity requirements High-performance hardware introduces virtually no latency to the network Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY

How It Works: Four Easy Steps Connect SSLV to network tools Set up “segments” –direct connections to active and passive devices. Select traffic types to decrypt and remain encrypted. Host Categorization powered by GIN helps enforce decryption policy Traffic is sent to the segments you select and received back after each appliance has performed its function. Manage SSL/TLS traffic throughout organization with powerful policy-based decryption Unsuppressed, original data is re-encrypted sent along to its destination. Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
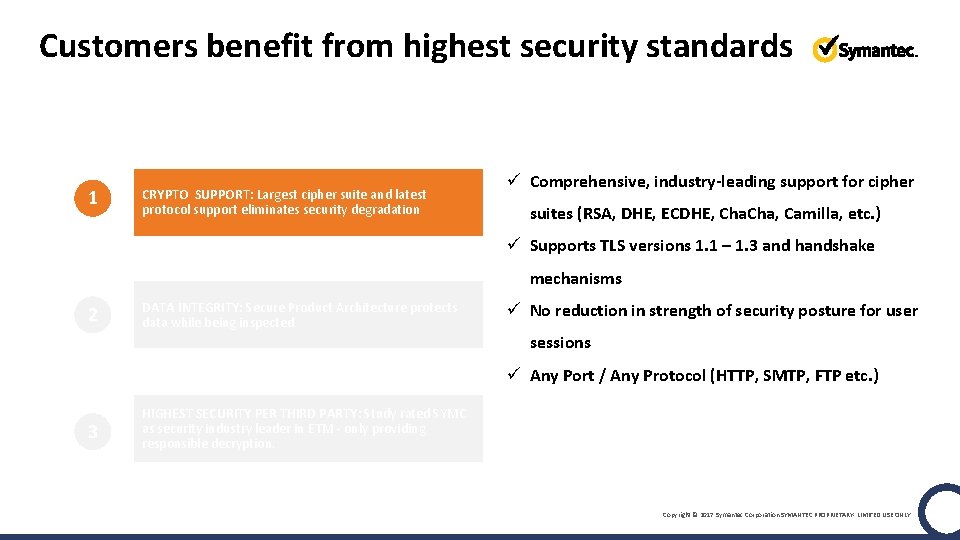
Customers benefit from highest security standards 1 CRYPTO SUPPORT: Largest cipher suite and latest protocol support eliminates security degradation ü Comprehensive, industry-leading support for cipher suites (RSA, DHE, ECDHE, Cha, Camilla, etc. ) ü Supports TLS versions 1. 1 – 1. 3 and handshake mechanisms 2 DATA INTEGRITY: Secure Product Architecture protects data while being inspected ü No reduction in strength of security posture for user sessions ü Any Port / Any Protocol (HTTP, SMTP, FTP etc. ) 3 HIGHEST SECURITY PER THIRD PARTY: Study rated SYMC as security industry leader in ETM - only providing responsible decryption. Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
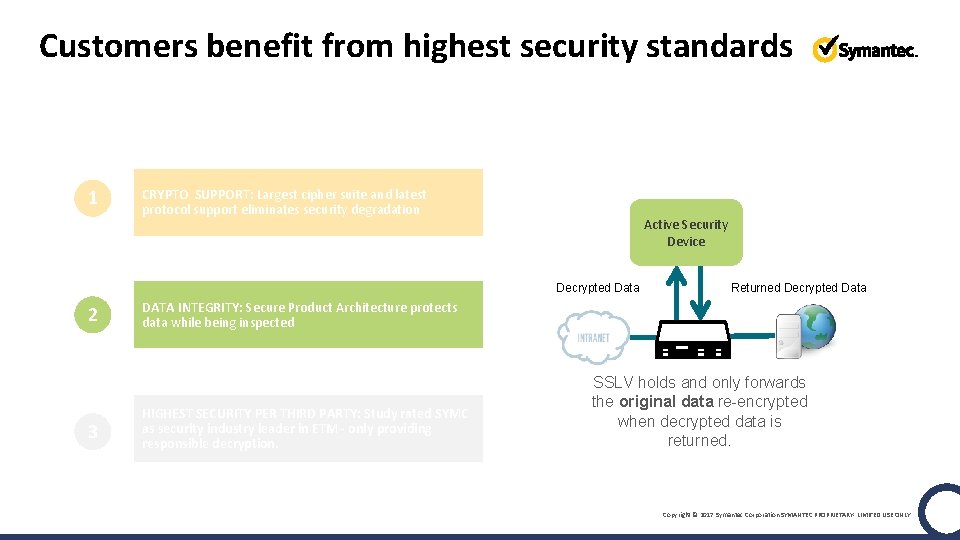
Customers benefit from highest security standards In-flight data integrity 1 CRYPTO SUPPORT: Largest cipher suite and latest protocol support eliminates security degradation Active Security Device Decrypted Data 2 3 Returned Decrypted Data DATA INTEGRITY: Secure Product Architecture protects data while being inspected HIGHEST SECURITY PER THIRD PARTY: Study rated SYMC as security industry leader in ETM - only providing responsible decryption. SSLV holds and only forwards the original data re-encrypted when decrypted data is returned. Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
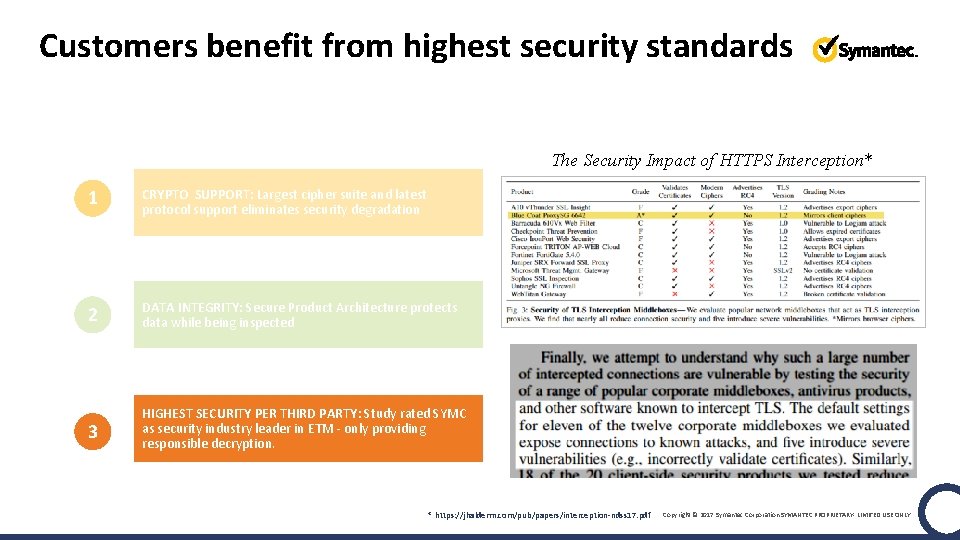
Customers benefit from highest security standards The Security Impact of HTTPS Interception* 1 CRYPTO SUPPORT: Largest cipher suite and latest protocol support eliminates security degradation 2 DATA INTEGRITY: Secure Product Architecture protects data while being inspected 3 HIGHEST SECURITY PER THIRD PARTY: Study rated SYMC as security industry leader in ETM - only providing responsible decryption. * https: //jhalderm. com/pub/papers/interception-ndss 17. pdf Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
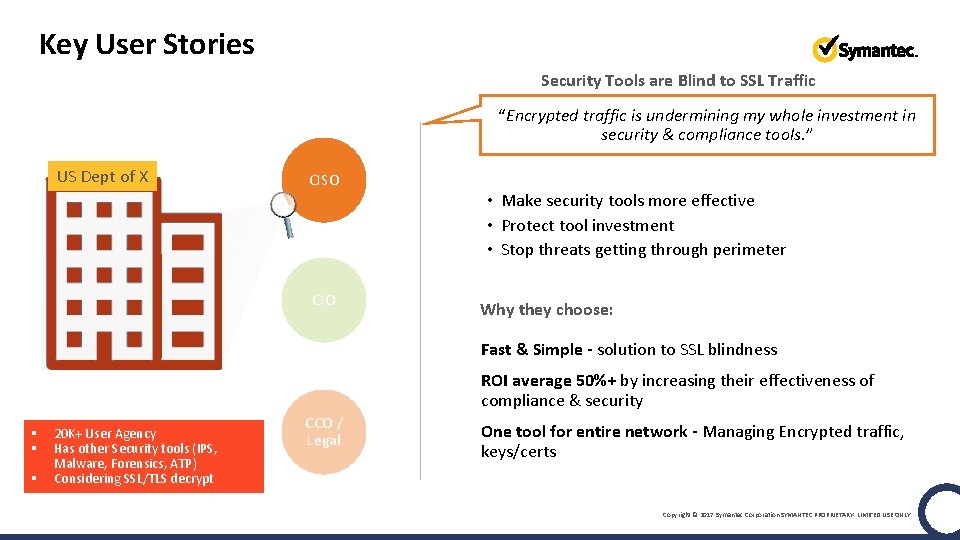
Key User Stories Security Tools are Blind to SSL Traffic “Encrypted traffic is undermining my whole investment in security & compliance tools. ” US Dept of X CISO CIO Needs • Make security tools more effective • Protect tool investment • Stop threats getting through perimeter Why they choose: Fast & Simple - solution to SSL blindness ROI average 50%+ by increasing their effectiveness of compliance & security § § § 20 K+ User Agency Has other Security tools (IPS, Malware, Forensics, ATP) Considering SSL/TLS decrypt CCO / Legal One tool for entire network - Managing Encrypted traffic, keys/certs Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
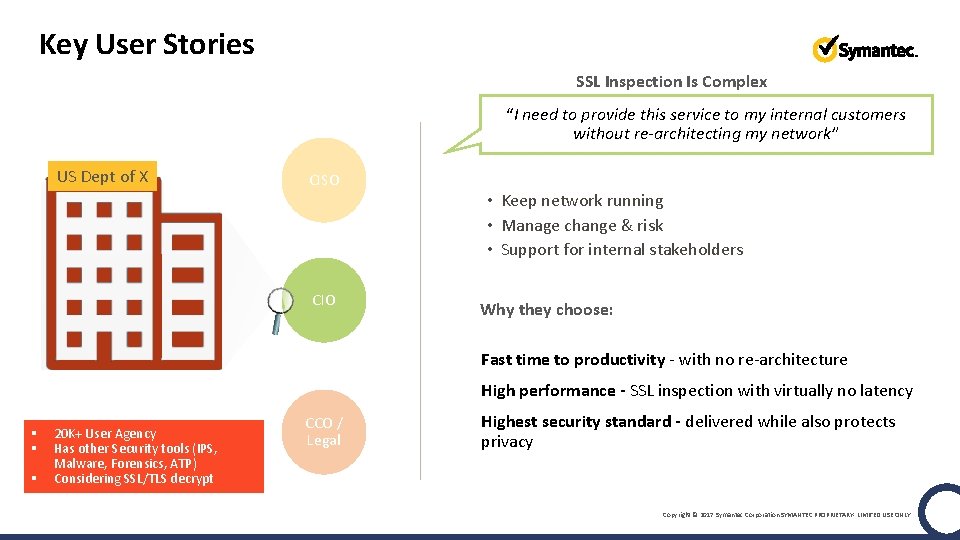
Key User Stories SSL Inspection Is Complex “I need to provide this service to my internal customers without re-architecting my network” US Dept of X CISO CIO Needs • Keep network running • Manage change & risk • Support for internal stakeholders Why they choose: Fast time to productivity - with no re-architecture High performance - SSL inspection with virtually no latency § § § 20 K+ User Agency Has other Security tools (IPS, Malware, Forensics, ATP) Considering SSL/TLS decrypt CCO / Legal Highest security standard - delivered while also protects privacy Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
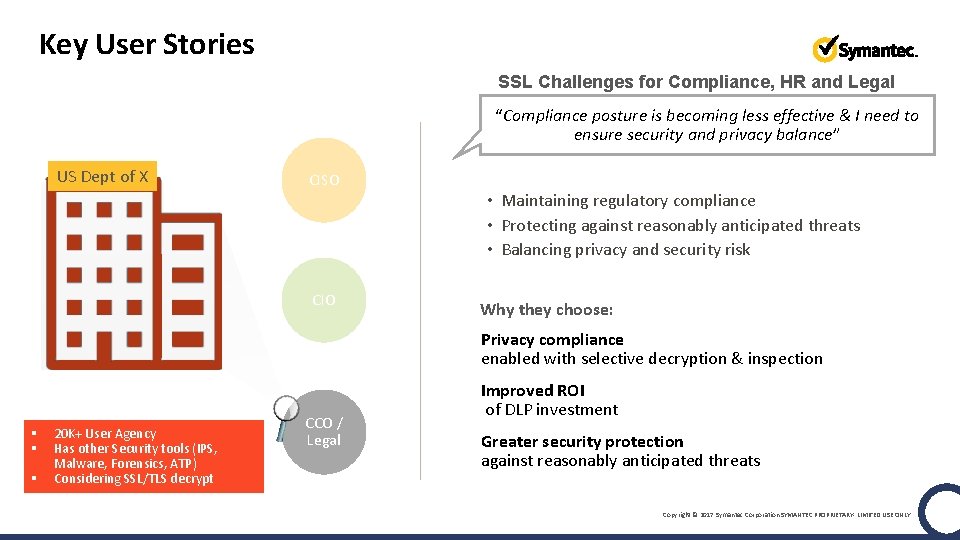
Key User Stories SSL Challenges for Compliance, HR and Legal “Compliance posture is becoming less effective & I need to ensure security and privacy balance” US Dept of X CISO CIO Needs • Maintaining regulatory compliance • Protecting against reasonably anticipated threats • Balancing privacy and security risk Why they choose: • Privacy compliance • enabled with selective decryption & inspection § § § 20 K+ User Agency Has other Security tools (IPS, Malware, Forensics, ATP) Considering SSL/TLS decrypt CCO / Legal • Improved ROI • of DLP investment • Greater security protection • against reasonably anticipated threats Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
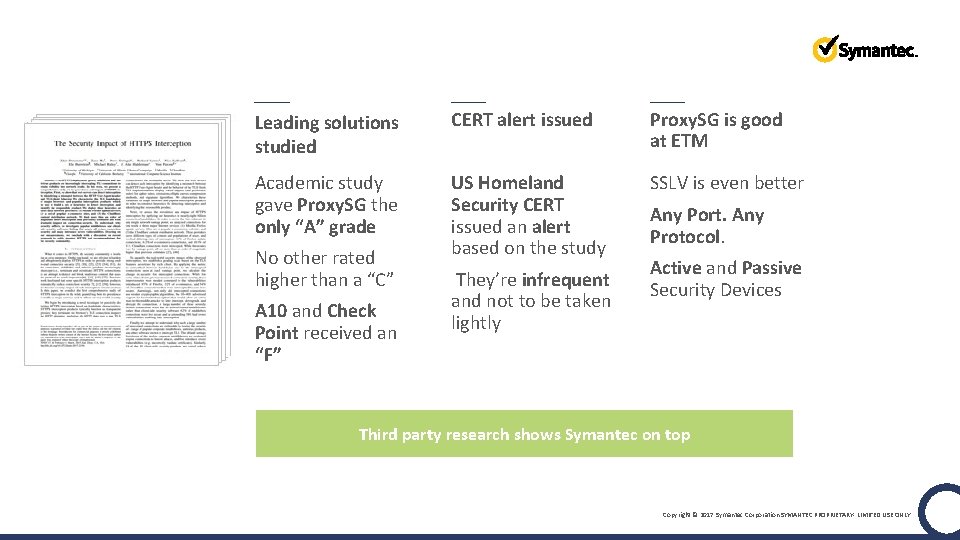
Leading solutions studied CERT alert issued Proxy. SG is good at ETM Academic study gave Proxy. SG the only “A” grade US Homeland Security CERT issued an alert based on the study SSLV is even better No other rated higher than a “C” A 10 and Check Point received an “F” They’re infrequent and not to be taken lightly Any Port. Any Protocol. Active and Passive Security Devices Third party research shows Symantec on top Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
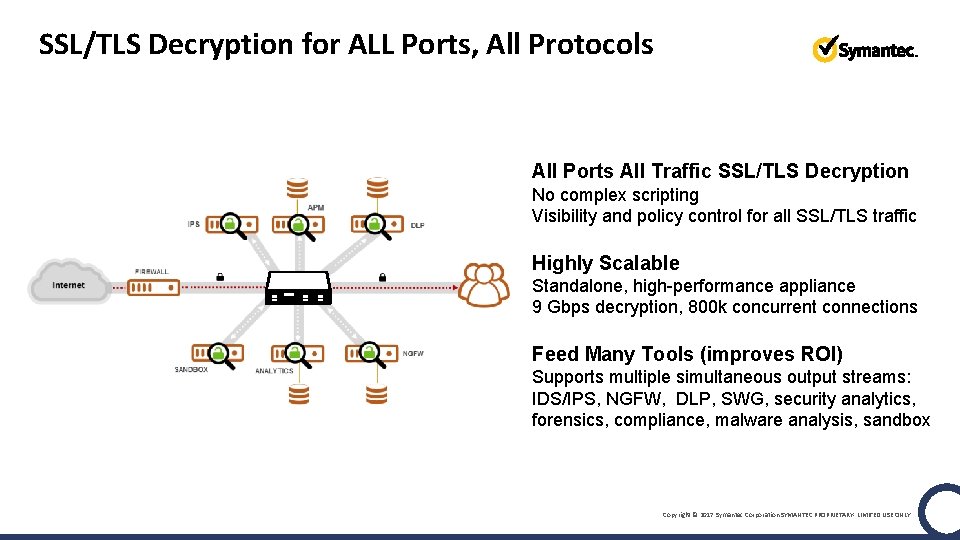
SSL/TLS Decryption for ALL Ports, All Protocols All Ports All Traffic SSL/TLS Decryption No complex scripting Visibility and policy control for all SSL/TLS traffic Highly Scalable Standalone, high-performance appliance 9 Gbps decryption, 800 k concurrent connections Feed Many Tools (improves ROI) Supports multiple simultaneous output streams: IDS/IPS, NGFW, DLP, SWG, security analytics, forensics, compliance, malware analysis, sandbox Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
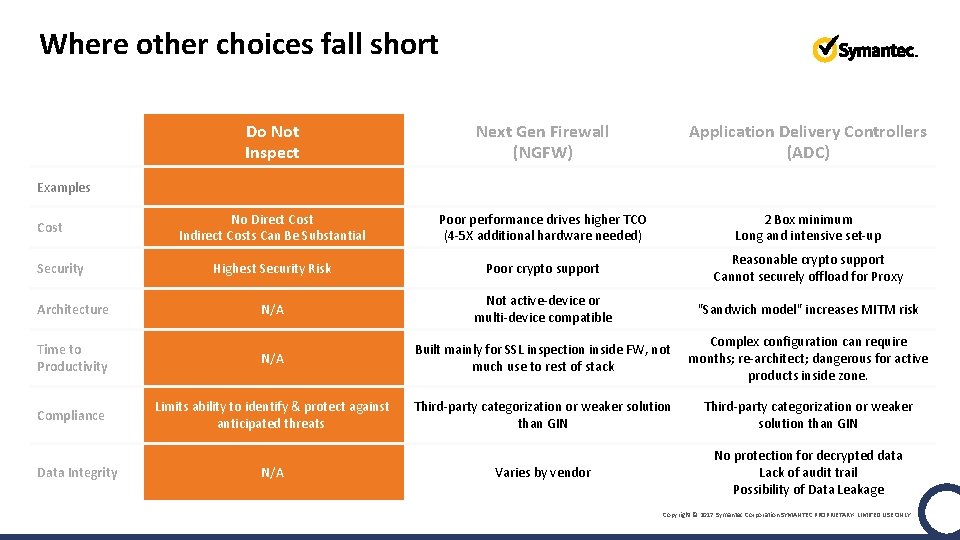
Where other choices fall short Do Not Inspect Next Gen Firewall (NGFW) Application Delivery Controllers (ADC) No Direct Cost Indirect Costs Can Be Substantial Poor performance drives higher TCO (4 -5 X additional hardware needed) 2 Box minimum Long and intensive set-up Highest Security Risk Poor crypto support Reasonable crypto support Cannot securely offload for Proxy N/A Not active-device or multi-device compatible "Sandwich model" increases MITM risk Time to Productivity N/A Built mainly for SSL inspection inside FW, not much use to rest of stack Complex configuration can require months; re-architect; dangerous for active products inside zone. Compliance Limits ability to identify & protect against anticipated threats Third-party categorization or weaker solution than GIN Varies by vendor No protection for decrypted data Lack of audit trail Possibility of Data Leakage Examples Cost Security Architecture Data Integrity N/A Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
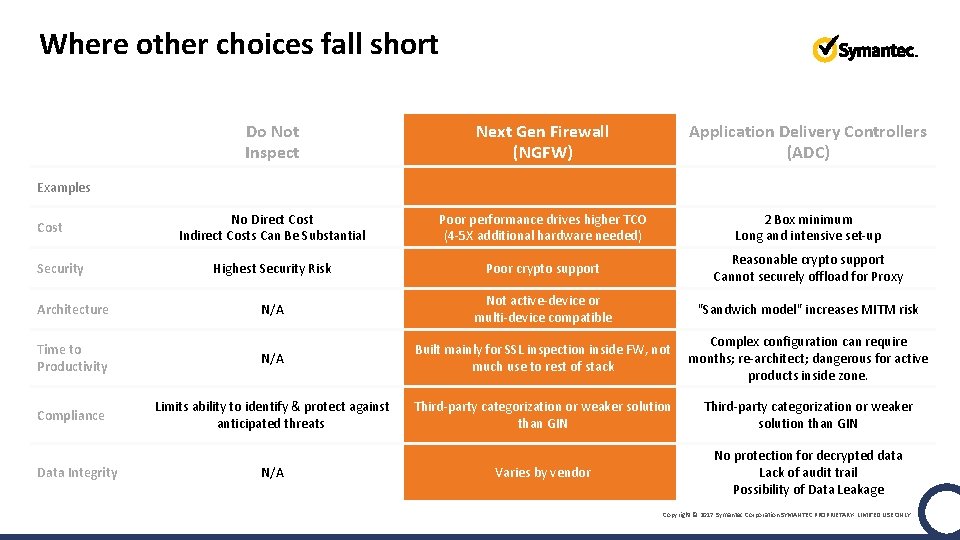
Where other choices fall short Do Not Inspect Next Gen Firewall (NGFW) Application Delivery Controllers (ADC) No Direct Cost Indirect Costs Can Be Substantial Poor performance drives higher TCO (4 -5 X additional hardware needed) 2 Box minimum Long and intensive set-up Highest Security Risk Poor crypto support Reasonable crypto support Cannot securely offload for Proxy N/A Not active-device or multi-device compatible "Sandwich model" increases MITM risk Time to Productivity N/A Built mainly for SSL inspection inside FW, not much use to rest of stack Complex configuration can require months; re-architect; dangerous for active products inside zone. Compliance Limits ability to identify & protect against anticipated threats Third-party categorization or weaker solution than GIN Varies by vendor No protection for decrypted data Lack of audit trail Possibility of Data Leakage Examples Cost Security Architecture Data Integrity N/A Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
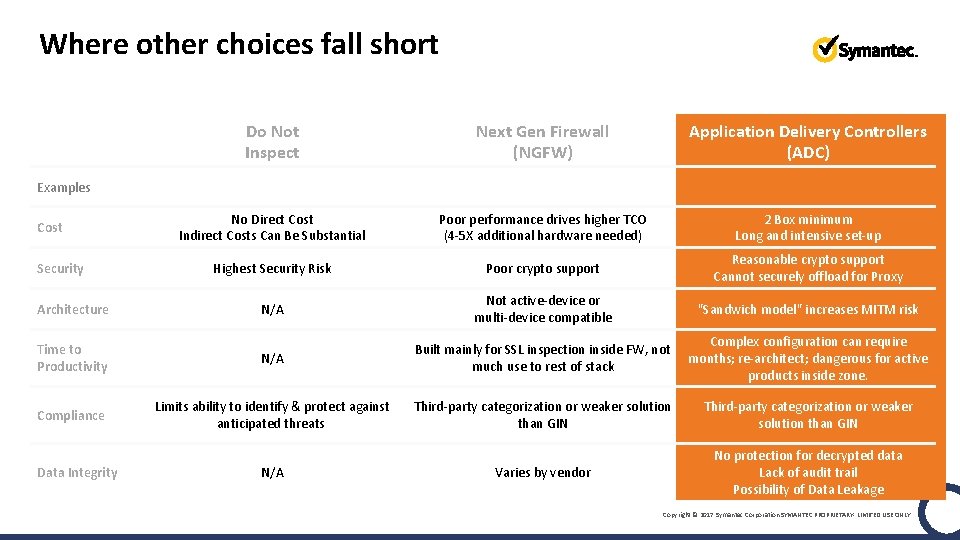
Where other choices fall short Do Not Inspect Next Gen Firewall (NGFW) Application Delivery Controllers (ADC) No Direct Cost Indirect Costs Can Be Substantial Poor performance drives higher TCO (4 -5 X additional hardware needed) 2 Box minimum Long and intensive set-up Highest Security Risk Poor crypto support Reasonable crypto support Cannot securely offload for Proxy N/A Not active-device or multi-device compatible "Sandwich model" increases MITM risk Time to Productivity N/A Built mainly for SSL inspection inside FW, not much use to rest of stack Complex configuration can require months; re-architect; dangerous for active products inside zone. Compliance Limits ability to identify & protect against anticipated threats Third-party categorization or weaker solution than GIN Varies by vendor No protection for decrypted data Lack of audit trail Possibility of Data Leakage Examples Cost Security Architecture Data Integrity N/A Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
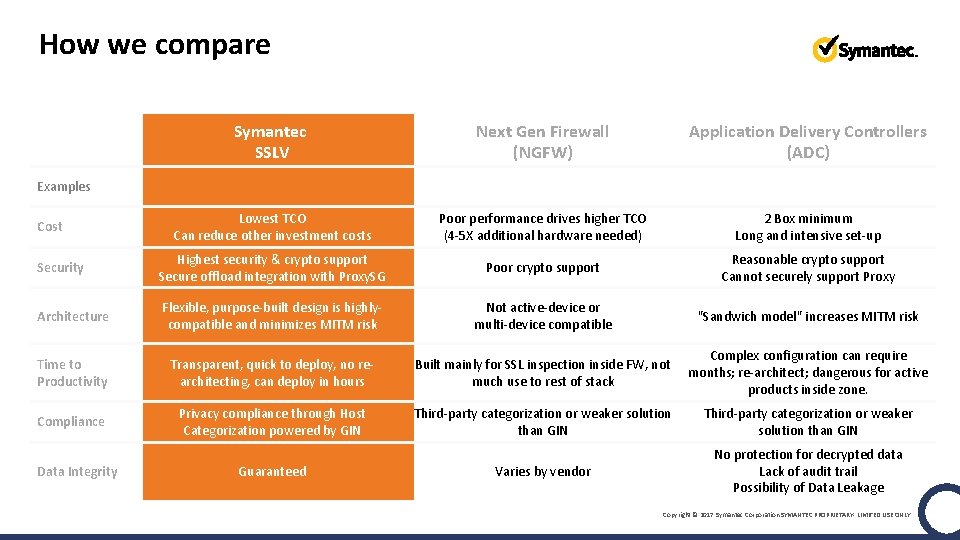
How we compare Symantec SSLV Next Gen Firewall (NGFW) Application Delivery Controllers (ADC) Lowest TCO Can reduce other investment costs Poor performance drives higher TCO (4 -5 X additional hardware needed) 2 Box minimum Long and intensive set-up Security Highest security & crypto support Secure offload integration with Proxy. SG Poor crypto support Reasonable crypto support Cannot securely support Proxy Architecture Flexible, purpose-built design is highlycompatible and minimizes MITM risk Not active-device or multi-device compatible "Sandwich model" increases MITM risk Time to Productivity Transparent, quick to deploy, no rearchitecting, can deploy in hours Built mainly for SSL inspection inside FW, not much use to rest of stack Complex configuration can require months; re-architect; dangerous for active products inside zone. Compliance Privacy compliance through Host Categorization powered by GIN Third-party categorization or weaker solution than GIN Varies by vendor No protection for decrypted data Lack of audit trail Possibility of Data Leakage Examples Cost Data Integrity Guaranteed Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
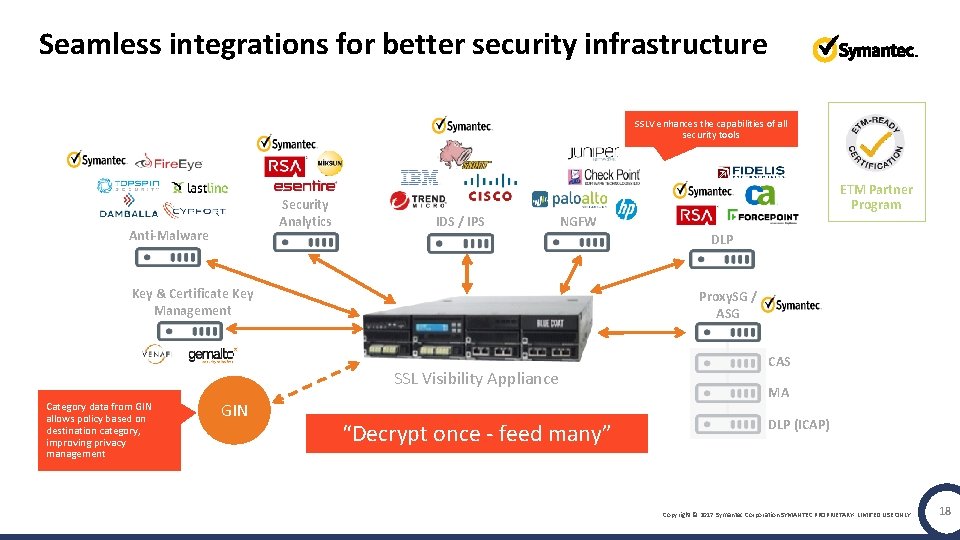
Seamless integrations for better security infrastructure SSLV enhances the capabilities of all security tools Security Analytics Anti-Malware ETM Partner Program IDS / IPS NGFW DLP Key & Certificate Key Management Proxy. SG / ASG SSL Visibility Appliance Category data from GIN allows policy based on destination category, improving privacy management GIN “Decrypt once - feed many” CAS MA DLP (ICAP) Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY 18
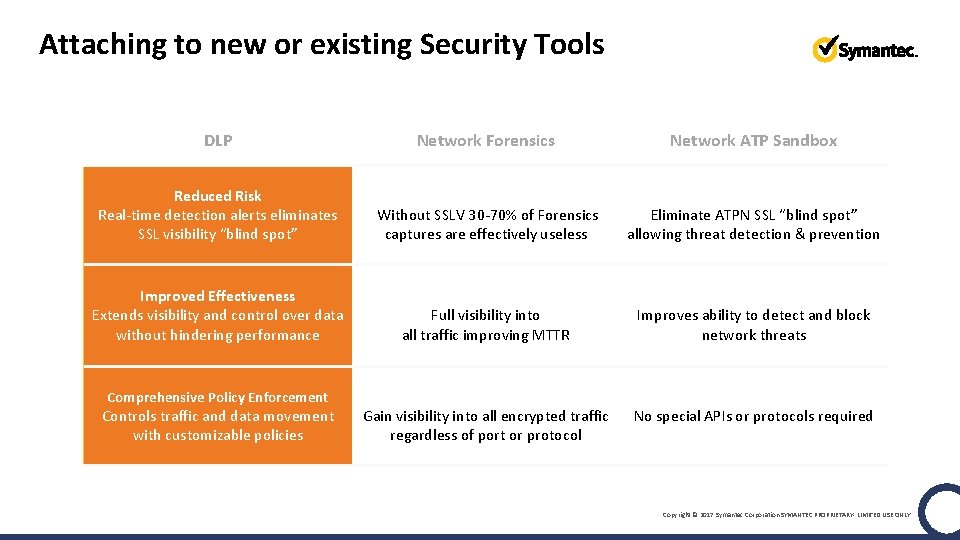
Attaching to new or existing Security Tools DLP Network Forensics Network ATP Sandbox Reduced Risk Real-time detection alerts eliminates SSL visibility “blind spot” Improved ROI Without SSLV 30 -70% of Forensics captures are effectively useless Reduced Risk Eliminate ATPN SSL “blind spot” allowing threat detection & prevention Improved Effectiveness Extends visibility and control over data without hindering performance Faster Incident Response Full visibility into all traffic improving MTTR Improved ROI Improves ability to detect and block network threats Comprehensive Policy Enforcement Full Visibility Gain visibility into all encrypted traffic regardless of port or protocol Interoperable & Easy-to-Deploy No special APIs or protocols required Controls traffic and data movement with customizable policies Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
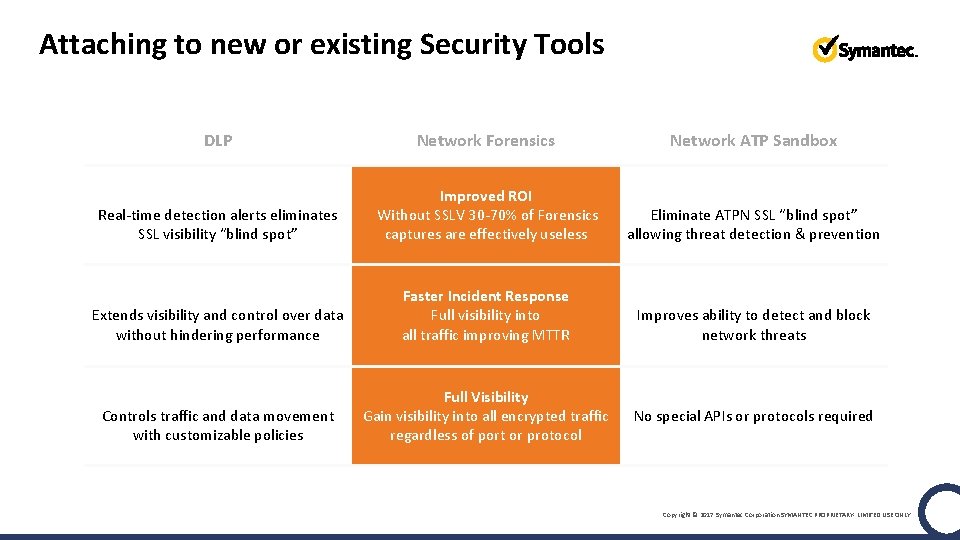
Attaching to new or existing Security Tools DLP Network Forensics Network ATP Sandbox Reduced Risk Real-time detection alerts eliminates SSL visibility “blind spot” Improved ROI Without SSLV 30 -70% of Forensics captures are effectively useless Reduced Risk Eliminate ATPN SSL “blind spot” allowing threat detection & prevention Improved Effectiveness Extends visibility and control over data without hindering performance Faster Incident Response Full visibility into all traffic improving MTTR Improved ROI Improves ability to detect and block network threats Comprehensive Policy Enforcement Full Visibility Gain visibility into all encrypted traffic regardless of port or protocol Interoperable & Easy-to-Deploy No special APIs or protocols required Controls traffic and data movement with customizable policies Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
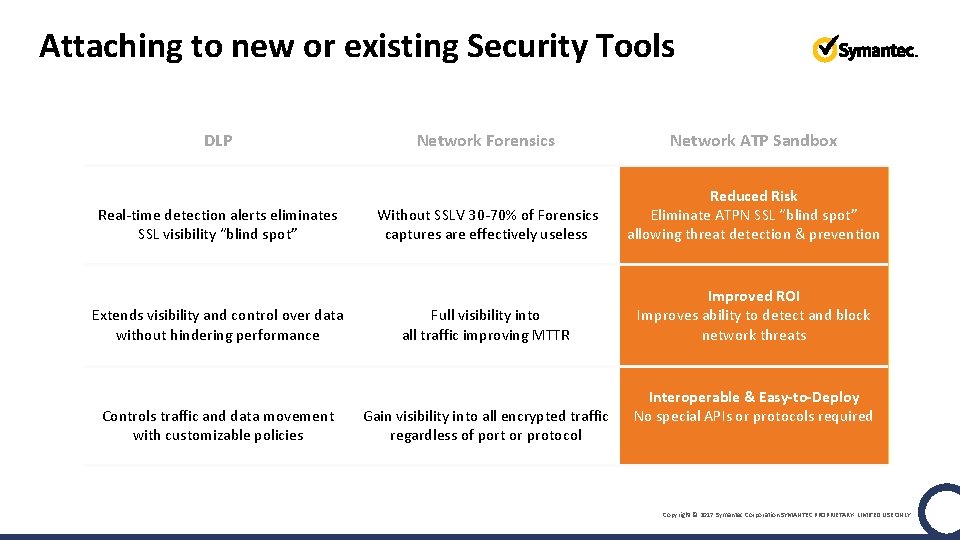
Attaching to new or existing Security Tools DLP Network Forensics Network ATP Sandbox Reduced Risk Real-time detection alerts eliminates SSL visibility “blind spot” Improved ROI Without SSLV 30 -70% of Forensics captures are effectively useless Reduced Risk Eliminate ATPN SSL “blind spot” allowing threat detection & prevention Improved Effectiveness Extends visibility and control over data without hindering performance Faster Incident Response Full visibility into all traffic improving MTTR Improved ROI Improves ability to detect and block network threats Comprehensive Policy Enforcement Full Visibility Gain visibility into all encrypted traffic regardless of port or protocol Interoperable & Easy-to-Deploy No special APIs or protocols required Controls traffic and data movement with customizable policies Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
Learn more • Understanding the Impact of SSL/TLS Encryption and Mitigation Options • • • ETM e-Guide ETM Videocast Demo Myth Busters Quiz ‘ 5 Things to Know about ETM’ infographic ETM for Dummies book • Ensuring Data Privacy Compliance and Security • Securosis white paper “Security and Privacy • on the Encrypted Network” “Implementing Data Privacy Requirements for Encrypted Traffic’ data sheet Website: www. go. symantec. com/uncoverssl Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
Thank you.
Appendix Optional content for customized presentations Copyright © 2017 Symantec Corporation 24
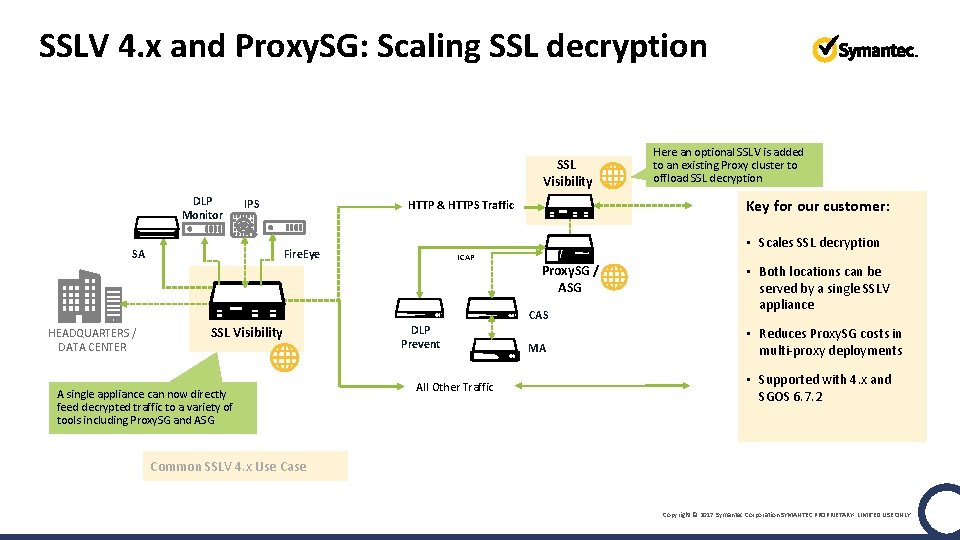
SSLV 4. x and Proxy. SG: Scaling SSL decryption SSL Visibility DLP Monitor IPS SA Key for our customer: HTTP & HTTPS Traffic • Scales SSL decryption Fire. Eye ICAP Proxy. SG / ASG CAS HEADQUARTERS / DATA CENTER SSL Visibility A single appliance can now directly feed decrypted traffic to a variety of tools including Proxy. SG and ASG Here an optional SSLV is added to an existing Proxy cluster to offload SSL decryption DLP Prevent All Other Traffic MA • Both locations can be served by a single SSLV appliance • Reduces Proxy. SG costs in multi-proxy deployments • Supported with 4. x and SGOS 6. 7. 2 Common SSLV 4. x Use Case Copyright © 2017 Symantec Corporation SYMANTEC PROPRIETARY- LIMITED USE ONLY
- Slides: 25