Reversible Data Hiding in Encrypted Images Based on
Reversible Data Hiding in Encrypted Images Based on Progressive Recovery Source: IEEE Signal Processing Letters (Accepted)2016 Authors:Zhenxing Qian, Xinpeng Zhang, Guorui Feng Speaker :Xiaozhu Xie Date : 2016/09/29 1
Outline Scenario Proposed schemes Experimental results Conclusions 2
Scenario Embed additional messages(e. g. , lables, time stamps, category information etc. ) KEMB KENC 3
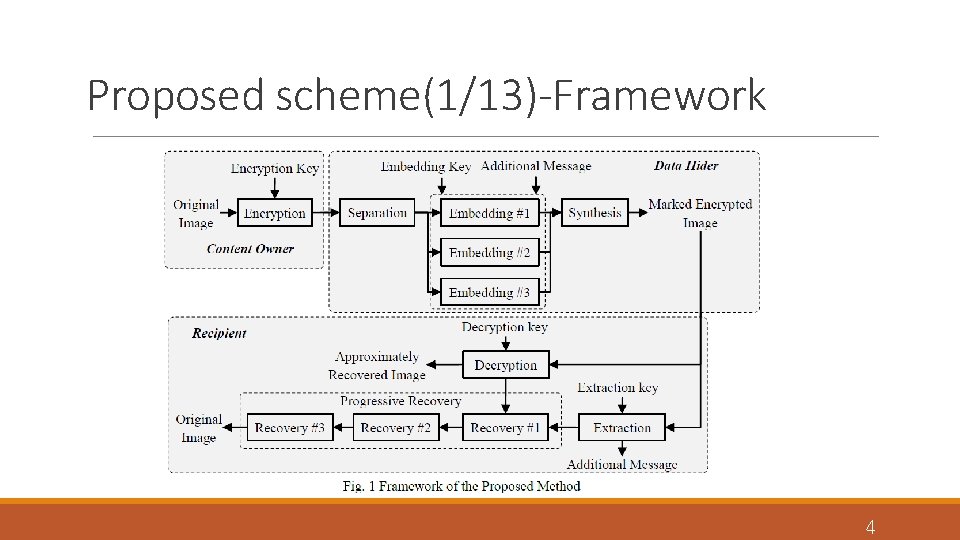
Proposed scheme(1/13)-Framework 4
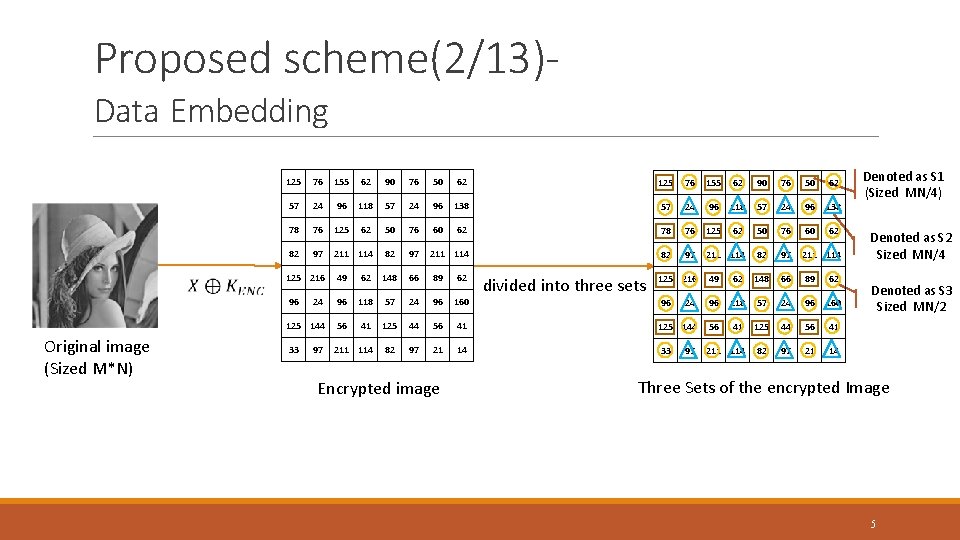
Proposed scheme(2/13)Data Embedding Original image (Sized M*N) 125 76 155 62 90 76 50 62 57 24 96 118 57 24 96 138 78 76 125 62 50 76 60 62 82 97 211 114 125 216 49 62 148 66 89 62 96 24 96 118 57 24 96 160 125 144 56 41 125 44 56 41 33 211 114 82 97 21 14 97 Encrypted image divided into three sets 97 Denoted as S 1 (Sized MN/4) Denoted as S 2 Sized MN/4 Denoted as S 3 Sized MN/2 Three Sets of the encrypted Image 5
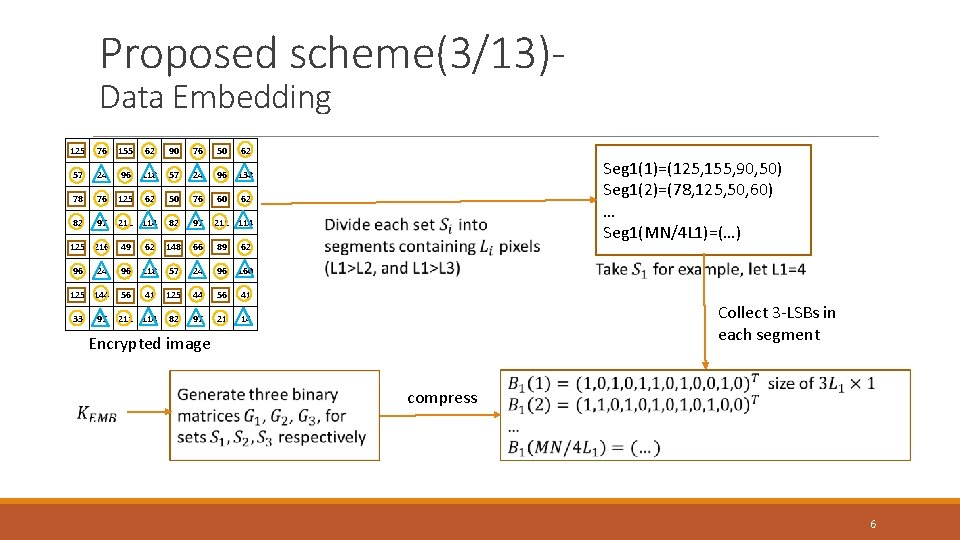
Proposed scheme(3/13)Data Embedding 125 76 155 62 90 76 50 62 57 24 96 118 57 24 96 138 78 76 125 62 50 76 60 62 82 97 211 114 125 216 49 62 148 66 89 62 96 24 96 118 57 24 96 160 125 144 56 41 125 44 56 41 33 211 114 82 97 21 14 97 Seg 1(1)=(125, 155, 90, 50) Seg 1(2)=(78, 125, 50, 60) … Seg 1(MN/4 L 1)=(…) Collect 3 -LSBs in each segment Encrypted image compress 6
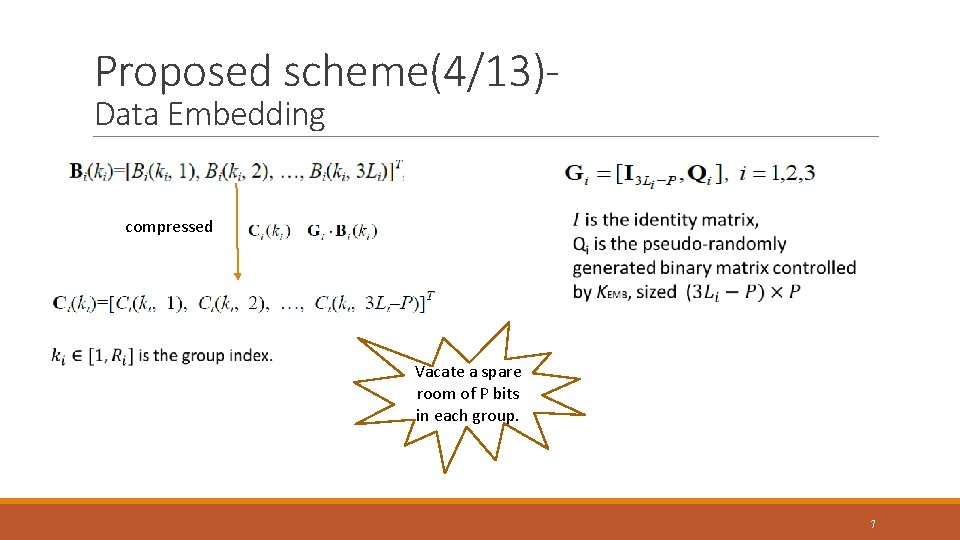
Proposed scheme(4/13)Data Embedding compressed Vacate a spare room of P bits in each group. 7
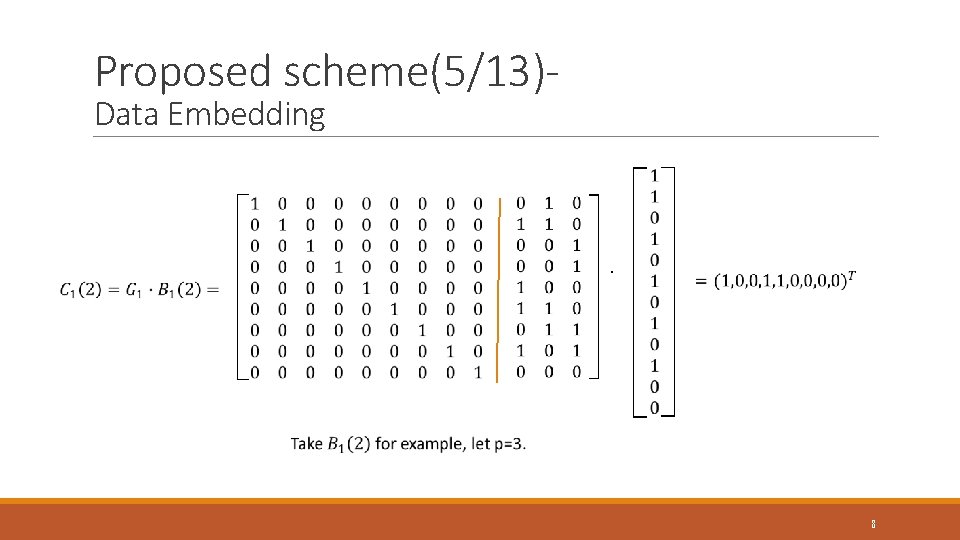
Proposed scheme(5/13)Data Embedding . 8
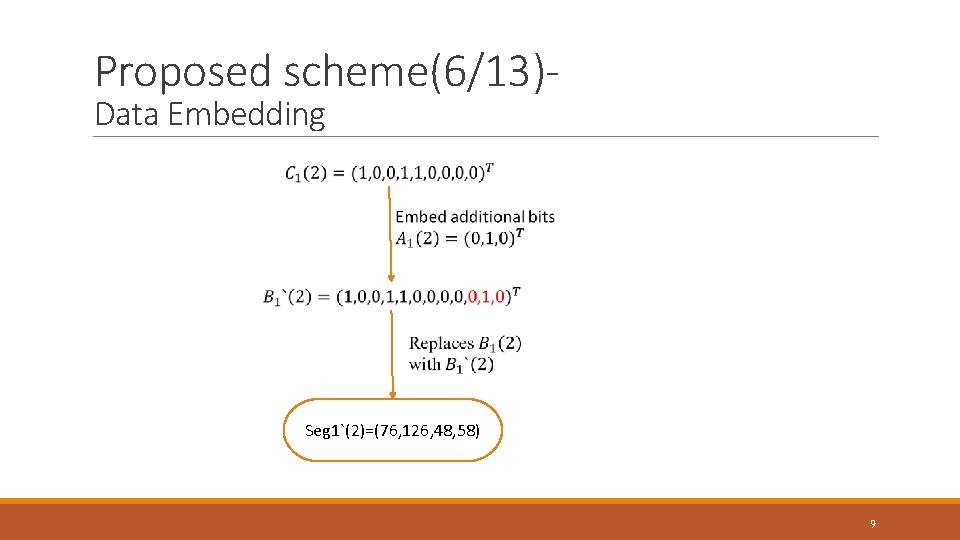
Proposed scheme(6/13)Data Embedding Seg 1`(2)=(76, 126, 48, 58) 9
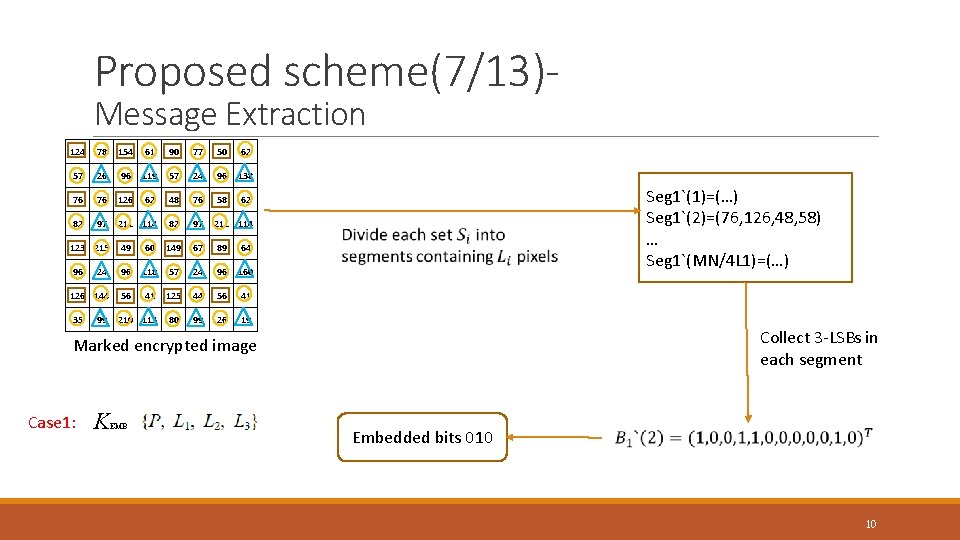
Proposed scheme(7/13)Message Extraction 124 78 154 61 90 77 50 62 57 26 96 119 57 24 96 138 76 76 126 62 48 76 58 62 82 97 211 114 123 215 49 60 149 67 89 64 96 24 96 118 57 24 96 160 126 144 56 41 125 44 56 41 35 210 113 80 99 26 19 99 Seg 1`(1)=(…) Seg 1`(2)=(76, 126, 48, 58) … Seg 1`(MN/4 L 1)=(…) Collect 3 -LSBs in each segment Marked encrypted image Case 1: K EMB Embedded bits 010 10
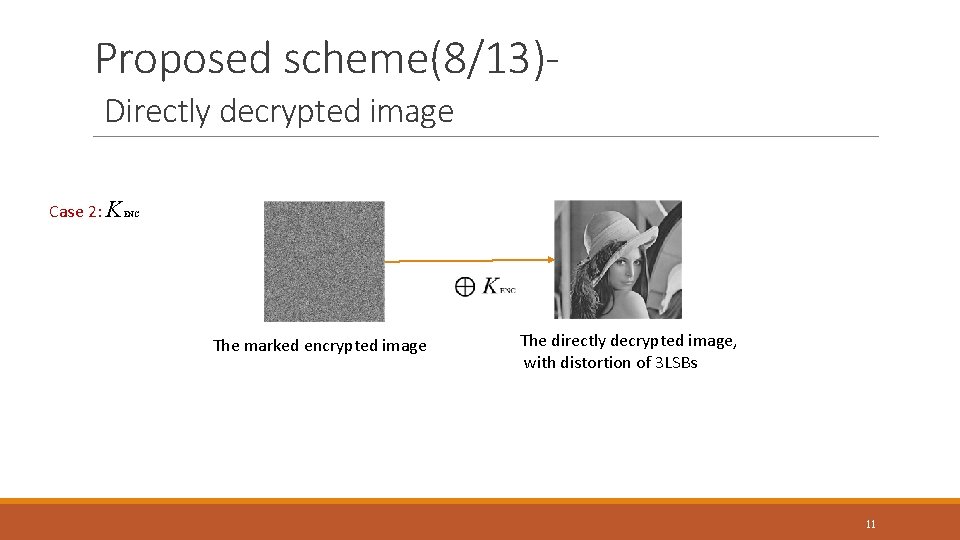
Proposed scheme(8/13)Directly decrypted image Case 2: K ENC The marked encrypted image The directly decrypted image, with distortion of 3 LSBs 11
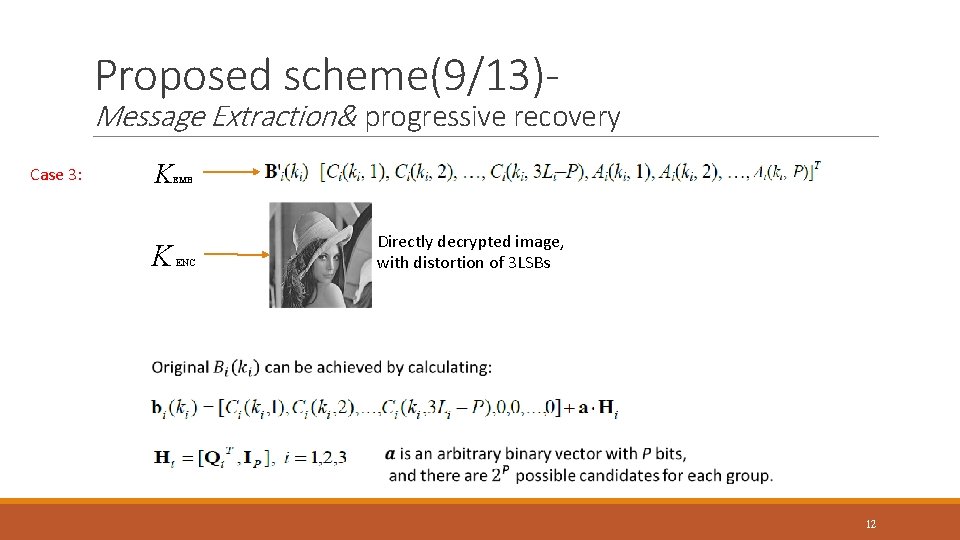
Proposed scheme(9/13)- Message Extraction& progressive recovery Case 3: K EMB K ENC Directly decrypted image, with distortion of 3 LSBs 12
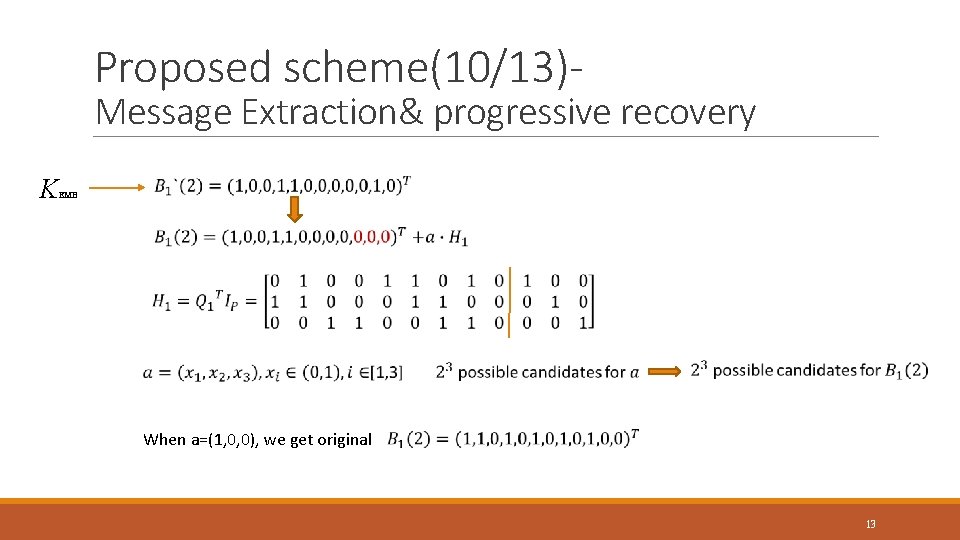
Proposed scheme(10/13)- Message Extraction& progressive recovery K EMB When a=(1, 0, 0), we get original 13
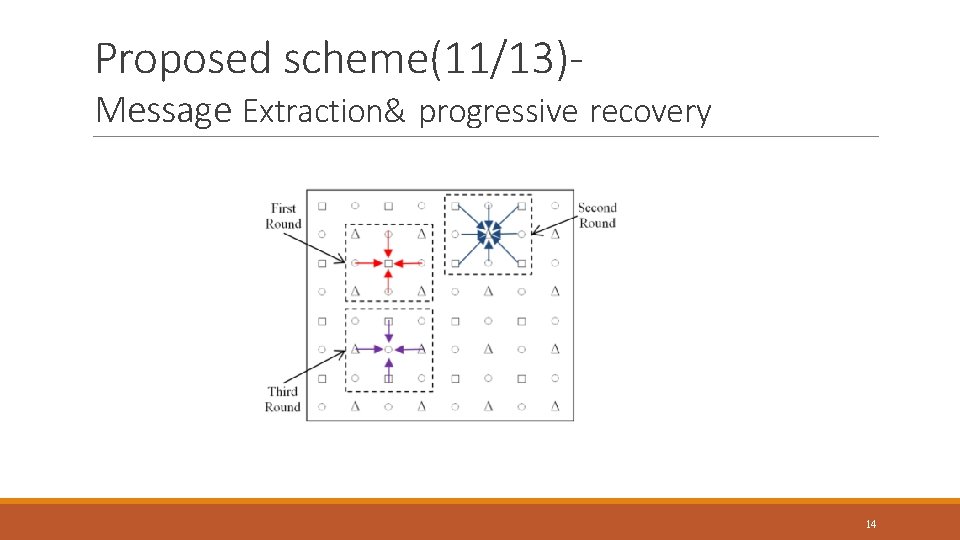
Proposed scheme(11/13)- Message Extraction& progressive recovery 14
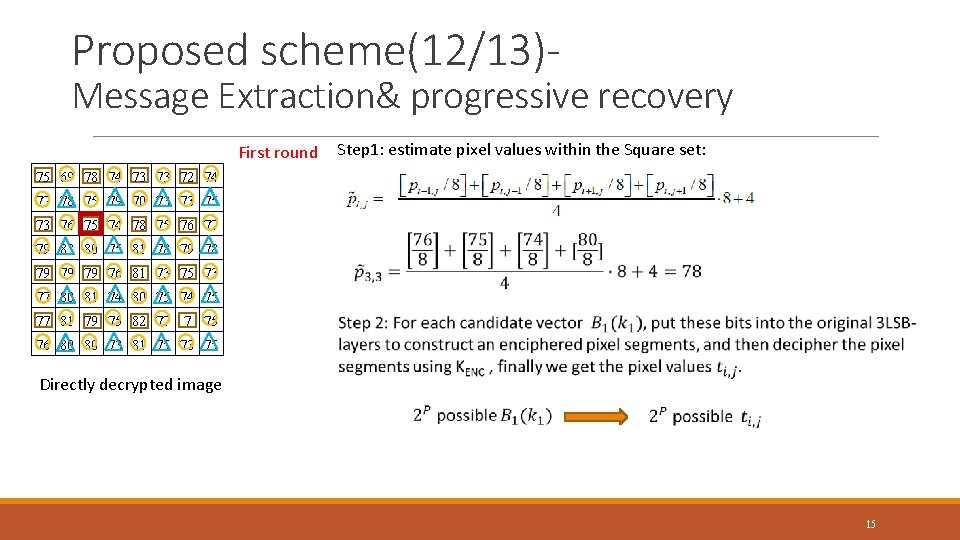
Proposed scheme(12/13)- Message Extraction& progressive recovery First round Step 1: estimate pixel values within the Square set: 75 69 78 74 73 73 72 74 77 78 75 79 70 73 73 75 73 76 75 74 78 75 76 77 79 83 80 75 81 78 79 79 79 76 81 73 75 73 77 80 81 74 80 75 74 75 77 81 79 75 82 77 7 75 76 80 80 73 81 75 73 75 Directly decrypted image 15
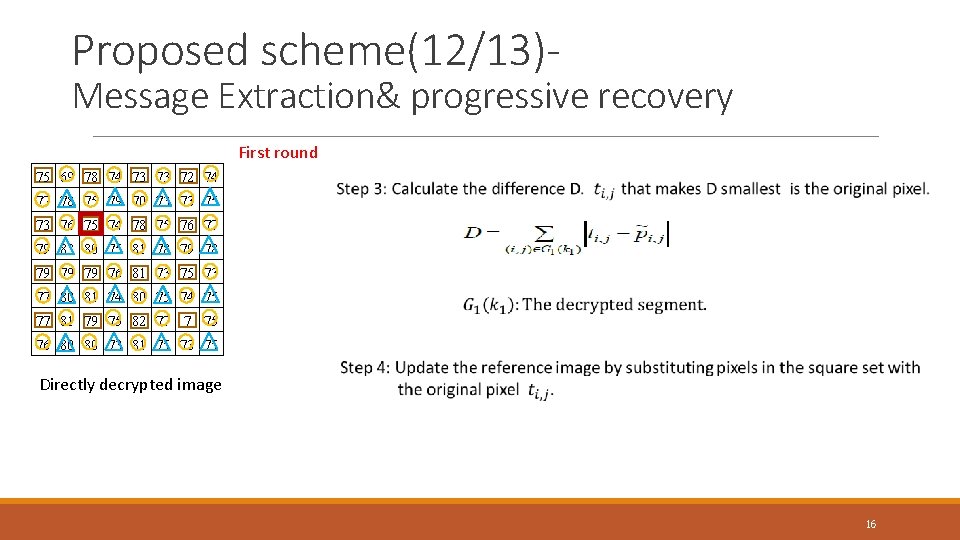
Proposed scheme(12/13)- Message Extraction& progressive recovery First round 75 69 78 74 73 73 72 74 77 78 75 79 70 73 73 75 73 76 75 74 78 75 76 77 79 83 80 75 81 78 79 79 79 76 81 73 75 73 77 80 81 74 80 75 74 75 77 81 79 75 82 77 7 75 76 80 80 73 81 75 73 75 Directly decrypted image 16
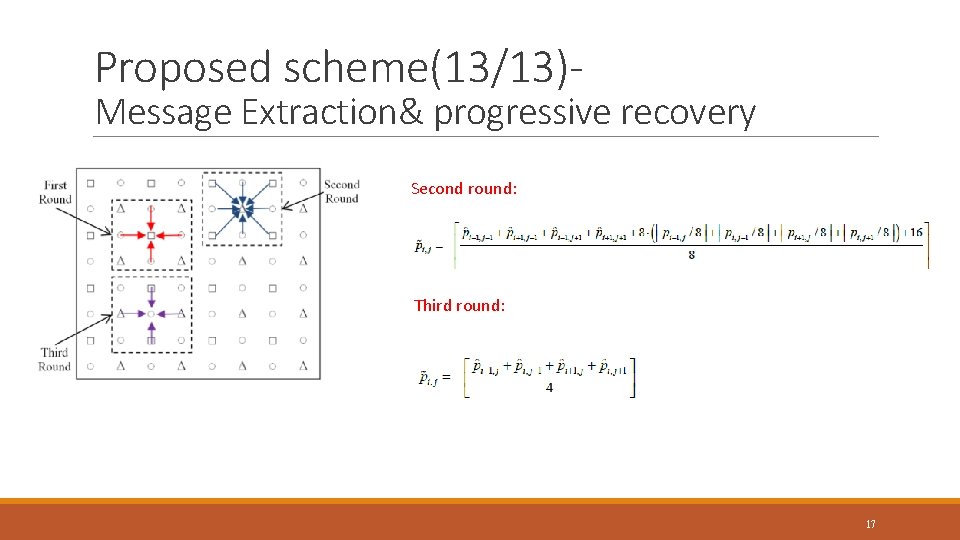
Proposed scheme(13/13)- Message Extraction& progressive recovery Second round: Third round: 17
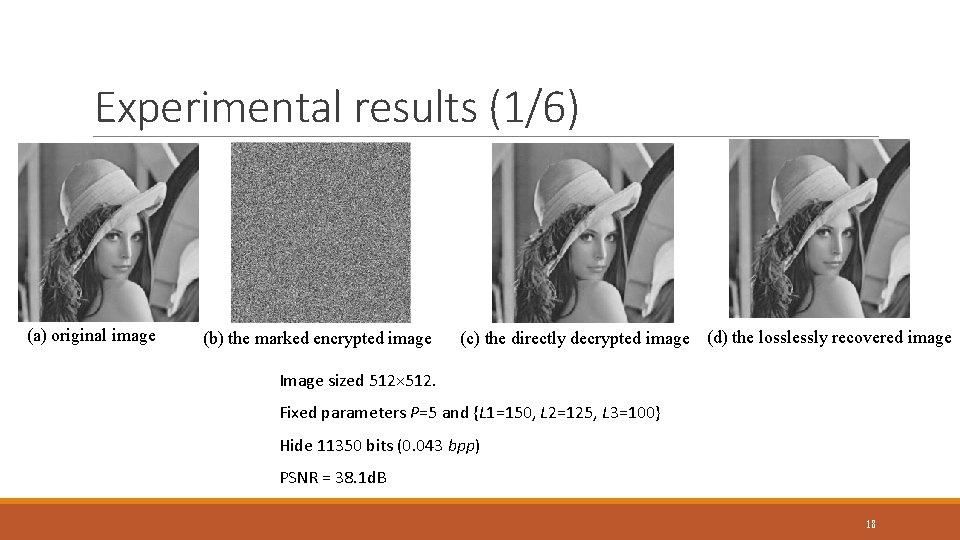
Experimental results (1/6) (a) original image (b) the marked encrypted image (c) the directly decrypted image (d) the losslessly recovered image Image sized 512× 512. Fixed parameters P=5 and {L 1=150, L 2=125, L 3=100} Hide 11350 bits (0. 043 bpp) PSNR = 38. 1 d. B 18
![Experimental results (2/6) [10] X. Zhang, Separable reversible data hiding in encrypted image, IEEE Experimental results (2/6) [10] X. Zhang, Separable reversible data hiding in encrypted image, IEEE](http://slidetodoc.com/presentation_image_h2/8445990828ae51c6bcf6f9273e5269cb/image-19.jpg)
Experimental results (2/6) [10] X. Zhang, Separable reversible data hiding in encrypted image, IEEE Transactions Information Forensics and Security, 7(2): 826– 832, 2012 19
![Experimental results (3/6) [5] X. Zhang, Reversible data hiding in encrypted images, IEEE Signal Experimental results (3/6) [5] X. Zhang, Reversible data hiding in encrypted images, IEEE Signal](http://slidetodoc.com/presentation_image_h2/8445990828ae51c6bcf6f9273e5269cb/image-20.jpg)
Experimental results (3/6) [5] X. Zhang, Reversible data hiding in encrypted images, IEEE Signal Processing Letters, 18(4): 255– 258, 2011 [6] W. Hong, T. Chen, and H. Wu, An improved reversible data hiding in encrypted images using side match, IEEE Signal Processing Letters, 19(4): 199– 202, 2012 [7] M. Li, D. Xiao, A. Kulsoom, and Y. Zhang, Improved reversible data hiding for encrypted images using full embedding strategy, Electronic Letters, 51(9): 690 -691, 2015 [10] X. Zhang, Separable reversible data hiding in encrypted image, IEEE Transactions Information Forensics and Security, 7(2): 826– 832, 2012 20
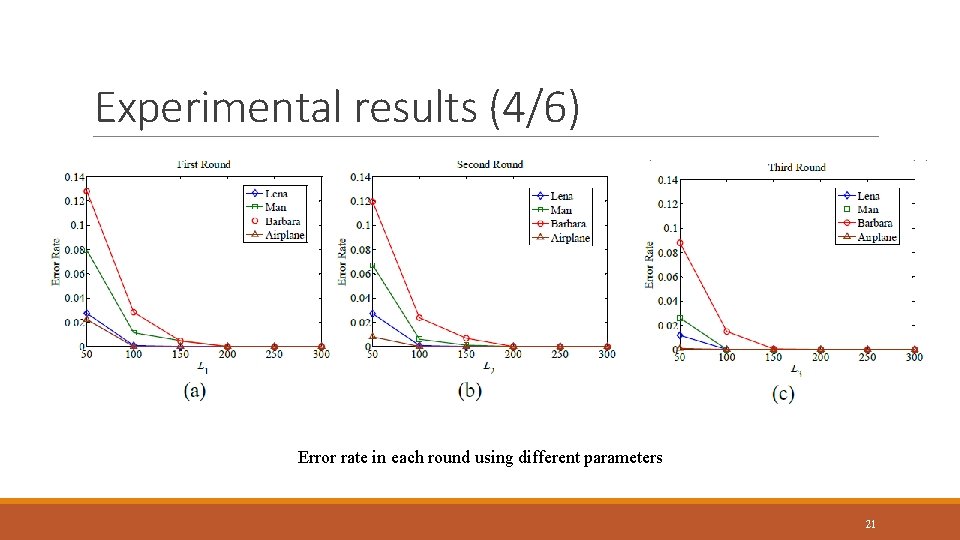
Experimental results (4/6) Error rate in each round using different parameters 21
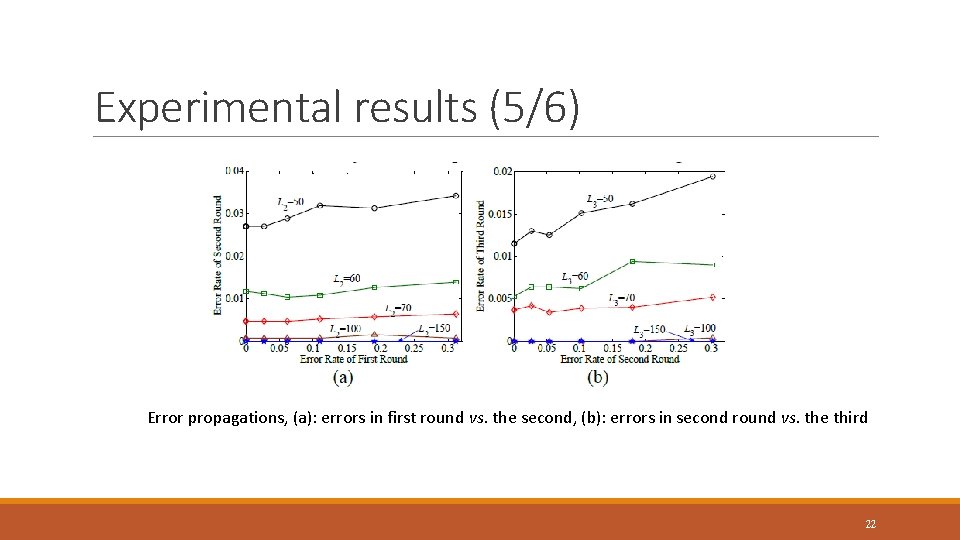
Experimental results (5/6) Error propagations, (a): errors in first round vs. the second, (b): errors in second round vs. the third 22
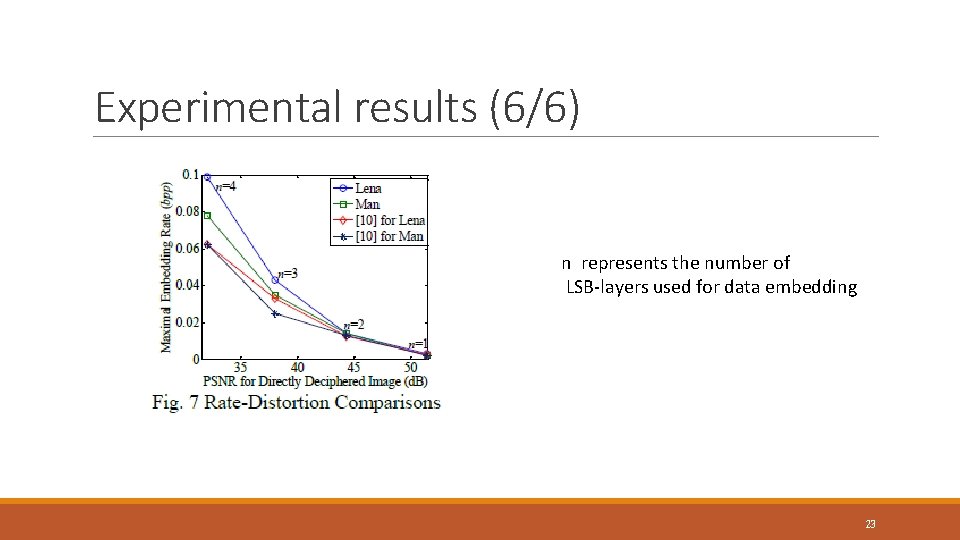
Experimental results (6/6) n represents the number of LSB-layers used for data embedding 23
CONCLUSIONS ØExtend the traditional recovery to the progressive based recovery. ØProvide a better prediction way for estimating the LSB-layers of the original image using three rounds. ØImprove the embedding rate. 24
Thank you! 25
- Slides: 25