A New Reversible Data Hiding in Encrypted Image
A New Reversible Data Hiding in Encrypted Image Based on Multi-Secret and Lightweight Cryptographic Algorithms Authors: Yu-Chi Chen, Tsung-Hsuan Hung and Chih-Wei Shiu Source: IEEE Transaction on information forensics and security, Vol. 14 No. 12, December, 2019: 3332 -3343 Speaker: Sisheng Chen Date: 2019. 10. 3 1
Outline • Introduction • Preliminaries • Proposed scheme • Experimental results • Conclusions 2
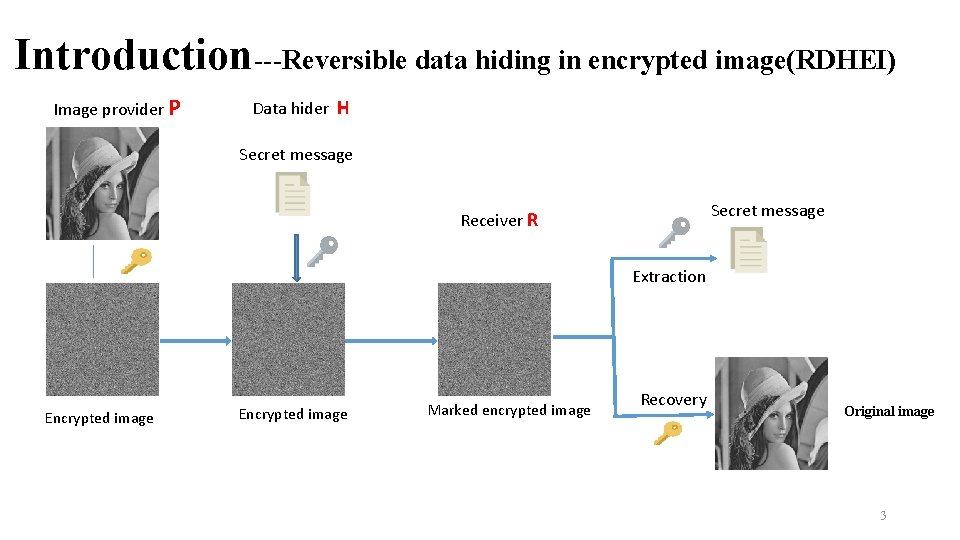
Introduction---Reversible data hiding in encrypted image(RDHEI) Image provider P Data hider H Secret message Receiver R Extraction Encrypted image Marked encrypted image Recovery Original image 3
Introduction---Motivation Two notions of RDHEI( by the factor of key setting ) n Share independent secret key (SIK): R shares independent keys, key. P and key. H, with P and H respectively. n Share no secret key(SNK) : In contrast to SIK, R does not need to share any secret key. This can be easily achieved through public key encryption where R has a public/secret key pair. • Those homomorphic encryption-based SNK-type RDHEI are practically inefficient. Can we construct an efficient scheme to satisfy the intermediate notion (between SIK and SNK) where P and R share a secret key, but no secret is shared with H? 4

Preliminaries(1/3)---Multi-secret Sharing(1/2) 1. Shamir’s secret sharing: (k, n)-threshold secret sharing 2. multi-secret sharing: (c, d, k, n)-multi-secret sharing The dealer takes d secrets to produce shares (1) Any k shares work together to recover all these secrets. (2) An adversary who can corrupt c shares (c<k) has no information about the d secrets Random number Scheme: d=t, k=2 t, n=2 t [30] M. Franklin and M. Yung, “Communication complexity of secure computation, ”in Proc. 24 th Annu. ACM Symp. Theory Comput. New York, NY, USA: ACM, 1992, pp. 5 699 – 710.

Preliminaries (2/3)---Multi-secret Sharing (2/2) (2, 2, 4, 4)-multi-secret sharing Secret message: Choose a random key: Generate a degree 3 polynomial: Secret sharing: Security: Given(1, 219) and (2, 243), it is hard to obtain (103, 99) Recovery the secret message: If we know the key , we obtain 6
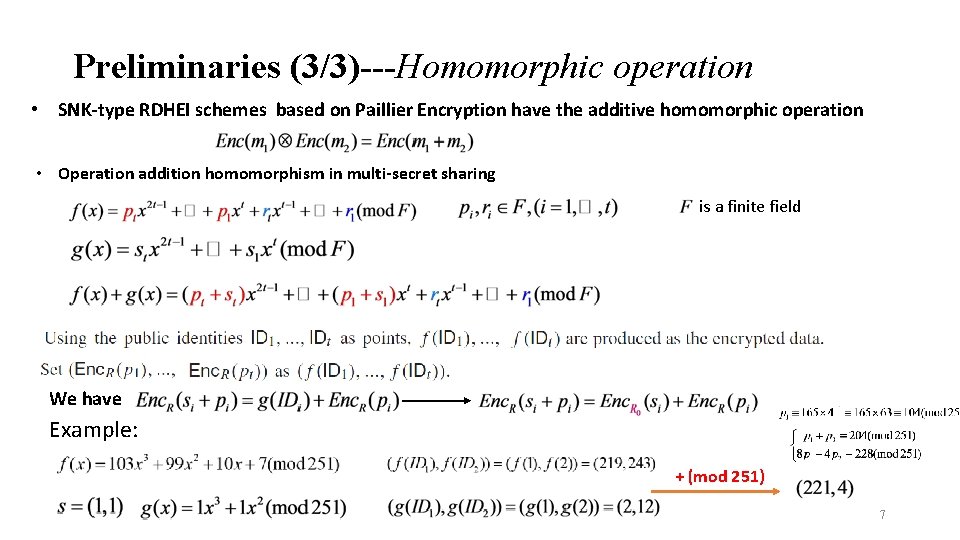
Preliminaries (3/3)---Homomorphic operation • SNK-type RDHEI schemes based on Paillier Encryption have the additive homomorphic operation • Operation addition homomorphism in multi-secret sharing is a finite field We have Example: + (mod 251) 7
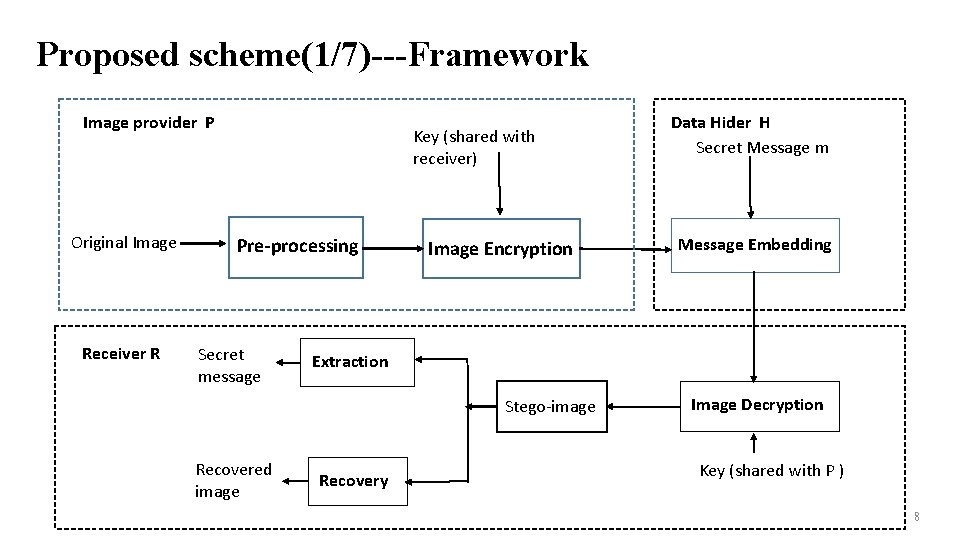
Proposed scheme(1/7)---Framework Image provider P Original Image Receiver R Key (shared with receiver) Pre-processing Secret message Image Encryption Message Embedding Extraction Stego-image Recovered image Data Hider H Secret Message m Recovery Image Decryption Key (shared with P ) 8
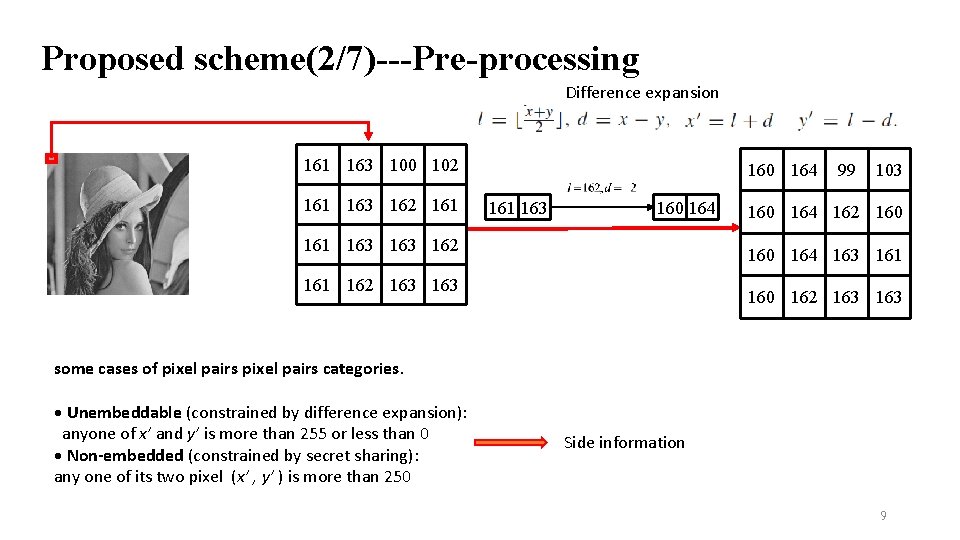
Proposed scheme(2/7)---Pre-processing Difference expansion 161 163 100 102 161 163 162 161 160 164 161 163 163 162 99 103 160 164 162 160 164 163 161 162 163 160 162 163 some cases of pixel pairs categories. • Unembeddable (constrained by difference expansion): anyone of x’ and y’ is more than 255 or less than 0 • Non-embedded (constrained by secret sharing): any one of its two pixel (x’ , y’ ) is more than 250 Side information 9
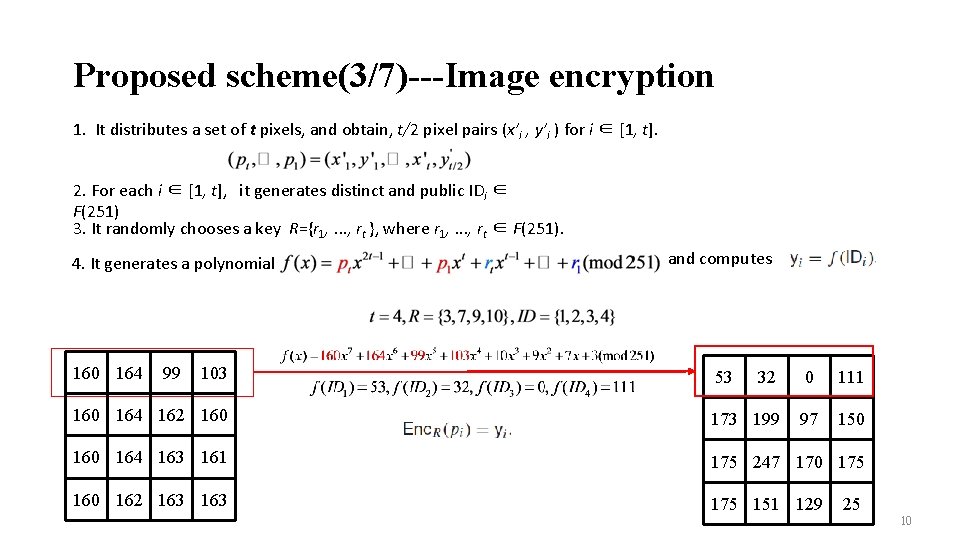
Proposed scheme(3/7)---Image encryption 1. It distributes a set of t pixels, and obtain, t/2 pixel pairs (x’i , y’i ) for i ∈ [1, t]. 2. For each i ∈ [1, t], it generates distinct and public IDi ∈ F(251) 3. It randomly chooses a key R={r 1, . . . , rt }, where r 1, . . . , rt ∈ F(251). 4. It generates a polynomial 160 164 99 103 and computes 53 32 0 111 160 164 162 160 173 199 97 150 164 163 161 175 247 170 175 160 162 163 175 151 129 25 10
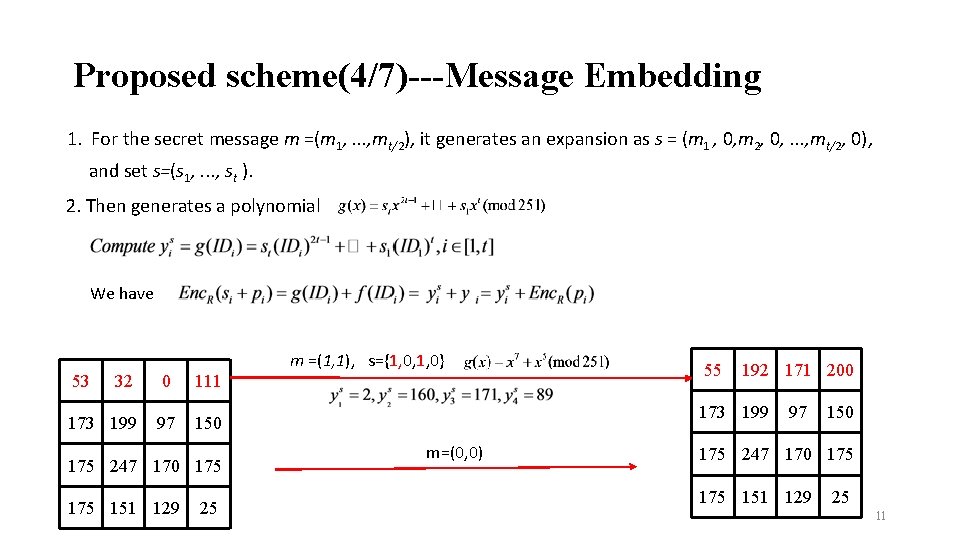
Proposed scheme(4/7)---Message Embedding 1. For the secret message m =(m 1, . . . , mt/2), it generates an expansion as s = (m 1 , 0, m 2, 0, . . . , mt/2, 0), and set s=(s 1, . . . , st ). 2. Then generates a polynomial We have m =(1, 1), s={1, 0, 1, 0} 53 32 0 111 173 199 97 150 175 247 170 175 151 129 25 55 192 171 200 173 199 m=(0, 0) 97 150 175 247 170 175 151 129 25 11
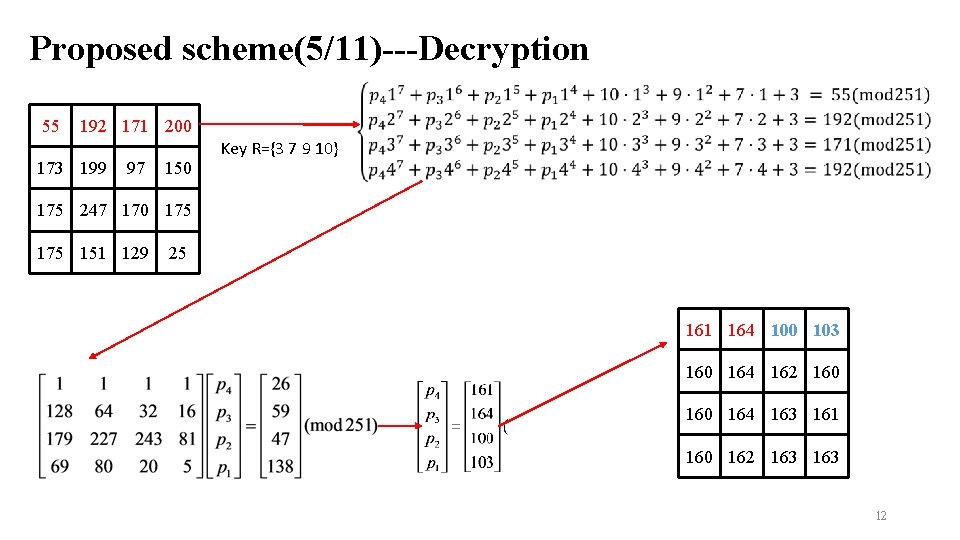
Proposed scheme(5/11)---Decryption 55 192 171 200 173 199 97 150 Key R={3 7 9 10} 175 247 170 175 151 129 25 161 164 100 103 160 164 162 160 164 163 161 160 162 163 12
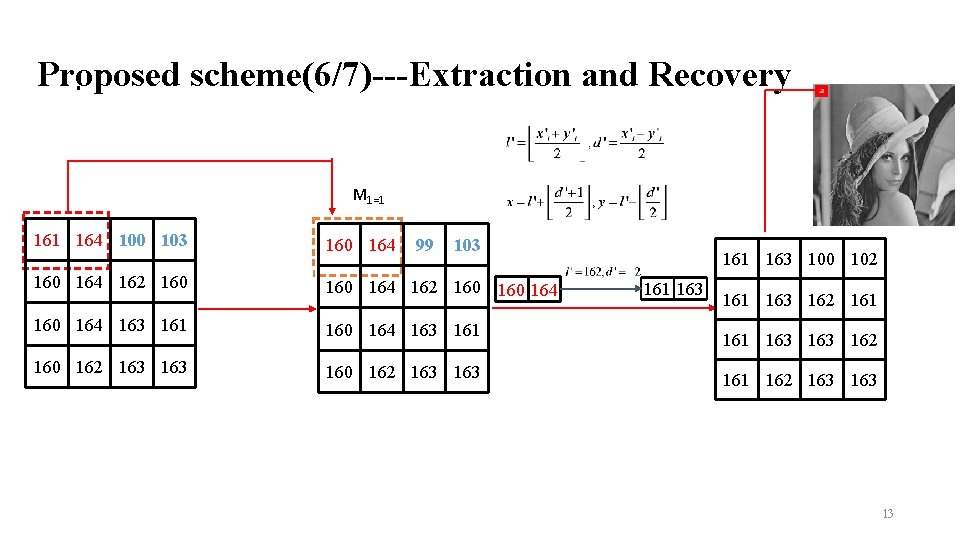
Proposed scheme(6/7)---Extraction and Recovery. M 1=1 164 100 103 160 164 162 160 160 164 163 161 160 162 163 163 99 103 161 163 100 102 161 163 162 161 162 163 13
Proposed scheme(7/7)---Handling side information For all pixels, we divide two parts: the first part is used to embed the side information, and the other to embed the real message (including the secret message). P does the following steps. • 1. Decouple the first and second parts, and collect the side information (denoted by I). • 2. Use the secret sharing to encrypt the pixel in the first part, and record the LSBs of the encrypted pixels as Q. • 3. The side information is embedded into the first part by directly replacing the LSBs. • 4. Q will be embedded into the second part by using our embedding procedure 14

Experimental results (1/3) Fig. 3. Left: Cover-image. Middle: Encrypted, Right: Stego (after decryption). 15
![Experimental results (2/3) [25] X. Zhang, J. Long, Z. Wang, and H. Cheng, “Lossless Experimental results (2/3) [25] X. Zhang, J. Long, Z. Wang, and H. Cheng, “Lossless](http://slidetodoc.com/presentation_image_h/25e718b5c3ea318713650dd053e44e60/image-16.jpg)
Experimental results (2/3) [25] X. Zhang, J. Long, Z. Wang, and H. Cheng, “Lossless and reversible data hiding in encrypted images with public-key cryptography, ” IEEE Trans. Circuits Syst. Video Technol. , vol. 26, no. 9, pp. 1622– 1631, Sep. 2016. [27] C. -W. Shiu, Y. -C. Chen, and W. Hong, “Encrypted image-based reversible data hiding with public key cryptography from difference expansion, ” Signal Process. , Image Commun. , vol. 39, pp. 226– 233, Nov. 2015. [32] S. Xiang and X. Luo, “Reversible data hiding in homomorphic encrypted domain by mirroring cipher text group, ” IEEE Trans. Circuits Syst. Video echnol. , vol. 28, no. 11, pp. 3099– 3110, Nov. 2018. 16
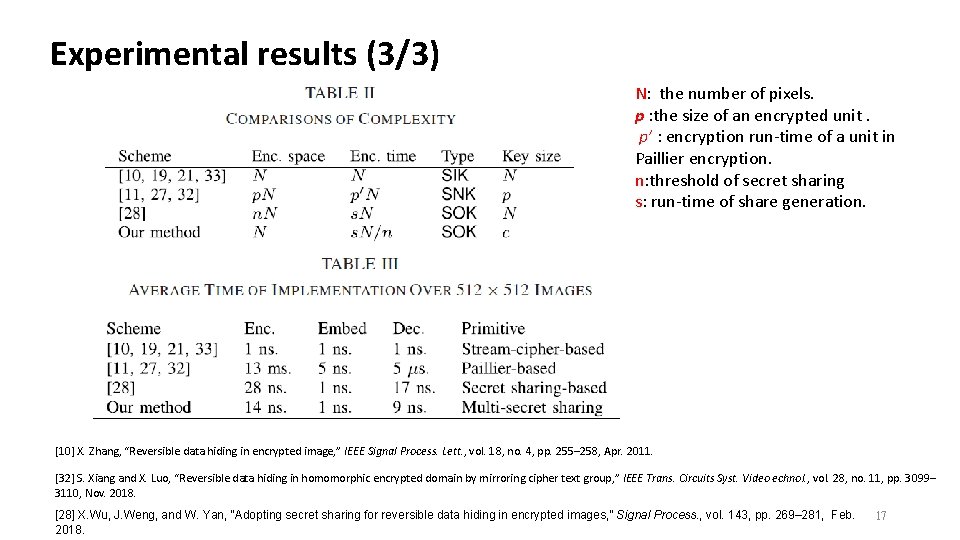
Experimental results (3/3) N: the number of pixels. p : the size of an encrypted unit. p’ : encryption run-time of a unit in Paillier encryption. n: threshold of secret sharing s: run-time of share generation. [10] X. Zhang, “Reversible data hiding in encrypted image, ” IEEE Signal Process. Lett. , vol. 18, no. 4, pp. 255– 258, Apr. 2011. [32] S. Xiang and X. Luo, “Reversible data hiding in homomorphic encrypted domain by mirroring cipher text group, ” IEEE Trans. Circuits Syst. Video echnol. , vol. 28, no. 11, pp. 3099– 3110, Nov. 2018. [28] X. Wu, J. Weng, and W. Yan, “Adopting secret sharing for reversible data hiding in encrypted images, ” Signal Process. , vol. 143, pp. 269– 281, Feb. 2018. 17
Conclusions • presenting a new class of reversible data hiding in encrypted images, referred to as shared-one-key (SOK). 18
. • Thanks 19
- Slides: 19