Highcapacity Reversible Data Hiding in Encrypted Image based
High-capacity Reversible Data Hiding in Encrypted Image based on Specific Encryption Process Sourse: Signal Processing: Image Communication (Available online 13 September 2019) Authors: De-lu Huang and Jian-jun Wang Speaker: Wang Xu Date: 2019/09/26
Outline • Introduction • Related work • Proposed method • Experiment results • Conclusions
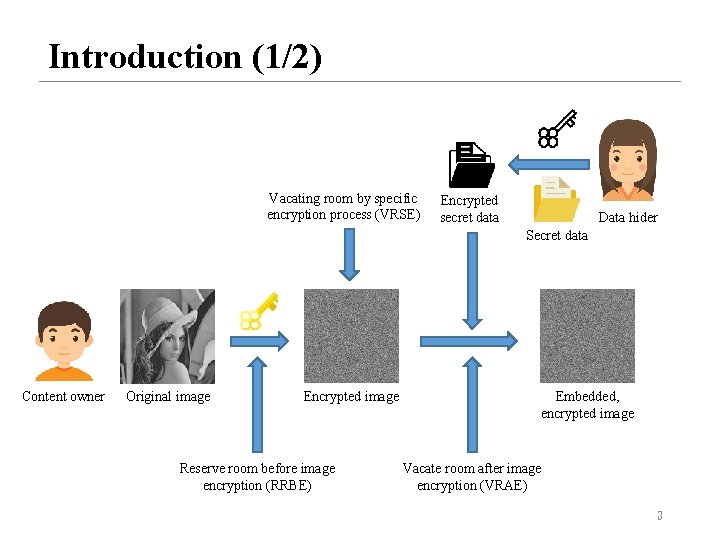
Introduction (1/2) Vacating room by specific encryption process (VRSE) Encrypted secret data Data hider Secret data Content owner Original image Encrypted image Reserve room before image encryption (RRBE) Embedded, encrypted image Vacate room after image encryption (VRAE) 3
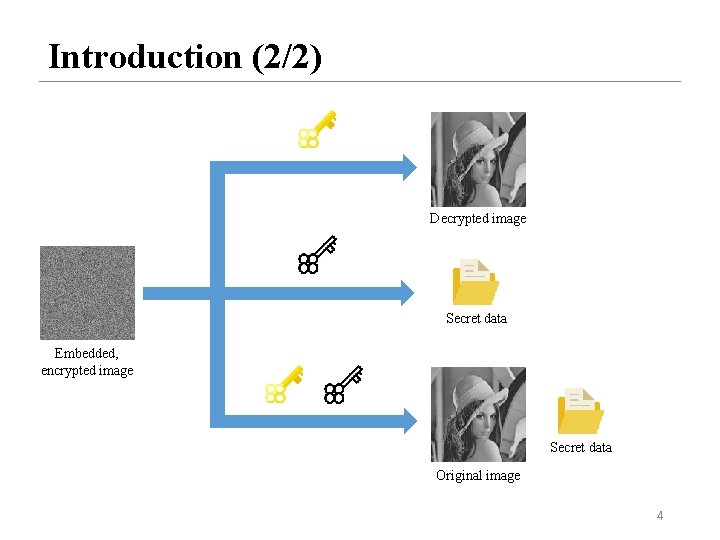
Introduction (2/2) Decrypted image Secret data Embedded, encrypted image Secret data Original image 4
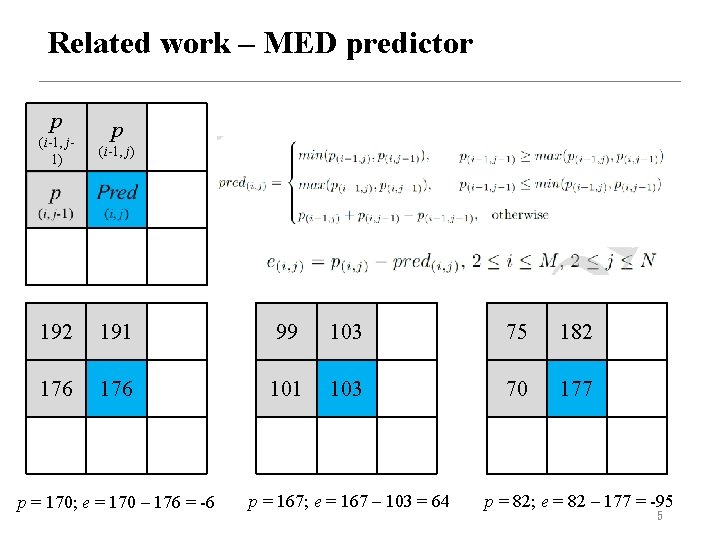
Related work – MED predictor p p (i-1, j 1) (i-1, j) 192 191 99 103 75 182 176 101 103 70 177 p = 170; e = 170 – 176 = -6 p = 167; e = 167 – 103 = 64 p = 82; e = 82 – 177 = -95 5
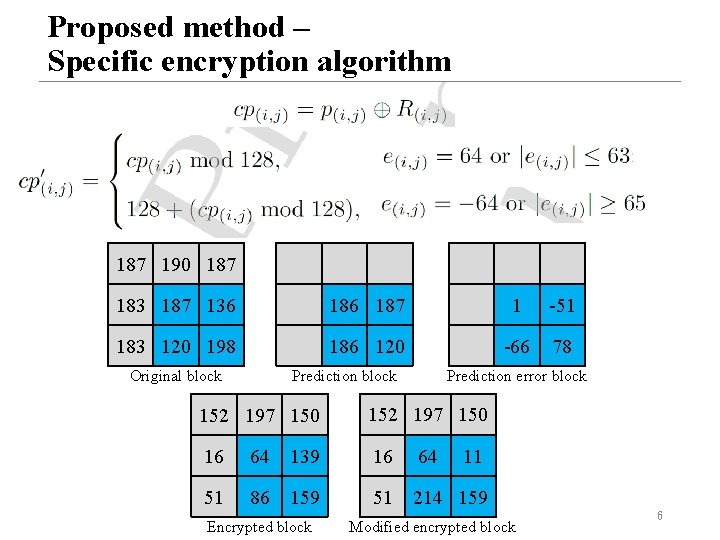
Proposed method – Specific encryption algorithm 187 190 187 183 187 136 187 1 -51 183 120 198 186 120 -66 78 Original block Prediction error block 152 197 150 16 64 139 16 64 51 86 159 51 214 159 Encrypted block 11 Modified encrypted block 6
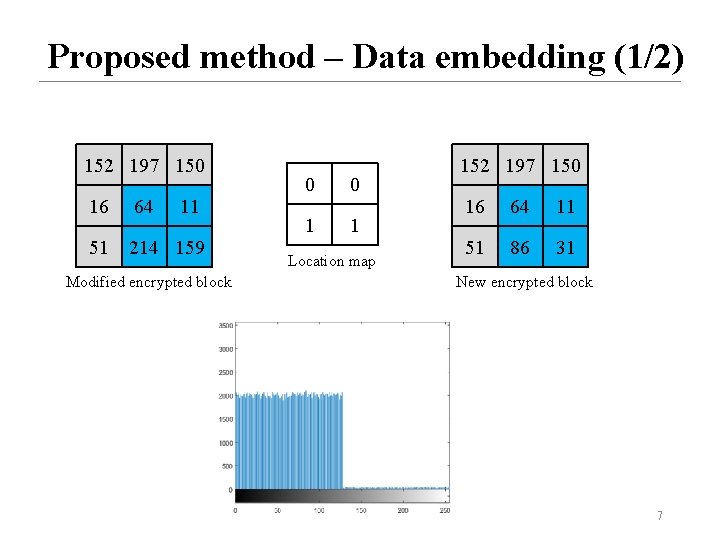
Proposed method – Data embedding (1/2) 152 197 150 16 64 11 51 214 159 Modified encrypted block 0 0 1 1 Location map 152 197 150 16 64 11 51 86 31 New encrypted block 7
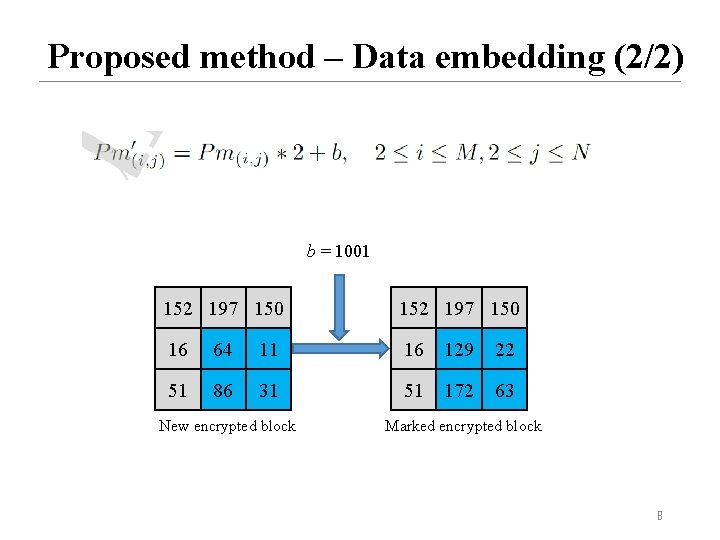
Proposed method – Data embedding (2/2) b = 1001 152 197 150 16 64 11 16 129 22 51 86 31 51 172 63 New encrypted block Marked encrypted block 8
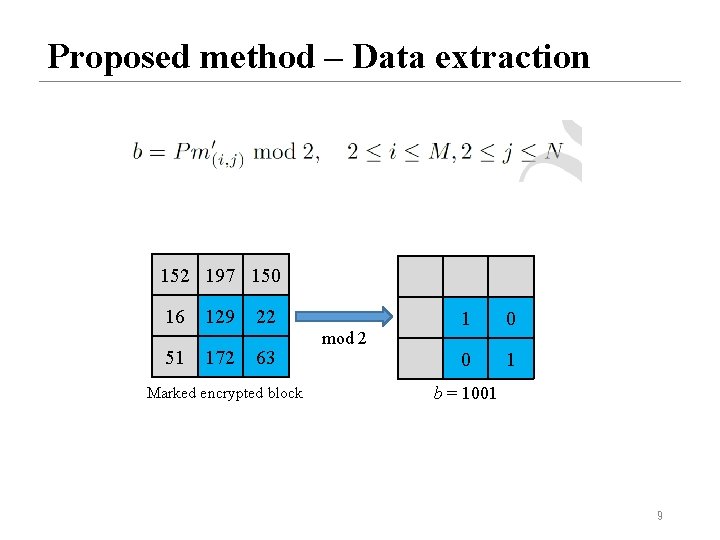
Proposed method – Data extraction 152 197 150 16 51 129 172 22 63 Marked encrypted block mod 2 1 0 0 1 b = 1001 9
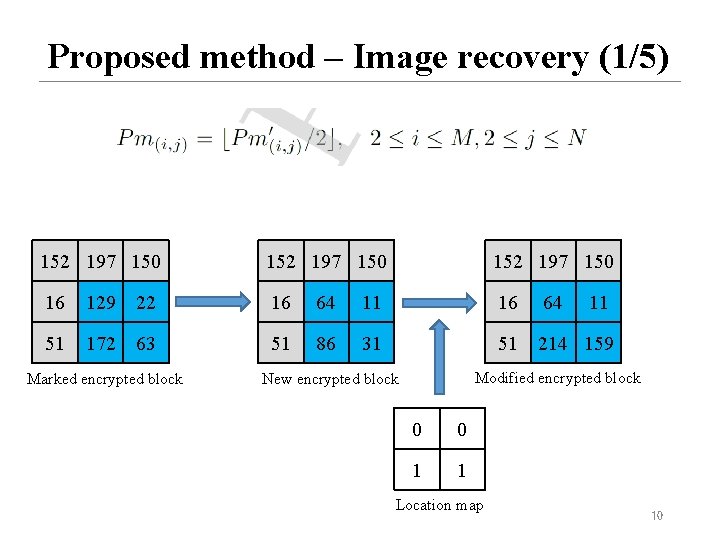
Proposed method – Image recovery (1/5) 152 197 150 16 129 22 16 64 11 16 64 51 172 63 51 86 31 51 214 159 Marked encrypted block 11 Modified encrypted block New encrypted block 0 0 1 1 Location map 10
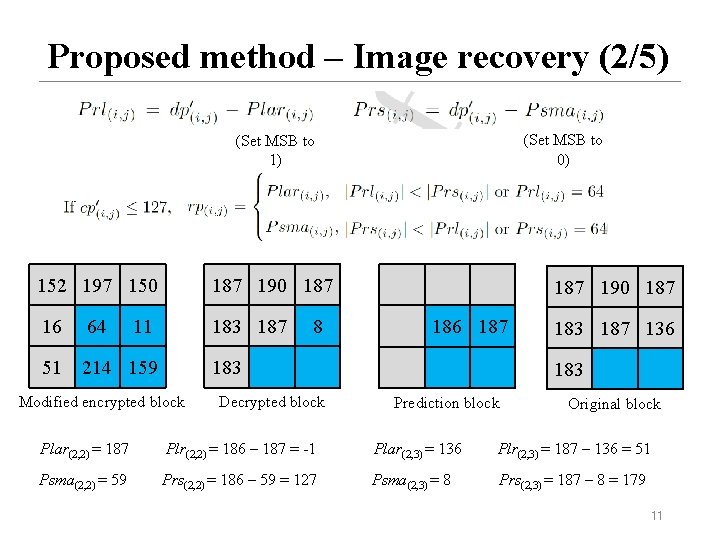
Proposed method – Image recovery (2/5) (Set MSB to 0) (Set MSB to 1) 152 197 150 187 190 187 16 64 183 187 51 214 159 11 8 187 190 187 186 187 183 Modified encrypted block Decrypted block 183 187 136 183 Prediction block Original block Plar(2, 2) = 187 Plr(2, 2) = 186 – 187 = -1 Plar(2, 3) = 136 Plr(2, 3) = 187 – 136 = 51 Psma(2, 2) = 59 Prs(2, 2) = 186 – 59 = 127 Psma(2, 3) = 8 Prs(2, 3) = 187 – 8 = 179 11
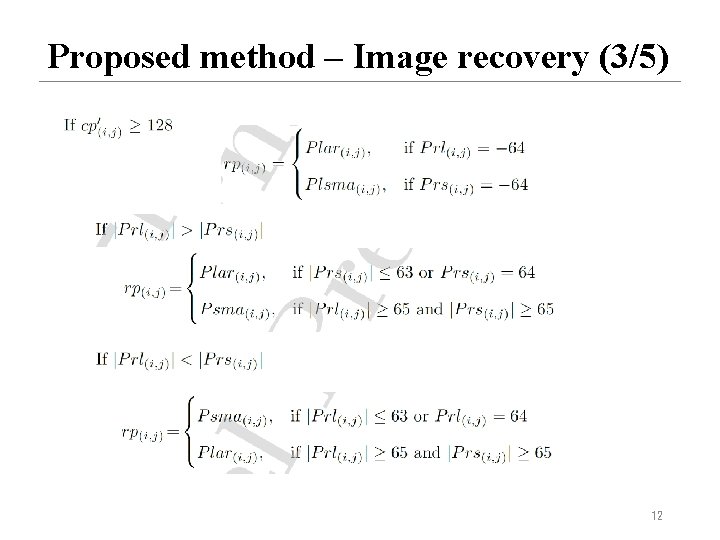
Proposed method – Image recovery (3/5) 12
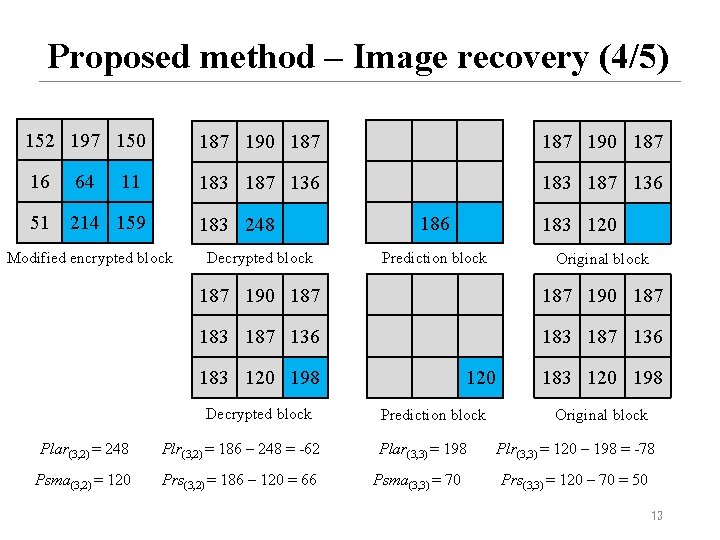
Proposed method – Image recovery (4/5) 152 197 150 187 190 187 16 64 183 187 136 51 214 159 11 183 248 Modified encrypted block Decrypted block 186 183 120 Prediction block Original block 187 190 187 183 187 136 183 120 198 Decrypted block Plar(3, 2) = 248 Plr(3, 2) = 186 – 248 = -62 Psma(3, 2) = 120 Prs(3, 2) = 186 – 120 = 66 120 Prediction block Plar(3, 3) = 198 Psma(3, 3) = 70 183 120 198 Original block Plr(3, 3) = 120 – 198 = -78 Prs(3, 3) = 120 – 70 = 50 13
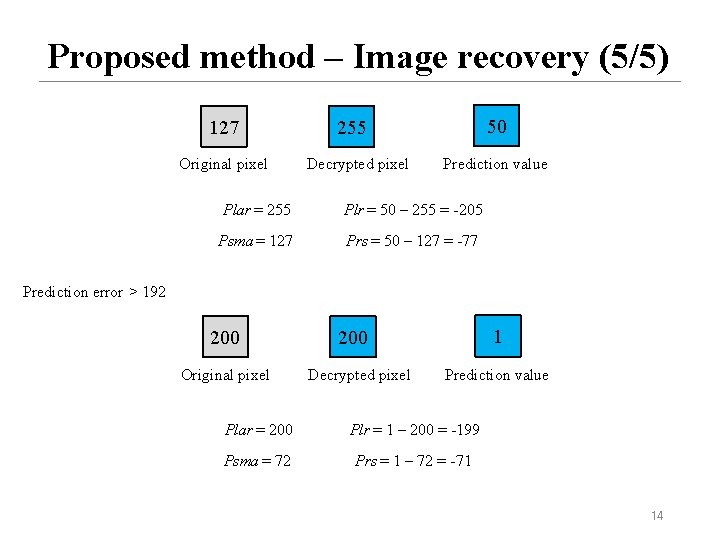
Proposed method – Image recovery (5/5) 127 Original pixel 50 255 Decrypted pixel Prediction value Plar = 255 Plr = 50 – 255 = -205 Psma = 127 Prs = 50 – 127 = -77 Prediction error > 192 200 Original pixel 1 200 Decrypted pixel Prediction value Plar = 200 Plr = 1 – 200 = -199 Psma = 72 Prs = 1 – 72 = -71 14
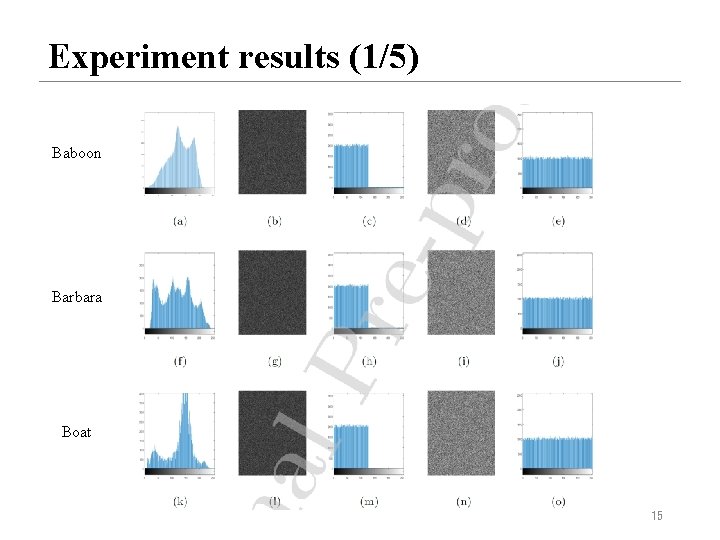
Experiment results (1/5) Baboon Barbara Boat 15
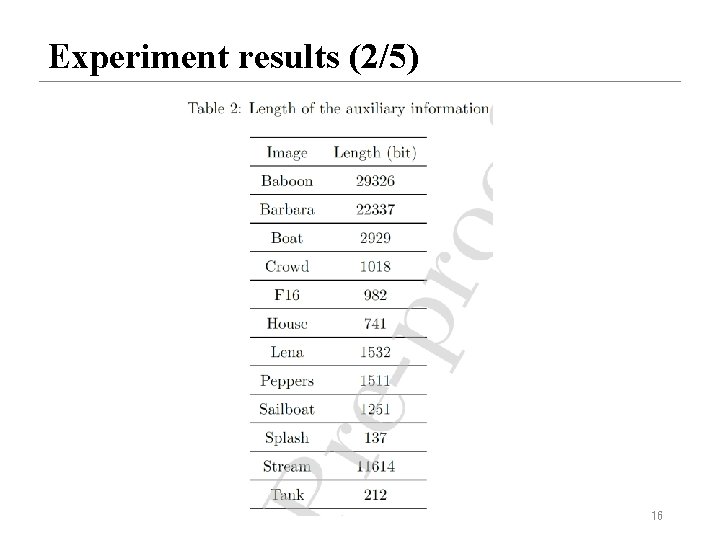
Experiment results (2/5) 16
![Experiment results (3/5) [19] X. Zhang, Reversible data hiding in encrypted image, IEEE Signal Experiment results (3/5) [19] X. Zhang, Reversible data hiding in encrypted image, IEEE Signal](http://slidetodoc.com/presentation_image_h2/ce72bcb2a97670064d312a12a2aa5fd9/image-17.jpg)
Experiment results (3/5) [19] X. Zhang, Reversible data hiding in encrypted image, IEEE Signal Process. Lett. 18 (4) (2011) 255– 258. [22] X. Zhang, Separable reversible data hiding in encrypted image, IEEE Trans. Inf. Forensics Security 7 (2) (2012) 826– 832. [29] F. Huang, J. Huang, Y. Q. Shi, New framework for reversible data hiding in encrypted domain, IEEE Trans. Inf. Forensics Security 11 (12) (2016) 2777– 2789. [30] H. Ge, Y. Chen, Z. Qian, J. Wang, A high capacity multi-level approach for reversible data hiding in encrypted images, IEEE Trans. 17 Inf. Forensics Security 29 (8) (2019) 2285– 2295.
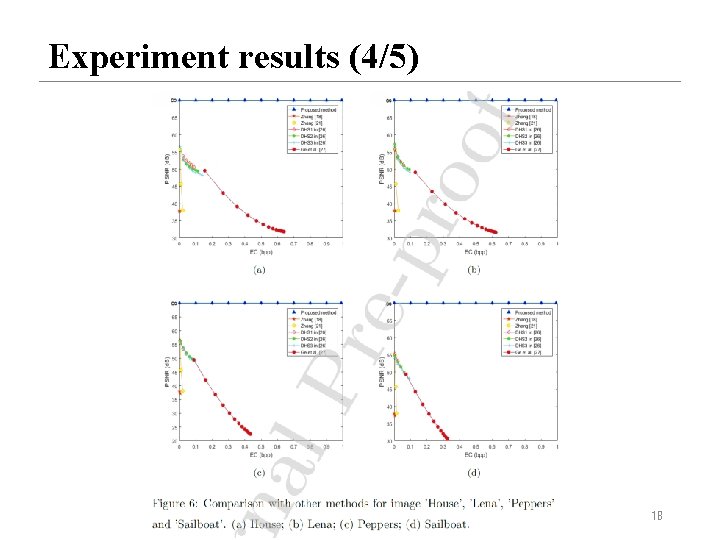
Experiment results (4/5) 18
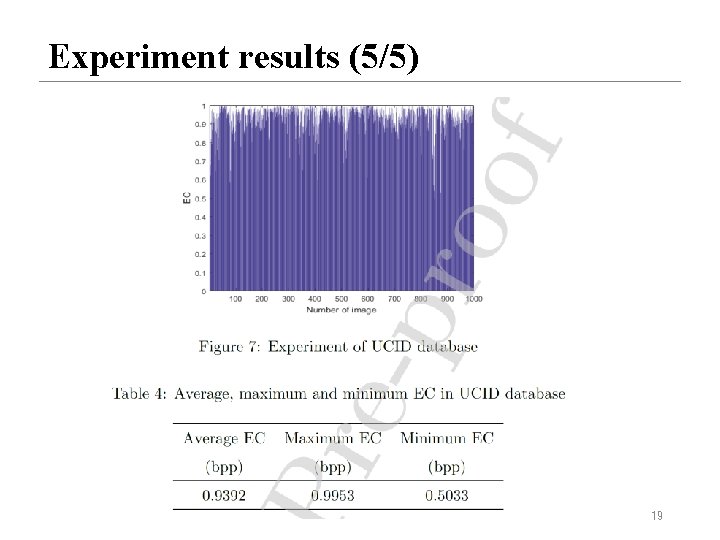
Experiment results (5/5) 19
Conclusions Ø Propose a specific encryption algorithm. Ø Use pixel value expansion method to embed a large amount of secret data. Ø Can perfectly extract the secret data and restore the original image. 20
- Slides: 20