A Reversible Data Hiding in Encrypted Images based
A Reversible Data Hiding in Encrypted Images based on Prediction-error Estimation and Location Map Authors: Asad Malik, Hong-Xia Wang, Yanli Chen, Ahmad Neyaz Khan Source: Multimedia Tools and Applications, January 2020. Speaker: Si. Sheng Chen Date: 2020. 3. 12 1
Outline • Introduction • Proposed scheme • Experimental results • Conclusions 2
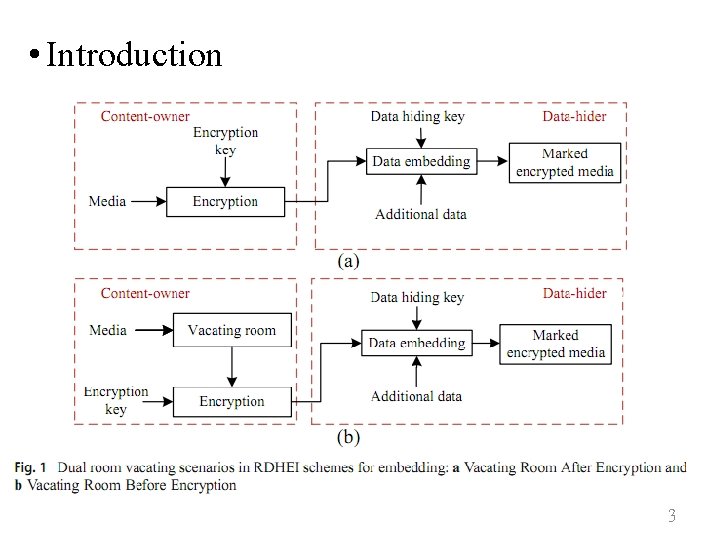
• Introduction 3
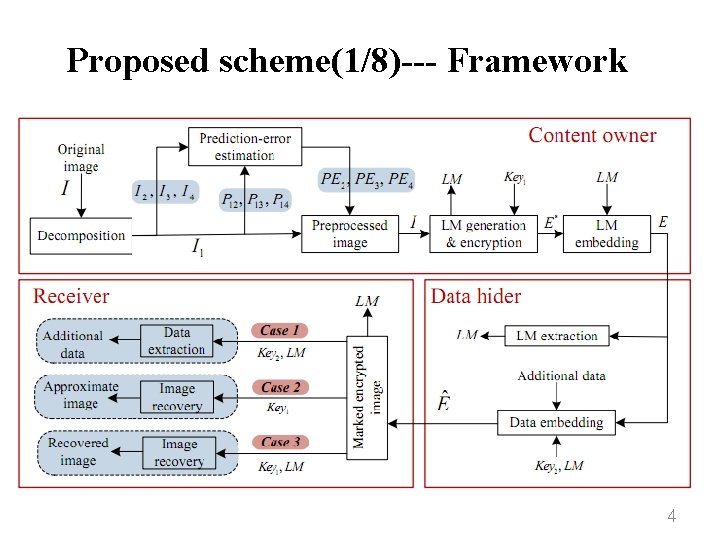
Proposed scheme(1/8)--- Framework 4
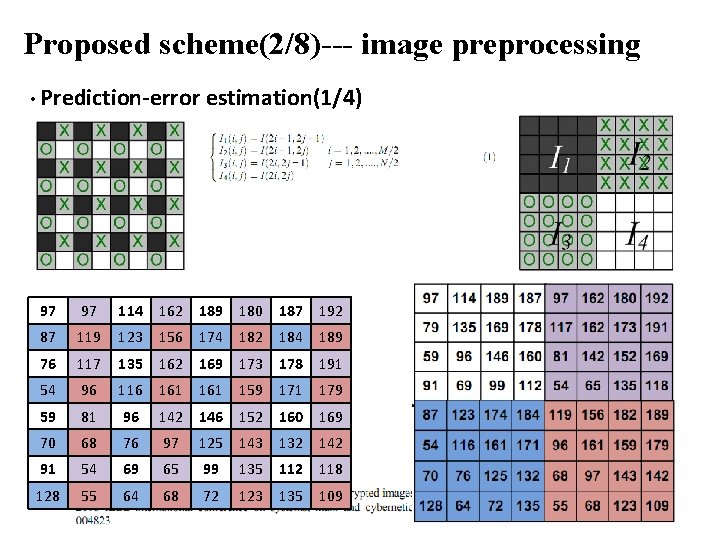
Proposed scheme(2/8)--- image preprocessing • Prediction-error estimation(1/4) 97 97 114 162 189 180 187 192 87 119 123 156 174 182 184 189 76 117 135 162 169 173 178 191 54 96 116 161 159 171 179 59 81 96 142 146 152 160 169 70 68 76 97 125 143 132 142 91 54 69 65 99 135 112 118 128 55 64 68 72 123 135 109 5
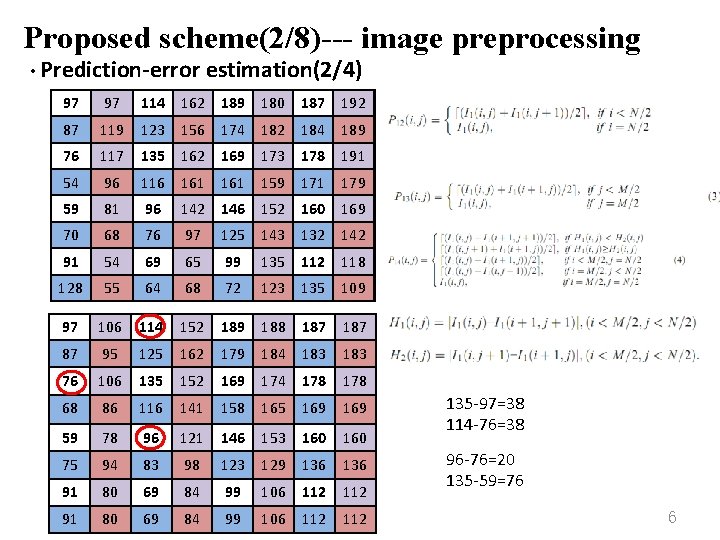
Proposed scheme(2/8)--- image preprocessing • Prediction-error estimation(2/4) 97 97 114 162 189 180 187 192 87 119 123 156 174 182 184 189 76 117 135 162 169 173 178 191 54 96 116 161 159 171 179 59 81 96 142 146 152 160 169 70 68 76 97 125 143 132 142 91 54 69 65 99 135 112 118 128 55 64 68 72 123 135 109 97 106 114 152 189 188 187 187 87 95 125 76 106 135 152 169 174 178 178 68 86 116 141 165 169 59 59 75 75 78 96 96 121 146 153 160 160 94 98 136 80 80 80 84 123 99 99 129 91 91 83 69 69 69 84 99 106 112 112 162 179 158 184 183 183 136 106 112 135 -97=38 114 -76=38 96 -76=20 135 -59=76 6
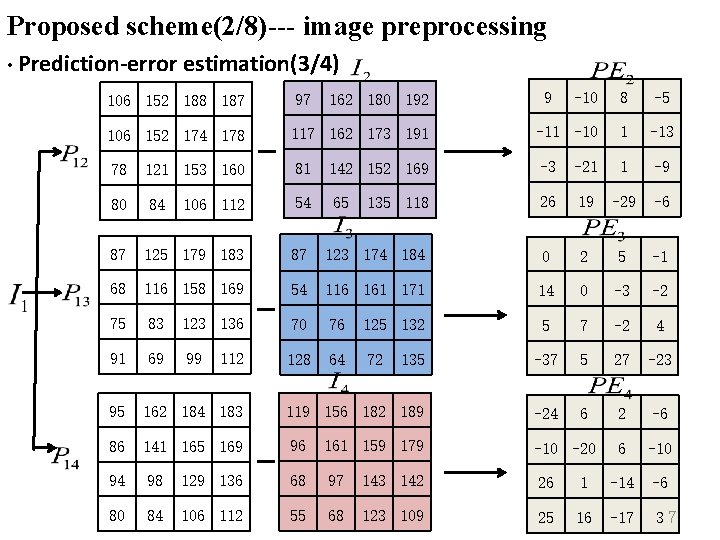
Proposed scheme(2/8)--- image preprocessing • Prediction-error estimation(3/4) -10 8 -5 117 162 173 191 -10 1 -13 121 153 160 81 142 152 169 -3 -21 1 -9 84 106 112 54 65 26 19 -29 -6 87 125 179 183 87 123 174 184 0 2 5 -1 68 116 158 169 54 116 161 171 14 0 -3 -2 75 83 123 136 70 76 125 132 5 7 -2 4 91 69 99 128 64 72 135 -37 5 27 -23 95 162 184 183 119 156 182 189 -24 6 2 -6 86 141 165 169 96 161 159 179 -10 -20 6 -10 94 98 129 136 68 97 143 142 26 1 -14 -6 80 84 106 112 55 68 123 109 25 16 -17 37 106 152 188 187 97 106 152 174 178 78 80 112 162 180 192 135 118 9
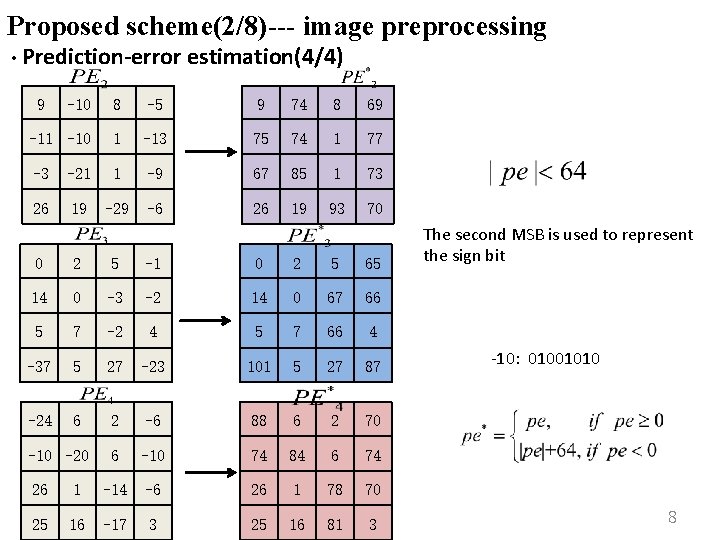
Proposed scheme(2/8)--- image preprocessing • Prediction-error estimation(4/4) 9 -10 8 -5 9 74 8 69 -11 -10 1 -13 75 74 1 77 -3 -21 1 -9 67 85 1 73 26 19 -29 -6 26 19 93 70 0 2 5 -1 0 2 5 65 14 0 -3 -2 14 0 67 66 5 7 -2 4 5 7 66 4 -37 5 27 -23 101 5 27 87 -24 6 2 -6 88 6 2 70 6 -10 74 84 6 74 -10 -20 26 1 -14 -6 26 1 78 70 25 16 -17 3 25 16 81 3 The second MSB is used to represent the sign bit -10: 01001010 8
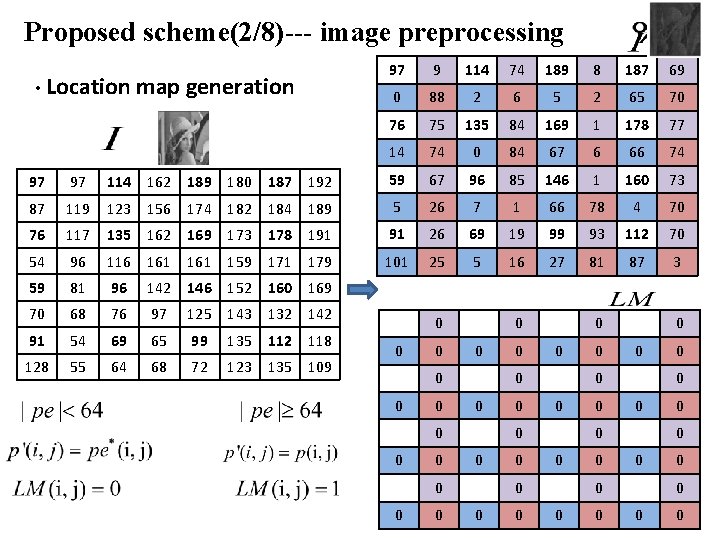
Proposed scheme(2/8)--- image preprocessing • Location map generation 97 9 114 74 189 8 187 69 0 88 2 6 5 2 65 70 76 75 135 84 169 1 178 77 14 74 0 84 67 6 66 74 97 97 114 162 189 180 187 192 59 67 96 85 146 1 160 73 87 119 123 156 174 182 184 189 5 26 7 1 66 78 4 70 76 117 135 162 169 173 178 191 91 26 69 19 99 93 112 70 54 96 116 161 159 171 179 101 25 5 16 27 81 87 3 59 81 96 142 146 152 160 169 70 68 76 97 125 143 132 142 91 54 69 65 99 135 112 118 128 55 64 68 72 123 135 109 0 0 0 0 0 0 0 0 0 0 0 0 90
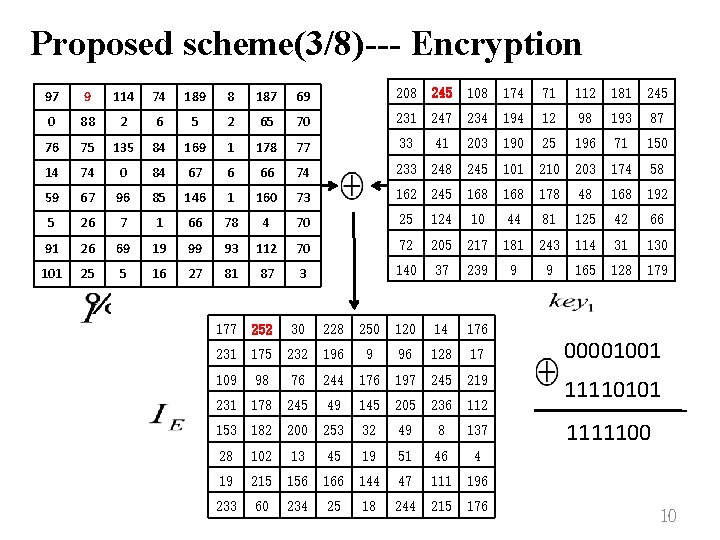
Proposed scheme(3/8)--- Encryption 97 9 114 74 189 8 187 69 208 245 108 174 71 112 181 245 0 88 2 6 5 2 65 70 231 247 234 194 12 98 193 87 76 75 135 84 169 1 178 77 33 41 203 190 25 196 71 150 14 74 0 84 67 6 66 74 233 248 245 101 210 203 174 58 59 67 96 85 146 1 160 73 162 245 168 178 48 168 192 5 26 7 1 66 78 4 70 25 124 10 44 81 125 42 66 91 26 69 19 99 93 112 70 72 205 217 181 243 114 31 130 101 25 5 16 27 81 87 3 140 37 239 9 9 165 128 179 177 252 30 228 250 120 14 176 231 175 232 196 9 96 128 17 109 98 76 244 176 197 245 219 231 178 245 49 145 205 236 112 153 182 200 253 32 49 8 137 28 102 13 45 19 51 46 4 19 215 156 166 144 47 111 196 233 60 234 25 18 244 215 176 00001001 11110101 1111100 10
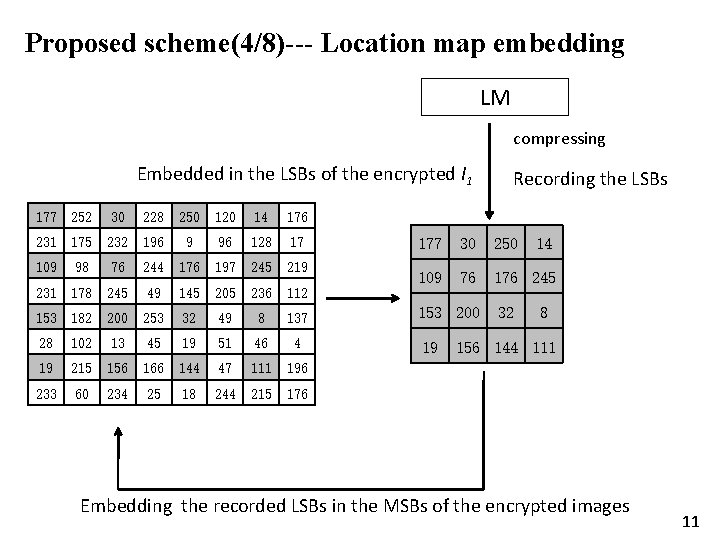
Proposed scheme(4/8)--- Location map embedding LM compressing Embedded in the LSBs of the encrypted I 1 177 252 30 228 250 120 14 176 231 175 232 196 9 96 128 17 109 98 76 244 176 197 245 219 231 178 245 49 145 205 236 112 153 182 200 253 32 49 8 137 28 102 13 45 19 51 46 4 19 215 156 166 144 47 111 196 233 60 234 25 18 244 215 176 Recording the LSBs 177 30 250 109 76 176 245 153 200 19 32 14 8 156 144 111 Embedding the recorded LSBs in the MSBs of the encrypted images 11
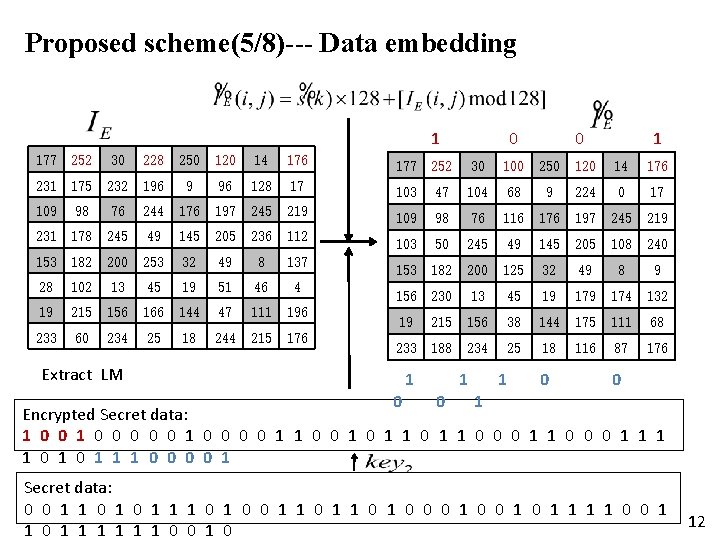
Proposed scheme(5/8)--- Data embedding 1 0 0 1 177 252 30 228 250 120 14 176 177 252 30 100 250 120 14 176 231 175 232 196 9 96 128 17 103 47 104 68 9 224 0 17 109 98 76 244 176 197 245 219 109 98 76 116 176 197 245 219 231 178 245 49 145 205 236 112 103 50 245 49 145 205 108 240 153 182 200 253 32 49 8 137 153 182 200 125 32 49 8 9 28 102 13 45 19 51 46 4 156 230 13 45 19 174 132 19 215 156 166 144 47 111 196 19 215 156 38 144 175 111 68 233 60 234 25 18 244 215 176 233 188 234 25 18 116 87 176 Extract LM 1 1 1 0 0 1 Encrypted Secret data: 1 0 0 0 0 0 1 1 0 0 1 1 0 0 0 1 1 1 0 0 1 Secret data: 0 0 1 1 1 0 0 1 1 0 1 0 1 1 0 0 1 1 1 1 0 0 12
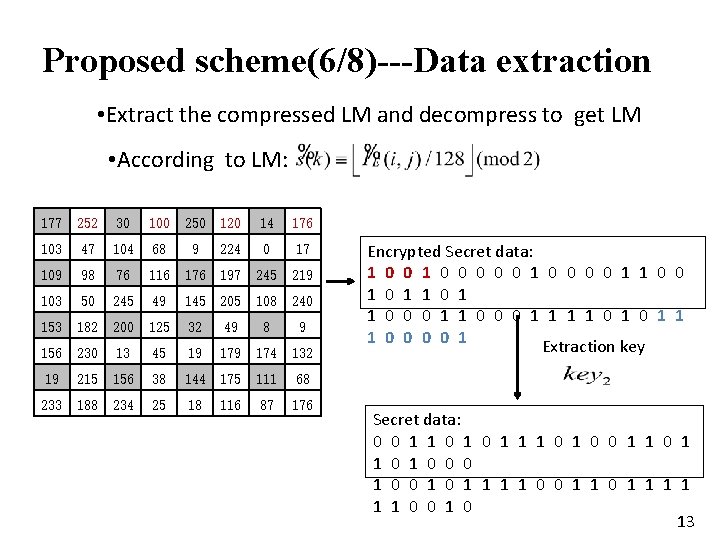
Proposed scheme(6/8)---Data extraction • Extract the compressed LM and decompress to get LM • According to LM: 177 252 30 100 250 120 14 176 103 47 104 68 9 224 0 17 109 98 76 116 176 197 245 219 103 50 245 49 145 205 108 240 153 182 200 125 32 49 8 9 156 230 13 45 19 174 132 19 215 156 38 144 175 111 68 233 188 234 25 18 116 87 176 Encrypted Secret data: 1 0 0 0 0 0 1 1 0 0 1 1 0 0 0 1 1 1 0 0 1 Extraction key Secret data: 0 0 1 1 1 0 0 1 1 0 1 0 1 1 0 0 1 1 1 1 0 0 13
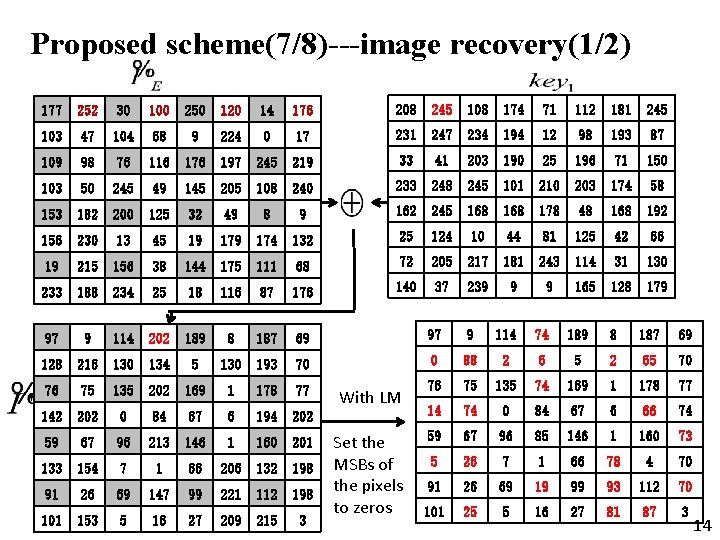
Proposed scheme(7/8)---image recovery(1/2) 177 252 30 100 250 120 14 176 208 245 108 174 71 112 181 245 103 47 104 68 9 224 0 17 231 247 234 194 12 98 193 87 109 98 76 116 176 197 245 219 33 41 203 190 25 196 71 150 103 50 245 49 145 205 108 240 233 248 245 101 210 203 174 58 153 182 200 125 32 49 8 9 162 245 168 178 48 168 192 156 230 13 45 19 174 132 25 124 10 44 81 125 42 66 19 215 156 38 144 175 111 68 72 205 217 181 243 114 31 130 233 188 234 25 18 116 87 176 140 37 239 9 9 165 128 179 97 9 114 202 189 8 187 69 97 9 114 74 189 8 187 69 128 216 130 134 5 130 193 70 0 88 2 6 5 2 65 70 76 75 135 202 169 1 178 77 76 75 135 74 169 1 178 77 142 202 0 84 67 6 194 202 14 74 0 84 67 6 66 74 59 67 96 213 146 1 160 201 59 67 96 85 146 1 160 73 133 154 7 1 66 206 132 198 5 26 7 1 66 78 4 70 91 26 69 147 99 221 112 198 91 26 69 19 99 93 112 70 101 153 5 16 27 209 215 3 101 25 5 16 27 81 87 14 3 With LM Set the MSBs of the pixels to zeros 14
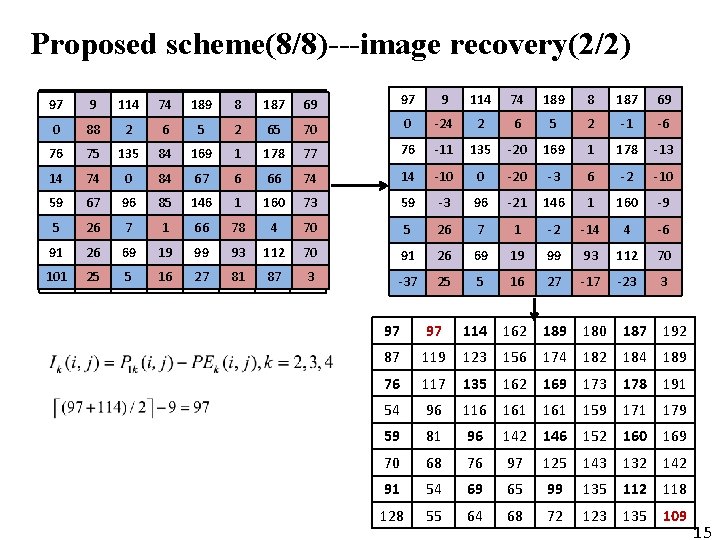
Proposed scheme(8/8)---image recovery(2/2) 97 9 114 74 189 8 187 69 69 97 9 114 74 189 8 187 69 0 88 2 6 5 2 65 65 70 70 0 -24 2 6 5 2 -1 -6 76 75 135 84 74 169 1 178 77 77 76 -11 135 -20 169 1 178 -13 14 14 74 74 00 84 84 67 67 66 66 66 74 74 14 -10 0 -20 -3 6 -2 -10 59 59 67 67 96 96 85 85 146 11 160 73 73 59 -3 96 -21 146 1 160 -9 55 26 26 77 11 66 66 78 78 44 70 70 5 26 7 1 -2 -14 4 -6 91 91 101 26 26 25 25 69 69 55 19 19 16 16 99 99 27 27 93 93 81 81 112 87 87 70 70 33 91 26 69 19 99 93 112 70 -37 25 5 16 27 -17 -23 3 97 97 114 162 189 180 187 192 87 119 123 156 174 182 184 189 76 117 135 162 169 173 178 191 54 96 116 161 159 171 179 59 81 96 142 146 152 160 169 70 68 76 97 125 143 132 142 91 54 69 65 99 135 112 118 128 55 64 68 72 123 135 15 109 15
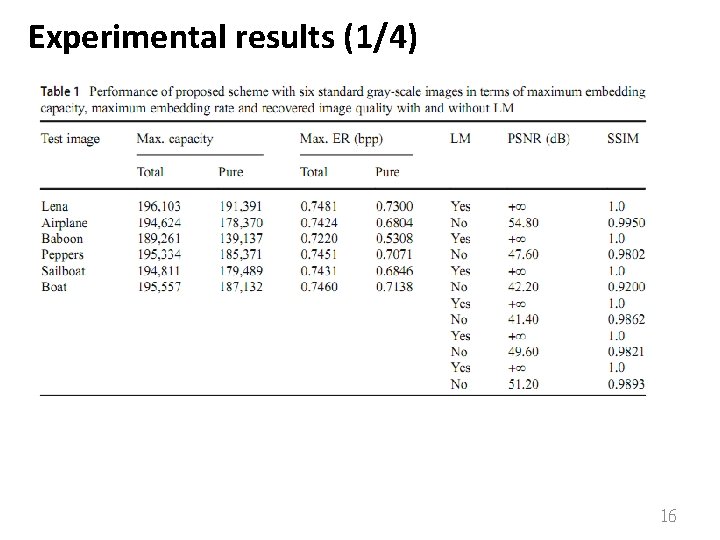
Experimental results (1/4) 16
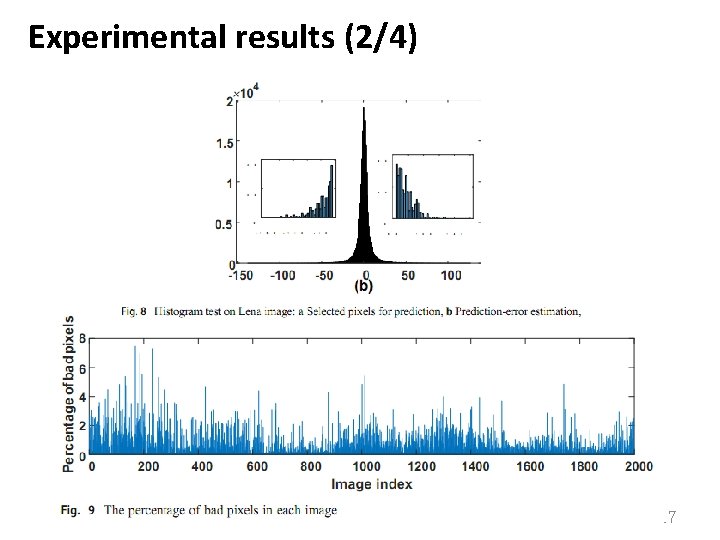
Experimental results (2/4) 17
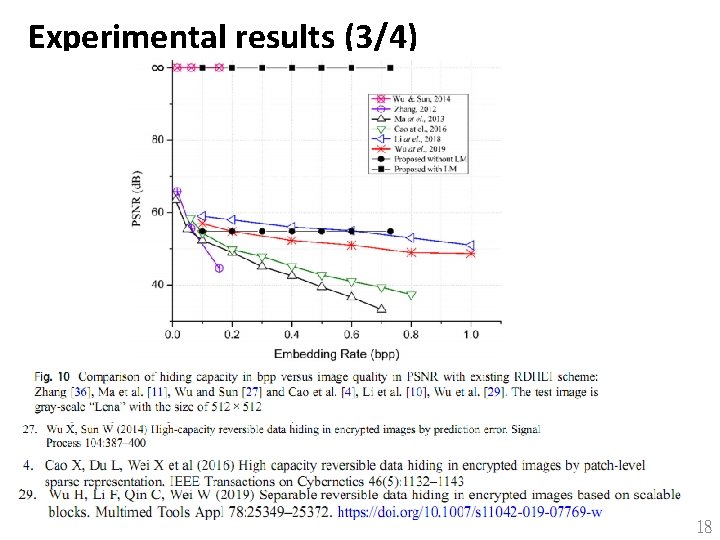
Experimental results (3/4) 18
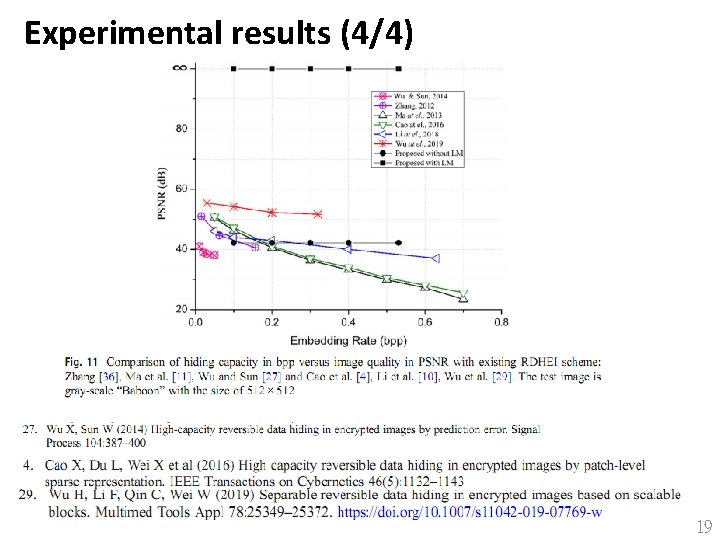
Experimental results (4/4) 19
Conclusions • This paper proposed a new RDH-EI method by reserving embedding room before image encryption. • To improve the embedding capacity 20
- Slides: 20