Reversible data hiding in encrypted images with separability
Reversible data hiding in encrypted images with separability and high embedding capacity Source: Signal Processing: Image Communication, 95, (2021), 116274 Authors: Dawen Xu, Shubing Su Speaker: Lin Jiang-Yi Date: 2021 -04 -29 1
Outline • Introduction • Proposed Scheme • Experimental Results • Comments 2
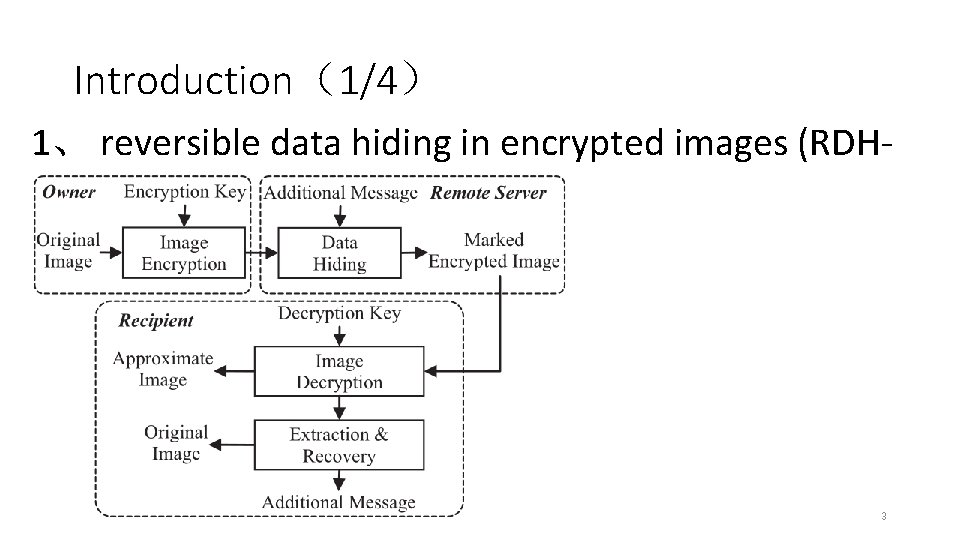
Introduction(1/4) 1、 reversible data hiding in encrypted images (RDHEI) 3
Introduction(2/4) 2、vacating room before encryption (VRBE) 1. 2. 3. K. Ma, W. Zhang, X. Zhao, N. Yu, and F. Li, Reversible data hiding in encrypted images by reserving room before encryption, IEEE Trans. Inf. Forensics Security, vol. 8, no. 3, pp. 553– 562, Mar. 2013. W. Zhang, K. Ma, and N. Yu, Reversibility improved data hiding in encrypted images, Signal Process. , vol. 94, no. 1, pp. 118– 127, Jan. 2014. Sh. Yi, Y. Zhou, Binary-block embedding for reversible data hiding in encrypted images, Signal Process. , vol. 133, pp. 40– 51, Apr. 2017. 4
Introduction(3/4) 3、vacating room after encryption (VRAE) 1. 2. 3. X. Zhang, Reversible data hiding in encrypted images, IEEE Signal Process. Lett. , vol. 18, no. 4, pp. 255– 258, Apr. 2011. W. Hong, T. Chen, and H. Wu, An improved reversible data hiding in encrypted images using side match, IEEE Signal Process. Lett. , vol. 19, no. 4, pp. 199– 202, Apr. 2012. X. Zhang, Separable reversible data hiding in encrypted image, IEEE Trans. Inf. Forensics Security, vol. 7, no. 2, pp. 826– 832, Apr. 2012. 5
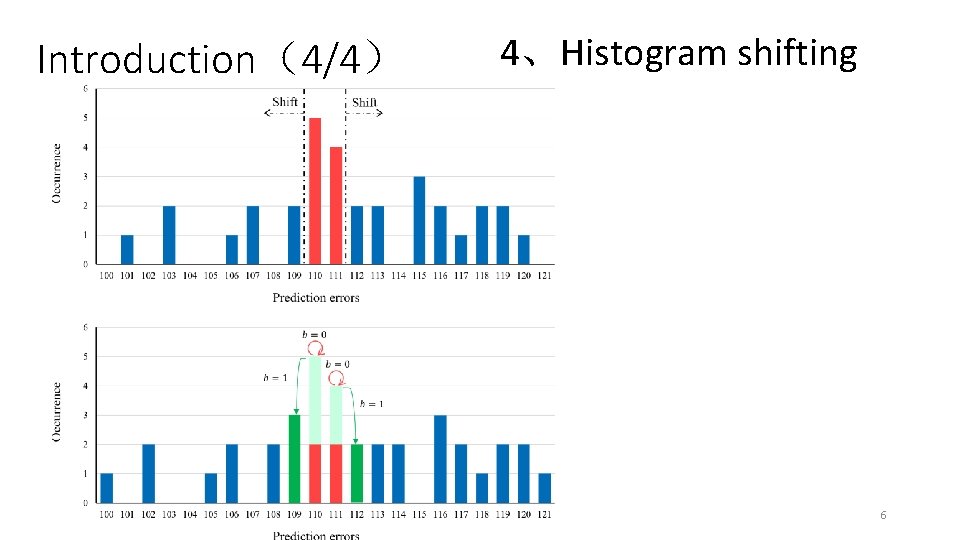
Introduction(4/4) 4、Histogram shifting 6
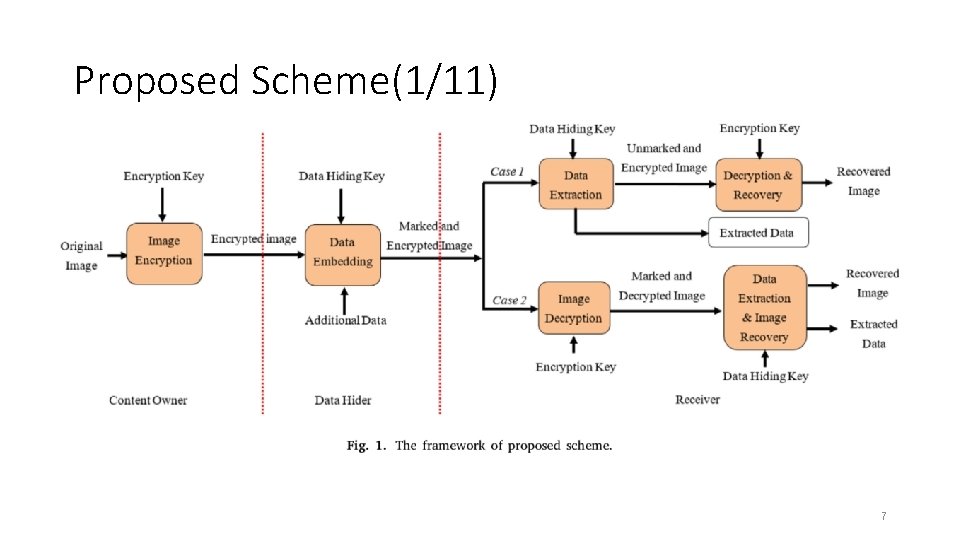
Proposed Scheme(1/11) 7
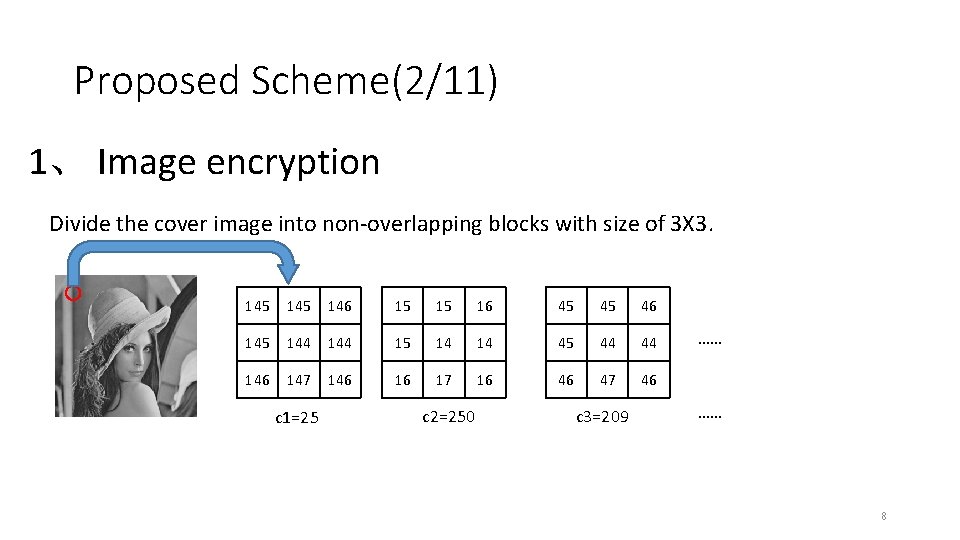
Proposed Scheme(2/11) 1、 Image encryption Divide the cover image into non-overlapping blocks with size of 3 X 3. 145 146 15 15 16 45 45 46 145 144 15 14 14 45 44 44 146 147 146 16 17 16 46 47 46 c 1=25 c 2=250 c 3=209 …… …… 8
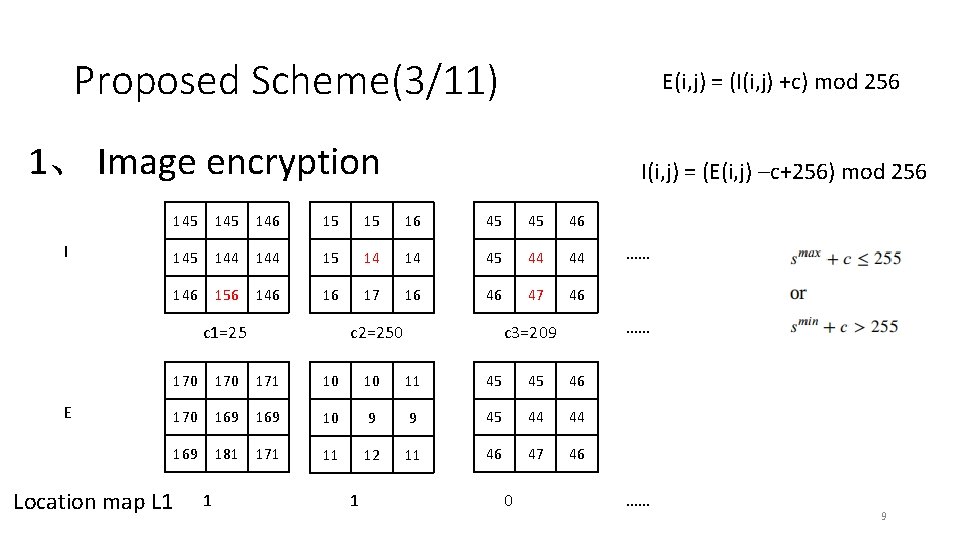
Proposed Scheme(3/11) E(i, j) = (I(i, j) +c) mod 256 1、 Image encryption I 145 146 15 15 16 45 45 46 145 144 15 14 14 45 44 44 146 156 146 16 17 16 46 47 46 c 2=250 c 1=25 E Location map L 1 I(i, j) = (E(i, j) –c+256) mod 256 …… c 3=209 170 171 10 10 11 45 45 46 170 169 10 9 9 45 44 44 169 181 171 11 12 11 46 47 46 1 1 0 …… …… 9
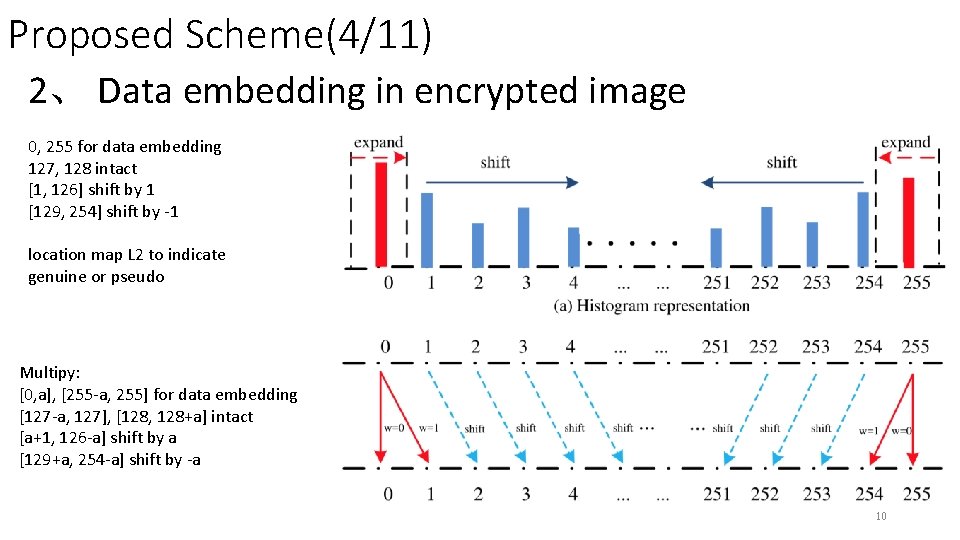
Proposed Scheme(4/11) 2、 Data embedding in encrypted image 0, 255 for data embedding 127, 128 intact [1, 126] shift by 1 [129, 254] shift by -1 location map L 2 to indicate genuine or pseudo Multipy: [0, a], [255 -a, 255] for data embedding [127 -a, 127], [128, 128+a] intact [a+1, 126 -a] shift by a [129+a, 254 -a] shift by -a 10
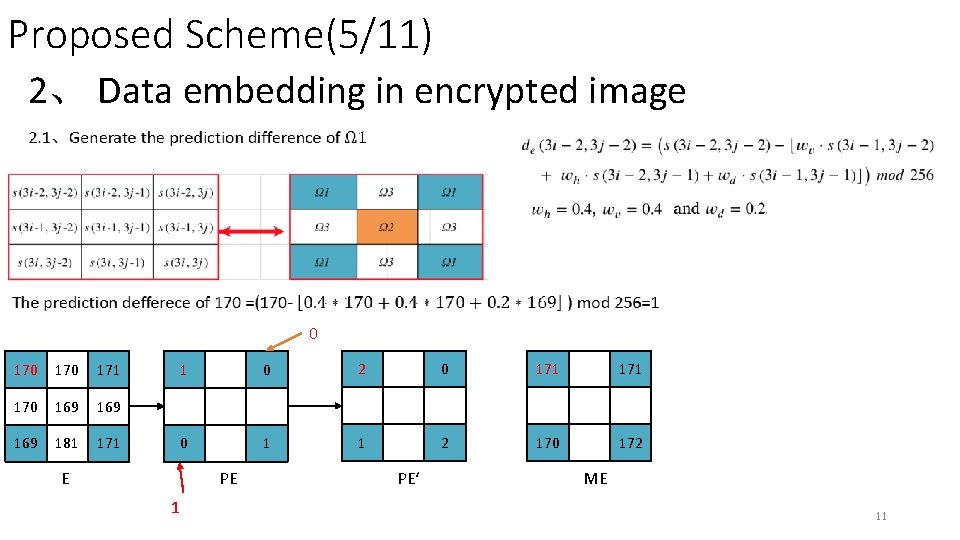
Proposed Scheme(5/11) 2、 Data embedding in encrypted image 0 170 171 170 169 169 181 171 E 1 0 2 0 171 0 1 1 2 170 172 PE 1 PE‘ ME 11
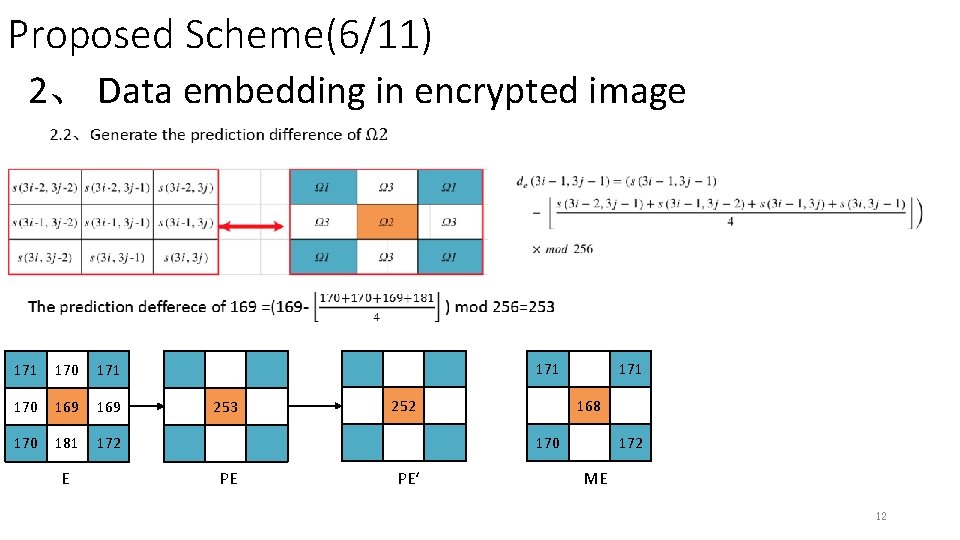
Proposed Scheme(6/11) 2、 Data embedding in encrypted image 171 170 169 170 181 172 E 171 253 252 171 168 170 PE PE‘ 172 ME 12
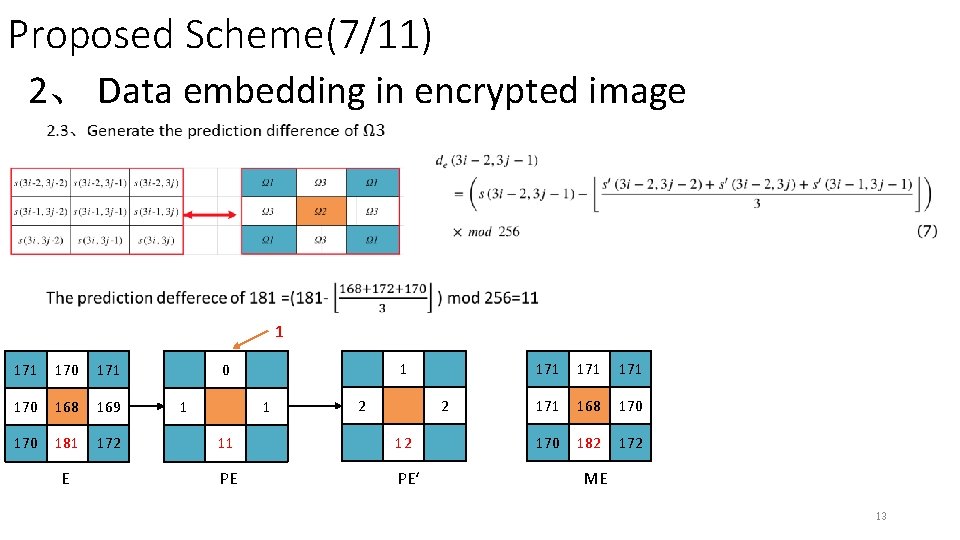
Proposed Scheme(7/11) 2、 Data embedding in encrypted image 1 170 171 170 168 169 170 181 172 E 1 0 1 1 2 2 11 12 PE PE‘ 171 171 168 170 182 172 ME 13
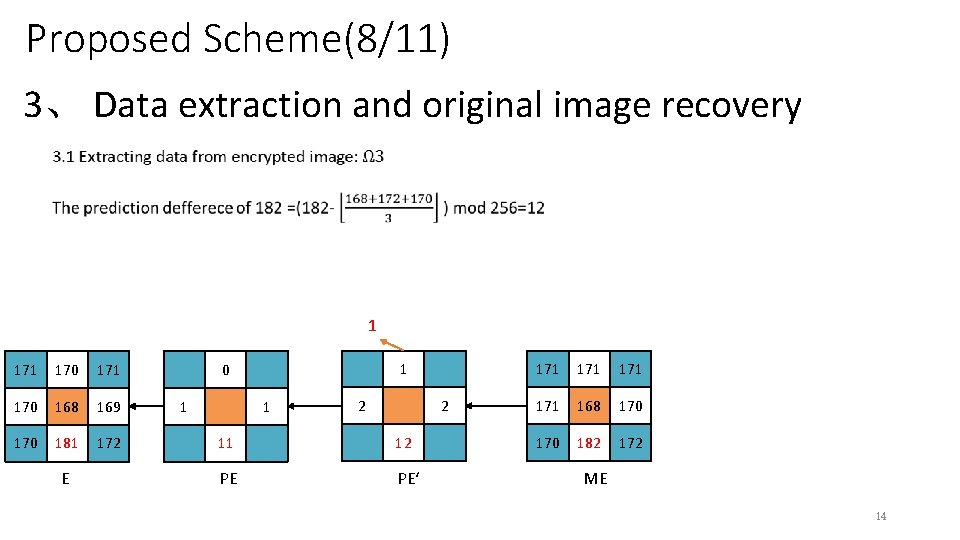
Proposed Scheme(8/11) 3、 Data extraction and original image recovery 1 170 171 170 168 169 170 181 172 E 1 0 1 1 2 2 11 12 PE PE‘ 171 171 168 170 182 172 ME 14
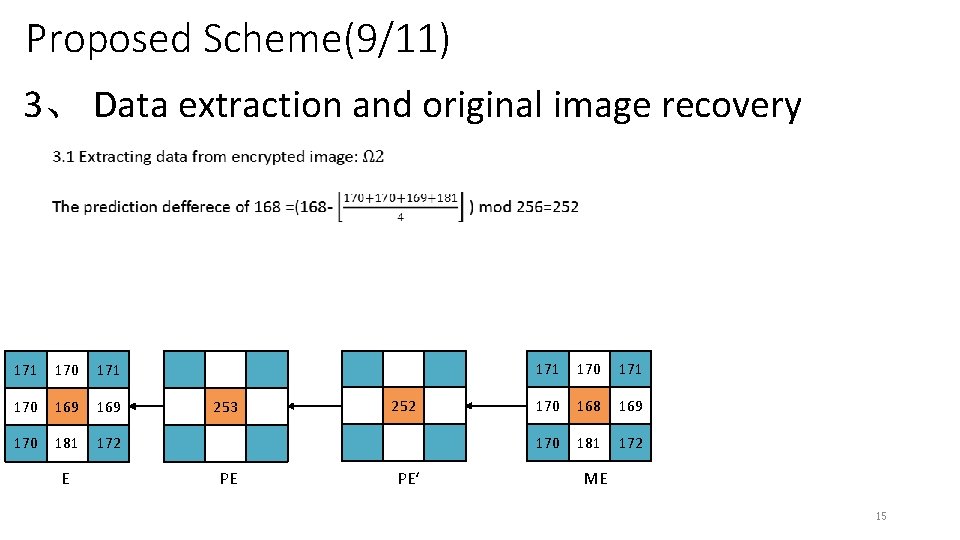
Proposed Scheme(9/11) 3、 Data extraction and original image recovery 171 170 169 170 181 172 E 253 PE 252 PE‘ 171 170 168 169 170 181 172 ME 15
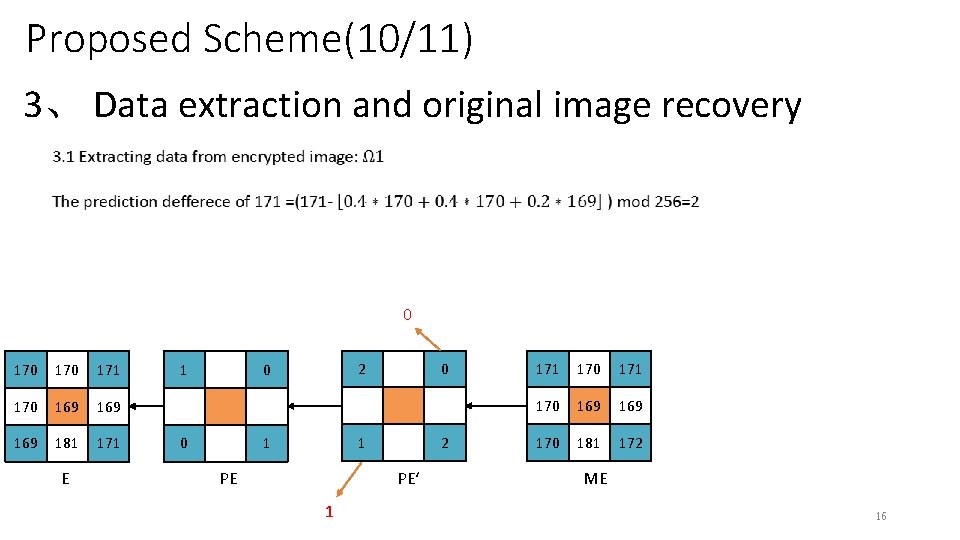
Proposed Scheme(10/11) 3、 Data extraction and original image recovery 0 170 171 170 169 169 181 171 E 1 2 0 0 0 1 1 2 PE‘ PE 1 170 171 170 169 170 181 172 ME 16
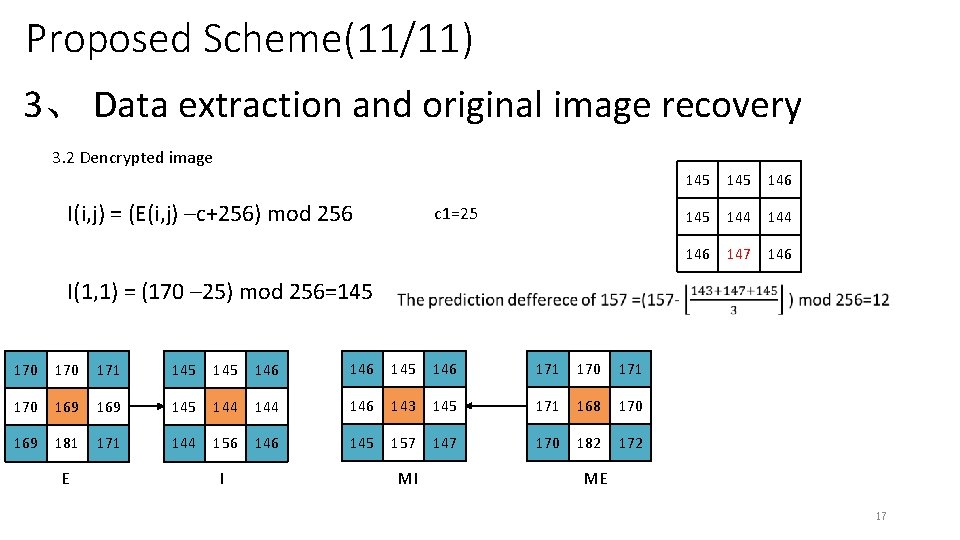
Proposed Scheme(11/11) 3、 Data extraction and original image recovery 3. 2 Dencrypted image I(i, j) = (E(i, j) –c+256) mod 256 c 1=25 145 146 145 144 146 147 146 I(1, 1) = (170 – 25) mod 256=145 170 171 145 146 171 170 169 145 144 146 143 145 171 168 170 169 181 171 144 156 145 157 147 170 182 172 E I MI ME 17
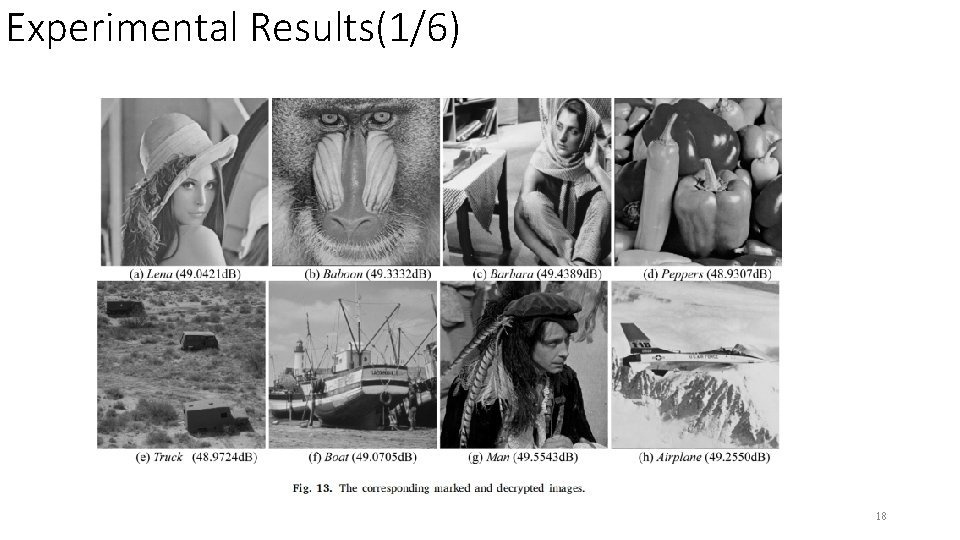
Experimental Results(1/6) 18
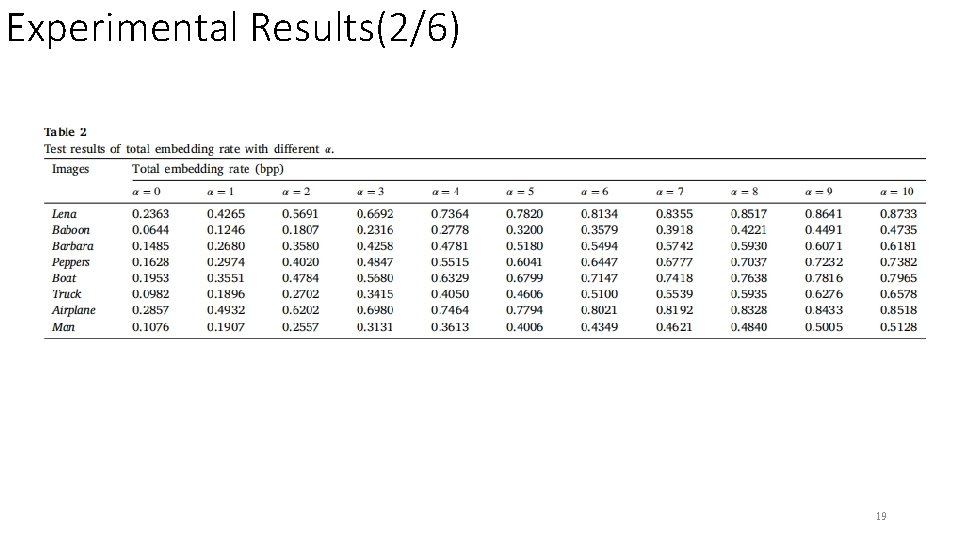
Experimental Results(2/6) 19
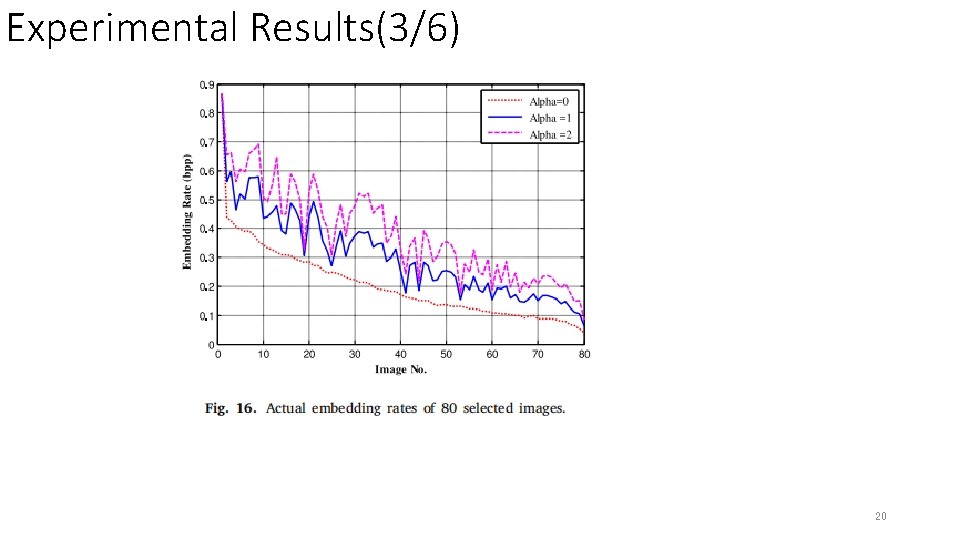
Experimental Results(3/6) 20
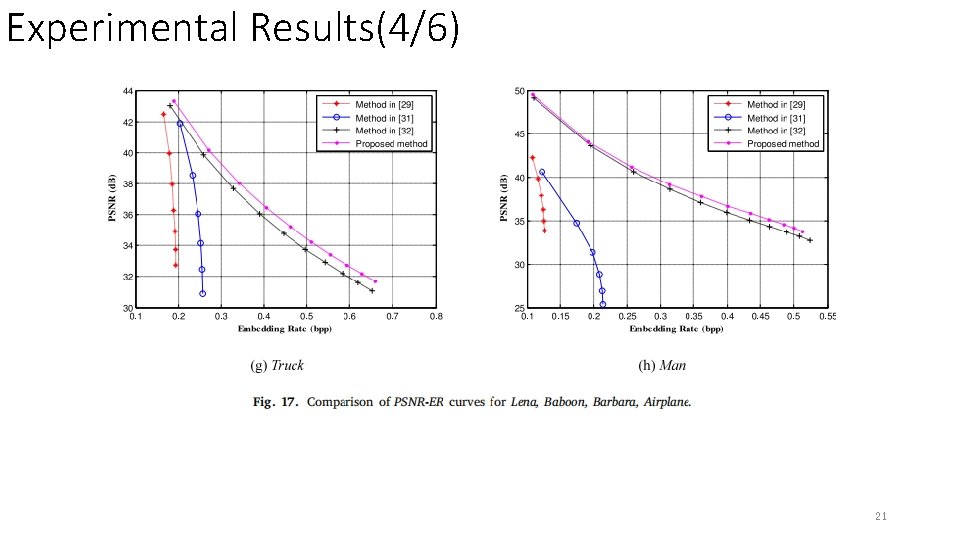
Experimental Results(4/6) 21
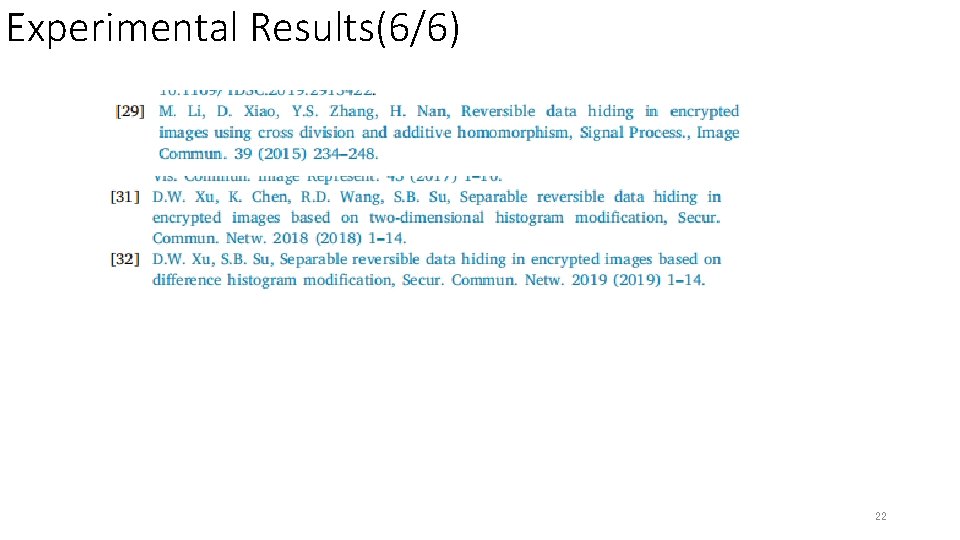
Experimental Results(6/6) 22
Comments • 1、contributions • Block by block encryption. • Hybrid prediction method. • marked image. • 2、Critique • Lack of innovation. 23
- Slides: 23