Reversible Data Hiding in Encrypted Images Using Median
Reversible Data Hiding in Encrypted Images Using Median Edge Detector and Two’s Complement Source: Symmetry, 21 May 2021. https: //doi. org/10. 3390/sym 13060921 Author: Rui Wang, Guohua Wu, Qiuhua Wang, Lifeng Yuan 1, 2, *, Zhen Zhang 1, * and Gongxun Miao 3 Speaker: Lin Li Date: 2021/07/21 1
Outline • Introduction • Related works • Proposed scheme • Experimental results • Conclusions 2
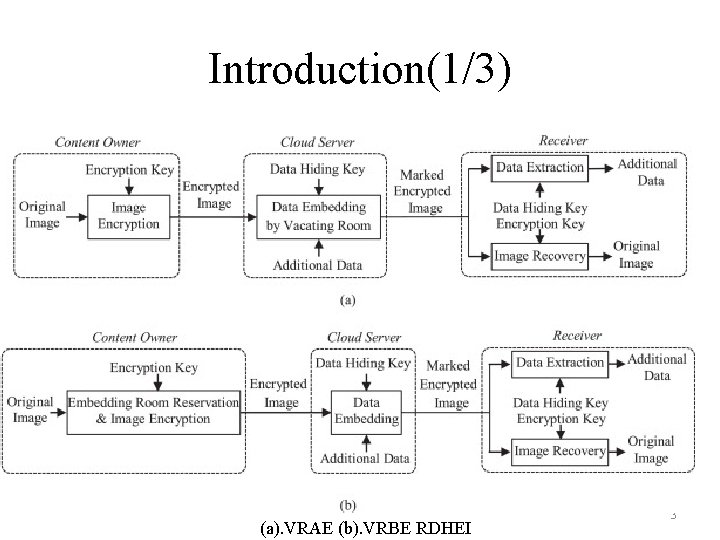
Introduction(1/3) (a). VRAE (b). VRBE RDHEI 3
![Introduction(2/3) (1) the methods by vacating room after encryption (VRAE) [24– 26] (2) the Introduction(2/3) (1) the methods by vacating room after encryption (VRAE) [24– 26] (2) the](http://slidetodoc.com/presentation_image_h2/91d31f6b8952c4aac2219bb007ab0365/image-4.jpg)
Introduction(2/3) (1) the methods by vacating room after encryption (VRAE) [24– 26] (2) the methods by reserving room before encryption (RRBE) [27– 29] 4
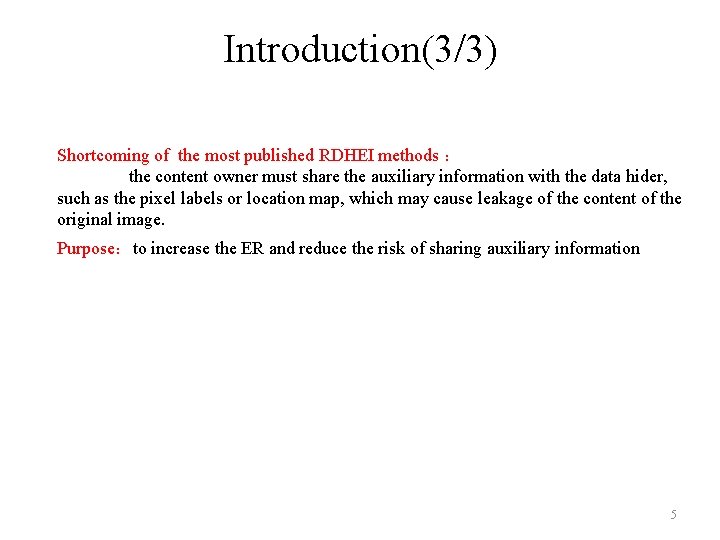
Introduction(3/3) Shortcoming of the most published RDHEI methods : the content owner must share the auxiliary information with the data hider, such as the pixel labels or location map, which may cause leakage of the content of the original image. Purpose:to increase the ER and reduce the risk of sharing auxiliary information 5
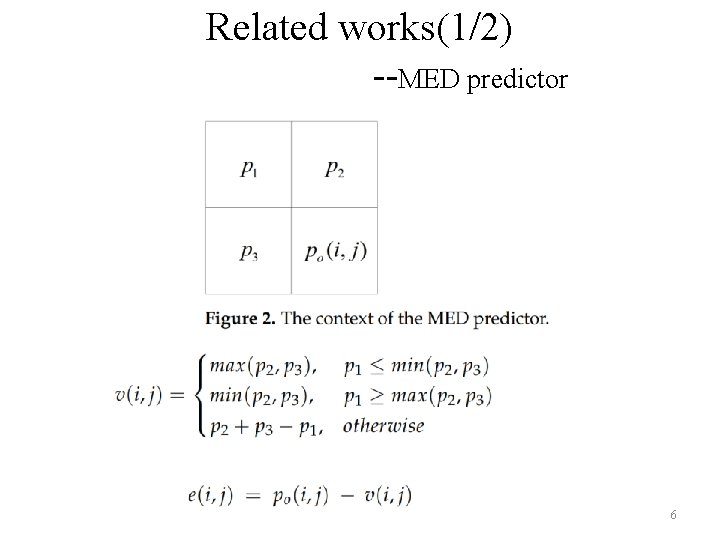
Related works(1/2) --MED predictor 6
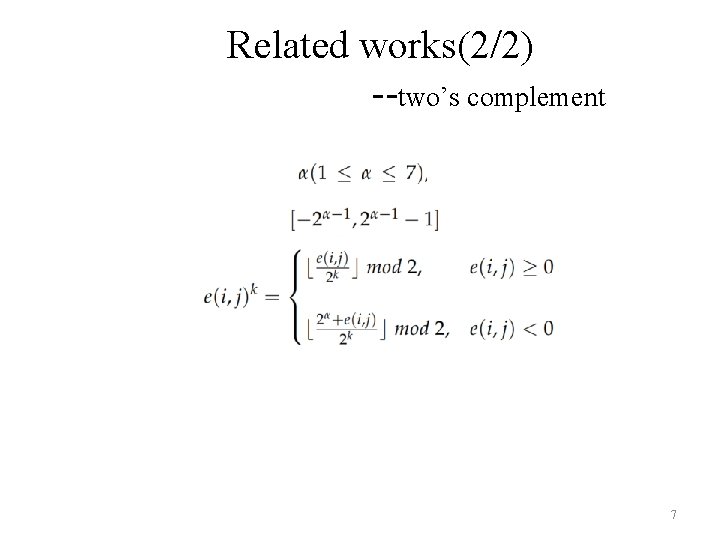
Related works(2/2) --two’s complement 7
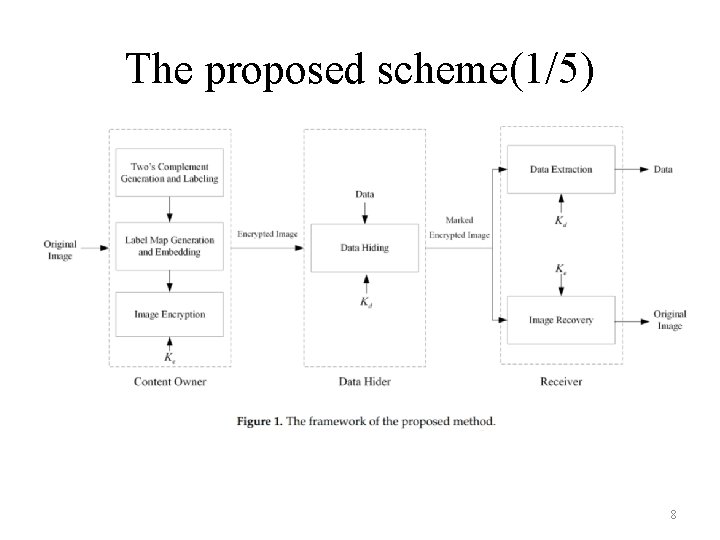
The proposed scheme(1/5) 8
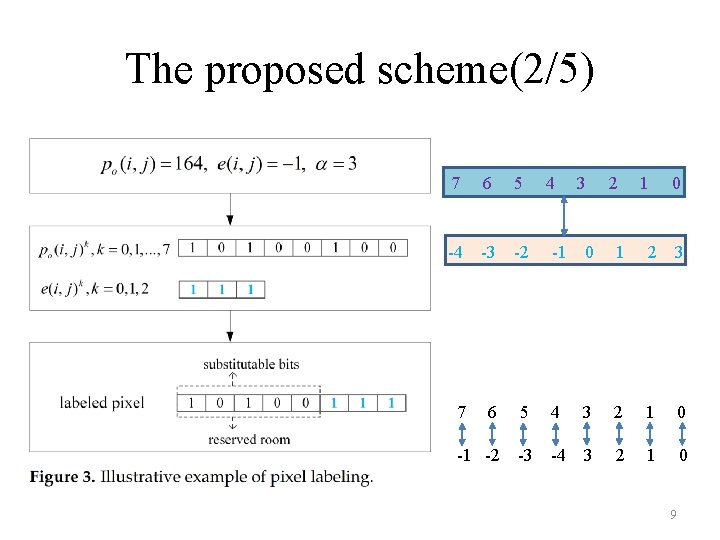
The proposed scheme(2/5) 7 6 -4 -3 5 4 3 2 1 0 -2 -1 0 1 2 3 6 5 4 3 2 1 0 -1 -2 -3 -4 3 2 1 0 7 9
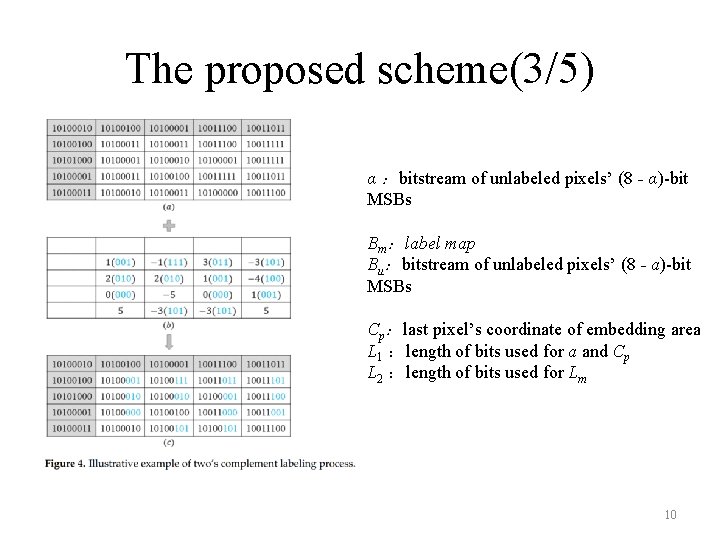
The proposed scheme(3/5) α :bitstream of unlabeled pixels’ (8 - α)-bit MSBs Bm:label map Bu:bitstream of unlabeled pixels’ (8 - a)-bit MSBs Cp:last pixel’s coordinate of embedding area L 1 :length of bits used for a and Cp L 2 :length of bits used for Lm 10
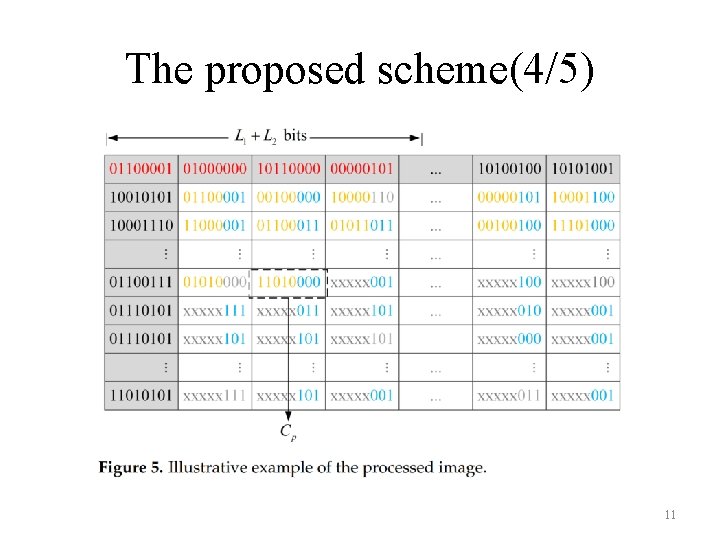
The proposed scheme(4/5) 11
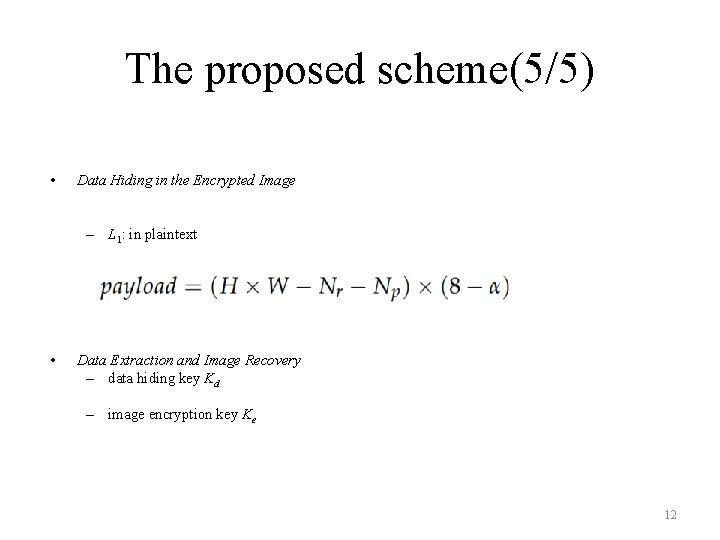
The proposed scheme(5/5) • Data Hiding in the Encrypted Image – L 1: in plaintext • Data Extraction and Image Recovery – data hiding key Kd – image encryption key Ke 12
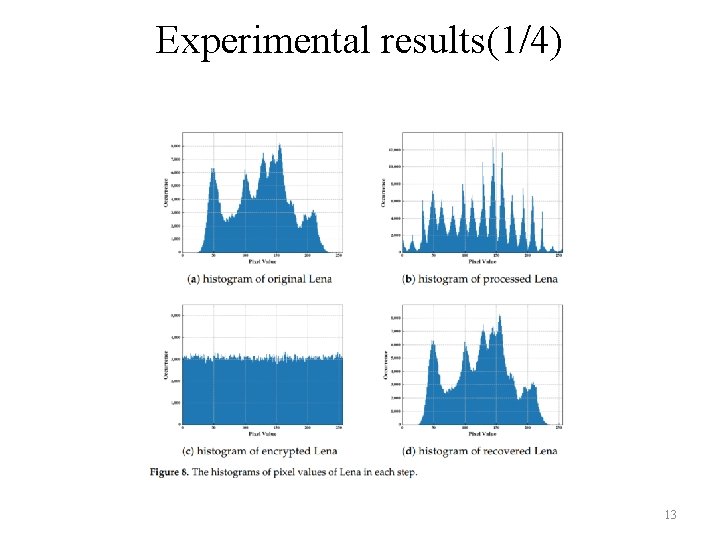
Experimental results(1/4) 13
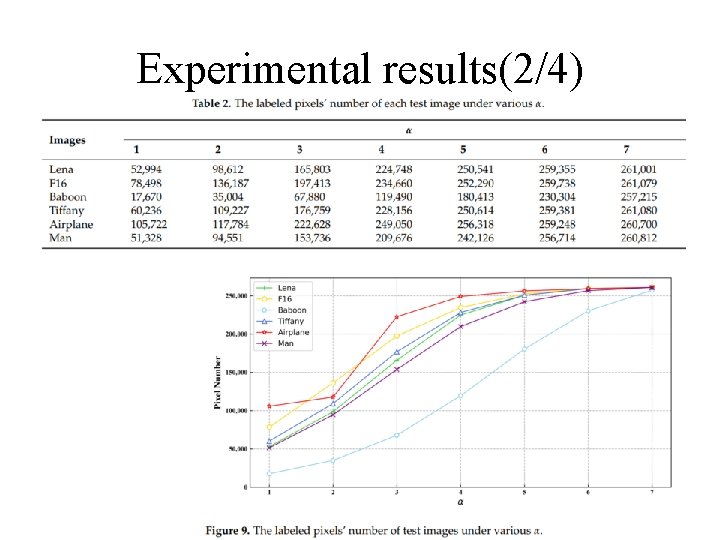
Experimental results(2/4) 14
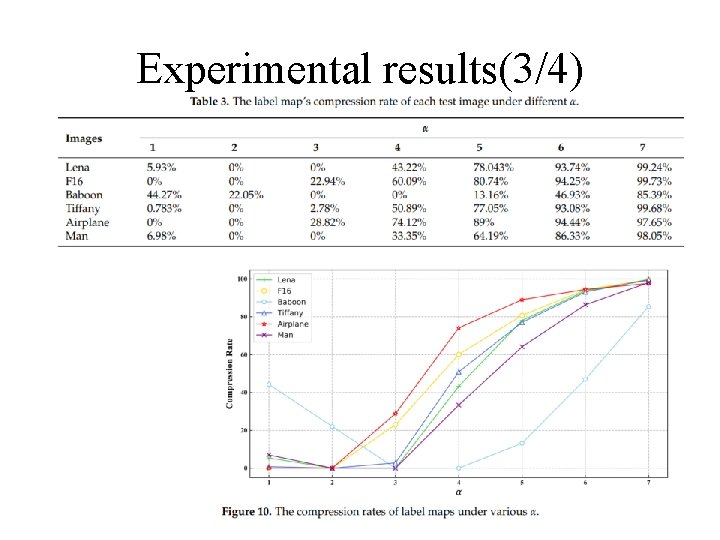
Experimental results(3/4) 15
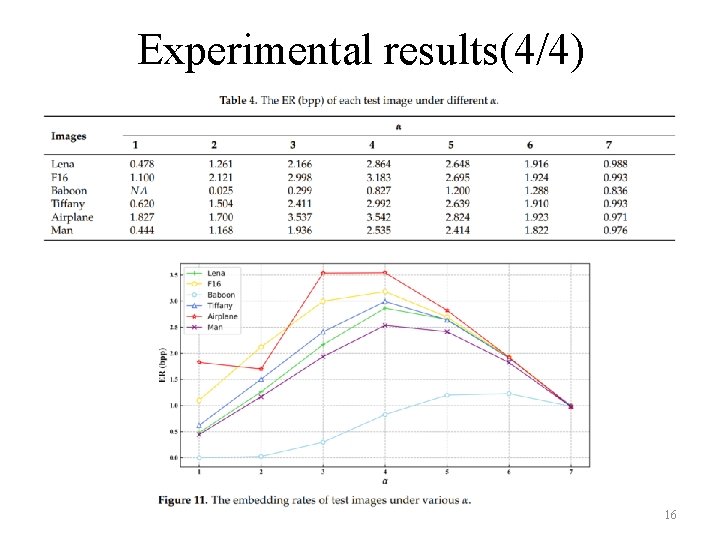
Experimental results(4/4) 16
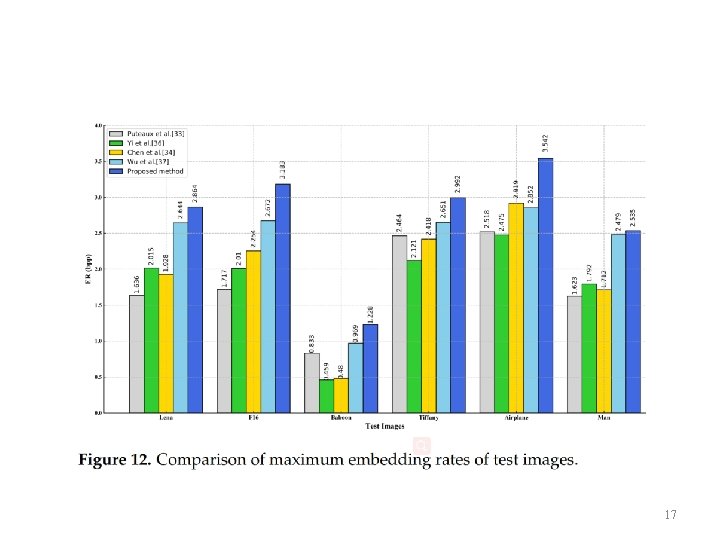
17
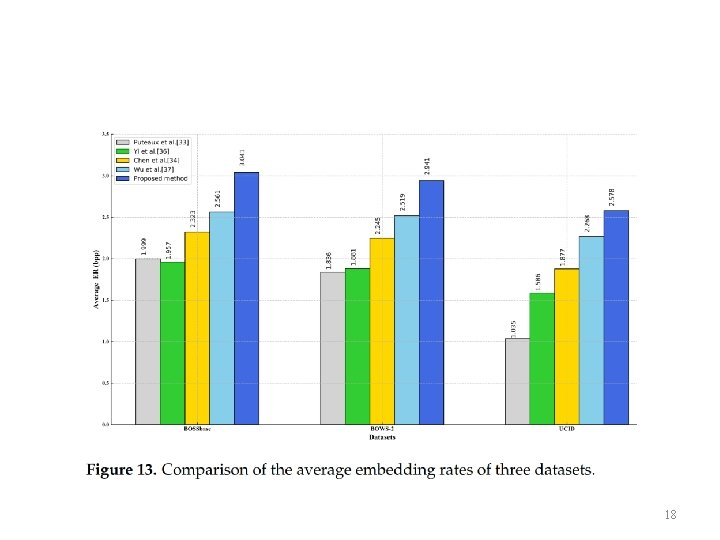
18
References 19
Conclusions l propose a new RDHEI method based on MED and two’s complement l can achieve a higher ER than previous methods Thanks for your listening! 20
- Slides: 20