Duke Systems Servers and secure communication Jeff Chase



- Slides: 63
Duke Systems Servers and secure communication Jeff Chase Duke University
Shell lab • We need to understand a little about: – job states: foreground and background – process states – blocking or sleep states: waiting for an external event • Shell exposes a fundamental problem: – Many programs monitor/control asynchronous activities. – E. g. , shell manages children, apps wait for clicks, servers wait for requests, everyone waits for I/O to complete. – How should a program wait for the next event, if there are many possible events to wait for? – Wait for a specific event may miss others. • Good event handling mechanisms are important.
Unix was wrong • Unix was designed around blocking system calls. – read from tty – wait* for child process – listen for arriving server connection – Blocked process makes no progress until event occurs. – signals an afterthought to “kill” a process • Unix got it wrong. – Evolving signal mechanisms for better shells. – Evolving designs for high-performance servers. • Newer systems (and Ux variants) have better event handling mechanisms. – Kqueue, epoll, Android component interfaces
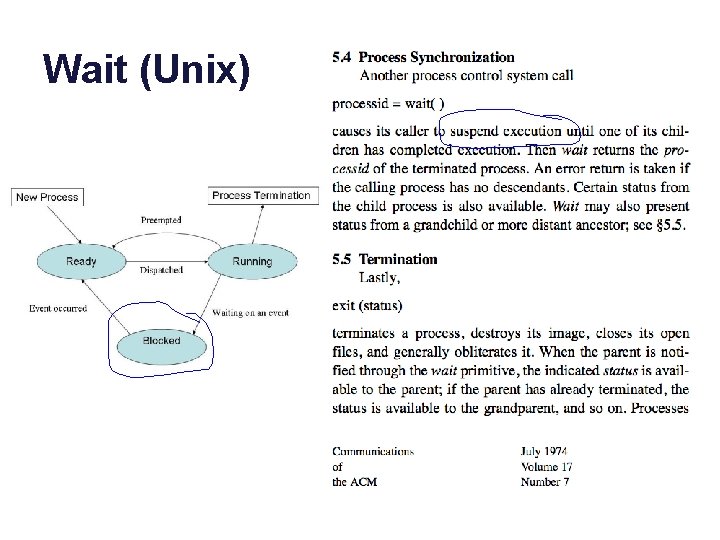
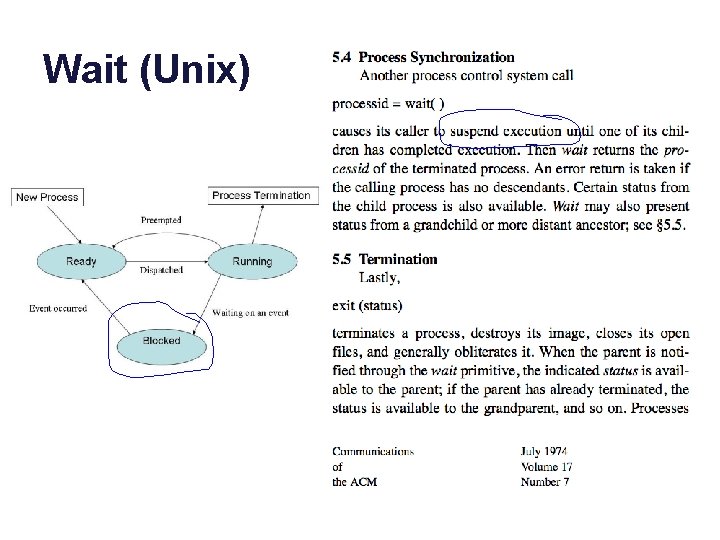
Wait (Unix)
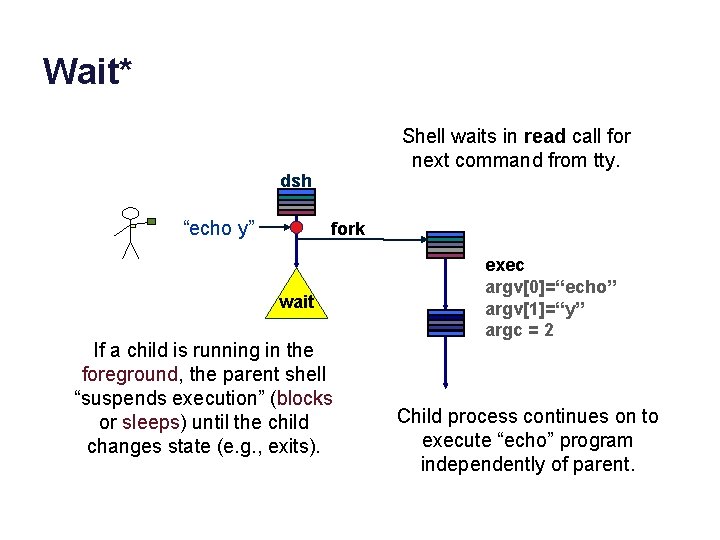
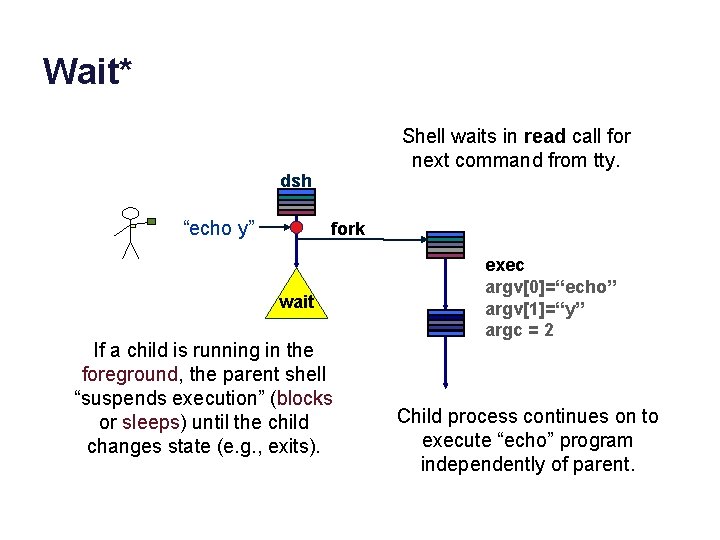
Wait* Shell waits in read call for next command from tty. dsh “echo y” fork wait If a child is running in the foreground, the parent shell “suspends execution” (blocks or sleeps) until the child changes state (e. g. , exits). exec argv[0]=“echo” argv[1]=“y” argc = 2 Child process continues on to execute “echo” program independently of parent.
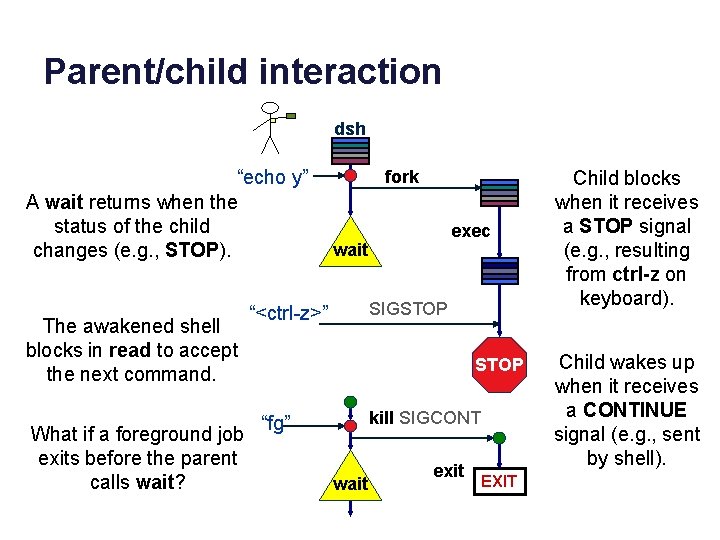
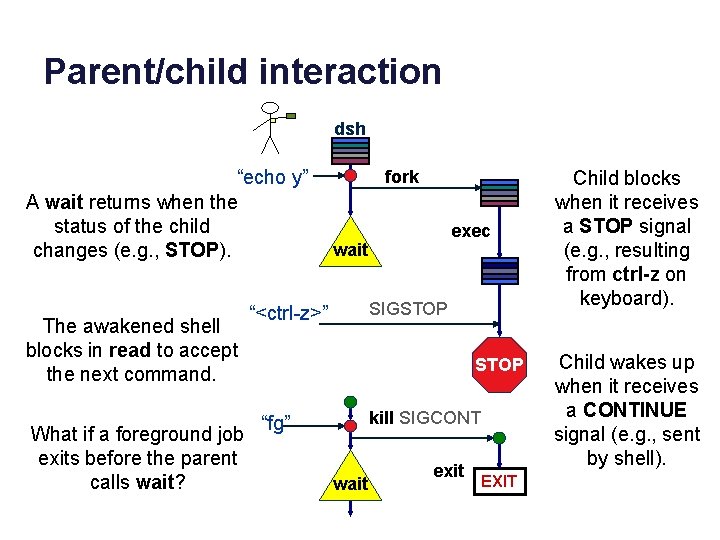
Parent/child interaction dsh “echo y” A wait returns when the status of the child changes (e. g. , STOP). The awakened shell blocks in read to accept the next command. What if a foreground job exits before the parent calls wait? fork exec wait SIGSTOP “<ctrl-z>” STOP kill SIGCONT “fg” wait exit EXIT Child blocks when it receives a STOP signal (e. g. , resulting from ctrl-z on keyboard). Child wakes up when it receives a CONTINUE signal (e. g. , sent by shell).
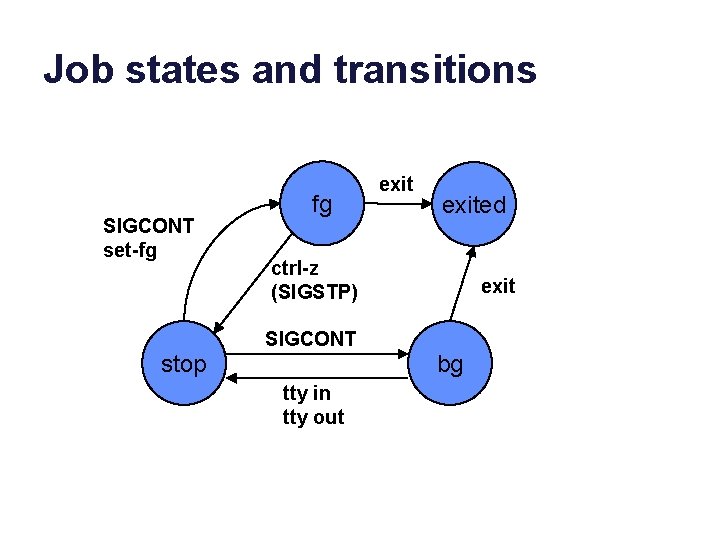
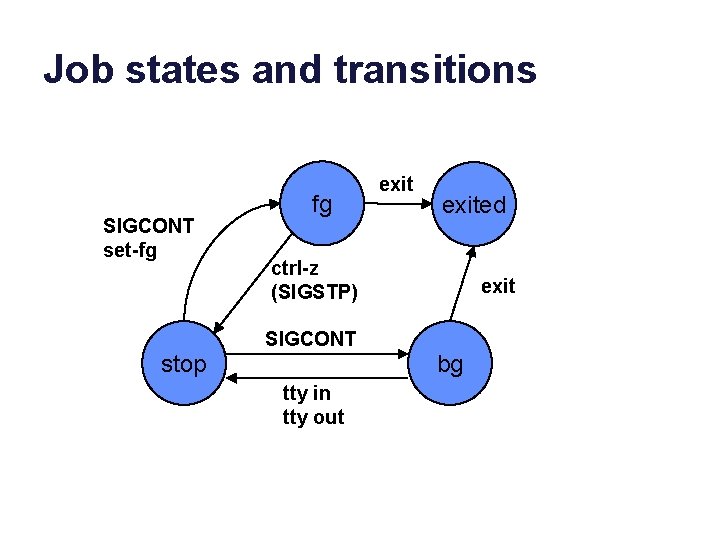
Job states and transitions SIGCONT set-fg fg exited ctrl-z (SIGSTP) exit SIGCONT stop bg tty in tty out
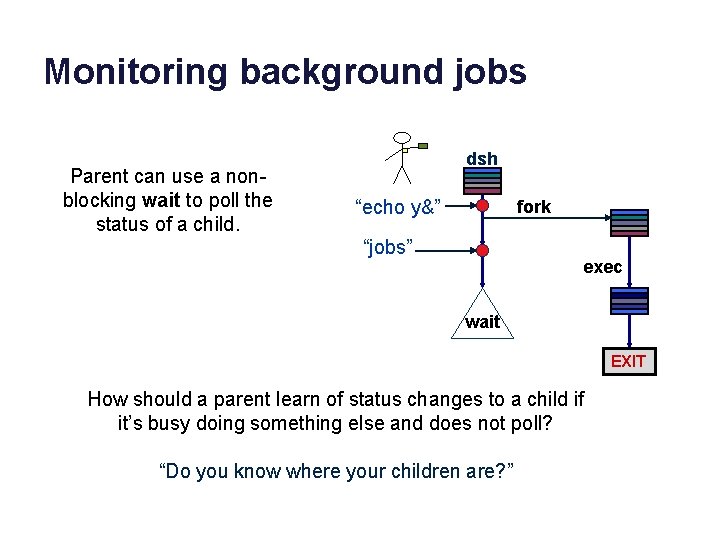
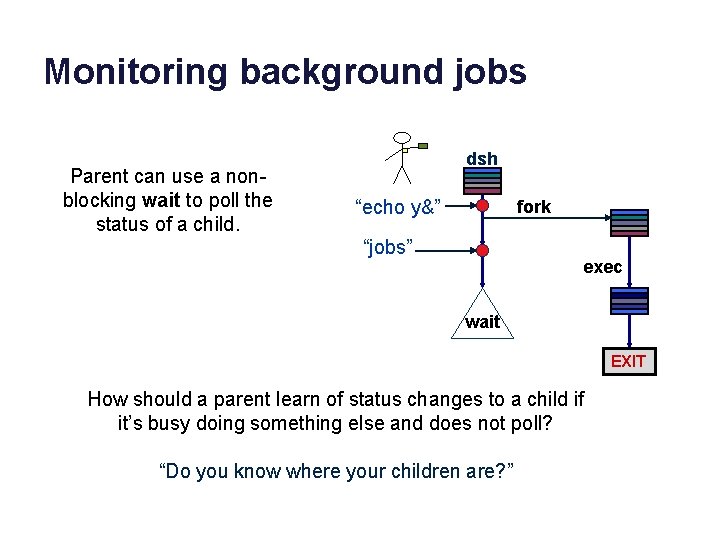
Monitoring background jobs Parent can use a nonblocking wait to poll the status of a child. dsh “echo y&” fork “jobs” exec wait EXIT How should a parent learn of status changes to a child if it’s busy doing something else and does not poll? “Do you know where your children are? ”
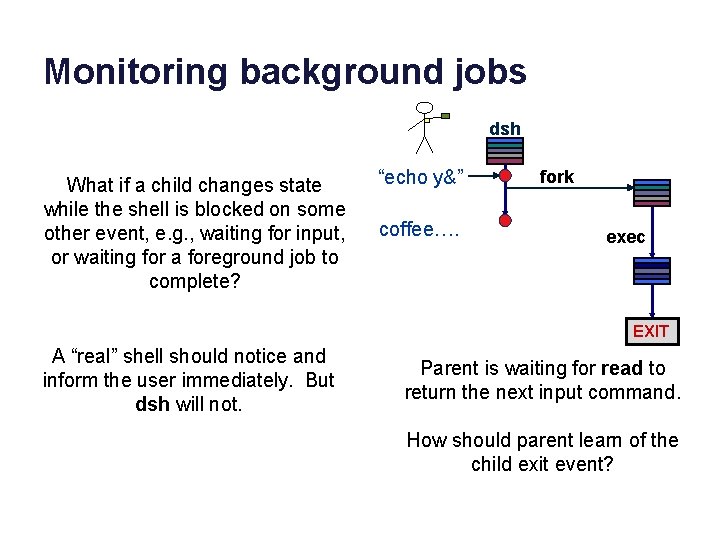
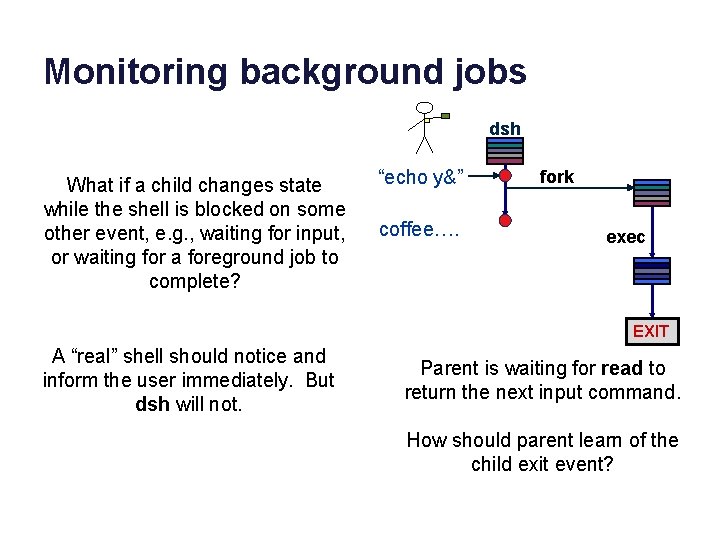
Monitoring background jobs dsh What if a child changes state while the shell is blocked on some other event, e. g. , waiting for input, or waiting for a foreground job to complete? “echo y&” coffee…. fork exec EXIT A “real” shell should notice and inform the user immediately. But dsh will not. Parent is waiting for read to return the next input command. How should parent learn of the child exit event?
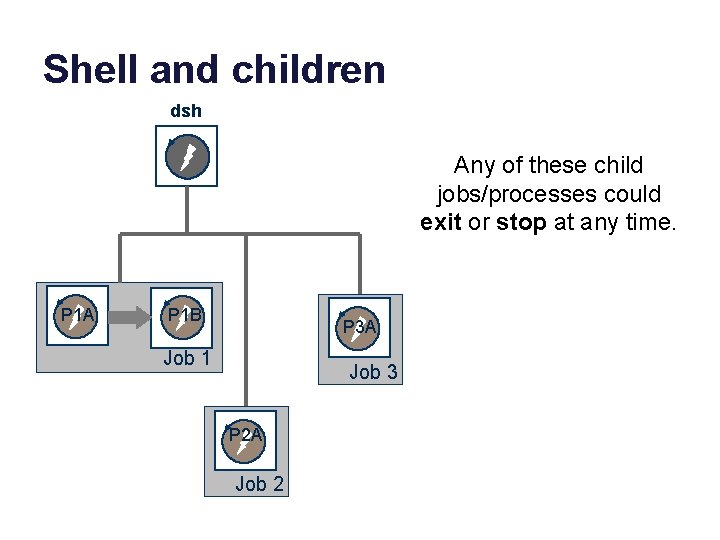
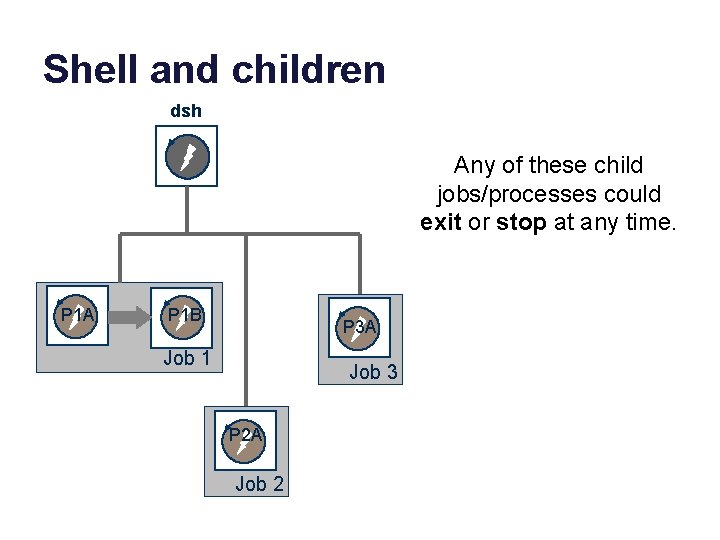
Shell and children dsh Any of these child jobs/processes could exit or stop at any time. P 1 A P 1 B P 3 A Job 1 Job 3 P 2 A Job 2
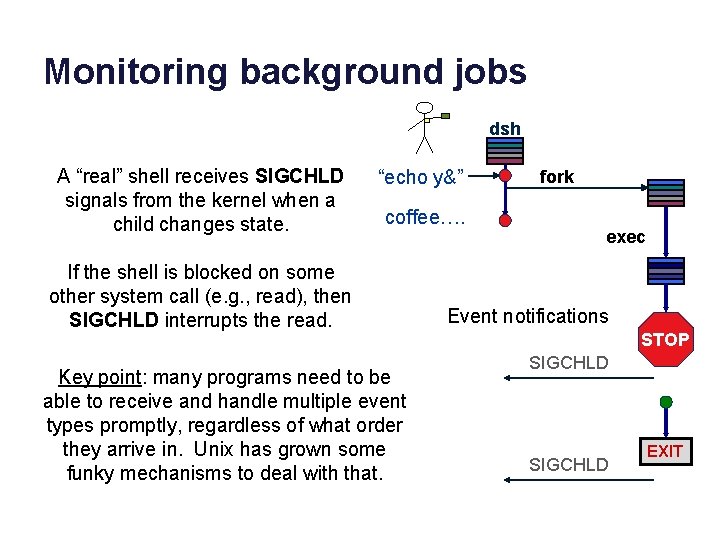
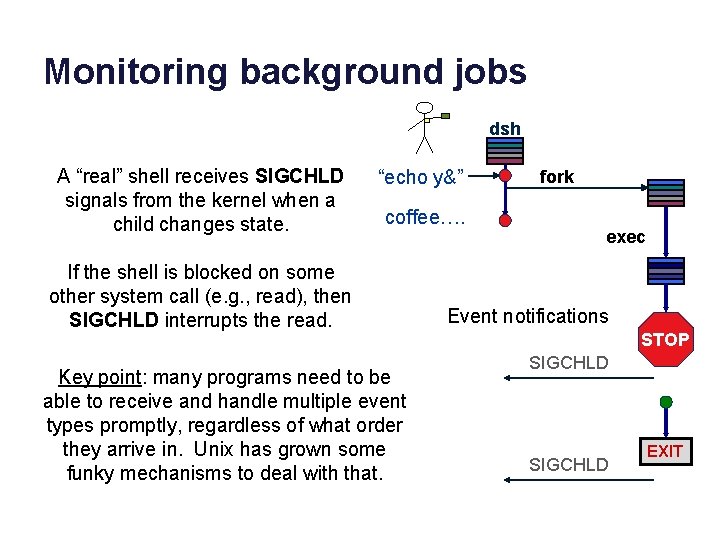
Monitoring background jobs dsh A “real” shell receives SIGCHLD signals from the kernel when a child changes state. “echo y&” coffee…. If the shell is blocked on some other system call (e. g. , read), then SIGCHLD interrupts the read. Key point: many programs need to be able to receive and handle multiple event types promptly, regardless of what order they arrive in. Unix has grown some funky mechanisms to deal with that. fork exec Event notifications STOP SIGCHLD EXIT
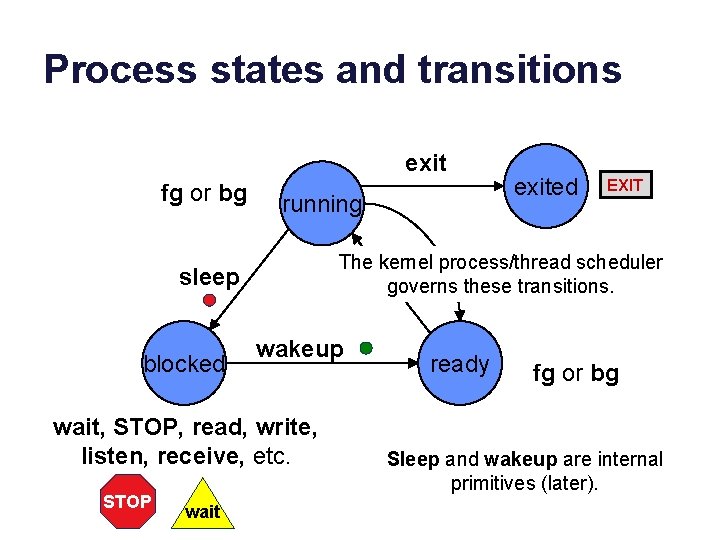
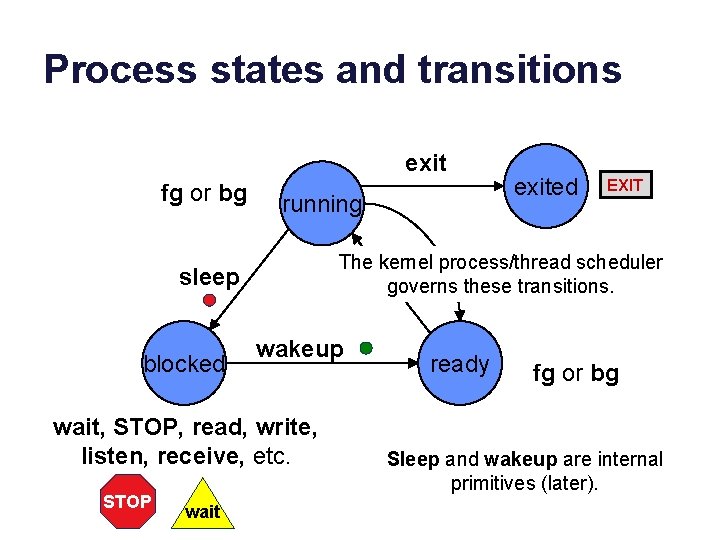
Process states and transitions exit fg or bg running wakeup wait, STOP, read, write, listen, receive, etc. STOP wait EXIT The kernel process/thread scheduler governs these transitions. sleep blocked exited ready fg or bg Sleep and wakeup are internal primitives (later).
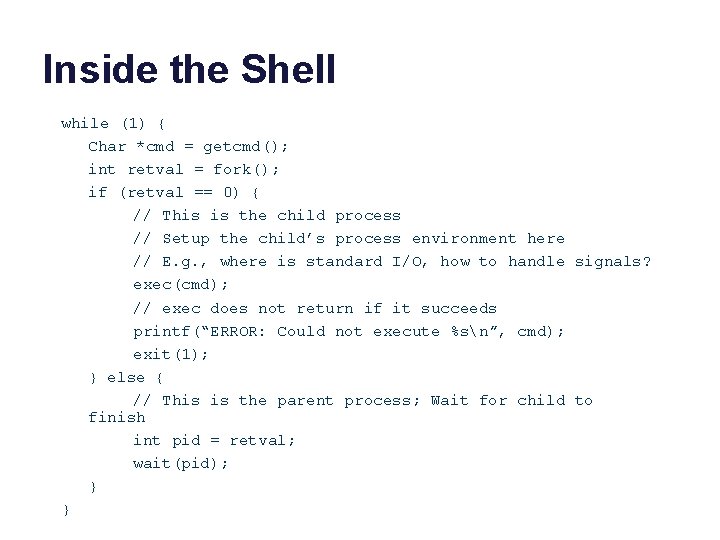
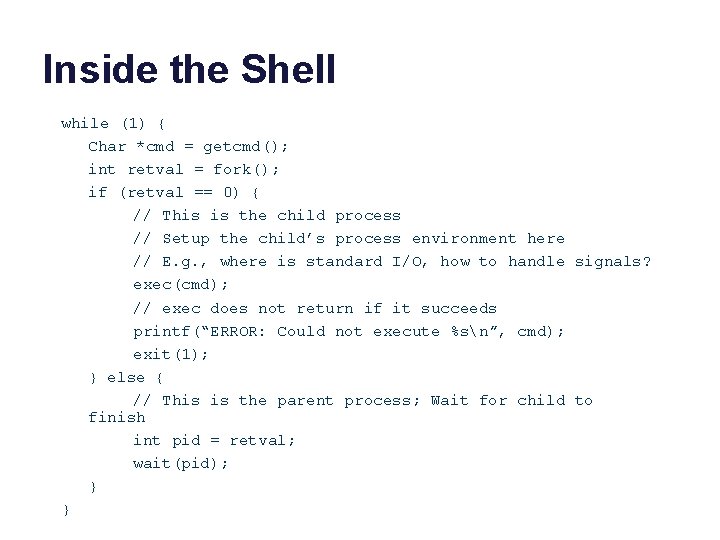
Inside the Shell while (1) { Char *cmd = getcmd(); int retval = fork(); if (retval == 0) { // This is the child process // Setup the child’s process environment here // E. g. , where is standard I/O, how to handle signals? exec(cmd); // exec does not return if it succeeds printf(“ERROR: Could not execute %sn”, cmd); exit(1); } else { // This is the parent process; Wait for child to finish int pid = retval; wait(pid); } }
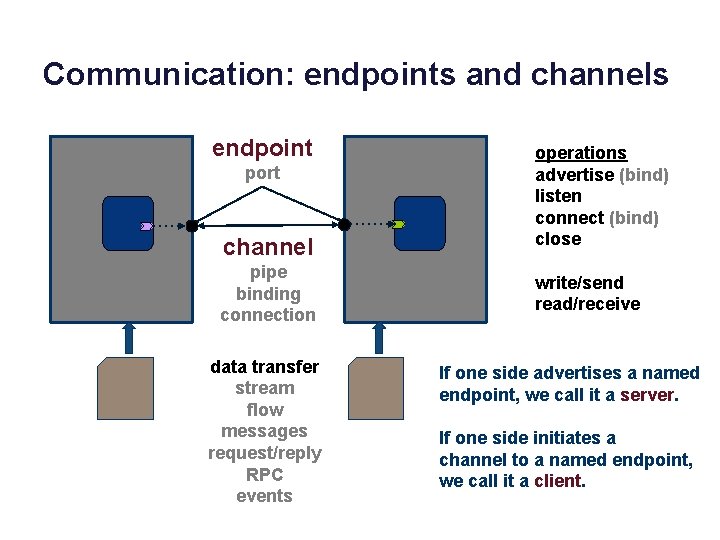
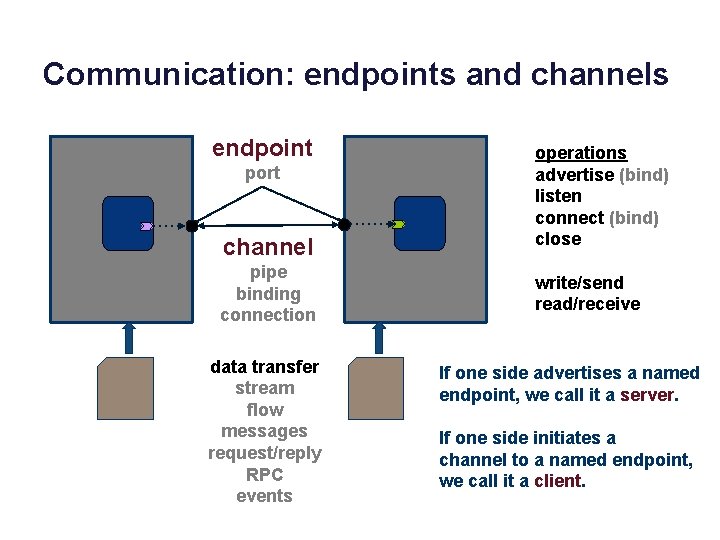
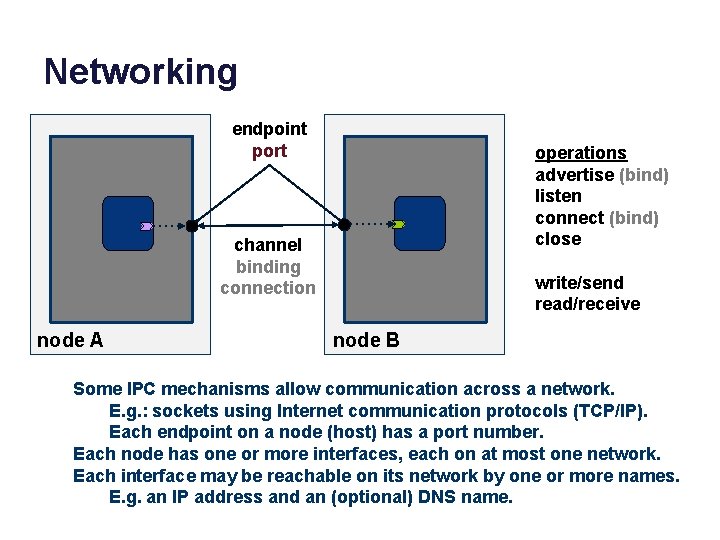
Communication: endpoints and channels endpoint port channel pipe binding connection data transfer stream flow messages request/reply RPC events operations advertise (bind) listen connect (bind) close write/send read/receive If one side advertises a named endpoint, we call it a server. If one side initiates a channel to a named endpoint, we call it a client.
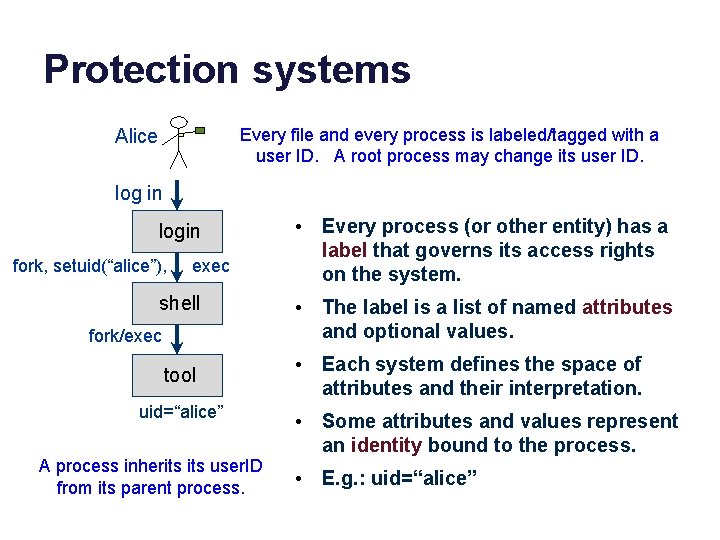
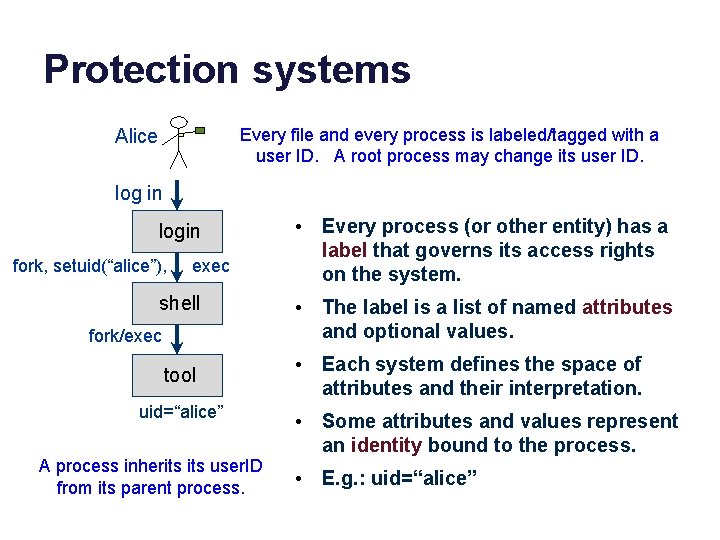
Protection systems Every file and every process is labeled/tagged with a user ID. A root process may change its user ID. Alice log in login fork, setuid(“alice”), exec shell fork/exec tool uid=“alice” A process inherits user. ID from its parent process. • Every process (or other entity) has a label that governs its access rights on the system. • The label is a list of named attributes and optional values. • Each system defines the space of attributes and their interpretation. • Some attributes and values represent an identity bound to the process. • E. g. : uid=“alice”
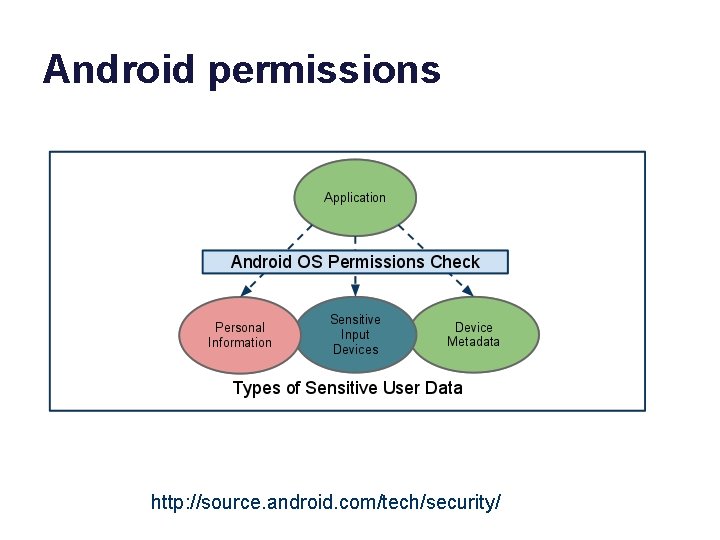
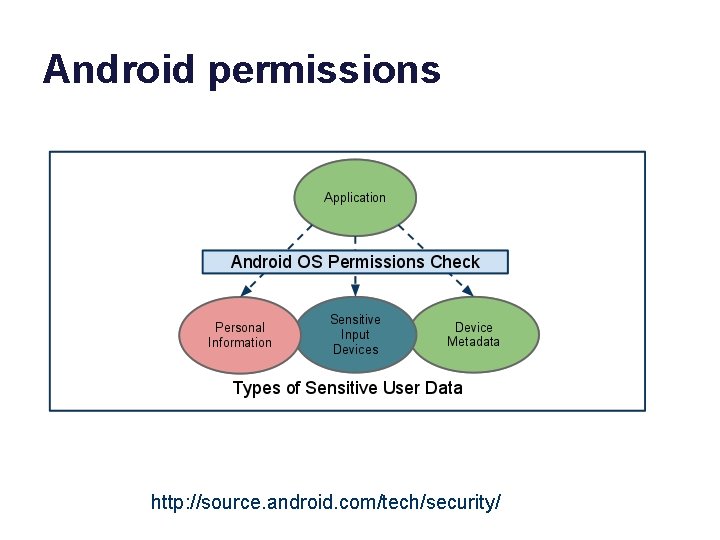
Android permissions http: //source. android. com/tech/security/
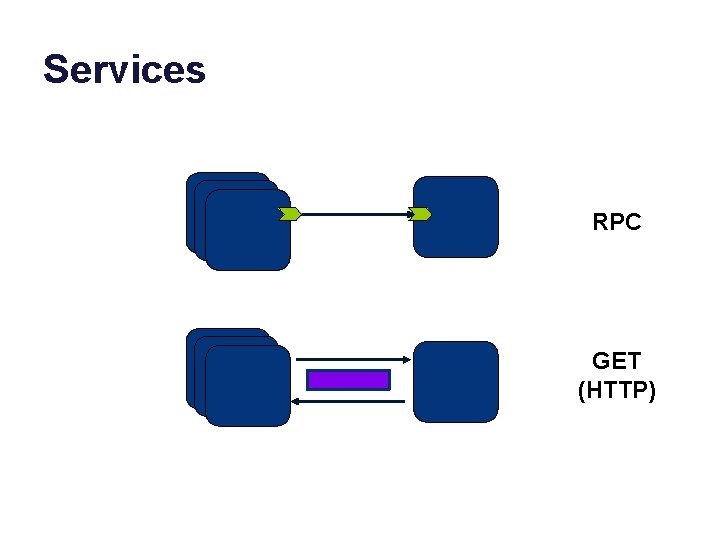
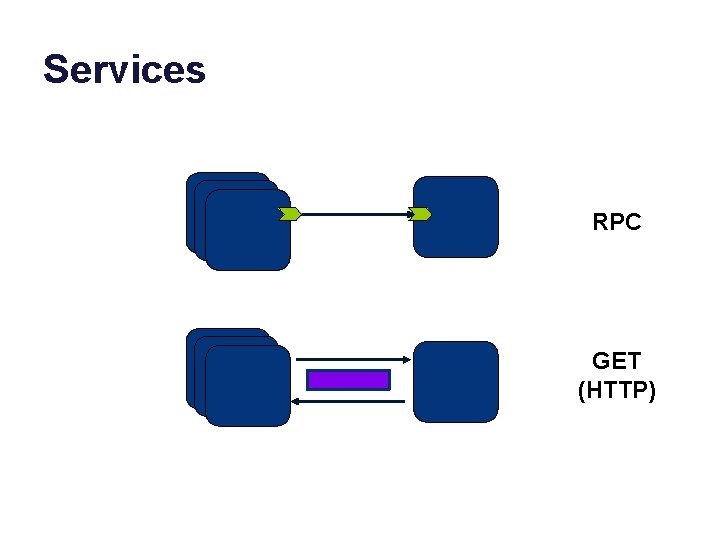
Services RPC GET (HTTP)
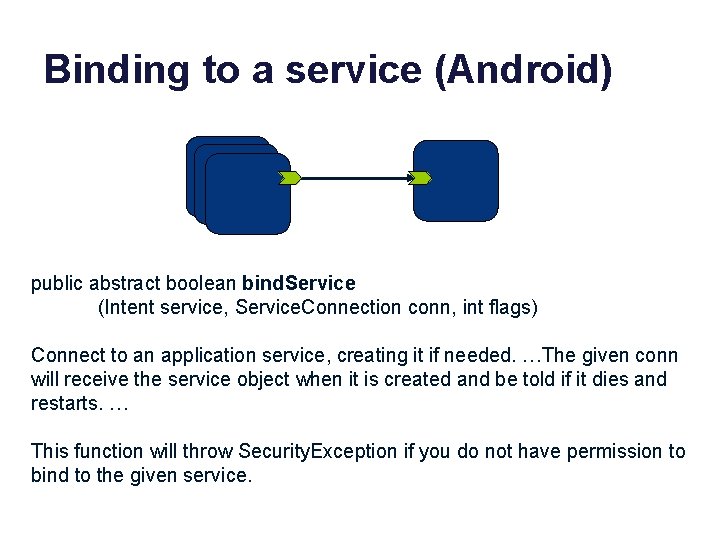
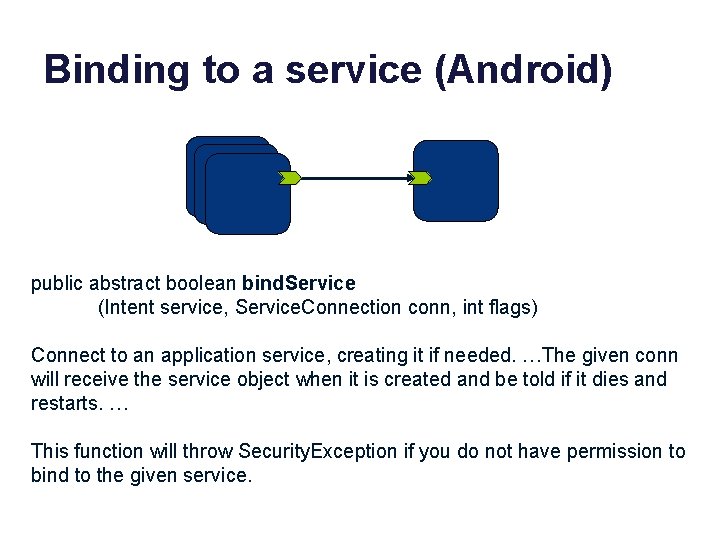
Binding to a service (Android) public abstract boolean bind. Service (Intent service, Service. Connection conn, int flags) Connect to an application service, creating it if needed. …The given conn will receive the service object when it is created and be told if it dies and restarts. … This function will throw Security. Exception if you do not have permission to bind to the given service.
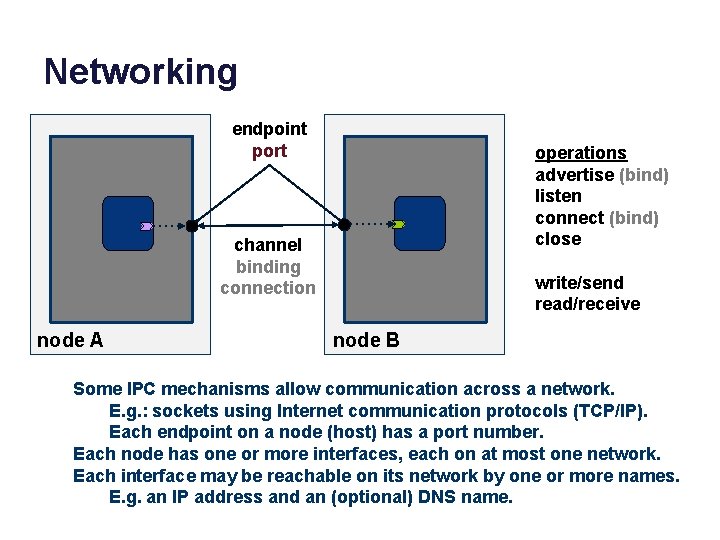
Networking endpoint port operations advertise (bind) listen connect (bind) close channel binding connection node A write/send read/receive node B Some IPC mechanisms allow communication across a network. E. g. : sockets using Internet communication protocols (TCP/IP). Each endpoint on a node (host) has a port number. Each node has one or more interfaces, each on at most one network. Each interface may be reachable on its network by one or more names. E. g. an IP address and an (optional) DNS name.
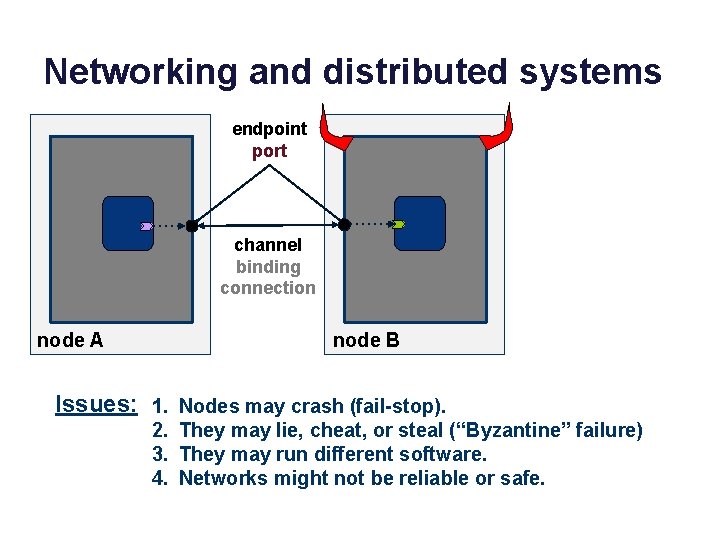
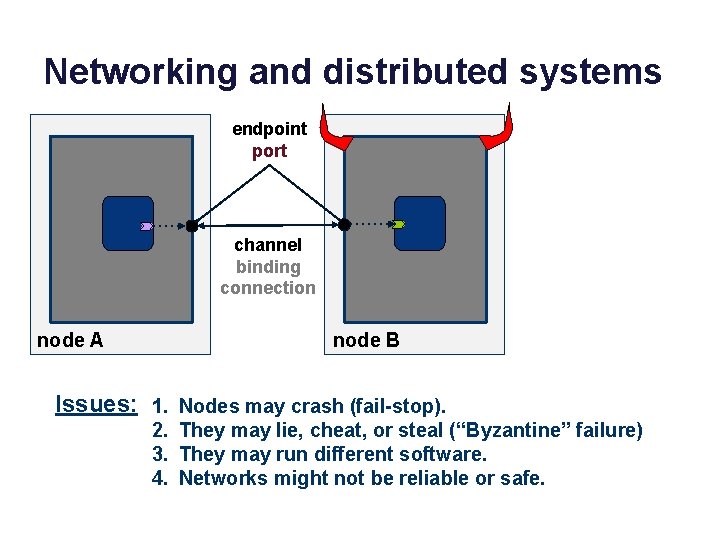
Networking and distributed systems endpoint port channel binding connection node A node B Issues: 1. Nodes may crash (fail-stop). 2. They may lie, cheat, or steal (“Byzantine” failure) 3. They may run different software. 4. Networks might not be reliable or safe.
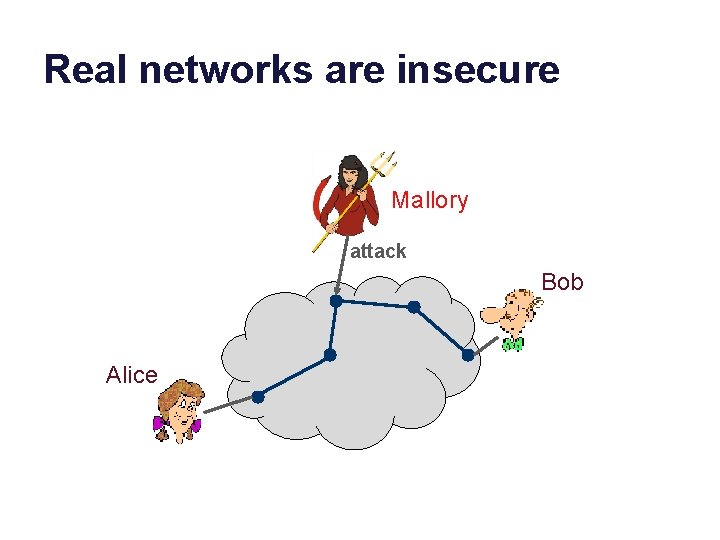
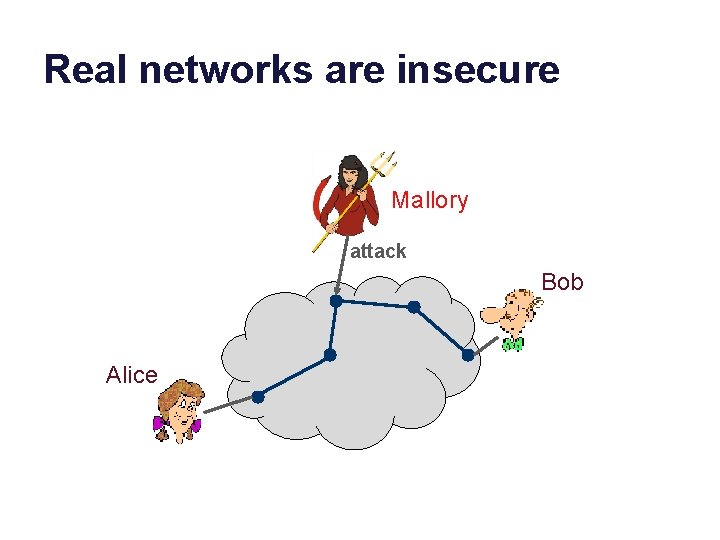
Real networks are insecure Mallory attack Bob Alice
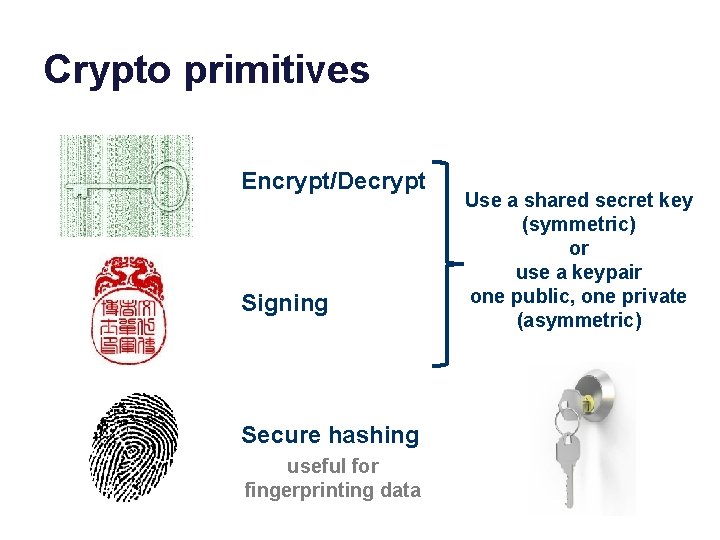
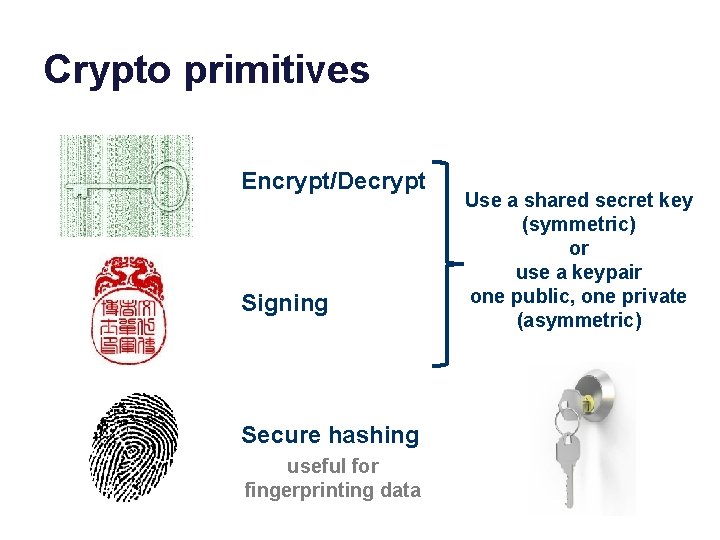
Crypto primitives Encrypt/Decrypt Signing Secure hashing useful for fingerprinting data Use a shared secret key (symmetric) or use a keypair one public, one private (asymmetric)
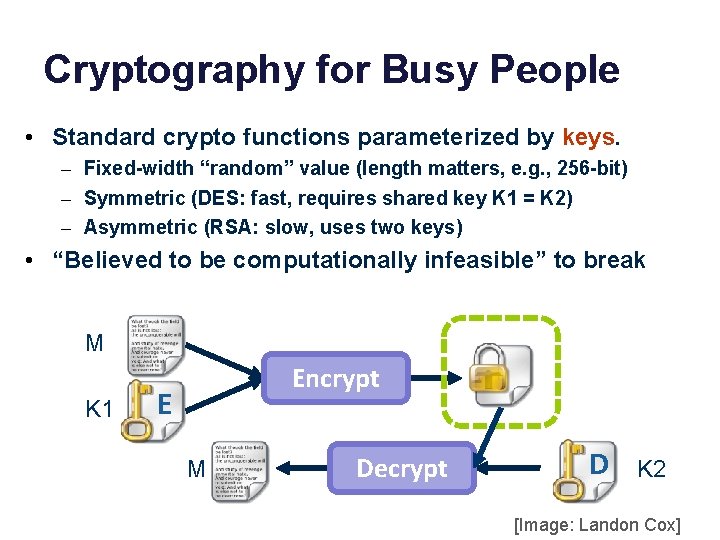
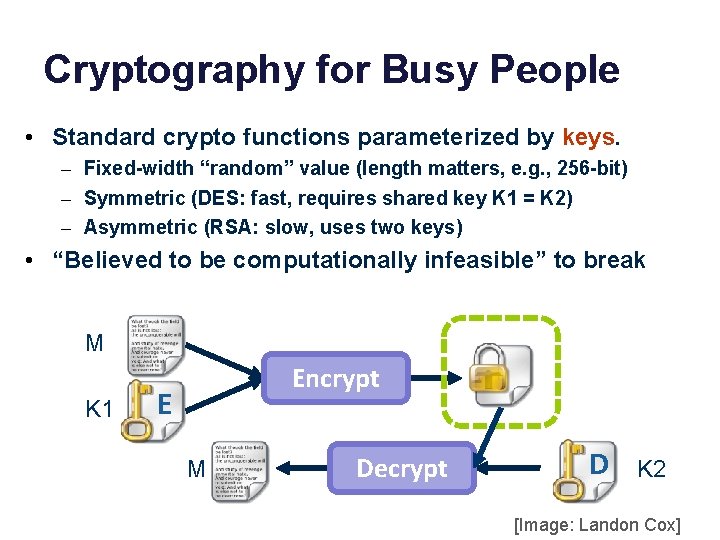
Cryptography for Busy People • Standard crypto functions parameterized by keys. – Fixed-width “random” value (length matters, e. g. , 256 -bit) – Symmetric (DES: fast, requires shared key K 1 = K 2) – Asymmetric (RSA: slow, uses two keys) • “Believed to be computationally infeasible” to break M K 1 Encrypt E M Decrypt D K 2 [Image: Landon Cox]
Symmetric Crypto • “Secret key” or “private key” cryptography. – DES, 3 DES, DESX, IDEA, AES • Sender and receiver must possess a shared secret – Shared key K – K = K 1 = K 2 • Message M, Key K {M}K = Encrypt(M, K) M = Decrypt({M}K , K)
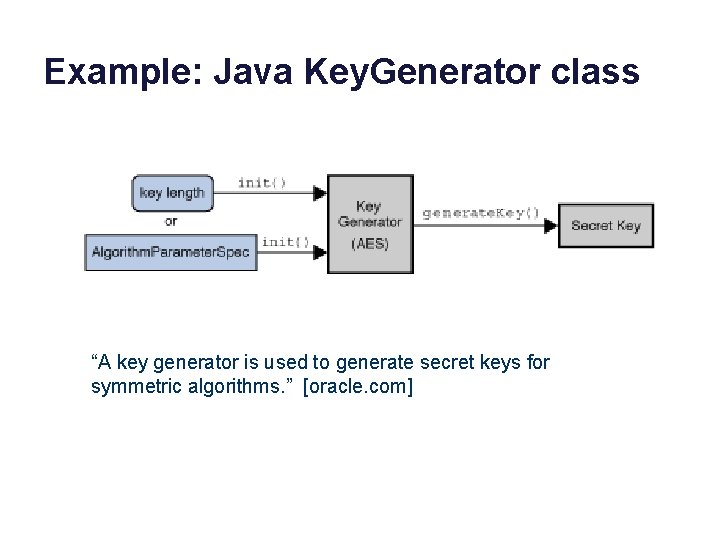
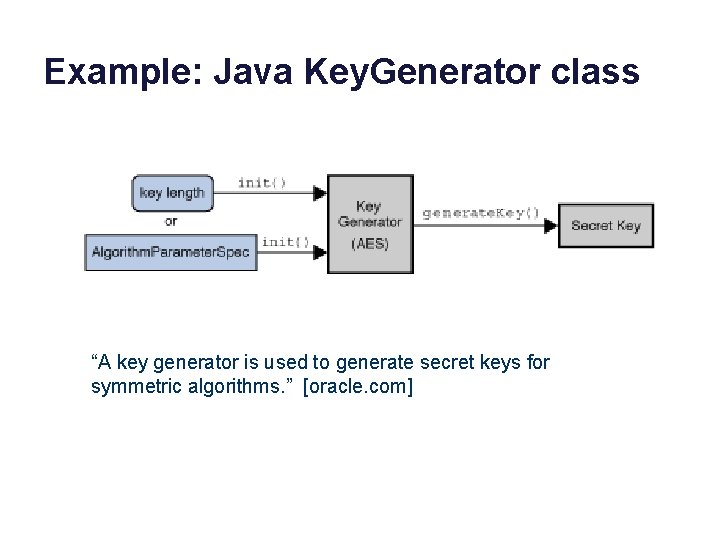
Example: Java Key. Generator class “A key generator is used to generate secret keys for symmetric algorithms. ” [oracle. com]
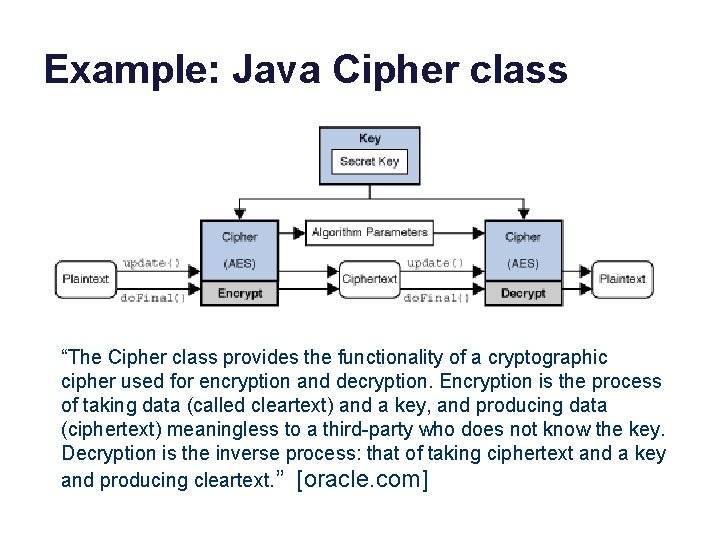
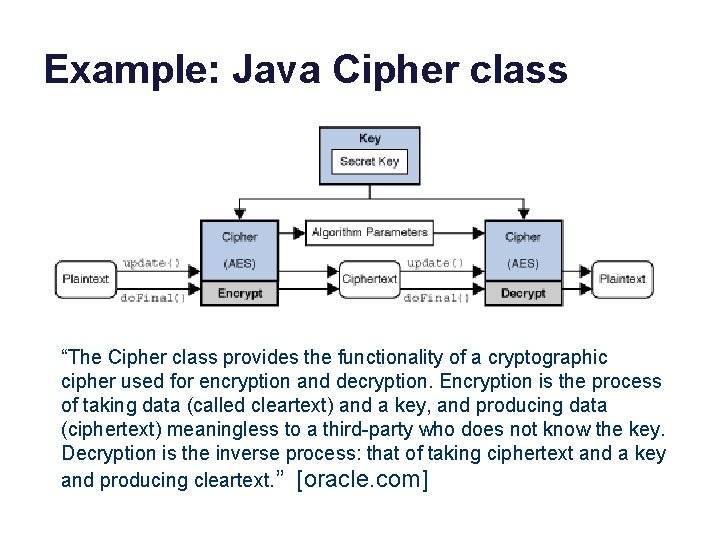
Example: Java Cipher class “The Cipher class provides the functionality of a cryptographic cipher used for encryption and decryption. Encryption is the process of taking data (called cleartext) and a key, and producing data (ciphertext) meaningless to a third-party who does not know the key. Decryption is the inverse process: that of taking ciphertext and a key and producing cleartext. ” [oracle. com]
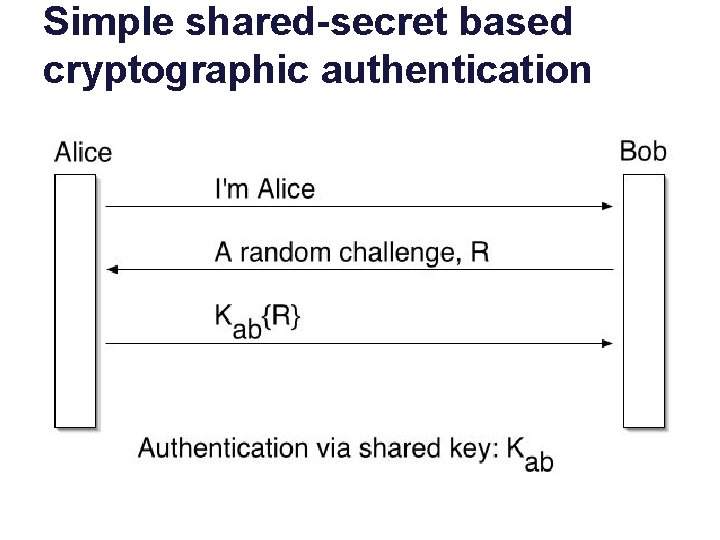
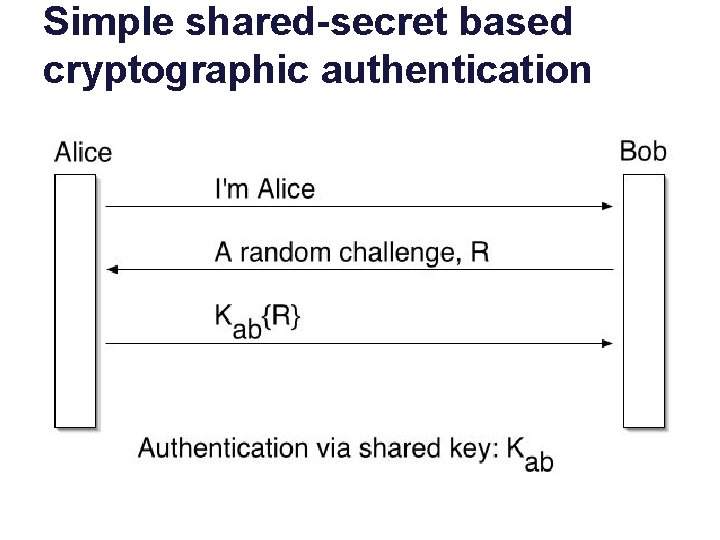
Simple shared-secret based cryptographic authentication shuque@isc. upenn
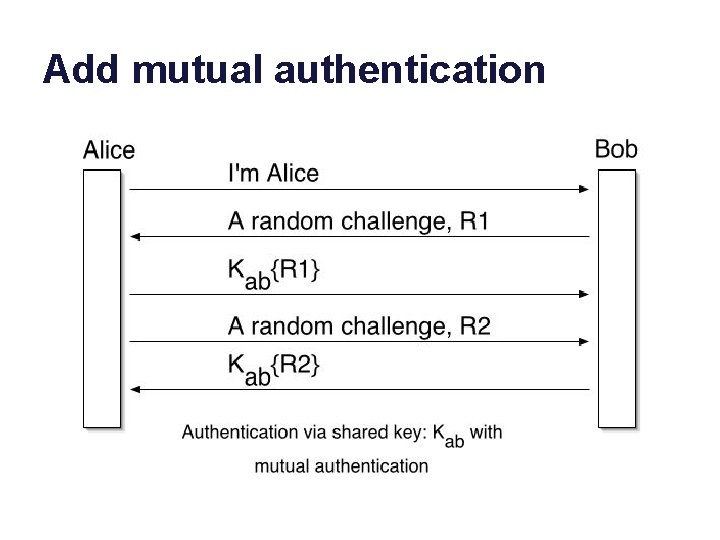
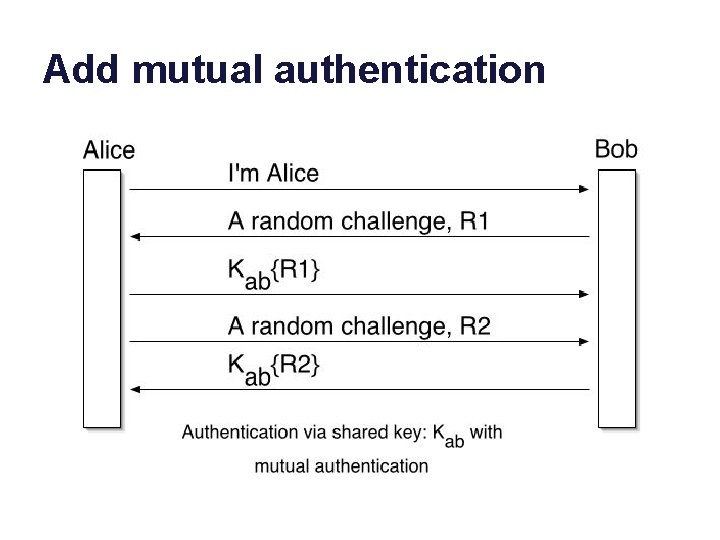
Add mutual authentication shuque@isc. upenn
Two “Key points” • The random challenge is a nonce. – “number used once” • Understand why the protocol uses a nonce. • In order for this protocol to work, Alice and Bob need a shared secret. • How can they establish this shared secret safely?
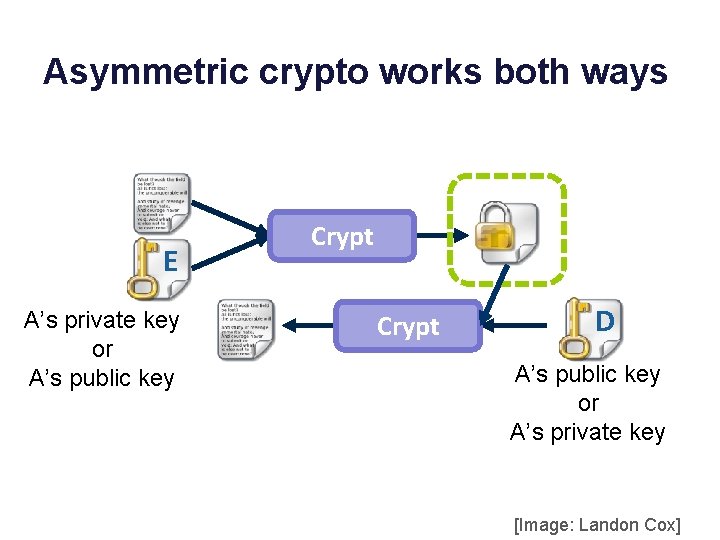
Asymmetric Crypto • Sometimes called “public key” cryptography. • Each subject/principal possesses a keypair: K-1 and K – Decrypt(K, Encrypt(K-1, M)) = M • Each principal keeps one key private. • The inverse key may be public. • Either key can be used to encrypt/decrypt.
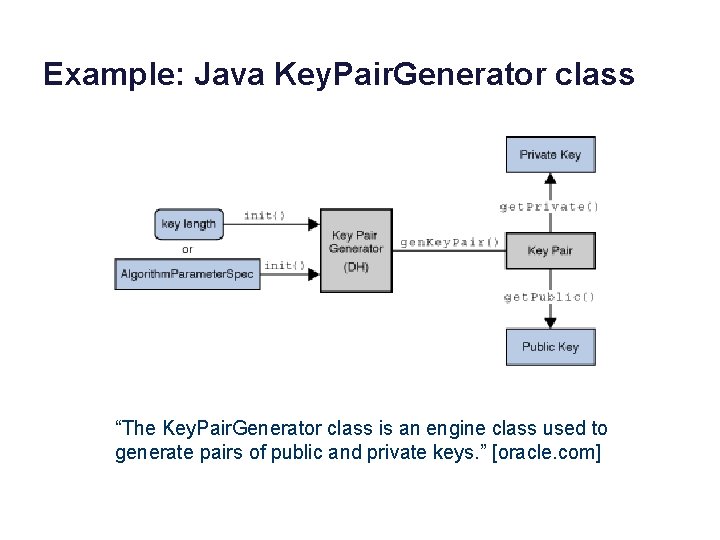
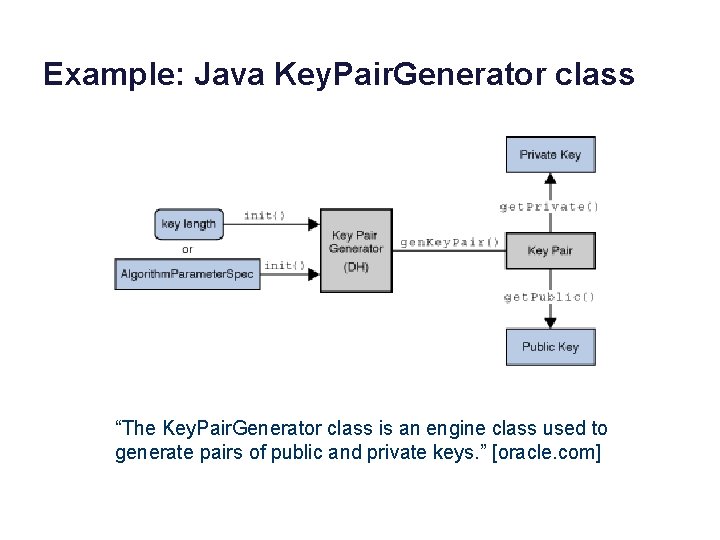
Example: Java Key. Pair. Generator class “The Key. Pair. Generator class is an engine class used to generate pairs of public and private keys. ” [oracle. com]
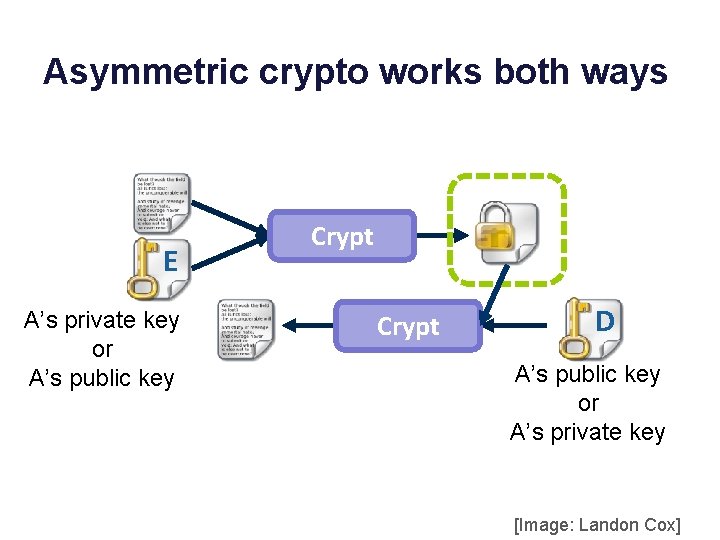
Asymmetric crypto works both ways E A’s private key or A’s public key Crypt D A’s public key or A’s private key [Image: Landon Cox]
Q • If Alice knows Bob’s public key, how can Alice use it to verify that the party on the other end of a channel is Bob? • What could go wrong? • How is this “better” than symmetric crypto? • How is it “worse”?
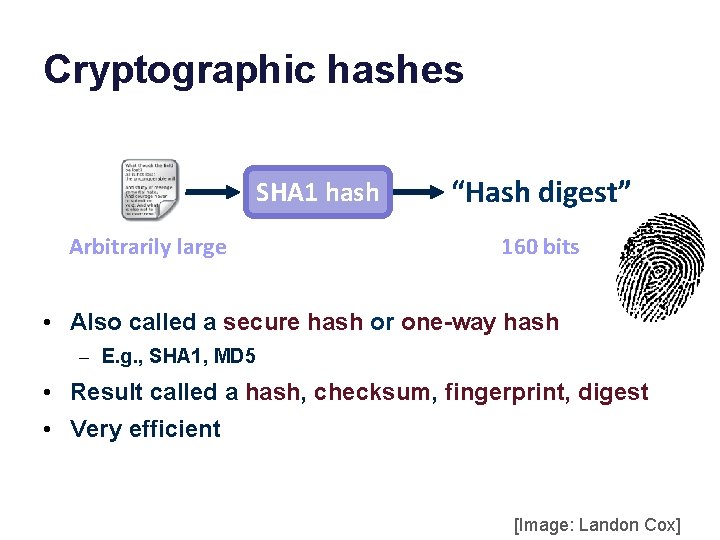
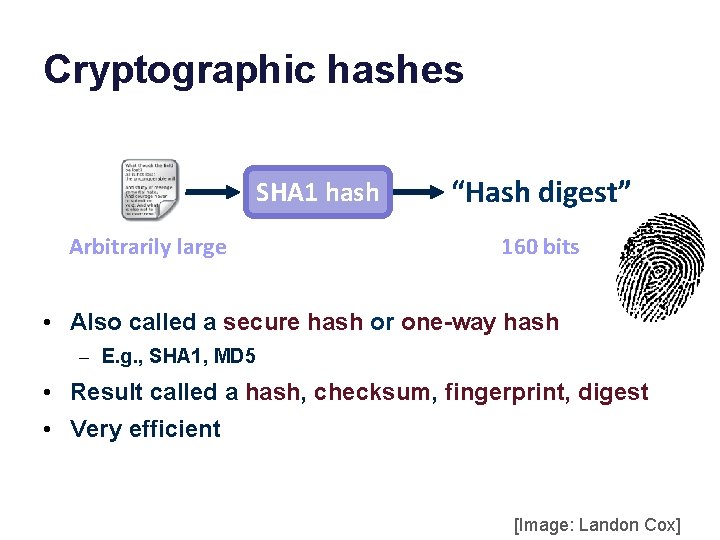
Cryptographic hashes SHA 1 hash Arbitrarily large “Hash digest” 160 bits • Also called a secure hash or one-way hash – E. g. , SHA 1, MD 5 • Result called a hash, checksum, fingerprint, digest • Very efficient [Image: Landon Cox]
Properties of Secure Hashing • Collision-resistant – There exist distinct M 1 and M 2 such that h(M 1) == h(M 2). – Such collisions are “hard” to find. • One way – Given digest, cannot generate an M with h(M) == digest. – Such collisions are “hard” to find. • Secure – The digest does not help to discover any part of M.
Properties of Secure Hashing • Collision-resistant – There exist distinct M 1 and M 2 such that h(M 1) == h(M 2). – Such collisions are “hard” to find. • One way – Given digest, cannot generate an M with h(M) == digest. – Such collisions are “hard” to find. • Secure – The digest does not help to discover any part of M. Haven’t SHA-1 and MD 5 been broken? Sort of…it turns out collisions are easier to find than thought, at least in some instances.
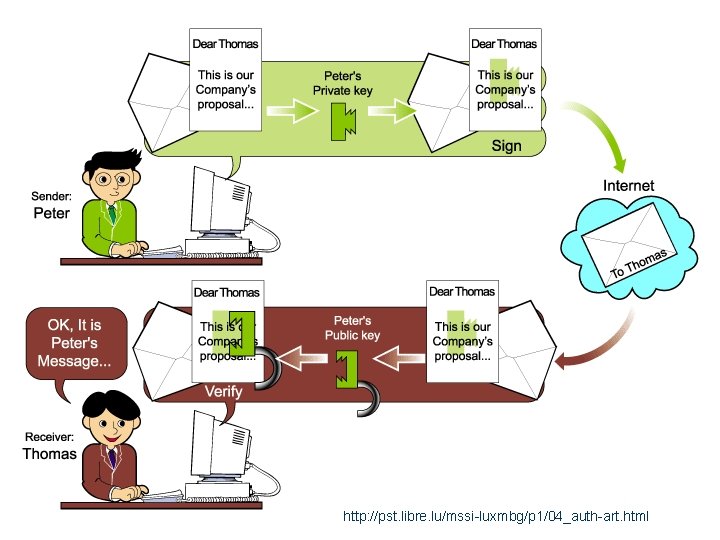
Digital Signature • A hash digest of M encrypted with a private key is called a digital signature – “Proves” that a particular identity sent M. • “Proves” M has not been tampered. • “Unforgeable” – The sender cannot deny sending M. • “non-repudiable” – Can be legally binding in the United States
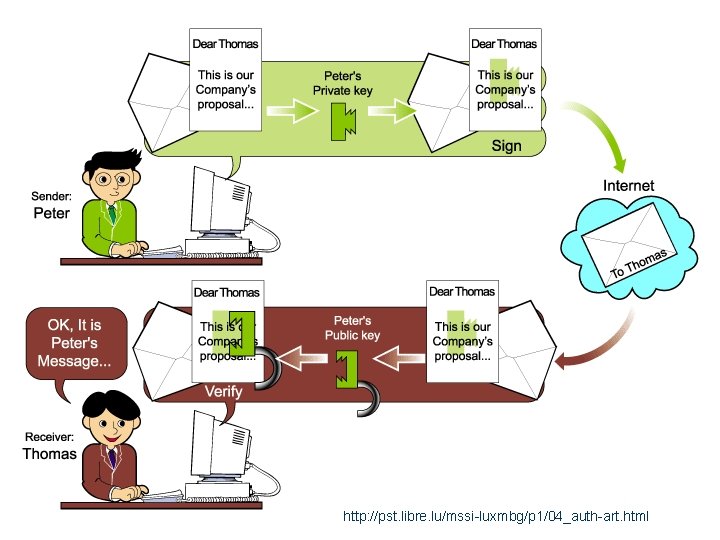
http: //pst. libre. lu/mssi-luxmbg/p 1/04_auth-art. html
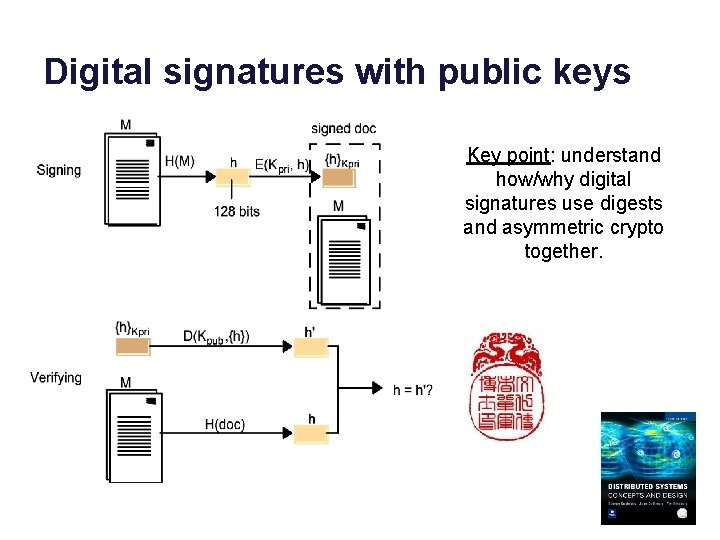
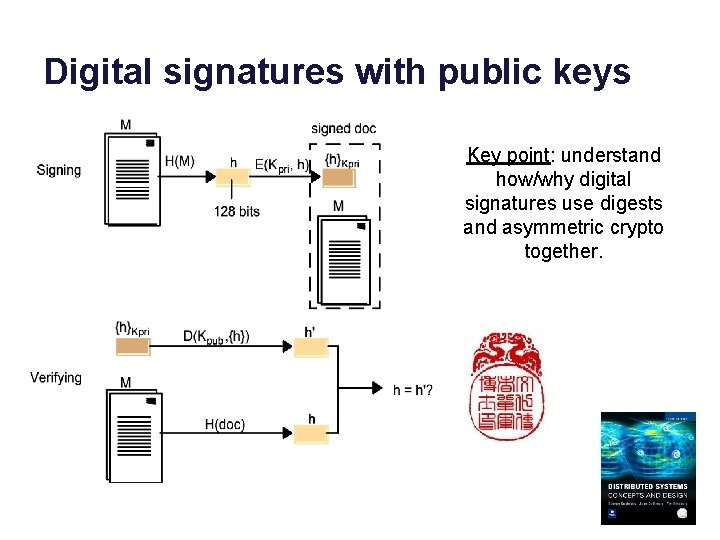
Digital signatures with public keys Key point: understand how/why digital signatures use digests and asymmetric crypto together.
Two “key points” • Digital signatures are “stronger” than physical signatures, because they are bound to the document contents. – Attacker cannot change the document contents without invalidating the signature. • To verify a signature, the receiver must already know the public key of the signer. – And it must be right. – But how to know for sure?
Two Flavors of “Signature” • A digest encrypted with a private asymmetric key is called a digital signature – “Proves” that a particular identity sent the message. • “Proves” the message has not been tampered. • “Unforgeable” – The sender cannot deny sending the message. • “non-repudiable” – Can be legally binding in the United States • A digest encrypted with a shared symmetric key is called a message authentication code (MAC). • faster, but…
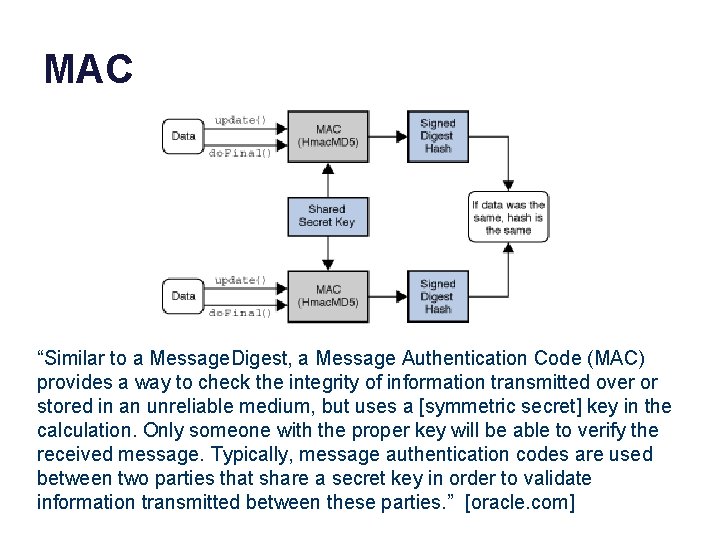
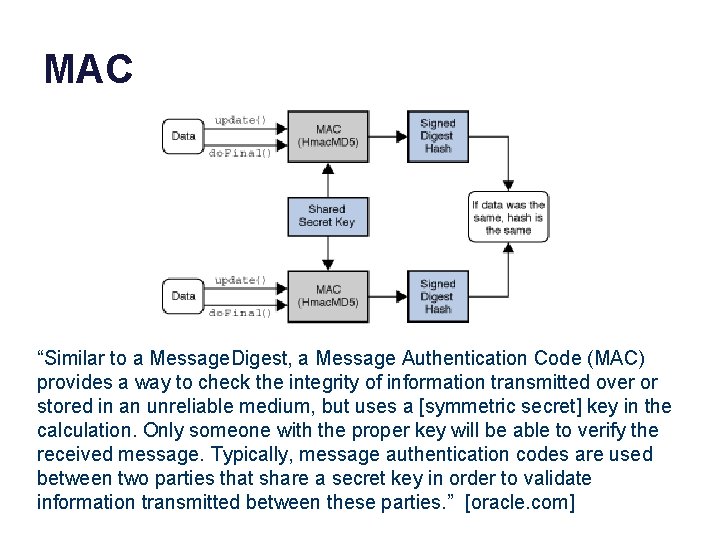
MAC “Similar to a Message. Digest, a Message Authentication Code (MAC) provides a way to check the integrity of information transmitted over or stored in an unreliable medium, but uses a [symmetric secret] key in the calculation. Only someone with the proper key will be able to verify the received message. Typically, message authentication codes are used between two parties that share a secret key in order to validate information transmitted between these parties. ” [oracle. com]
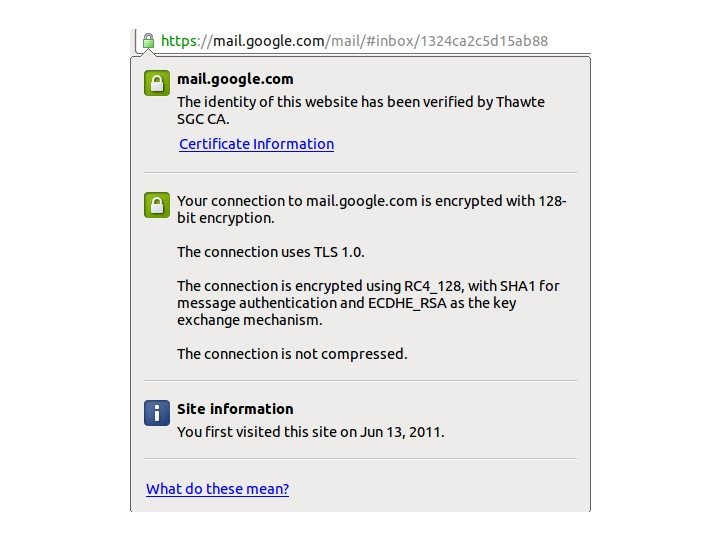
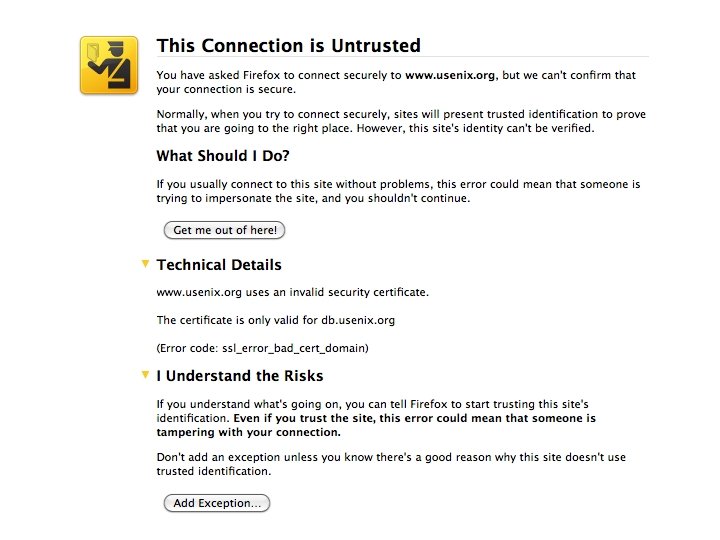
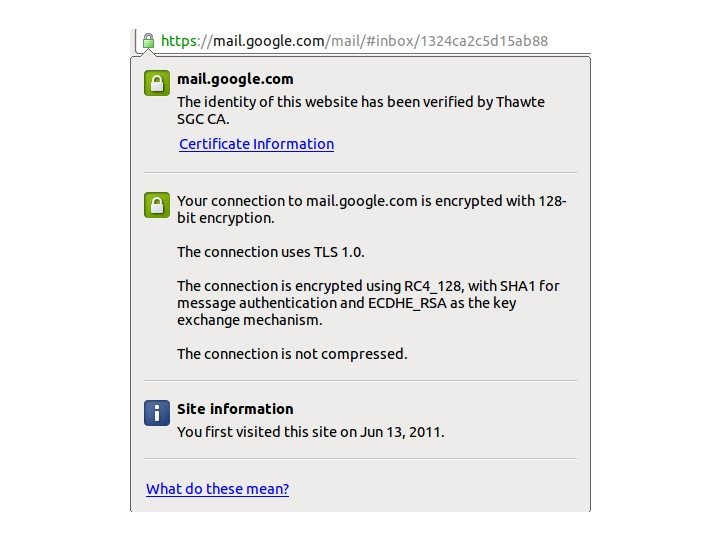
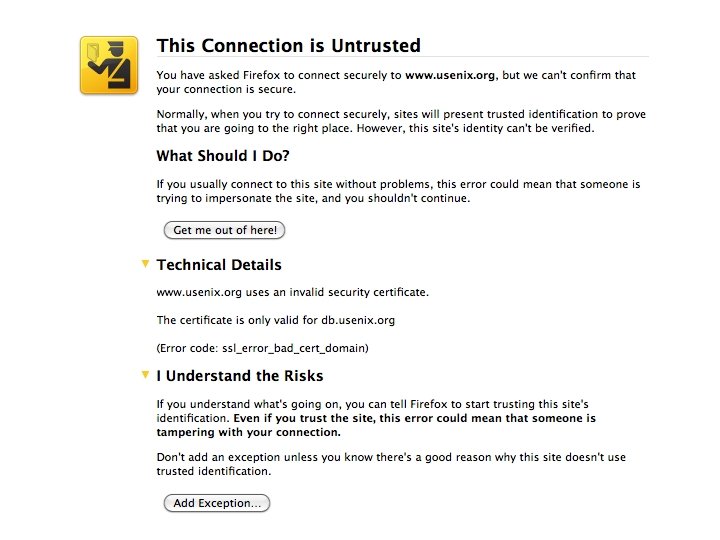
What happens… https: //www. shop. com/shop. html • How to authenticate shop. com? • How to assure integrity/privacy of communications? • How to prevent man-in-the-middle attack? • How does shop. com authenticate you? • Answer: Secure Sockets (SSL) or Transport. Layer Security (TLS)
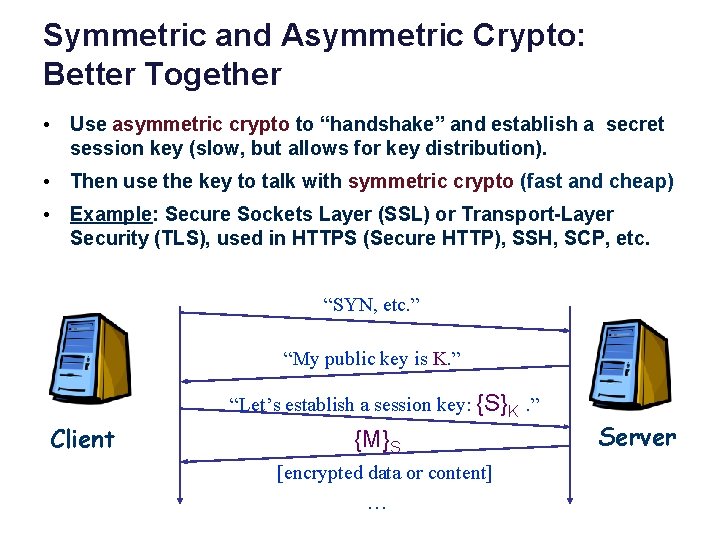
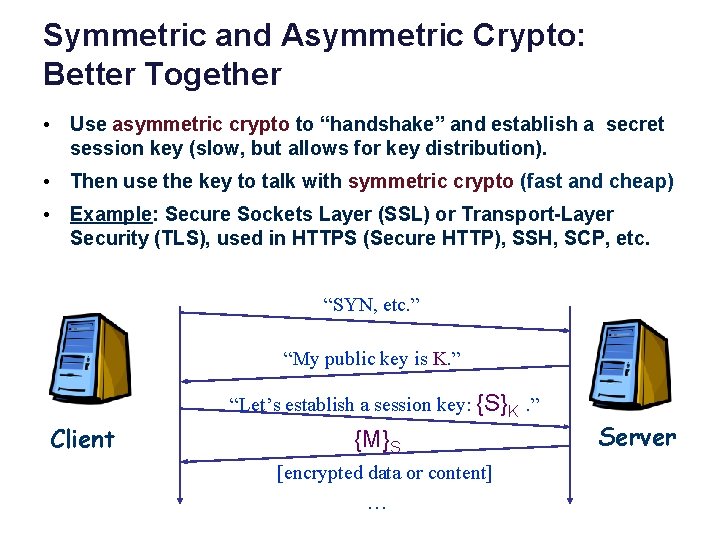
Symmetric and Asymmetric Crypto: Better Together • Use asymmetric crypto to “handshake” and establish a secret session key (slow, but allows for key distribution). • Then use the key to talk with symmetric crypto (fast and cheap) • Example: Secure Sockets Layer (SSL) or Transport-Layer Security (TLS), used in HTTPS (Secure HTTP), SSH, SCP, etc. “SYN, etc. ” “My public key is K. ” “Let’s establish a session key: {S}K. ” Client {M}S [encrypted data or content] … Server
What are we missing? • Does C know (believe) that K really is the public key of S? • How to authenticate S?
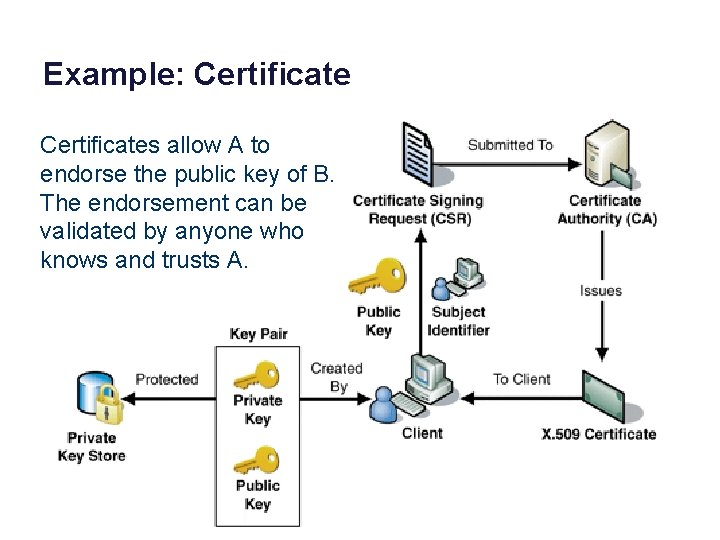
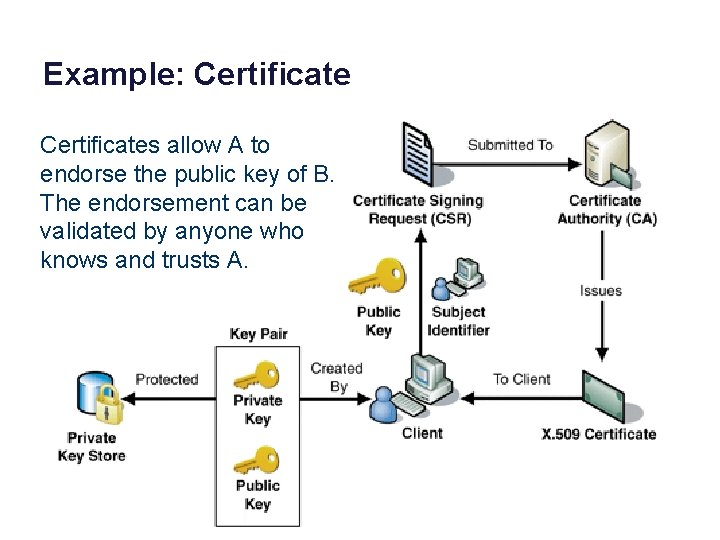
Example: Certificates allow A to endorse the public key of B. The endorsement can be validated by anyone who knows and trusts A.
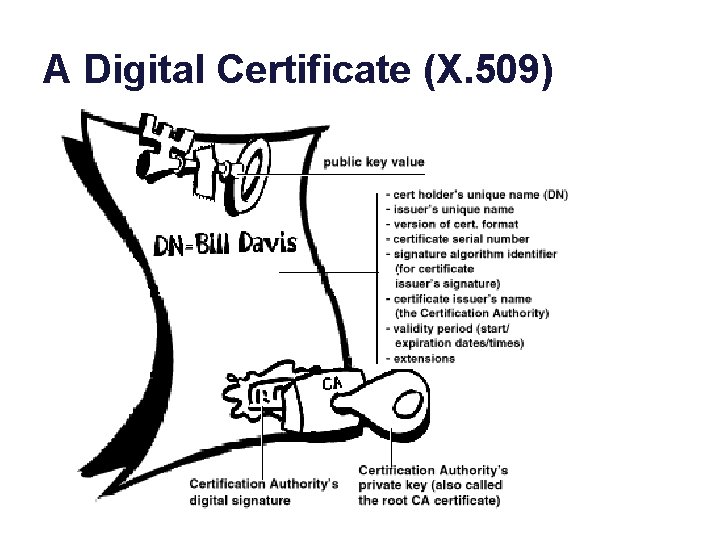
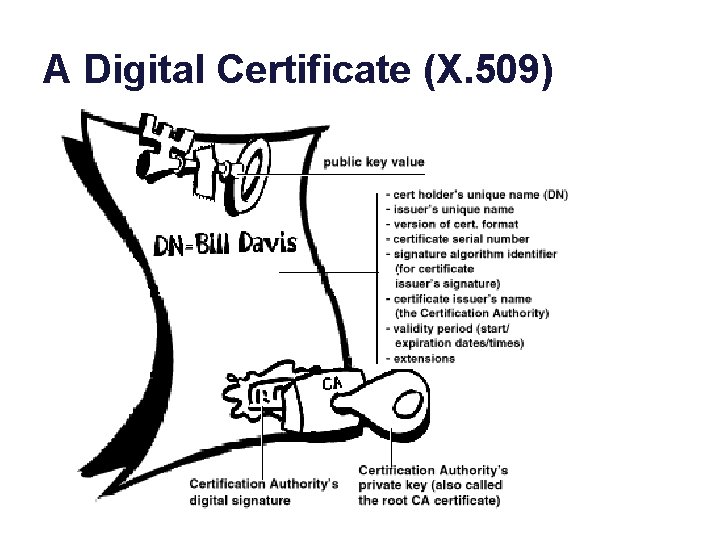
A Digital Certificate (X. 509)
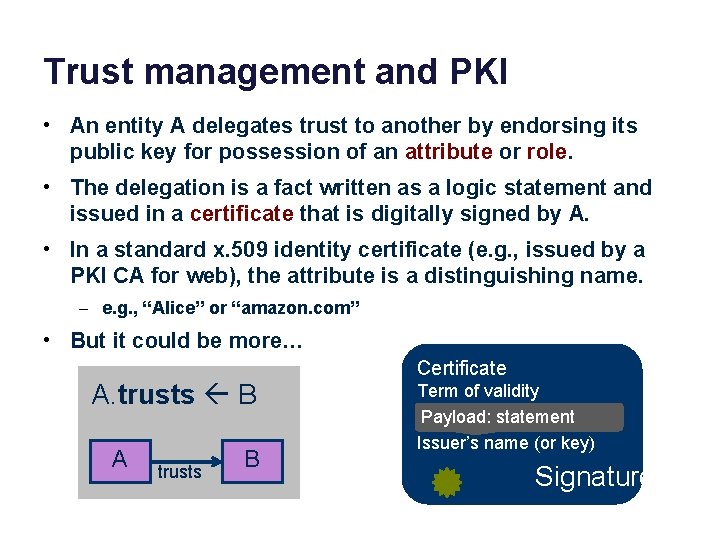
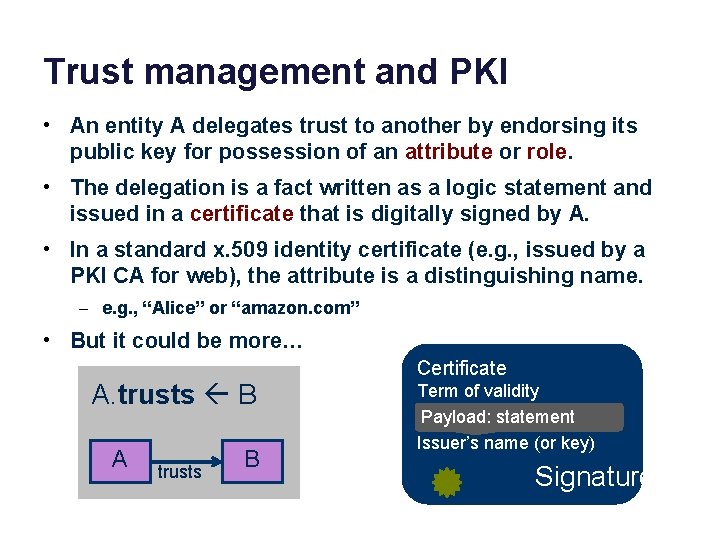
Trust management and PKI • An entity A delegates trust to another by endorsing its public key for possession of an attribute or role. • The delegation is a fact written as a logic statement and issued in a certificate that is digitally signed by A. • In a standard x. 509 identity certificate (e. g. , issued by a PKI CA for web), the attribute is a distinguishing name. – e. g. , “Alice” or “amazon. com” • But it could be more… A. trusts B A trusts B Certificate Term of validity Payload: statement Issuer’s name (or key) Signature
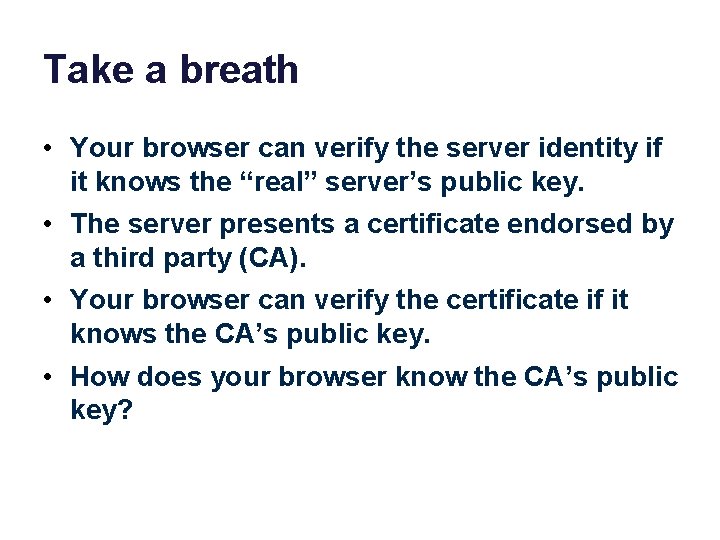
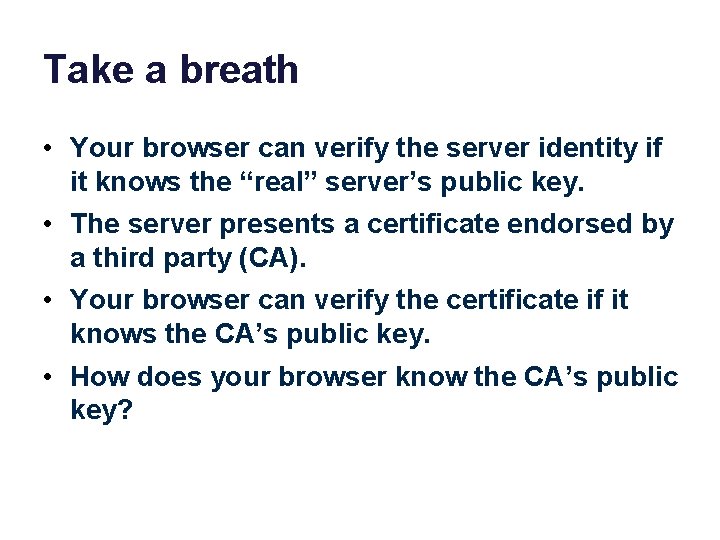
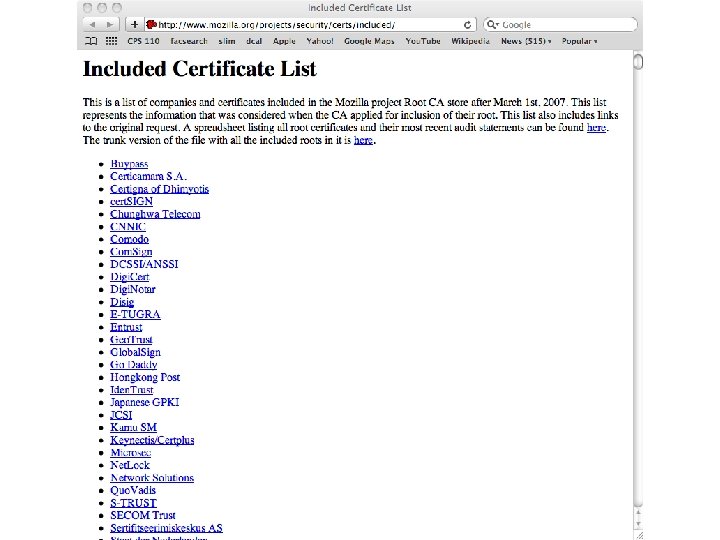
Take a breath • Your browser can verify the server identity if it knows the “real” server’s public key. • The server presents a certificate endorsed by a third party (CA). • Your browser can verify the certificate if it knows the CA’s public key. • How does your browser know the CA’s public key?


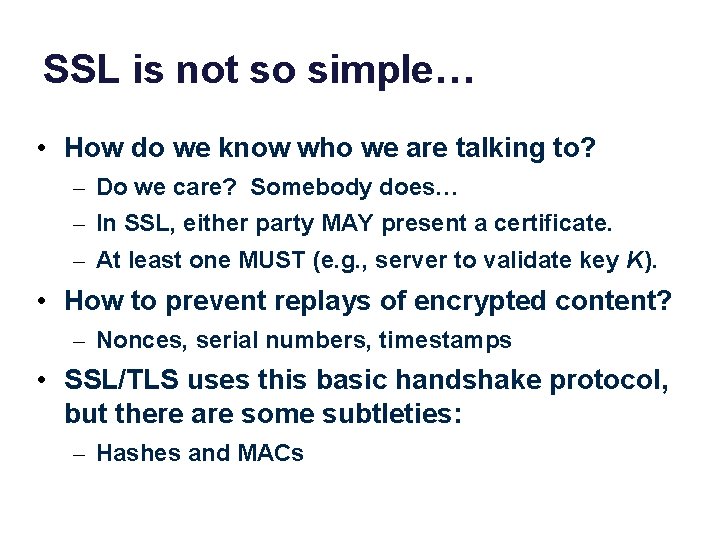
SSL is not so simple… • How do we know who we are talking to? – Do we care? Somebody does… – In SSL, either party MAY present a certificate. – At least one MUST (e. g. , server to validate key K). • How to prevent replays of encrypted content? – Nonces, serial numbers, timestamps • SSL/TLS uses this basic handshake protocol, but there are some subtleties: – Hashes and MACs
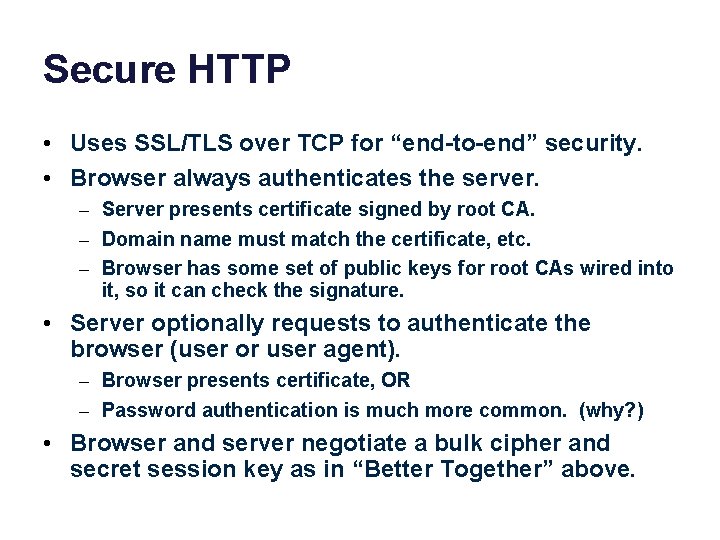
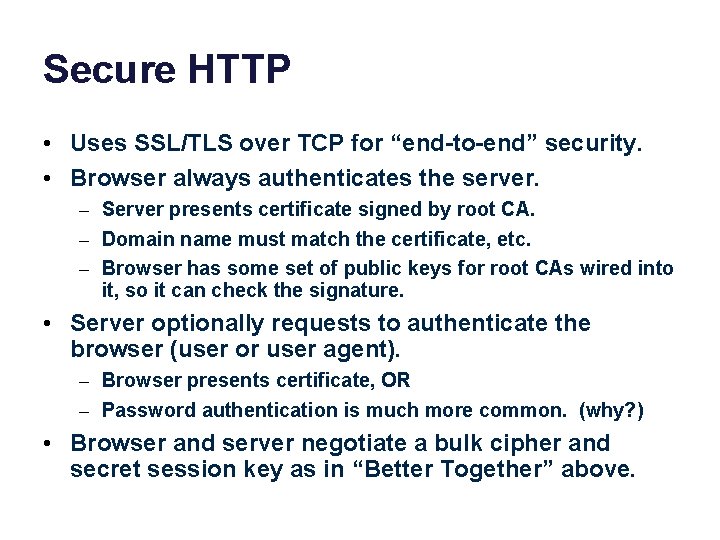
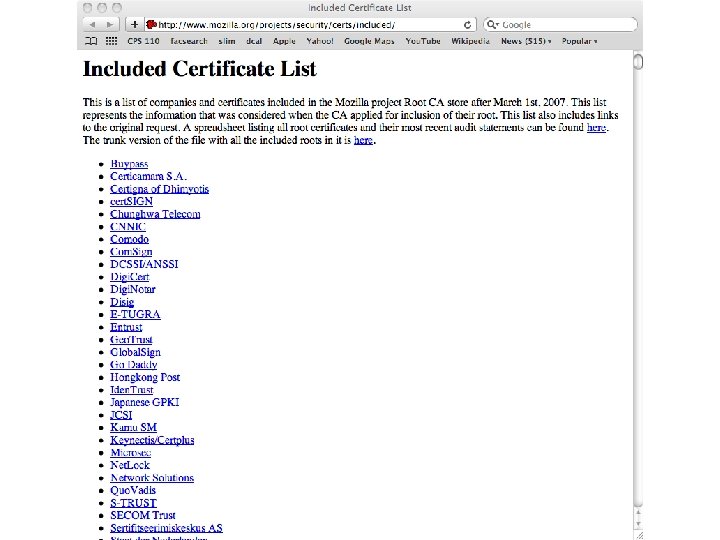
Secure HTTP • Uses SSL/TLS over TCP for “end-to-end” security. • Browser always authenticates the server. – Server presents certificate signed by root CA. – Domain name must match the certificate, etc. – Browser has some set of public keys for root CAs wired into it, so it can check the signature. • Server optionally requests to authenticate the browser (user or user agent). – Browser presents certificate, OR – Password authentication is much more common. (why? ) • Browser and server negotiate a bulk cipher and secret session key as in “Better Together” above.
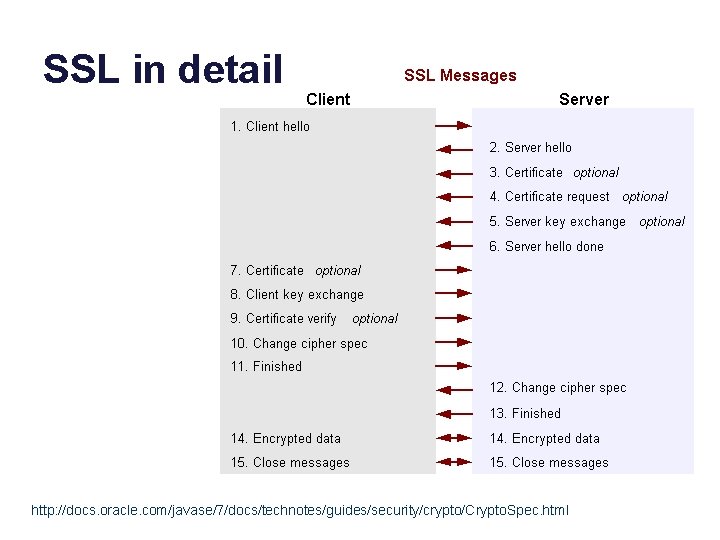
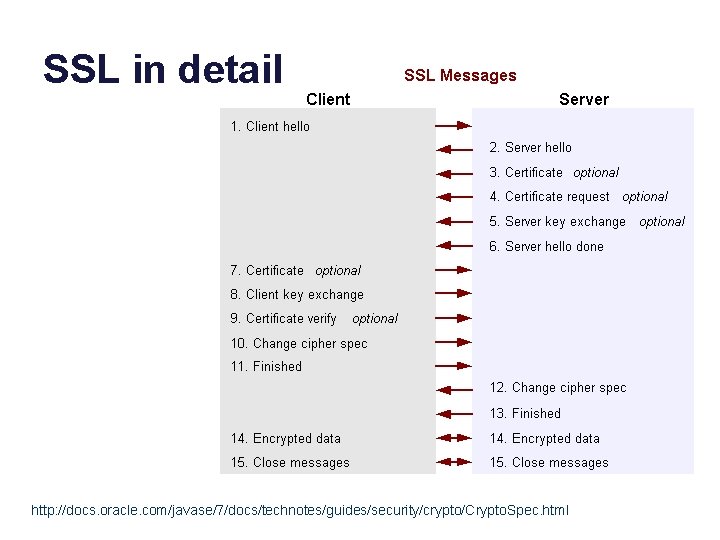
SSL in detail http: //docs. oracle. com/javase/7/docs/technotes/guides/security/crypto/Crypto. Spec. html
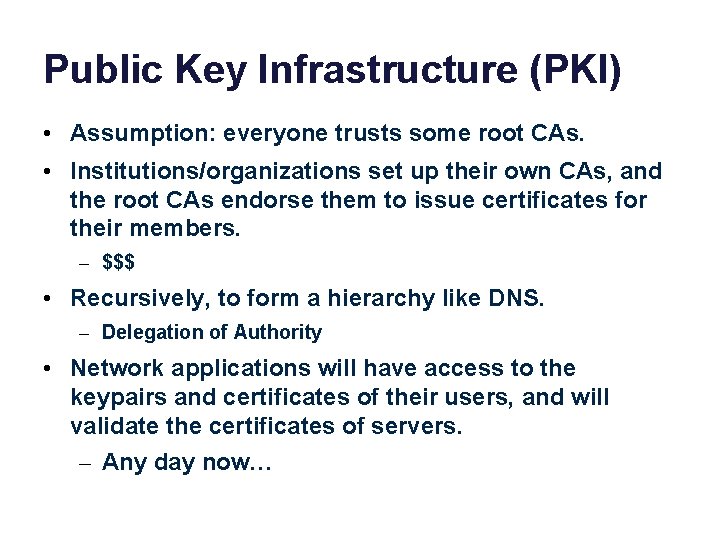
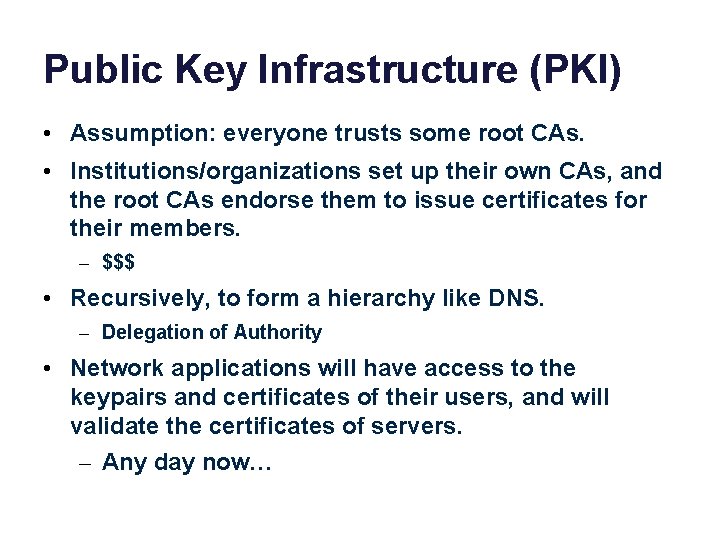
Public Key Infrastructure (PKI) • Assumption: everyone trusts some root CAs. • Institutions/organizations set up their own CAs, and the root CAs endorse them to issue certificates for their members. – $$$ • Recursively, to form a hierarchy like DNS. – Delegation of Authority • Network applications will have access to the keypairs and certificates of their users, and will validate the certificates of servers. – Any day now…

Distributing session keys • We want to use symmetric crypto because it is cheap. • But we need a way to negotiate and distribute a shared secret (session key). • Two examples to looks at: – SSL/TLS/HTTPS – Kerberos (Needham/Schroeder) authentication protocol – Shibboleth single-sign-on (SSO)