HOW TO BUILD A SECURE COMMUNICATION CHANNEL Guomin
HOW TO BUILD A SECURE COMMUNICATION CHANNEL Guomin Yang Temasek Laboratories National University of Singapore
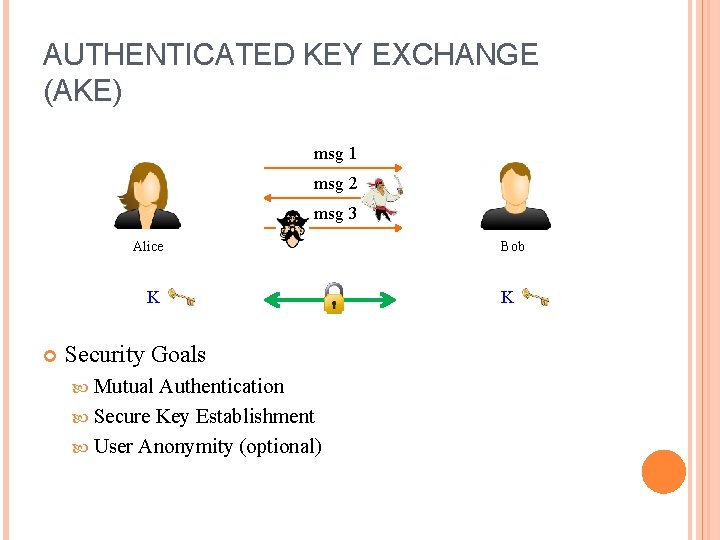
AUTHENTICATED KEY EXCHANGE (AKE) msg 1 msg 2 msg 3 Alice K Security Goals Mutual Authentication Secure Key Establishment User Anonymity (optional) Bob K
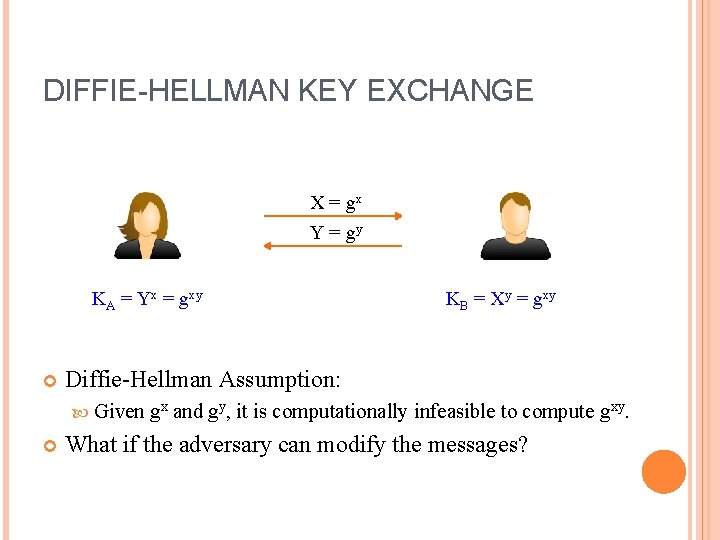
DIFFIE-HELLMAN KEY EXCHANGE X = gx Y = gy KA = Yx = gxy Diffie-Hellman Assumption: Given gx KB = Xy = gxy and gy, it is computationally infeasible to compute gxy. What if the adversary can modify the messages?
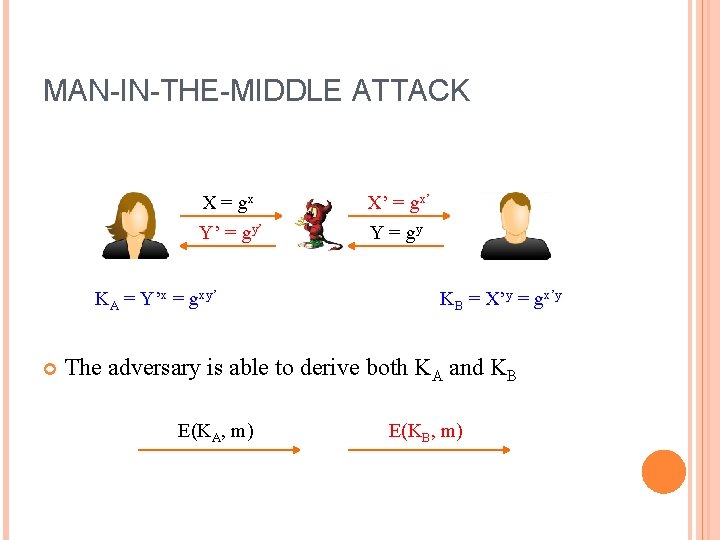
MAN-IN-THE-MIDDLE ATTACK X = gx Y’ = gy’ KA = Y’x = gxy’ X’ = gx’ Y = gy KB = X’y = gx’y The adversary is able to derive both KA and KB E(KA, m) E(KB, m)
OUTLINE Security Model and Definition Two-party AKE ISO/IEC SIGMA (H)MQV AKE under Bad Randomness Secure Roaming GSM/3 GPP Universal AKE Other AKE Protocols
SECURITY MODEL AND DEFINITION
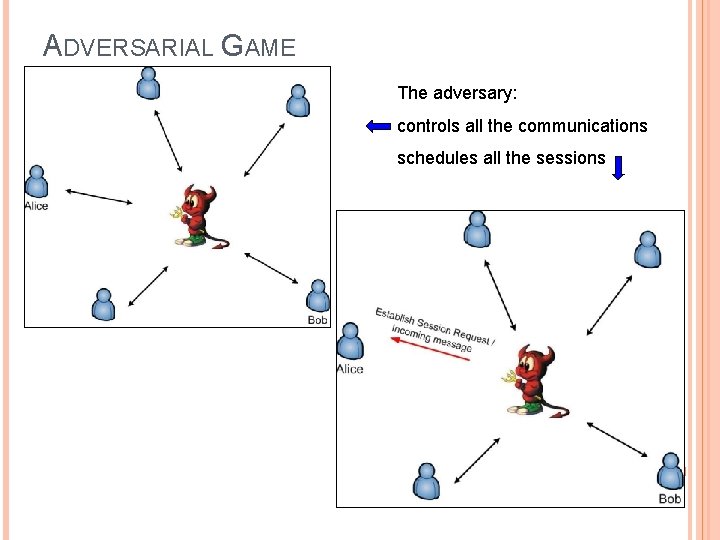
ADVERSARIAL GAME The adversary: controls all the communications schedules all the sessions
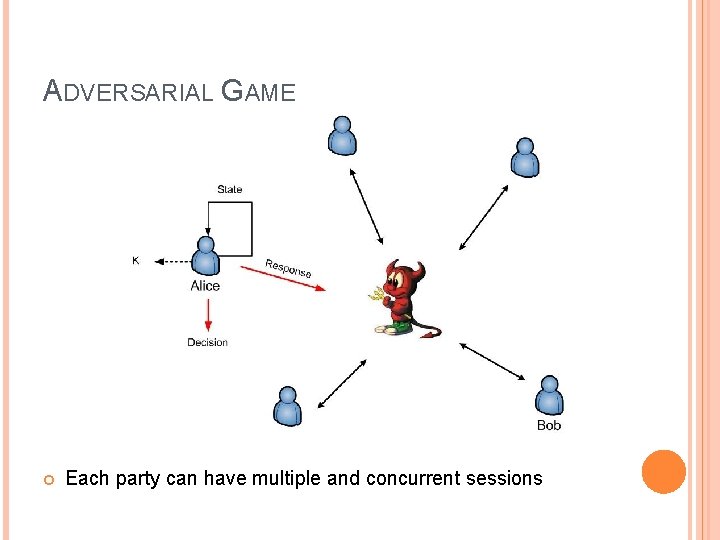
ADVERSARIAL GAME Each party can have multiple and concurrent sessions
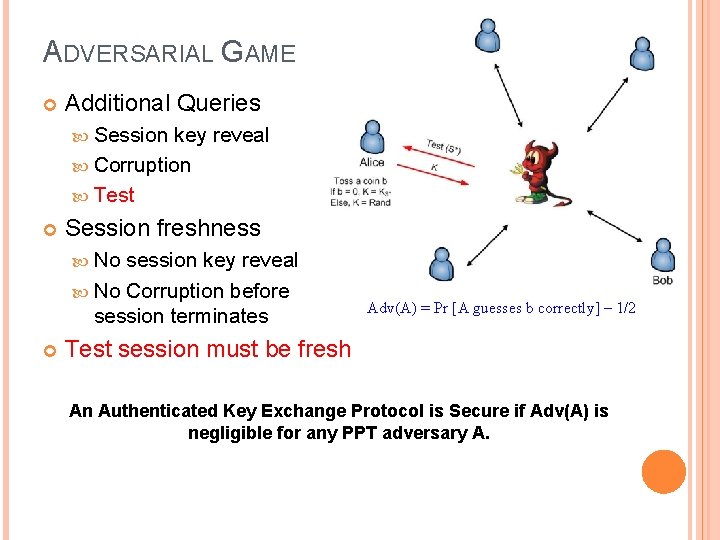
ADVERSARIAL GAME Additional Queries Session key reveal Corruption Test Session freshness No session key reveal No Corruption before session terminates Adv(A) = Pr [A guesses b correctly] – 1/2 Test session must be fresh An Authenticated Key Exchange Protocol is Secure if Adv(A) is negligible for any PPT adversary A.
TWO-PARTY AKE PROTOCOLS
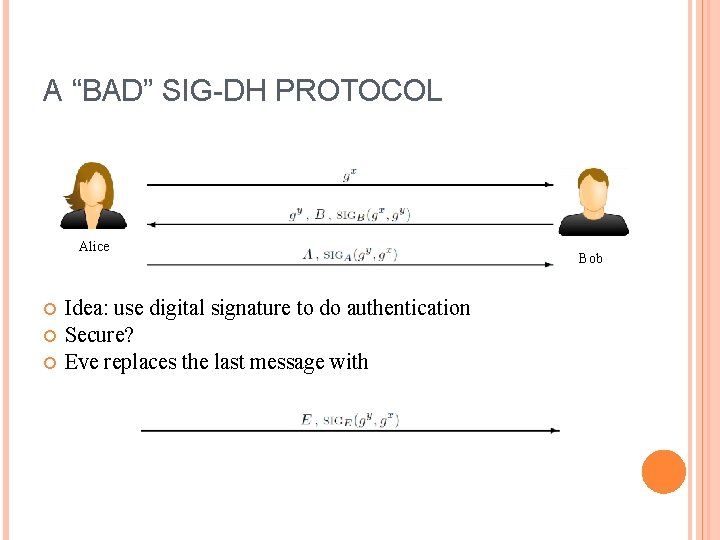
A “BAD” SIG-DH PROTOCOL Alice Idea: use digital signature to do authentication Secure? Eve replaces the last message with Bob
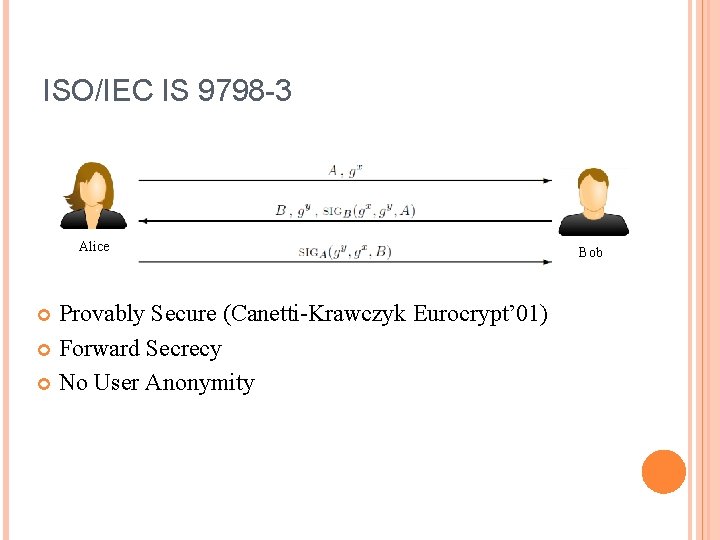
ISO/IEC IS 9798 -3 Alice Provably Secure (Canetti-Krawczyk Eurocrypt’ 01) Forward Secrecy No User Anonymity Bob
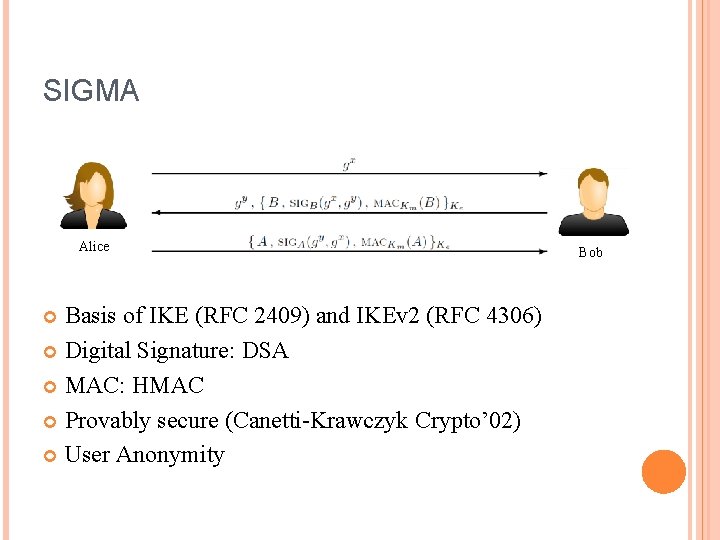
SIGMA Alice Basis of IKE (RFC 2409) and IKEv 2 (RFC 4306) Digital Signature: DSA MAC: HMAC Provably secure (Canetti-Krawczyk Crypto’ 02) User Anonymity Bob
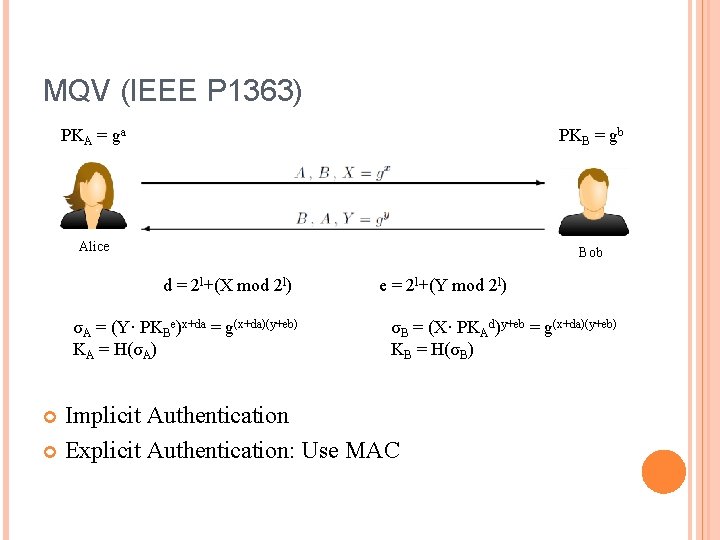
MQV (IEEE P 1363) PKA = ga PKB = gb Alice Bob d = 2 l+(X mod 2 l) σA = (Y· PKBe)x+da = g(x+da)(y+eb) KA = H(σA) e = 2 l+(Y mod 2 l) σB = (X· PKAd)y+eb = g(x+da)(y+eb) KB = H(σB) Implicit Authentication Explicit Authentication: Use MAC
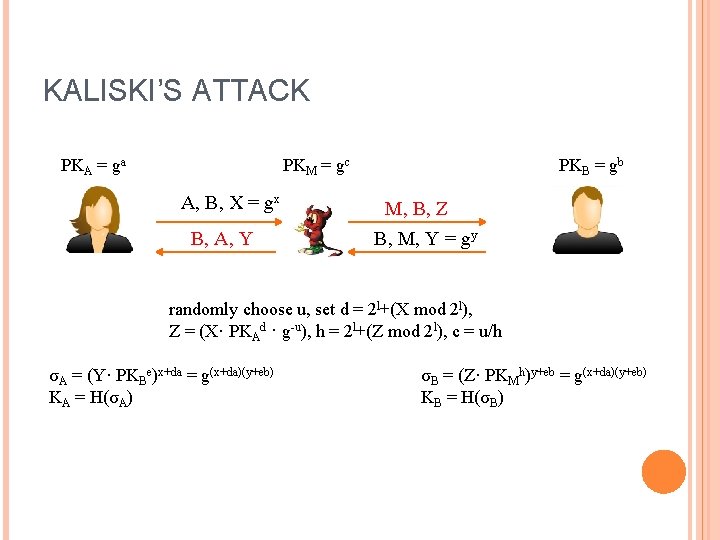
KALISKI’S ATTACK PKA = ga PKM = gc A, B, X = gx B, A, Y PKB = gb M, B, Z B, M, Y = gy randomly choose u, set d = 2 l+(X mod 2 l), Z = (X· PKAd · g-u), h = 2 l+(Z mod 2 l), c = u/h σA = (Y· PKBe)x+da = g(x+da)(y+eb) KA = H(σA) σB = (Z· PKMh)y+eb = g(x+da)(y+eb) KB = H(σB)
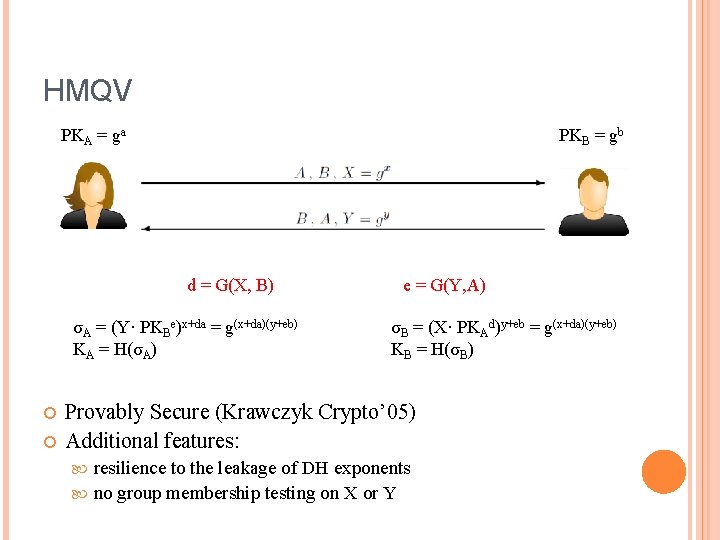
HMQV PKA = ga PKB = gb d = G(X, B) σA = (Y· PKBe)x+da = g(x+da)(y+eb) KA = H(σA) e = G(Y, A) σB = (X· PKAd)y+eb = g(x+da)(y+eb) KB = H(σB) Provably Secure (Krawczyk Crypto’ 05) Additional features: resilience to the leakage of DH exponents no group membership testing on X or Y
AKE UNDER BAD RANDOMNESS CASE 1: RESET ATTACKS
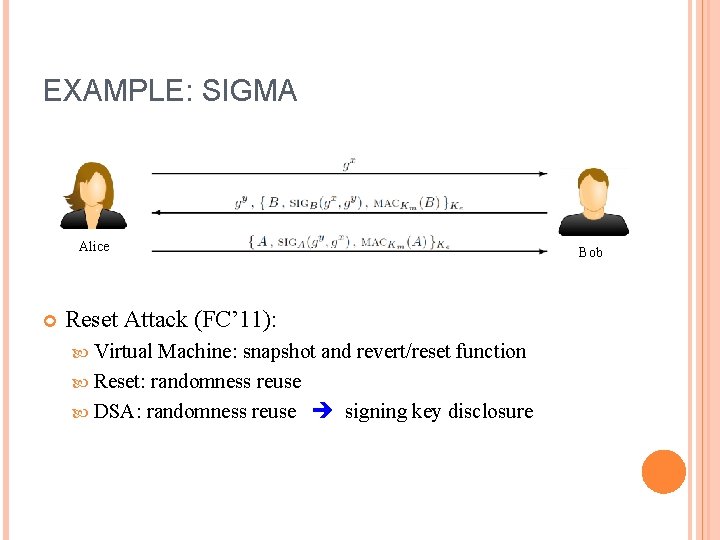
EXAMPLE: SIGMA Alice Reset Attack (FC’ 11): Virtual Machine: snapshot and revert/reset function Reset: randomness reuse DSA: randomness reuse signing key disclosure Bob
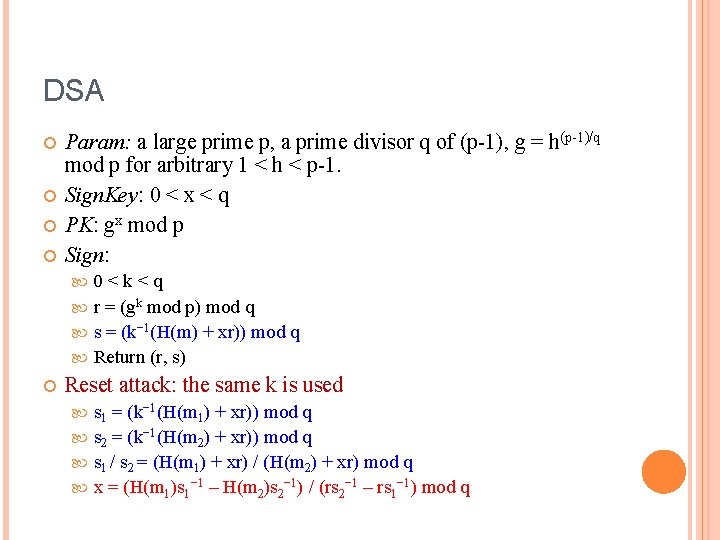
DSA Param: a large prime p, a prime divisor q of (p-1), g = h(p-1)/q mod p for arbitrary 1 < h < p-1. Sign. Key: 0 < x < q PK: gx mod p Sign: 0<k<q r = (gk mod p) mod q s = (k− 1(H(m) + xr)) mod q Return (r, s) Reset attack: the same k is used s 1 = (k− 1(H(m 1) + xr)) mod q s 2 = (k− 1(H(m 2) + xr)) mod q s 1 / s 2 = (H(m 1) + xr) / (H(m 2) + xr) mod q x = (H(m 1)s 1− 1 – H(m 2)s 2− 1) / (rs 2− 1 – rs 1− 1) mod q
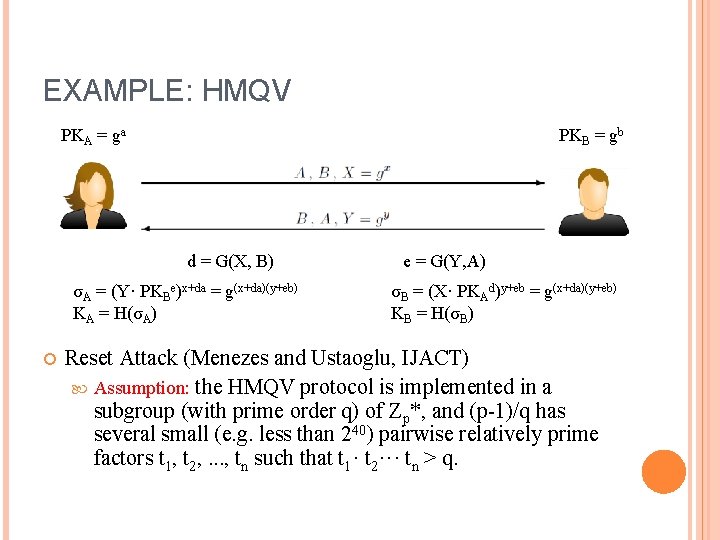
EXAMPLE: HMQV PKA = ga PKB = gb d = G(X, B) σA = (Y· PKBe)x+da = g(x+da)(y+eb) KA = H(σA) e = G(Y, A) σB = (X· PKAd)y+eb = g(x+da)(y+eb) KB = H(σB) Reset Attack (Menezes and Ustaoglu, IJACT) Assumption: the HMQV protocol is implemented in a subgroup (with prime order q) of Zp*, and (p-1)/q has several small (e. g. less than 240) pairwise relatively prime factors t 1, t 2, . . . , tn such that t 1· t 2··· tn > q.
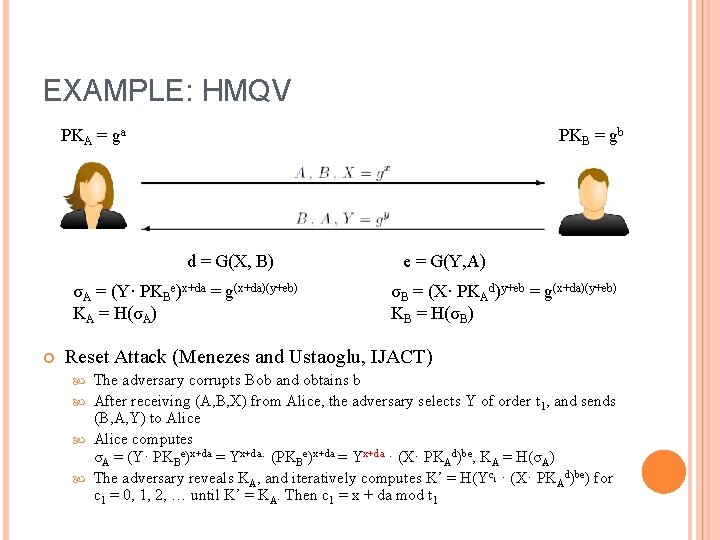
EXAMPLE: HMQV PKA = ga PKB = gb d = G(X, B) σA = (Y· PKBe)x+da = g(x+da)(y+eb) KA = H(σA) e = G(Y, A) σB = (X· PKAd)y+eb = g(x+da)(y+eb) KB = H(σB) Reset Attack (Menezes and Ustaoglu, IJACT) The adversary corrupts Bob and obtains b After receiving (A, B, X) from Alice, the adversary selects Y of order t 1, and sends (B, A, Y) to Alice computes σA = (Y· PKBe)x+da = Yx+da· (PKBe)x+da = Yx+da · (X· PKAd)be, KA = H(σA) The adversary reveals KA, and iteratively computes K’ = H(Yc 1 · (X· PKAd)be) for c 1 = 0, 1, 2, … until K’ = KA. Then c 1 = x + da mod t 1
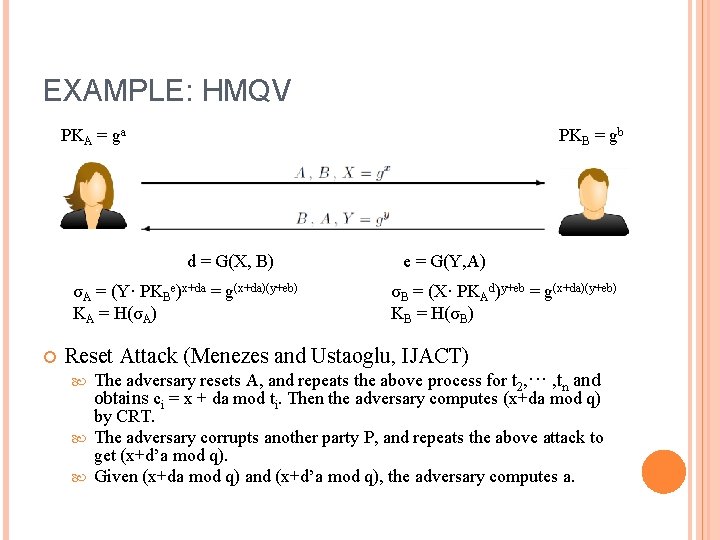
EXAMPLE: HMQV PKA = ga PKB = gb d = G(X, B) σA = (Y· PKBe)x+da = g(x+da)(y+eb) KA = H(σA) e = G(Y, A) σB = (X· PKAd)y+eb = g(x+da)(y+eb) KB = H(σB) Reset Attack (Menezes and Ustaoglu, IJACT) The adversary resets A, and repeats the above process for t 2, ··· , tn and obtains ci = x + da mod ti. Then the adversary computes (x+da mod q) by CRT. The adversary corrupts another party P, and repeats the above attack to get (x+d’a mod q). Given (x+da mod q) and (x+d’a mod q), the adversary computes a.
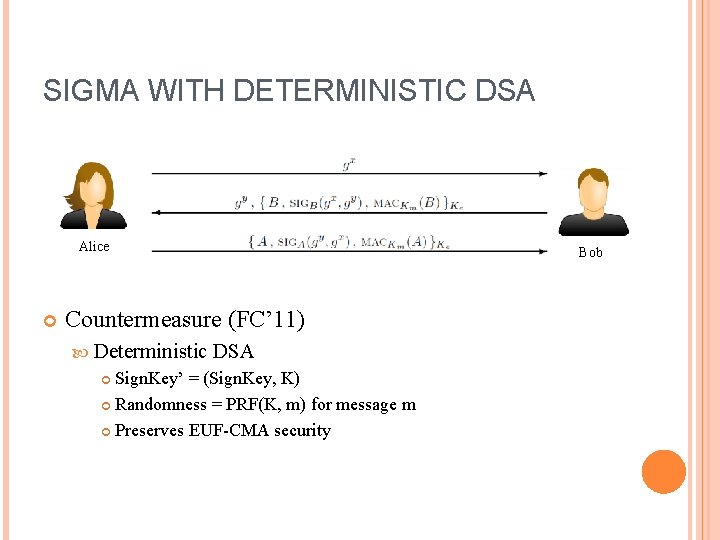
SIGMA WITH DETERMINISTIC DSA Alice Bob Countermeasure (FC’ 11) Deterministic DSA Sign. Key’ = (Sign. Key, K) Randomness = PRF(K, m) for message m Preserves EUF-CMA security
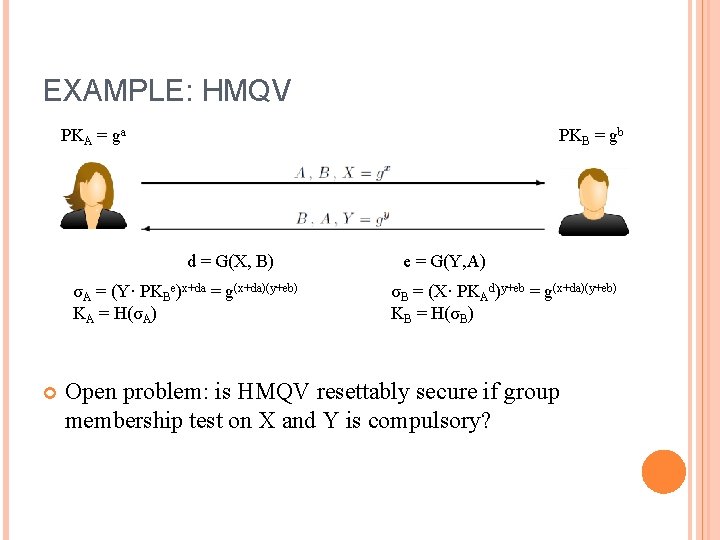
EXAMPLE: HMQV PKA = ga PKB = gb d = G(X, B) σA = (Y· PKBe)x+da = g(x+da)(y+eb) KA = H(σA) e = G(Y, A) σB = (X· PKAd)y+eb = g(x+da)(y+eb) KB = H(σB) Open problem: is HMQV resettably secure if group membership test on X and Y is compulsory?
AKE UNDER BAD RANDOMNESS CASE 2: ADVERSARY-GENERATED RANDOMNESS
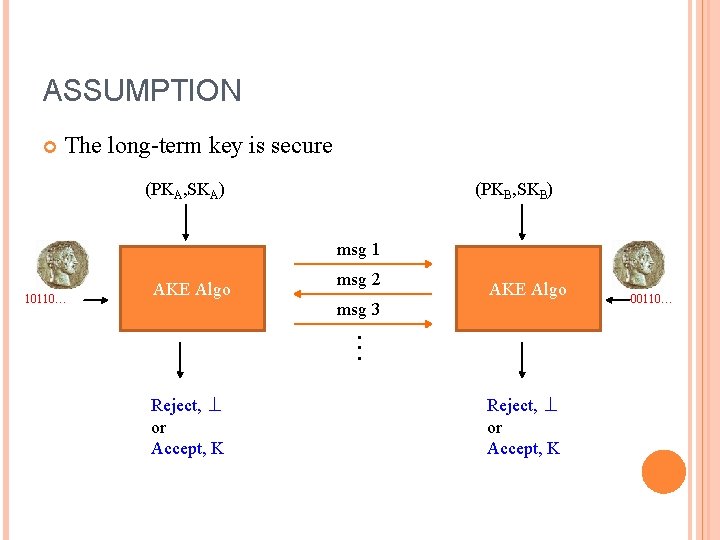
ASSUMPTION The long-term key is secure (PKA, SKA) (PKB, SKB) msg 1 10110… AKE Algo msg 2 AKE Algo msg 3 ··· Reject, ⊥ or Accept, K 00110…
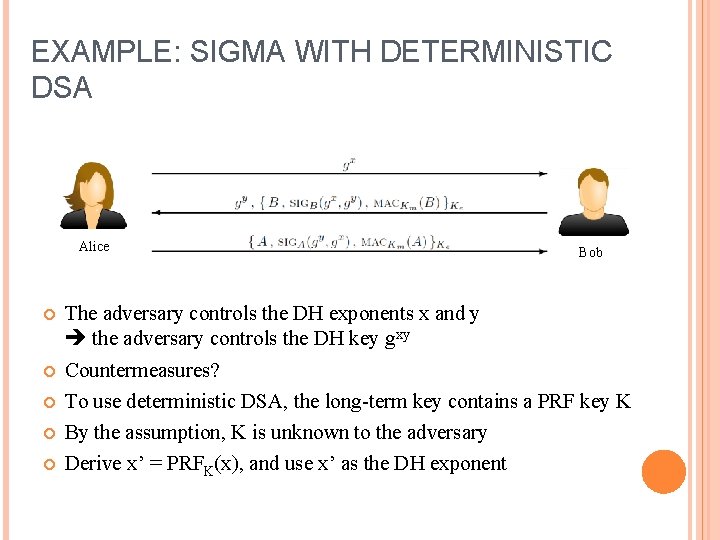
EXAMPLE: SIGMA WITH DETERMINISTIC DSA Alice Bob The adversary controls the DH exponents x and y the adversary controls the DH key gxy Countermeasures? To use deterministic DSA, the long-term key contains a PRF key K By the assumption, K is unknown to the adversary Derive x’ = PRFK(x), and use x’ as the DH exponent
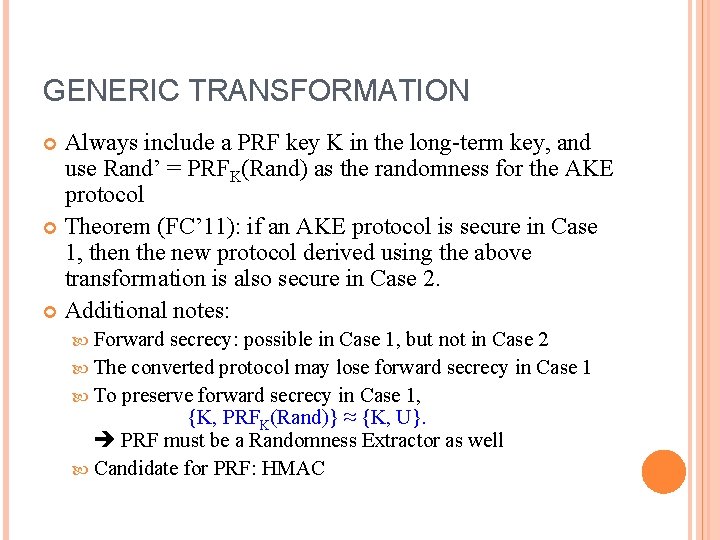
GENERIC TRANSFORMATION Always include a PRF key K in the long-term key, and use Rand’ = PRFK(Rand) as the randomness for the AKE protocol Theorem (FC’ 11): if an AKE protocol is secure in Case 1, then the new protocol derived using the above transformation is also secure in Case 2. Additional notes: Forward secrecy: possible in Case 1, but not in Case 2 The converted protocol may lose forward secrecy in Case 1 To preserve forward secrecy in Case 1, {K, PRFK(Rand)} ≈ {K, U}. PRF must be a Randomness Extractor as well Candidate for PRF: HMAC

SECURE ROAMING PROTOCOLS
SECURE ROAMING Roaming WLAN Telecommunication ATM/Credit …… Card
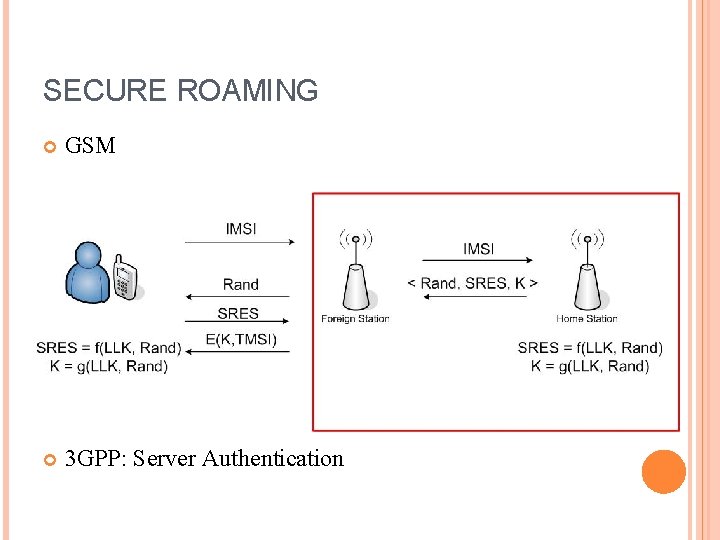
SECURE ROAMING GSM 3 GPP: Server Authentication
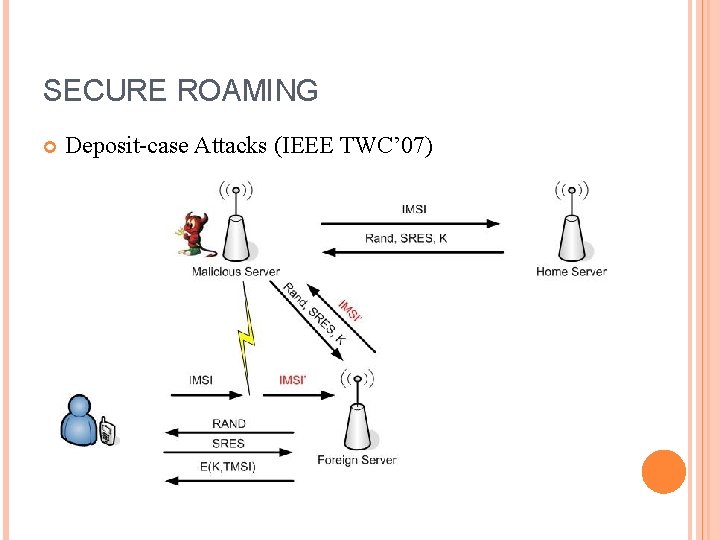
SECURE ROAMING Deposit-case Attacks (IEEE TWC’ 07)
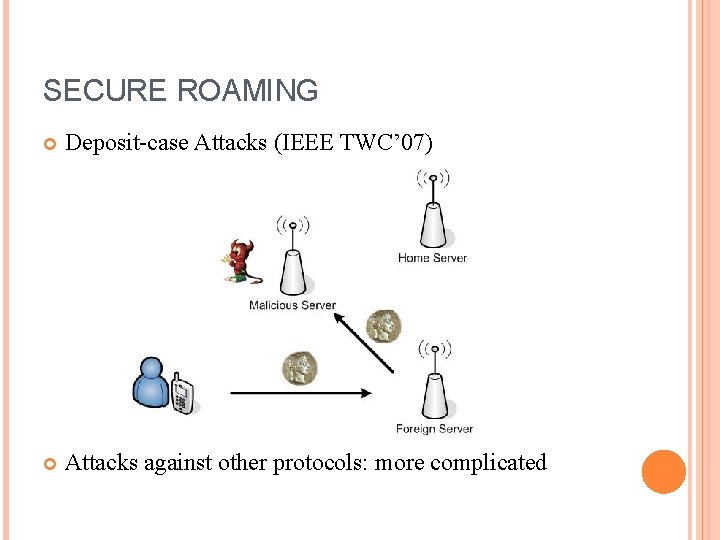
SECURE ROAMING Deposit-case Attacks (IEEE TWC’ 07) Attacks against other protocols: more complicated
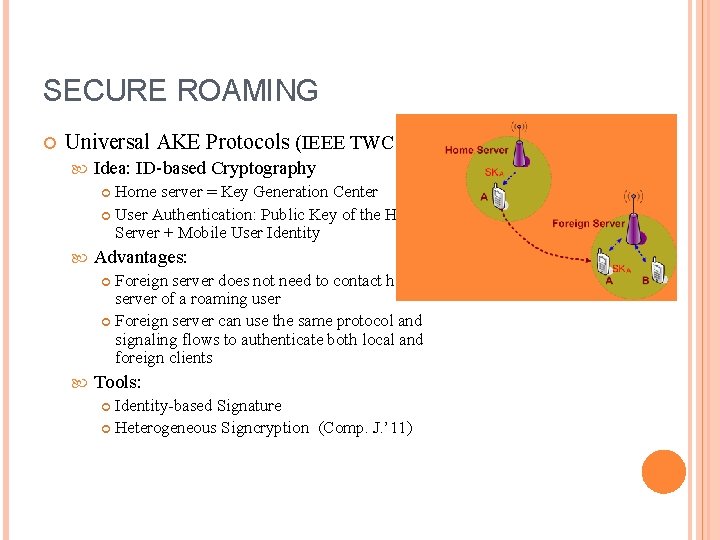
SECURE ROAMING Universal AKE Protocols (IEEE TWC’ 10) Idea: ID-based Cryptography Home server = Key Generation Center User Authentication: Public Key of the Home Server + Mobile User Identity Advantages: Foreign server does not need to contact home server of a roaming user Foreign server can use the same protocol and signaling flows to authenticate both local and foreign clients Tools: Identity-based Signature Heterogeneous Signcryption (Comp. J. ’ 11)
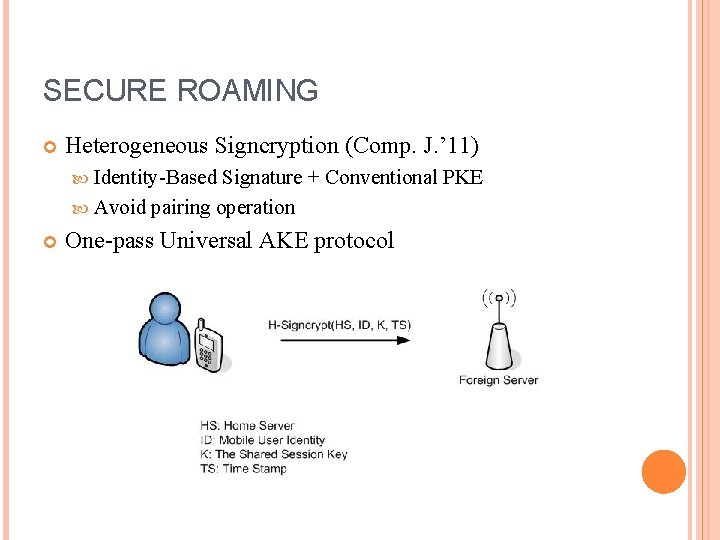
SECURE ROAMING Heterogeneous Signcryption (Comp. J. ’ 11) Identity-Based Signature + Conventional PKE Avoid pairing operation One-pass Universal AKE protocol
OTHER AKE PROTOCOLS
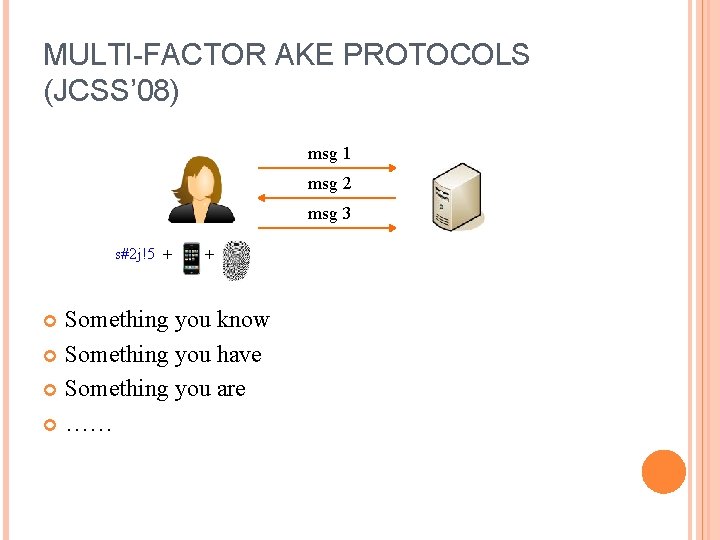
MULTI-FACTOR AKE PROTOCOLS (JCSS’ 08) msg 1 msg 2 msg 3 s#2 j!5 + + Something you know Something you have Something you are ……
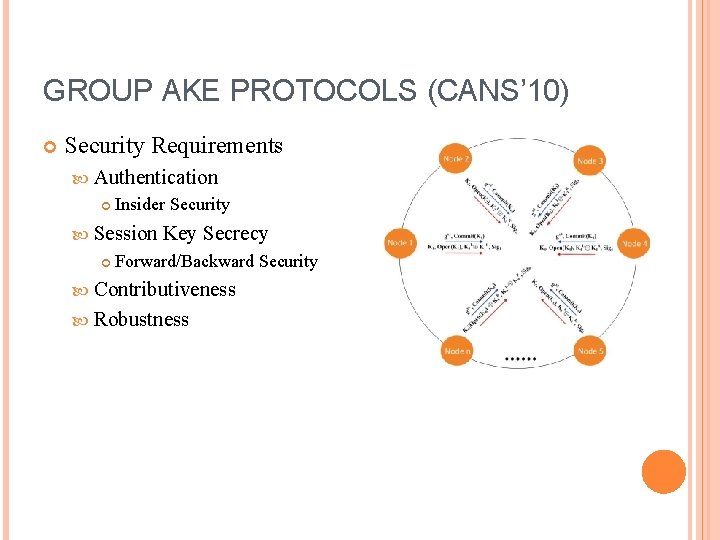
GROUP AKE PROTOCOLS (CANS’ 10) Security Requirements Authentication Insider Security Session Key Secrecy Forward/Backward Security Contributiveness Robustness

THANK YOU EMAIL: TSLYG@NUS. EDU. SG
- Slides: 39