COM 1032 MOBILE COMPUTING 20190 Lecture 7 IO
COM 1032: MOBILE COMPUTING 2019/0 Lecture 7 I/O Management And Disk Scheduling & File Management Dr. Manal Helal
Learning Outcomes Attributes Developed 001 I/O Function KC 002 Buffering KC 003 File Management KPTC 004 Sharing and Synchronisation KPTC Attributes Developed C - Cognitive/analytical K - Subject knowledge T - Transferable skills P - Professional/Practical skills
Outline § § § I/O Functions: – Direct Memory Access – I/O Buffering – Use Cases: Windows, Unix Files, Directories structures and management: – File Sharing – Record Blocking – Secondary Storage – Use Cases: Windows, Unix, Android Further Learning: Android Things – Raspberry PI 3 – Google Android Device Kit (ADK) robots - Smart Home and sensor network applications
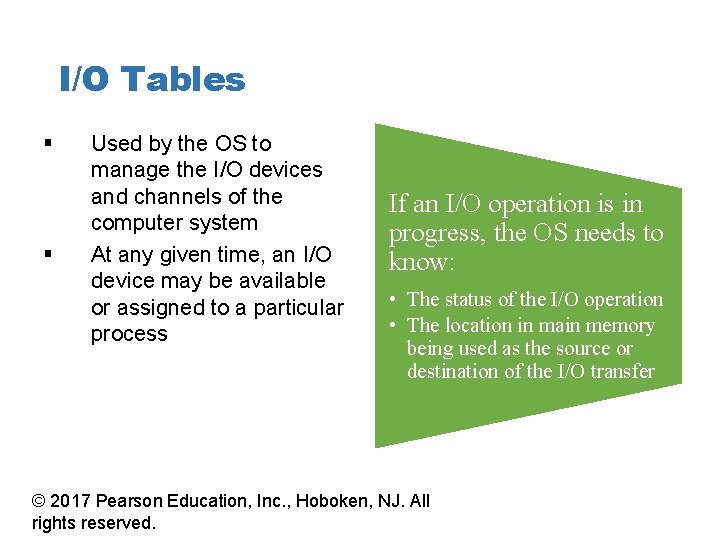
I/O Tables § § Used by the OS to manage the I/O devices and channels of the computer system At any given time, an I/O device may be available or assigned to a particular process If an I/O operation is in progress, the OS needs to know: • The status of the I/O operation • The location in main memory being used as the source or destination of the I/O transfer © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
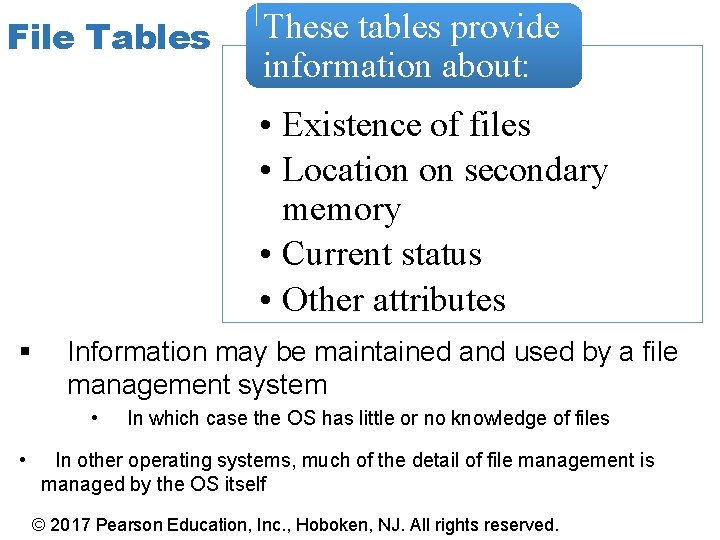
File Tables These tables provide information about: • Existence of files • Location on secondary memory • Current status • Other attributes § Information may be maintained and used by a file management system • • In which case the OS has little or no knowledge of files In other operating systems, much of the detail of file management is managed by the OS itself © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
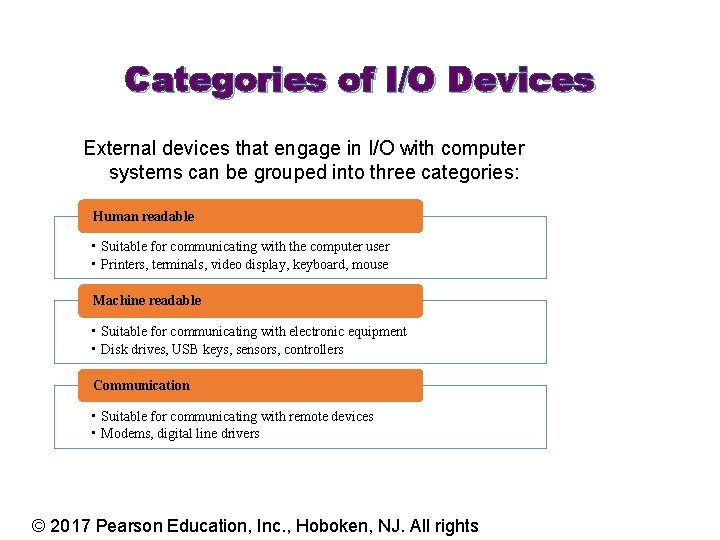
Categories of I/O Devices External devices that engage in I/O with computer systems can be grouped into three categories: Human readable • Suitable for communicating with the computer user • Printers, terminals, video display, keyboard, mouse Machine readable • Suitable for communicating with electronic equipment • Disk drives, USB keys, sensors, controllers Communication • Suitable for communicating with remote devices • Modems, digital line drivers © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights
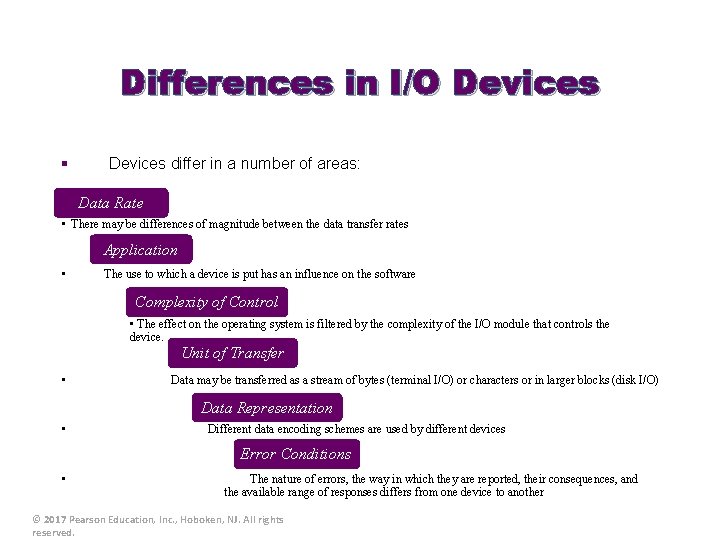
Differences in I/O Devices § Devices differ in a number of areas: Data Rate • There may be differences of magnitude between the data transfer rates Application • The use to which a device is put has an influence on the software Complexity of Control • The effect on the operating system is filtered by the complexity of the I/O module that controls the device. Unit of Transfer • Data may be transferred as a stream of bytes (terminal I/O) or characters or in larger blocks (disk I/O) Data Representation • Different data encoding schemes are used by different devices Error Conditions • The nature of errors, the way in which they are reported, their consequences, and the available range of responses differs from one device to another © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
© 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
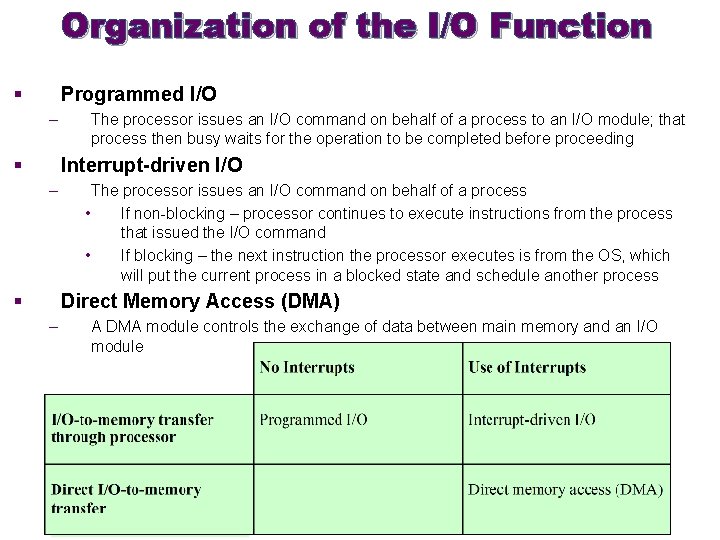
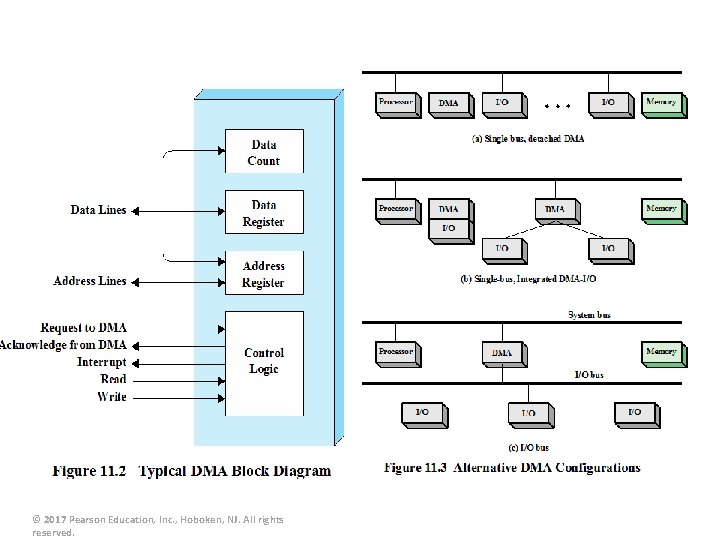
Organization of the I/O Function § Programmed I/O – § The processor issues an I/O command on behalf of a process to an I/O module; that process then busy waits for the operation to be completed before proceeding Interrupt-driven I/O – § The processor issues an I/O command on behalf of a process • If non-blocking – processor continues to execute instructions from the process that issued the I/O command • If blocking – the next instruction the processor executes is from the OS, which will put the current process in a blocked state and schedule another process Direct Memory Access (DMA) – A DMA module controls the exchange of data between main memory and an I/O module
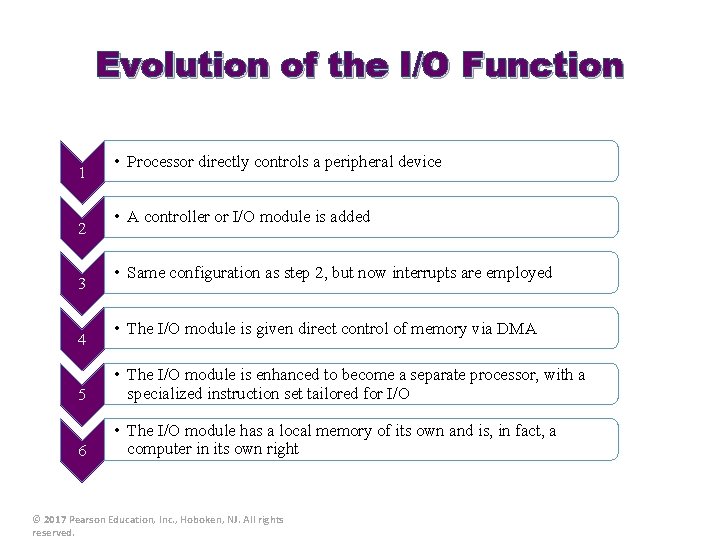
Evolution of the I/O Function 1 2 3 4 • Processor directly controls a peripheral device • A controller or I/O module is added • Same configuration as step 2, but now interrupts are employed • The I/O module is given direct control of memory via DMA 5 • The I/O module is enhanced to become a separate processor, with a specialized instruction set tailored for I/O 6 • The I/O module has a local memory of its own and is, in fact, a computer in its own right © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
© 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
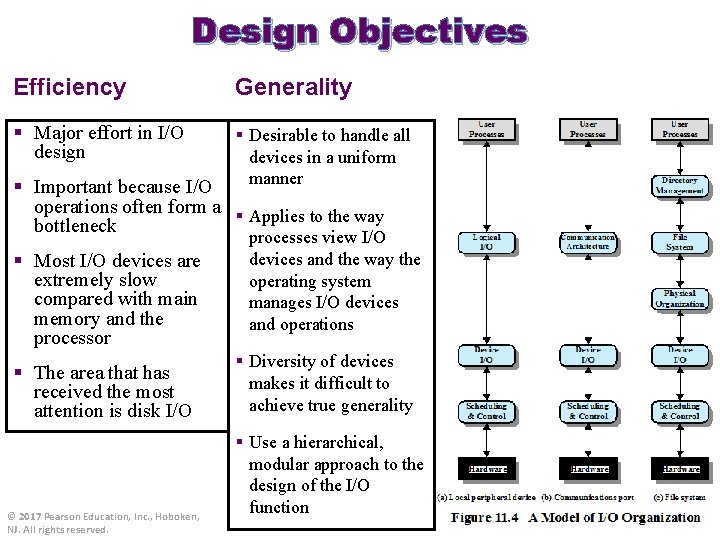
Design Objectives Efficiency Generality § Major effort in I/O design § Desirable to handle all devices in a uniform manner § Important because I/O operations often form a § Applies to the way bottleneck § Most I/O devices are extremely slow compared with main memory and the processor § The area that has received the most attention is disk I/O © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved. processes view I/O devices and the way the operating system manages I/O devices and operations § Diversity of devices makes it difficult to achieve true generality § Use a hierarchical, modular approach to the design of the I/O function
Outline § § § I/O Functions: – Direct Memory Access – I/O Buffering – Use Cases: Windows, Unix Files, Directories structures and management: – File Sharing – Record Blocking – Secondary Storage – Use Cases: Windows, Unix, Android Further Learning: Android Things – Raspberry PI 3 – Google Android Device Kit (ADK) robots - Smart Home and sensor network applications
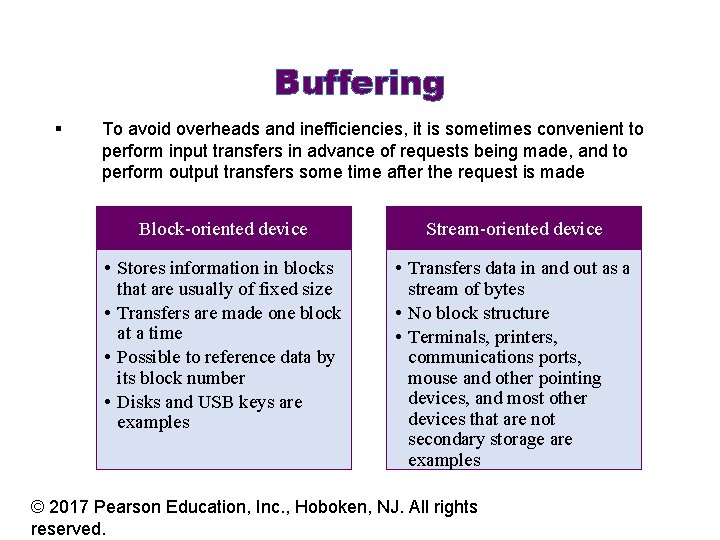
Buffering § To avoid overheads and inefficiencies, it is sometimes convenient to perform input transfers in advance of requests being made, and to perform output transfers some time after the request is made Block-oriented device Stream-oriented device • Stores information in blocks that are usually of fixed size • Transfers are made one block at a time • Possible to reference data by its block number • Disks and USB keys are examples • Transfers data in and out as a stream of bytes • No block structure • Terminals, printers, communications ports, mouse and other pointing devices, and most other devices that are not secondary storage are examples © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
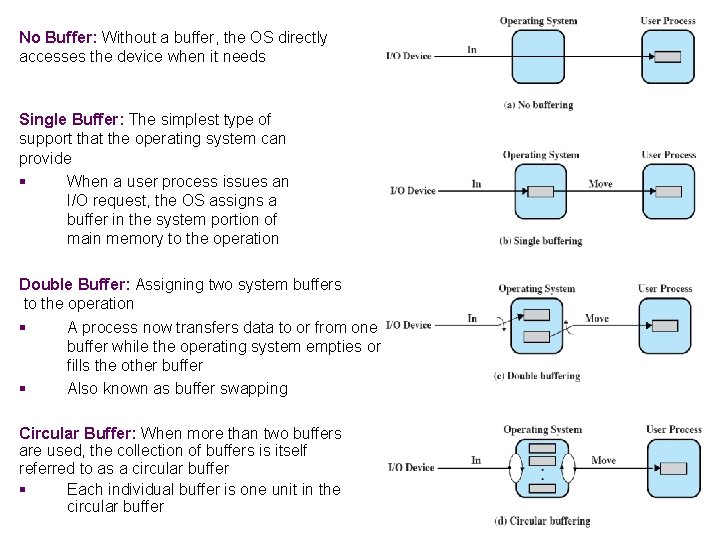
No Buffer: Without a buffer, the OS directly accesses the device when it needs Single Buffer: The simplest type of support that the operating system can provide § When a user process issues an I/O request, the OS assigns a buffer in the system portion of main memory to the operation Double Buffer: Assigning two system buffers to the operation § A process now transfers data to or from one buffer while the operating system empties or fills the other buffer § Also known as buffer swapping Circular Buffer: When more than two buffers are used, the collection of buffers is itself referred to as a circular buffer § Each individual buffer is one unit in the circular buffer
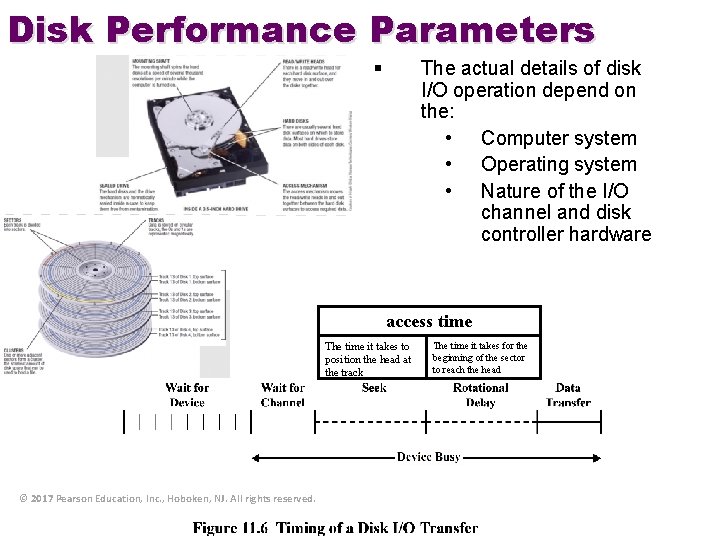
Disk Performance Parameters § The actual details of disk I/O operation depend on the: • Computer system • Operating system • Nature of the I/O channel and disk controller hardware access time The time it takes to position the head at the track © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved. The time it takes for the beginning of the sector to reach the head
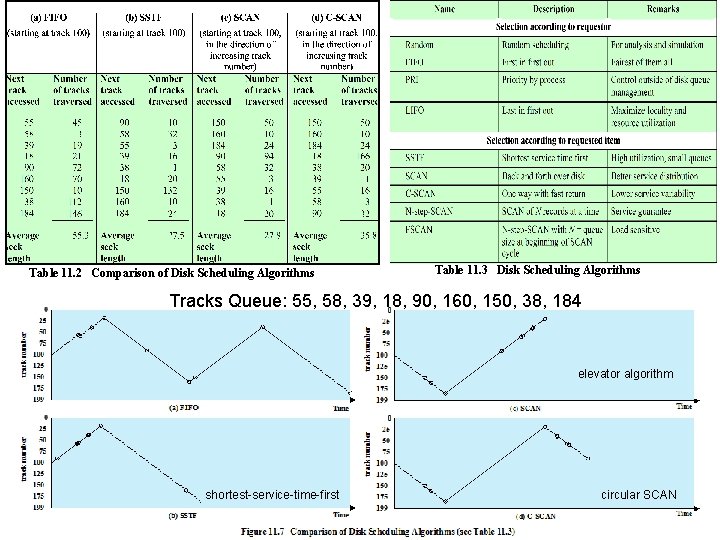
Table 11. 2 Comparison of Disk Scheduling Algorithms Table 11. 3 Disk Scheduling Algorithms Tracks Queue: 55, 58, 39, 18, 90, 160, 150, 38, 184 elevator algorithm shortest-service-time-first circular SCAN
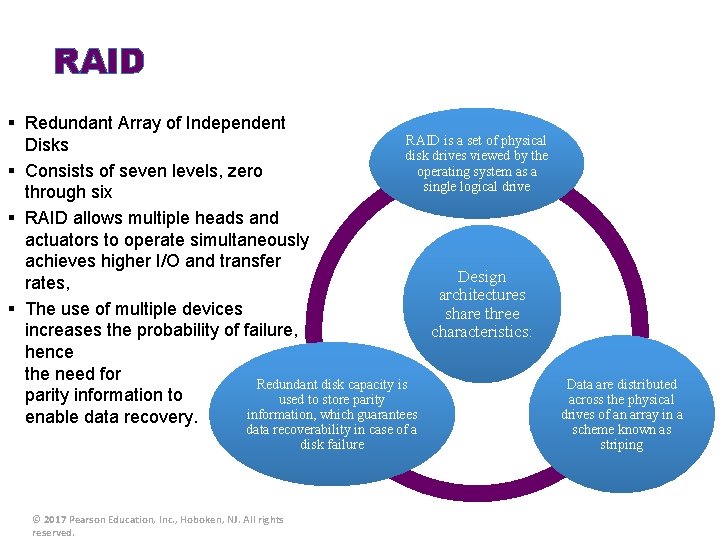
RAID § Redundant Array of Independent RAID is a set of physical Disks disk drives viewed by the operating system as a § Consists of seven levels, zero single logical drive through six § RAID allows multiple heads and actuators to operate simultaneously achieves higher I/O and transfer Design rates, architectures § The use of multiple devices share three increases the probability of failure, characteristics: hence the need for Redundant disk capacity is parity information to used to store parity information, which guarantees enable data recovery. data recoverability in case of a disk failure © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved. Data are distributed across the physical drives of an array in a scheme known as striping
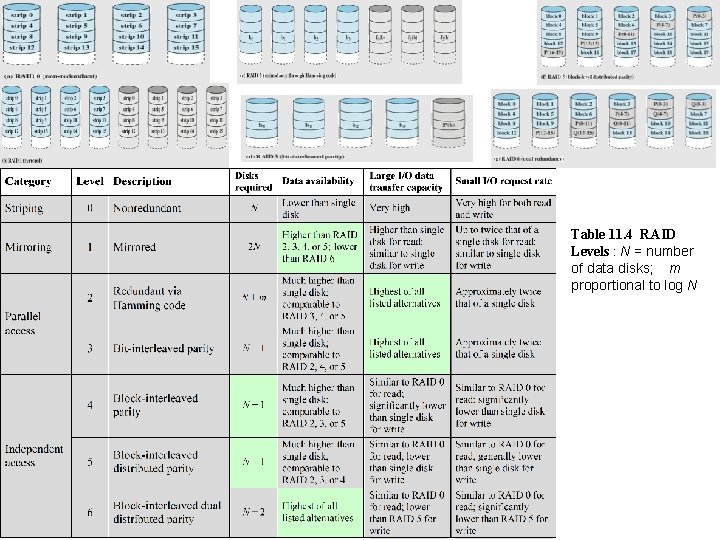
Table 11. 4 RAID Levels : N = number of data disks; m proportional to log N
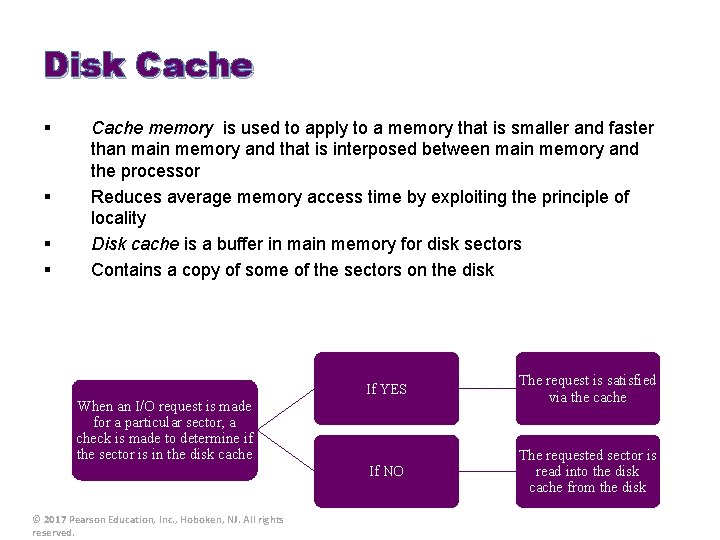
Disk Cache § § Cache memory is used to apply to a memory that is smaller and faster than main memory and that is interposed between main memory and the processor Reduces average memory access time by exploiting the principle of locality Disk cache is a buffer in main memory for disk sectors Contains a copy of some of the sectors on the disk If YES The request is satisfied via the cache If NO The requested sector is read into the disk cache from the disk When an I/O request is made for a particular sector, a check is made to determine if the sector is in the disk cache © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
Outline § § § I/O Functions: – Direct Memory Access – I/O Buffering – Use Cases: Windows, Unix Files, Directories structures and management: – File Sharing – Record Blocking – Secondary Storage – Use Cases: Windows, Unix, Android Further Learning: Android Things – Raspberry PI 3 – Google Android Device Kit (ADK) robots - Smart Home and sensor network applications
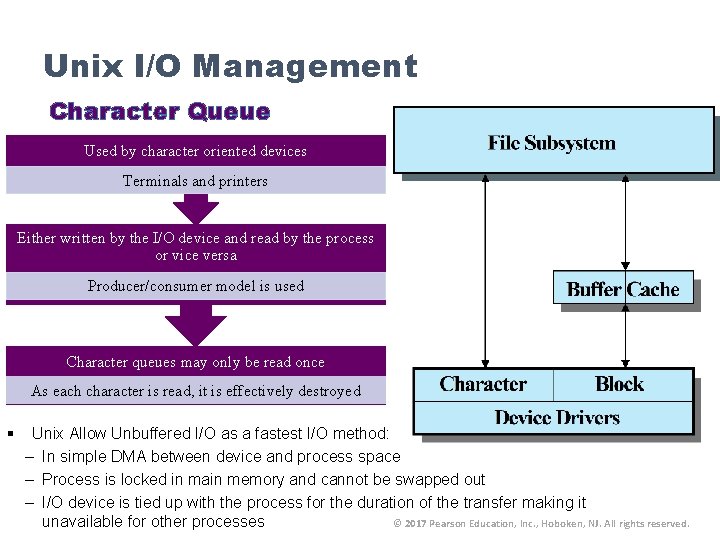
Unix I/O Management Character Queue Used by character oriented devices Terminals and printers Either written by the I/O device and read by the process or vice versa Producer/consumer model is used Character queues may only be read once As each character is read, it is effectively destroyed § Unix Allow Unbuffered I/O as a fastest I/O method: – In simple DMA between device and process space – Process is locked in main memory and cannot be swapped out – I/O device is tied up with the process for the duration of the transfer making it unavailable for other processes © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
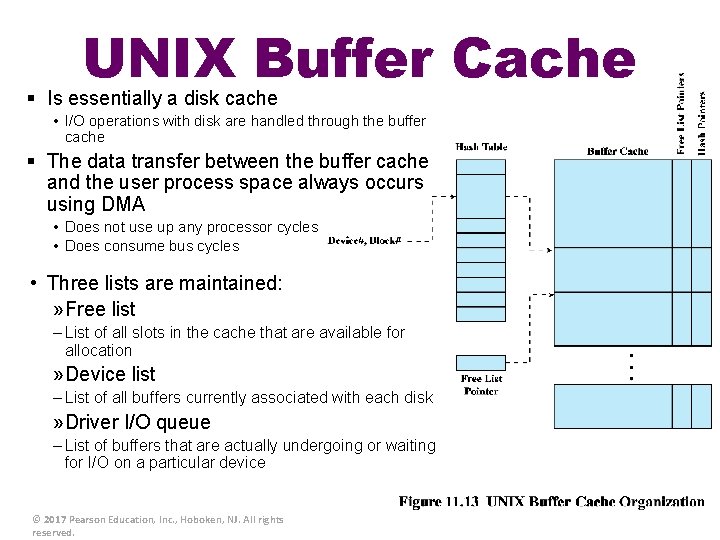
UNIX Buffer Cache § Is essentially a disk cache • I/O operations with disk are handled through the buffer cache § The data transfer between the buffer cache and the user process space always occurs using DMA • Does not use up any processor cycles • Does consume bus cycles • Three lists are maintained: » Free list – List of all slots in the cache that are available for allocation » Device list – List of all buffers currently associated with each disk » Driver I/O queue – List of buffers that are actually undergoing or waiting for I/O on a particular device © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
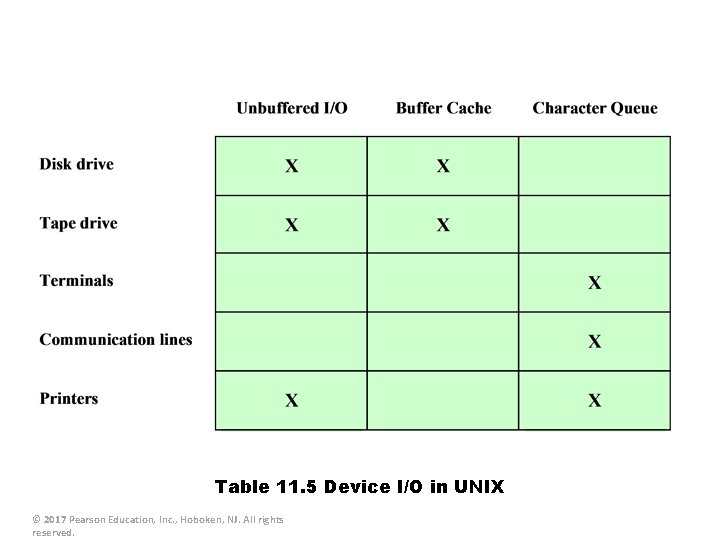
Table 11. 5 Device I/O in UNIX © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
Linux I/O § § Very similar to other UNIX implementation Associates a special file with each I/O device driver Block, character, and network devices are recognized Default disk scheduler in Linux 2. 4 is the Linux Elevator For Linux 2. 6 the Elevator algorithm has been augmented by two additional algorithms: • The deadline I/O scheduler • The anticipatory I/O scheduler © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
Completely Fair Queuing I/O Scheduler (CFQ) § § § Was developed in 2003 Is the default I/O scheduler in Linux The CFQ scheduler guarantees a fair allocation of the disk I/O bandwidth among all processes It maintains per process I/O queues • • • Each process is assigned a single queue Each queue has an allocated timeslice Requests are submitted into these queues and are processed in round robin When the scheduler services a specific queue, and there are no more requests in that queue, it waits in idle mode for a predefined time interval for new requests, and if there are no requests, it continues to the next queue © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
Linux Page Cache § § For Linux 2. 4 and later there is a single unified page cache for all traffic between disk and main memory Benefits: – When it is time to write back dirty pages to disk, a collection of them can be ordered properly and written out efficiently – Because of the principle of temporal locality, pages in the page cache are likely to be referenced again before they are flushed from the cache, thus saving a disk I/O operation © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
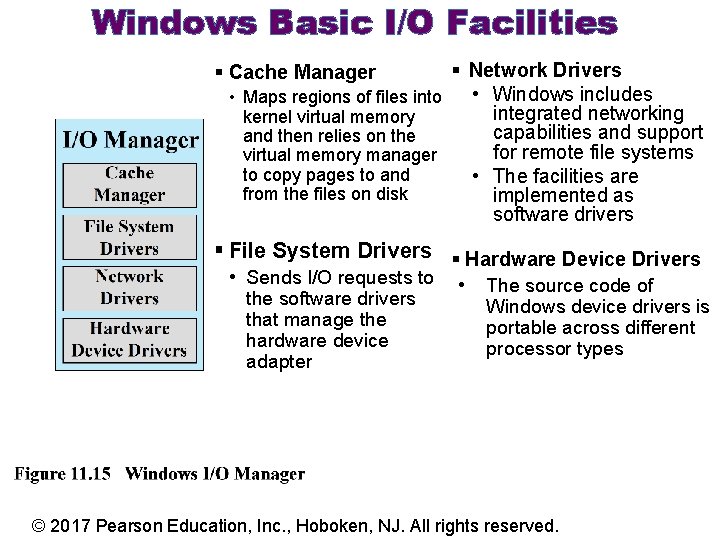
Windows Basic I/O Facilities § Network Drivers • Maps regions of files into • Windows includes integrated networking kernel virtual memory capabilities and support and then relies on the for remote file systems virtual memory manager to copy pages to and • The facilities are from the files on disk implemented as software drivers § Cache Manager § File System Drivers § Hardware Device Drivers • Sends I/O requests to • the software drivers that manage the hardware device adapter The source code of Windows device drivers is portable across different processor types © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
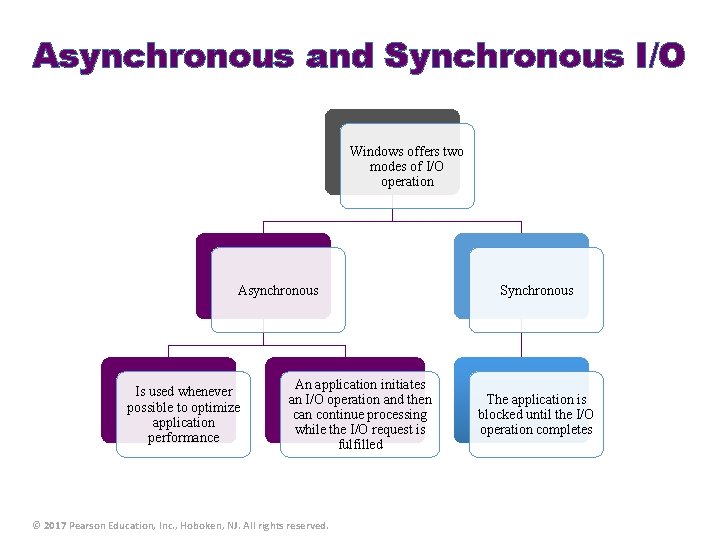
Asynchronous and Synchronous I/O Windows offers two modes of I/O operation Asynchronous Is used whenever possible to optimize application performance An application initiates an I/O operation and then can continue processing while the I/O request is fulfilled © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved. Synchronous The application is blocked until the I/O operation completes
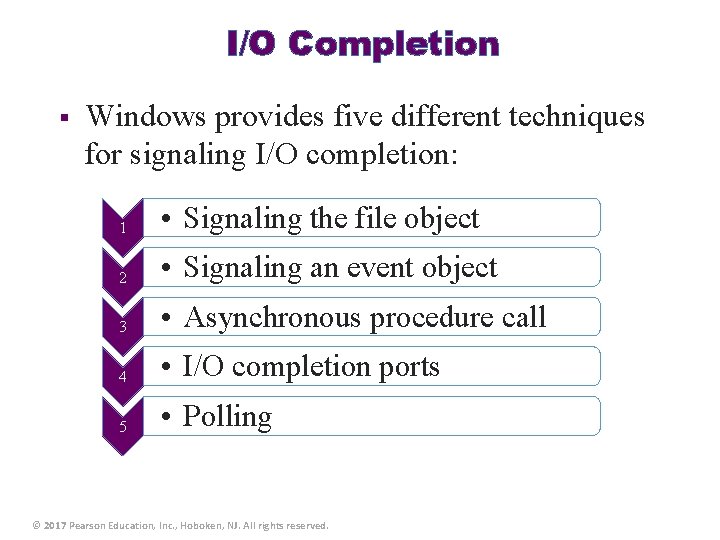
I/O Completion § Windows provides five different techniques for signaling I/O completion: 1 • Signaling the file object 2 • Signaling an event object 3 • Asynchronous procedure call 4 • I/O completion ports 5 • Polling © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
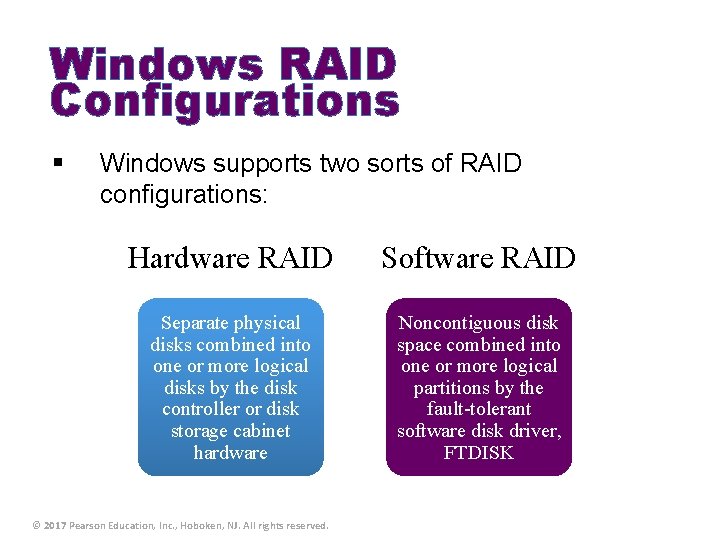
Windows RAID Configurations § Windows supports two sorts of RAID configurations: Hardware RAID Software RAID Separate physical disks combined into one or more logical disks by the disk controller or disk storage cabinet hardware Noncontiguous disk space combined into one or more logical partitions by the fault-tolerant software disk driver, FTDISK © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
Volume Shadow Copies and Volume Encryption § Volume Shadow Copies – – – Efficient way of making consistent snapshots of volumes so they can be backed up Also useful for archiving files on a per-volume basis Implemented by a software driver that makes copies of data on the volume before it is overwritten © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved. n Volume Encryption n Windows uses Bit. Locker to encrypt entire volumes n More secure than encrypting individual files n Allows multiple interlocking layers of security

Outline § § § I/O Functions: – Direct Memory Access – I/O Buffering – Use Cases: Windows, Unix Files, Directories structures and management: – File Sharing – Record Blocking – Secondary Storage – Use Cases: Windows, Unix, Android Further Learning: Android Things – Raspberry PI 3 – Google Android Device Kit (ADK) robots - Smart Home and sensor network applications
Files § § § Data collections created by users The File System is one of the most important parts of the OS to a user Desirable properties of files: Long-term existence • Files are stored on disk or other secondary storage and do not disappear when a user logs off Sharable between processes • Files have names and can have associated access permissions that permit controlled sharing Structure • Files can be organized into hierarchical or more complex structure to reflect the relationships among files © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
File Systems § § § Provide a means to store data organized as files as well as a collection of functions that can be performed on files Maintain a set of attributes associated with the file Typical operations include: – Create – Delete – Open – Close – Read – Write © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
Structure Terms Field • • • Basic element of data Contains a single value Fixed or variable length Record • • Database File • • Collection of similar records Treated as a single entity May be referenced by name Access control restrictions usually apply at the file level • • © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved. Collection of related fields that can be treated as a unit by some application program Fixed or variable length Collection of related data Relationships among elements of data are explicit Designed for use by a number of different applications Consists of one or more types of files
Minimal User Requirements § Each user: 1 2 3 4 5 6 • Should be able to create, delete, read, write and modify files • May have controlled access to other users’ files • May control what type of accesses are allowed to the users’ files • Should be able to move data between files • Should be able to back up and recover files in case of damage • Should be able to access his or her files by name rather than by numeric identifier © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
© 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
© 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
File Organization and Access § § § File organization is the logical structuring of the records as determined by the way in which they are accessed In choosing a file organization, several criteria are important: – Short access time – Ease of update – Economy of storage – Simple maintenance – Reliability Priority of criteria depends on the application that will use the file © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
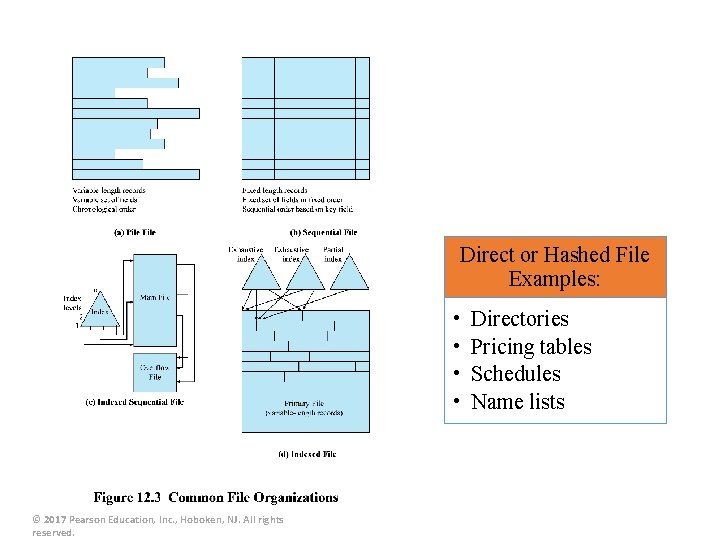
Direct or Hashed File Examples: • • © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved. Directories Pricing tables Schedules Name lists
B-Trees § § A balanced tree structure with all branches of equal length Standard method of organizing indexes for databases Commonly used in OS file systems Provides for efficient searching, adding, and deleting of items © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
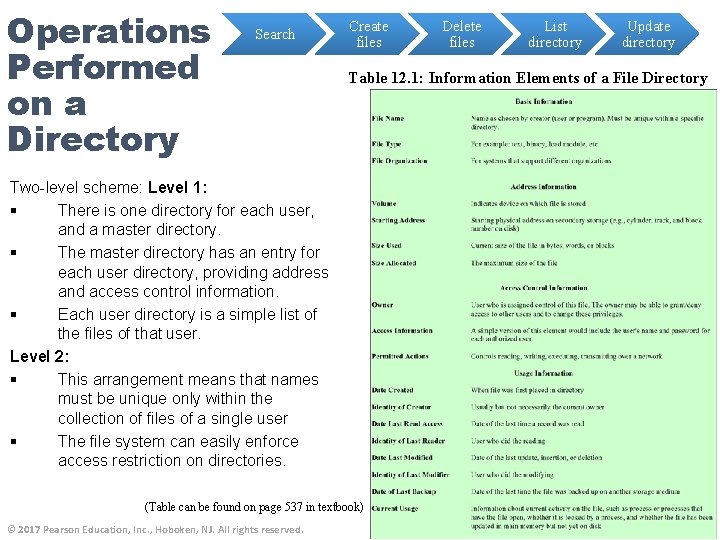
Operations Performed on a Directory Search Create files List directory Update directory Table 12. 1: Information Elements of a File Directory Two-level scheme: Level 1: § There is one directory for each user, and a master directory. § The master directory has an entry for each user directory, providing address and access control information. § Each user directory is a simple list of the files of that user. Level 2: § This arrangement means that names must be unique only within the collection of files of a single user § The file system can easily enforce access restriction on directories. (Table can be found on page 537 in textbook) © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved. Delete files

© 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
Outline § § § I/O Functions: – Direct Memory Access – I/O Buffering – Use Cases: Windows, Unix Files, Directories structures and management: – File Sharing – Record Blocking – Secondary Storage – Use Cases: Windows, Unix, Android Further Learning: Android Things – Raspberry PI 3 – Google Android Device Kit (ADK) robots - Smart Home and sensor network applications
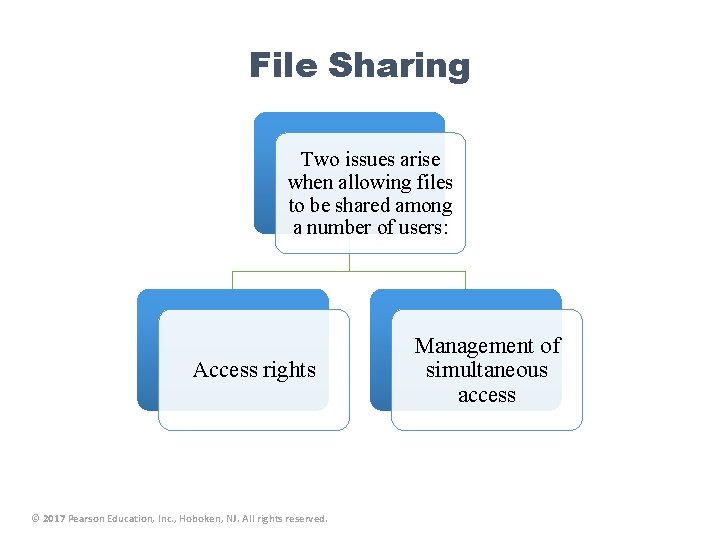
File Sharing Two issues arise when allowing files to be shared among a number of users: Access rights © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved. Management of simultaneous access
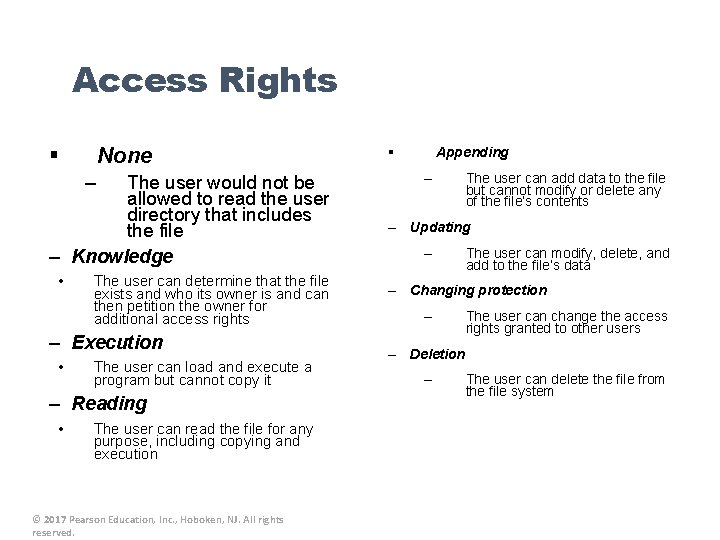
Access Rights § None – The user would not be allowed to read the user directory that includes the file – Knowledge • The user can determine that the file exists and who its owner is and can then petition the owner for additional access rights – Execution • The user can load and execute a program but cannot copy it – Reading • The user can read the file for any purpose, including copying and execution © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved. § Appending – The user can add data to the file but cannot modify or delete any of the file’s contents – Updating – The user can modify, delete, and add to the file’s data – Changing protection – The user can change the access rights granted to other users – Deletion – The user can delete the file from the file system
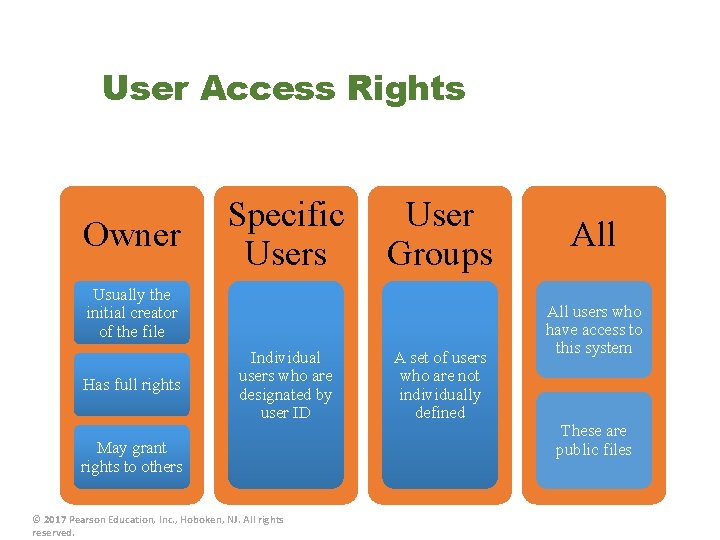
User Access Rights Owner Specific Users User Groups Usually the initial creator of the file Has full rights Individual users who are designated by user ID May grant rights to others © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved. A set of users who are not individually defined All users who have access to this system These are public files
k a e r B
Outline § § § I/O Functions: – Direct Memory Access – I/O Buffering – Use Cases: Windows, Unix Files, Directories structures and management: – File Sharing – Record Blocking – Secondary Storage – Use Cases: Windows, Unix, Android Further Learning: Android Things – Raspberry PI 3 – Google Android Device Kit (ADK) robots - Smart Home and sensor network applications
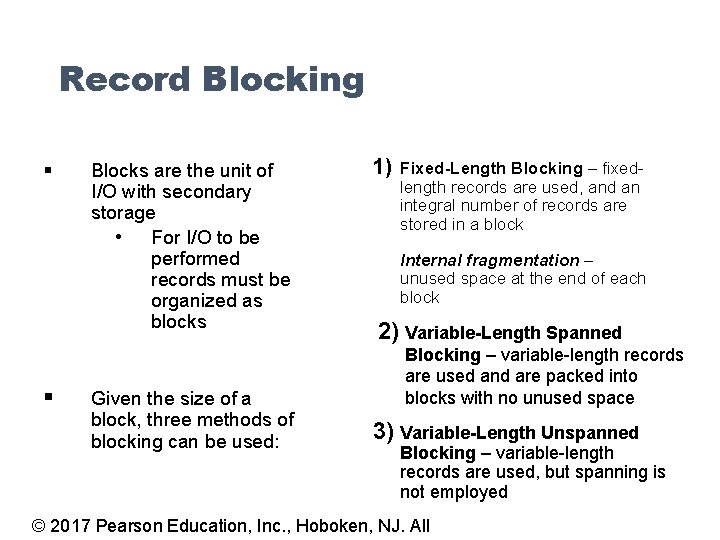
Record Blocking § § Blocks are the unit of I/O with secondary storage • For I/O to be performed records must be organized as blocks Given the size of a block, three methods of blocking can be used: 1) Fixed-Length Blocking – fixedlength records are used, and an integral number of records are stored in a block Internal fragmentation – unused space at the end of each block 2) Variable-Length Spanned Blocking – variable-length records are used and are packed into blocks with no unused space 3) Variable-Length Unspanned Blocking – variable-length records are used, but spanning is not employed © 2017 Pearson Education, Inc. , Hoboken, NJ. All
© 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
Outline § § § I/O Functions: – Direct Memory Access – I/O Buffering – Use Cases: Windows, Unix Files, Directories structures and management: – File Sharing – Record Blocking – Secondary Storage – Use Cases: Windows, Unix, Android Further Learning: Android Things – Raspberry PI 3 – Google Android Device Kit (ADK) robots - Smart Home and sensor network applications
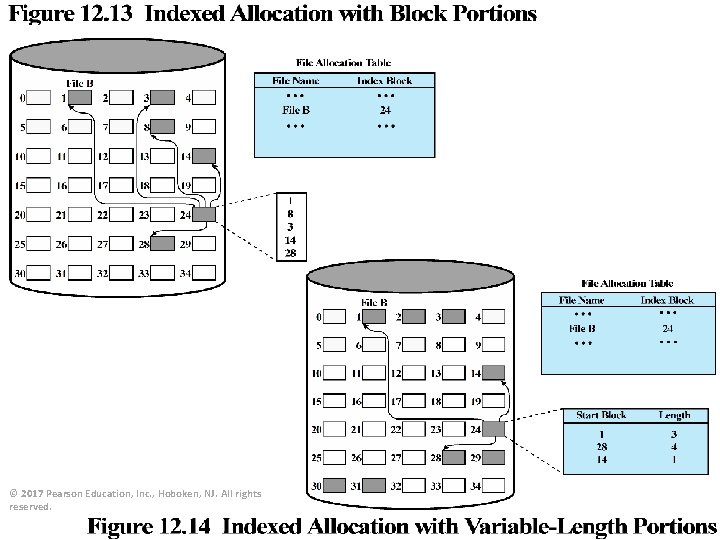
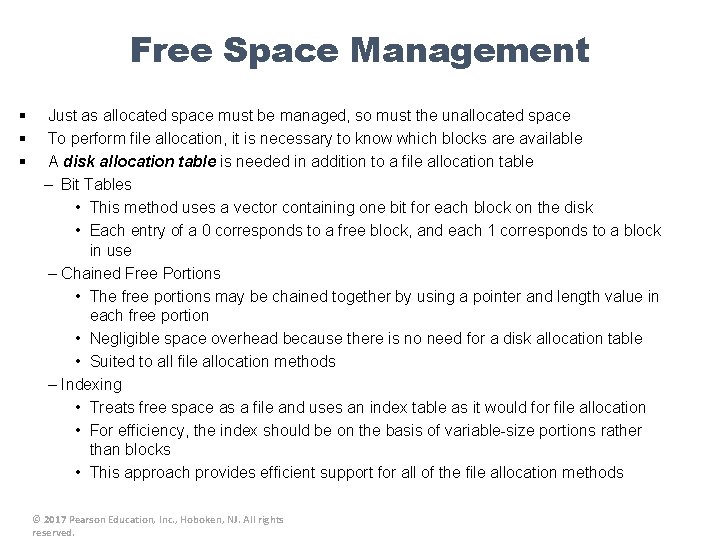
File Allocation § § § On secondary storage, a file consists of a collection of blocks The operating system or file management system is responsible for allocating blocks to files The approach taken for file allocation may influence the approach taken for free space management Space is allocated to a file as one or more portions (contiguous set of allocated blocks) File allocation table (FAT) § Data structure used to keep track of the portions assigned to a file © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
Preallocation vs Dynamic Allocation § § • A preallocation policy requires that the maximum size of a file be declared at the time of the file creation request For many applications it is difficult to estimate reliably the maximum potential size of the file • Tends to be wasteful because users and application programmers tend to overestimate size Dynamic allocation allocates space to a file in portions as needed © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
Portion Size § § In choosing a portion size there is a trade-off between efficiency from the point of view of a single file versus overall system efficiency Items to be considered: 1) Contiguity of space increases performance, especially for Retrieve_Next operations, and greatly for transactions running in a transaction-oriented operating system 2) Having a large number of small portions increases the size of tables needed to manage the allocation information 3) Having fixed-size portions simplifies the reallocation of space 4) Having variable-size or small fixed-size portions minimizes waste of unused storage due to overallocation © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
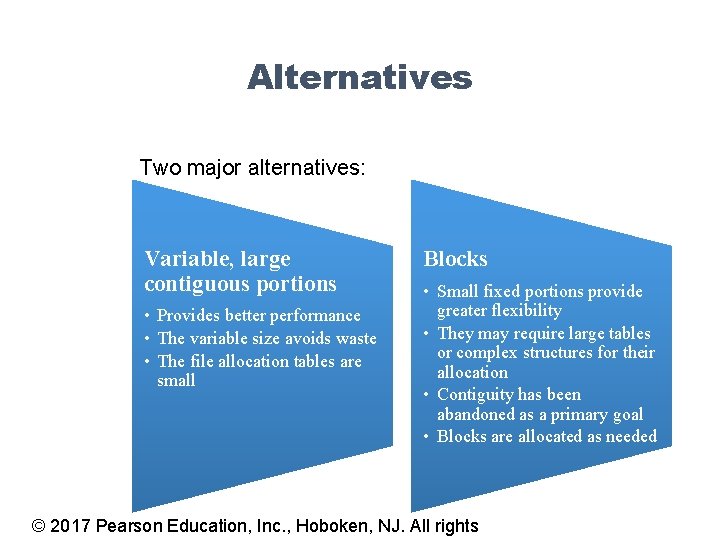
Alternatives Two major alternatives: Variable, large contiguous portions • Provides better performance • The variable size avoids waste • The file allocation tables are small Blocks • Small fixed portions provide greater flexibility • They may require large tables or complex structures for their allocation • Contiguity has been abandoned as a primary goal • Blocks are allocated as needed © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights
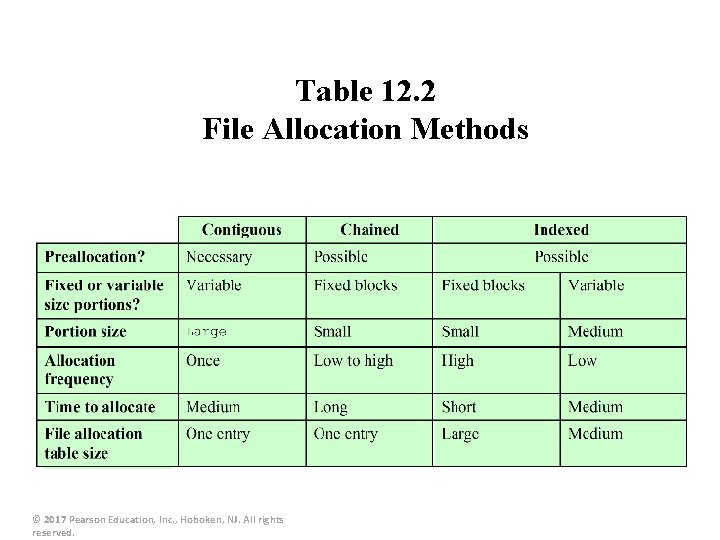
Table 12. 2 File Allocation Methods © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
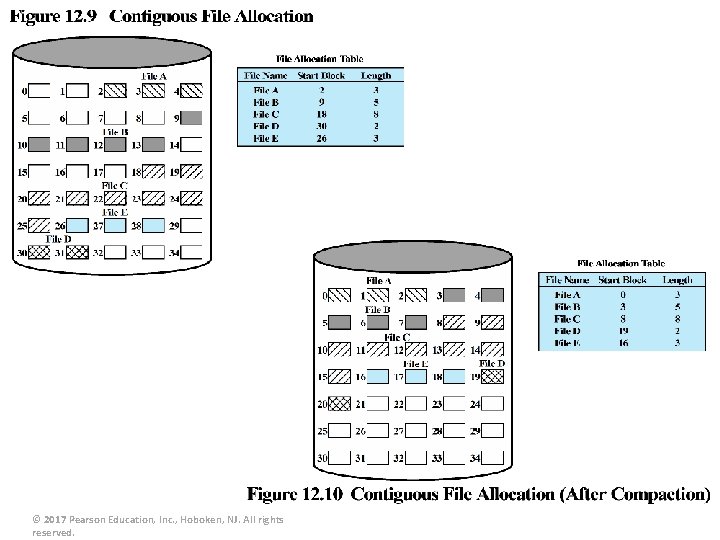
© 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
© 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
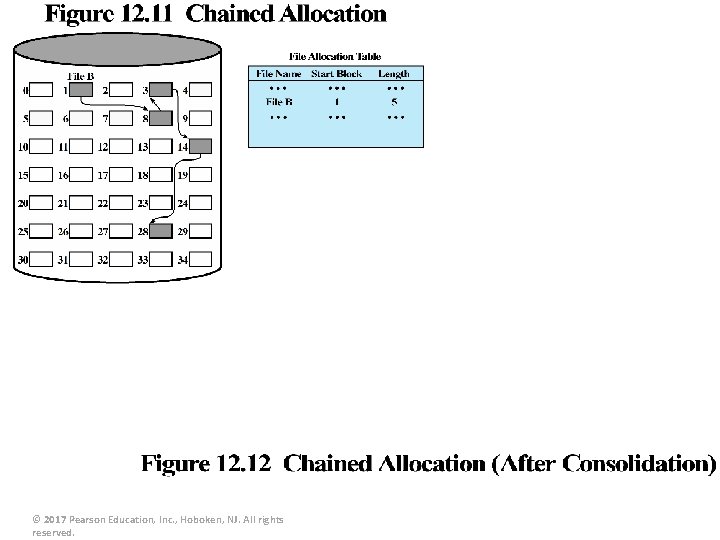
© 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
Free Space Management § § § Just as allocated space must be managed, so must the unallocated space To perform file allocation, it is necessary to know which blocks are available A disk allocation table is needed in addition to a file allocation table – Bit Tables • This method uses a vector containing one bit for each block on the disk • Each entry of a 0 corresponds to a free block, and each 1 corresponds to a block in use – Chained Free Portions • The free portions may be chained together by using a pointer and length value in each free portion • Negligible space overhead because there is no need for a disk allocation table • Suited to all file allocation methods – Indexing • Treats free space as a file and uses an index table as it would for file allocation • For efficiency, the index should be on the basis of variable-size portions rather than blocks • This approach provides efficient support for all of the file allocation methods © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
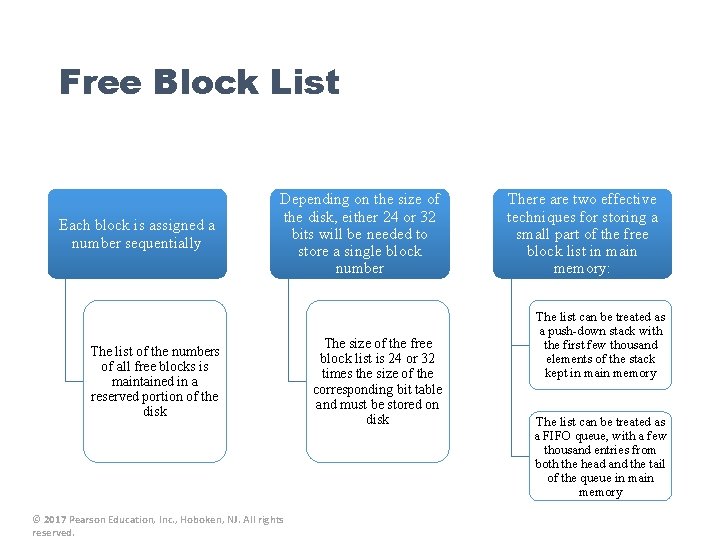
Free Block List Each block is assigned a number sequentially Depending on the size of the disk, either 24 or 32 bits will be needed to store a single block number The list of the numbers of all free blocks is maintained in a reserved portion of the disk © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved. The size of the free block list is 24 or 32 times the size of the corresponding bit table and must be stored on disk There are two effective techniques for storing a small part of the free block list in main memory: The list can be treated as a push-down stack with the first few thousand elements of the stack kept in main memory The list can be treated as a FIFO queue, with a few thousand entries from both the head and the tail of the queue in main memory
Volumes § § A collection of addressable sectors in secondary memory that an OS or application can use for data storage The sectors in a volume need not be consecutive on a physical storage device • § They need only appear that way to the OS or application A volume may be the result of assembling and merging smaller volumes © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
Outline § § § I/O Functions: – Direct Memory Access – I/O Buffering – Use Cases: Windows, Unix Files, Directories structures and management: – File Sharing – Record Blocking – Secondary Storage – Use Cases: Windows, Unix, Android Further Learning: Android Things – Raspberry PI 3 – Google Android Device Kit (ADK) robots - Smart Home and sensor network applications
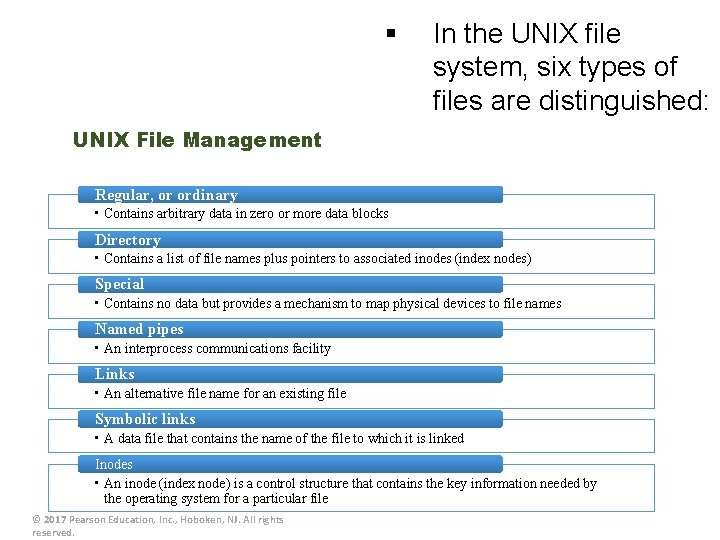
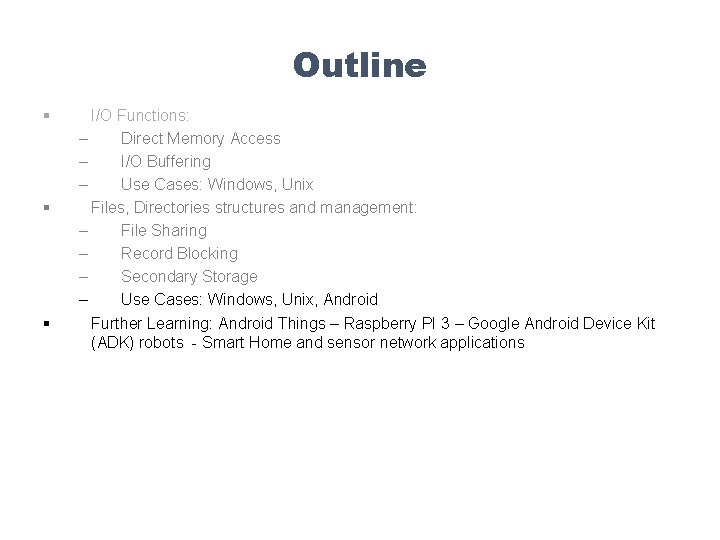
§ In the UNIX file system, six types of files are distinguished: UNIX File Management Regular, or ordinary • Contains arbitrary data in zero or more data blocks Directory • Contains a list of file names plus pointers to associated inodes (index nodes) Special • Contains no data but provides a mechanism to map physical devices to file names Named pipes • An interprocess communications facility Links • An alternative file name for an existing file Symbolic links • A data file that contains the name of the file to which it is linked Inodes • An inode (index node) is a control structure that contains the key information needed by the operating system for a particular file © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
© 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
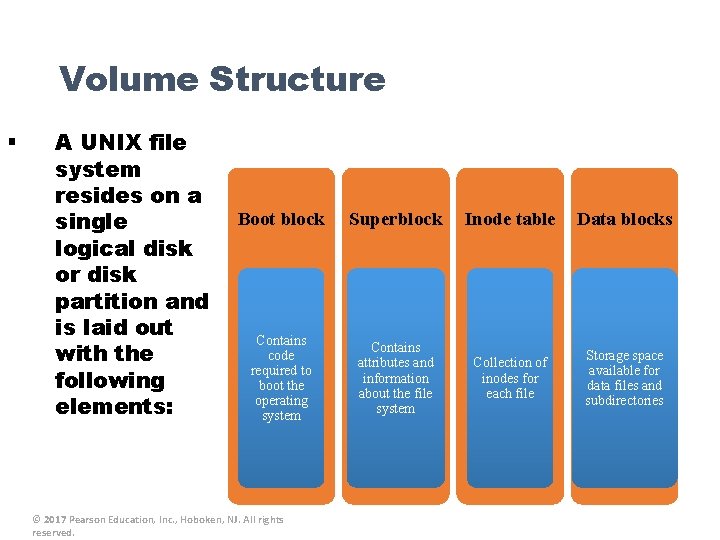
Volume Structure § A UNIX file system resides on a single logical disk or disk partition and is laid out with the following elements: Boot block Superblock Inode table Data blocks Contains code required to boot the operating system Contains attributes and information about the file system Collection of inodes for each file Storage space available for data files and subdirectories © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
© 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
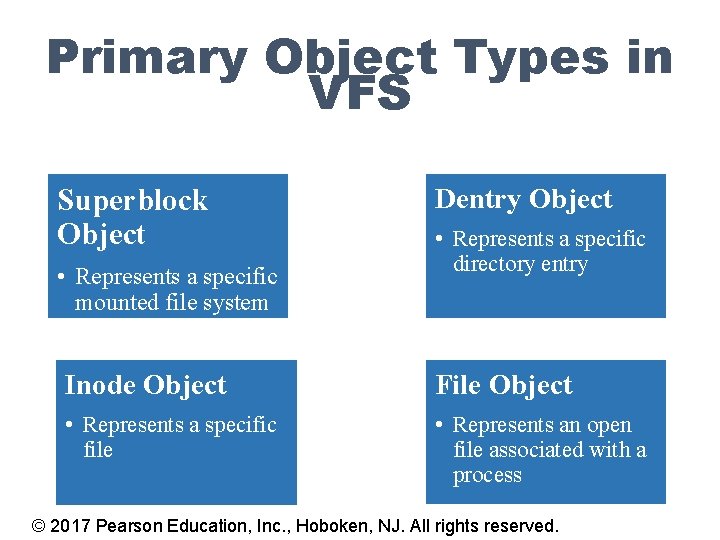
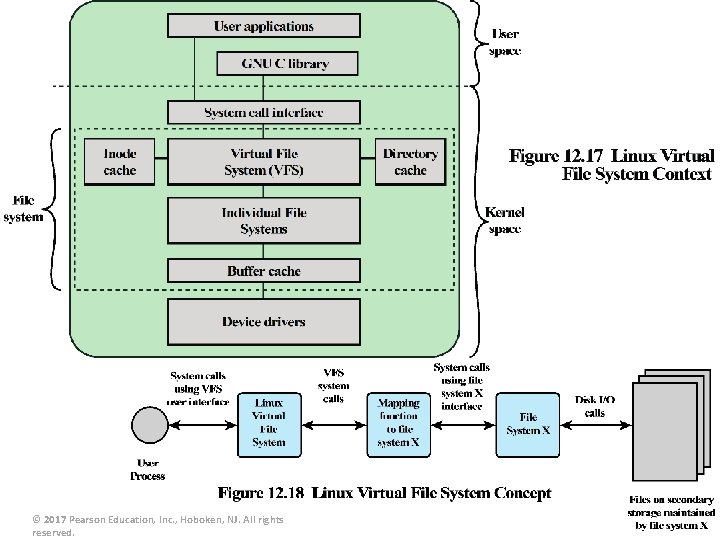
Primary Object Types in VFS Superblock Object • Represents a specific mounted file system Dentry Object • Represents a specific directory entry Inode Object File Object • Represents a specific file • Represents an open file associated with a process © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
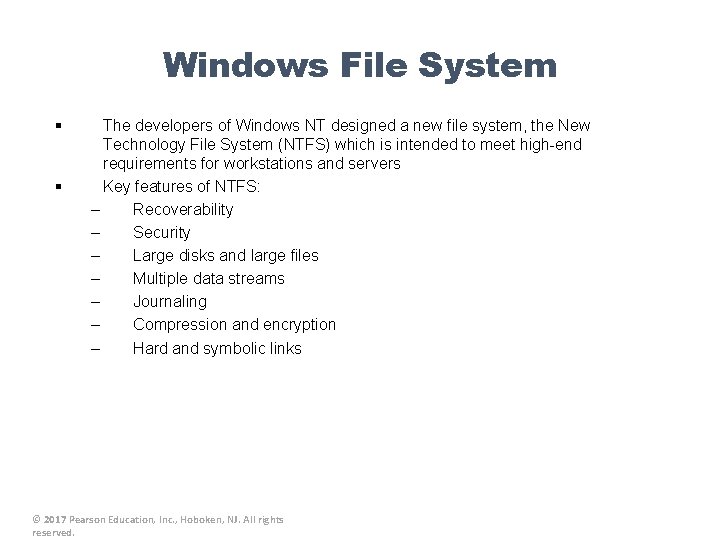
Windows File System § § The developers of Windows NT designed a new file system, the New Technology File System (NTFS) which is intended to meet high-end requirements for workstations and servers Key features of NTFS: – Recoverability – Security – Large disks and large files – Multiple data streams – Journaling – Compression and encryption – Hard and symbolic links © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
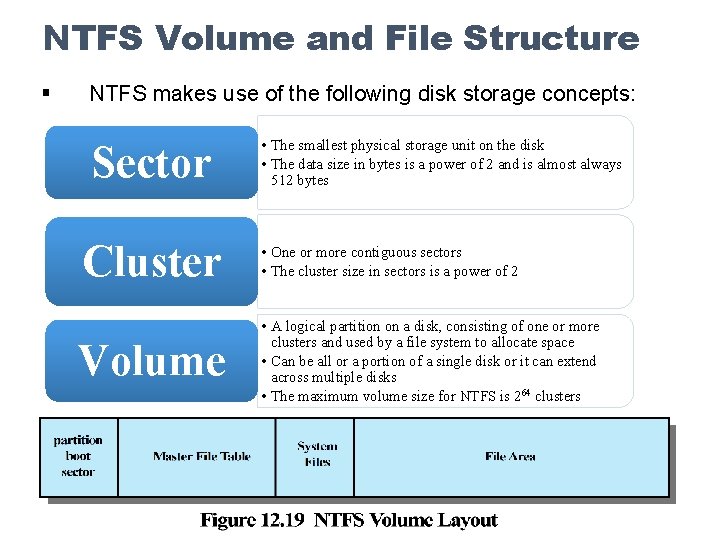
NTFS Volume and File Structure § NTFS makes use of the following disk storage concepts: Sector • The smallest physical storage unit on the disk • The data size in bytes is a power of 2 and is almost always 512 bytes Cluster • One or more contiguous sectors • The cluster size in sectors is a power of 2 Volume • A logical partition on a disk, consisting of one or more clusters and used by a file system to allocate space • Can be all or a portion of a single disk or it can extend across multiple disks • The maximum volume size for NTFS is 264 clusters
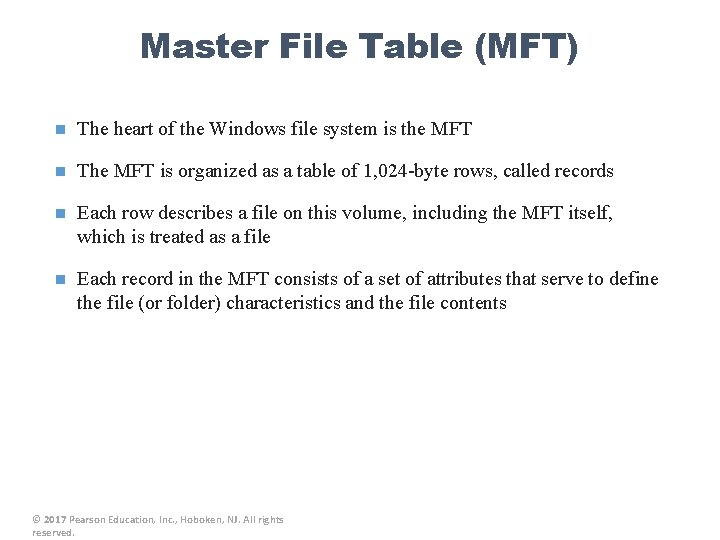
Master File Table (MFT) n The heart of the Windows file system is the MFT n The MFT is organized as a table of 1, 024 -byte rows, called records n Each row describes a file on this volume, including the MFT itself, which is treated as a file n Each record in the MFT consists of a set of attributes that serve to define the file (or folder) characteristics and the file contents © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
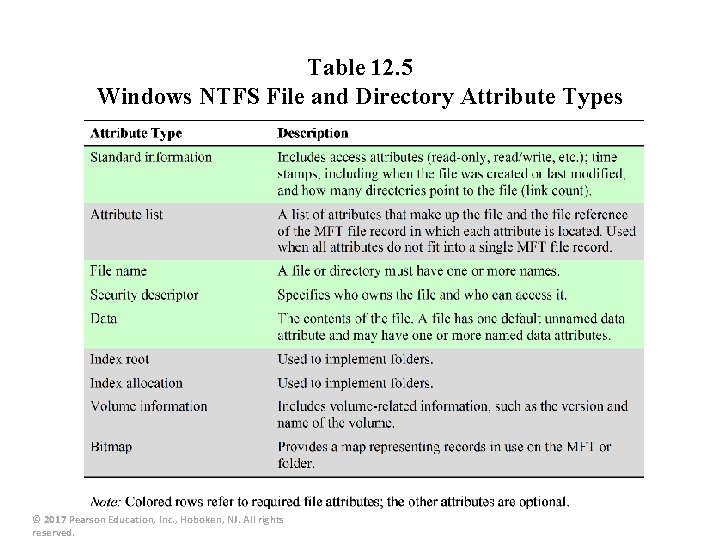
Table 12. 5 Windows NTFS File and Directory Attribute Types © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
© 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
© 2017 Pearson Education, Inc. , Hoboken, NJ. All rights reserved.
SQLite § § § Most widely deployed SQL database engine in the world Based on the Structured Query Language (SQL) Designed to provide a streamlined SQL-based database management system suitable for embedded systems and other limited memory systems The full SQLite library can be implemented in under 400 KB In contrast to other database management systems, SQLite is not a separate process that is accessed from the client application • The SQLite library is linked in, and thus becomes an integral part of the application program © 2017 Pearson Education, Inc. , Hoboken, NJ. All rights
Outline § § § I/O Functions: – Direct Memory Access – I/O Buffering – Use Cases: Windows, Unix Files, Directories structures and management: – File Sharing – Record Blocking – Secondary Storage – Use Cases: Windows, Unix, Android Further Learning: Android Things – Raspberry PI 3 – Google Android Device Kit (ADK) robots - Smart Home and sensor network applications
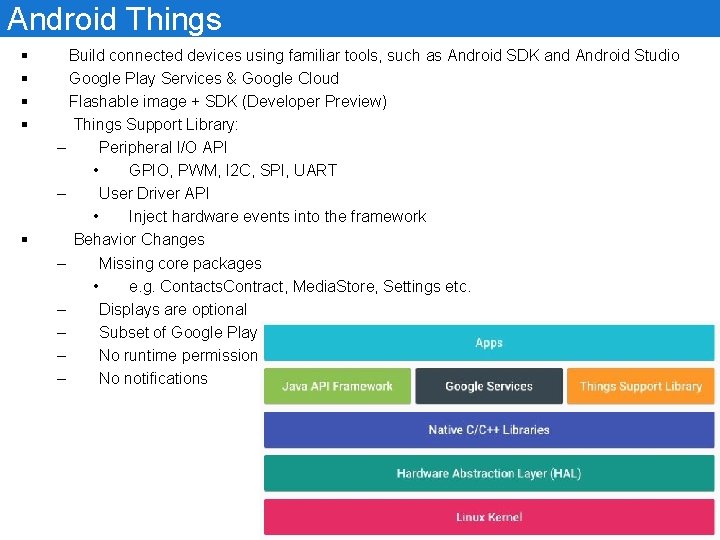
Android Things § § § Build connected devices using familiar tools, such as Android SDK and Android Studio Google Play Services & Google Cloud Flashable image + SDK (Developer Preview) Things Support Library: – Peripheral I/O API • GPIO, PWM, I 2 C, SPI, UART – User Driver API • Inject hardware events into the framework Behavior Changes – Missing core packages • e. g. Contacts. Contract, Media. Store, Settings etc. – Displays are optional – Subset of Google Play Services available – No runtime permissions – No notifications
Hardware § § § Certified development boards So. Ms (System-on-Modules) – So. C, RAM, Flash Storage, Wi. Fi, Bluetooth etc. Board Support Package (BSP) managed by Google Intel® Edison NXP Pico i. MX 6 UL Feb 2019: Google ‘refocuses’ Android Things as a platform for developing Smart Speakers and Displays, ends hardware support for Io. T devices https: //ausdroid. net/2019/02/13/google-refocuses-android-things-platform-developing-smartspeakers-displays-ends-hardware-support-iot-devices/ Raspberry Pi 3
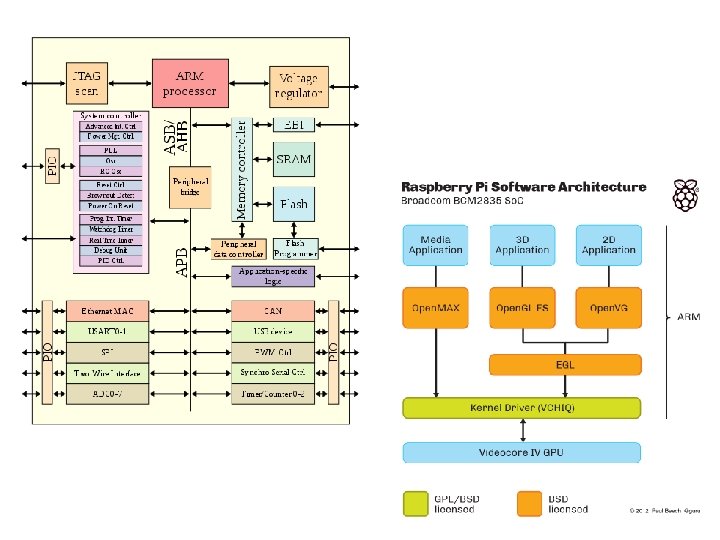
Raspbian OS § § § The original Raspberry Pi's CPU was based on ARMv 6. Raspbian is a Debian-based computer operating system for Raspberry Pi. There are several versions of Raspbian including Raspbian Stretch and Raspbian Jessie.
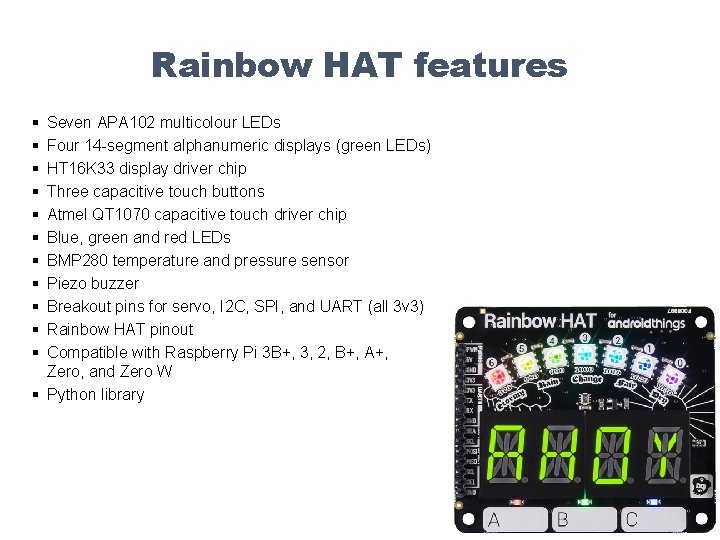
Rainbow HAT features § § § Seven APA 102 multicolour LEDs Four 14 -segment alphanumeric displays (green LEDs) HT 16 K 33 display driver chip Three capacitive touch buttons Atmel QT 1070 capacitive touch driver chip Blue, green and red LEDs BMP 280 temperature and pressure sensor Piezo buzzer Breakout pins for servo, I 2 C, SPI, and UART (all 3 v 3) Rainbow HAT pinout Compatible with Raspberry Pi 3 B+, 3, 2, B+, A+, Zero, and Zero W § Python library
Deep Learning on Raspberry Pi § The workflow for Deep Learning: 1. Gathering Training Data Using Raspberry Pi’ s Camera 2. Training the model using Tensor Flow installed on Raspberry Pi 3. Predictions on New Images captured by Raspberry Pi’ s Camera https: //medium. com/nanonets/how-to-easily-detect-objects-with-deep-learning-onraspberrypi-225 f 29635 c 74
Summary § § § § OS divides the memory spaces into kernel space and user space. Designing the OS to be as modular as possible to include the minimum functionality in the kernel space is preferred than the monolithic structure Process Management and scheduling is the major OS Functionality. Processes often spawns multiple threads of execution to benefit from concurrent simultaneous processing. Synchronization between processes and threads on shared resources is required. Memory Management is required to allocate for processes and threads requirements. Major Functionality include partitioning using paging and segmentation. I/O employ similar scheduling policies as used in process scheduling, and employs buffering cache as in cache memory and apply synchronization using producer/consumer model. File management using similar partitioning schemes in variable portions (such as segments in memory partitioning) and fixed block size (such as pages in memory partitioning), and employ disk caches and buffering as well.
- Slides: 88