Introduction Pervasive and Mobile Computing Defining Pervasive Computing
Introduction: Pervasive and Mobile Computing
Defining Pervasive Computing Make computing available beyond desktop q Make it mobile and connected q Instrument the person q Instrument the physical surroundings q
Scenario 1 (at home) q q At Sue and Mike’s home, 10 minutes before their alarm clock goes off (at 4: 00 AM), the coffee machine is automatically started. In making breakfast, Mike realizes that the egg supply is low. He adds eggs to the electronic shopping list. The refrigerator, scanning the barcode on the milk, realizes that it will soon expire. Milk gets added to the shopping list. Before leaving for work, Sue sees that she has a message reminding her that her driver’s license is soon to expire. Sue uses her computer with the video camera to get her picture taken and sent to the nearest office.
Scenario 1 (at home) q q Mike is diabetic. Mike uses a device that measures the glucose level and transmits this information to his doctor’s office. The doctor’s office keeps track of the measures and if the doctor is concerned about a trend observed in the measurements, the doctor’s office will send a message for Mike’s home asking for an appointment. If the problem is serious, then Mike’s dental appointment may be cancelled since treating the diabetes has high priority. If this happens, Mike’s personal electronic agent negotiates with the dental office-computing environment for an alternative time which gets put into Mike’s schedule.
Scenario 1 (Mike at work) q q q Mike works in an office tower for a company called Big Internet Company (Bi Co) which occupies floors 11 -21. There is a separate elevator that accesses these floors. Mike places his hand on the scanner near the elevator. The elevator has sensed Mike’s badge, passed that information to a computer that took a measurement of Mike’s hand, validated Mike and ordered the elevator to the ground floor.
Scenario 1 (Mike at work) q q q When Mike’s office senses that he is within 5 feet of his office door, it unlocks. The computer is already turned on, the printer turned on and a list of the day’s meetings and relevant background material is already printing. Let’s say Mike finds that he has a conference call with two colleagues in California and Toronto. Mike verbally orders the conference call: “Connect me with John Robinson and Tom Smith at 9”. The room picks up this information and passes it to the communication system to arrange for the call.
Scenario 1 (Mike at work) q q Mike’s badge beeps at 8: 55 indicating that his conference call is imminent. Mike returns to his office. Mike has his conference call at 9: 01. Just before 10 AM Mike heads to the Conference Room A to meet with his lead developers. On the way, Mike’s badge beeps and he sees that he has a message from a developer, Tom who is away at a conference. Mike opens his PDA and selects PRINTERS. He enters “Conference Room A” and three rooms near Room A appear with brief descriptions of printers. He selects one of the printers. The message from Tom is printed.
Scenario 1 (Mike at work) During Mike’s conference call, he writes on a whiteboard. q The contents of the whiteboard are transmitted to the other conference call participants and sent to Mike’s PC in his office. q The entire verbal dialog is recorded and stored. It can be retrieved if one of the conference call participants wishes to review the meeting in further detail. q
Scenario 1 (Mike at work) q q q After Mike’s meeting he spends the rest of the day quietly in his office doing work and reading news. Mike has the news delivered to him personalized. He is especially interested in sports and local politics. He started reading at home, but didn’t have time. During the day (at work) he finishes reading the news. Mike is working on sensitive documents. When he does leave the office (e. g. , lunch) his terminal automatically invokes a screen saver. Sue’s personalized news consist of national politics and technical stories.
Scenario 1 (Sue at work) Sue is a doctor who starts rounds at 6 AM. q When Sue gets to the hospital, she has the charts of patients downloaded to her PDA for immediate perusal. q During rounds she orders that a patient be given a new medication. q This gets sent to a computer in the hospital which may find that the supply of this medication is not enough. An order is automatically made to a pharmacy. q
Scenario 1 (Sue at work) q q q After rounds, Sue has a series of appointments and lectures to attend. She is not able to get to her PC for hours. She has been tracking several favorite stocks especially XYZ. Since she is busy she initializes her personalized financial advisor agent, Fred. Sue tells Fred that she wants to know if the price of XYZ reaches a certain point so that she may buy it. At 11: 17, Fred notifies her about XYZ.
Scenario 1 (Sue at work) Sue asks Fred to check to see if she has enough funds to cover for this. q If the answer is yes, Fred buys the stock and updates all of Sue’s accounts. q Sue leaves at 5. Before she leaves, she finds out that there has been a change in her schedule and she doesn’t start rounds until 7: 00 AM. q
Scenario 1 (Back at Home) q q q Sue cooks for relaxation. She feels like making a special dish for which she knows that she doesn’t have ingredients. She goes to a grocery store. She doesn’t remember all the ingredients so she asks her PDA to get the recipe from home and the current shopping list. Mike and Sue both arrive at home at 6: 00 PM. The home-computing environment greets them on arrival with a message for Mike telling him it is imperative for him to check his messages. Mike has the next day off and Sue gets to start a little later. They instruct the home-computing environment to set the alarm an hour later.
Scenario 2 Middlesex Building Pervasive Computing Environment q The application scenarios focus on users requesting building-related that can be accessed by their PDA, laptop or PC. q We will refer to this as Building Information Management (BIM). q
Scenario 2 q BIM Services for Resource Location o o o A user in a building is able to query for the location of rooms or nearest available resource (e. g. , nearest available workstation, printer). Maps and directions are provided to the user upon request. For example, Bob can request the location of the nearest printer (in Middlesex) that he is allowed access to. If needed, Bob could request a map or specific directions. Different maps and directions are returned based on Bob's location. Different users will have different requests
Scenario 2 q BIM Services for Activity Information o o A user can request information about activities in the building (e. g. , class , exam, meeting). Such a query should return a list of activities with room numbers. For example, upon entering Middlesex, Bob requests information on activities. Seeing the category for `final exam schedule', Bob asks for final exams taking place in the building at that time.
Scenario 2 q BIM Services for Status Information o o A user is able to request information about the status of a person within a building. For example, Bob can request information about Sue. The BIM should be able to tell Bob if Sue is busy or not. Sue is inferred to be busy if her location is in a meeting room or if she is working at a computer;
Scenario 2 q Other BIM Services o o A meeting causes the room to become warm. Temperature should be adjusted.
What do we need to support this? Lots of things. q We need a very complex and distributed infrastructure that has the following properties: q o o o Invisible from the user’s point of view. Adaptive Very dependable All devices are network enabled, although not all devices are connected all the time. Everywhere
Issues in Network Communications Mix of wireless and wired q A heterogeneous set of technologies will most likely be needed q Mobility brings its own sets of problems. q
Issues in Network Communications (Mobility) q Link Effects o o o Bandwidth is lower than the bandwidth provided by the wired network. The link between the base station and mobile host is not a reliable as links in a wired network (limits bandwidth) Need to be able to adapt content based on device and available bandwidth.
Issues in Network Communications (Mobility) q Link Effects (Continued) o o Remember Mike’s and Sue’s personalized news. The presentation of that news may vary depending not only on the type of device they are using to read the news, but also on the available bandwidth between the PDA and a base station. Let’s say Mike is driving while Sue is reading the news off her PDA. As Mike moves, the available bandwidth will change. How should the presentation change?
Issues in Network Communications (Mobility) q Constraints imposed by portable devices o o o User interface: little “real estate” Power management has an impact on the available computing resources available for the mobile device. Currently, it is not always desirable to have mobile devices always connected. This saves power, but results in problems related in intermittent connections (discussed in more detail later).
Issues in Network Communications (Mobility) q Dynamic information o The request for information sometimes depends on the location — — o Example: Where is the nearest gas station? Example: Where is the nearest Italian restaurant where the average meal is less than 30 dollars Canadian. The presentation of the information relies on the available computing resources. — Example: Text is used if available bandwidth is below some specified threshold else images may be used.
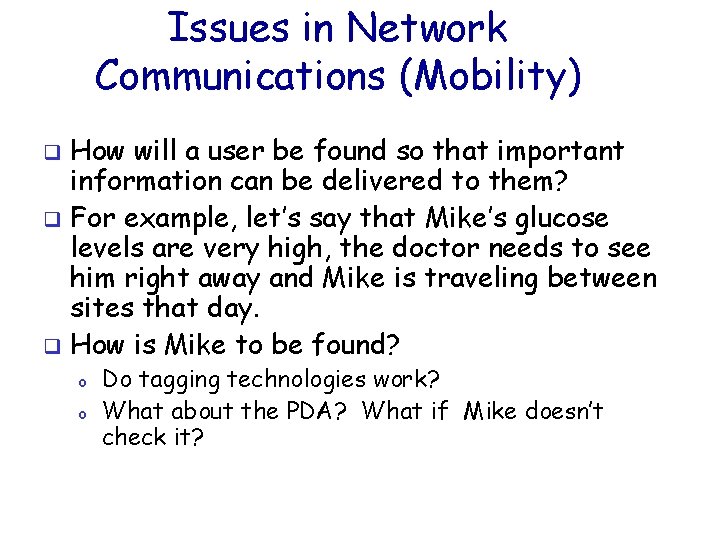
Issues in Network Communications (Mobility) How will a user be found so that important information can be delivered to them? q For example, let’s say that Mike’s glucose levels are very high, the doctor needs to see him right away and Mike is traveling between sites that day. q How is Mike to be found? q o o Do tagging technologies work? What about the PDA? What if Mike doesn’t check it?
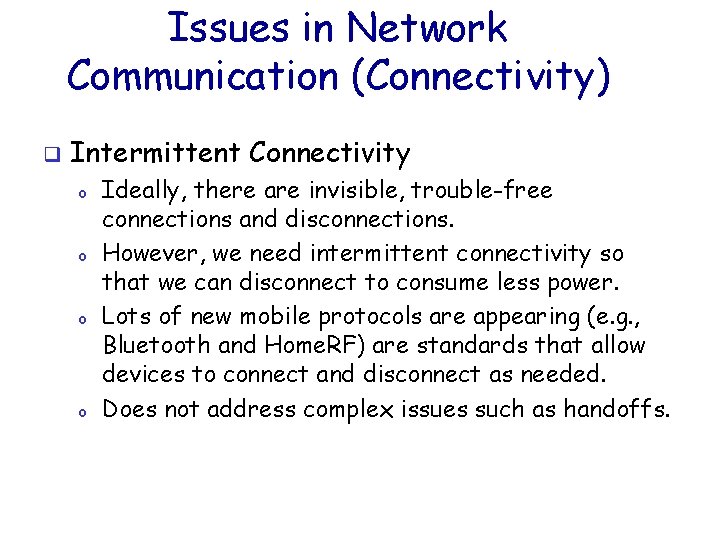
Issues in Network Communication (Connectivity) q Intermittent Connectivity o o Ideally, there are invisible, trouble-free connections and disconnections. However, we need intermittent connectivity so that we can disconnect to consume less power. Lots of new mobile protocols are appearing (e. g. , Bluetooth and Home. RF) are standards that allow devices to connect and disconnect as needed. Does not address complex issues such as handoffs.
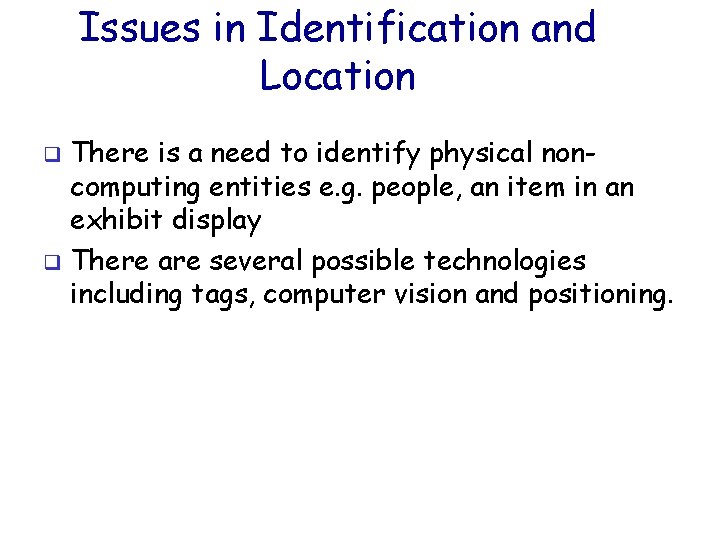
Issues in Identification and Location There is a need to identify physical noncomputing entities e. g. people, an item in an exhibit display q There are several possible technologies including tags, computer vision and positioning. q
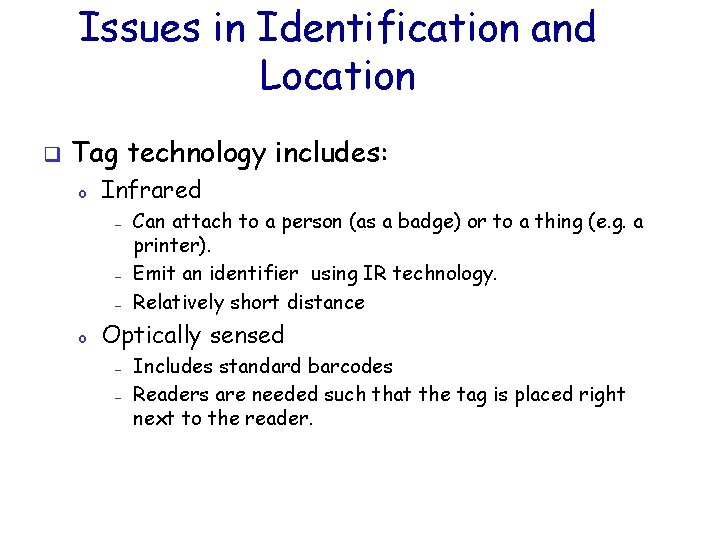
Issues in Identification and Location q Tag technology includes: o Infrared — — — o Can attach to a person (as a badge) or to a thing (e. g. a printer). Emit an identifier using IR technology. Relatively short distance Optically sensed — — Includes standard barcodes Readers are needed such that the tag is placed right next to the reader.
Issues in Identification and Location q Tag technology includes: o RFID — — — o Use radio frequency (RF) Can be read from a distance Do not require their own power source Contact tags — Do not require their own power source.
Issues in Identification and Location q Tagging technology o o o There is not one correct tagging technology to use. The best choice depends on cost and suitability of the physical environment Exact location may be difficult to determine. — Example: IR receivers are really only detecting that an IR transmitter has sent an identifier. You may need several IR receivers reporting that they have seen an IR identifier to pinpoint location.
Issues in Identification and Location q Computer Vision o o q Computer vision techniques can be used for object recognition Example: Room uses footsteps to identify a person Requires a good deal of computing resources A lot of work is needed to make this a viable technology Positioning o o Can be used where objects move rarely Example: GPS
Data Transfer q q Need to be able to transfer data in a seamless fashion. Data initiation and termination takes place using a variety of devices. o o o Sue sending a picture of herself to get her license renewed. Mike downloading a document (through his PDA) sent by Tom could have sent the document using his PDA or a PC and Mike could have downloaded the document through his PC. Making sure that the “personalized newspaper” getting to the device that the user is reading from. User should not have to worry about things like different formats or ftp. The presentation of the content should adapt to the device that the user is using.
Data Transfer q Data is heterogeneous in nature o o q Video, Image, Text, WORD Document, Audio, etc Services are needed to take content and transform to appropriate presentation. Network topologies of devices (eg. , PDAs, sensors, printers, coffee makers) are becoming increasingly more dynamic and thus increasingly are networks are becoming more ad-hoc.
Data Transfer The progression of data through the network needs to be seamless i. e. , the users should not have to know which devices the data is being transferred over or the formats needed to the end user to read it. q The “computing system” must also manage a ubiquitous persistent storage. q Replicated data should be consistent. q
Resource Discovery q q In the scenario, Mike asked for a list of printers that were available to him. The set of printers in a building constantly change i. e. , it is not static. When a printer is “plugged” in how does the printer tell the building that it is available. There are issues with lookup services and connectivity. o o A PDA may store the list of printers so that if the lookup service is down, the user still has a list of printers. When the list of printers changes, when should the PDA be informed?
Resource Discovery q The home environment will have “appliances” that are part of the home computing environment. This includes alarm clock, coffee make, refrigerator, etc; When an appliance is bought and plugged in, it must be made known to the computing environment.
Agent Technology q q q The scenario described the use of agents -- one for scheduling and one that bought stocks. An agent can be defined as a “component of software and/or hardware which is capable of acting exactingly in order to accomplish tasks on behalf of its user. ” Agent technology and protocols for mobile computing is not well understood. This will draw upon knowledge from AI, networking and distributed systems, and databases.
Trigger Management q q An event could cause a number of actions. Examples: o o o q Alarm clock and coffee maker Entering an office and having the temperature set and the PC turned on. A high glucose level causing an appointment to be made. Issues o o o What if there are conflicts? Seamless integration Dynamically changing
Trigger Management Example: Sue and Mike’s scheduled changed so that there is a new time to ring the alarm, start the coffee maker. q Example: What if Sue and Mike decided to only drink coffee on the weekend or eliminate it alltogether. q Example: How does Mike’s home computing system know that it is ok to have the doctor’s office override all appointments. What if Mike wants to hide something from Sue? q
Sensors q If we are to adjust temperature based on the number of people and the current temperature then: o o q Sensors measuring temperature are needed Determining the number of people in a room is needed Sensors are “lightweight” devices; o o Current network protocols e. g. , TCP may not work well. What about power?
User Interface Devices q q q Currently, the primary devices we use to interact with the “computing system” are a keyboard and a mouse. Voice recognition systems are becoming more sophisticated, but I can’t tell the room “make me coffee” or “set up a conference call”. At least not yet. What about “pen” input? o o o In a conference, a person may write something on a whiteboard. If the participants are in remote locations, it would be nice if that information on the whiteboard appeared at each participant’s preferred device. This would certainly be easier than having someone record everything, type it up and then send it.
Ease of Use People can’t program their VCR and yet they are to program event management in their homes or offices. q We don’t want to know about data formats, battery power. q We care about a seamless and inexpensive environment. q
Privacy and Security Take the temperature adjustment q An “enemy” organization could seize control and adjust the temperature so that it is difficult for people work and thus making it less secure. q
Software Development How can software development be faciliated? q Testing q Maintenance q
- Slides: 44