Block Ciphers INSTRUCTOR DANIA ALOMAR Secret Key Cryptography
Block Ciphers INSTRUCTOR: DANIA ALOMAR
Secret Key Cryptography • Both encryption and decryption keys are the same and are kept secret. • The secret key must be known at both ends to perform encryption or decryption. • Secret Key algorithms are fast and they are used for encryptingdecrypting high volume data • Secret key cryptography is classified into two types o Block Ciphers o Stream Ciphers
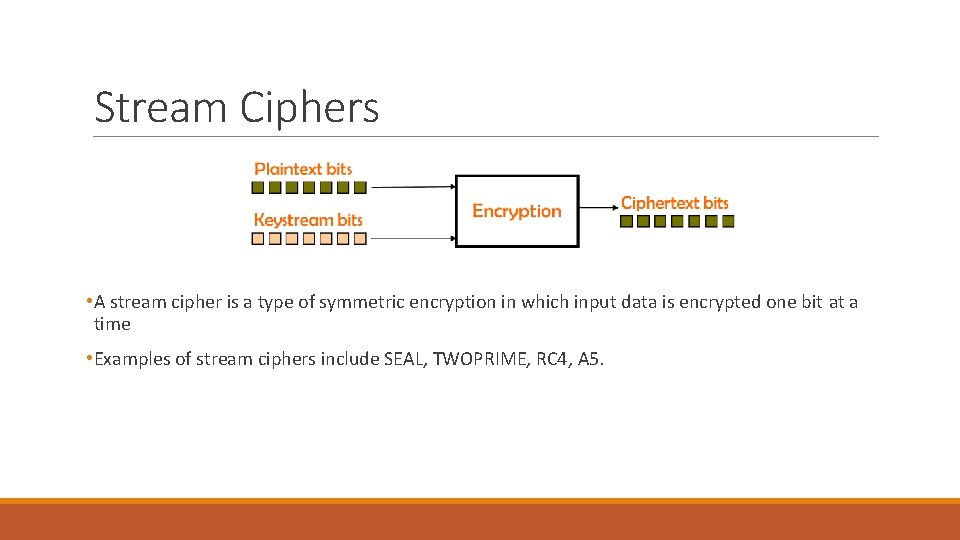
Stream Ciphers • A stream cipher is a type of symmetric encryption in which input data is encrypted one bit at a time • Examples of stream ciphers include SEAL, TWOPRIME, RC 4, A 5.
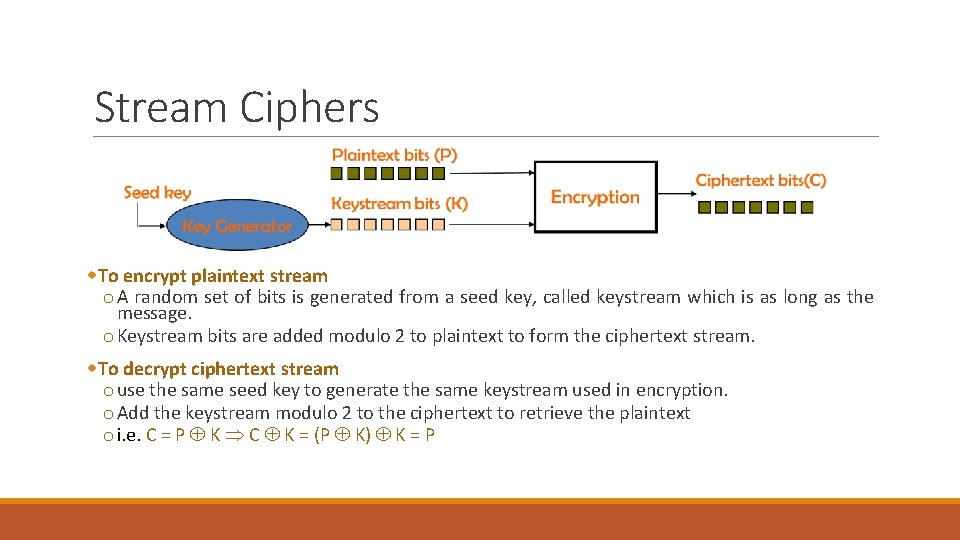
Stream Ciphers w. To encrypt plaintext stream o A random set of bits is generated from a seed key, called keystream which is as long as the message. o Keystream bits are added modulo 2 to plaintext to form the ciphertext stream. w. To decrypt ciphertext stream o use the same seed key to generate the same keystream used in encryption. o Add the keystream modulo 2 to the ciphertext to retrieve the plaintext o i. e. C = P K C K = (P K) K = P
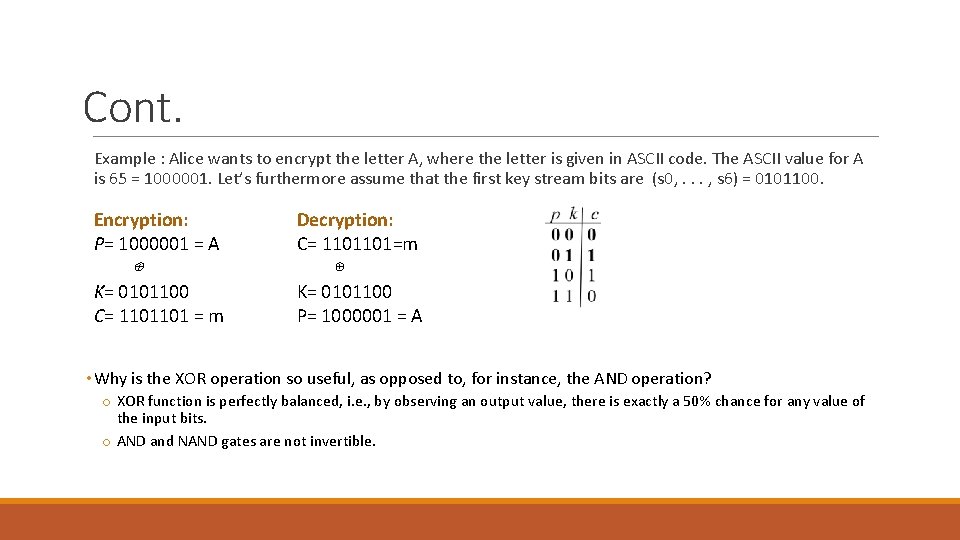
Cont. Example : Alice wants to encrypt the letter A, where the letter is given in ASCII code. The ASCII value for A is 65 = 1000001. Let’s furthermore assume that the first key stream bits are (s 0, . . . , s 6) = 0101100. Encryption: P= 1000001 = A ⊕ K= 0101100 C= 1101101 = m Decryption: C= 1101101=m ⊕ K= 0101100 P= 1000001 = A • Why is the XOR operation so useful, as opposed to, for instance, the AND operation? o XOR function is perfectly balanced, i. e. , by observing an output value, there is exactly a 50% chance for any value of the input bits. o AND and NAND gates are not invertible.
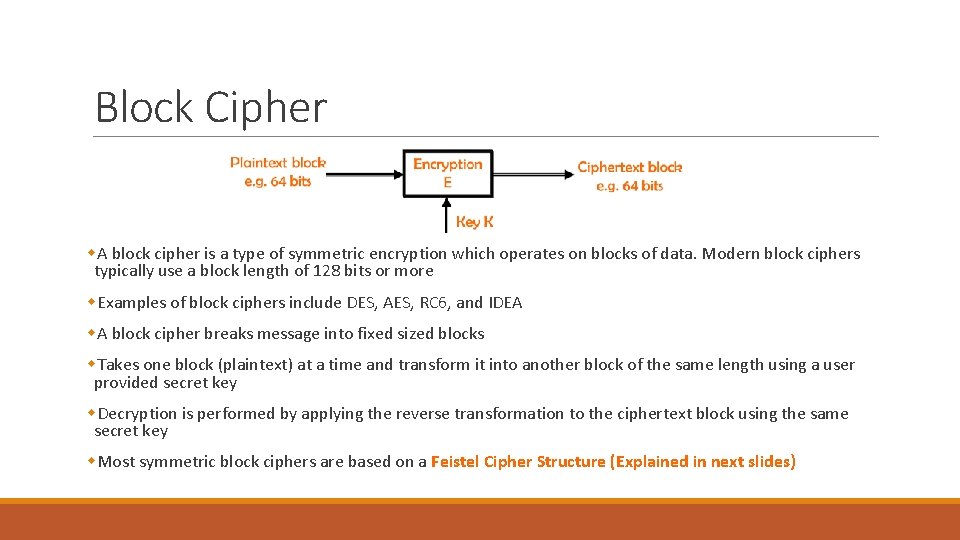
Block Cipher w. A block cipher is a type of symmetric encryption which operates on blocks of data. Modern block ciphers typically use a block length of 128 bits or more w. Examples of block ciphers include DES, AES, RC 6, and IDEA w. A block cipher breaks message into fixed sized blocks w. Takes one block (plaintext) at a time and transform it into another block of the same length using a user provided secret key w. Decryption is performed by applying the reverse transformation to the ciphertext block using the same secret key w. Most symmetric block ciphers are based on a Feistel Cipher Structure (Explained in next slides)
Properties of Good Ciphers • In cryptography, confusion and diffusion are two properties of the operation of a secure cipher which were identified by Shannon in his paper, "Communication Theory of Secrecy Systems" published in 1949. • Confusion refers to making the relationship between the key and the ciphertext as complex as possible. o Substitution is one of the mechanism for primarily confusion • Diffusion refers to the property that redundancy in the statistics of the plaintext is "dissipated" in the statistics of the ciphertext. o Transposition (Permutation) is a technique for diffusion
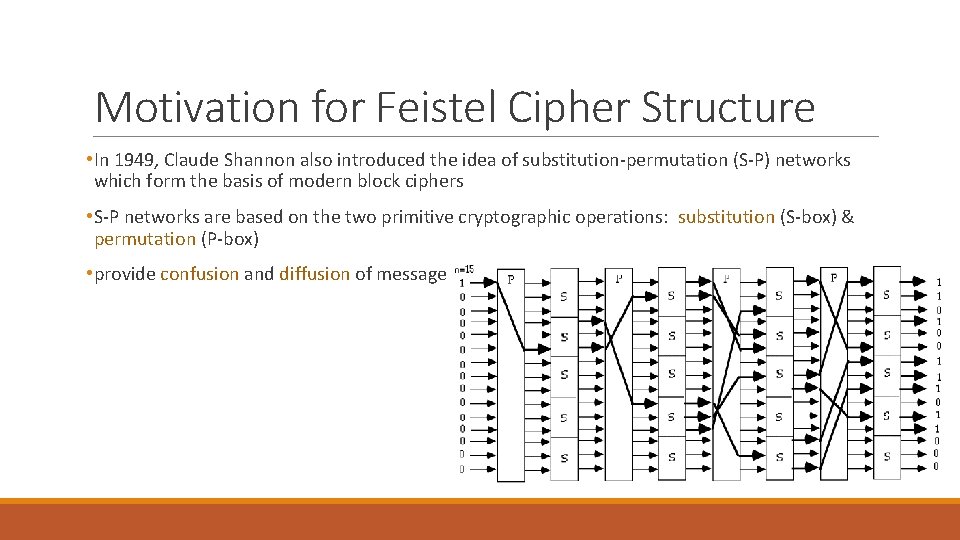
Motivation for Feistel Cipher Structure • In 1949, Claude Shannon also introduced the idea of substitution-permutation (S-P) networks which form the basis of modern block ciphers • S-P networks are based on the two primitive cryptographic operations: substitution (S-box) & permutation (P-box) • provide confusion and diffusion of message
Motivation for Feistel Cipher Structure • S-P network: a special form of substitution-permutation product cipher • Product cipher o Two or more simple ciphers are performed in sequence in such a way that the final result or product is cryptographically stronger than any of the component ciphers • Feistel cipher o In 1970’s, Horst Feistel (IBM T. J. Watson Research Labs) invented a suitable (practical) structure which adapted Shannon’s S-P network o Encryption and decryption use the same structure
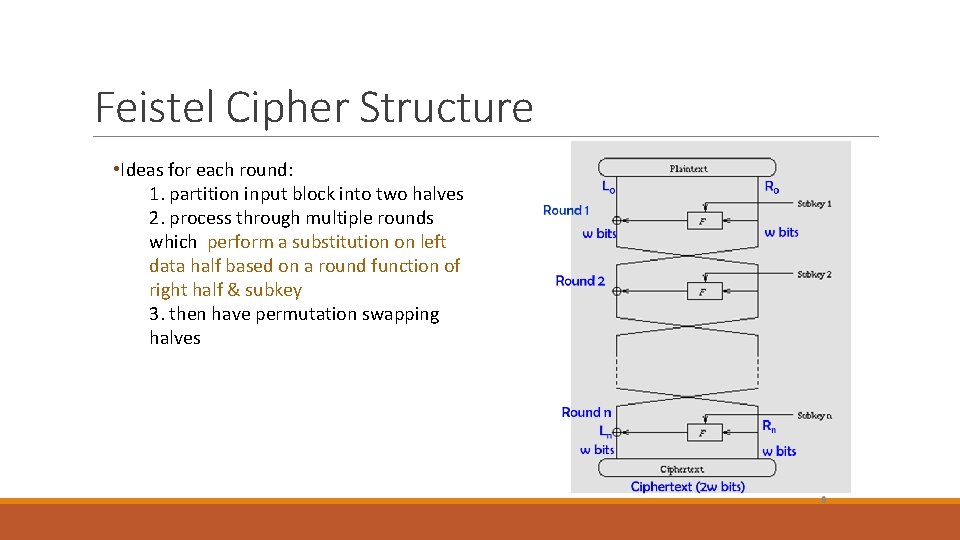
Feistel Cipher Structure • Ideas for each round: 1. partition input block into two halves 2. process through multiple rounds which perform a substitution on left data half based on a round function of right half & subkey 3. then have permutation swapping halves
Feistel Cipher Design Principles • Block size o increasing size improves security, but slows cipher • Key size o increasing size improves security, makes exhaustive key searching harder, but may slow cipher • Number of rounds o increasing number improves security, but slows cipher • Subkey generation o greater complexity can make analysis harder, but slows cipher • Round function o greater complexity can make analysis harder, but slows cipher • Fast software en/decryption & ease of analysis o are more recent concerns for practical use and testing
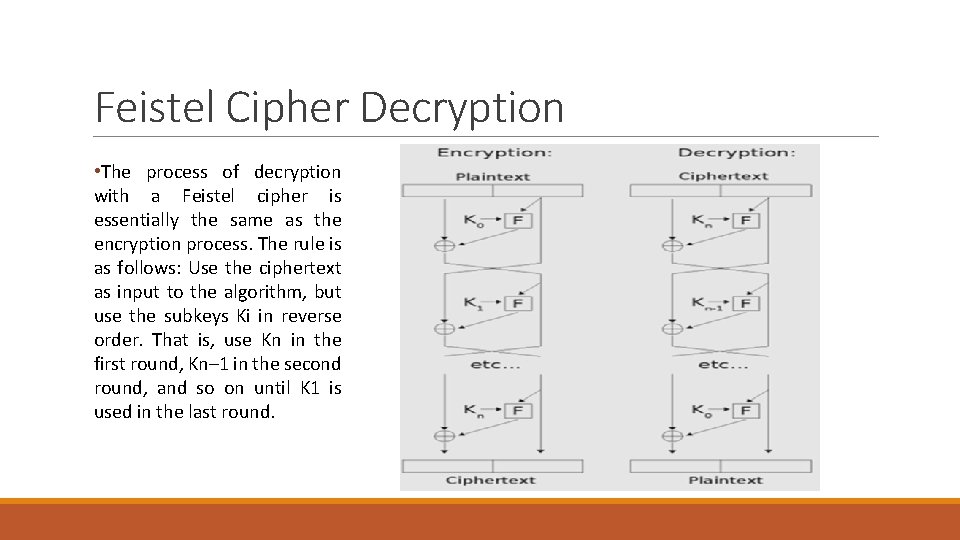
Feistel Cipher Decryption • The process of decryption with a Feistel cipher is essentially the same as the encryption process. The rule is as follows: Use the ciphertext as input to the algorithm, but use the subkeys Ki in reverse order. That is, use Kn in the first round, Kn– 1 in the second round, and so on until K 1 is used in the last round.
DES: a specific design • Overview • Encryption • Decryption • Security
DES – Data Encryption Standard • A Block cipher • Data encrypted in 64 -bit blocks using a 56 -bit key (effective key); Ciphertext is of 64 -bit long • Encrypts by series of substitution and transpositions (or permutations)
DES History • The first commercially available Feistel Cipher was developed by IBM in the 1960's; called Lucifer (by Feistel and Coppersmith) • US National Bureau of Standards (NBS) issued a call for proposals in 1972 • Lucifer was refined, renamed the Data Encryption Algorithm (DEA) in 1974 • Adopted as the standard by NBS in 1977 • DES is the first official U. S. government cipher intended for commercial use
DES Design Controversy • There has been considerable controversy over design oin choice of 56 -bit key (vs Lucifer 128 -bit) oand because design criteria were classified • subsequent events and public analysis show in fact design was appropriate • DES has become widely used, especially in financial applications • Best known and widely used symmetric algorithm in the world • But, no longer is considered secure for highly sensitive applications.
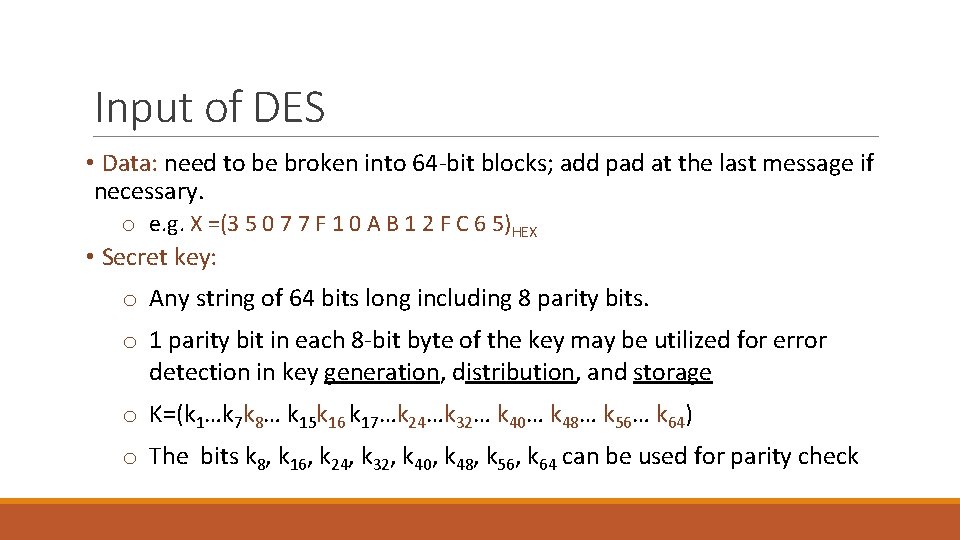
Input of DES • Data: need to be broken into 64 -bit blocks; add pad at the last message if necessary. o e. g. X =(3 5 0 7 7 F 1 0 A B 1 2 F C 6 5)HEX • Secret key: o Any string of 64 bits long including 8 parity bits. o 1 parity bit in each 8 -bit byte of the key may be utilized for error detection in key generation, distribution, and storage o K=(k 1…k 7 k 8… k 15 k 16 k 17…k 24…k 32… k 40… k 48… k 56… k 64) o The bits k 8, k 16, k 24, k 32, k 40, k 48, k 56, k 64 can be used for parity check
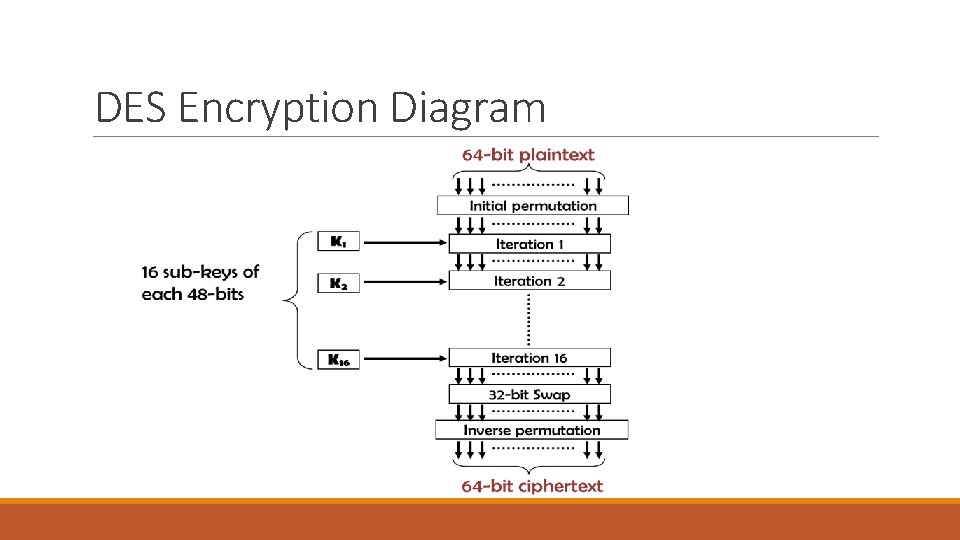
DES Encryption Diagram
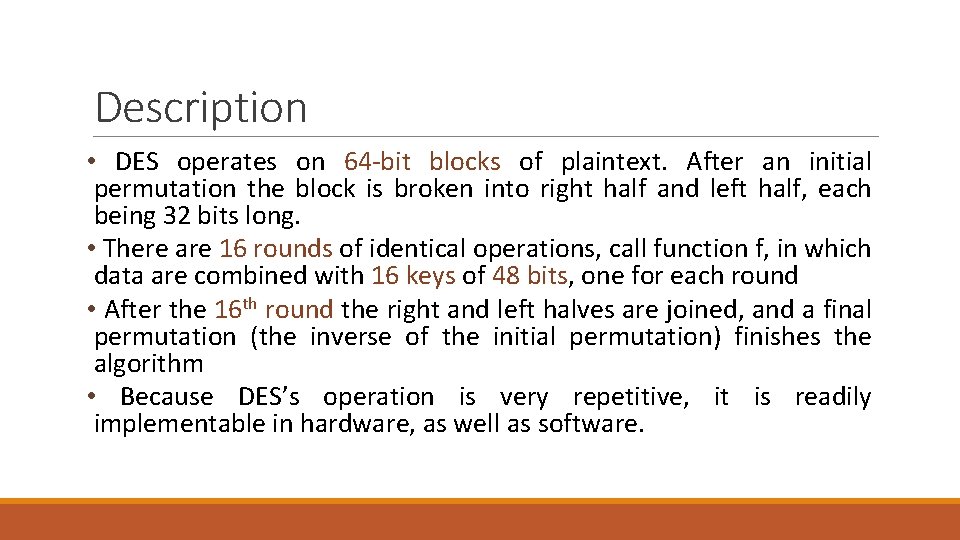
Description • DES operates on 64 -bit blocks of plaintext. After an initial permutation the block is broken into right half and left half, each being 32 bits long. • There are 16 rounds of identical operations, call function f, in which data are combined with 16 keys of 48 bits, one for each round • After the 16 th round the right and left halves are joined, and a final permutation (the inverse of the initial permutation) finishes the algorithm • Because DES’s operation is very repetitive, it is readily implementable in hardware, as well as software.
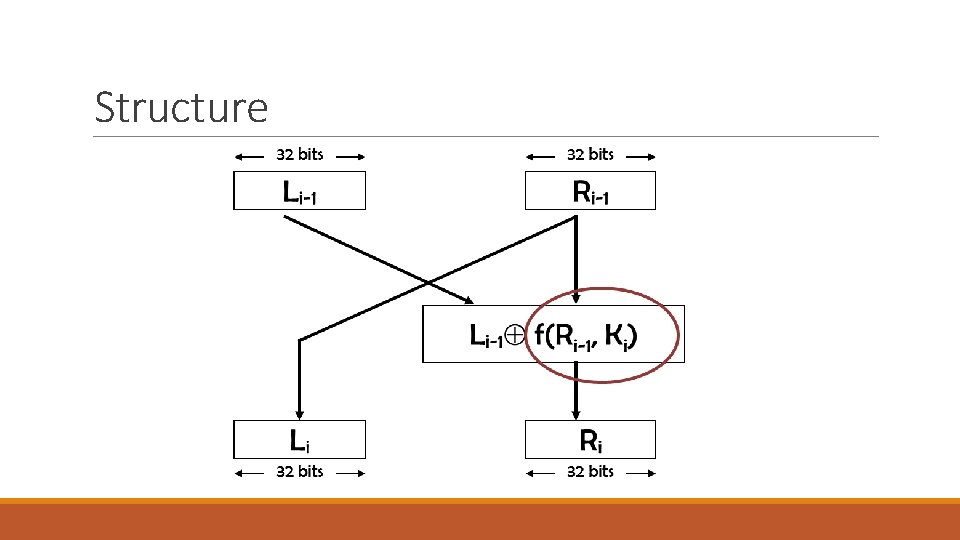
Structure
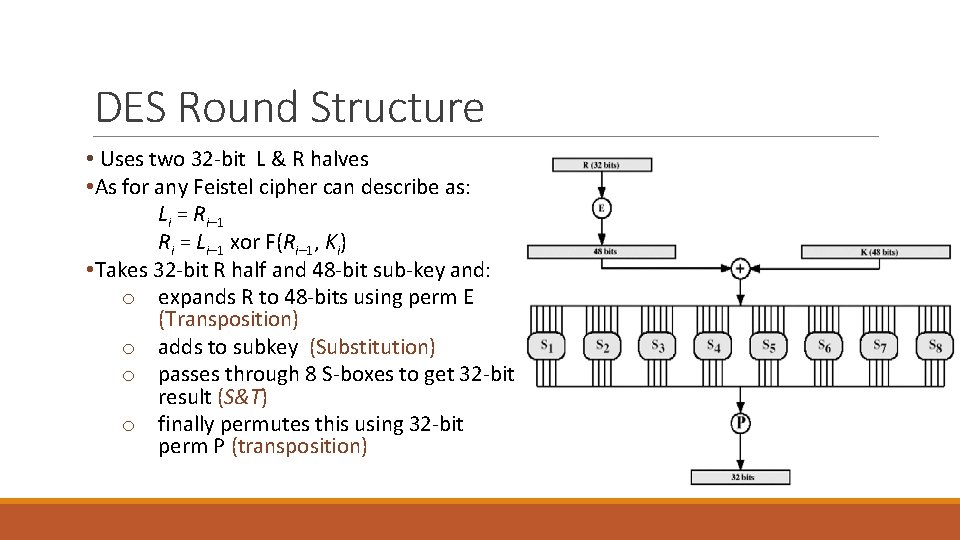
DES Round Structure • Uses two 32 -bit L & R halves • As for any Feistel cipher can describe as: Li = Ri– 1 Ri = Li– 1 xor F(Ri– 1, Ki) • Takes 32 -bit R half and 48 -bit sub-key and: o expands R to 48 -bits using perm E (Transposition) o adds to subkey (Substitution) o passes through 8 S-boxes to get 32 -bit result (S&T) o finally permutes this using 32 -bit perm P (transposition)
DES Module Operations • Permutation boxes o Specific boxes used in DES includes: PC 1 and PC 2 for subkey generation; IP, IP-1, E-box and P-box • Substitution boxes o 8 specific S-boxes are used in DES; This is the core of DES. • Modulo 2 addition o Addition in binary form; used in function f. • 32 bits registers o Use only to store data. In the key generator two shift registers are used to cyclically shift the data used in key generation
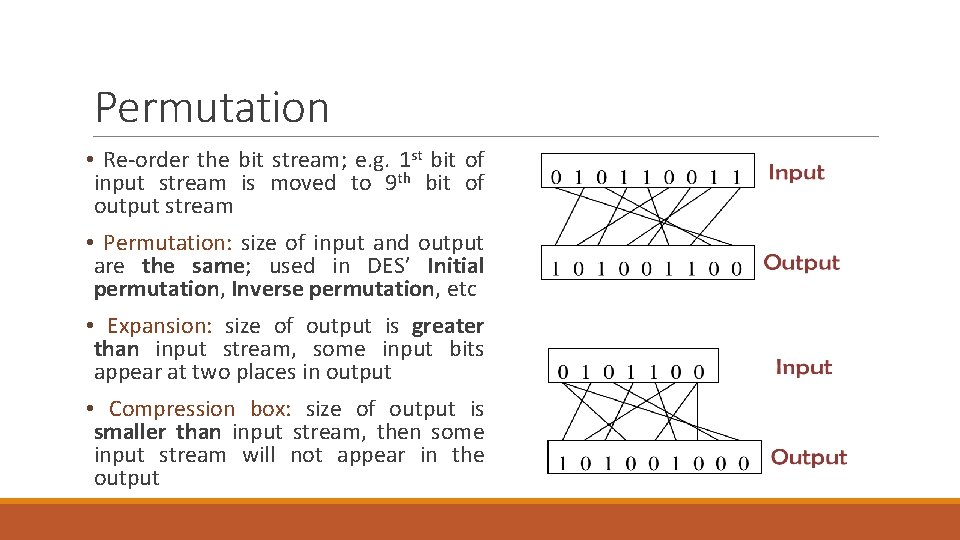
Permutation • Re-order the bit stream; e. g. 1 st bit of input stream is moved to 9 th bit of output stream • Permutation: size of input and output are the same; used in DES’ Initial permutation, Inverse permutation, etc • Expansion: size of output is greater than input stream, some input bits appear at two places in output • Compression box: size of output is smaller than input stream, then some input stream will not appear in the output
Substitution • Substitution boxes provide a substitution code, i. e. there is a code output stored for each input • Each S box stores a different set of 64 hexadecimal numbers in a matrix of 16 4. • There are 8 S-boxes in DES, each accepts a 6 -bit input and returns a 4 -bit output. • Consider a 48 -bit input stream, first 6 bits input will be input to the first S box, next 6 bits will be for the second S box, and so on.
DES Key Schedule
Generating subkeys used in each round • consists of: o Initial permutation of the key Permuted Choice 1 (PC 1) which selects 56 -bits in two 28 -bit halves o 16 stages consisting of: § selecting 28 -bits from each half § permuting them by Permuted Choice 2 (PC 2) for use in function f, § rotating each half separately either 1 or 2 places depending on the key rotation schedule K
Sub-Key generations w Now, let’s first learn how to generate 16 sub-keys for each round of DES, given a secret key K of 64 bits long (includes 8 parity bits) by the sender ðK= [0101 1000 0001 1111 1011 1100 1001 0100 1101 0011 1010 0101 0010 1110 1010] ðFor each byte, the 8 th bit is 1 if the number of 1 s in the first 7 bits is even, 0 otherwise.
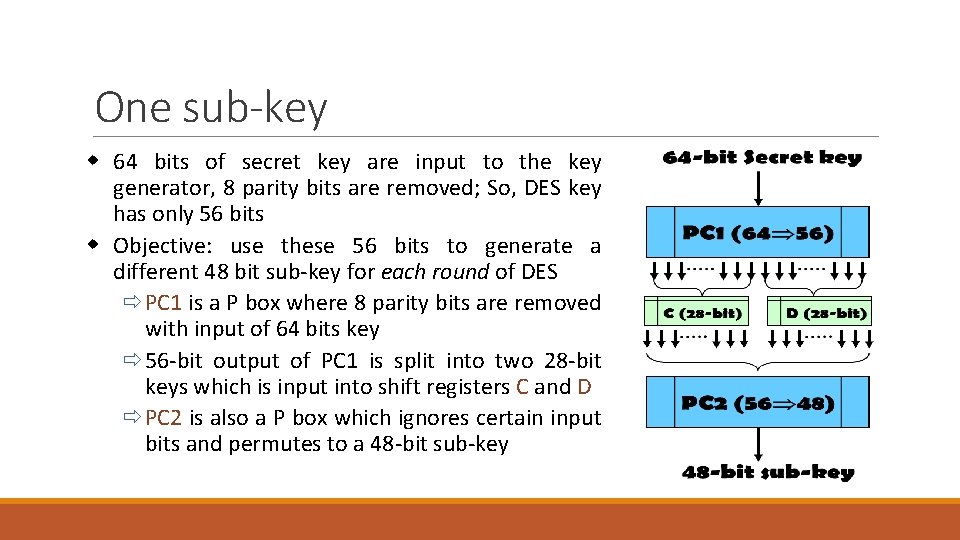
One sub-key w 64 bits of secret key are input to the key generator, 8 parity bits are removed; So, DES key has only 56 bits w Objective: use these 56 bits to generate a different 48 bit sub-key for each round of DES ðPC 1 is a P box where 8 parity bits are removed with input of 64 bits key ð 56 -bit output of PC 1 is split into two 28 -bit keys which is input into shift registers C and D ðPC 2 is also a P box which ignores certain input bits and permutes to a 48 -bit sub-key
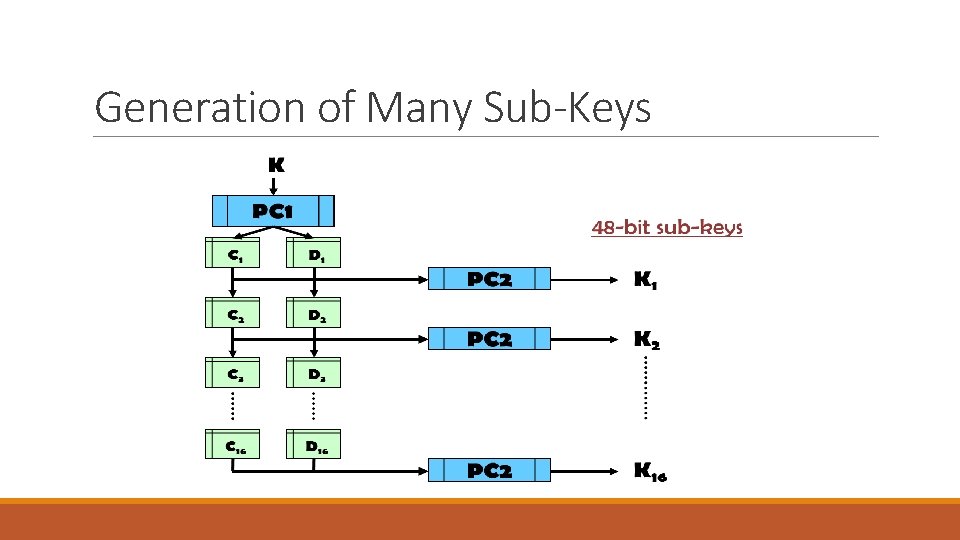
Generation of Many Sub-Keys
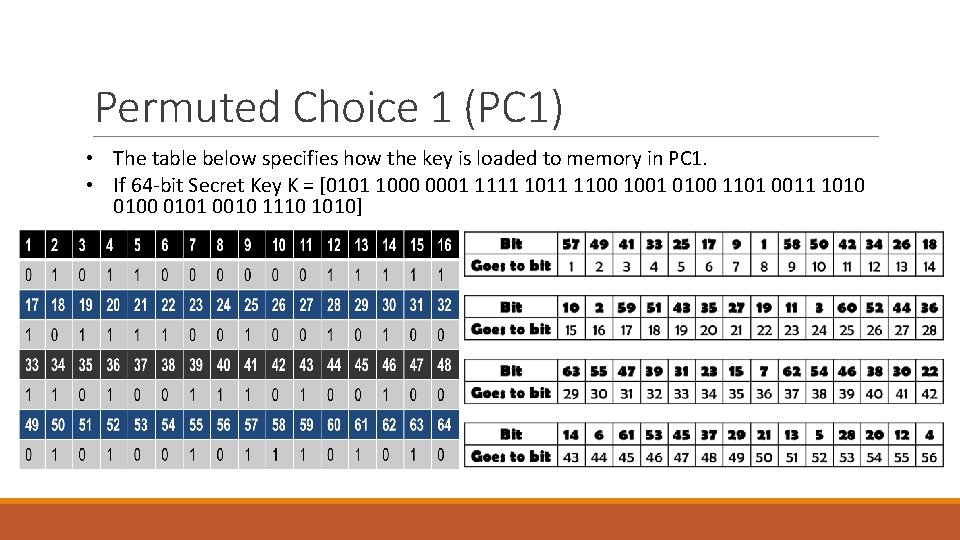
Permuted Choice 1 (PC 1) • The table below specifies how the key is loaded to memory in PC 1. • If 64 -bit Secret Key K = [0101 1000 0001 1111 1011 1100 1001 0100 1101 0011 1010 0101 0010 1110 1010]
![Cont. • Then PC 1(K) = [L R] where both L and R are Cont. • Then PC 1(K) = [L R] where both L and R are](http://slidetodoc.com/presentation_image_h/72f83fb707b996fd79761d31a14db3ca/image-31.jpg)
Cont. • Then PC 1(K) = [L R] where both L and R are 28 bits long and L = [101111001101001000101] and R = [110100101110100001111111]
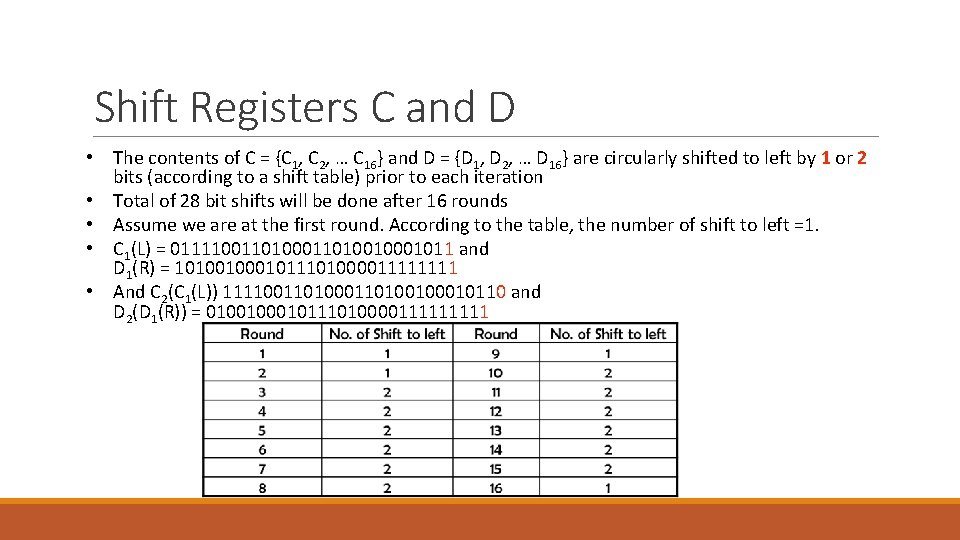
Shift Registers C and D • The contents of C = {C 1, C 2, … C 16} and D = {D 1, D 2, … D 16} are circularly shifted to left by 1 or 2 bits (according to a shift table) prior to each iteration • Total of 28 bit shifts will be done after 16 rounds • Assume we are at the first round. According to the table, the number of shift to left =1. • C 1(L) = 011110011010010001011 and D 1(R) = 10100101110100001111 • And C 2(C 1(L)) 111100110100100010110 and D 2(D 1(R)) = 01001011101000011111
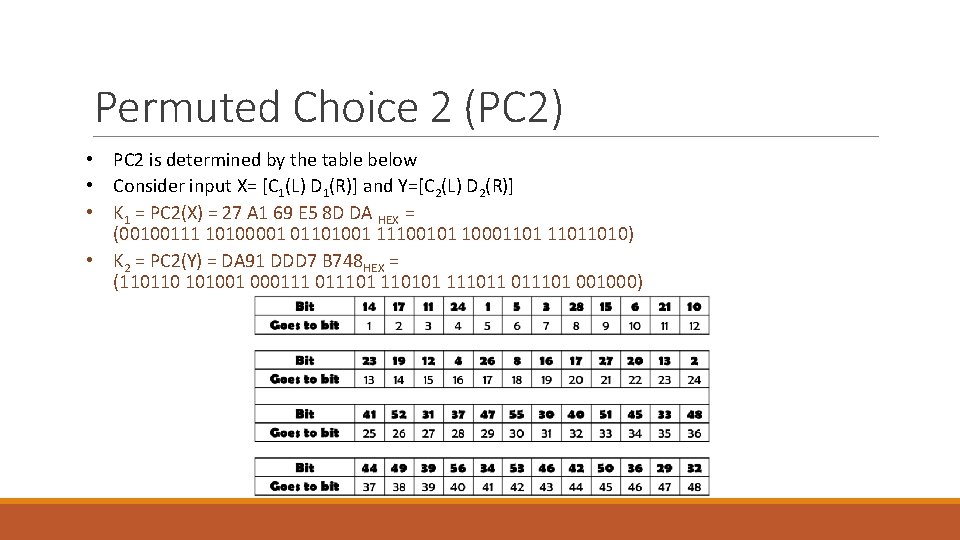
Permuted Choice 2 (PC 2) • PC 2 is determined by the table below • Consider input X= [C 1(L) D 1(R)] and Y=[C 2(L) D 2(R)] • K 1 = PC 2(X) = 27 A 1 69 E 5 8 D DA HEX = (00100111 10100001 01101001 11100101 100011011010) • K 2 = PC 2(Y) = DA 91 DDD 7 B 748 HEX = (110110 101001 00011101 110101 111011 011101 001000)
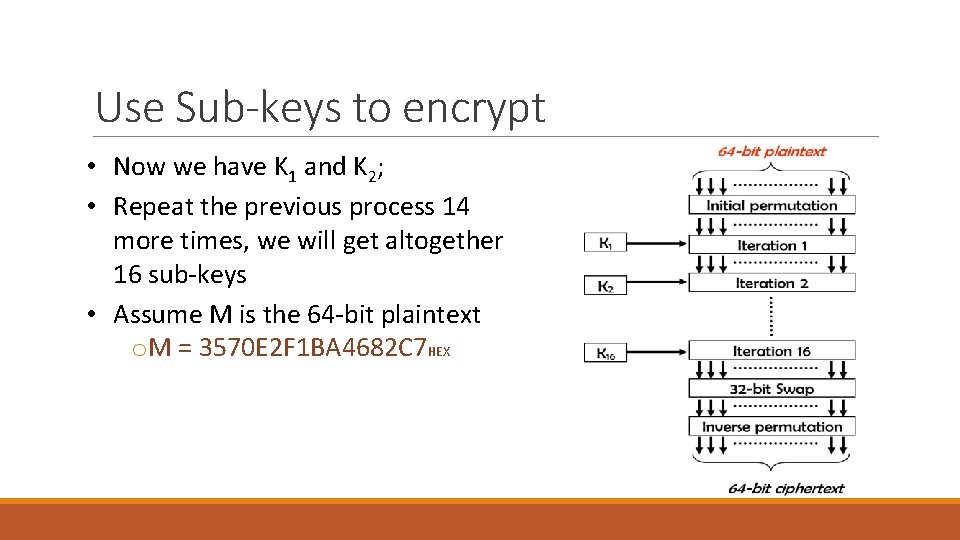
Use Sub-keys to encrypt • Now we have K 1 and K 2; • Repeat the previous process 14 more times, we will get altogether 16 sub-keys • Assume M is the 64 -bit plaintext o. M = 3570 E 2 F 1 BA 4682 C 7 HEX
Initial Permutation
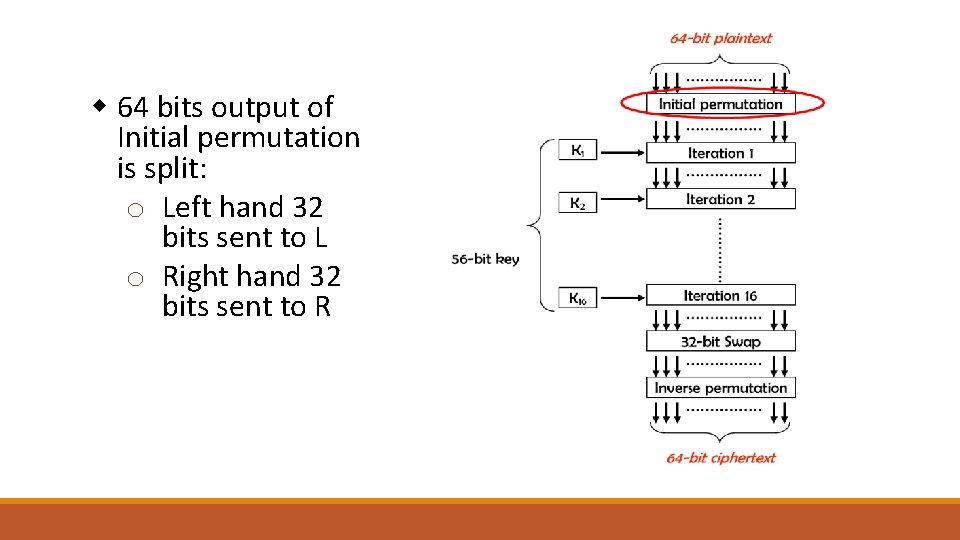
w 64 bits output of Initial permutation is split: o Left hand 32 bits sent to L o Right hand 32 bits sent to R
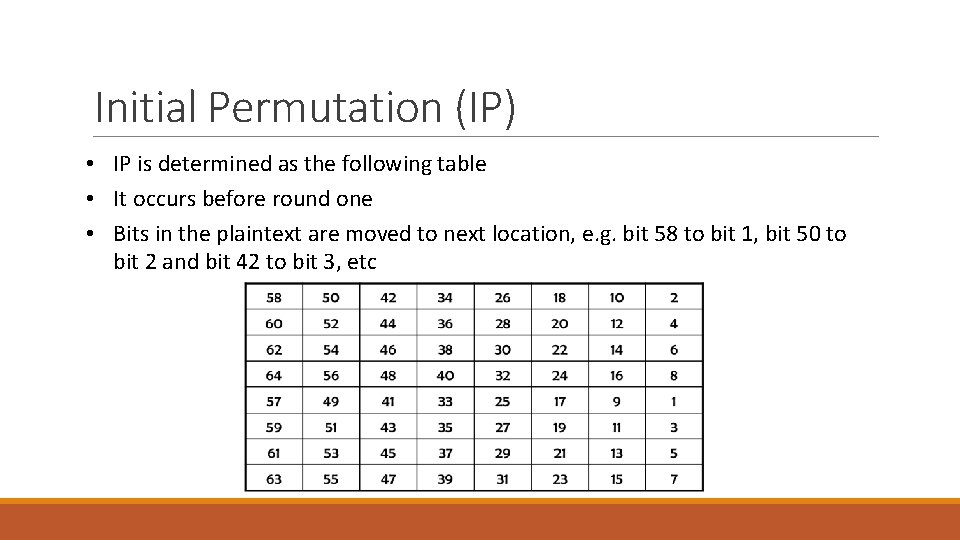
Initial Permutation (IP) • IP is determined as the following table • It occurs before round one • Bits in the plaintext are moved to next location, e. g. bit 58 to bit 1, bit 50 to bit 2 and bit 42 to bit 3, etc
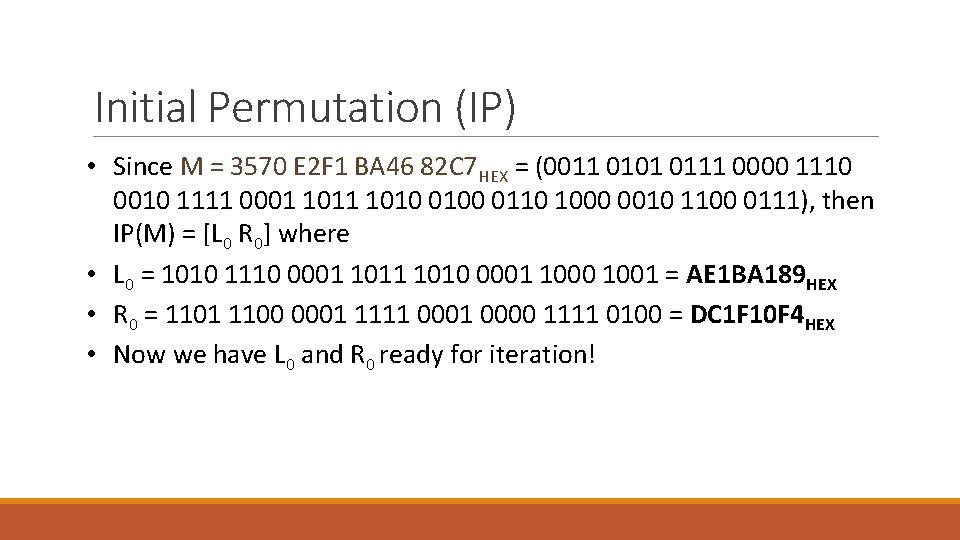
Initial Permutation (IP) • Since M = 3570 E 2 F 1 BA 46 82 C 7 HEX = (0011 0101 0111 0000 1110 0010 1111 0001 1010 0100 0110 1000 0010 1100 0111), then IP(M) = [L 0 R 0] where • L 0 = 1010 1110 0001 1010 0001 1000 1001 = AE 1 BA 189 HEX • R 0 = 1101 1100 0001 1111 0000 1111 0100 = DC 1 F 10 F 4 HEX • Now we have L 0 and R 0 ready for iteration!
Operations in Each Round
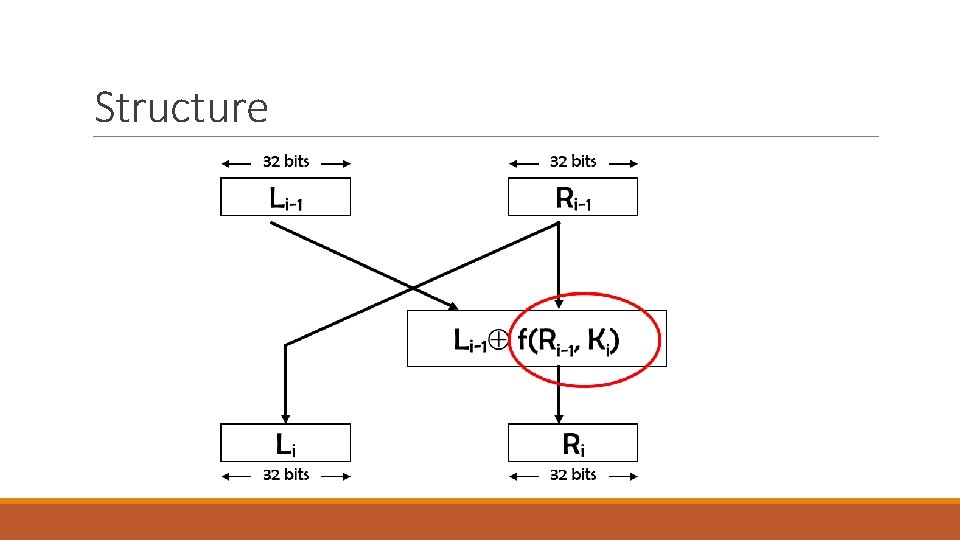
Structure
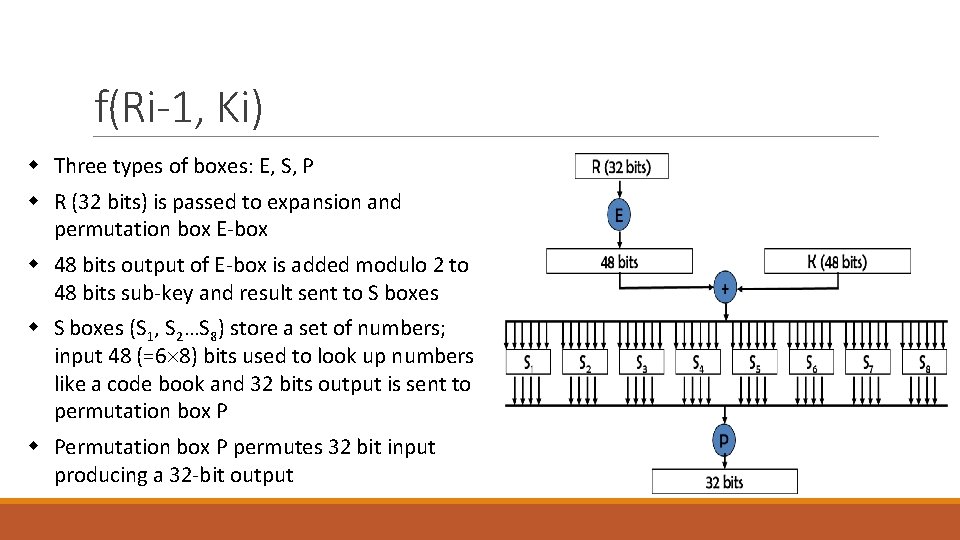
f(Ri-1, Ki) w Three types of boxes: E, S, P w R (32 bits) is passed to expansion and permutation box E-box w 48 bits output of E-box is added modulo 2 to 48 bits sub-key and result sent to S boxes w S boxes (S 1, S 2…S 8) store a set of numbers; input 48 (=6 8) bits used to look up numbers like a code book and 32 bits output is sent to permutation box P w Permutation box P permutes 32 bit input producing a 32 -bit output
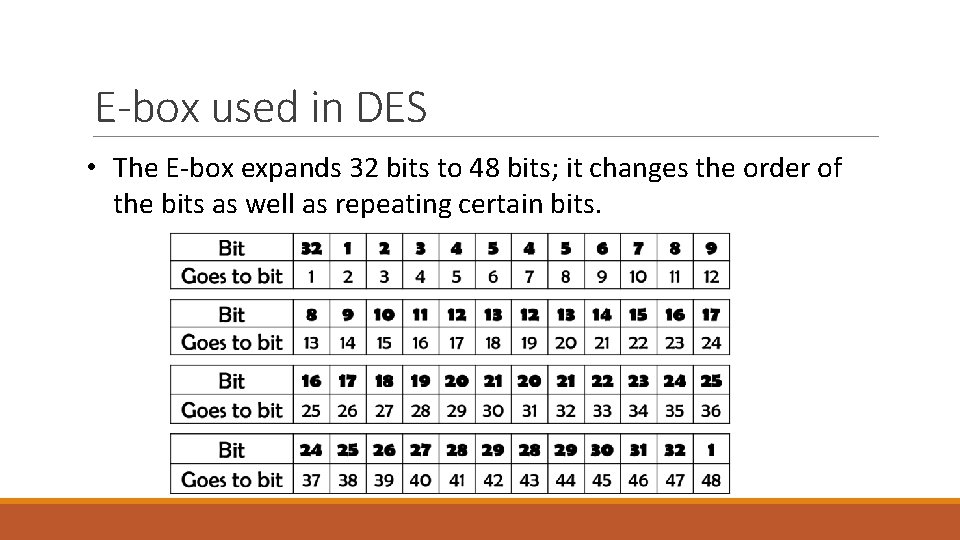
E-box used in DES • The E-box expands 32 bits to 48 bits; it changes the order of the bits as well as repeating certain bits.
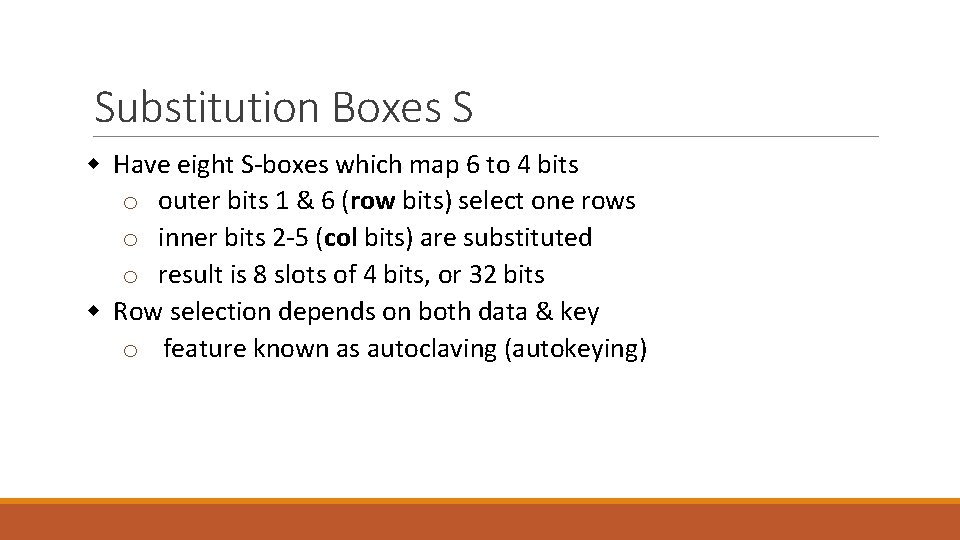
Substitution Boxes S w Have eight S-boxes which map 6 to 4 bits o outer bits 1 & 6 (row bits) select one rows o inner bits 2 -5 (col bits) are substituted o result is 8 slots of 4 bits, or 32 bits w Row selection depends on both data & key o feature known as autoclaving (autokeying)
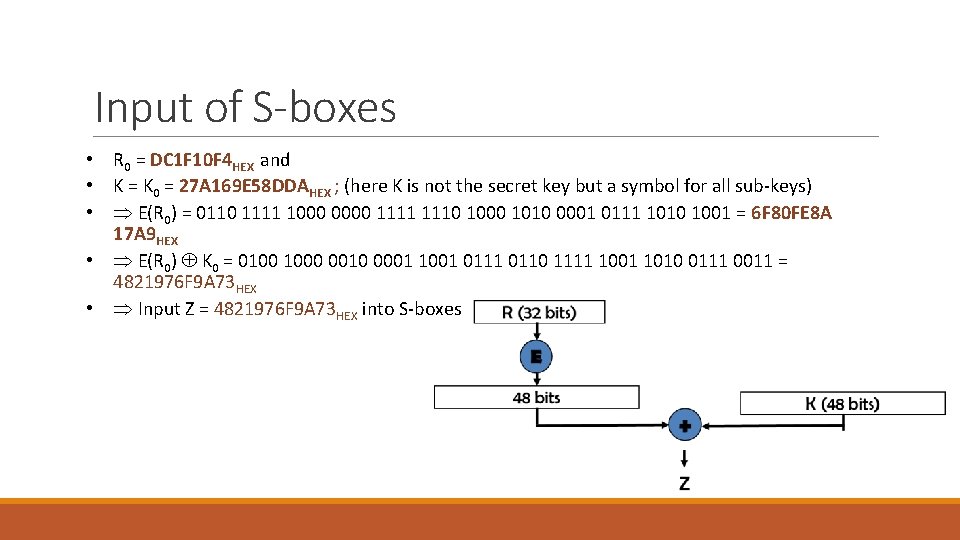
Input of S-boxes • R 0 = DC 1 F 10 F 4 HEX and • K = K 0 = 27 A 169 E 58 DDAHEX ; (here K is not the secret key but a symbol for all sub-keys) • E(R 0) = 0110 1111 1000 0000 1111 1110 1000 1010 0001 0111 1010 1001 = 6 F 80 FE 8 A 17 A 9 HEX • E(R 0) K 0 = 0100 1000 0010 0001 1001 0110 1111 1001 1010 0111 0011 = 4821976 F 9 A 73 HEX • Input Z = 4821976 F 9 A 73 HEX into S-boxes
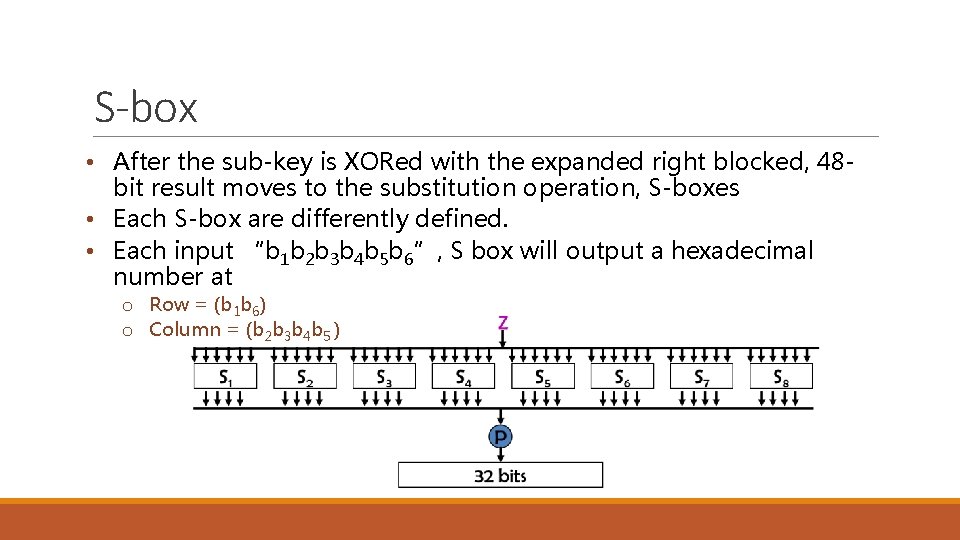
S-box • After the sub-key is XORed with the expanded right blocked, 48 bit result moves to the substitution operation, S-boxes • Each S-box are differently defined. • Each input “b 1 b 2 b 3 b 4 b 5 b 6”, S box will output a hexadecimal number at o Row = (b 1 b 6) o Column = (b 2 b 3 b 4 b 5 )
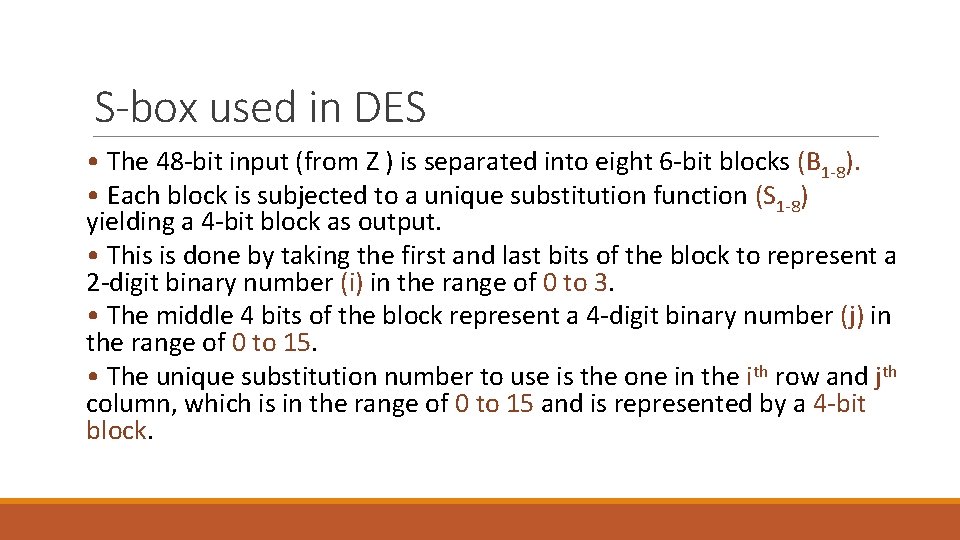
S-box used in DES • The 48 -bit input (from Z ) is separated into eight 6 -bit blocks (B 1 -8). • Each block is subjected to a unique substitution function (S 1 -8) yielding a 4 -bit block as output. • This is done by taking the first and last bits of the block to represent a 2 -digit binary number (i) in the range of 0 to 3. • The middle 4 bits of the block represent a 4 -digit binary number (j) in the range of 0 to 15. • The unique substitution number to use is the one in the ith row and jth column, which is in the range of 0 to 15 and is represented by a 4 -bit block.
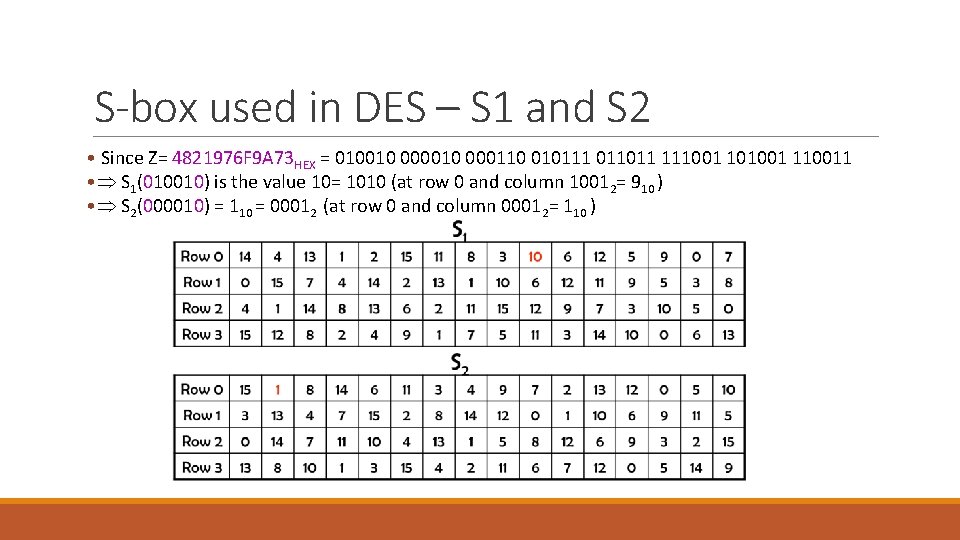
S-box used in DES – S 1 and S 2 • Since Z= 4821976 F 9 A 73 HEX = 010010 000110 010111 011011 111001 101001 110011 • S 1(010010) is the value 10= 1010 (at row 0 and column 10012= 910 ) • S 2(000010) = 110 = 00012 (at row 0 and column 00012= 110 )
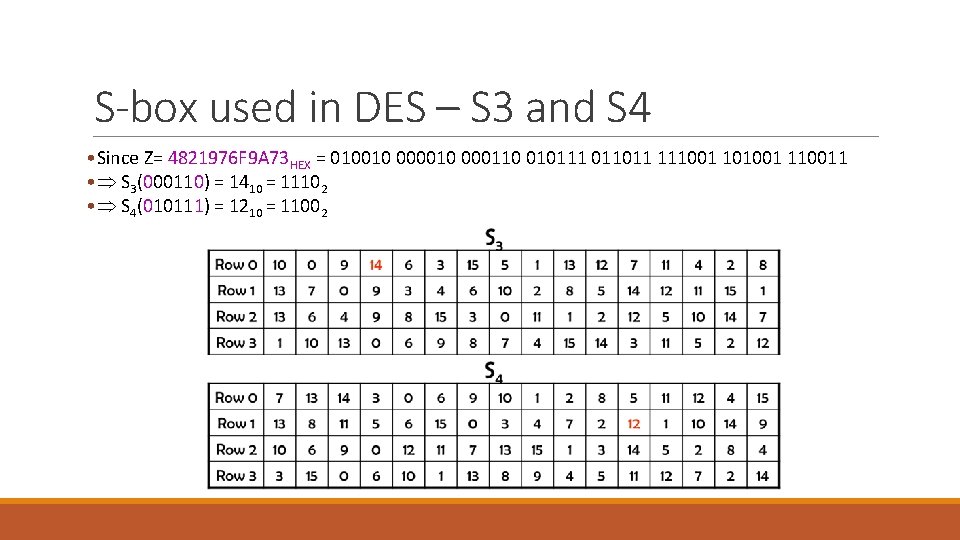
S-box used in DES – S 3 and S 4 • Since Z= 4821976 F 9 A 73 HEX = 010010 000110 010111 011011 111001 101001 110011 • S 3(000110) = 1410 = 11102 • S 4(010111) = 1210 = 11002
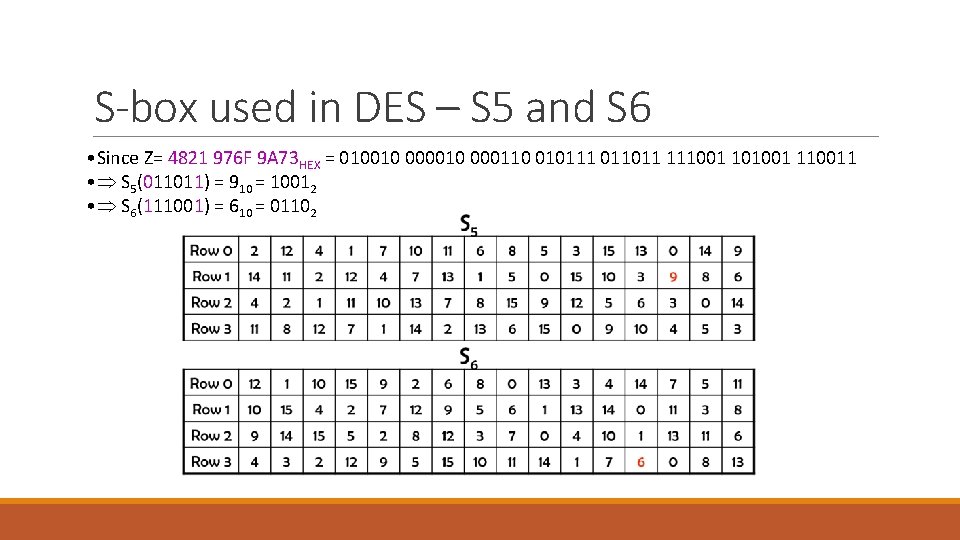
S-box used in DES – S 5 and S 6 • Since Z= 4821 976 F 9 A 73 HEX = 010010 000110 010111 011011 111001 101001 110011 • S 5(011011) = 910 = 10012 • S 6(111001) = 610 = 01102
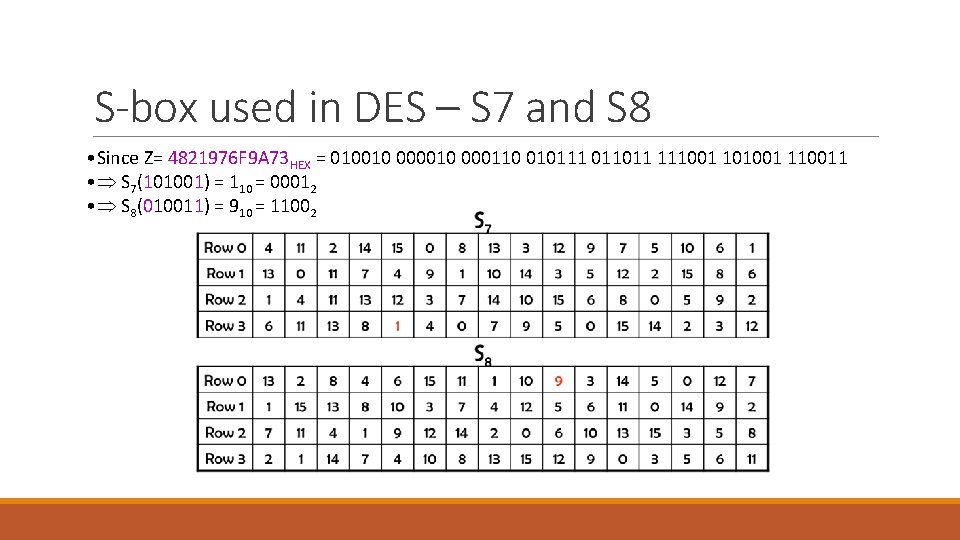
S-box used in DES – S 7 and S 8 • Since Z= 4821976 F 9 A 73 HEX = 010010 000110 010111 011011 111001 101001 110011 • S 7(101001) = 110 = 00012 • S 8(010011) = 910 = 11002
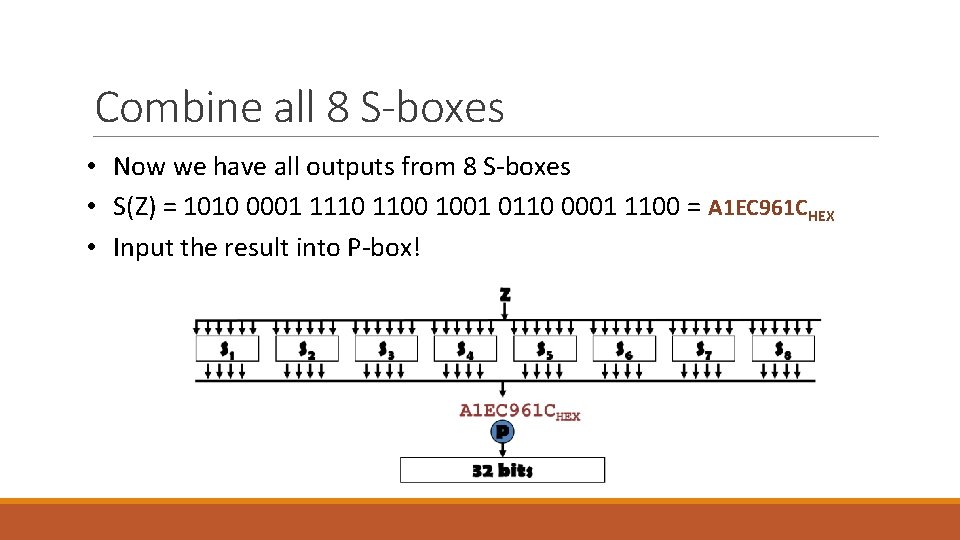
Combine all 8 S-boxes • Now we have all outputs from 8 S-boxes • S(Z) = 1010 0001 1110 1100 1001 0110 0001 1100 = A 1 EC 961 CHEX • Input the result into P-box!
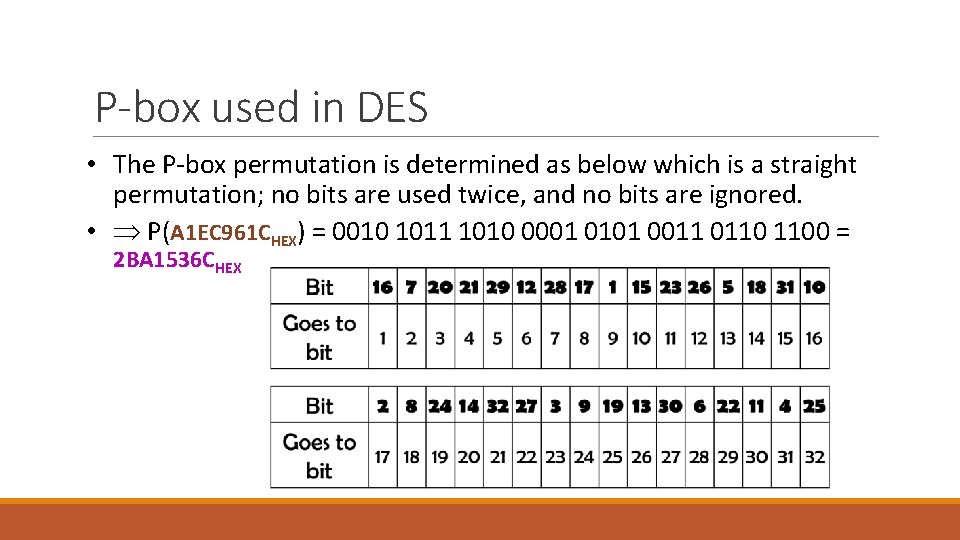
P-box used in DES • The P-box permutation is determined as below which is a straight permutation; no bits are used twice, and no bits are ignored. • P(A 1 EC 961 CHEX) = 0010 1011 1010 0001 0101 0011 0110 1100 = 2 BA 1536 CHEX
The last step to get Ciphertext
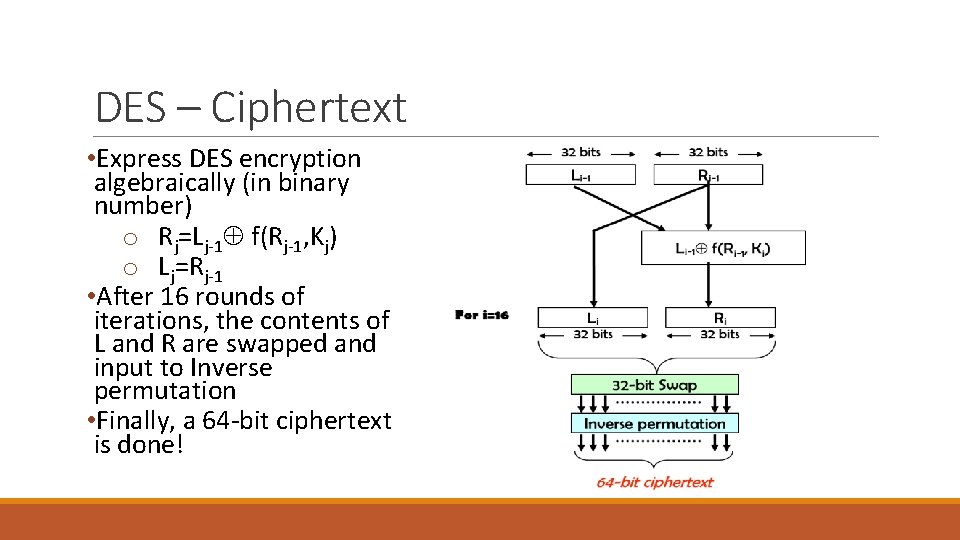
DES – Ciphertext • Express DES encryption algebraically (in binary number) o Rj=Lj-1 f(Rj-1, Kj) o Lj=Rj-1 • After 16 rounds of iterations, the contents of L and R are swapped and input to Inverse permutation • Finally, a 64 -bit ciphertext is done!
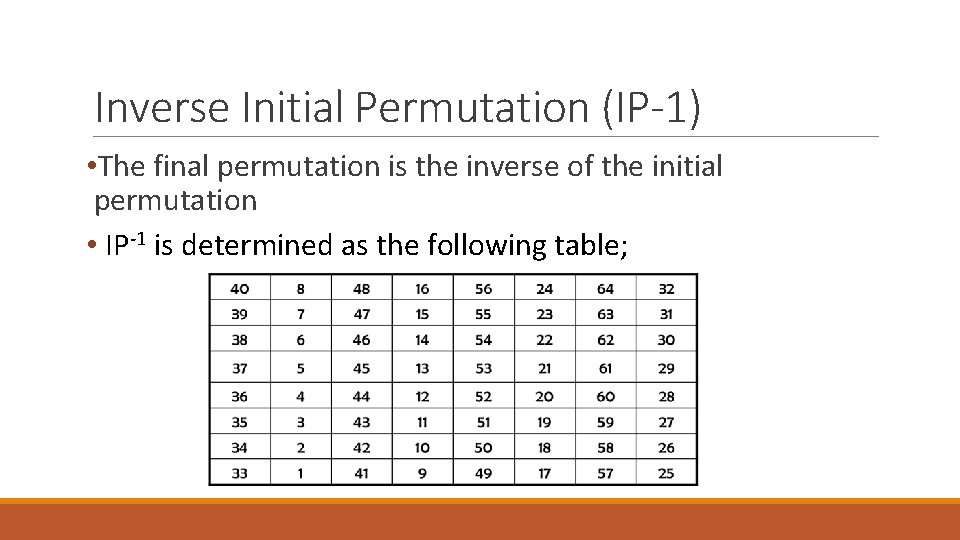
Inverse Initial Permutation (IP-1) • The final permutation is the inverse of the initial permutation • IP-1 is determined as the following table;
DES – Decryption
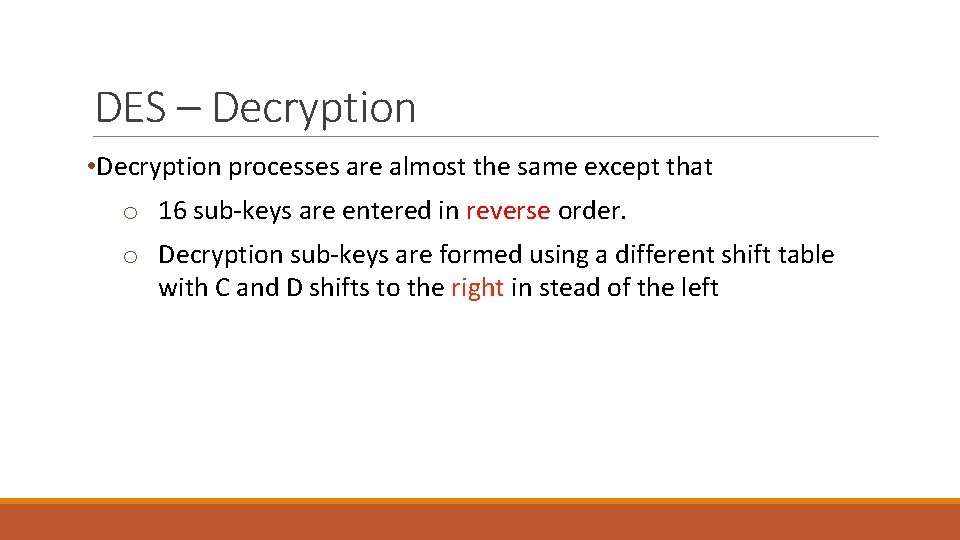
DES – Decryption • Decryption processes are almost the same except that o 16 sub-keys are entered in reverse order. o Decryption sub-keys are formed using a different shift table with C and D shifts to the right in stead of the left
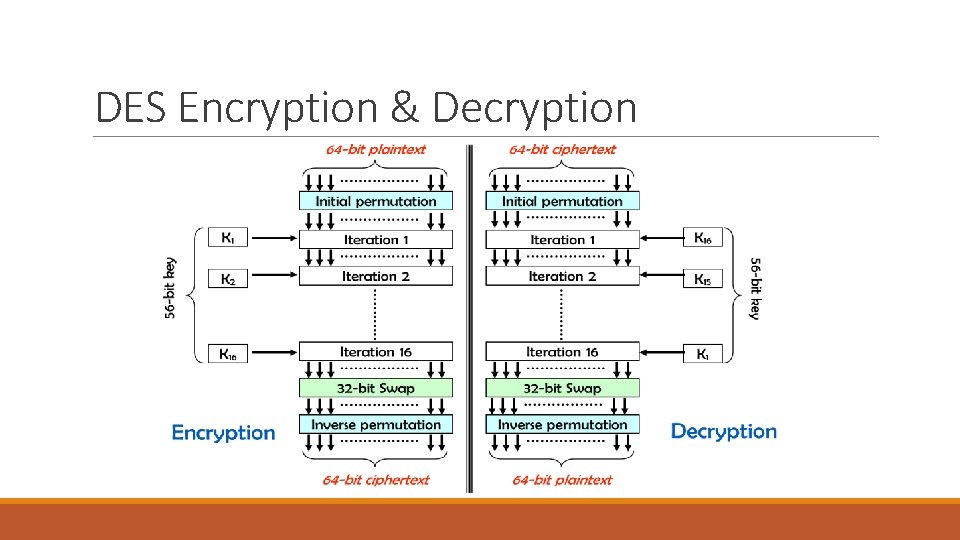
DES Encryption & Decryption
Detailed Description • Decrypt must “undo” steps of data computation • With Feistel design, do encryption steps again • Using subkeys in reverse order (SK 16 … SK 1) • Note that IP undoes final FP step of encryption • 1 st round with SK 16 undoes 16 th encrypt round • …. • 16 th round with SK 1 undoes 1 st encrypt round • Then final FP undoes initial encryption IP • Thus recovering original data value
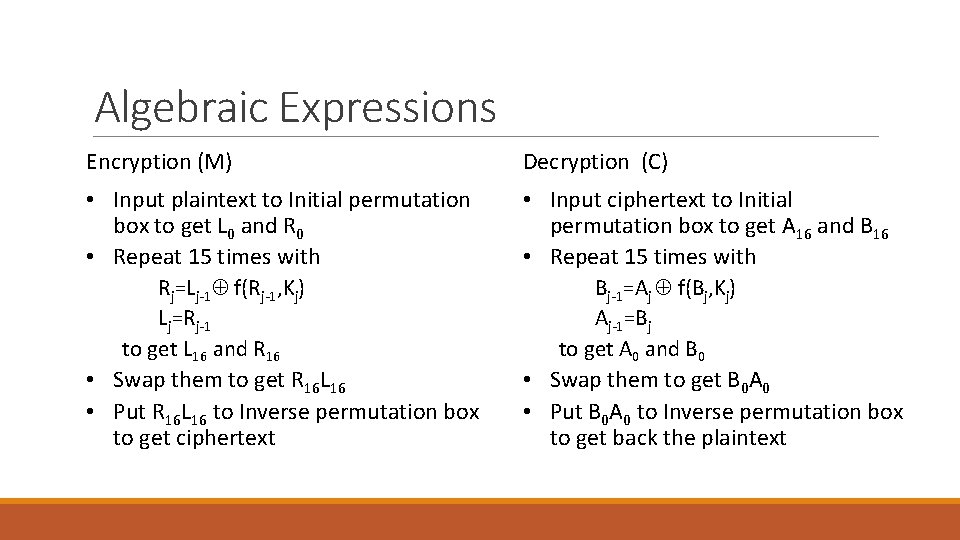
Algebraic Expressions Encryption (M) Decryption (C) • Input plaintext to Initial permutation box to get L 0 and R 0 • Repeat 15 times with • Input ciphertext to Initial permutation box to get A 16 and B 16 • Repeat 15 times with Rj=Lj-1 f(Rj-1, Kj) Lj=Rj-1 to get L 16 and R 16 • Swap them to get R 16 L 16 • Put R 16 L 16 to Inverse permutation box to get ciphertext Bj-1=Aj f(Bj, Kj) Aj-1=Bj to get A 0 and B 0 • Swap them to get B 0 A 0 • Put B 0 A 0 to Inverse permutation box to get back the plaintext
A Simple Example w w w w Consider there are only 2 rounds in DES Given ciphertext = C = D 7698224283 E 0 AEAHEX Let’s decipher it to get back our plaintext M. Normally, in deciphering operation, sub-key must be used in reversed order; i. e. K 16, K 15, … In our case, we will use K 2 and then K 1 only Also, those shift registers C = {C 1, C 2} and D = {D 1, D 2} will be altered to right shift IP(C) = 8321290385 BAF 2 E 5 HEX Let A 2= 83212903 HEX and B 2= 85 BAF 2 E 5 HEX
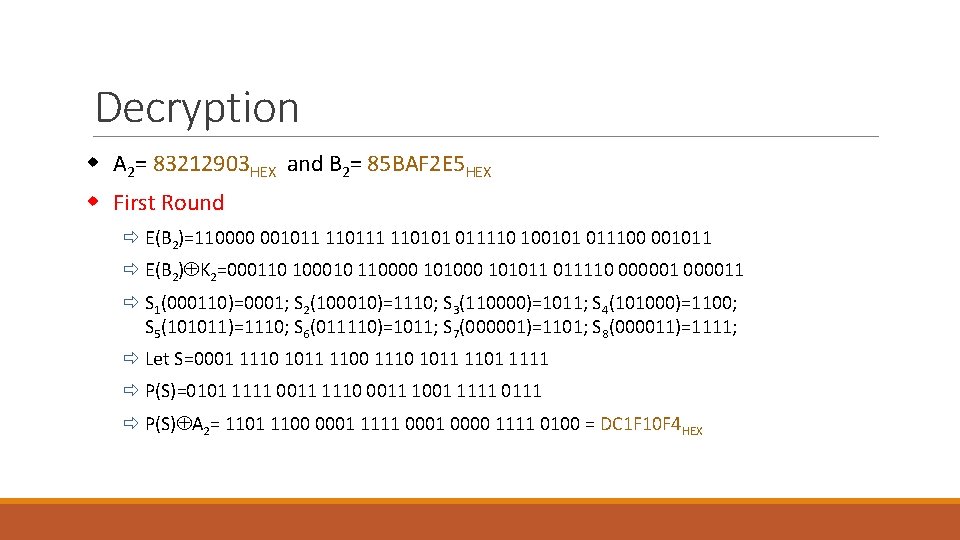
Decryption w A 2= 83212903 HEX and B 2= 85 BAF 2 E 5 HEX w First Round ð E(B 2)=110000 001011 110101 011110 100101 011100 001011 ð E(B 2) K 2=000110 100010 110000 101011 011110 0000011 ð S 1(000110)=0001; S 2(100010)=1110; S 3(110000)=1011; S 4(101000)=1100; S 5(101011)=1110; S 6(011110)=1011; S 7(000001)=1101; S 8(000011)=1111; ð Let S=0001 1110 1011 1100 1110 1011 1101 1111 ð P(S)=0101 1111 0011 1110 0011 1001 1111 0111 ð P(S) A 2= 1101 1100 0001 1111 0000 1111 0100 = DC 1 F 10 F 4 HEX
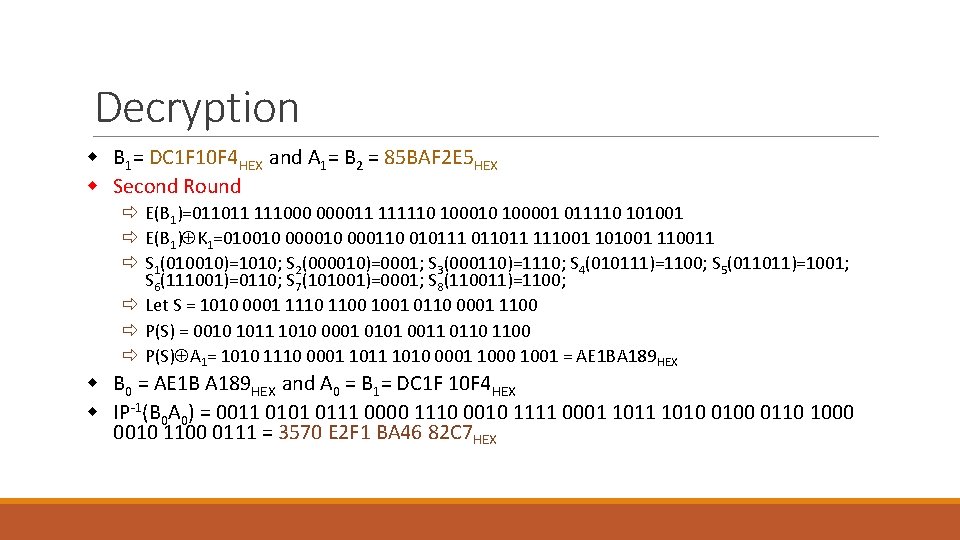
Decryption w B 1= DC 1 F 10 F 4 HEX and A 1= B 2 = 85 BAF 2 E 5 HEX w Second Round ð E(B 1)=011011 111000 000011 111110 100001 011110 101001 ð E(B 1) K 1=010010 000110 010111 011011 111001 101001 110011 ð S 1(010010)=1010; S 2(000010)=0001; S 3(000110)=1110; S 4(010111)=1100; S 5(011011)=1001; S 6(111001)=0110; S 7(101001)=0001; S 8(110011)=1100; ð Let S = 1010 0001 1110 1100 1001 0110 0001 1100 ð P(S) = 0010 1011 1010 0001 0101 0011 0110 1100 ð P(S) A 1= 1010 1110 0001 1010 0001 1000 1001 = AE 1 BA 189 HEX w B 0 = AE 1 B A 189 HEX and A 0 = B 1= DC 1 F 10 F 4 HEX w IP-1(B 0 A 0) = 0011 0101 0111 0000 1110 0010 1111 0001 1010 0100 0110 1000 0010 1100 0111 = 3570 E 2 F 1 BA 46 82 C 7 HEX
Reading “Cryptography and Network Security Principles and Practices”, Fourth Edition by William Stallings Chapter 3
- Slides: 64