Public Key Cryptography and RSA Principles of Public
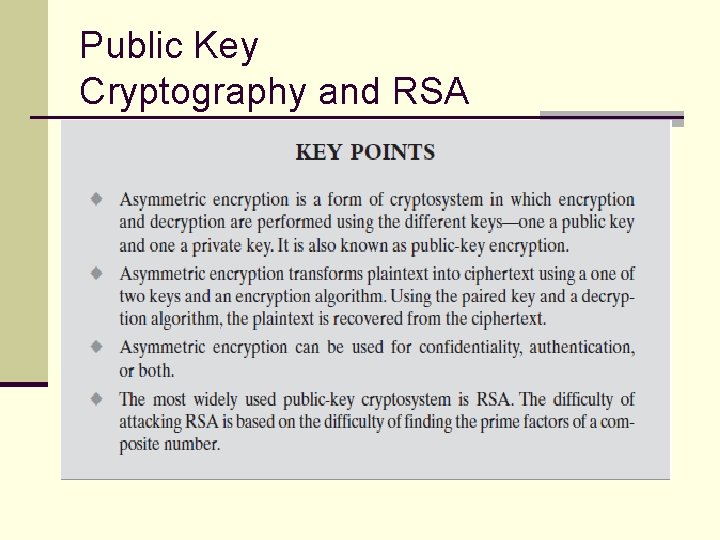
Public Key Cryptography and RSA
Principles of Public Key Crypto Systems v Private-Key Cryptography n traditional private/secret/single key cryptography n n n uses one key shared by both sender and receiver if this key is disclosed communications are compromised also is symmetric, parties are equal hence does not protect sender from receiver forging a message & claiming is sent by sender.
Principles of Public Key Crypto Systems v Public-Key Cryptography n n n probably most significant advance in the 3000 year history of cryptography uses two keys – a public & a private key asymmetric since parties are not equal uses clever application of number theoretic concepts to function complements rather than replaces private key crypto
Principles of Public Key cryptosystems v public-key/two-key/asymmetric cryptography involves the use of two keys: n a public-key, which may be known by anybody, and can be used to encrypt messages, and verify signatures n a private-key, known only to the recipient, used to decrypt messages, and sign (create) signatures v is asymmetric because n those who encrypt messages or verify signatures cannot decrypt messages or create signatures.
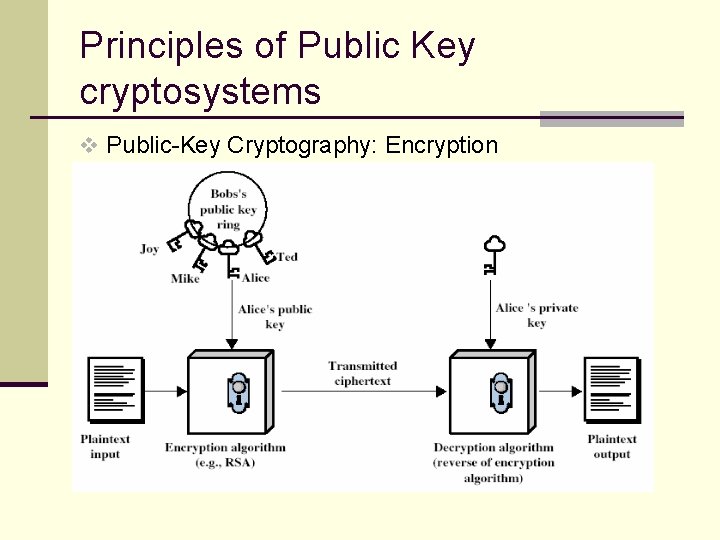
Principles of Public Key cryptosystems v Public-Key Cryptography: Encryption
Principles of Public Key cryptosystems n 1. Each system generates a pair of keys. n 2. Each system publishes its encryption key (public key) keeping its companion key private. n 3. If A wishes to send a message to B it encrypts the message using B’s public key. n 4. When B receives the message, it decrypts the message using its private key. No one else can decrypt the message because only B knows its private key.
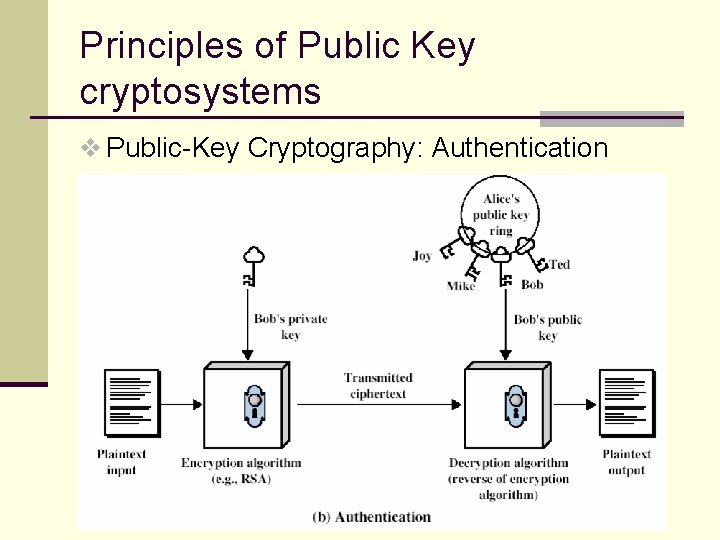
Principles of Public Key cryptosystems v Public-Key Cryptography: Authentication
Principles of Public Key Crypto Systems v Why Public-Key Cryptography? n developed to address two key issues: n n n key distribution – how to have secure communications in general without having to trust a KDC with your key digital signatures – how to verify a message comes intact from the claimed sender public invention due to Whitfield Diffie & Martin Hellman at Stanford Uni in 1976 n known earlier in classified community
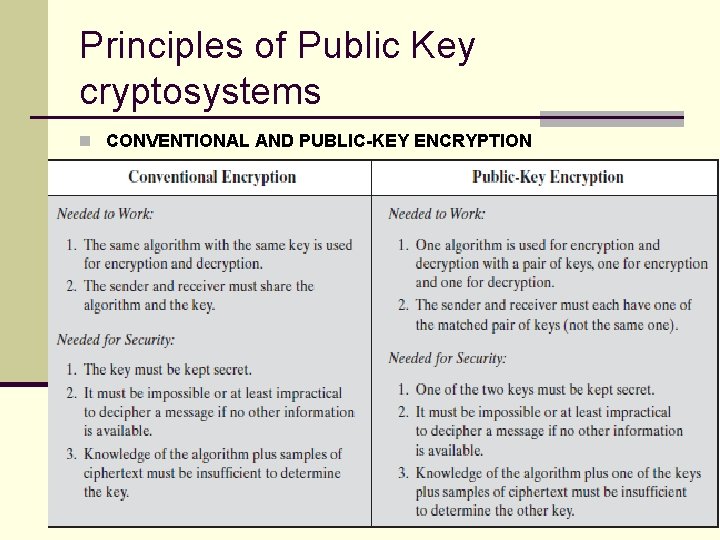
Principles of Public Key cryptosystems n CONVENTIONAL AND PUBLIC-KEY ENCRYPTION
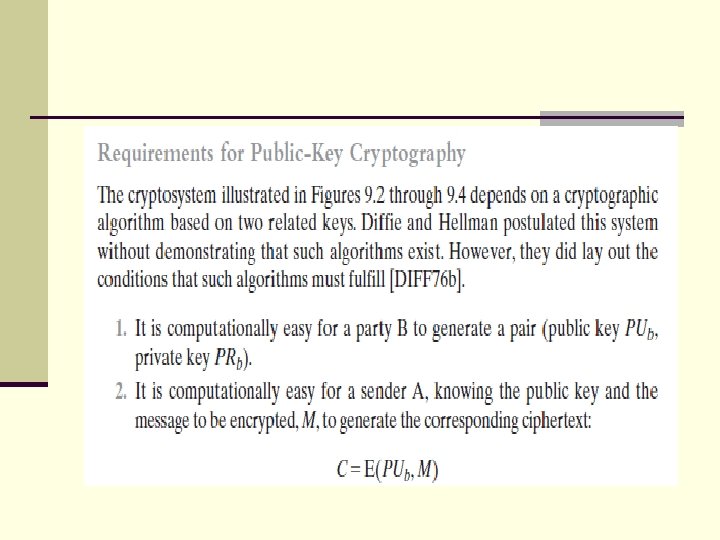
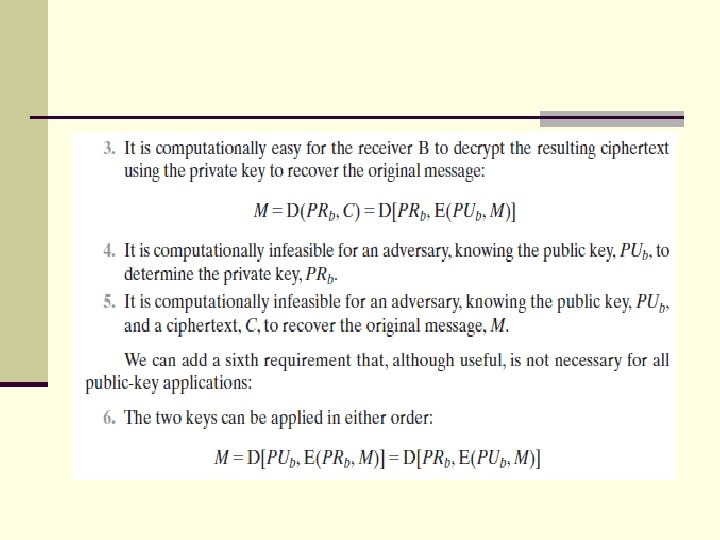
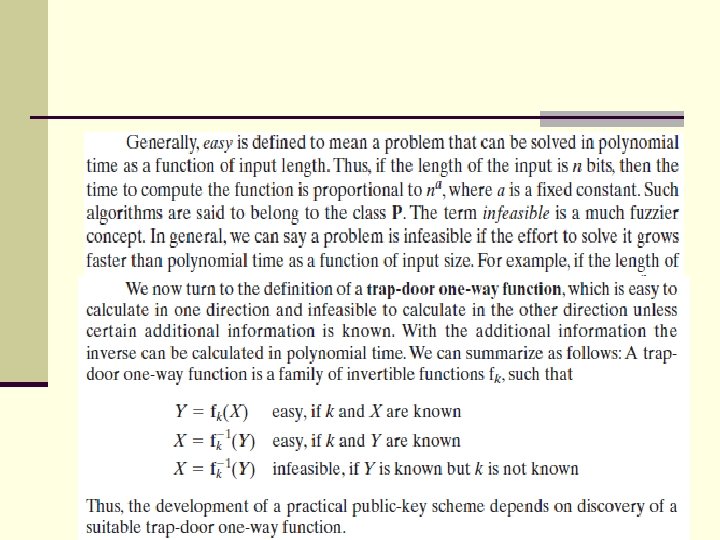
Principles of Public Key Crypto Systems v Public-Key Characteristics n Public-Key algorithms rely on two keys with the characteristics that it is: n n n computationally infeasible to find decryption key knowing only algorithm & encryption key computationally easy to en/decrypt messages when the relevant (en/decrypt) key is known either of the two related keys can be used for encryption, with the other used for decryption (in some schemes)
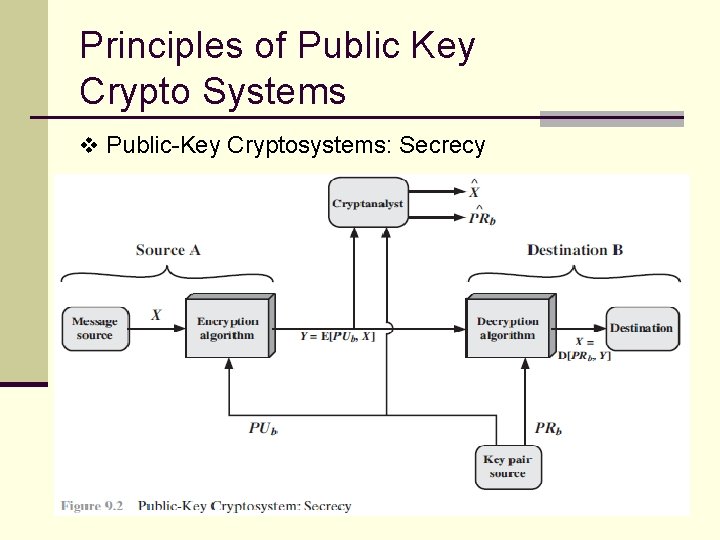
Principles of Public Key Crypto Systems v Public-Key Cryptosystems: Secrecy
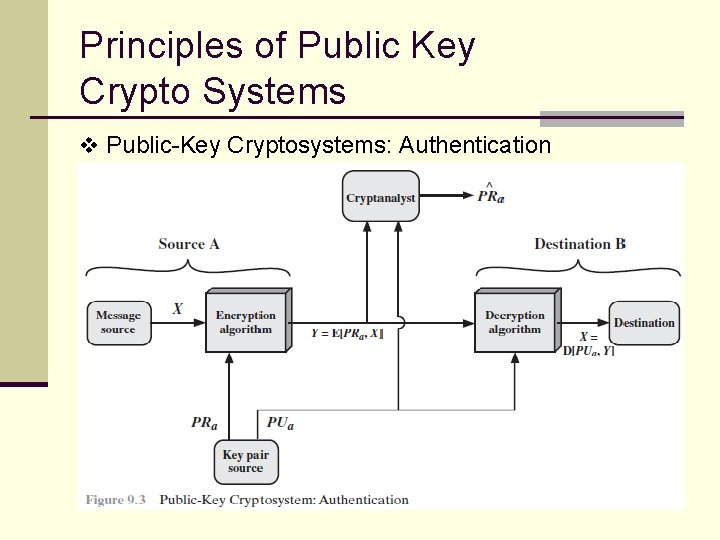
Principles of Public Key Crypto Systems v Public-Key Cryptosystems: Authentication
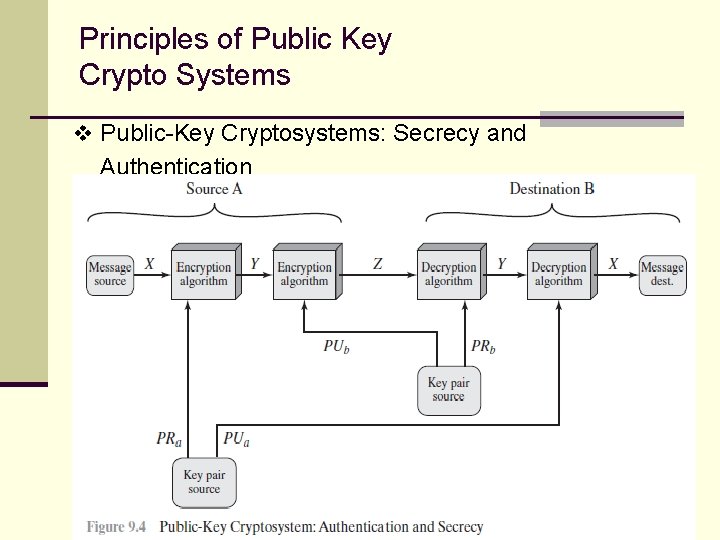
Principles of Public Key Crypto Systems v Public-Key Cryptosystems: Secrecy and Authentication
Principles of Public Key Crypto Systems v Public-Key Applications n can classify uses into 3 categories: n encryption/decryption (provide secrecy) n digital signatures (provide authentication) n key exchange (of session keys) n some algorithms are suitable for all uses, others are specific to one.
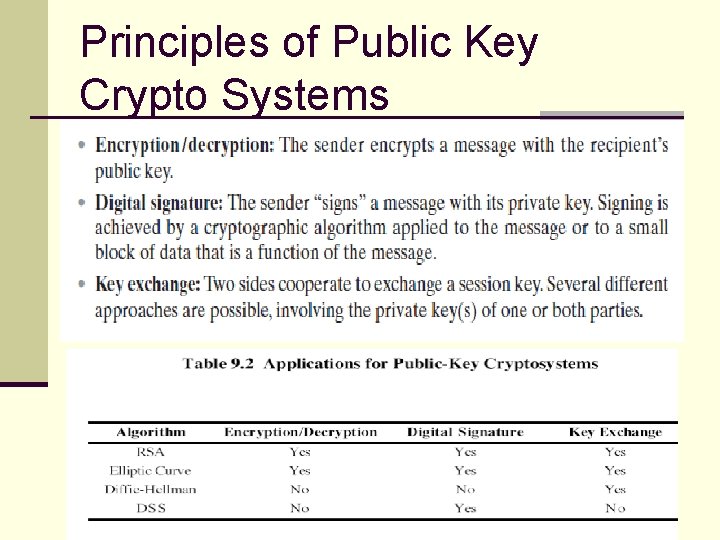
Principles of Public Key Crypto Systems
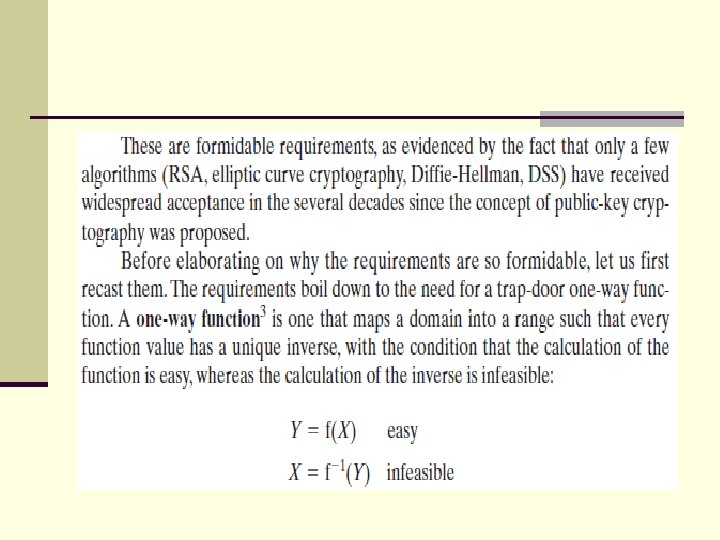
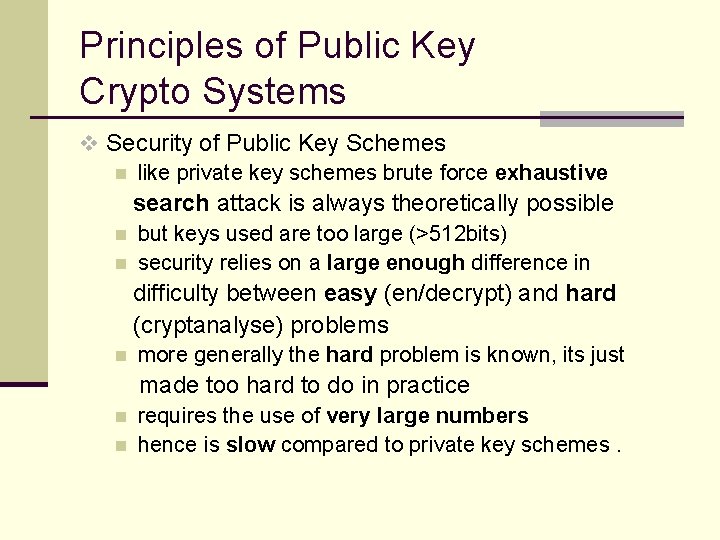
Principles of Public Key Crypto Systems v Security of Public Key Schemes n like private key schemes brute force exhaustive search attack is always theoretically possible n n but keys used are too large (>512 bits) security relies on a large enough difference in difficulty between easy (en/decrypt) and hard (cryptanalyse) problems n more generally the hard problem is known, its just made too hard to do in practice n n requires the use of very large numbers hence is slow compared to private key schemes.
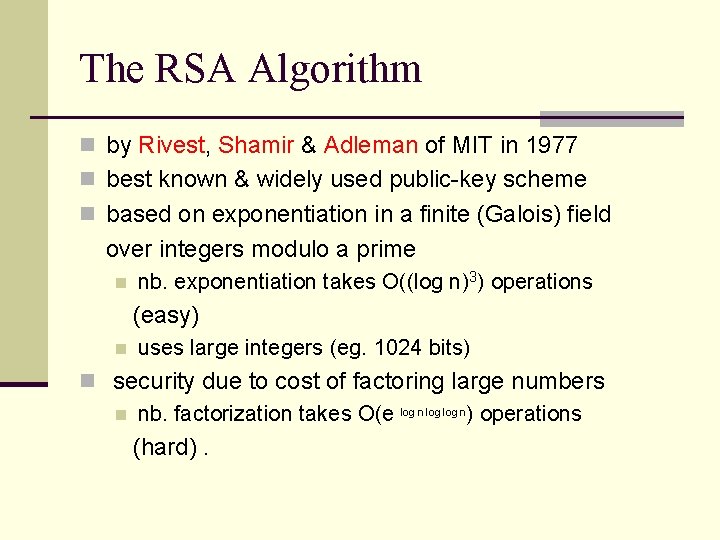
The RSA Algorithm n by Rivest, Shamir & Adleman of MIT in 1977 n best known & widely used public-key scheme n based on exponentiation in a finite (Galois) field over integers modulo a prime n nb. exponentiation takes O((log n)3) operations (easy) n uses large integers (eg. 1024 bits) n security due to cost of factoring large numbers n nb. factorization takes O(e log n) operations (hard).
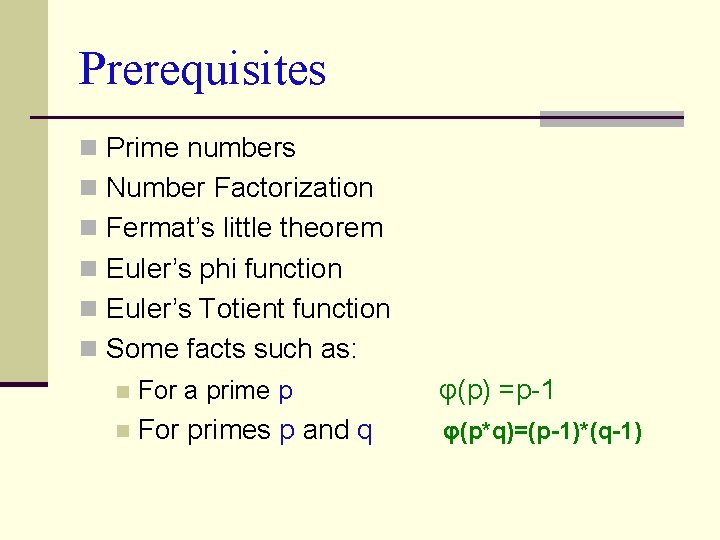
Prerequisites n Prime numbers n Number Factorization n Fermat’s little theorem n Euler’s phi function n Euler’s Totient function n Some facts such as: n For a prime p φ(p) =p-1 n For primes p and q φ(p*q)=(p-1)*(q-1)
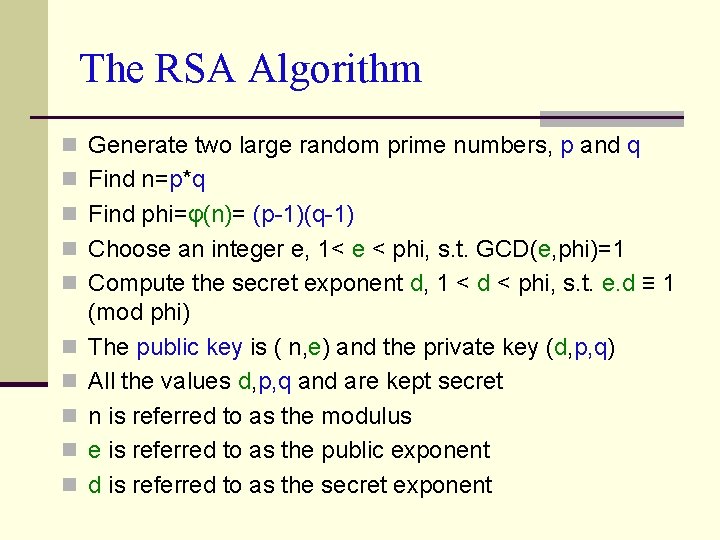
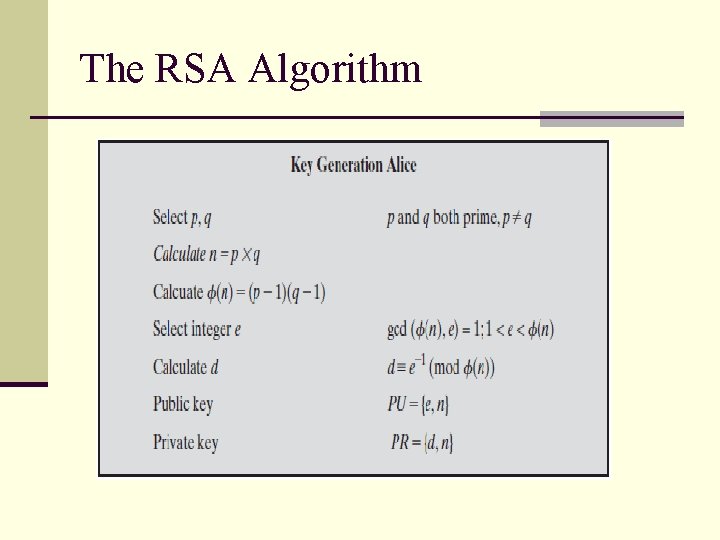
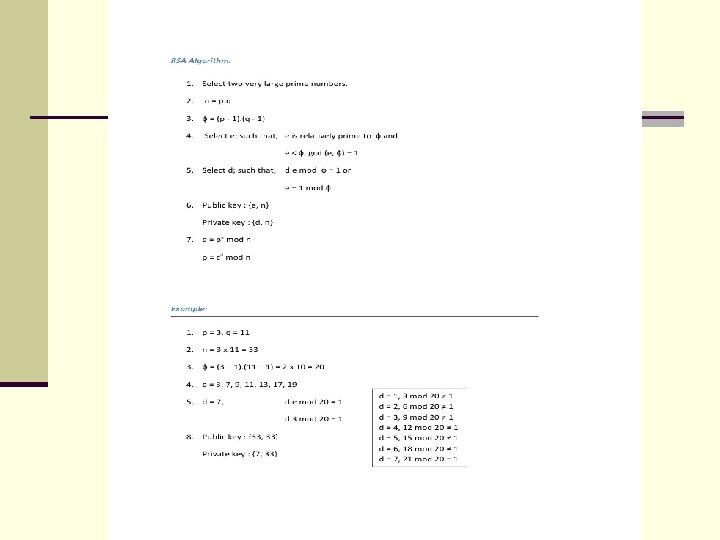
The RSA Algorithm n Generate two large random prime numbers, p and q n Find n=p*q n Find phi=φ(n)= (p-1)(q-1) n Choose an integer e, 1< e < phi, s. t. GCD(e, phi)=1 n Compute the secret exponent d, 1 < d < phi, s. t. e. d ≡ 1 n n n (mod phi) The public key is ( n, e) and the private key (d, p, q) All the values d, p, q and are kept secret n is referred to as the modulus e is referred to as the public exponent d is referred to as the secret exponent
The RSA Algorithm
The RSA Algorithm
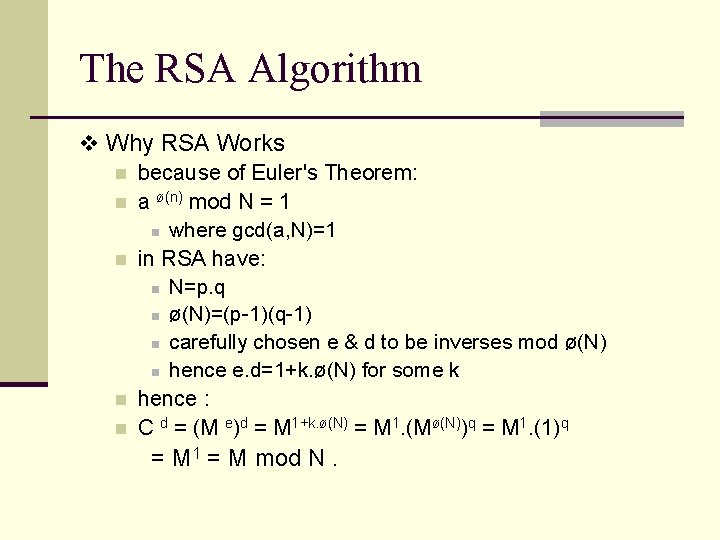
The RSA Algorithm v Why RSA Works n because of Euler's Theorem: n a ø(n) mod N = 1 n where gcd(a, N)=1 n in RSA have: n N=p. q n ø(N)=(p-1)(q-1) n carefully chosen e & d to be inverses mod ø(N) n hence e. d=1+k. ø(N) for some k n hence : n C d = (M e)d = M 1+k. ø(N) = M 1. (Mø(N))q = M 1. (1)q = M 1 = M mod N.
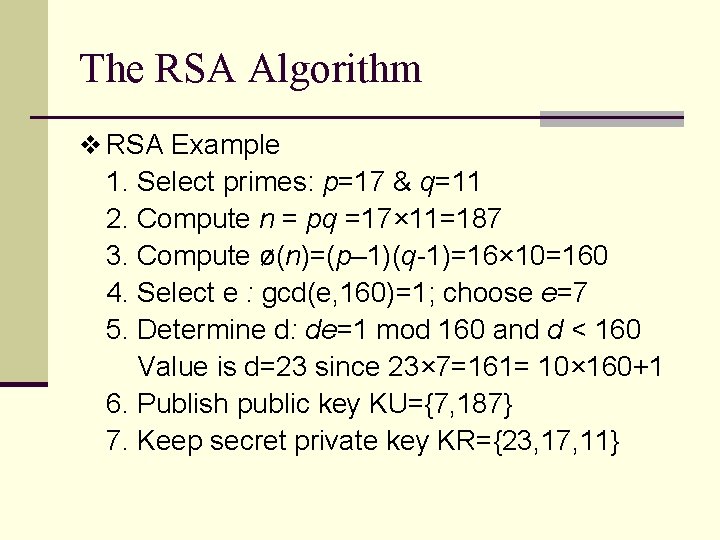
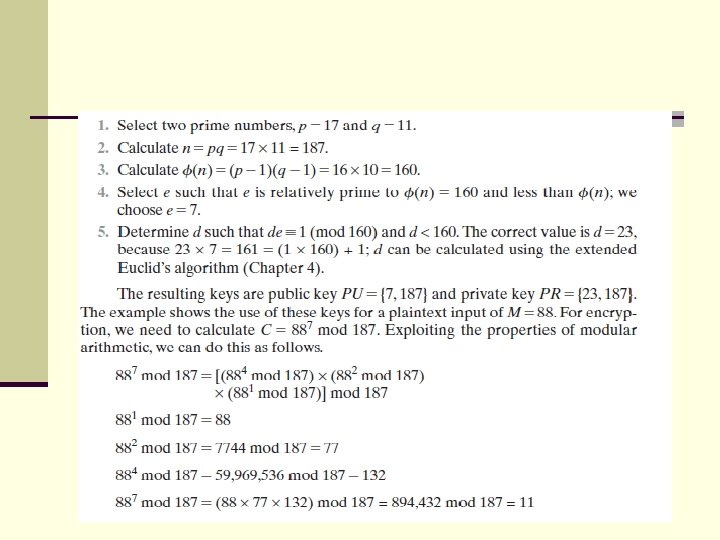
The RSA Algorithm v RSA Example 1. Select primes: p=17 & q=11 2. Compute n = pq =17× 11=187 3. Compute ø(n)=(p– 1)(q-1)=16× 10=160 4. Select e : gcd(e, 160)=1; choose e=7 5. Determine d: de=1 mod 160 and d < 160 Value is d=23 since 23× 7=161= 10× 160+1 6. Publish public key KU={7, 187} 7. Keep secret private key KR={23, 17, 11}
Why is RSA Special? n Given two large prime numbers p and q, a composite number n can be compute as : n=p*q n But, given such n, there is no known algorithm to efficiently find the p and q (i. e. the prime factors of n )
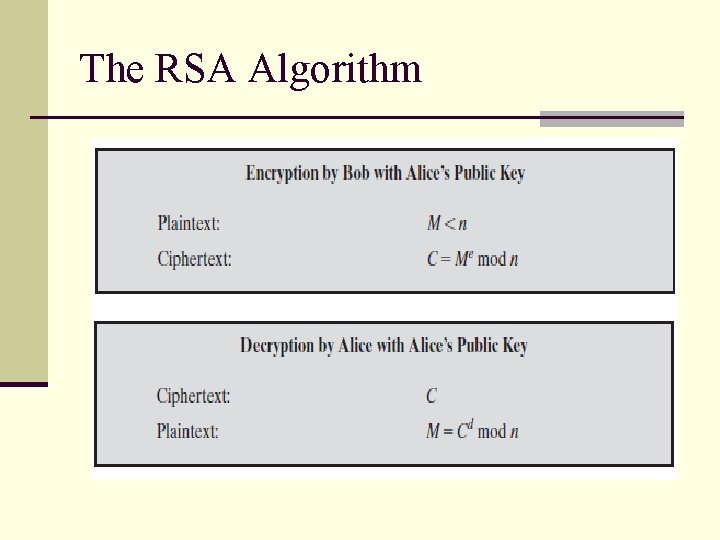
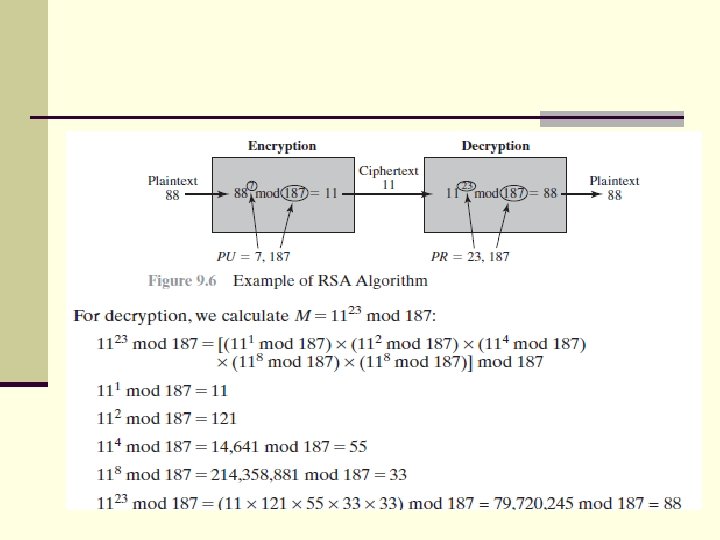
The RSA Algorithm v sample RSA encryption/decryption is: n given message M = 88 (nb. 88<187) n encryption: C = 887 mod 187 = 11 n decryption: M = 1123 mod 187 = 88.
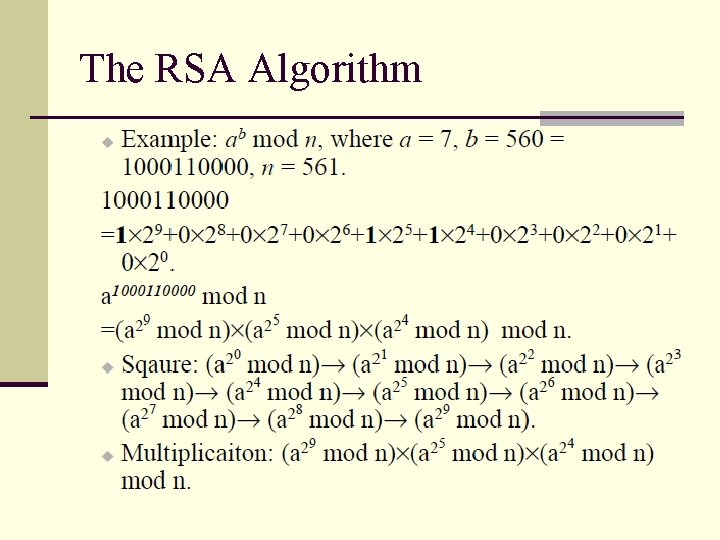
The RSA Algorithm v Computational Aspects: Encryption and Decryption n Square and Multiply Algorithm for Exponentiation n a fast, efficient algorithm for exponentiation n concept is based on repeatedly squaring base n and multiplying in the ones that are needed to compute the result n look at binary representation of exponent n only takes O(log 2 n) multiples for number n 5 4 1 n eg. 7 = 7. 7 = 3. 7 = 10 mod 11 129 = 3128. 31 = 5. 3 = 4 mod 11 n eg. 3
The RSA Algorithm
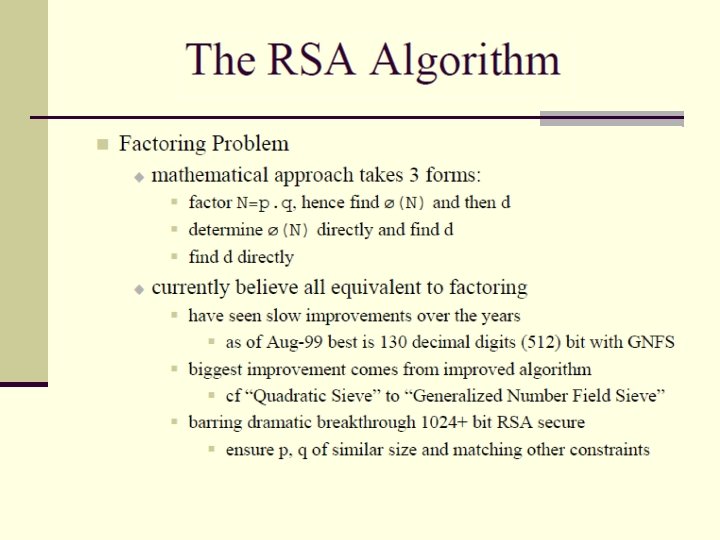
n Until the mid-1990 s, factoring attacks were made using an approach known as the quadratic sieve. n The attack on RSA-130 used a newer algorithm, the generalized number field sieve (GNFS). n The threat to larger key sizes is twofold: The continuing increase in computing power, n The continuing refinement of factoring algorithms. n
n A related algorithm, the special number field sieve (SNFS), can factor numbers with a specialized form considerably faster than the GNFS. n We need to be careful in choosing a key size for RSA. For a near future, a key size in the range of 1024 to 2048 bits seems reasonable.
RSA Algorithm: Timing attack n Timing attacks are applicable not just to RSA, but to other public-key cryptography systems. n This attack is alarming for two reasons: n It comes from a completely unexpected direction, and it is a ciphertext-only attack.
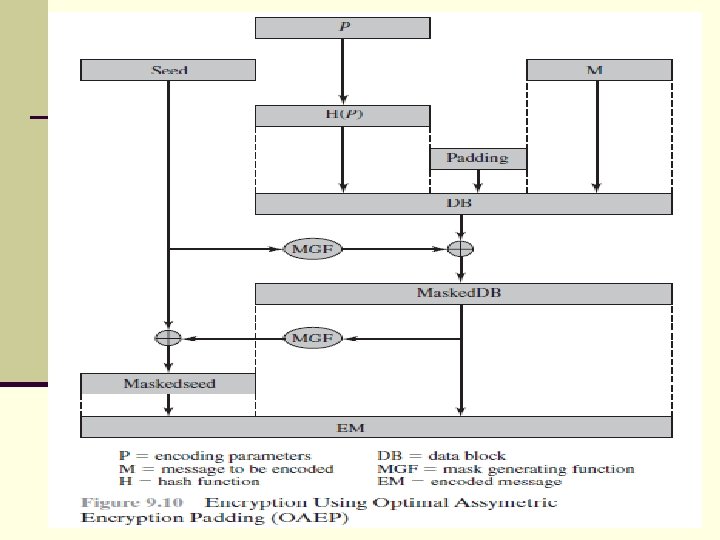
The security of RSA: OAEP encryption n To counter such attacks RSA security Inc. , recommends modifying the plain text using a procedure known as optimal asymmetric encryption padding (OAEP). Step 1: n The message M to be encrypted is padded. n A set of optional parameters P is passed through a hash function H. The output is then padded with zeros to get the desired length in the overall data block (DB).
The security of RSA: OAEP encryption Step 2: n A random seed is generated and passed through another hash function, called the mask generating function (MGF). n The resulting hash value is bit-by-bit XORed with DB to produce a masked. DB. n The masked. DB is in turn passed through the MGF to form a hash that is XORed with the seed to produce the masked seed.
The security of RSA: OAEP encryption Step 3: n The concatenation of the maskedseed and the masked. DB forms the encoded message EM. n The resulting hash value is bit-by-bit XORed with DB to produce a masked. DB. n The EM includes the padded message, masked by the seed, and the seed, masked by the masked. DB. n The EM is then encrypted using RSA.
Hash function definition: n Hash functions are extremely useful and appear in almost all information security applications. n A hash function is a mathematical function that converts a numerical input value into another compressed numerical value. The input to the hash function is of arbitrary length but output is always of fixed length. n Values returned by a hash function are called message digest or simply hash values.
- Slides: 50