AES Rijndael Outline Introduction Mathematical background Specification Motivation

AES: Rijndael 林志信 王偉全
Outline Introduction Mathematical background Specification Motivation for design choice Conclusion Discussion
Introduction AES (Advanced Encryption Standard) n n Motivation 01/02/97 NIST announced the initiation. w w w w Security Computational efficiency Memory requirement Hardware and software suitability Simplicity Flexibility Licensing requirements
Introduction(Cont. ) n n 10/02/00 NIST announced the AES algorithm is Rijndael w Joan Daemen & Vincent Rijmen w Rijndael (Rijmen & Daemen)
Mathematical background The field GF(28) n n n Example: (57)16 x 6+x 4+x 2+x+1 Addition Multiplication by x Polynomials with coefficients in GF(28) n Multiplication by x
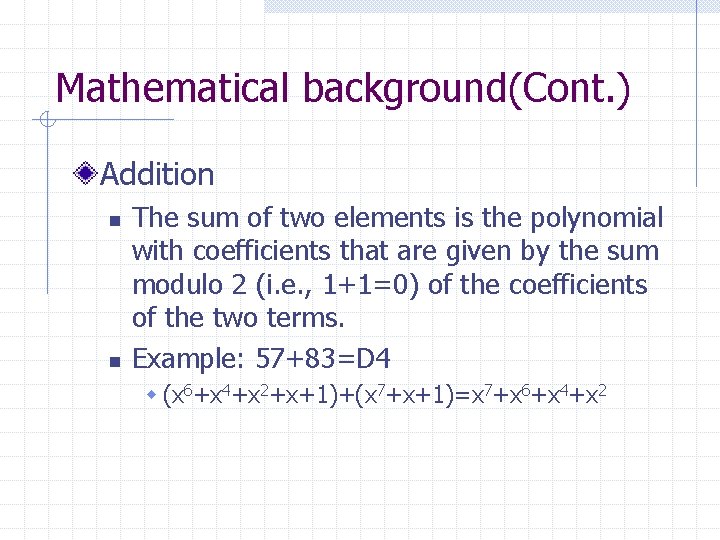
Mathematical background(Cont. ) Addition n n The sum of two elements is the polynomial with coefficients that are given by the sum modulo 2 (i. e. , 1+1=0) of the coefficients of the two terms. Example: 57+83=D 4 w (x 6+x 4+x 2+x+1)+(x 7+x+1)=x 7+x 6+x 4+x 2
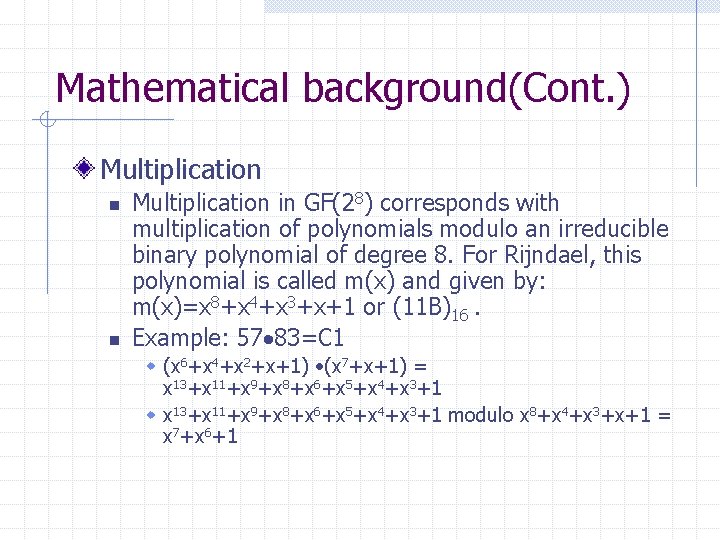
Mathematical background(Cont. ) Multiplication n n Multiplication in GF(28) corresponds with multiplication of polynomials modulo an irreducible binary polynomial of degree 8. For Rijndael, this polynomial is called m(x) and given by: m(x)=x 8+x 4+x 3+x+1 or (11 B)16. Example: 57 83=C 1 w (x 6+x 4+x 2+x+1) (x 7+x+1) = x 13+x 11+x 9+x 8+x 6+x 5+x 4+x 3+1 w x 13+x 11+x 9+x 8+x 6+x 5+x 4+x 3+1 modulo x 8+x 4+x 3+x+1 = x 7+x 6+1
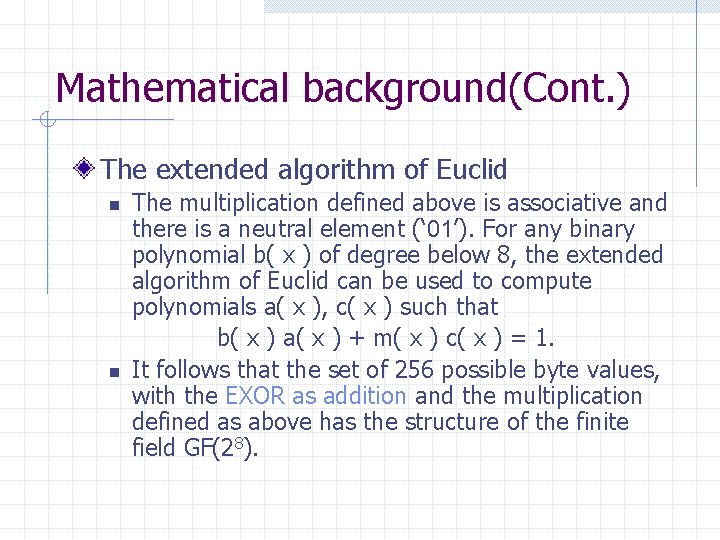
Mathematical background(Cont. ) The extended algorithm of Euclid n n The multiplication defined above is associative and there is a neutral element (‘ 01’). For any binary polynomial b( x ) of degree below 8, the extended algorithm of Euclid can be used to compute polynomials a( x ), c( x ) such that b( x ) a( x ) + m( x ) c( x ) = 1. It follows that the set of 256 possible byte values, with the EXOR as addition and the multiplication defined as above has the structure of the finite field GF(28).
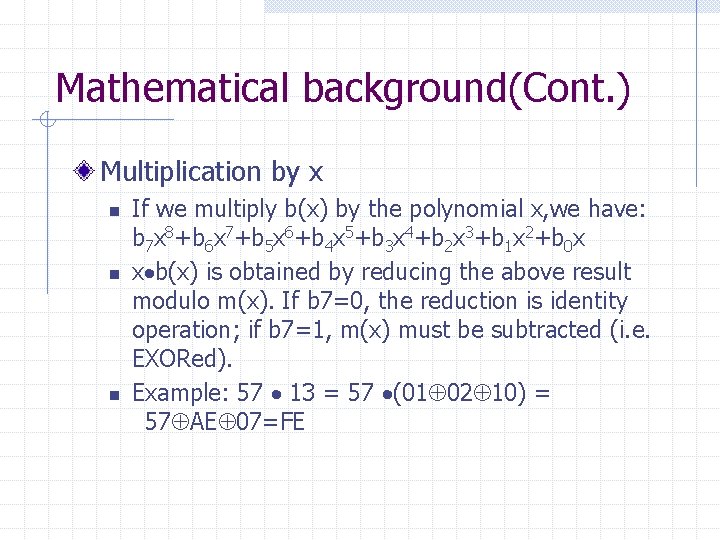
Mathematical background(Cont. ) Multiplication by x n n n If we multiply b(x) by the polynomial x, we have: b 7 x 8+b 6 x 7+b 5 x 6+b 4 x 5+b 3 x 4+b 2 x 3+b 1 x 2+b 0 x x b(x) is obtained by reducing the above result modulo m(x). If b 7=0, the reduction is identity operation; if b 7=1, m(x) must be subtracted (i. e. EXORed). Example: 57 13 = 57 (01 02 10) = 57 AE 07=FE

Mathematical background(Cont. ) Polynomials with coefficients in GF(28) n Assume we have two polynomials over GF(28): a(x)=a 3 x 3+a 2 x 2+a 1 x+a 0 b(x)=b 3 x 3+b 2 x 2+b 1 x+b 0 n c(x)= a(x) * b(x) = c 6 x 6+c 5 x 5+c 4 x 4+c 3 x 3+c 2 x 2+c 1 x+c 0
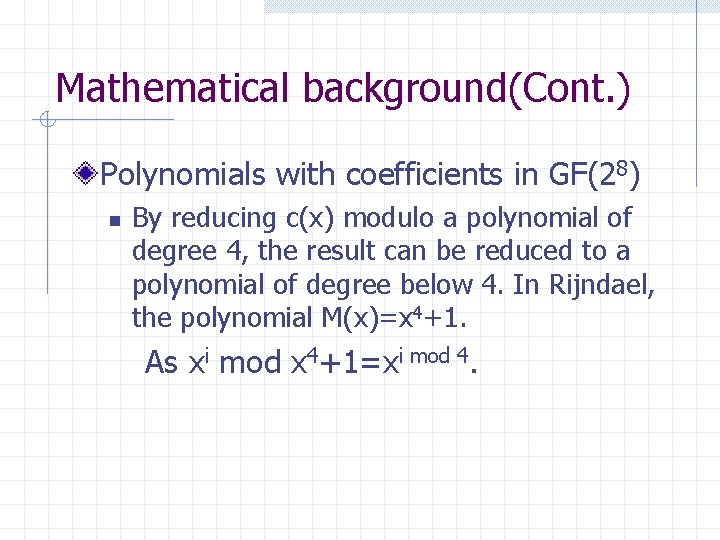
Mathematical background(Cont. ) Polynomials with coefficients in GF(28) n By reducing c(x) modulo a polynomial of degree 4, the result can be reduced to a polynomial of degree below 4. In Rijndael, the polynomial M(x)=x 4+1. As xi mod x 4+1=xi mod 4.
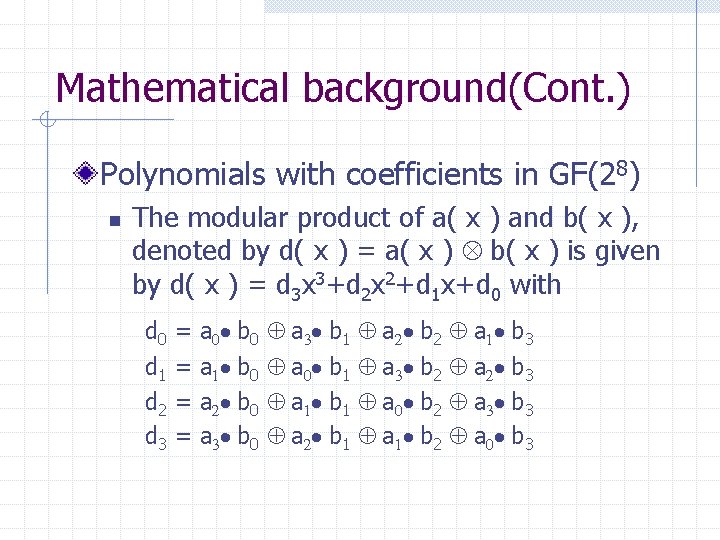
Mathematical background(Cont. ) Polynomials with coefficients in GF(28) n The modular product of a( x ) and b( x ), denoted by d( x ) = a( x ) Ä b( x ) is given by d( x ) = d 3 x 3+d 2 x 2+d 1 x+d 0 with d 0 d 1 d 2 d 3 = = a 0 b 0 a 1 b 0 a 2 b 0 a 3 b 0 a 3 b 1 a 0 b 1 a 1 b 1 a 2 b 2 a 3 b 2 a 0 b 2 a 1 b 3 a 2 b 3 a 3 b 3 a 0 b 3
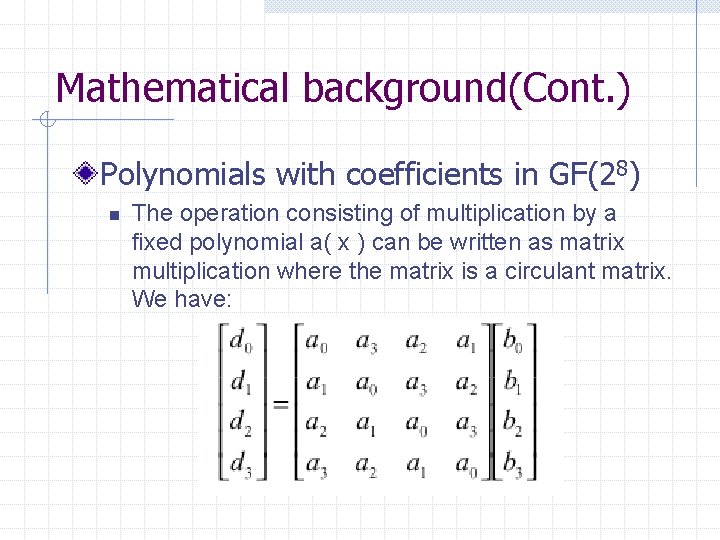
Mathematical background(Cont. ) Polynomials with coefficients in GF(28) n The operation consisting of multiplication by a fixed polynomial a( x ) can be written as matrix multiplication where the matrix is a circulant matrix. We have:
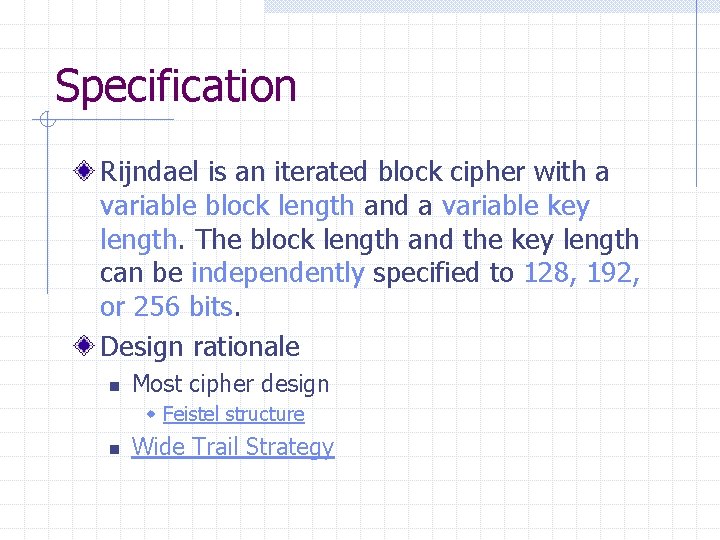
Specification Rijndael is an iterated block cipher with a variable block length and a variable key length. The block length and the key length can be independently specified to 128, 192, or 256 bits. Design rationale n Most cipher design w Feistel structure n Wide Trail Strategy
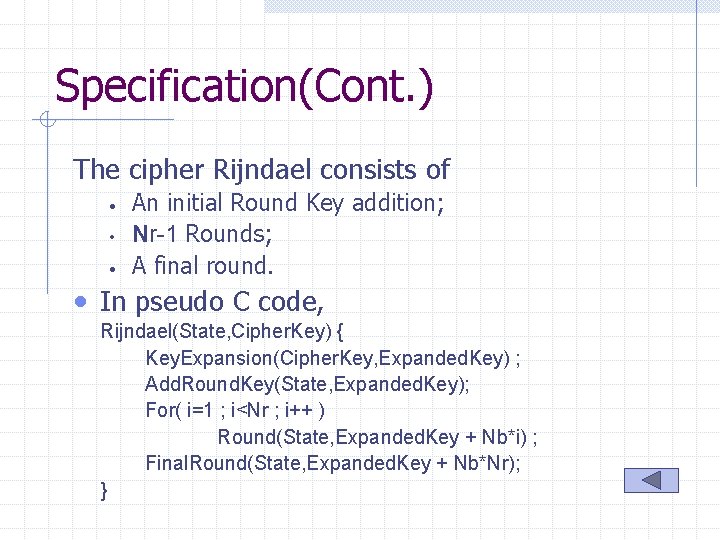
Specification(Cont. ) The cipher Rijndael consists of • • • An initial Round Key addition; Nr-1 Rounds; A final round. • In pseudo C code, Rijndael(State, Cipher. Key) { Key. Expansion(Cipher. Key, Expanded. Key) ; Add. Round. Key(State, Expanded. Key); For( i=1 ; i<Nr ; i++ ) Round(State, Expanded. Key + Nb*i) ; Final. Round(State, Expanded. Key + Nb*Nr); }
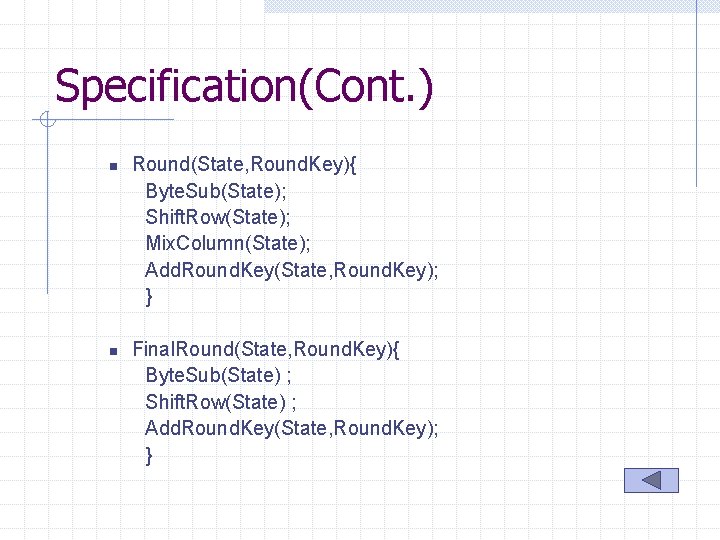
Specification(Cont. ) n n Round(State, Round. Key){ Byte. Sub(State); Shift. Row(State); Mix. Column(State); Add. Round. Key(State, Round. Key); } Final. Round(State, Round. Key){ Byte. Sub(State) ; Shift. Row(State) ; Add. Round. Key(State, Round. Key); }
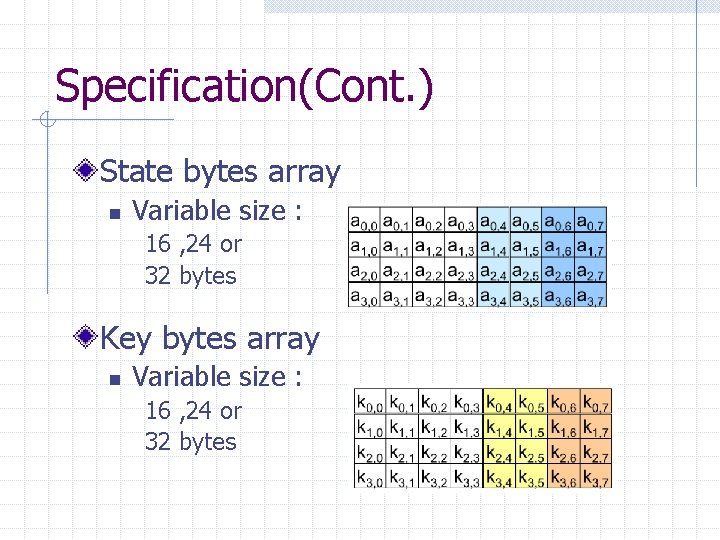
Specification(Cont. ) State bytes array n Variable size : 16 , 24 or 32 bytes Key bytes array n Variable size : 16 , 24 or 32 bytes
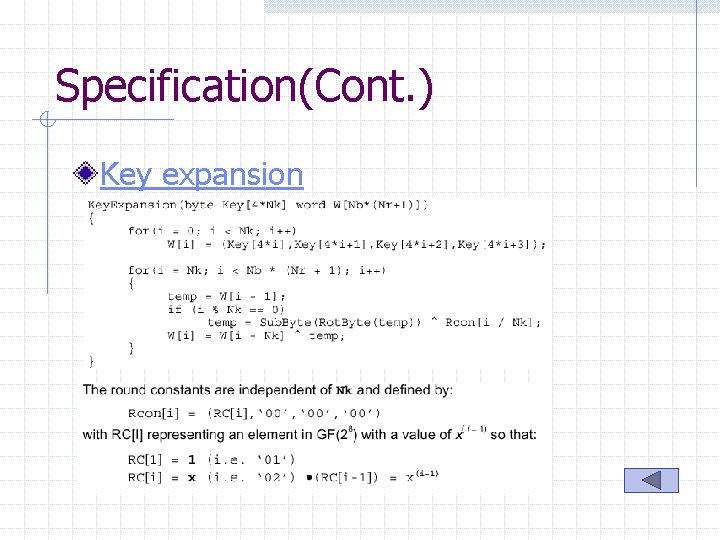
Specification(Cont. ) Key expansion
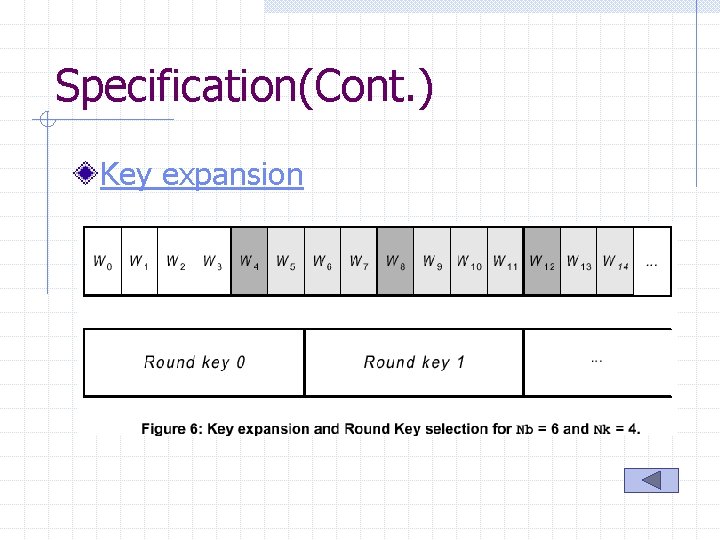
Specification(Cont. ) Key expansion
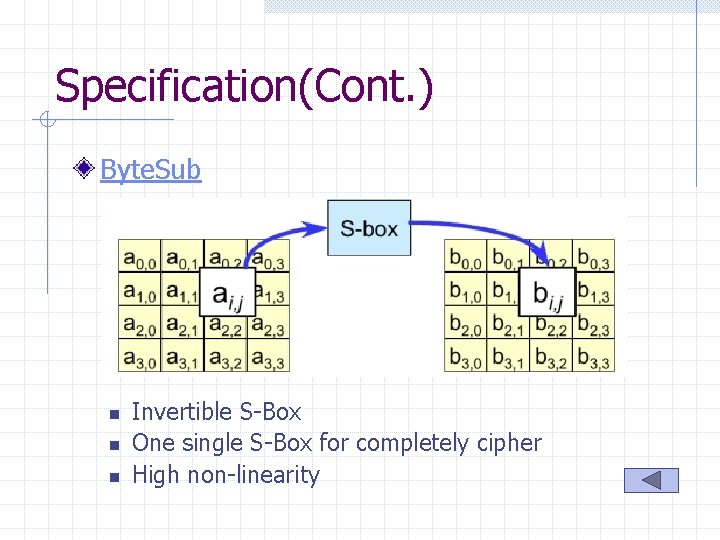
Specification(Cont. ) Byte. Sub n n n Invertible S-Box One single S-Box for completely cipher High non-linearity
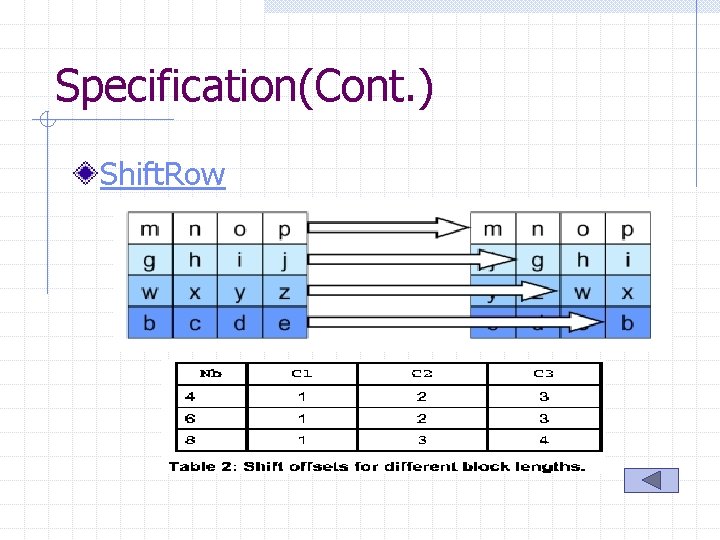
Specification(Cont. ) Shift. Row
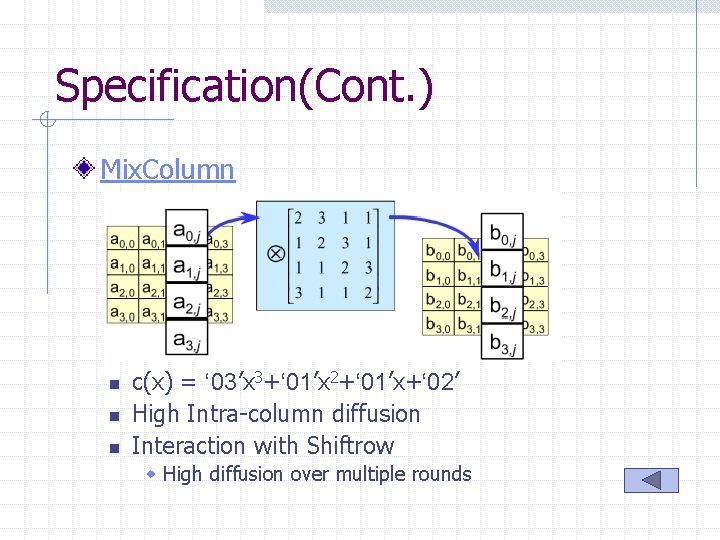
Specification(Cont. ) Mix. Column n c(x) = ‘ 03’x 3+‘ 01’x 2+‘ 01’x+‘ 02’ High Intra-column diffusion Interaction with Shiftrow w High diffusion over multiple rounds
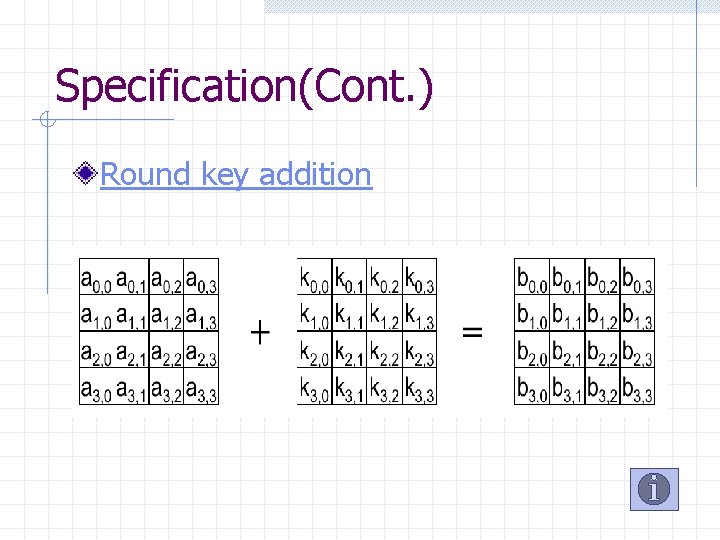
Specification(Cont. ) Round key addition
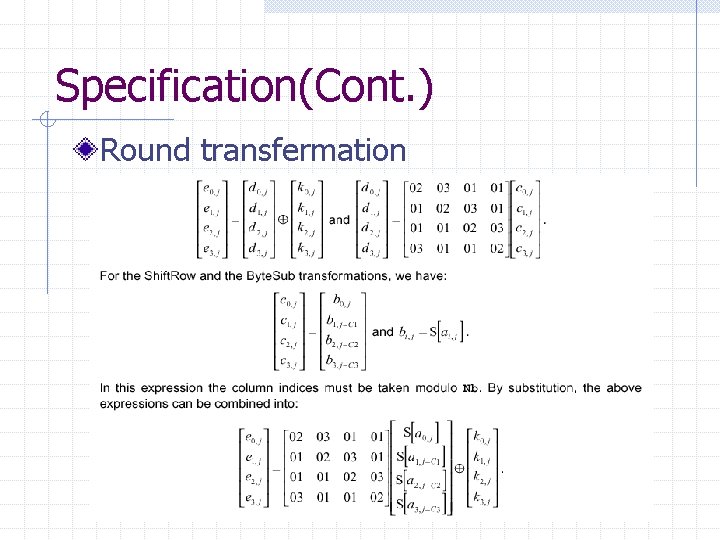
Specification(Cont. ) Round transfermation
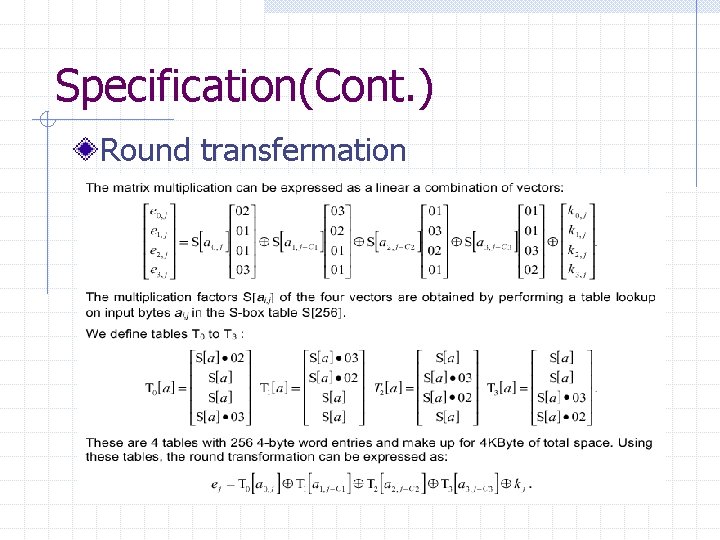
Specification(Cont. ) Round transfermation
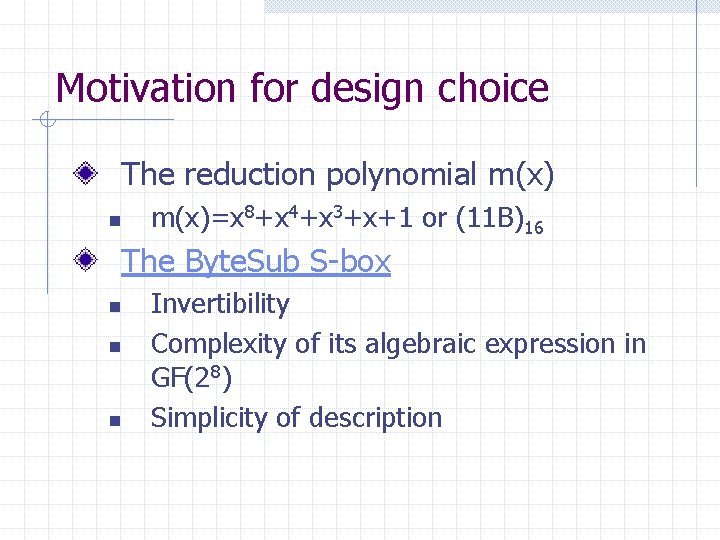
Motivation for design choice The reduction polynomial m(x) n m(x)=x 8+x 4+x 3+x+1 or (11 B)16 The Byte. Sub S-box n n n Invertibility Complexity of its algebraic expression in GF(28) Simplicity of description
Motivation for design choice The Mix. Column transformation n n n Invertibility Linearity in GF(2) Relevant diffusion power Speed on 8 -bit processors Symmetry Simplicity of description (Cont. )
Motivation for design choice (Cont. ) The Shift. Row offsets n n The four offsets are different and C 0 = 0 Simplicity The key expansion n Use a invertible transformation Diffusion of Cipher Key differences into the Round Keys Simplicity of description
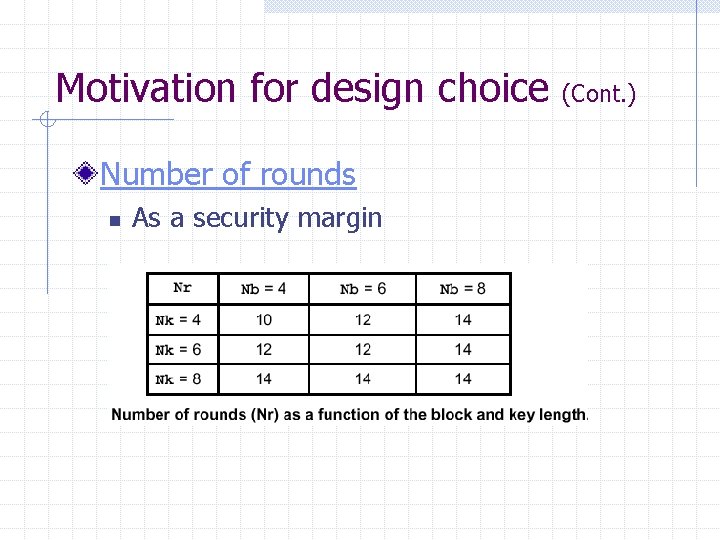
Motivation for design choice Number of rounds n As a security margin (Cont. )
Conclusion Rijndael has the symmetric and parallel structure. n n Gives implementer a lot of flexibility Have not allowed effective cryptanalytic attacks Rijndael is well adapted to modern processors. Rijndael is suited for Smart cards
Future Discussion Strength against known attacks n Differential cryptanalysis, linear cryptanalysis, and etc. Weak keys Application
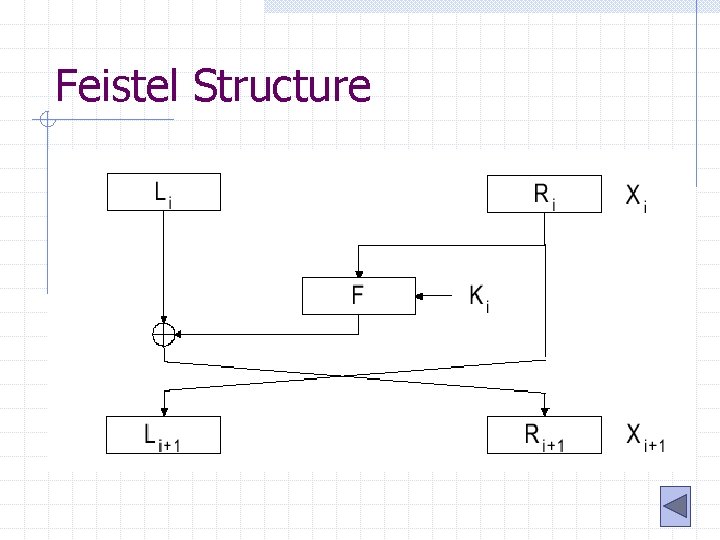
Feistel Structure
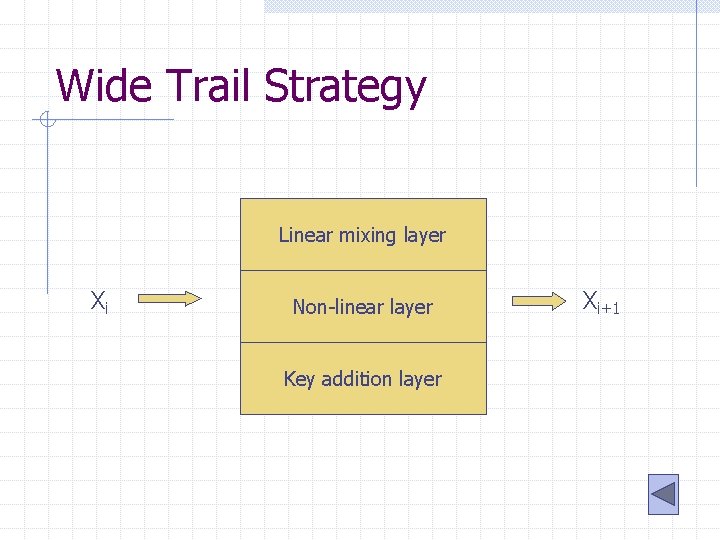
Wide Trail Strategy Linear mixing layer Xi Non-linear layer Key addition layer Xi+1
- Slides: 33