Unit 1 Security Basics Prepared by Gunjan Deshmukh
Unit 1: Security Basics Prepared by: Gunjan Deshmukh
Topics: 1) Information Security Concepts 2) Security Threats and Vulnerabilities 3) Security Architectures and 4) Operational Models, 5) Types of Security attacks, 6) Goals of Security, 7) Malicious code, 8) Intrusiondetection system (IDS): Need, Types, Limitations and Challenges, security and privacy.
Computer Security • Computer Security: The protection afforded to an automated information system in order to attain the applicable objectives of preserving the integrity, availability, and confidentiality of information system resources (includes hardware, software, firmware, information/data, and telecommunications).

Security Concepts Authenticity Accountability
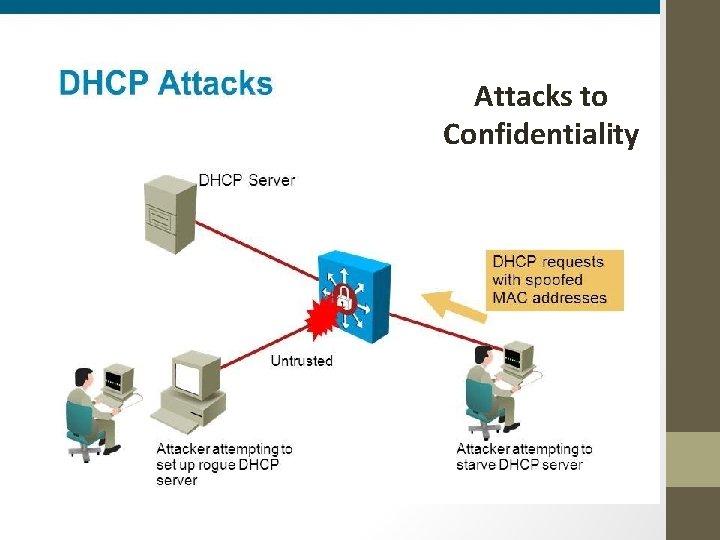
Attacks to Confidentiality
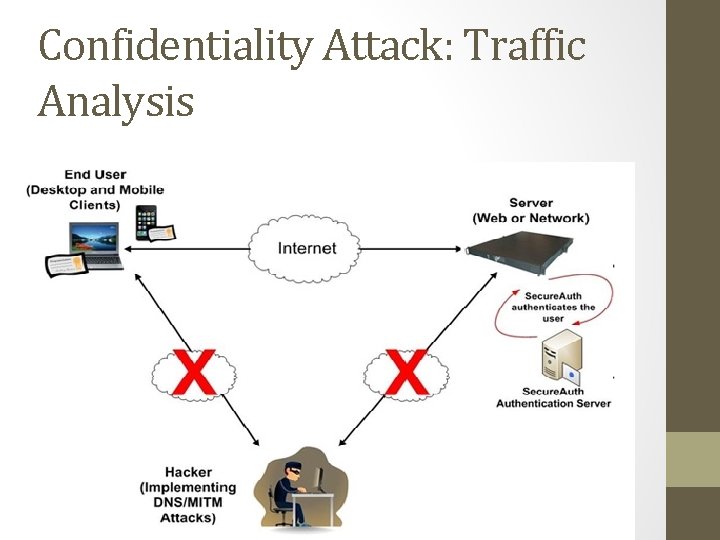
Confidentiality Attack: Traffic Analysis
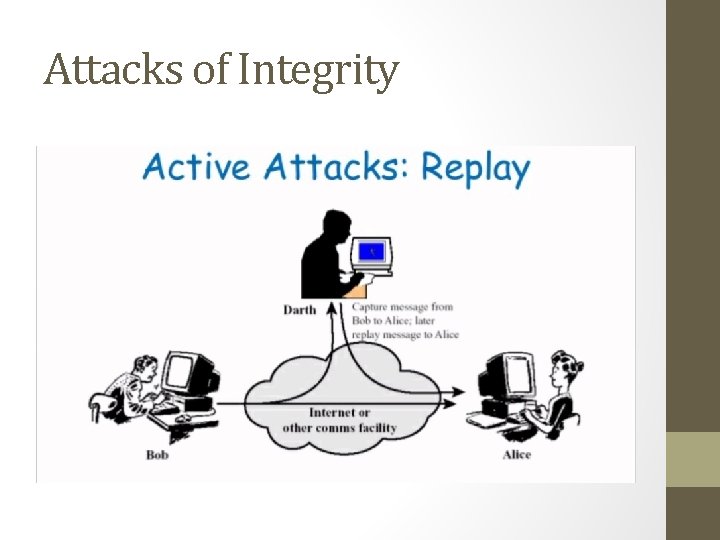
Attacks of Integrity
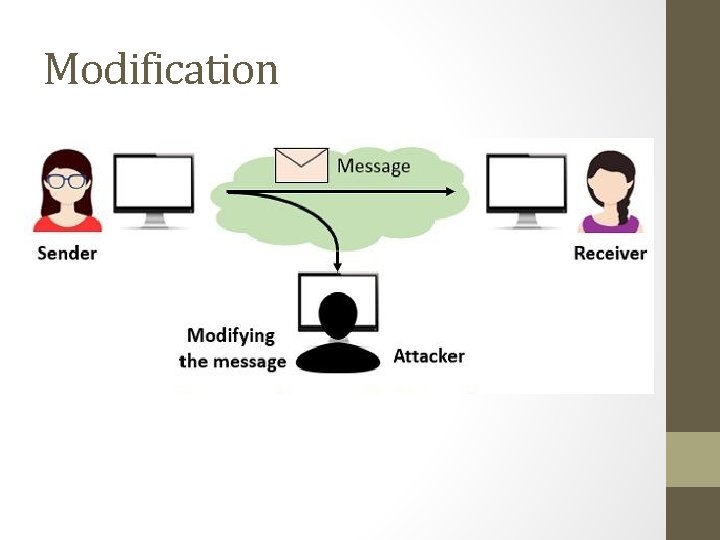
Modification
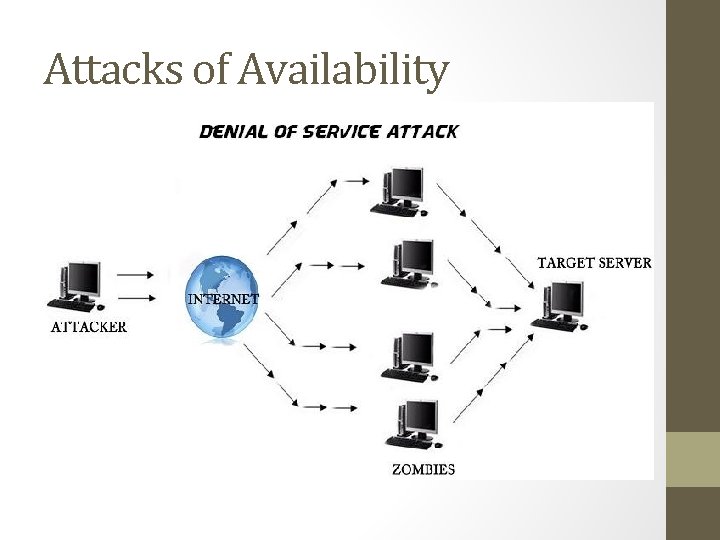
Attacks of Availability
Security Models and Architectures No Security through obscurity Hot Security Network Security OSI Security Model
OSI Security Model • The OSI security architecture is useful to managers as a way of organizing the task of providing security. • Because this architecture was developed as an international standard. • Computer and communications vendors have developed security features for their products and services that relate to this structured definition of services and mechanisms.
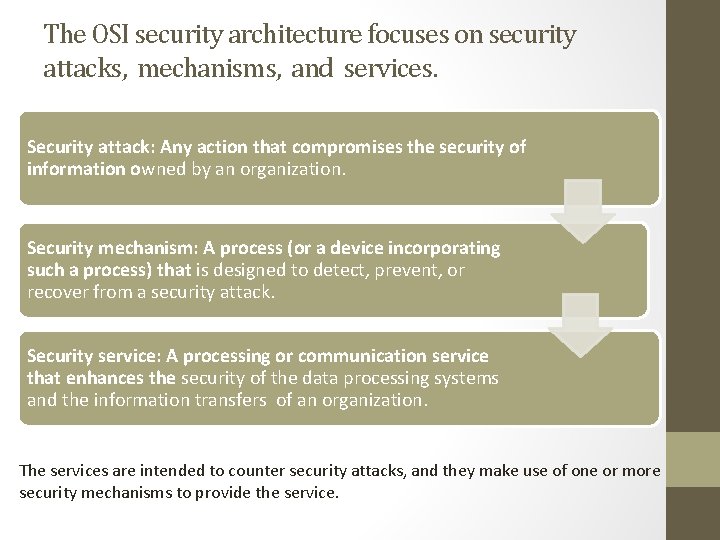
The OSI security architecture focuses on security attacks, mechanisms, and services. Security attack: Any action that compromises the security of information owned by an organization. Security mechanism: A process (or a device incorporating such a process) that is designed to detect, prevent, or recover from a security attack. Security service: A processing or communication service that enhances the security of the data processing systems and the information transfers of an organization. The services are intended to counter security attacks, and they make use of one or more security mechanisms to provide the service.
Security Threats and Vulnerabilities • Asset – People, property, and information. • People may include employees and customers along with other invited persons such as contractors or guests. • Property assets consist of both tangible and intangible items that can be assigned a value. • Intangible assets include reputation and proprietary information. Information may include databases, software code, critical company records, and many other intangible items. An asset is what we’re trying to protect.
Security Threats and Vulnerabilities • Threat – Anything that can exploit a vulnerability, intentionally or accidentally, and obtain, damage, or destroy an asset. A threat is what we’re trying to protect against.
Security Threats and Vulnerabilities • Vulnerability – Weaknesses or gaps in a security program that can be exploited by threats to gain unauthorized access to an asset. A vulnerability is a weakness or gap in our protection efforts.
Security Threats and Vulnerabilities • Risk – The potential for loss, damage or destruction of an asset as a result of a threat exploiting a vulnerability. Risk is the intersection of assets, threats, and vulnerabilities. A+T+V=R
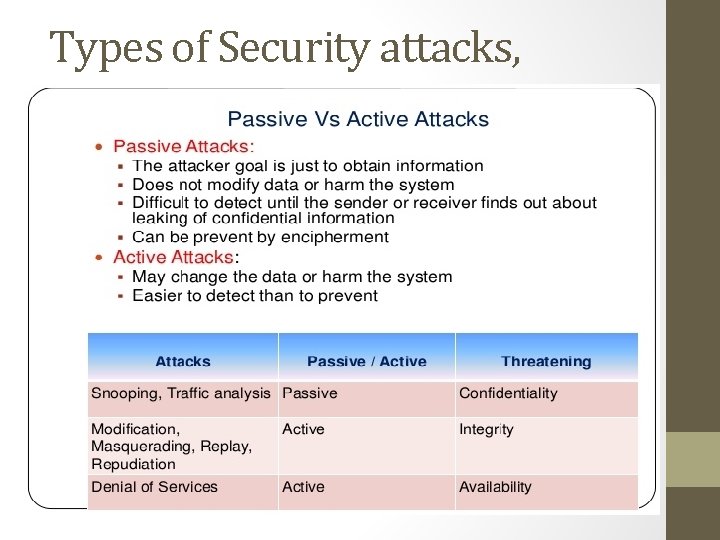
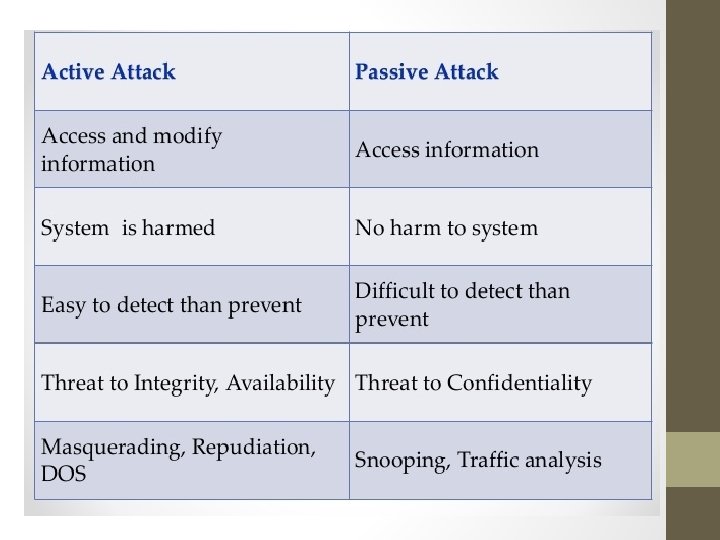
Types of Security attacks,
Malicious code 1) 2) 3) 4) What is malicious code? Types of Malicious Code Where does Malicious Code Hide? Malicious Code: a Dangerous Threat
What is malicious code? • Malicious code is the term used to describe any code in any part of a software system or script that is intended to cause undesired effects, security breaches or damage to a system. • Malicious code is an application security threat that cannot be efficiently controlled by conventional antivirus software alone.
• Malicious code can take the form of: • Java Applets • Active. X Controls • Scripting languages • Browser plug-ins • Pushed content • Once inside your environment, malicious code can enter network drives and propagate. Malicious code can also cause network and mail server overload by sending email messages; stealing data and passwords; deleting document files, email files or passwords; and even reformatting hard drives.
Examples of Malicious code • Early in 1997, a serious threat that involved a free Plug-In advertised as a multimedia viewer for Web movies was exposed. • The free Plug-In silently redirected the computer's modem from the Internet access line to a pay-per-minute number which cost users thousands of dollars in phone bills. • Within a few months of this attack, a hacker organization used an Active. X control to transfer funds by modifying Quicken files located on the local drives of people viewing their web page. • In 1999, a program called "Picture. EXE" forwarded the usernames and passwords of many America Online users to unknown email addresses. Over 250 examples of malicious code has been documented since 1997.
Types of Malicious Code Access Violations Denial of Service
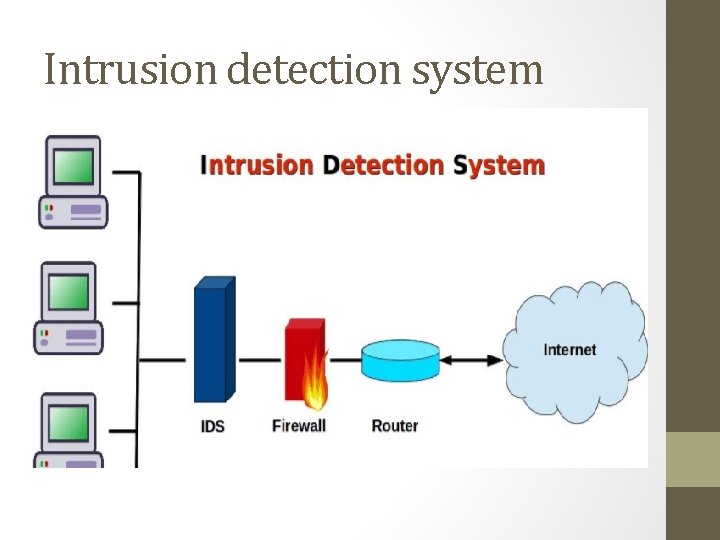
Intrusion detection system
IDS • An IDS (Intrusion Detection System) is the term for a mechanism which quietly listens to network traffic in order to detect abnormal or suspicious activity, thereby reducing the risk of intrusion.
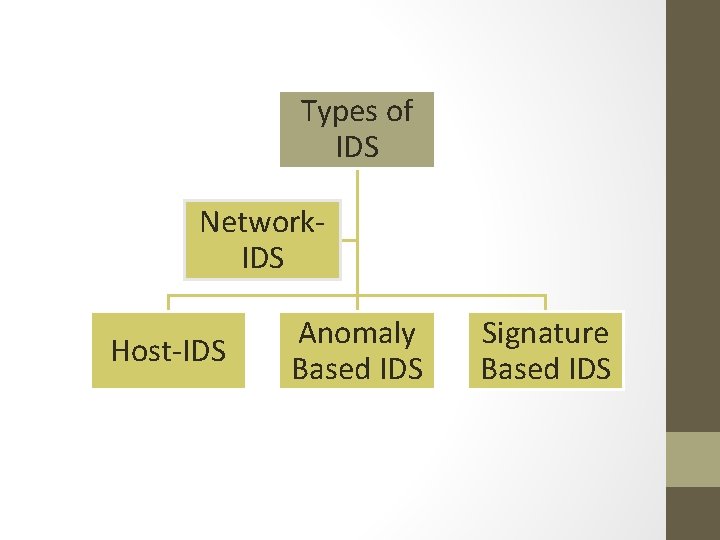
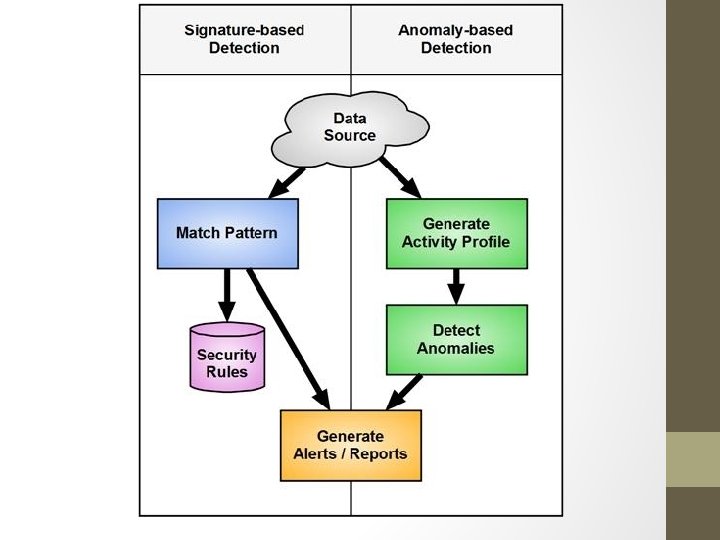
Types of IDS Network. IDS Host-IDS Anomaly Based IDS Signature Based IDS
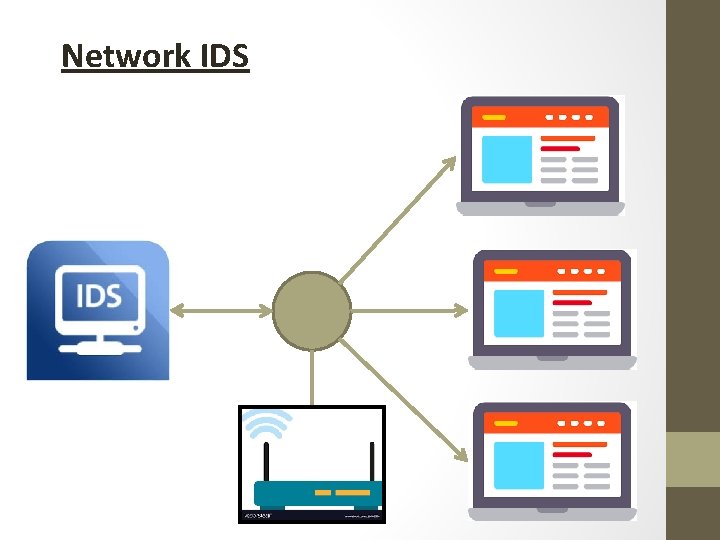
Network IDS
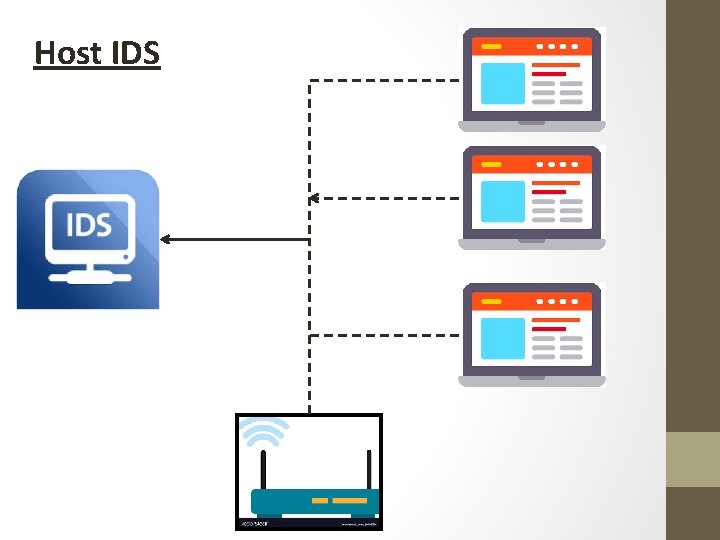
Host IDS
IDS techniques Checking the protocol stack • Ping-Of-Death. TCP Stealth Scanning IP, TCP, UDP & ICMP Violations Recognising "pattern matching" attacks Checking application layer protocols • Few intrusions employ invalid protocol behaviours such as Win. Nuke
What IDSs Do? Reconfiguring third-party devices (firewall or ACLs on routers) Sending an SNMP trap to a third-party hypervisor Sending an email to one or more users Logging the attack Saving suspicious packets Opening an application

- Slides: 34