Unit I Security Basics Information Security Concepts Security
Unit I Security Basics ü ü ü ü Information Security Concepts Security Threats and Vulnerabilities Security Architectures and Operational Models Types of Security attacks Goals of Security, Malicious code Intrusion detection system (IDS) Security and privacy.
Information Security Concepts Computer data travel from one to another. Sensitive and confidential information must be protect. Computer Security: The protection afforded to an automated information system in order to attain the applicable objectives of preserving the integrity, availability, and confidentiality of information system resources (includes hardware, software, firmware, information/data, and telecommunications). network and Internet security consists of measures to prevent, detect, and correct security violations that involve the transmission of information
User A transmits a file to user B. The file contains sensitive information (e. g. , payroll records). User C, who is not authorized to read the file, is able to monitor the transmission and capture a copy of the file during its transmission. A network manager, D, transmits a message to a computer, E. The message instructs computer E to update identities of new users. User F intercepts the message, alters its contents to add or delete entries, and then forwards the message to computer E. Rather than intercept a message, user F constructs its own message with the desired entries and transmits that message to computer E as if it had come from manager D.
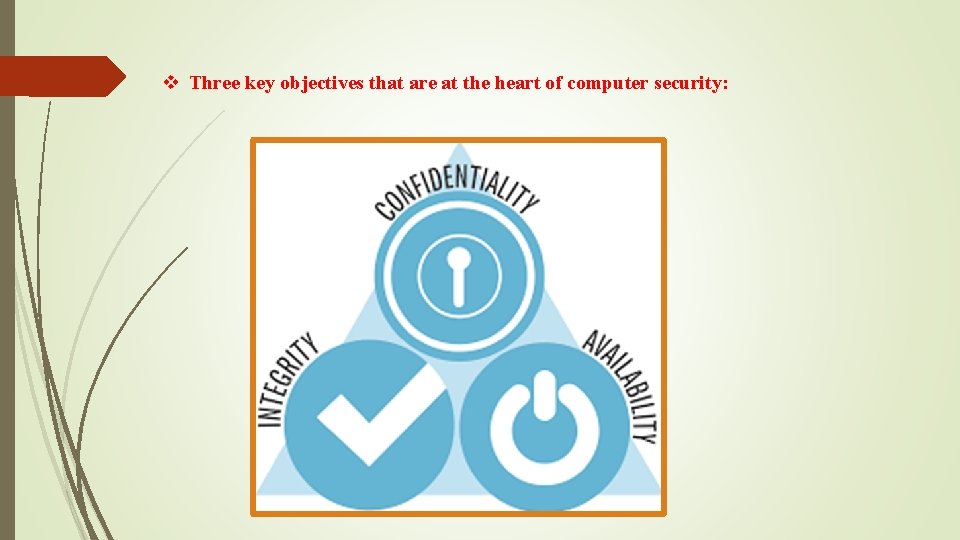
v Three key objectives that are at the heart of computer security:
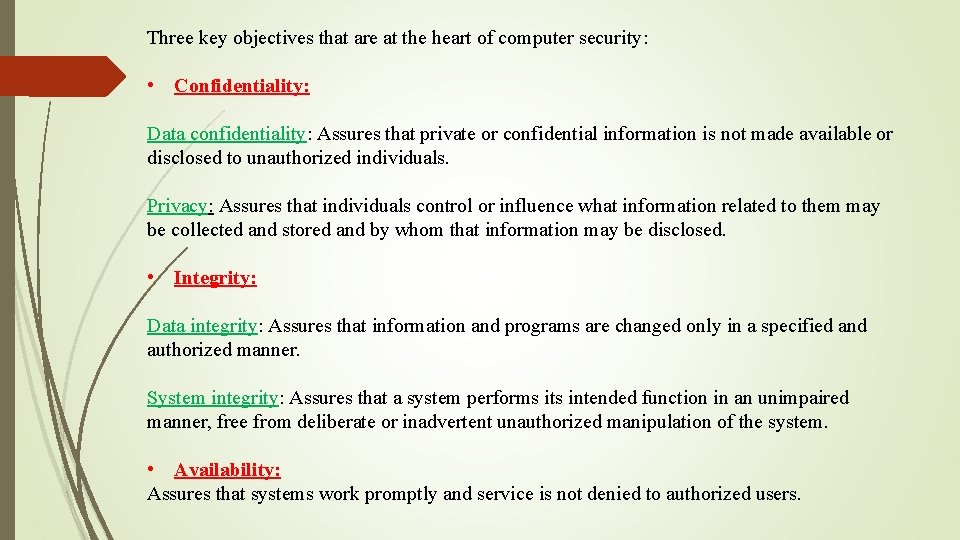
Three key objectives that are at the heart of computer security: • Confidentiality: Data confidentiality: Assures that private or confidential information is not made available or disclosed to unauthorized individuals. Privacy: Assures that individuals control or influence what information related to them may be collected and stored and by whom that information may be disclosed. • Integrity: Data integrity: Assures that information and programs are changed only in a specified and authorized manner. System integrity: Assures that a system performs its intended function in an unimpaired manner, free from deliberate or inadvertent unauthorized manipulation of the system. • Availability: Assures that systems work promptly and service is not denied to authorized users.
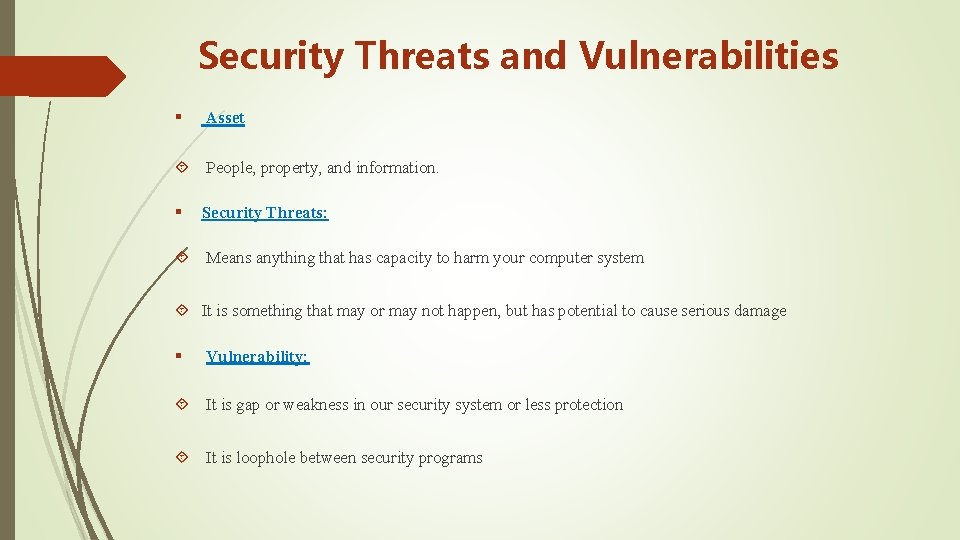
Security Threats and Vulnerabilities § Asset People, property, and information. § Security Threats: Means anything that has capacity to harm your computer system It is something that may or may not happen, but has potential to cause serious damage § Vulnerability: It is gap or weakness in our security system or less protection It is loophole between security programs
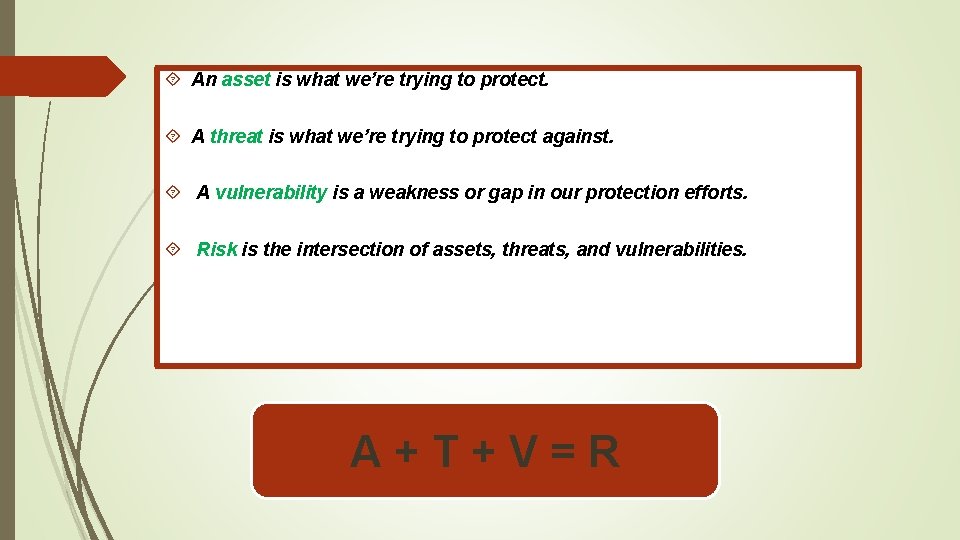
An asset is what we’re trying to protect. A threat is what we’re trying to protect against. A vulnerability is a weakness or gap in our protection efforts. Risk is the intersection of assets, threats, and vulnerabilities. A+T+V=R
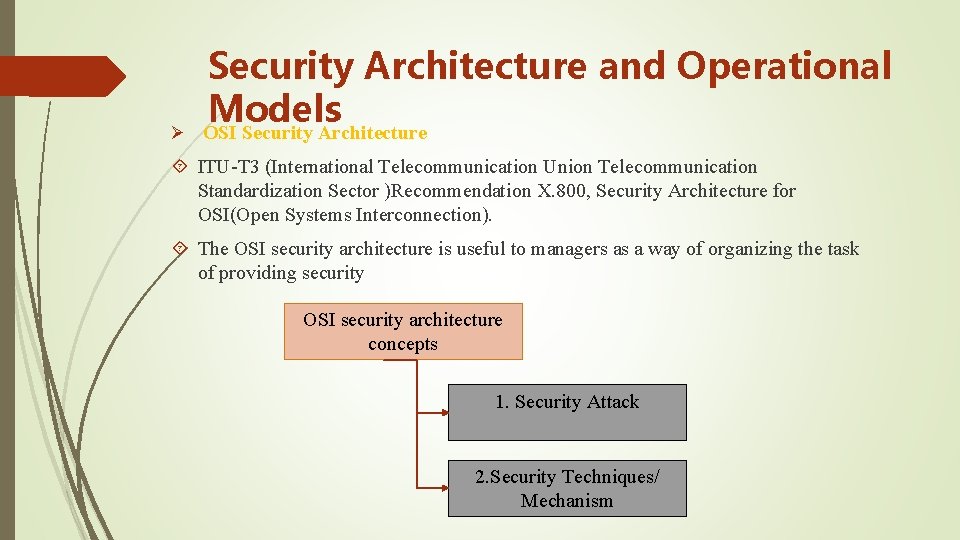
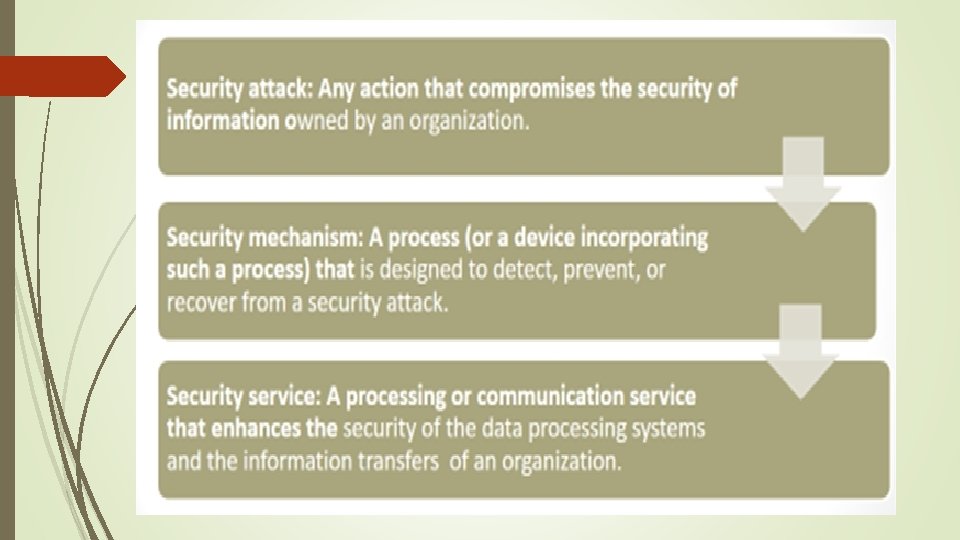
Ø Security Architecture and Operational Models OSI Security Architecture ITU-T 3 (International Telecommunication Union Telecommunication Standardization Sector )Recommendation X. 800, Security Architecture for OSI(Open Systems Interconnection). The OSI security architecture is useful to managers as a way of organizing the task of providing security OSI security architecture concepts 1. Security Attack 2. Security Techniques/ Mechanism
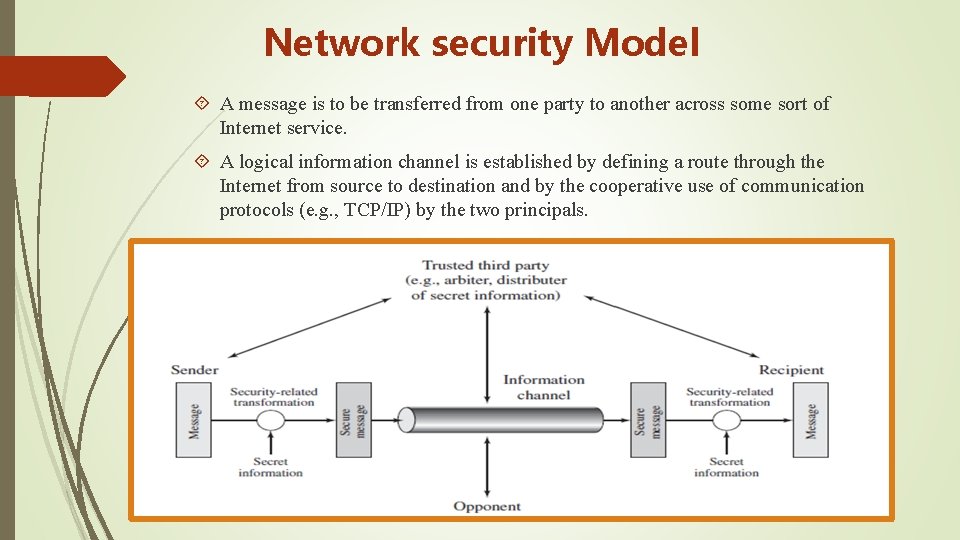
Network security Model A message is to be transferred from one party to another across some sort of Internet service. A logical information channel is established by defining a route through the Internet from source to destination and by the cooperative use of communication protocols (e. g. , TCP/IP) by the two principals.
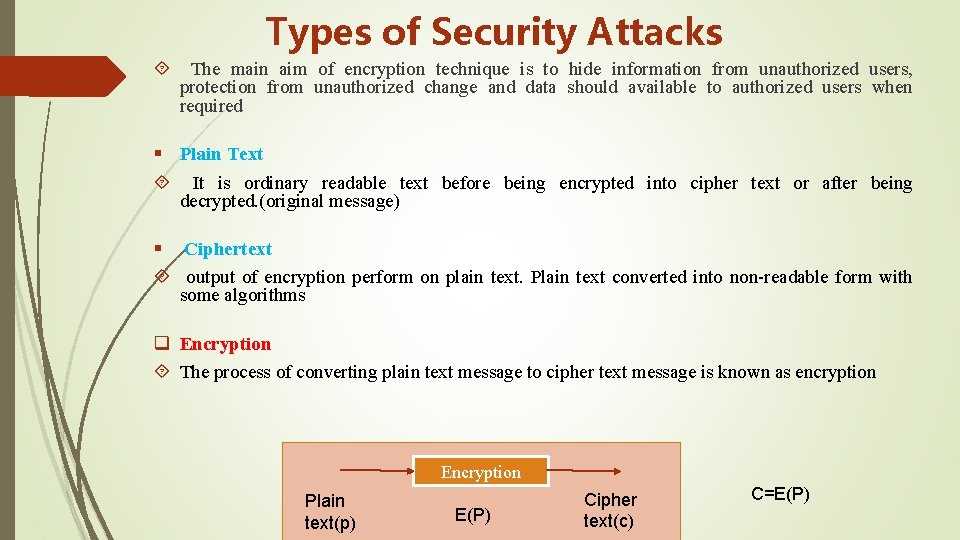
Types of Security Attacks The main aim of encryption technique is to hide information from unauthorized users, protection from unauthorized change and data should available to authorized users when required § Plain Text It is ordinary readable text before being encrypted into cipher text or after being decrypted. (original message) § Ciphertext output of encryption perform on plain text. Plain text converted into non-readable form with some algorithms q Encryption The process of converting plain text message to cipher text message is known as encryption Encryption Plain text(p) E(P) Cipher text(c) C=E(P)
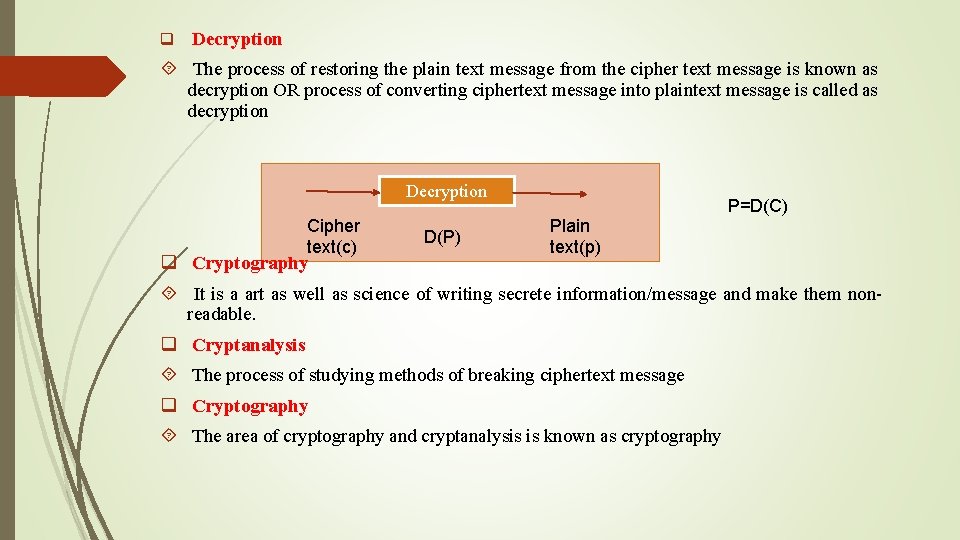
q Decryption The process of restoring the plain text message from the cipher text message is known as decryption OR process of converting ciphertext message into plaintext message is called as decryption Decryption Cipher text(c) q Cryptography D(P) Plain text(p) P=D(C) It is a art as well as science of writing secrete information/message and make them nonreadable. q Cryptanalysis The process of studying methods of breaking ciphertext message q Cryptography The area of cryptography and cryptanalysis is known as cryptography
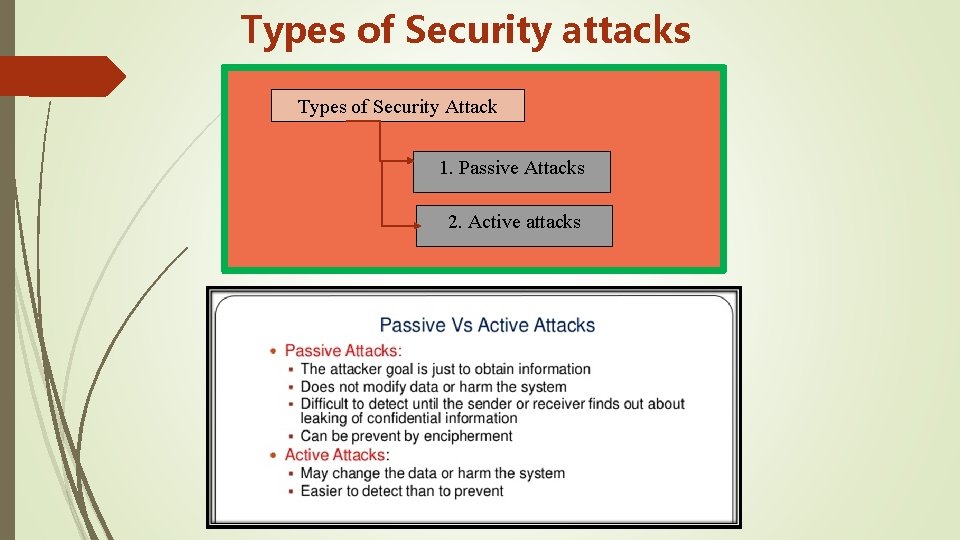
Types of Security attacks Types of Security Attack 1. Passive Attacks 2. Active attacks
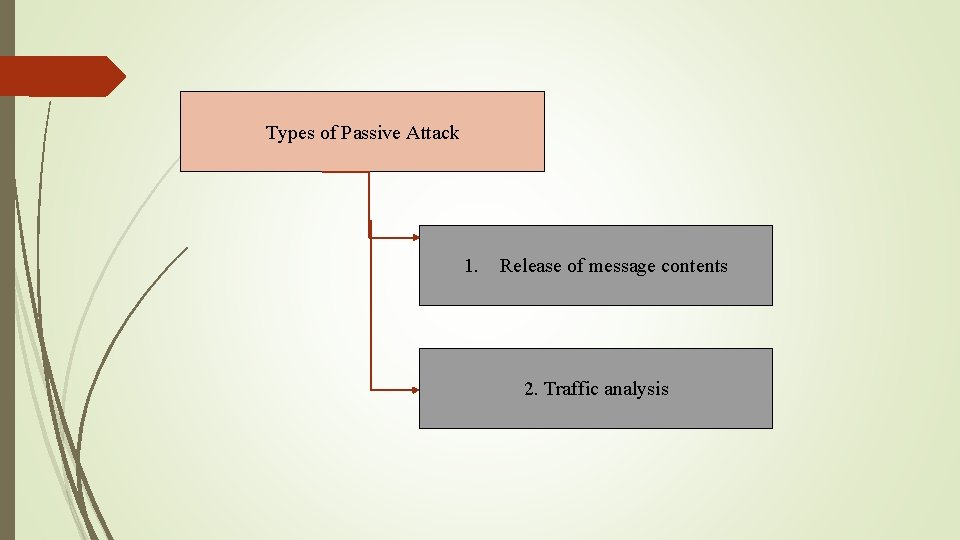
Types of Passive Attack 1. Release of message contents 2. Traffic analysis
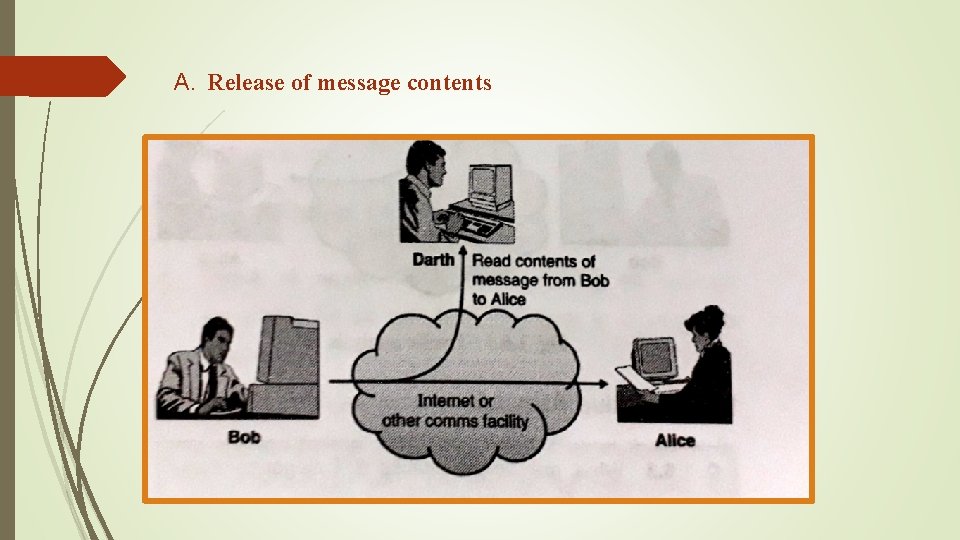
A. Release of message contents
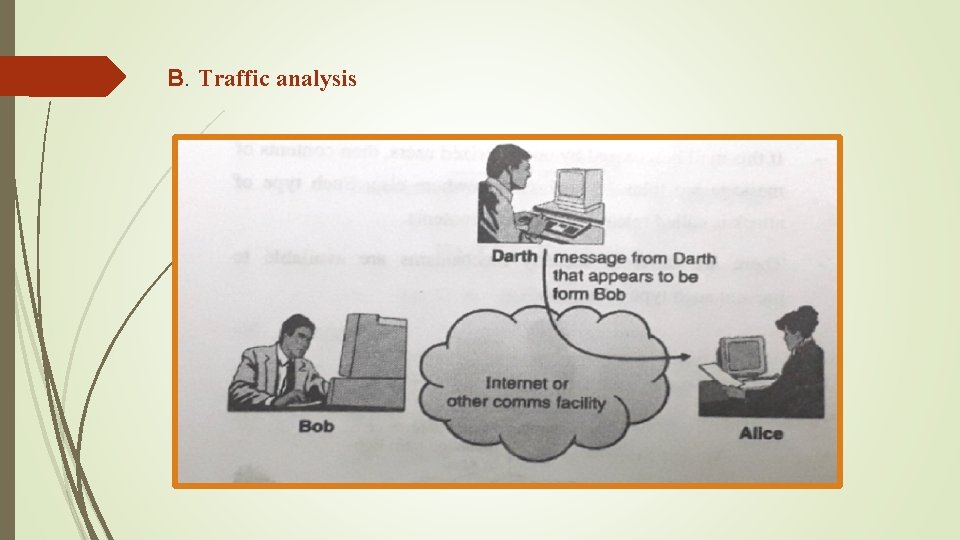
B. Traffic analysis
Types of active attacks 1. Masquerade 2. Replay Attacks 3. Modification of message 4. Denial of services
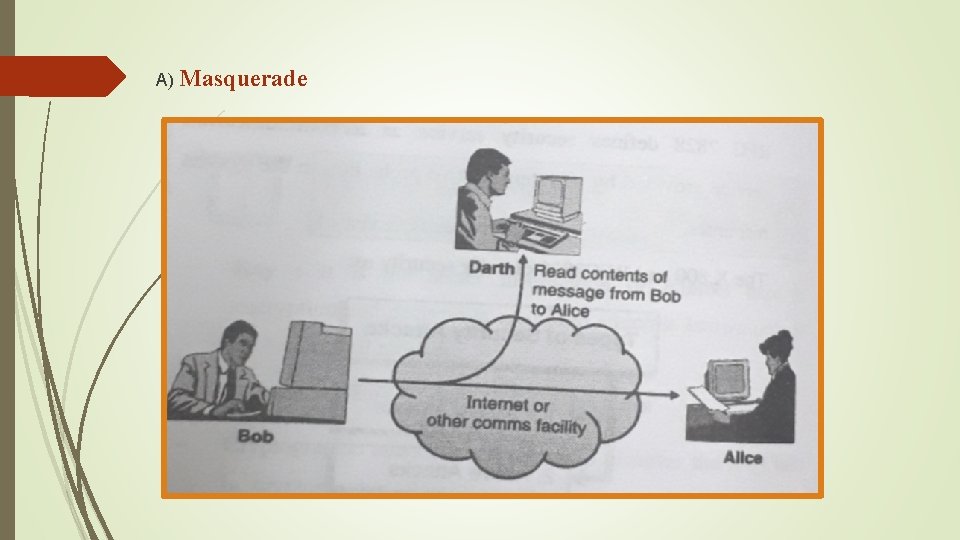
A) Masquerade
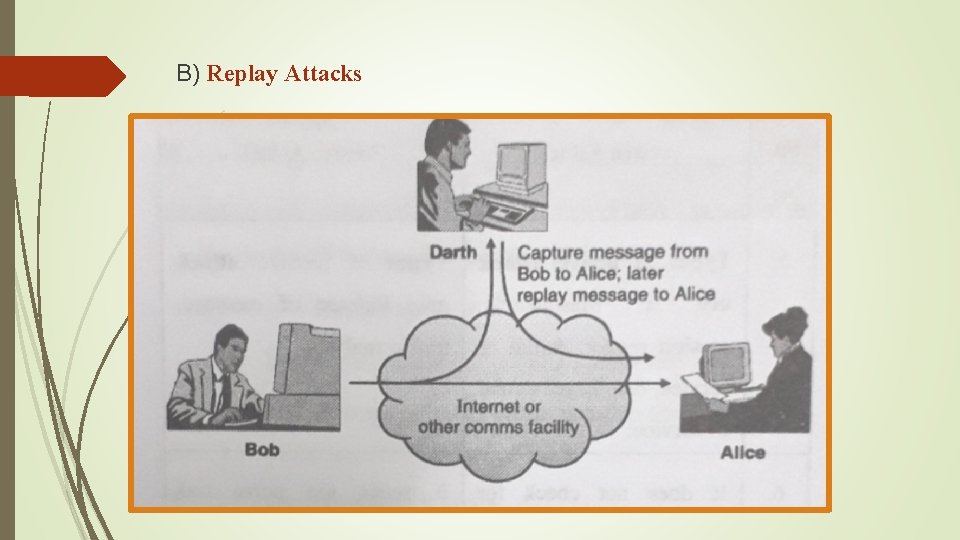
B) Replay Attacks
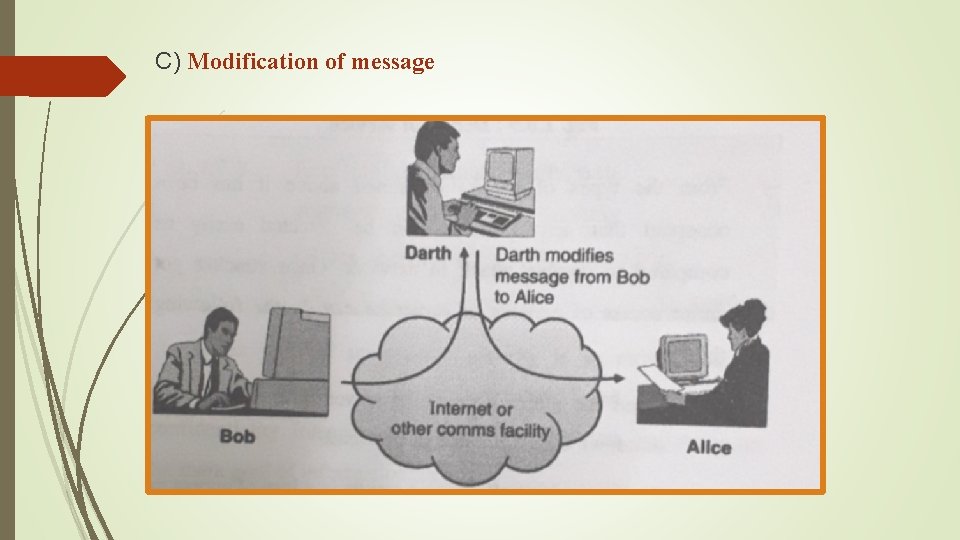
C) Modification of message
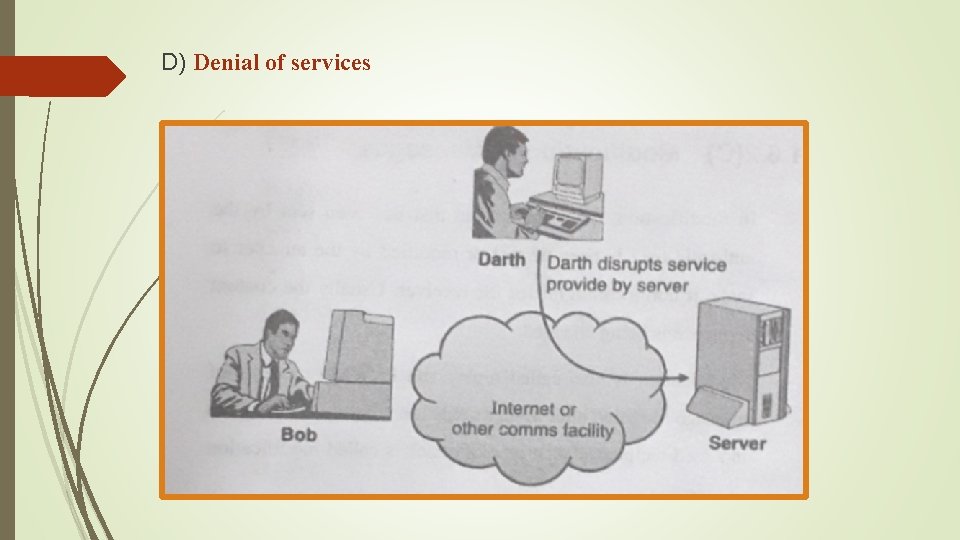
D) Denial of services

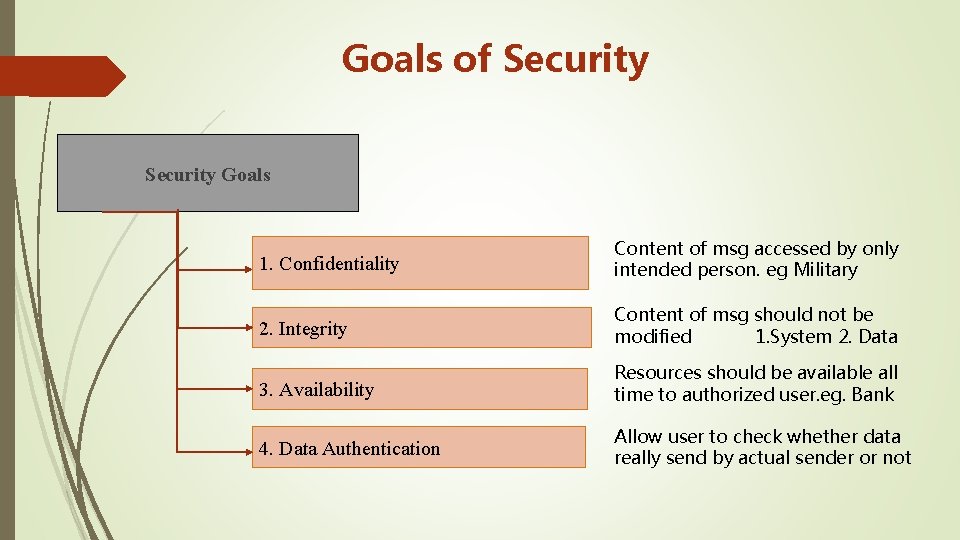
Goals of Security Goals 1. Confidentiality Content of msg accessed by only intended person. eg Military 2. Integrity Content of msg should not be modified 1. System 2. Data 3. Availability Resources should be available all time to authorized user. eg. Bank 4. Data Authentication Allow user to check whether data really send by actual sender or not
Malicious code is the term used to describe any code in any part of a software system or script that is intended to cause undesired effects, security breaches or damage to a system. Malicious code is an application security threat that cannot be efficiently controlled by conventional antivirus software alone. Malicious code can also cause network and mail server overload by sending email messages; stealing data and passwords; deleting document files, email files or passwords; and even reformatting hard drives.
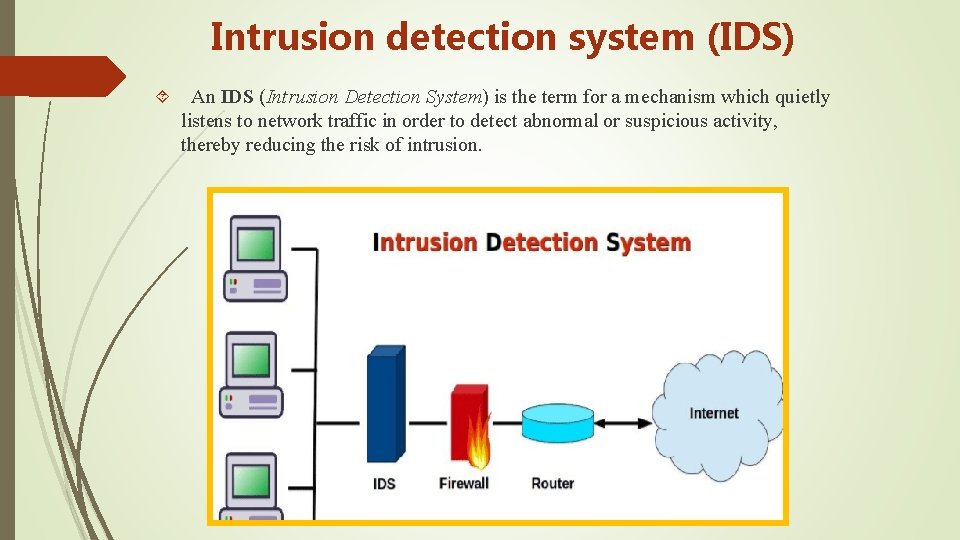
Intrusion detection system (IDS) An IDS (Intrusion Detection System) is the term for a mechanism which quietly listens to network traffic in order to detect abnormal or suspicious activity, thereby reducing the risk of intrusion.
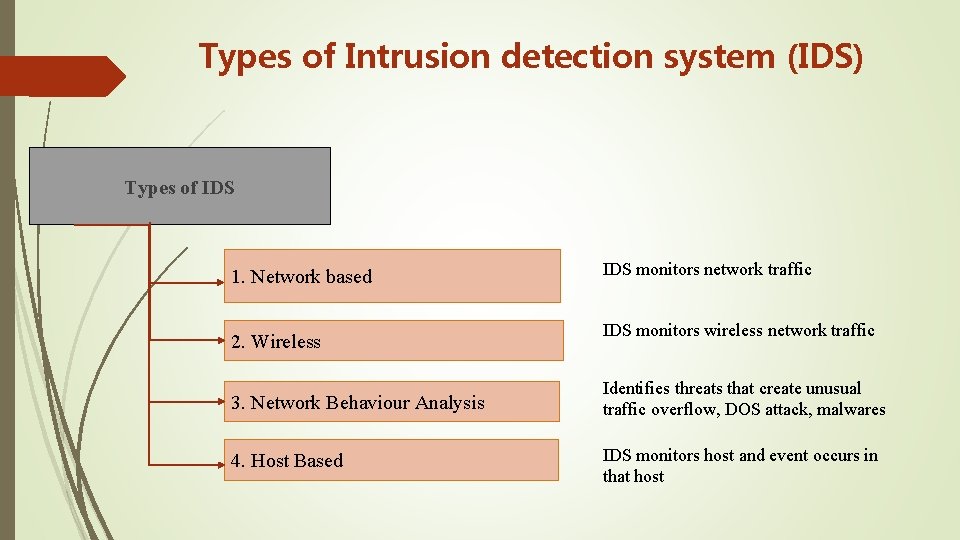
Types of Intrusion detection system (IDS) Types of IDS 1. Network based 2. Wireless IDS monitors network traffic IDS monitors wireless network traffic 3. Network Behaviour Analysis Identifies threats that create unusual traffic overflow, DOS attack, malwares 4. Host Based IDS monitors host and event occurs in that host
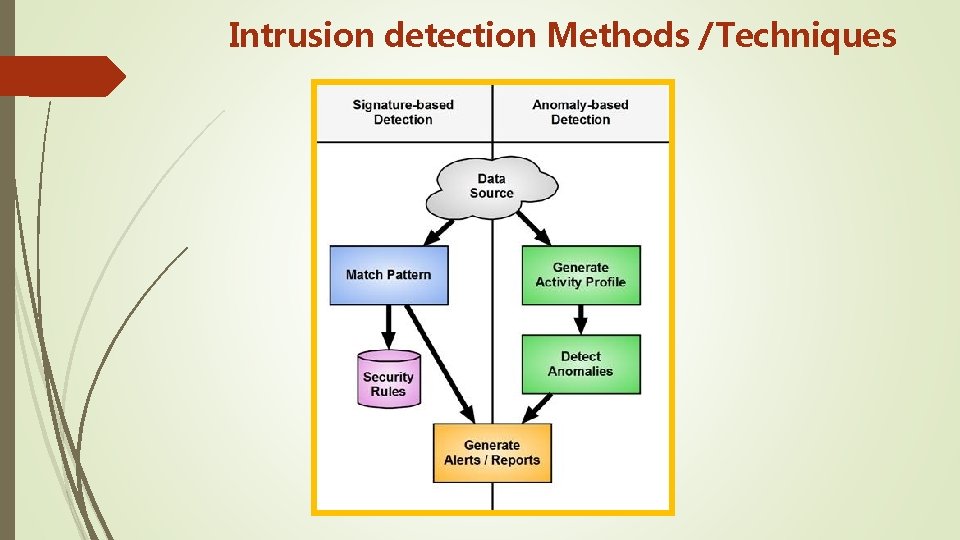
Intrusion detection Methods /Techniques
Security and privacy of IDS Notify administrator in case of detection of malicious activity. If required to monitored logs on daily basis. work on Attack Signature/Attack Pattern which stores previous pattern of attack
- Slides: 28