Smart Phone Security by YY Android permissions demystified
Smart Phone Security --by YY小分队 • Android permissions demystified, CCS’ 11. – Presenter: Xu Xiangyu(徐翔宇) • Life after App Uninstallation: Are the Data Still Alive? Data Residue Attacks on Android, NDSS’ 16 – Presenter: Huang Kaixin(黄凯欣) • Tracking Mobile Web Users Through Motion Sensors: Attacks and Defenses, NDSS’ 16 – Presenter: Cheng Weiyu(程威宇)
Android Permissions Demystified Adrienne Porter Felt, Erika Chin, Steve Hanna, Dawn Song, David Wagner University of California, Berkeley ACM CCS 2011
Outline • • Introduction Android Permission System Permission Testing Methodology Permission Map Result Application Analysis Tool Application Analysis Results Conclusion
Introduction • The lack of reliable permission information that Android provides may cause developer error. • Stowaway, that detects over privilege in compiled Android applications. • a static analysis tool that determines what API calls an application makes • a permission map that identifies what permissions are needed for each API call • About one-third of 940 apps are over-privileged
Android Permission System • Android 2. 2 defines 134 permissions – Normal permissions – Dangerous permissions – Signature/System permissions
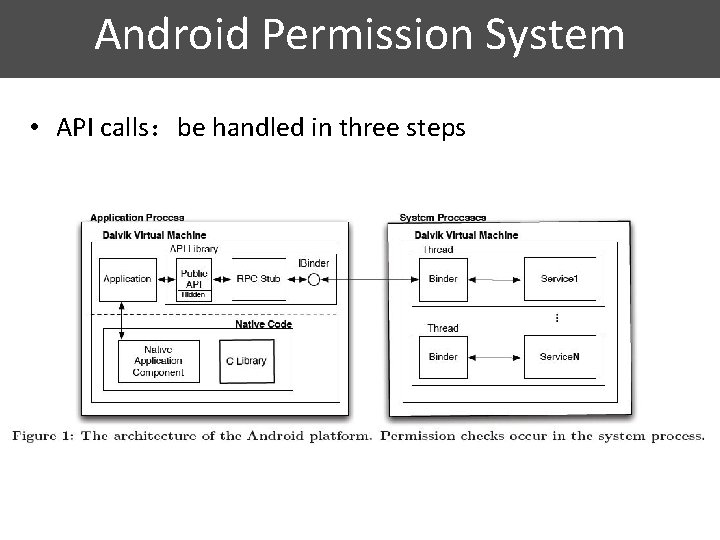
Android Permission System • API calls:be handled in three steps
Android Permission System • Content Providers • • are protected with both static and dynamic permission checks. Intents • • Some Intents can only be sent by applications with appropriate permissions. Other system Intents can only be sent by processes whose UID matches the system's.
Permission Testing Methodology • Construct a permission map that identifies the permissions required for each method in the Android API. • Modified Android 2. 2's permission verification mechanism to log permission checks as they occur. • Generated unit test cases for API calls, Content Providers, and Intents.
Permission Testing Methodology • API calls testing in three phases – Feedback-directed testing • Randoop – Customizable test case generation – Manual verification
Permission Testing Methodology • Content Providers – Collected a list of URIs from the android. provider package to determine the core set of Content Providers to test. – Attempted to execute each type of database operation without any permissions and check for each URI – Finding the minimum set of permissions required to complete the operation • Intents – Built a pair of applications to send and receive Intents – Recorded whether permission checks occurred and whether the Intents were delivered or received successfully
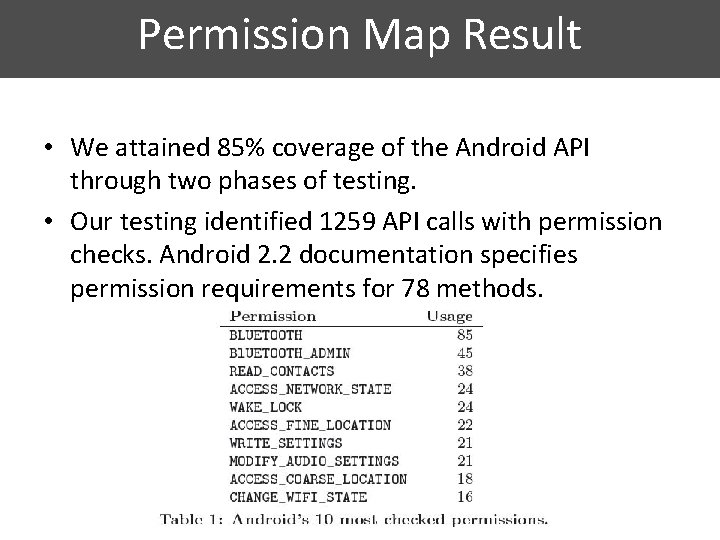
Permission Map Result • We attained 85% coverage of the Android API through two phases of testing. • Our testing identified 1259 API calls with permission checks. Android 2. 2 documentation specifies permission requirements for 78 methods.
Permission Map Result • Characterizing Permissions – – – Signature/System Permissions. Unused Permissions. Hierarchical Permissions. Permission Granularity. Class Characteristics.
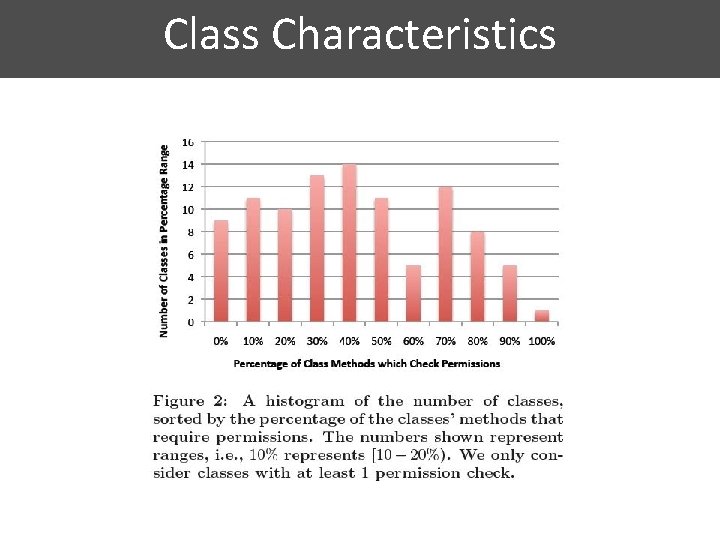
Class Characteristics
Application Analysis Tool • Stowaway, which analyzes an Android application and determines the maximum set of permissions it may require. – API calls • It parses the disassembled DEX(Dalvik executable) files and identify all calls to standard API methods. – Content Providers • Stowaway collects all strings that could be used as Content Provider URIs and links those strings to the Content Providers' permission requirements. – Intent • Use Com. Droid to detect the sending and receiving of Intents that require permissions.
Application Analysis Results • We applied Stowaway to 940 Android applications to identify the prevalence of overprivilege • Manual Analysis • Automated Analysis • The Challenges of Java Reflection – Reflection is commonly used in Android applications. Of the 900 applications, 545 (61%) use Java reflection to make API calls.
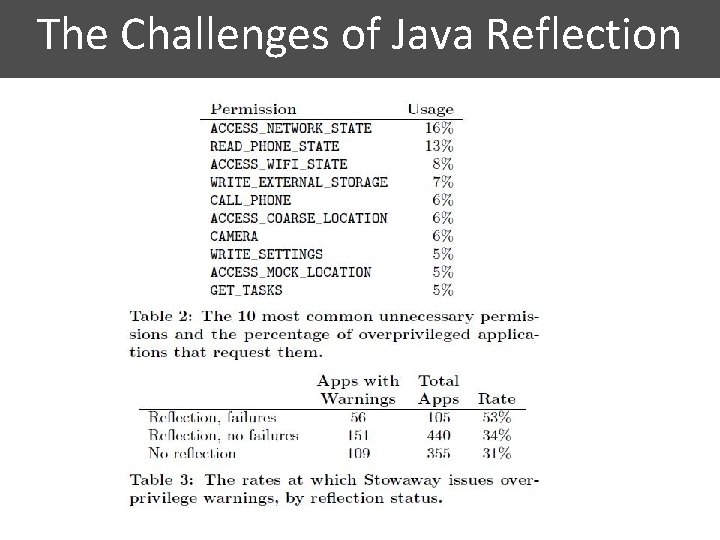
The Challenges of Java Reflection
Application Analysis Results • Common Developer Errors – – – – Permission Name. Deputies Related Methods Copy and Paste Deprecated Permissions Testing Artifacts Signature/System Permissions
Conclusion • Applied automated testing techniques to Android 2. 2 to determine the permissions required to invoke each API method. • Stowaway, generates the maximum set of permissions needed for an application and compares them to the set of permissions actually requested. • about one-third of them are over-privileged
Thank you!
Life after App Uninstallation: Are the Data Still Alive? Data Residue Attacks on Android • Xiao Zhang, Kailiang Ying, Yousra Aafer, Zhenshen Qiu, and Wenliang Du
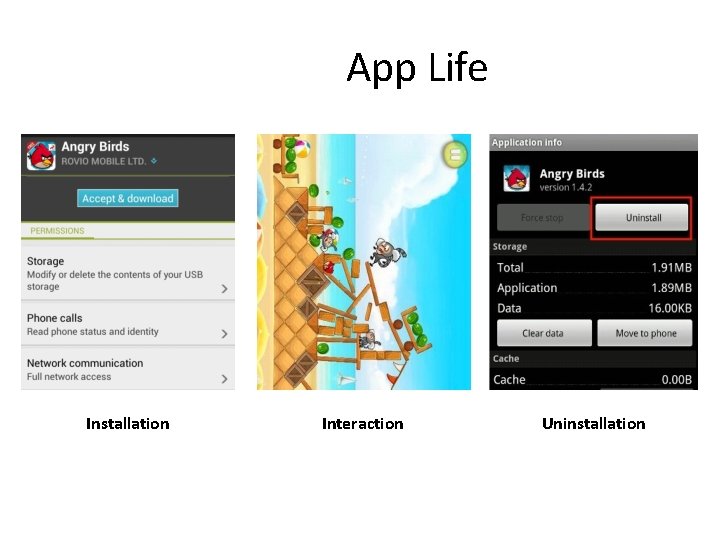
App Life Installation Interaction Uninstallation
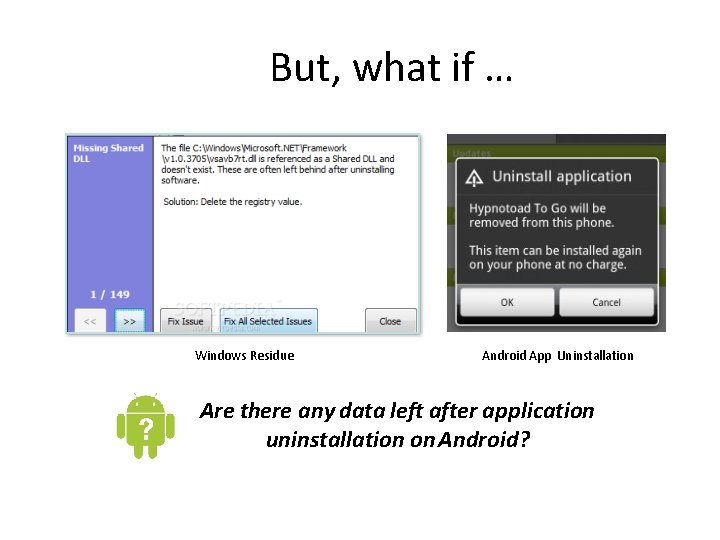
But, what if … Windows Residue Android App Uninstallation Are there any data left after application uninstallation on Android?
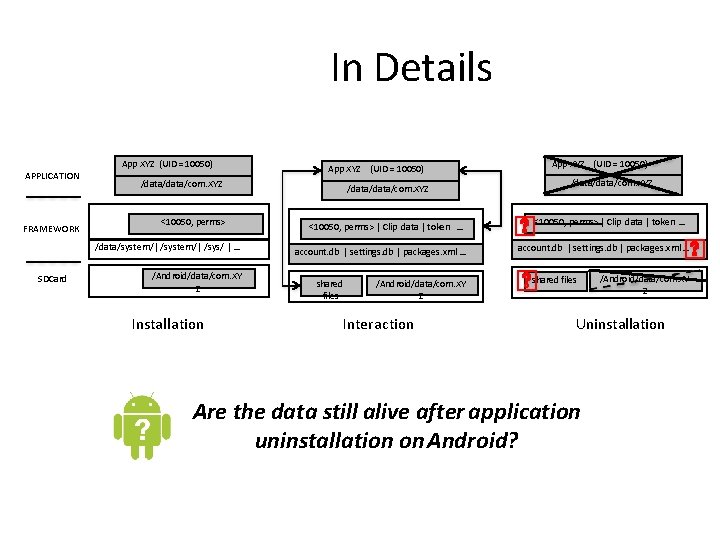
In Details APPLICATION FRAMEWORK App XYZ (UID = 10050) /data/com. XYZ <10050, perms> /data/system/| /sys/ | … SDCard App XYZ (UID = 10050) /Android/data/com. XY Z Installation /data/com. XYZ <10050, perms> | Clip data | token … account. db | settings. db | packages. xml … shared files /Android/data/com. XY Z Interaction App XYZ (UID = 10050) /data/com. XYZ <10050, perms> | Clip data | token … account. db | settings. db | packages. xml … shared files /Android/data/com. XY Z Uninstallation Are the data still alive after application uninstallation on Android?
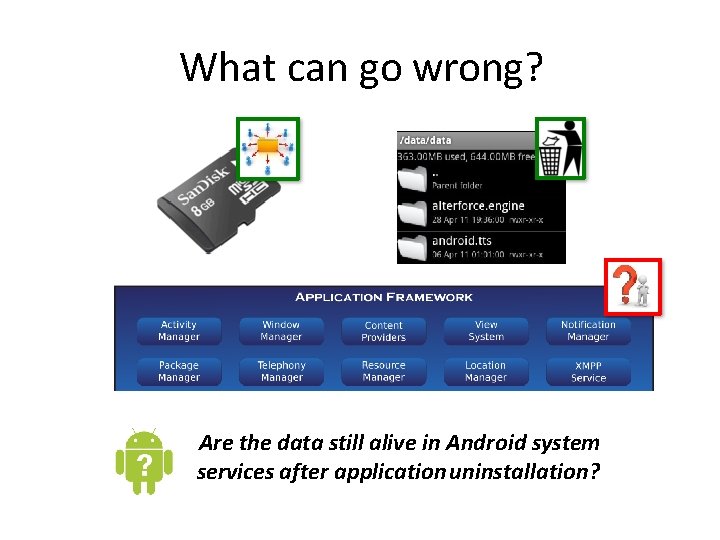
What can go wrong? Are the data still alive in Android system services after application uninstallation?
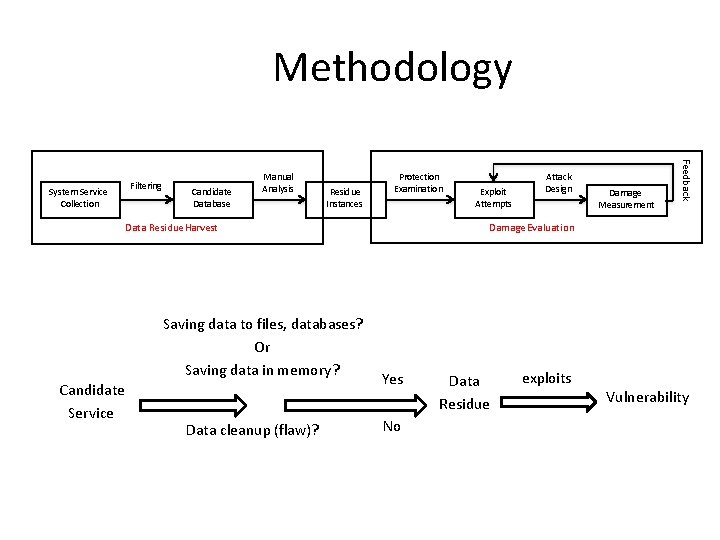
Methodology Filtering Candidate Database Manual Analysis Residue Instances Protection Examination Data Residue Harvest Saving data to files, databases? Or Saving data in memory? Candidate Service Data cleanup (flaw)? Exploit Attempts Attack Design Damage Measurement Feedback System Service Collection Damage Evaluation Yes No Data Residue exploits Vulnerability
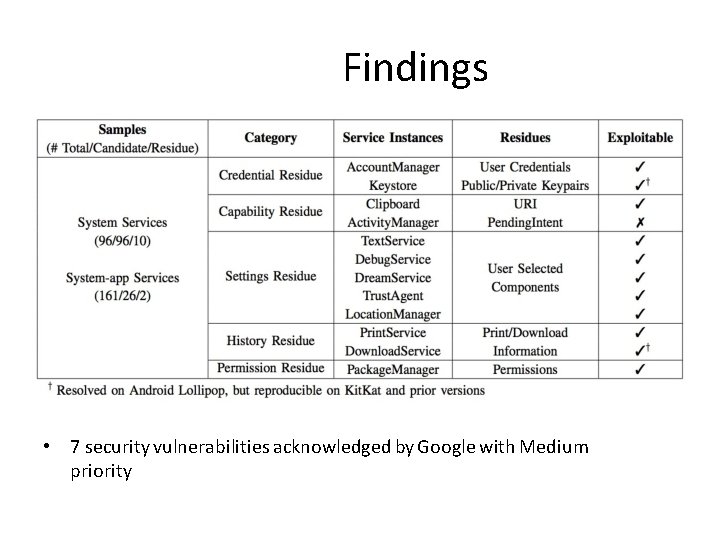
Findings • 7 security vulnerabilities acknowledged by Google with Medium priority
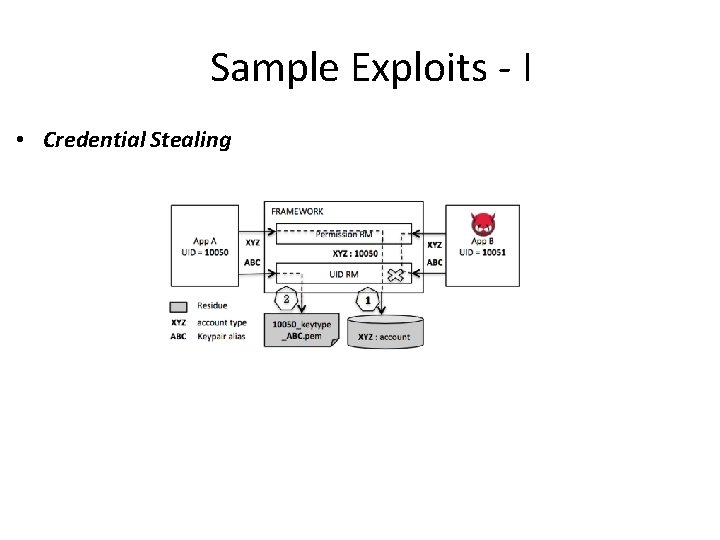
Sample Exploits - I • Credential Stealing
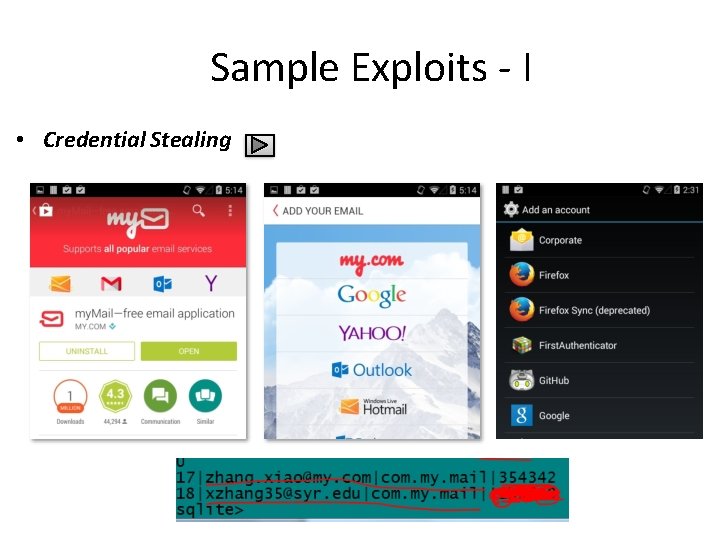
Sample Exploits - I • Credential Stealing
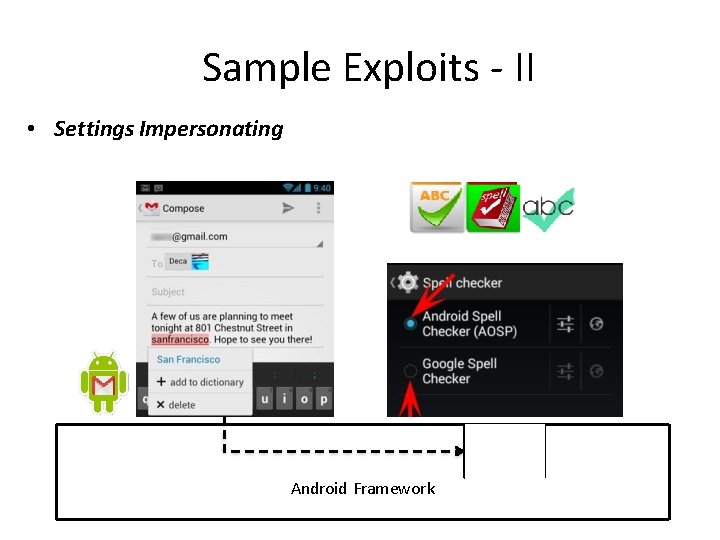
Sample Exploits - II • Settings Impersonating Spell Checker Module Android Framework
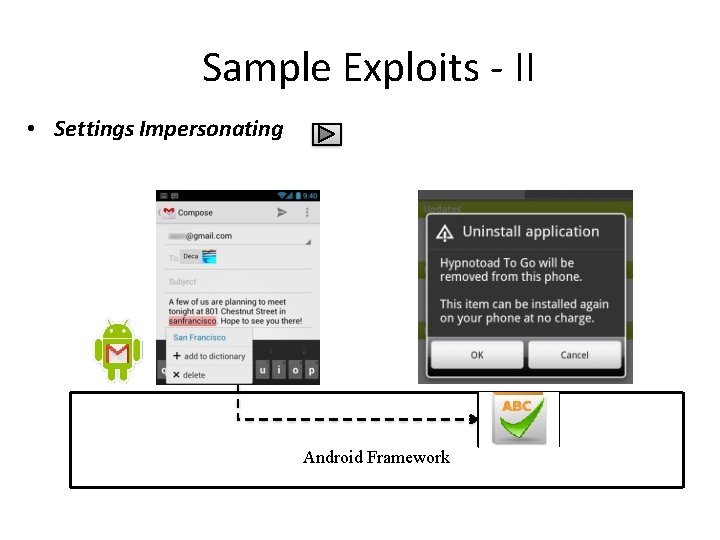
Sample Exploits - II • Settings Impersonating Spell Checker Module Android Framework
Even More … Details are available at: https: //sites. google. com/site/droidnotsecure/
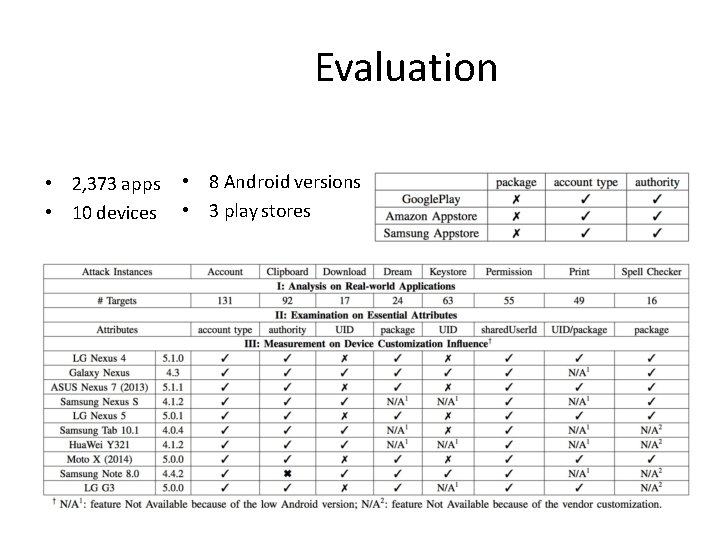
Evaluation • 2, 373 apps • 10 devices • 8 Android versions • 3 play stores
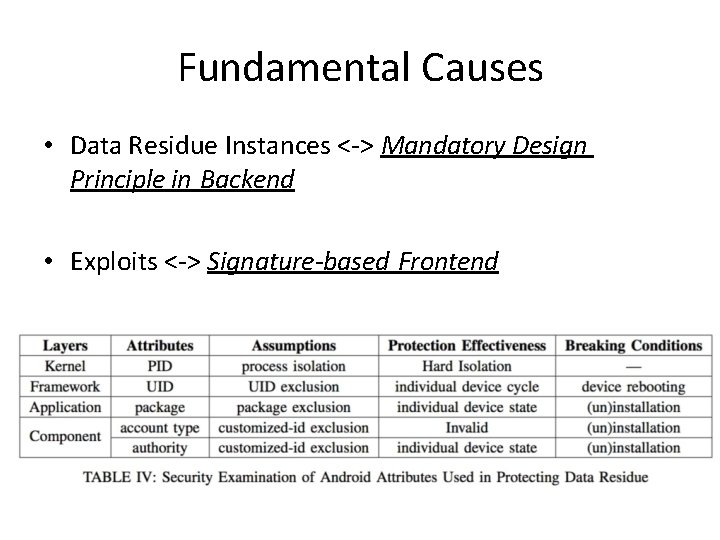
Fundamental Causes • Data Residue Instances <-> Mandatory Design Principle in Backend • Exploits <-> Signature-based Frontend
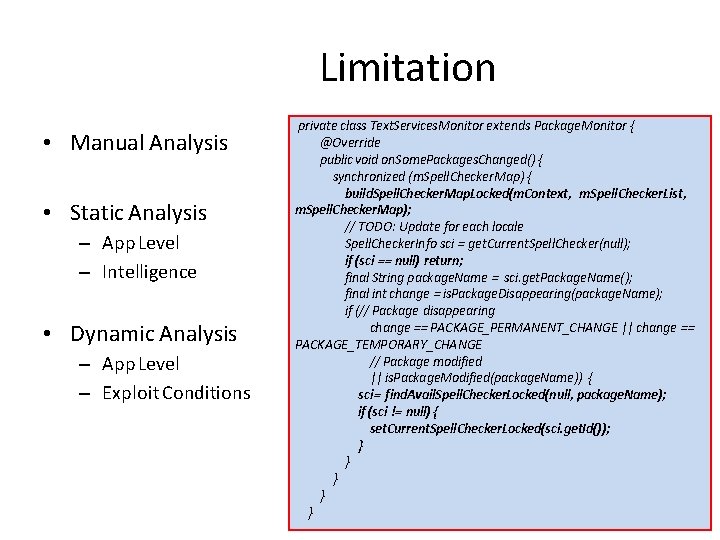
Limitation • Manual Analysis • Static Analysis – App Level – Intelligence • Dynamic Analysis – App Level – Exploit Conditions private class Text. Services. Monitor extends Package. Monitor { @Override public void on. Some. Packages. Changed() { synchronized (m. Spell. Checker. Map) { build. Spell. Checker. Map. Locked(m. Context, m. Spell. Checker. List, m. Spell. Checker. Map); // TODO: Update for each locale Spell. Checker. Info sci = get. Current. Spell. Checker(null); if (sci == null) return; final String package. Name = sci. get. Package. Name(); final int change = is. Package. Disappearing(package. Name); if (// Package disappearing change == PACKAGE_PERMANENT_CHANGE || change == PACKAGE_TEMPORARY_CHANGE // Package modified || is. Package. Modified(package. Name)) { sci= find. Avail. Spell. Checker. Locked(null, package. Name); if (sci != null) { set. Current. Spell. Checker. Locked(sci. get. Id()); } } }
Conclusion • Data Residue Vulnerability • Systematic Study • Comprehensive Evaluation • Trigger more research efforts

Questions? https: //sites. google. com/site/droidnotsecure/
Introduction • Smartphones are equipped with motion sensors, such as accelerometers and gyroscopes, that are available to applications and websites. • Manufacturing imperfections result in each sensor having unique characteristics in their produced signal. • These characteristics can be captured in the form of a fingerprint and be used to track users across repeated visits. 3 8
Overview • Why accelerometers and gyroscopes can be used to generate unique fingerprint? • How can accelerometers and gyroscopes be used to generate unique fingerprint? • Countermeasure techniques to sensor fingerprint-ing. 3 9
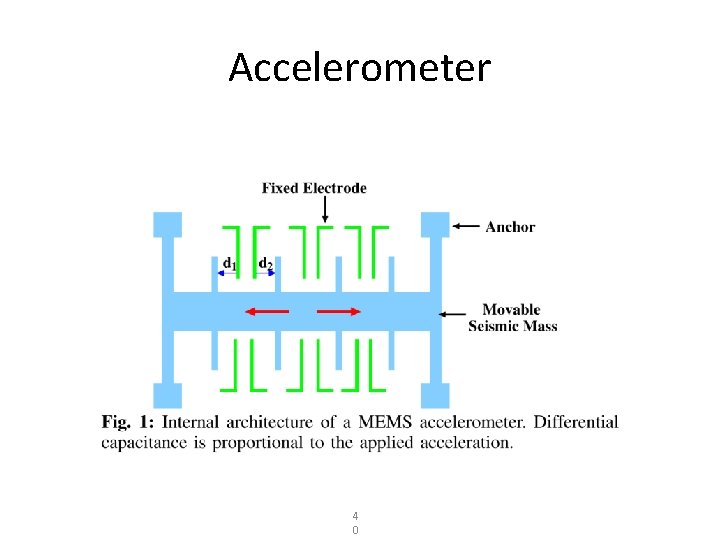
Accelerometer 4 0
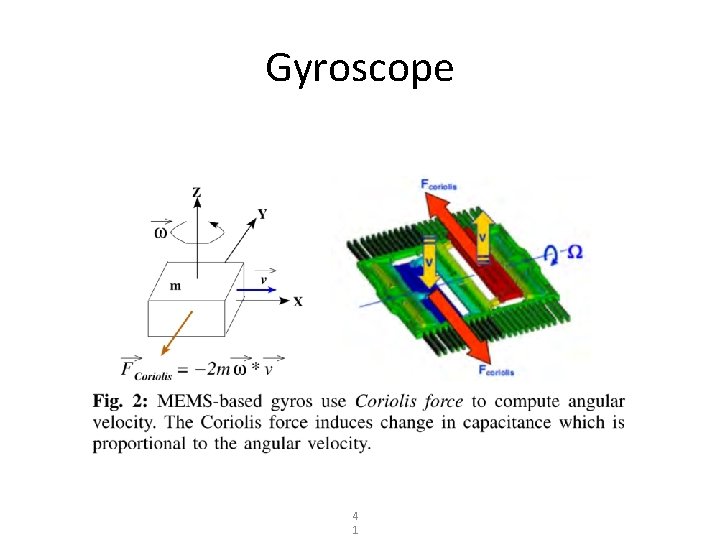
Gyroscope 4 1
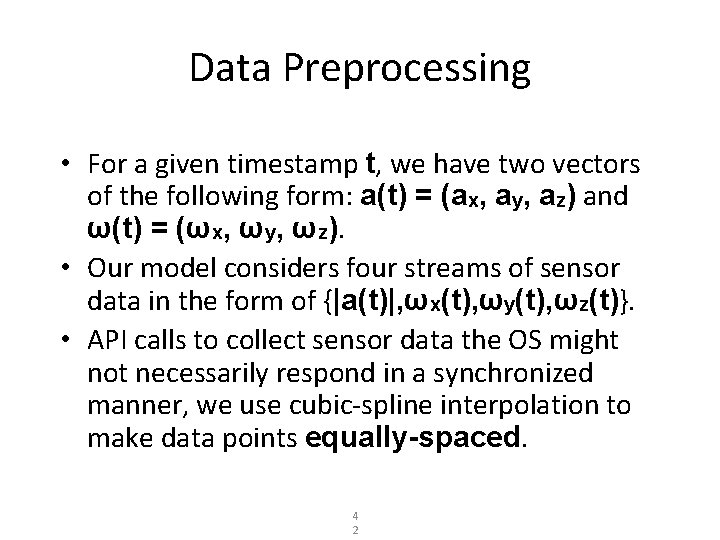
Data Preprocessing • For a given timestamp t, we have two vectors of the following form: a(t) = (ax, ay, az) and ω(t) = (ωx, ωy, ωz). • Our model considers four streams of sensor data in the form of {|a(t)|, ωx(t), ωy(t), ωz(t)}. • API calls to collect sensor data the OS might not necessarily respond in a synchronized manner, we use cubic-spline interpolation to make data points equally-spaced. 4 2
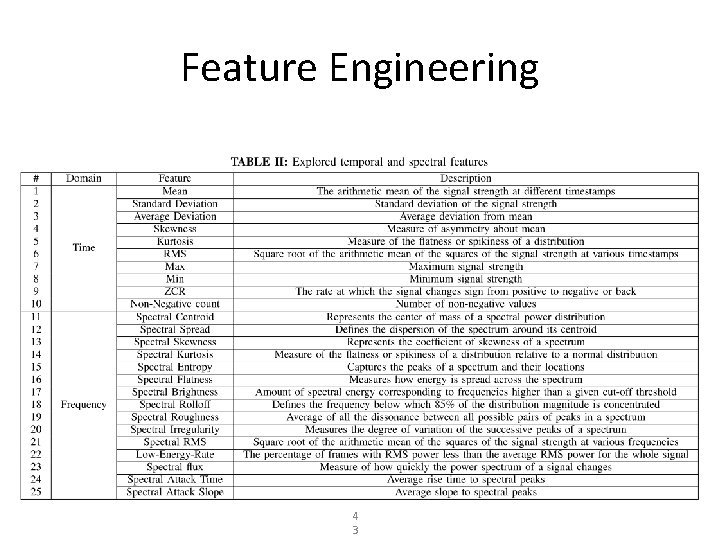
Feature Engineering 4 3
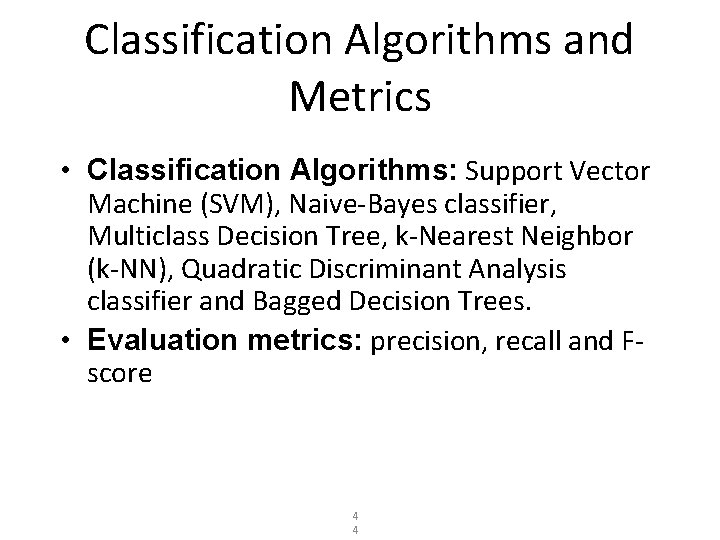
Classification Algorithms and Metrics • Classification Algorithms: Support Vector Machine (SVM), Naive-Bayes classifier, Multiclass Decision Tree, k-Nearest Neighbor (k-NN), Quadratic Discriminant Analysis classifier and Bagged Decision Trees. • Evaluation metrics: precision, recall and Fscore 4 4
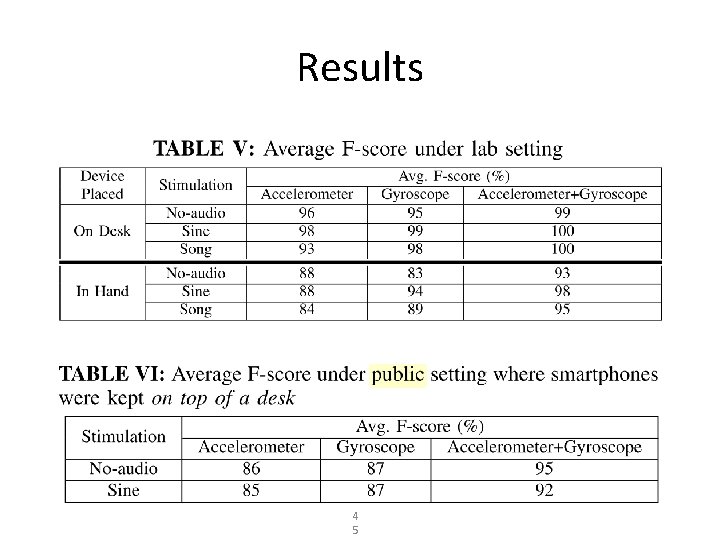
Results 4 5
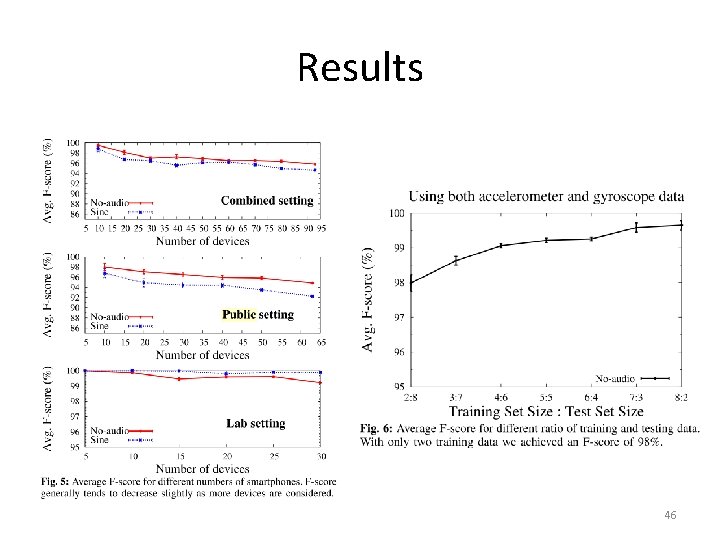
Results 46
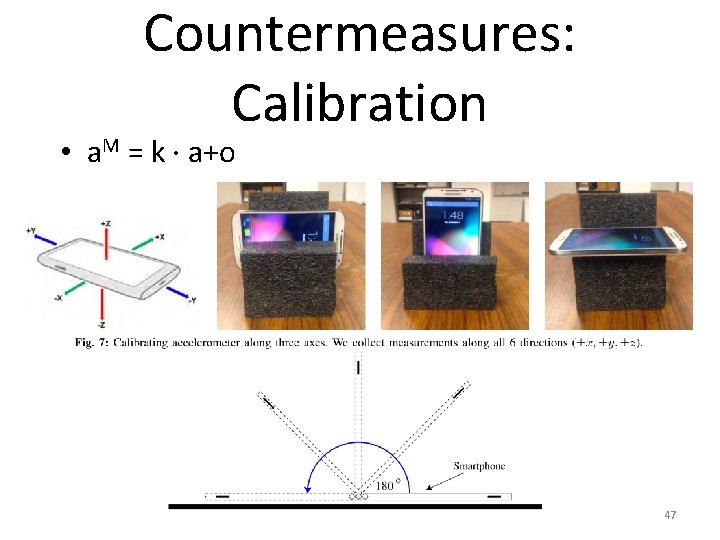
Countermeasures: Calibration • a. M = k · a+o 47
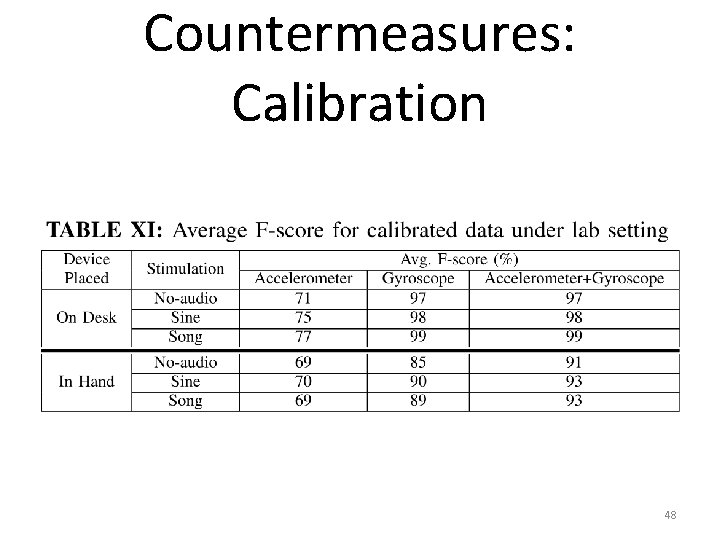
Countermeasures: Calibration 48
Countermeasures: Data Obfuscation • Rather than removing calibration errors, we can instead add extra noise to hide the miscalibration. • Not requiring a calibration step, which requires user intervention. • Adds extra noise and can therefore negatively impact the utility of the sensors 49
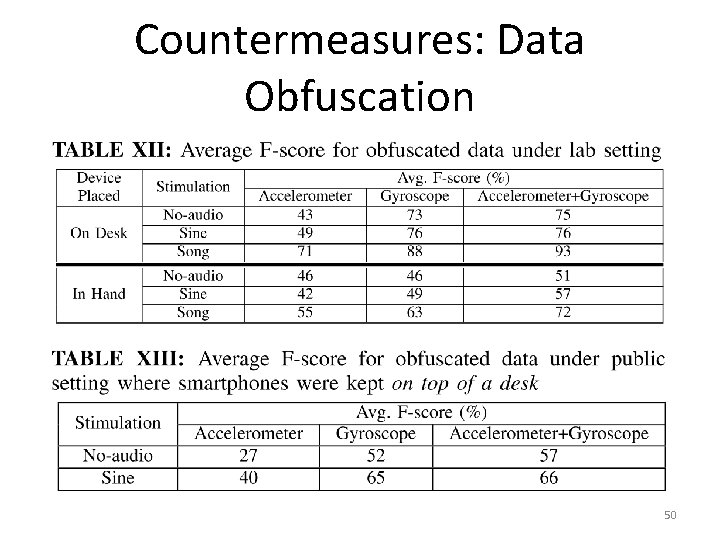
Countermeasures: Data Obfuscation 50
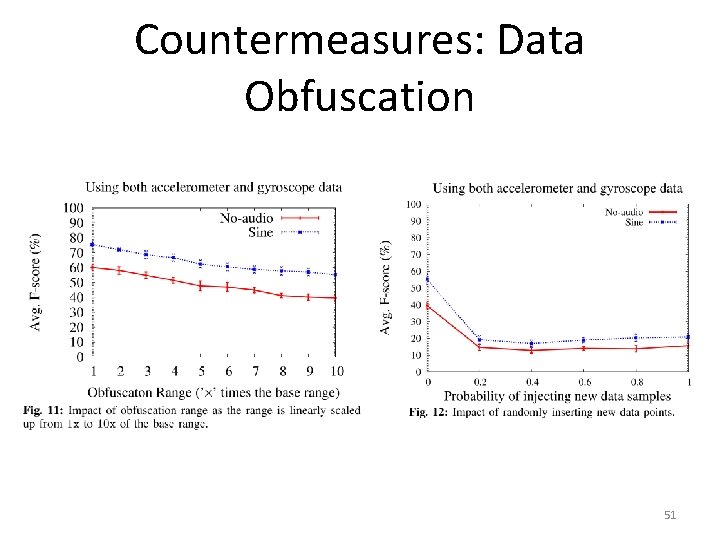
Countermeasures: Data Obfuscation 51
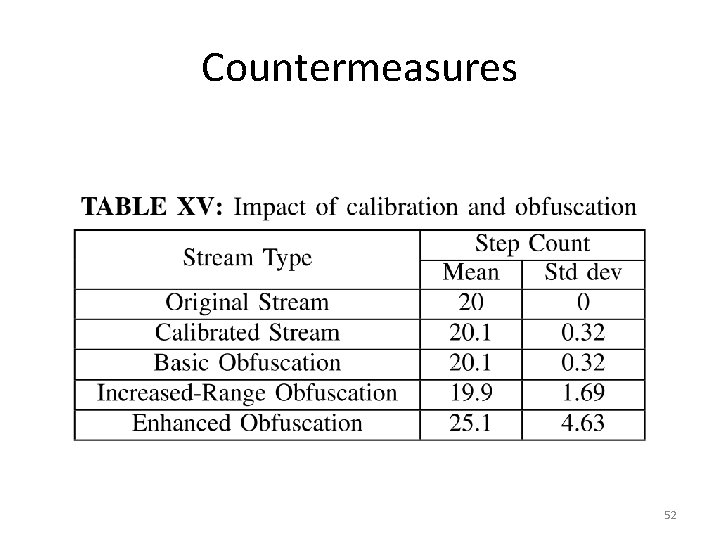
Countermeasures 52
Conclusion • Motion sensors such as accelerometers and gyroscopes can be used to uniquely identify smart-phones. • Injecting audio stimulation in the background improves detection rate. • We suggest using our obfuscation techniques in the absence of explicit user permission/awareness. 53
- Slides: 53