By Collin Molnar ANDROID SECURITY Overview Intro to
By: Collin Molnar ANDROID SECURITY
Overview � Intro to Android � Security basics � Android architecture � Application isolation � Application permissions � Physical access control � Encryption
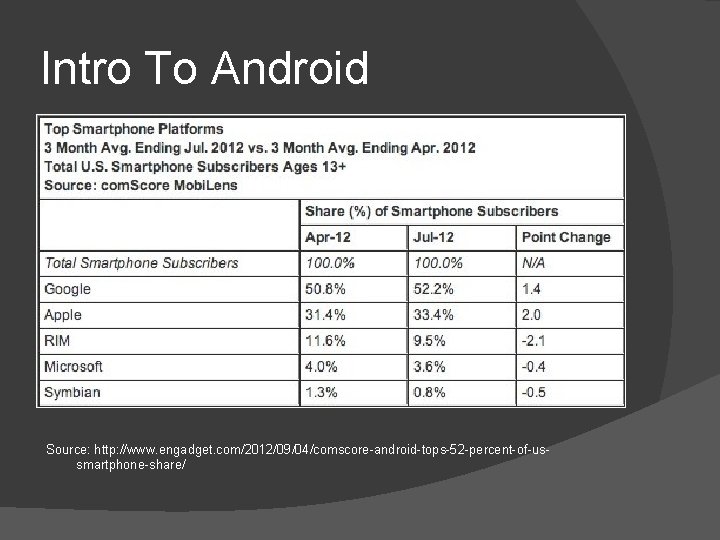
Intro To Android Source: http: //www. engadget. com/2012/09/04/comscore-android-tops-52 -percent-of-ussmartphone-share/
Intro To Android � Open Source � Based of a modified Linux kernel �Ice Cream Sandwich is based off of 3. x � Apps are developed in Java �Does not use Java Virtual Machine � Libraries and kernel developed in C/C++
Basics of Security � Permissions and application isolation �Prevent app from changing system � Storing data �Encryption �Keeping data safe � Access Control �Keep unwanted users from accessing phone
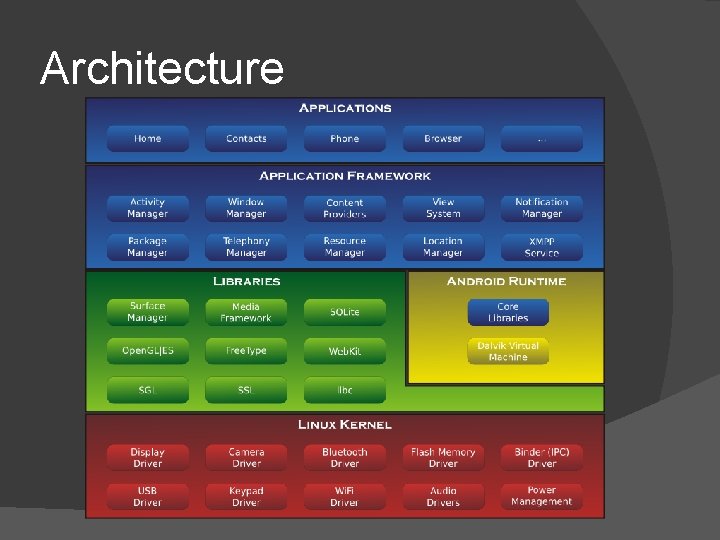
Architecture
Application Isolation � Each app runs on it’s own �Apps don’t share resources or memory � Each app runs in a separate process �Based of Linux security � Dalvik Virtual Machine does not control security � Foundation of Security for Android
Android Permissions � Default permissions �Cannot effect other apps or system �Cannot access contacts, SMS, email � Each app is contained in a sandbox �Apps use intents to talk to other apps �Otherwise, apps must request permissions ○ Permissions are only once when app is installed
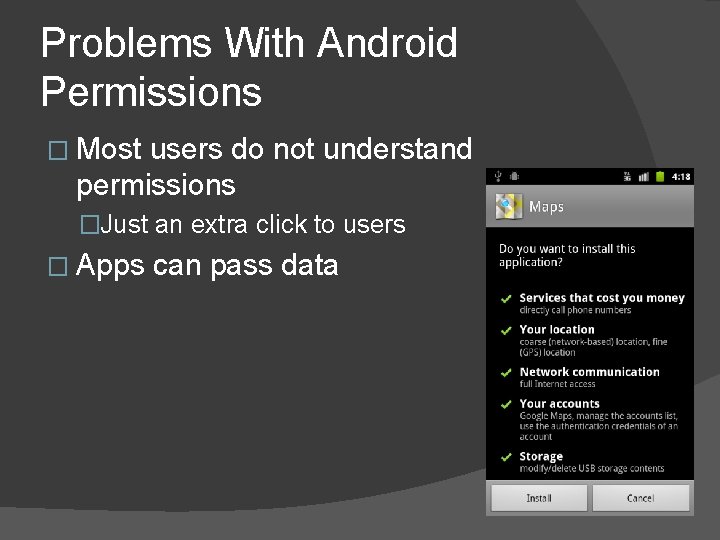
Problems With Android Permissions � Most users do not understand permissions �Just an extra click to users � Apps can pass data
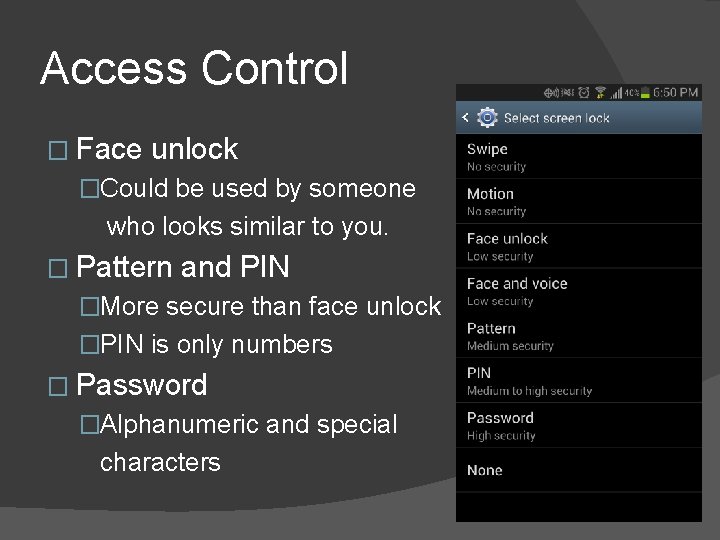
Access Control � Face unlock �Could be used by someone who looks similar to you. � Pattern and PIN �More secure than face unlock �PIN is only numbers � Password �Alphanumeric and special characters
Encryption � Added in Android 2. 3. 4 � Uses dm-crypt from the Linux kernel � Requires lock screen PIN or password � Each time phone is powered on the password must be entered � SD card may also be encrypted
Conclusion � Security is based of Linux kernel �Each application runs in a sandbox �Permissions are used to control apps � Newer � Built devices can be encrypted in physical access control
- Slides: 12