Security Fundamentals Robin Anderson UMBC Office of Information
Security Fundamentals Robin Anderson UMBC, Office of Information Technology 25 -SEPT-2001 1
A Little About Me… ¨ Unix Sys. Admin, Specialist with the Office of Information Technology at UMBC ¨ Taught Unix Administration and SANS Level One Security courses at UMBC ¨ Certified by the SANS Institute GIAC program in UNIX Security and Incident Handling 25 -SEPT-2001 2
Topics Outline ¨ Post-Mortems in the News… ¨ Identifying Threats ¨ Countering Threats ¨ The (Vulnerable) Network ¨ Questions You Need to Ask ¨ Recommendations You Want to Make ¨ Resources Online 25 -SEPT-2001 3
What Happened to Amazon®? ¨ Website defacing: Hackers broke in & put up phony web pages (And now, newer worms/viruses are doing the same!) – – – September 2000: OPEC 1 February 2000: Amazon® , e. Bay® 2 November 1999: NASA/Goddard 3 October 31, 1999: Associated Press® 4 August 1999: ABC® 5 June 1999: U. S. Army 25 -SEPT-2001 4
What Happened to Yahoo®? ¨ Denial of Service (Do. S) – February 2000: Yahoo and CNN 1 ¨ Multiple Hits – September 2000: – May 2000: Slashdot defaced Slashdot suffered Do. S The irony is that slashdot. org is a popular "news for nerds" website 25 -SEPT-2001 5
If They’re Vulnerable… …then you are, too. 25 -SEPT-2001 6
The Fundamental Theorem ¨ You have computers because they perform some function that furthers your organization’s goals ¨ If you lose the use of those computers, their function is compromised ¨ So - anything that interferes with your organization’s effort to achieve its goals is a security concern 25 -SEPT-2001 7
What Are You Protecting? ¨ Information ¨ Availability of the Systems ¨ Reputation & Goodwill 25 -SEPT-2001 8
Your Information ¨ Crown Jewels – Trade secrets, patent ideas, research ¨ Financial information ¨ Personnel records ¨ Organizational structure 25 -SEPT-2001 9
Your Availability ¨ Internal use – When employees can’t use the network, servers, or other necessary systems, they can’t work ¨ Website / online transactions – Often when systems are unavailable, the organization is losing money 25 -SEPT-2001 10
Your Reputation ¨ Public trust – If your organization is hacked, how reliable will people think you are you in other areas? – Who wants to do business with companies that leak credit card information? ¨ Being a good neighbor – Your organization may be hacked so it can be used as a springboard to attack others 25 -SEPT-2001 11
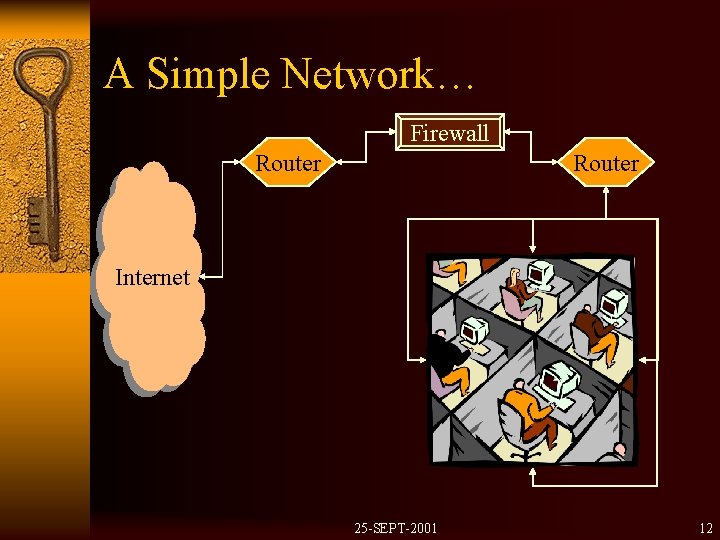
A Simple Network… Firewall Router Internet 25 -SEPT-2001 12
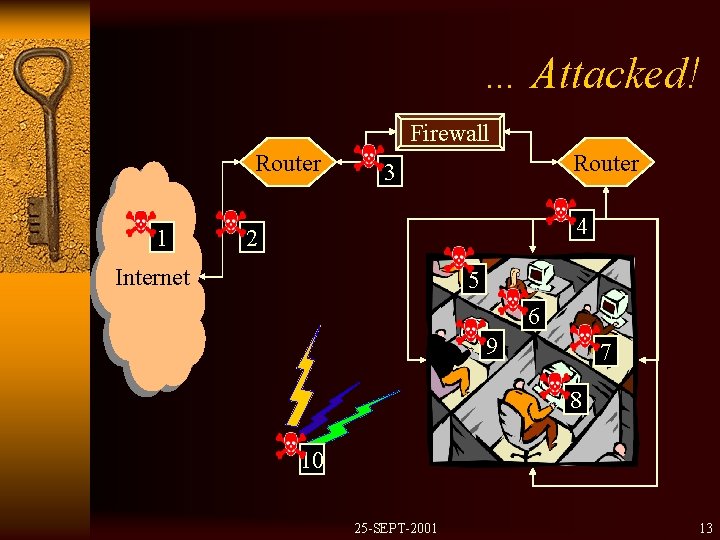
… Attacked! Firewall Router 1 Router 3 4 2 Internet 5 6 9 7 8 10 25 -SEPT-2001 13
What Are These Threats? 1. Do. S coming from the Internet 2. Severed Physical link 3. Masquerader / Spoofer – They look like they’re already inside 4. Password sniffer 25 -SEPT-2001 14
What Are These Threats? (2) 5. Alan brought a floppy from home that has a virus on it 6. Beatrice is about to be fired – and she’s going to be angry about it 7. Carter is careless with his passwords – he writes them down and loses the paper 25 -SEPT-2001 15
What Are These Threats? (3) 8. David has unprotected shares on his NT box 9. Evan installed a modem on his PC (PCAnywhere) 10. Severed Power / HVAC 25 -SEPT-2001 16
What Are Threat Vectors? Vectors are the pathways by which threats enter your network 25 -SEPT-2001 17
Threat Vectors - Internal ¨ Careless employees – “Floyd the clumsy janitor” – “Contraband” hardware / software – “Oops, did I just type that? ” ¨ Random twits (somewhere between careless & malicious) ¨ Malicious employees – Current or former employees with axes to grind ¨ Anyone who can get physical access 25 -SEPT-2001 18
Threat Vectors - External ¨ Competitors / spies / saboteurs ¨ Casual & incidental hackers – Some hackers don’t want your systems except to use them to get at their real target ¨ Malicious hackers ¨ Accidental tourists ¨ Natural disasters – Be ready to face down the hurricane 25 -SEPT-2001 19
What Are Threat Categories? Categories are the different kinds of threat you may encounter 25 -SEPT-2001 20
Threat Categories ¨ Opportunistic – Basic “ankle biters” and “script kiddies” – More advanced hackers, hacker groups out trolling ¨ Targeted – These attackers know what they want; anything from data to disruption to springboards ¨ “Omnipotent” – Government-sponsored professional hackers 25 -SEPT-2001 21
Threat Consequences ¨ Bad press – Breach of confidentiality • Medical data • Credit card information – Attack platform (you’ve been subverted!) ¨ Loss of income – How much does it cost you in sales to have your databases, website, etc, down for any given length of time? – Loss of trade secrets (crown jewels) 25 -SEPT-2001 22
The 3 Goals of Security ¨ Ensure Availability ¨ Ensure Integrity ¨ Ensure Authorization & Authentication 25 -SEPT-2001 23
Threats to Availability ¨ Denial of Service (Do. S) – Connection flooding ¨ Destroying data – Hardware failure – Manual deletion – Software agents: virus, trojans 25 -SEPT-2001 24
Threats to Integrity ¨ Hardware failure ¨ Software corruption – Buggy software – Improperly terminated programs ¨ Attacker altering data 25 -SEPT-2001 25
Threats to Authorization ¨ Attacker stealing data ¨ Lost / Stolen passwords ¨ Information Reconnaissance • Organization information 25 -SEPT-2001 26
Countering These Threats… …is what security is all about. 25 -SEPT-2001 27
Defining Security ¨ Security is a process – Training is ongoing • Threats change, admins need to keep up • Security is inconvenient, all staff needs training ¨ Security is also about policies ¨ There is no silver bullet to fix it all – For example, a firewall won’t save you • Remember the Maginot Line 25 -SEPT-2001 28
Notes: ¨ The underlying assumption in the next section is that you, as the auditor, admin, or manager, are in a position to make security recommendations ¨ The following list of questions should not be considered in any way to be exhaustive, but a starting point to build your own list 25 -SEPT-2001 29
Questions You Need to Ask ¨ What is the physical access policy to systems, routers, and backup media? – Are the servers and main routers in a controlled -access environment? – Who monitors access? ¨ Are desktop systems / workstations physically secured? 25 -SEPT-2001 30
Questions You Need to Ask ¨ Is there a documented security policy? – Where is it located? – Who is responsible for maintaining it? – Is the policy being consistently enforced? – Who is the enforcer for the organization? ¨ Is there a firewall? – Who maintains it and its rule-sets? – Do its rules match the policy? 25 -SEPT-2001 31
Questions You Need to Ask ¨ What is the backup policy & schedule? – What kind of backup media & software is used? – Where is the backup media stored? Is there an off-site safe/storage rotation? – If the systems were utterly destroyed today, how up to date could you bring their replacements? – Have the backups ever been tested (via a restore) for completeness and integrity? 25 -SEPT-2001 32
Questions You Need to Ask ¨ Does the organization know what is on its network? – If so, how does it know? – Where are the records kept? – Who has access to them? 25 -SEPT-2001 33
Questions You Need to Ask ¨ Are routine network vulnerability scans run? – If so, what tools are used? – Where are the reports stored? – Who has access to the tool and the reports? ¨ Is any routine network monitoring done? – If so, what tools are used? – Where are the reports stored? – Who has access to the tool and the reports? 25 -SEPT-2001 34
Questions You Need to Ask ¨ What kind of power management contingencies are available? – Uninterruptible Power Supplies (UPS)? – Power regulation? – Backup generators? – Mean time to recovery from outage? 25 -SEPT-2001 35
Questions You Need to Ask ¨ What kind of authentication does your organization use? – Passwords • Multi-use, one-time? • Expiration? – Biometric authentication? – Smart-cards 25 -SEPT-2001 36
Questions You Need to Ask ¨ If you use passwords, how does your organization replace lost ones? – Any policy on verifying user’s identity, etc? 25 -SEPT-2001 37
Questions You Need to Ask ¨ What kind of network connections does your organization allow? – Are they clear-text protocols (like telnet, rlogin, rsh, ftp)? – Can your organization migrate to using encrypted protocols (like ssh, stunnel, etc)? 25 -SEPT-2001 38
Recommendations You Really Want to Make ¨ No matter what, recommend a dedicated security officer – One individual responsible for security • NOT the sys admin, network admin – Qualifications: • Training • Certification (CISSP, SANS) • Demonstrated proficiency 25 -SEPT-2001 39
Recommendations You Really Want to Make ¨ Routine Vulnerability Scanning – Tools like Saint, Nessus, Legion, Nmap, SARA ¨ Principle of Least Privilege ¨ Documented Procedures for Incident Handling 25 -SEPT-2001 40
So, What Is a Security Officer? ¨ Protector – Internal, external ¨ Assessor ¨ Monitor ¨ Contact point – Law enforcement – Internal – External 25 -SEPT-2001 41
What Does It All Mean? ¨ It’s a dangerous world, but we’re not necessarily doomed! ¨ Security is an ongoing process (it’s worth repeating!) – Ask the questions you’ve seen here – Ask any others you think of – Ask them all again tomorrow – new challenges are arising every day! 25 -SEPT-2001 42
Acknowledgements ¨ Andy Johnston, manager and co-conspirator ¨ Jon Lasser, author of Think UNIX ¨ Stephen Northcutt, SANS instructor and author of Network Intrusion Detection 25 -SEPT-2001 43
Resources Online ¨ Training and Certifications – SANS Institute http: //www. sans. org/ – CISSP “Certification for Information System Security Professional” http: //www. cissps. com 25 -SEPT-2001 44
Resources Online (2) ¨ News & Alerts – Security Focus http: //www. securityfocus. com/ – CERT was “Computer Emergency Response Team” http: //www. cert. org/ – CIAC “Computer Incident Advisory Capability” http: //ciac. llnl. gov/ 25 -SEPT-2001 45
Resources Online (3) ¨ Federal Information Sharing Organizations – NIPC “National Infrastructure Protection Center” http: //www. nipc. gov – Infragard “Guarding the Nation’s Infrastructure” http: //www. infragard. net – Infragard Maryland Chapter http: //www. mdinfragard. org 25 -SEPT-2001 46
Resources Online (4) ¨ SSH http: //www. ssh. fi http: //www. openssh. org ¨ SSH tunnel http: //linuxdoc. org/HOWTO/mini/VPN. html http: //www. ccs. neu. edu/groups/systems/howto-sshtunnel. html ¨ Stunnel http: //mike. daewoo. com. pl/computer/stunnel/ http: //www. stanton. dtcc. edu/stanton/cs/admin/notes/ssl/ 25 -SEPT-2001 47
Resources Online (5) ¨ Network Monitoring Software – Snort http: //www. snort. org ¨ Network Vulnerability Scanners – Saint http: //wdsilx. wwdsi. com/saint – Nessus http: //www. nessus. org 25 -SEPT-2001 48
Resources Online (6) ¨ Kerberos http: //web. mit. edu/kerberos/www ¨ This Presentation http: //www. gl. umbc. edu/~robin/security. html 25 -SEPT-2001 49
- Slides: 49