Network Security DDo S l What is computer

- Slides: 41
Network Security - DDo. S l What is computer network security and why is important l Types and Strategies of DDo. S Attacks l DDo. S Attack Prevention l Conclusion
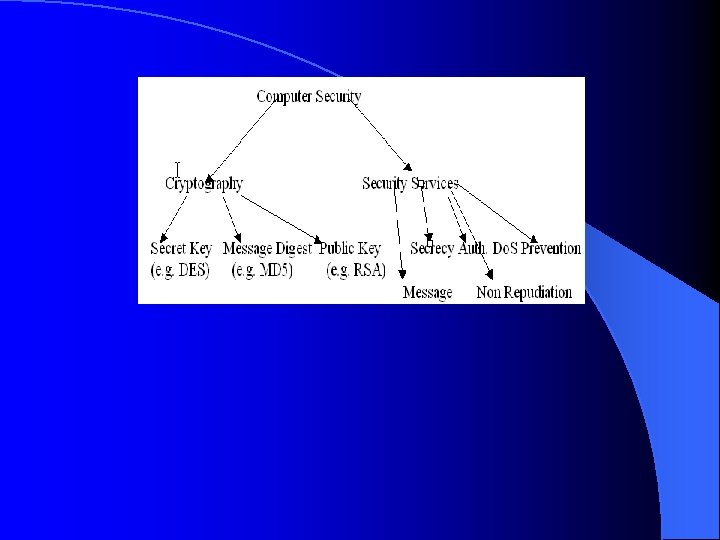
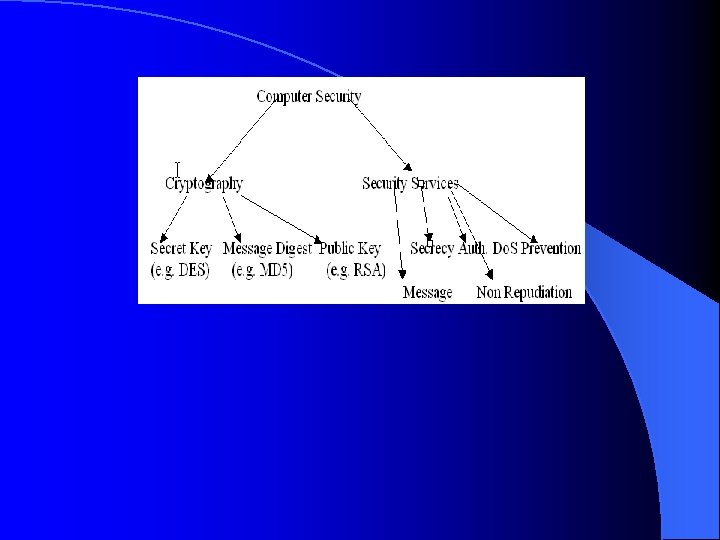
What is Network Security l Network Security is a huge topic that can be divided into two categories: - Cryptography - Network Security Services
Cryptography A process associated with scrambling plaintext (ordinary text, or clear text) into cipher text (a process called encryption), then back again ( a process called decryption) l
Network Security Services l 1. Secrecy The purpose of secrecy is to keep information out of the hands of unauthorized users. l 2. Authentication It deals with determining of whom you are talking to before releasing sensitive information or making a business deal. The sender and the receiver should be able to verify their identity l 3. Non Reputation It concerns with signatures. It’s purpose it’s to prove that the customer placed an order with the correct amount. l 4. Message Integrity The sender and the receiver should be able to verify that the message sent by the sender and received by the receiver is the correct one and it’s not malicious modified in transit. l 5. Denial of Service (Do. S) Prevention Do. S is a type of attack on a network that is designed to bring the network to its knees by flooding it with useless traffic.
WHY DO WE NEED SECURITY? With the rapid development of the Internet , companies build their own LANs and give Internet access to their employees. As a result any Internet user can connect to an insecure LAN. Computer and Network Security is Important l To protect company assets “Assets” can be any information that is housed on a company’s computers. l To gain a competitive advantage For example no one will use an Internet Banking System if that system is being hacked in the past. l To ensure the continuity of the organization. (Some organizations rely on computers for their continuing operations) l For the System Administrators and Network Engineers to keep their job.
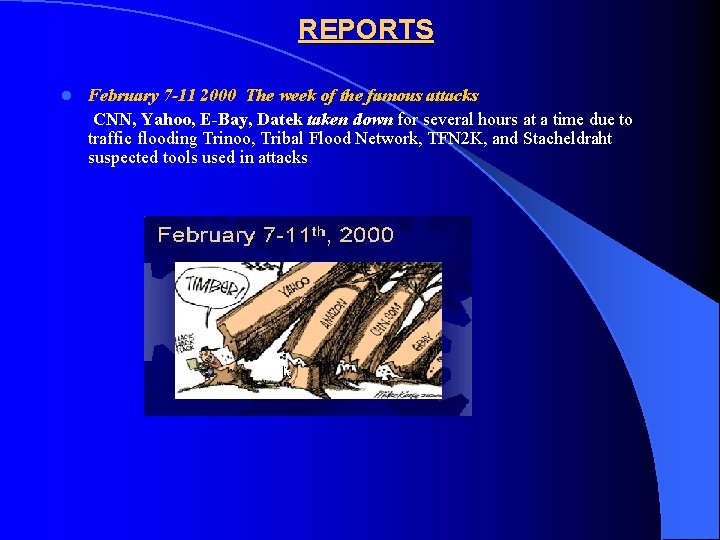
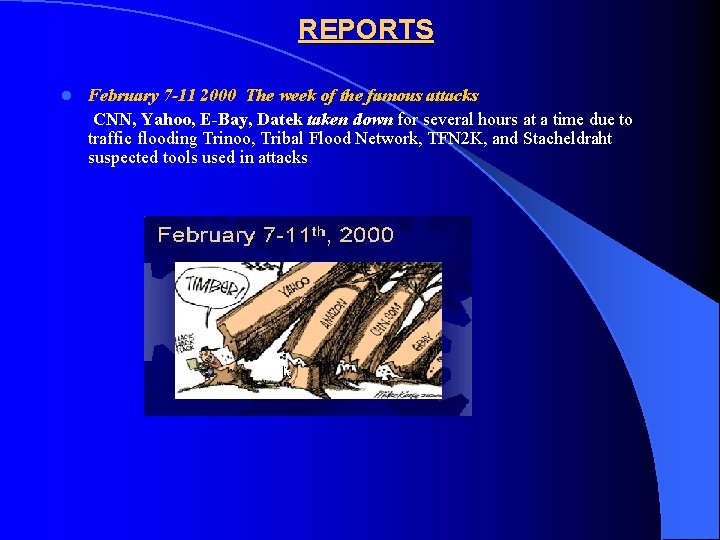
REPORTS February 7 -11 2000 The week of the famous attacks CNN, Yahoo, E-Bay, Datek taken down for several hours at a time due to traffic flooding Trinoo, Tribal Flood Network, TFN 2 K, and Stacheldraht suspected tools used in attacks l
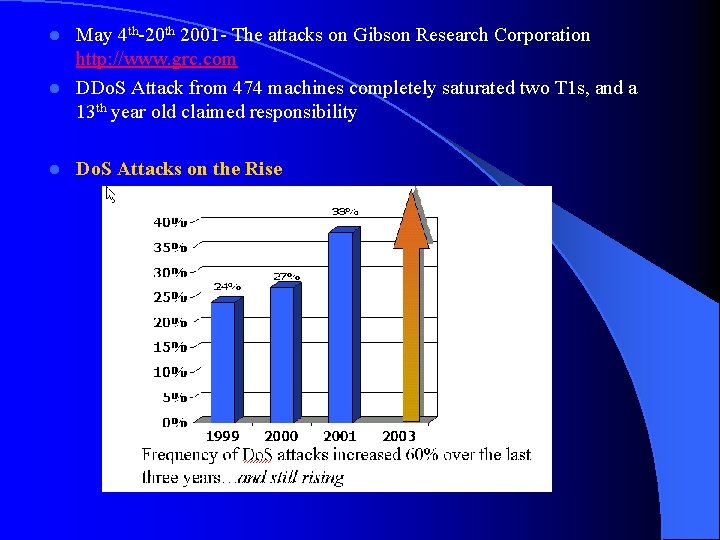
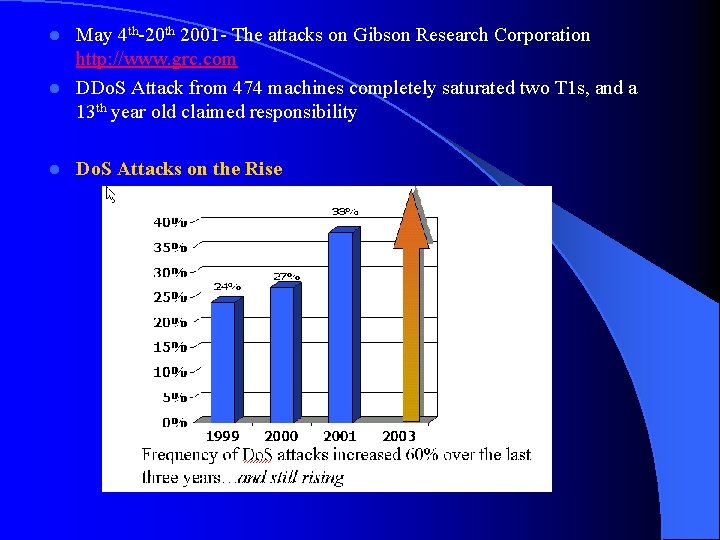
May 4 th-20 th 2001 - The attacks on Gibson Research Corporation http: //www. grc. com l DDo. S Attack from 474 machines completely saturated two T 1 s, and a 13 th year old claimed responsibility l l Do. S Attacks on the Rise
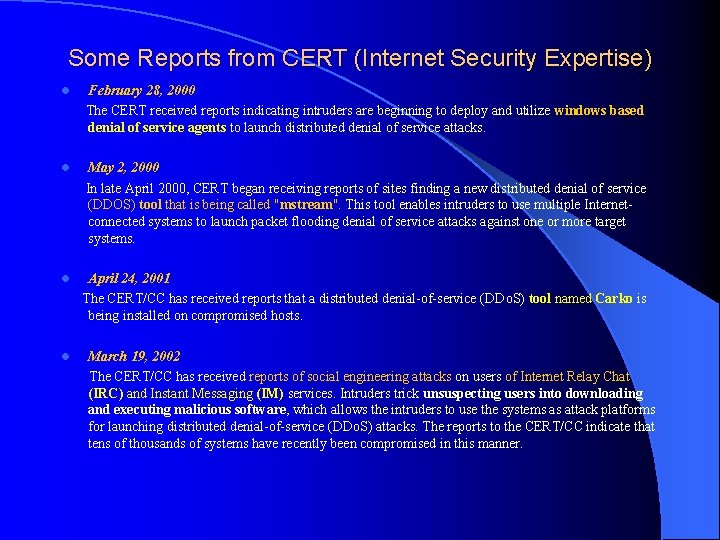
Some Reports from CERT (Internet Security Expertise) February 28, 2000 The CERT received reports indicating intruders are beginning to deploy and utilize windows based denial of service agents to launch distributed denial of service attacks. l May 2, 2000 In late April 2000, CERT began receiving reports of sites finding a new distributed denial of service (DDOS) tool that is being called "mstream". This tool enables intruders to use multiple Internetconnected systems to launch packet flooding denial of service attacks against one or more target systems. l April 24, 2001 The CERT/CC has received reports that a distributed denial-of-service (DDo. S) tool named Carko is being installed on compromised hosts. l March 19, 2002 The CERT/CC has received reports of social engineering attacks on users of Internet Relay Chat (IRC) and Instant Messaging (IM) services. Intruders trick unsuspecting users into downloading and executing malicious software, which allows the intruders to use the systems as attack platforms for launching distributed denial-of-service (DDo. S) attacks. The reports to the CERT/CC indicate that tens of thousands of systems have recently been compromised in this manner. l
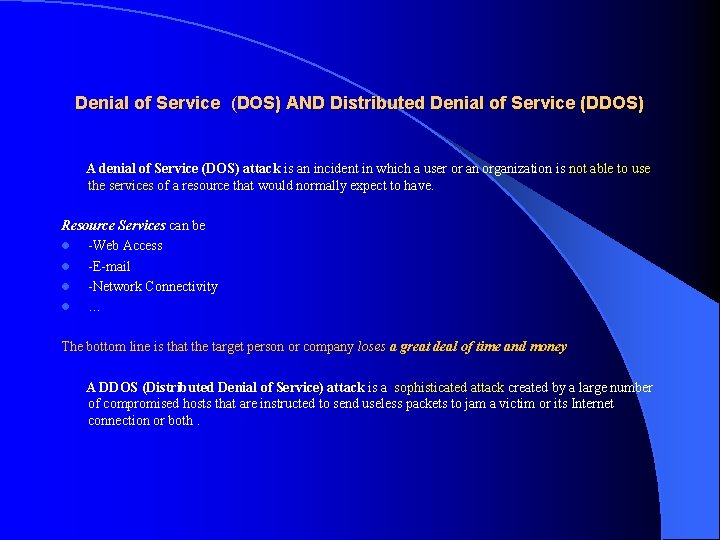
Denial of Service (DOS) AND Distributed Denial of Service (DDOS) A denial of Service (DOS) attack is an incident in which a user or an organization is not able to use the services of a resource that would normally expect to have. Resource Services can be l -Web Access l -E-mail l -Network Connectivity l … The bottom line is that the target person or company loses a great deal of time and money A DDOS (Distributed Denial of Service) attack is a sophisticated attack created by a large number of compromised hosts that are instructed to send useless packets to jam a victim or its Internet connection or both.
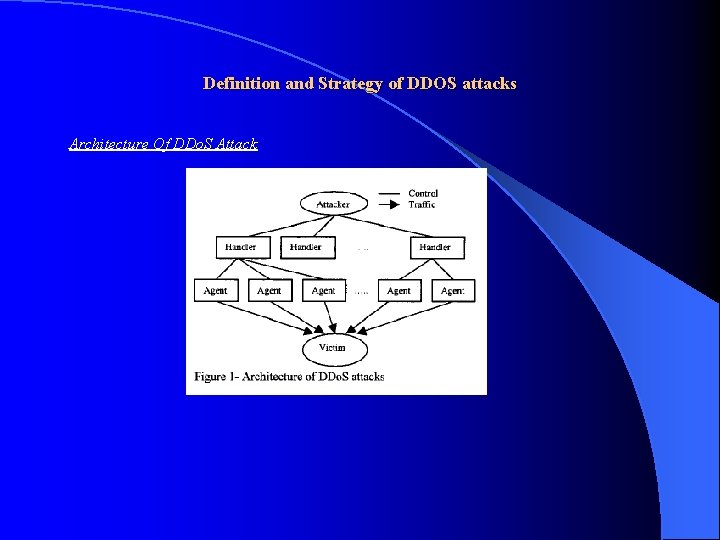
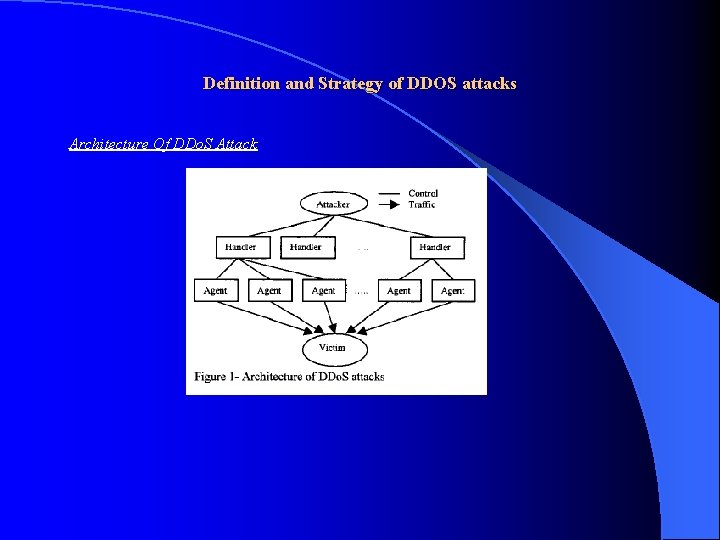
Definition and Strategy of DDOS attacks Architecture Of DDo. S Attack
Architecture of DDOS Attack A DDOS Attack uses many computers to launch a coordinate DOS attack against one or more targets. Using client/server technology the penetrator is able to multiply the effectiveness of the Do. S significantly by harnessing the resources of multiple computers which serve attack platforms. A DDOS is composed of four elements l The Real Attacker l The Handlers or master compromised hosts, who are capable of controlling multiple agents l The Attack daemon agents or zombie hosts who are responsible for generating a stream of packets toward the victim l The victim or the target host Step 1: Recruitment l q The Attacker chooses the vulnerable agents which will be used to perform the attack Step 2: Compromise l q The Attacker exploits the vulnerabilities of the agents and plants the attack code, protecting l it simultaneously from discovery and deactivation. Step 3: Communication l q The agents inform the attacker via handlers that they are ready Step 4: Attack l q The Attacker commands the onset of the attack
Powerful DDOS toolkits Sophisticated and powerful DDOS toolkits are available to potential attackers such as l v TRINOO l v TFN l v STACHELDRAHT l v TFN 2 K l v MSTREAM l v SHAFT
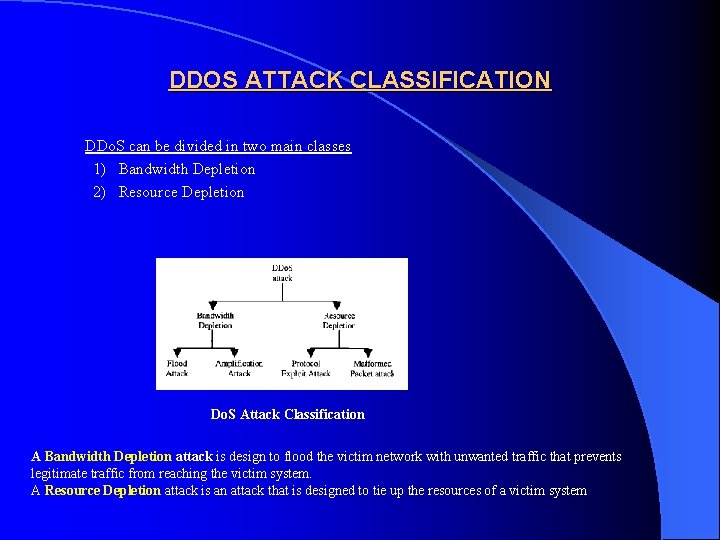
DDOS ATTACK CLASSIFICATION DDo. S can be divided in two main classes 1) Bandwidth Depletion 2) Resource Depletion Do. S Attack Classification A Bandwidth Depletion attack is design to flood the victim network with unwanted traffic that prevents legitimate traffic from reaching the victim system. A Resource Depletion attack is an attack that is designed to tie up the resources of a victim system
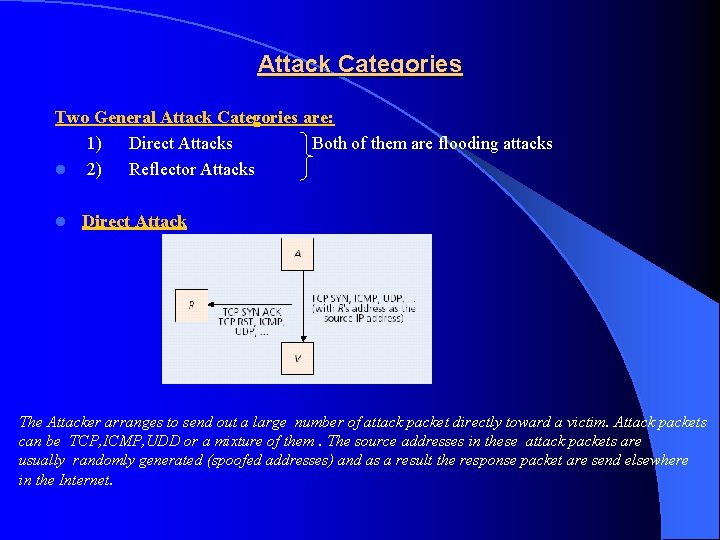
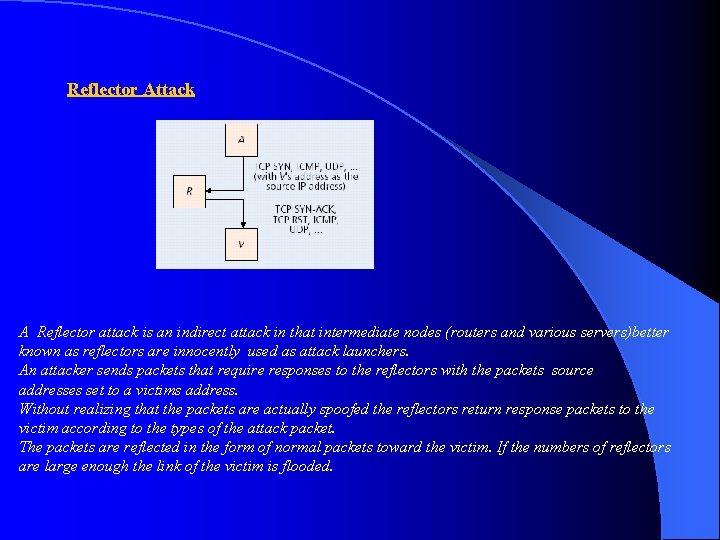
Attack Categories Two General Attack Categories are: 1) Direct Attacks Both of them are flooding attacks l 2) Reflector Attacks l Direct Attack The Attacker arranges to send out a large number of attack packet directly toward a victim. Attack packets can be TCP, ICMP, UDD or a mixture of them. The source addresses in these attack packets are usually randomly generated (spoofed addresses) and as a result the response packet are send elsewhere in the Internet.
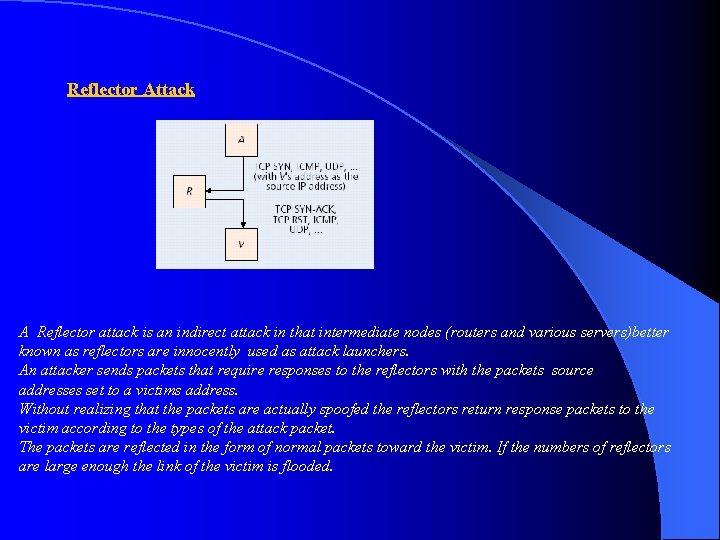
Reflector Attack A Reflector attack is an indirect attack in that intermediate nodes (routers and various servers)better known as reflectors are innocently used as attack launchers. An attacker sends packets that require responses to the reflectors with the packets source addresses set to a victims address. Without realizing that the packets are actually spoofed the reflectors return response packets to the victim according to the types of the attack packet. The packets are reflected in the form of normal packets toward the victim. If the numbers of reflectors are large enough the link of the victim is flooded.
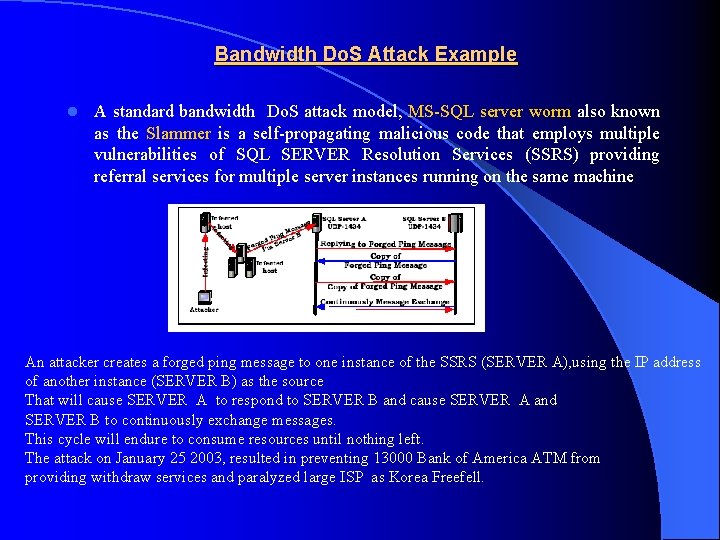
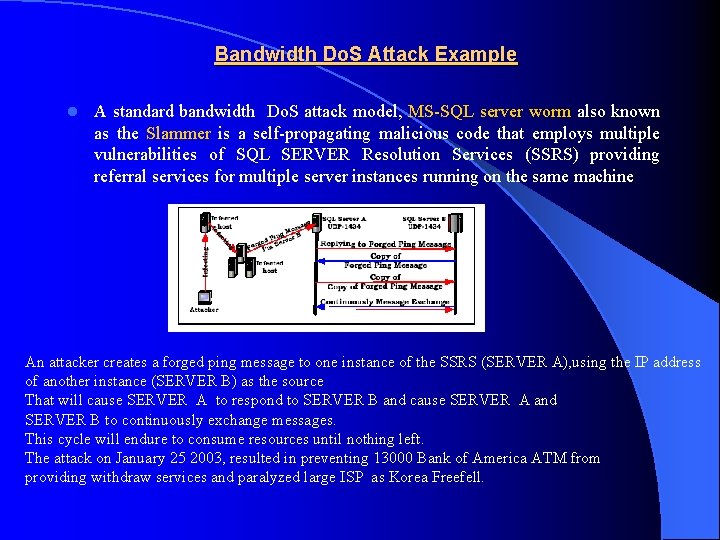
Bandwidth Do. S Attack Example l A standard bandwidth Do. S attack model, MS-SQL server worm also known as the Slammer is a self-propagating malicious code that employs multiple vulnerabilities of SQL SERVER Resolution Services (SSRS) providing referral services for multiple server instances running on the same machine An attacker creates a forged ping message to one instance of the SSRS (SERVER A), using the IP address of another instance (SERVER B) as the source That will cause SERVER A to respond to SERVER B and cause SERVER A and SERVER B to continuously exchange messages. This cycle will endure to consume resources until nothing left. The attack on January 25 2003, resulted in preventing 13000 Bank of America ATM from providing withdraw services and paralyzed large ISP as Korea Freefell.
Memory Do. S Attack l l Every TCP connection establishment requires an allocation of significant memory resources. Typically 280 Bytes on BSD. There is a limit on the number of concurrent TCP half-open connections. The range of the backlog queue size on various Oses is 6 to 128 By sending overdosed connection requests with spoofed source addresses to the victim, an attacker can disable all successive connection establishment attempts including those of legitimate users.
DDo. S TYPES A. FLOOD ATTACK B. LOGIC OR SOFTWARE ATTACKS
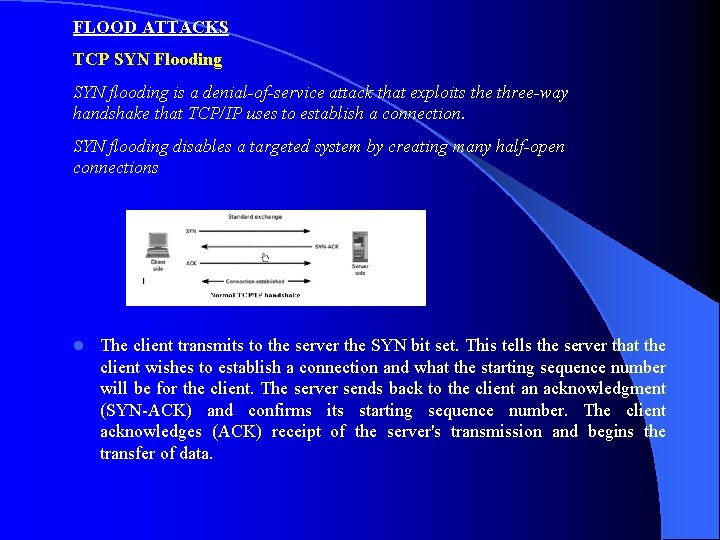
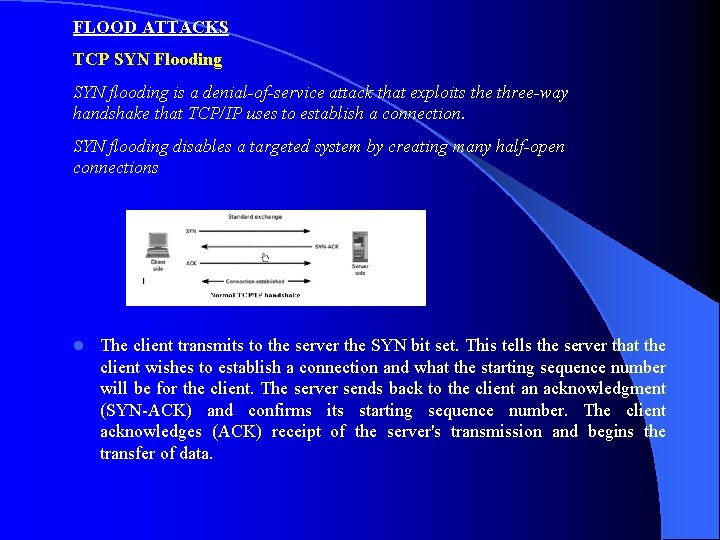
FLOOD ATTACKS TCP SYN Flooding SYN flooding is a denial-of-service attack that exploits the three-way handshake that TCP/IP uses to establish a connection. SYN flooding disables a targeted system by creating many half-open connections l The client transmits to the server the SYN bit set. This tells the server that the client wishes to establish a connection and what the starting sequence number will be for the client. The server sends back to the client an acknowledgment (SYN-ACK) and confirms its starting sequence number. The client acknowledges (ACK) receipt of the server's transmission and begins the transfer of data.
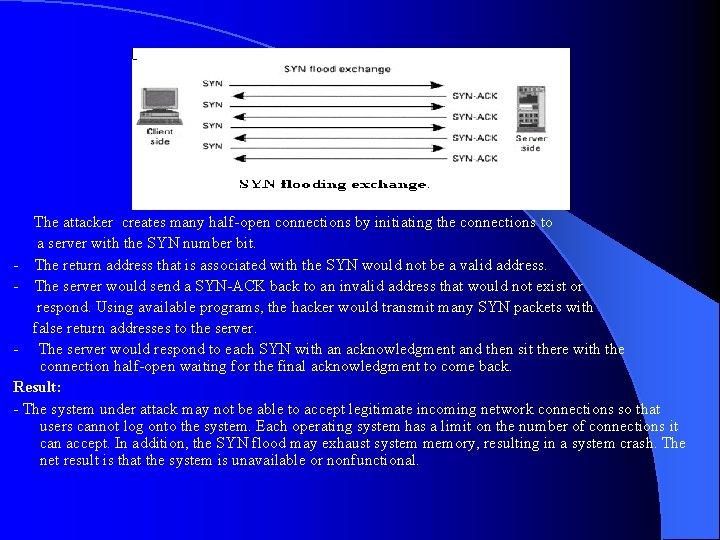
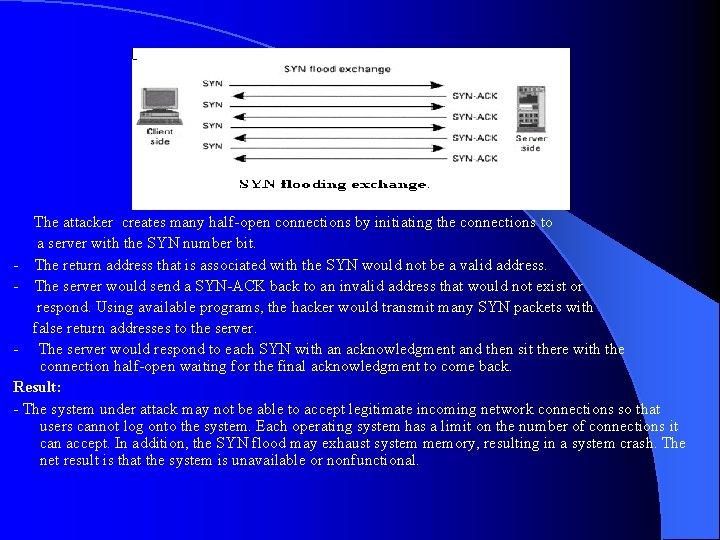
The attacker creates many half-open connections by initiating the connections to a server with the SYN number bit. - The return address that is associated with the SYN would not be a valid address. - The server would send a SYN-ACK back to an invalid address that would not exist or respond. Using available programs, the hacker would transmit many SYN packets with false return addresses to the server. - The server would respond to each SYN with an acknowledgment and then sit there with the connection half-open waiting for the final acknowledgment to come back. Result: - The system under attack may not be able to accept legitimate incoming network connections so that users cannot log onto the system. Each operating system has a limit on the number of connections it can accept. In addition, the SYN flood may exhaust system memory, resulting in a system crash. The net result is that the system is unavailable or nonfunctional.
Smurf Attack: – Smurf Attack l Amplification attack Sends ICMP ECHO to network l Network sends response to victim system l l The "smurf" attack's cousin is called "fraggle", which uses UDP echo packets in the same fashion
• The attacker wants a result of tons of ping replies flooding the host they intend to exploit. This attack causes a Do. S.
UDP Flood Attack: UDP is a connectionless protocol and it does not require any connection setup procedure to transfer data. A UDP Flood attack is possible when an attacker sends a UDP packet to a random port on the victim system. When the victim system receives a UDP packet, it will determine what application is waiting on the destination port. When it realizes that there is no application that is waiting on the port, it will generate an ICMP packet of destination unreachable to the forged source address. If enough UDP packets are delivered to ports on victim, the system will go down. http: //www. cert. org/advisories/CA-1996 -01. html l
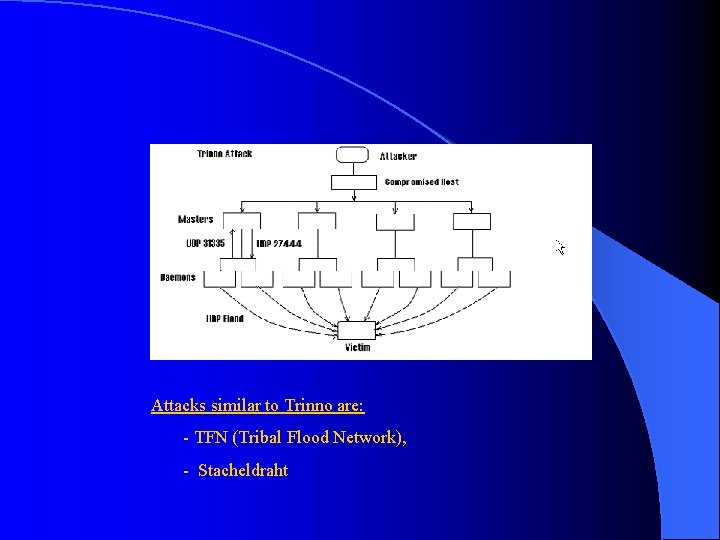
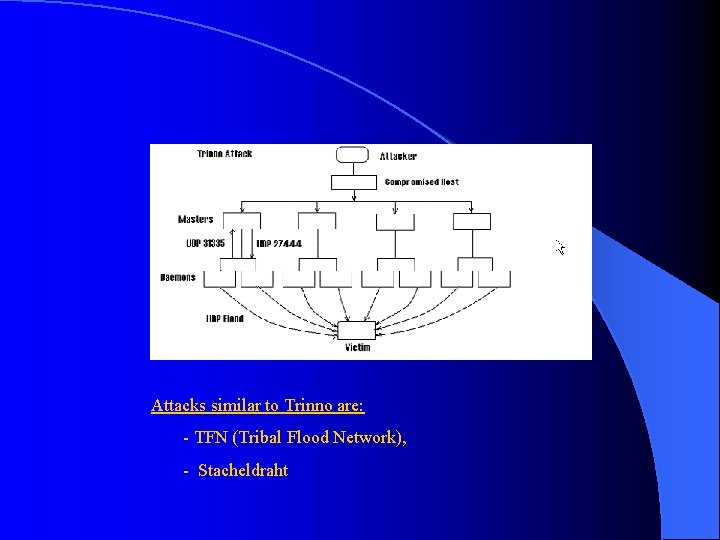
Attacks similar to Trinno are: - TFN (Tribal Flood Network), - Stacheldraht
Logic or Software Attacks Ping of Death: An attacker sends an ICMP ECHO request packet that is much larger than the maximum IP packet size to victim. Since the received ICMP echo request packet is bigger than the normal IP packet size, the victim cannot reassemble the packets. The OS may be crashed or rebooted as a result. ping -l 65510 your. host. ip. address http: //www. insecure. org/sploits/ping-o-death. html l
Teardrop: An attacker sends two fragments that cannot be reassembled properly by manipulating the offset value of packet and cause reboot or halt of victim system. Many other variants such as targa, SYNdrop, Boink, Nestea Bonk, Tear. Drop 2 and New. Tear are available. http: //www. cert. org/advisories/CA-1997 -28. html l l Land: An attacker sends a forged packet with the same source and destination IP address. The victim system will be confused and crashed or rebooted http: //www. cert. org/advisories/CA-1997 -28. html
l Echo/Chargen: The character generator (chargen) service is designed to simply generate a stream of characters. It is primarily used for testing purposes. Remote users/intruders can abuse this service by exhausting system resources. Spoofed network sessions that appear to come from that local system's echo service can be pointed at the chargen service to form a "loop. " This session will cause huge amounts of data to be passed in an endless loop that causes heavy load to the system. When this spoofed session is pointed at a remote system's echo service, this denial of service attack will cause heavy network traffic/overhead that considerably slows your network down. It should be noted that an attacker does not need to be on your subnet to perform this attack as he/she can forge the source addresses to these services with relative ease.
Defending Measures A. System Self Defense B. Packet Filtering A lot of defensive measures exist, but few of them are effective under DDo. S. Actually some of them are vulnerable to Do. S themselves. Defending can be very difficult because the syn packets are part of normal traffic, and the source IP can be fake. A. System Self Defense 1. Reduce the number of targets that can be attacked. Stop all unnecessary or non- essential system services or network ports. 2. Increase the difficulty of TCP Syn attacks by : a. Enlarging the length of backlog queue b. Reduce the time-out period in order to cope with more simultaneous halfopen connection
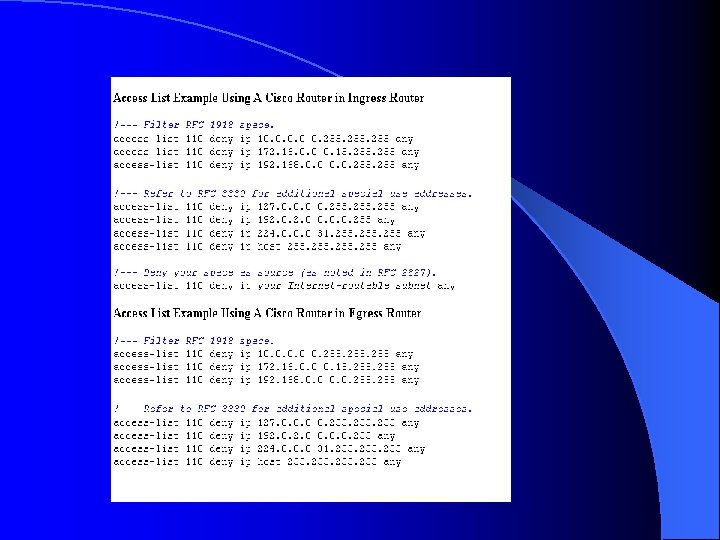
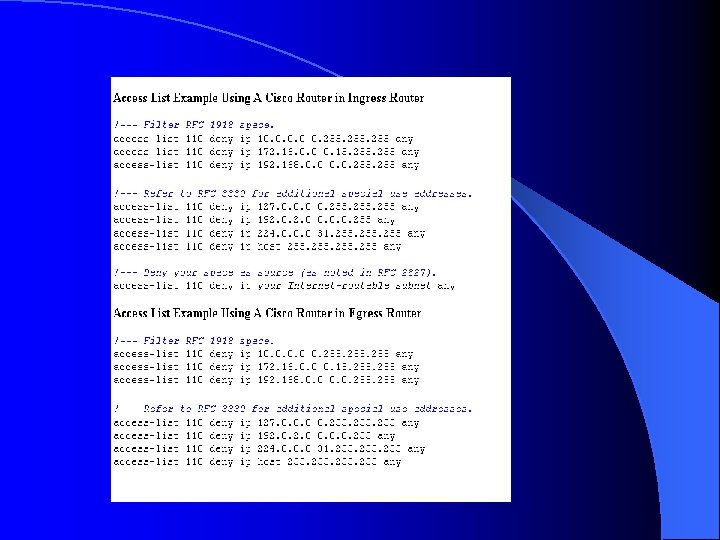
B. Packet Filtering It deals on how to continuously monitor TCP/IP traffic in a network, looking for irregularity in packet behavior. Once a packet is determined as being malicious, the monitor agent will either discard it or reset any pending connection request. 1. Ingress Filtering ISPs take actions against Do. S/DDo. S that include: - Eliminating routing of spoofed packets by discarding any packet that contains any RFC 1918 or reserved IP address RFC 3330 in the IP source or destination address Drop packets with IP addresses outside the range of a customer’s network, so they can prevent attackers from using forge source addresses to launch a Do. S attack. The weaknesses of applying ingress filtering technique is that, it does nothing to address flooding attacks that originate from valid IP addresses.
2. Egress Filtering is a source-network mechanism. It prevents one’s network from being the source of forged communications used in Do. S attacks These filters analyze packets as they are forwarded to their intended destination, looking forged (spoofed) IP addresses. Since any particular network is assigned a specific subset of IP addresses, any packet containing an invalid IP address is assumed to be spoofed, and the filter drops such packets. This ensures that only IP packets with valid source IP addresses leave the network and thus protects the outside from spoofed packets. Weakness l Does not protect the network from attack but it only keeps an attacker from using the network to perform a DDo. S l Cannot detect internal spoofed IPs.
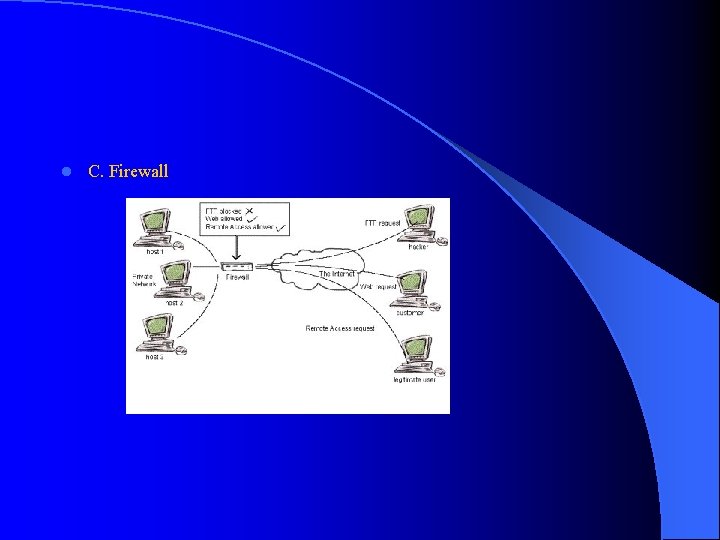
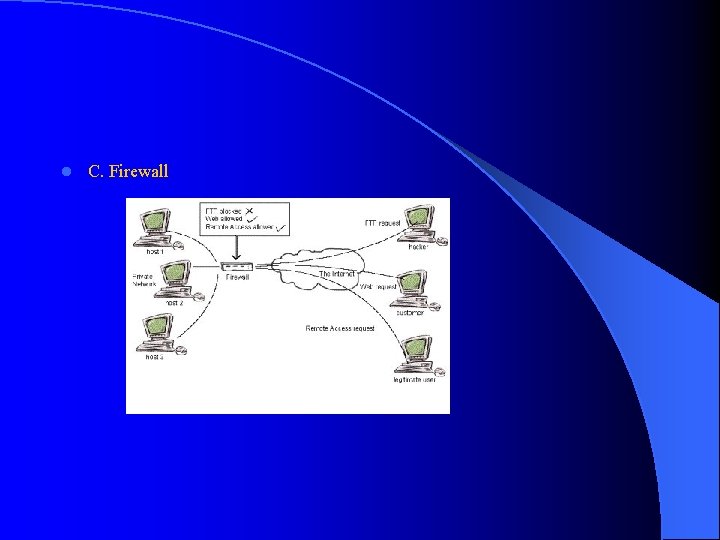
l C. Firewall
Firewall - A firewall is used to secure the network of an organization. It is a device that attempts to prevent unauthorized access to a network. It is usually located at the boundary where a private network interfaces with the external world - A firewall can block the arrival of potentially malicious TCP connection request at the destination host’s packets - It is used as a request proxy that answers the requests on its behalf, or as a TCP connection request monitor The negative points are : l a. The firewall causes new delays for every connection, including those for legitimate users. l b. A firewall might be vulnerable by itself. l c. A specialized firewall can be disabled by a flood of 14000 packets per second
State Monitoring D. State Monitoring: Some software agents are used to determine whether or not a packet is malicious Real. Secure monitors the local network for SYN packets that are not acknowledged for a period of time defined by the users. Synkill supports a finite state machine that classifies IP addresses as good or bad. Unicast RPF examines all packets received at the input interface to make sure that the source address and the source interface pair is in a special routing table. WATCHER maintains multiple decentralized counters that are exchanged periodically among the neighbors of the suspected router.
State Monitoring TDSAM describes flow behavior by classifying individual profiles as either short -term or long-term components. All of these software agents need to maintain tremendous states to determine whether or not a packet is malicious. Hence, they are vulnerable to Do. S attacks.
Congestion Control E. Congestion Control - Pushback is a router-based solution against bandwidth attacks, which employs the concept of aggregate-based congestion control to identify most of the malicious packets. - It uses the destination prefix as a congestion signature to distinguish and protect the legitimate traffic within the aggregate - It adds rate-limiting functionality to the routers to detect and drop suspicious packets -Pushback notifies the upstream routers to rate limiting packets destined to a victim order to let other legitimate traffic move - However, pushback cannot block effectively bad traffic under a DDo. S attack that is uniformly distributed on inbound links It cannot distinguish between good and bad traffic going to the destination, and will drop them equally (Aggregate: Is a set of packets with a common feature)

Other Defense Approaches l Traceback l D-Ward l Net. Bouncer l Secure Overlay Services (SOS) l Proof of Work l Hop-Count Filtering l…
Conclusions DDos attacks are very difficult to defend against but following the defensive measures mentioned will greatly reduce the chances of the network to be used as source or as the victim in a DDo. S attack. l Network engineers should be updated about the new attacking tools, and with the new defending techniques. They should always be in an alert situation l A lot of money are spend daily in computer network security, and they will be spend in the future. Computer Network Security is a subject that will always keep be in the headline news. l
References l l l Analysis of Denial-of-Service Attacks on Denial-of-Service Defensive - Measures Bao-Tung Wang, Henning Schulzrinne Defending against Flooding-Based Distributed Denial-of-Service Attacks - Rocky K. C. Chang, The Hong Kong Polytechnic University On the Defense of the Distributed Denial of Service - Attacks: An On–Off Feedback Control Approach – Yong Xiong, Steve. Liu, and Peter. Sun, Member, IEEE Protocol Scrubbing: Network Security Through Transparent Flow Modification David Watson, Matthew Smart, G. Robert Malan, Member, IEEE, and Farnam Jahanian, Member, IEEE What Is Computer Security? - Matt Bishop, bishop@cs. ucdavis. edu An Active Network-Based Intrusion Detection and Response Systems – Han-Pang Hang and Chia Ming Chang Dos Attacks and Defense Mechanism: A Classification – Christos Douligenis, Aikaterini Mitrokotsa Computer Network 4 th Edition – A. Tanenbaum Dr. Christos Panayiotou Lecture Notes http: //www. cert. org http: //www. cisco. com