SDNNFV DDo S Requirements The Mobile Use Case
SDN/NFV DDo. S Requirements "The Mobile Use Case – 5 G" Bipin Mistry, VP Product Management © 2015 Corero www. corero. com
The Shift from Transport Centric to Service Centric Architectures § Yesterday’s SP Network – • Access Edge, • Pre-Agg, • Aggregation, • Transport Core, • Centralized • Services/services complex • Not open • Security - maybe as an overlay, some level of encryption - DDo. S – either RTBH, scrubbed or passed on downstream 2 © 2015 Corero www. corero. com
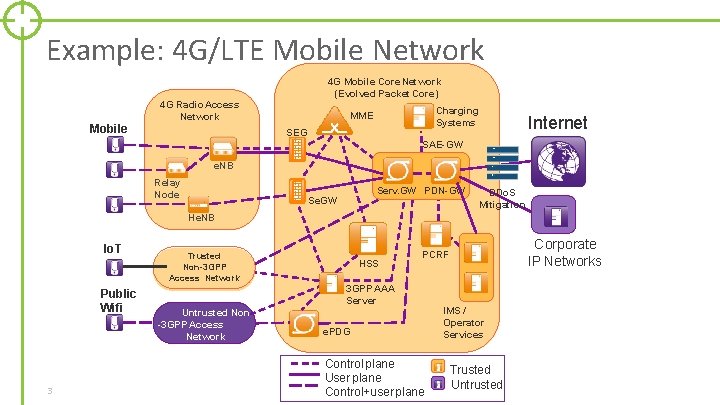
Example: 4 G/LTE Mobile Network Mobile 4 G Mobile Core Network (Evolved Packet Core) 4 G Radio Access Network Charging Systems MME SEG Internet SAE-GW e. NB Relay Node Serv. GW PDN-GW Se. GW DDo. S Mitigation He. NB Io. T Public Wifi 3 Trusted Non-3 GPP Access Network HSS 3 GPP AAA Server Untrusted Non -3 GPP Access Network Corporate IP Networks PCRF e. PDG Control plane User plane Control+user plane IMS / Operator Services Trusted Untrusted
Threat mitigation • § § 3 GPP addresses security of interfaces mainly § Security specified for radio interface, backhaul link, core interfaces § protects traffic against interception, modification, replay § Subscriber authentication § protects against theft of service, impersonation of other subscribers, fraud There’s a new trend in 3 GPP to cover also platform security – by § standardizing requirements (solutions are proprietary) This leaves a lot to address otherwise: § Flooding, crashing or compromising nodes by exploiting implementation flaws, § compromising network elements via weak O&M procedures, … § IP network security, network element security § Out of scope here: physical site protection, organizational security measures (e. g. malicious insider threat)
The Shift from Transport Centric to Service Centric Architectures § Tomorrow’s SP Network Architecture: • Service/subscriber centric • Virtualized - At the Network and Application level • Programmable • Server Centric - Not appliance centric - White box solutions • • 5 Elastic Intelligent – Analytics driven Service Velocity Has to be SECURE!!!! – What type of security ? © 2015 Corero www. corero. com

5 G – as an example
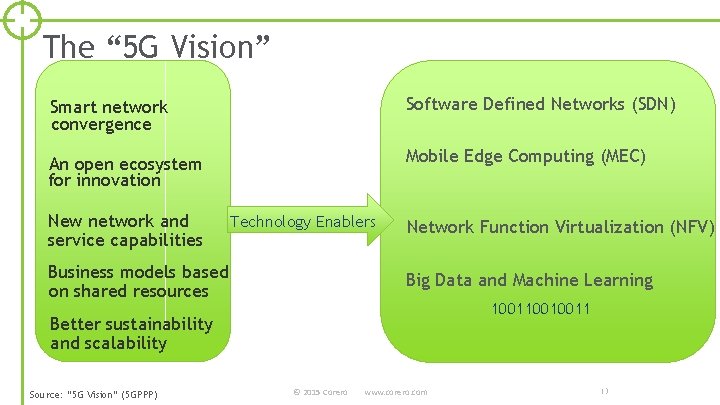
The “ 5 G Vision” Smart network convergence Software Defined Networks (SDN) An open ecosystem for innovation Mobile Edge Computing (MEC) New network and service capabilities Technology Enablers Business models based on shared resources Network Function Virtualization (NFV) Big Data and Machine Learning 10010011 Better sustainability and scalability Source: “ 5 G Vision” (5 GPPP) © 2015 Corero www. corero. com 13
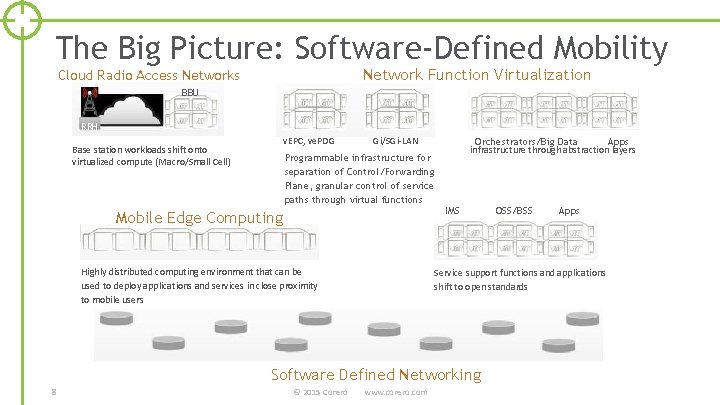
The Big Picture: Software-Defined Mobility Network Function Virtualization Cloud Radio Access Networks BBU RRH v. EPC, ve. PDG Base station workloads shift onto virtualized compute (Macro/Small Cell) Gi/SGi-LAN Orchestrators/Big Data Apps infrastructure through abstraction layers Programmable infrastructure for separation of Control/Forwarding Plane, granular control of service paths through virtual functions IMS Mobile Edge Computing Highly distributed computing environment that can be used to deploy applications and services in close proximity to mobile users © 2015 Corero Apps Service support functions and applications shift to open standards Software Defined Networking 8 OSS/BSS www. corero. com

Security – Specifically DDo. S
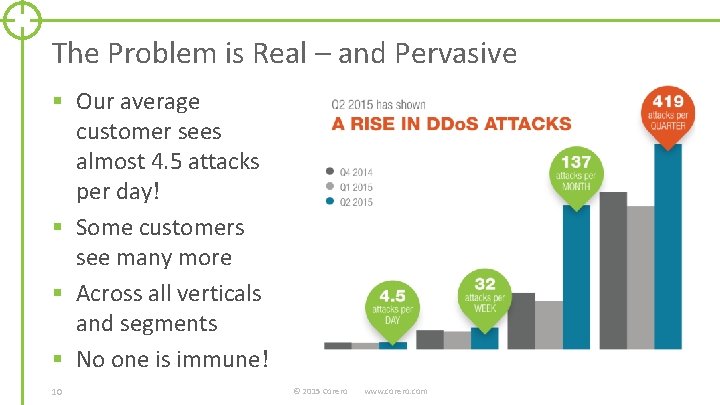
The Problem is Real – and Pervasive § Our average customer sees almost 4. 5 attacks per day! § Some customers see many more § Across all verticals and segments § No one is immune! 10 © 2015 Corero www. corero. com
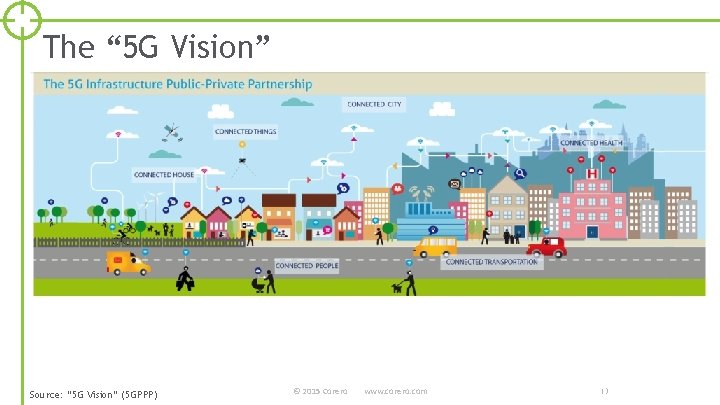
The “ 5 G Vision” Source: “ 5 G Vision” (5 GPPP) © 2015 Corero www. corero. com 13

Thank You
- Slides: 12