On the Feasibility of Reroutingbased DDo S Defenses
On the Feasibility of Rerouting-based DDo. S Defenses Muoi Tran, Min Suk Kang, Hsu-Chun Hsiao, Wei-Hsuan Chiang, Shu-Po Tung, Yu-Su Wang May 2019 | San Francisco, CA
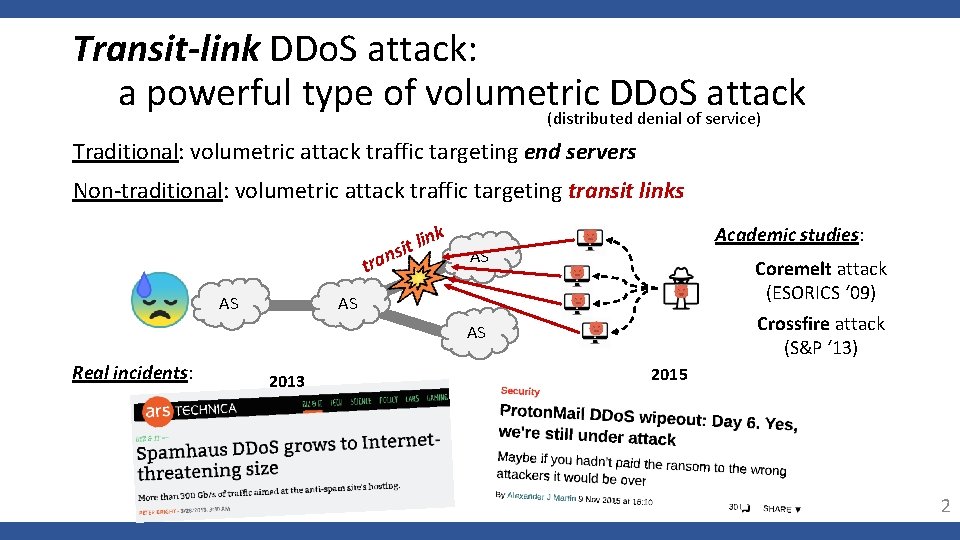
Transit-link DDo. S attack: a powerful type of volumetric DDo. S attack (distributed denial of service) Traditional: volumetric attack traffic targeting end servers Non-traditional: volumetric attack traffic targeting transit links tr k n i l it ans Academic studies: AS Coremelt attack (ESORICS ‘ 09) AS AS Crossfire attack (S&P ‘ 13) AS Real incidents: 2013 2015 2
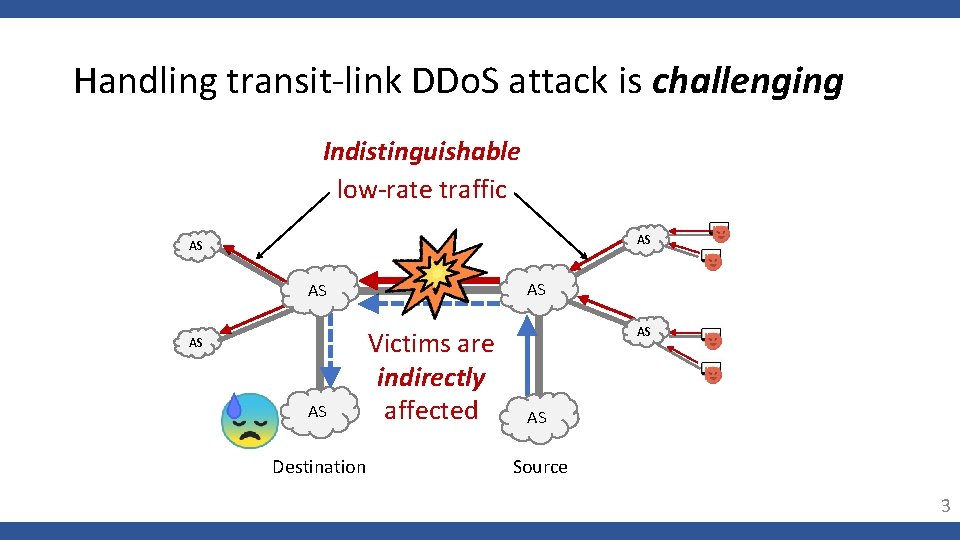
Handling transit-link DDo. S attack is challenging Indistinguishable low-rate traffic AS AS AS Destination Victims are indirectly affected AS AS Source 3
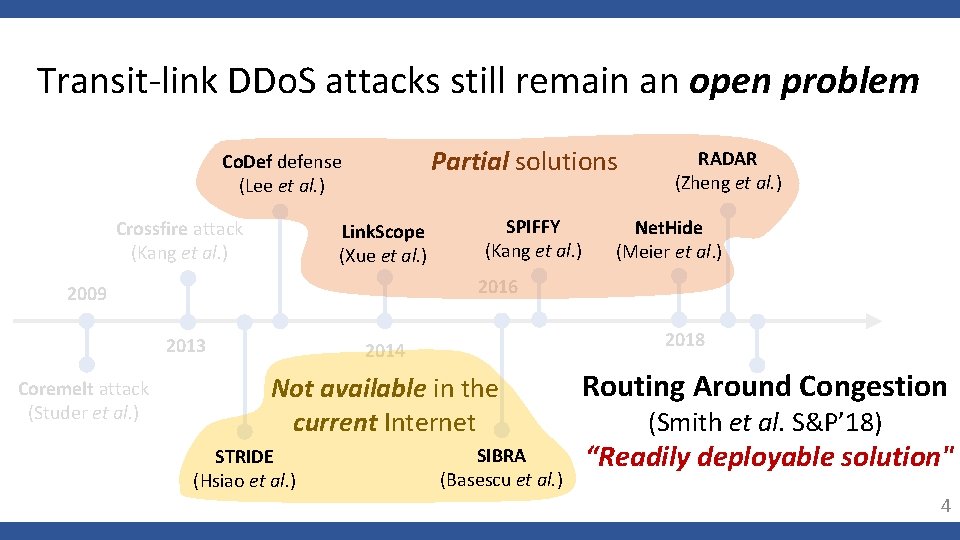
Transit-link DDo. S attacks still remain an open problem Partial solutions Co. Def defense (Lee et al. ) Crossfire attack (Kang et al. ) Link. Scope (Xue et al. ) Net. Hide (Meier et al. ) 2016 2009 2013 Coremelt attack (Studer et al. ) SPIFFY (Kang et al. ) RADAR (Zheng et al. ) 2018 2014 Not available in the current Internet STRIDE (Hsiao et al. ) SIBRA (Basescu et al. ) Routing Around Congestion (Smith et al. S&P’ 18) “Readily deployable solution" 4
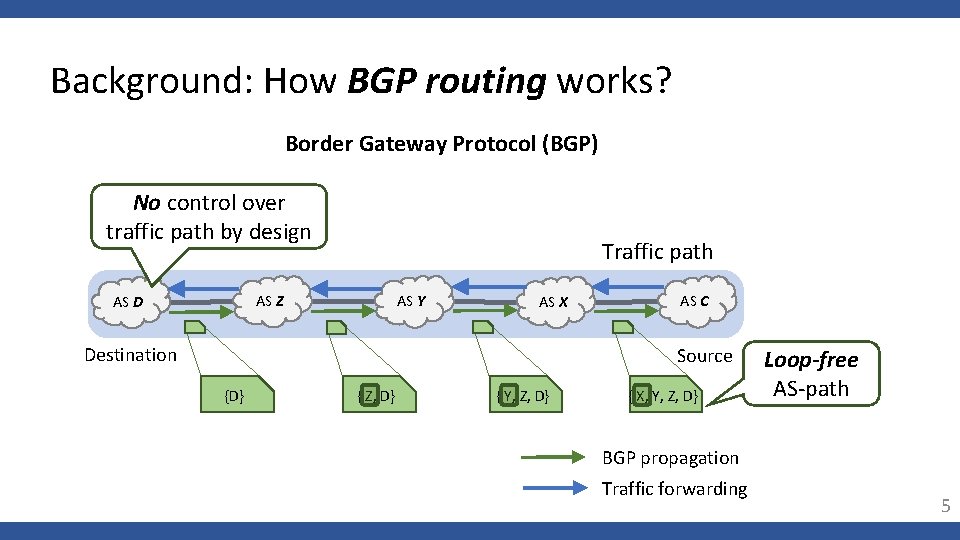
Background: How BGP routing works? Border Gateway Protocol (BGP) No control over traffic path by design Traffic path AS Y AS Z AS D AS X Destination AS C Source {D} { Z, D} { Y, Z, D} { X, Y, Z, D} Loop-free AS-path BGP propagation Traffic forwarding 5
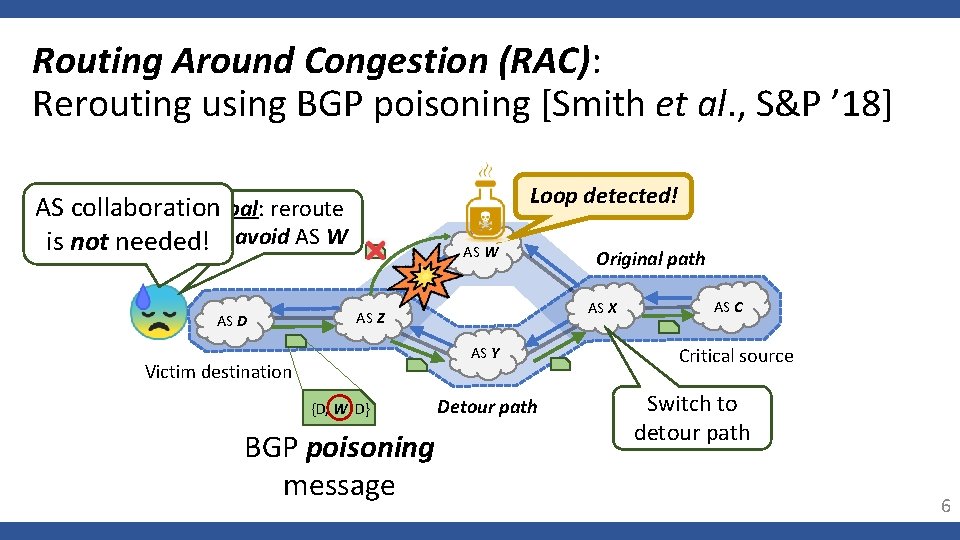
Routing Around Congestion (RAC): Rerouting using BGP poisoning [Smith et al. , S&P ’ 18] x Loop detected! AS collaboration. Goal: reroute is not needed!to avoid AS W AS D AS W AS X AS Z AS Y Victim destination {D, W, D} BGP poisoning message Original path Detour path AS C Critical source Switch to detour path 6
Will RAC defense still work against adaptive attackers? 7
Our contributions Adaptive detour-learning attack against rerouting solutions Practical challenge of mitigating adaptive detour-learning attack Future directions for transit-link DDo. S defenses 8
Adaptive detour-learning attack: Threat model Goals: (1) To detect rerouting in real-time (2) To learn new detour path accurately (3) To congest new detour path (see the paper) Capabilities: - Same botnets used in transit-link DDo. S attack 9
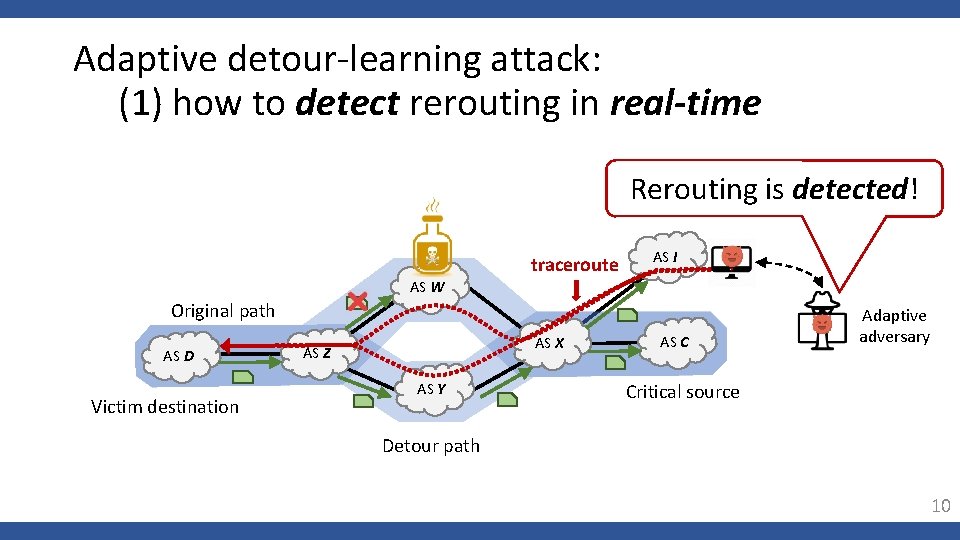
Adaptive detour-learning attack: (1) how to detect rerouting in real-time Rerouting is detected! traceroute AS I AS W Original path AS D Victim destination AS X AS Z AS Y AS C Adaptive adversary Critical source Detour path 10
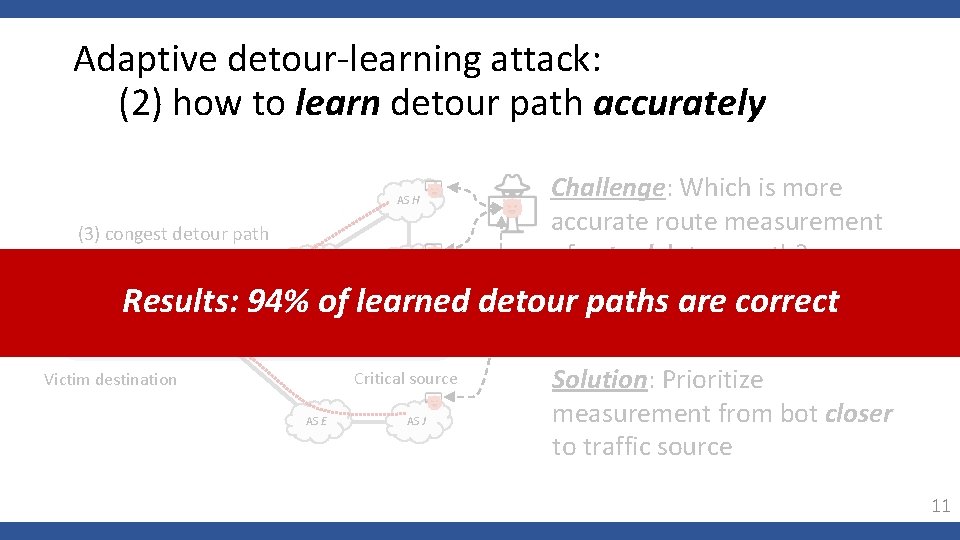
Adaptive detour-learning attack: (2) how to learn detour path accurately AS H (3) congest detour path (see the paper) AS G AS I Challenge: Which is more accurate route measurement of actual detour path? closer AS paths are correct Results: 94% of learned detour Detour path AS D AS Y AS X AS C Critical source Victim destination AS E AS J (e. g. , shorter AS-path) Solution: Prioritize measurement from bot closer to traffic source 11
Our contributions Adaptive detour-learning attack against rerouting solutions Practical challenge of mitigating adaptive detour-learning attack Future directions for transit-link DDo. S defenses 12
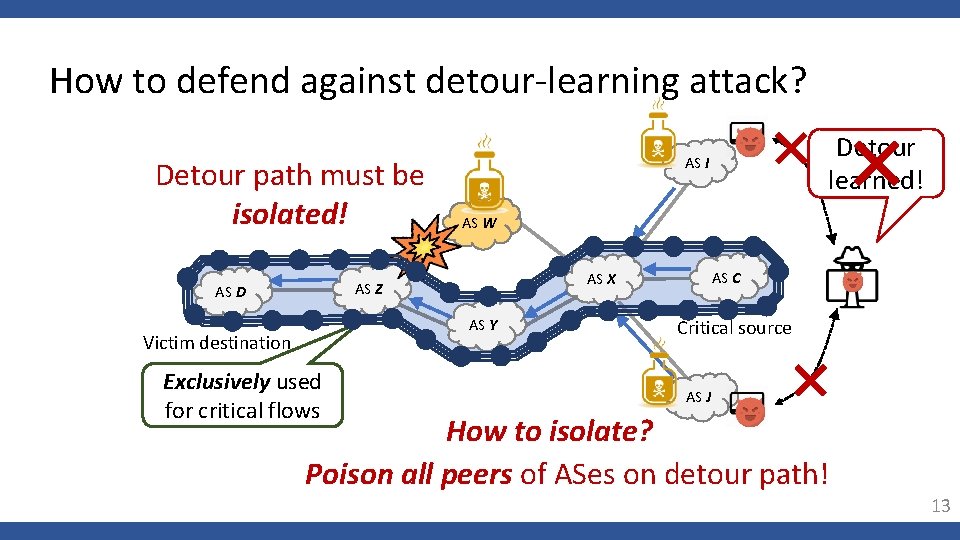
How to defend against detour-learning attack? Detour path must be isolated! AS W AS Y Victim destination Exclusively used for critical flows AS C AS X AS Z AS D Detour learned! AS I Critical source AS J How to isolate? Poison all peers of ASes on detour path! 13
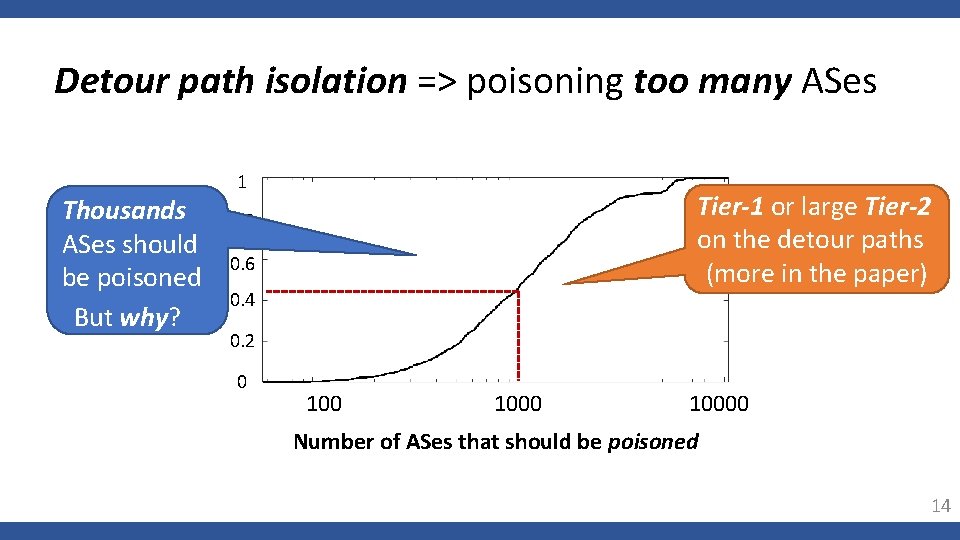
Detour path isolation => poisoning too many ASes Thousands ASes should be poisoned CDF But why? 1 Tier-1 or large Tier-2 on the detour paths (more in the paper) 0. 8 0. 6 0. 4 0. 2 0 10000 Number of ASes that should be poisoned 14
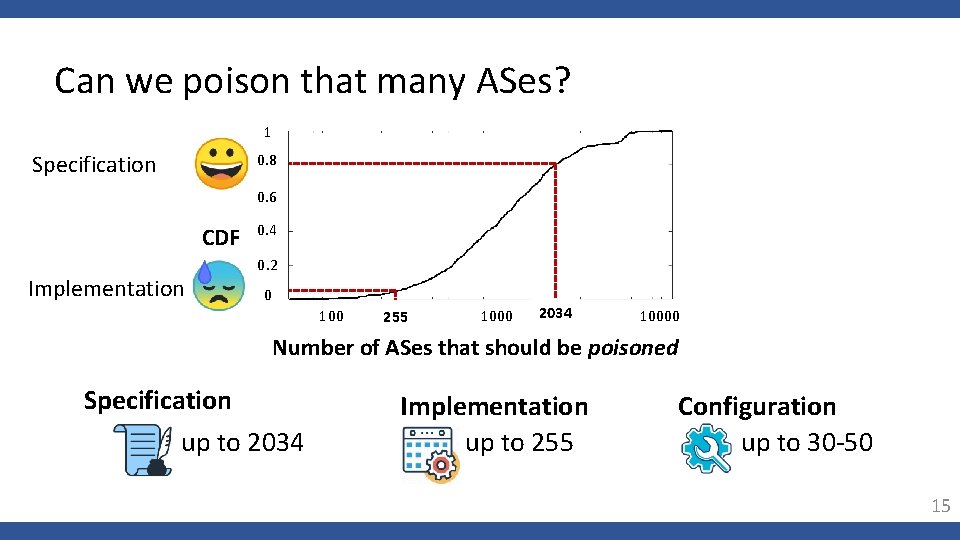
Can we poison that many ASes? 1 Specification 0. 8 0. 6 CDF Implementation 0. 4 0. 2 0 100 255 1000 2034 10000 Number of ASes that should be poisoned Specification up to 2034 Implementation up to 255 Configuration up to 30 -50 15
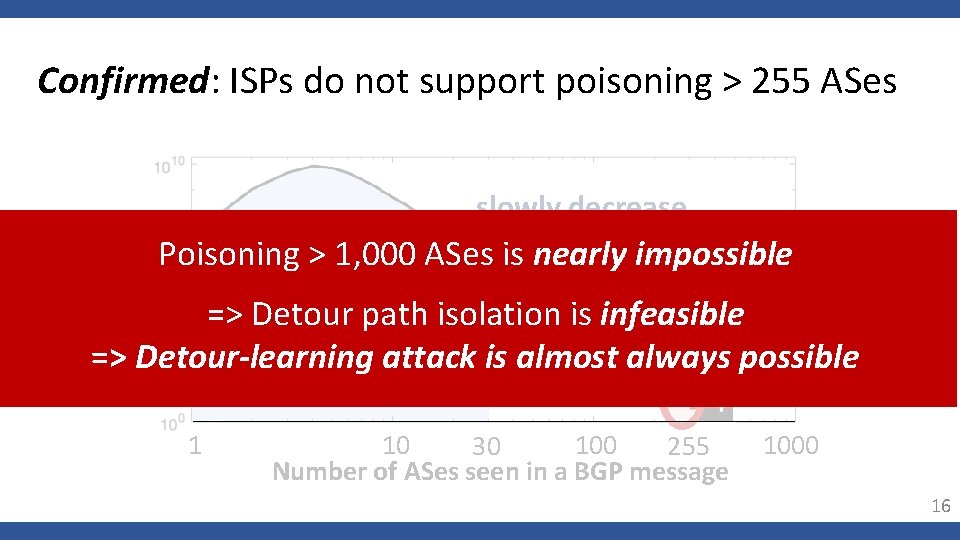
Confirmed: ISPs do not support poisoning > 255 ASes slowly decrease Number of in frequency Poisoning > 1, 000 ASes is nearly impossible observed 50 x drop 99. 99% BGP in frequency => Detour path isolation is infeasible messages => Detour-learning attack is almost always possible 1 10 100 30 255 Number of ASes seen in a BGP message 1000 16
Our contributions Adaptive detour-learning attack against rerouting solutions Practical challenge of mitigating adaptive detour-learning attack Future directions for transit-link DDo. S defenses 17
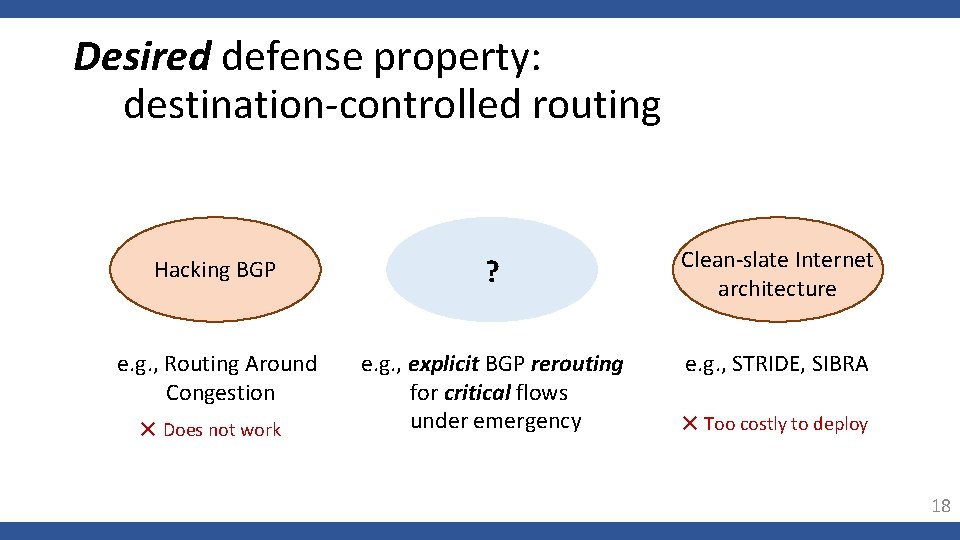
Desired defense property: destination-controlled routing Hacking BGP ? Clean-slate Internet architecture e. g. , Routing Around Congestion e. g. , explicit BGP rerouting for critical flows under emergency e. g. , STRIDE, SIBRA ✕ Does not work ✕ Too costly to deploy 18
Two Lessons Learned 19
Lesson 1 Hacking the current Internet routing is a flawed idea! 20
üAdaptive attacks are possible üMitigation is hard ü Adaptive defense is slower than adaptive attacker (more in the paper) 21
Lesson 2 Analysis of protocol specifications alone is insufficient! 22
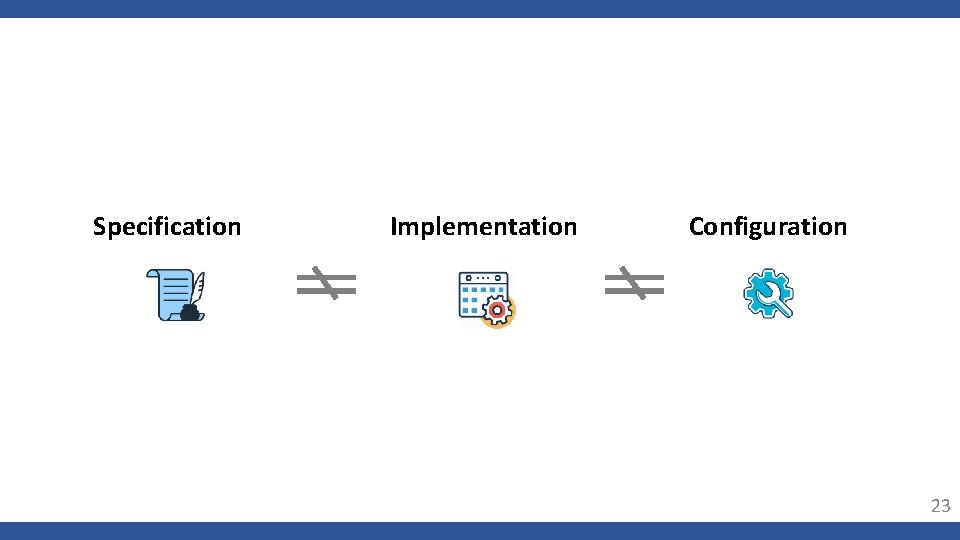
Specification Implementation Configuration 23
Conclusion • Detour-learning attacks are effective and hard to mitigate üTransit-link DDo. S attacks still remain an open problem • Suggestion on research direction üBalance destination-controlled routing and deployability • 2 lessons learned: üHacking BGP for rerouting is a flawed idea üAnalysis with specification only can be dangerous 24

Question? Muoi Tran muoitran@comp. nus. edu. sg
- Slides: 25